►
From YouTube: IETF97-NETMOD-20161117-1110
Description
NETMOD meeting session at IETF97
2016/11/17 1110
A
D
D
Welcome,
thank
you
for
the
help
of
the
door.
We
fail
to
mention
that
we
have
an
acting
secretary
and
we
really
appreciate
his
help.
He
tells
us
to
call
him
Michael
so
we'll
do
that,
but
yeah
there's
his
name
he's
also
been
really
helpful
on
preparing
the
notes
and
he's
the
first
secretary
that
I've
ever
worked
with.
That
has
the
session
written
up
before
well
before
the
second
session
and
serve,
and
certainly
before
the
end
of
the
week,
so
that
that's
a
huge
win
and
we
really
appreciate
this
helped
Michael.
D
We
have
the
note
well
mid-late
week.
We
should
be
familiar
with
it.
Everything
you
say
here
becomes
part
of
our
record
and
you
have
certain
obligations
if
you
contribute
to
the
IETF.
Yes,
we
are
again
running
recordings.
Please
use
the
microphone,
make
sure
your
say
your
name.
We
do
have
the
jabber
room
going
I'm
about
to
jump
in
if
anyone
else
wants
to
jump
in
that'd
be
great.
Most
importantly,
we
have
etherpad
for
collective
crowd-sourced
note-taking,
please
join,
please
contribute
even
if
it's
just
fixing
someone
else's
edits
we're
in
our
second
session.
D
D
D
D
F
E
I'll
go
and
start
so
yesterday
we
had
a
breakout
meeting
in
the
afternoon.
It
was
137
and
we
thought
we
were
joking
when
Kent
gave
us
that
minute
that
many
hours
and
turns
out,
we
actually
used
them
all.
It
was,
I
think,
yeah,
that's
one.
It
was
a
positive
meeting.
It
was,
I
think,
was
it
confirmed
the
design
of
the
of
the
design
team
yeah.
E
E
Eric
had
the
point
that
data
in
running
essentially
appears
immediately.
Sorry,
I,
don't
say
me:
it
appears
in
sync
with
intended.
The
two
are
lockstep
and
there's
also
a
lockstep
relationship
between
applied
and
operational
state
simply
because
applied
can
be
viewed
as
a
subset
of
operational
state.
So
so
those
two
need
to
be.
That
point
needs
to
be
more
clearly
made
that
those
really
are
bound
together.
E
The
other
issue
we
discussed
was
factory
default
configurations,
a
lot
of
devices
when
they
start
up
will
if
the
config
is
length,
zero
or
if
they
know
it's
the
first
boot
or
if
some
magic
happens,
they
will
load
a
default
configuration.
This
is
in
running
or
in
candidate,
and
it's
a
it's.
It's
typically
just
a
static
file
that
gets
loaded
to
point
users
in
the
right
direction,
but
we
want
to
call
that
out
in
the
draft
as
as
expected,
behavior.
E
So
I
want
to
walk
through
some
of
the
examples
I'm
going
to
add
and
and
make
sure,
because
I
think
these
because
I
want
to.
I
want
to
do
two
things.
I
want
to
use
them
as
a
mechanism
of
explaining
the
draft
and
also
as
a
means
of
saying
this
is
what
we're
going
to
put
in
so
that
you're,
aware
of
the
ongoing
work.
E
The
first
example
will
be
a
just
straightforward
configuration
a
full
walkthrough
from
edifact
config
payload
into
running
intended,
applied
and
op.
What
you
shall
state
what
you
can
expect
in
each
of
the
databases,
how
they'll
behave
and
well,
at
the
same
time,
we'll
discuss
the
the
perhaps
an
example
of
inactive
or
template,
or
something.
B
E
To
make
that
more,
to
give
an
example
of
that,
the
the
second
example
we
discussed
was
a
system
system
control
configuration
an
example
of
this
would
be
a
loopback
interface,
where
your
l,
0
0,
shows
up
implicitly
in
your
configuration.
Let's
say
it
shows
up
with
a
127.
2020
got
one
address,
whether
the
user
were
these
e
likes,
whether
the
user
likes
it
or
not.
E
If
you,
if
you
commit
you'll,
see
that
in
applied
and
operational
state
with
the
origin
of
system,
if
the
user,
then
steps
into
the
configuration
and
adds
creates
explicitly
in
their
in
their
configuration
database
that
that
ellos
ero
interface
and
adds
say
a
couple
more
knobs
to
it,
then
then
that
interface
will
now
show
up
in
running
and
and
intended
and
in
applied
an
operational
state
and
the
origin
will
be
static.
It's
a
good
example
of
of
the
different
types
and
how
they,
how
the
how
the
flow
between
the
between
the
database
happens.
E
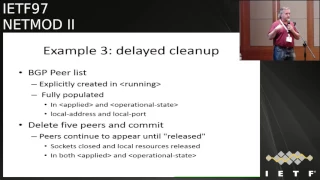
The
third
example
would
be
a
BGP
peer
list.
This
is
something
that's
explicitly,
creating
and
running.
It's
fully
populated
in
in
applied
and
in
op
state,
and
what
I
mean
by
fully
populated
is
no
Leafs
that
aren't
specified
in
the
configuration
will
show
up
an
operational
state.
For
example,
a
local
address
in
a
local
port
that
are
left
unconfigured
will
show
up
in
in
the
applied
in
the
applied
and
operational
state
configuration
I.
E
G
E
E
So
let's
say
you
go
into
your
configuration,
you
delete
55
peers
and
do
a
commit.
There
will
be
a
time
lag
before
those
those
peers
are
actually
removed
from
applied.
They'll
they'll
continue
to
to
exist,
you'll,
be
able
to
see
them
as
the
as
a
responsible
system.
Subcomponent
steps
up
and
does
the
work.
You
know
as
sockets
closed
and
and
resources
are
released.
They
will
disappear
from
applied
and
operational
state.
E
E
It
has
no
installed
through,
so
it
doesn't
appear
in
applied
or
operational
state
when
you
plug
in
your
through
the
responsible
system,
subcomponent
will
create
the
interface
and
populate
it
with
the
data
from
from
intended
and
it
and
and
and
when
the
FRU
isn't
created,
it
will
actually-
or
it
may,
depending
on
the
data
model,
create
additional
additional
objects
like
ports
on
an
interface.
If
the
weather,
the
ports
are
configured
or
not,
they
will
appear
in
the
operational
state
at
that
point
field
replaceable
unit.
Yes,
please.
E
E
E
E
One
other
minor
point
that
was
made
during
the
breakout
was
when
you,
when
you
replace,
when
you
insert
or
through
statistics
for
that
interface,
should
be
reset
to
zero.
It
should
be
a
fresh
new
interface.
You
shouldn't
reclaim
a
interface
statistics
should
not
persist
from
a
previous
incarnation
of
that
object,
and
the
key
here
which
I
think
is
made
in
this
point,
is
made
in
the
yang
RFC
as
well.
The
key
is
that
we
don't
want
fruits
to
break
configuration.
Your
configuration
state,
your
configuration
validity,
should
not
depend
on
cruise
in
the
box.
E
E
You
know
we
want
to
talk
about
how
data
is
merged
between
between
dynamic
data
stores
and
intended
into
active
and
I.
While
writing
the
slide.
I
think
I
came
up
with
another
issue
from
the
draft.
In
the
original
picture
we
had
lines
going
into
into
our
data
stream
between
active
and
operational
state
and
I.
Don't
believe.
That's
accurate,
because
operational
state
is
this
is
a
proper
subset.
Of
sorry.
Active
is
a
is
a
proper
subset
of
operational
state.
So
all
the
config,
true
knobs
in
operational
state,
should
appear
in
active.
E
E
E
So
we
went
through
the
issues
list.
The
first
issue
was:
do
we
need
an
active,
which
is
why
it's
stuck
in
my
head?
Do
we
need
an
active
data
store
simply
for
the
removal
of
inactive
nodes,
and
the
consensus
in
the
in
the
breakout
session
was
that
we
do
not
that
intended
serves
that
purpose
and
it
serves
it
without
specifying
how
any
any
templating
mechanism
or
expansion
interacts
with
inactive
and-
and
we
can
continue
to
ignore
that
until
it's
defined.
E
We
talked
a
bit
about
the
constraints
on
applied
and
operational
state
in
general,
there's
a
feeling
that
that
these
should
apply,
but
the
device
should
be
able
to
send
send
data
as
accurately
as
possible.
For
example,
if
there's
a
constraint
that
says
you
know,
many
elements
is
seven
and
you
actually
have
one.
E
You
should
send
that
you
have
one
you
shouldn't
feel
like
you
have
to
make
up
six
fake
ones
simply
to
satisfy
their
the
constraint
of
the
data
model,
the
the
particular
one
that
we
that
we
really
that
we
really
feel
should
be
like
a
very,
very
should
is
when,
because
that
that
will
break
expectations
of
what
data
is
received.
If
you
say
you
know
these
this,
this
augmentation
happens
when
the
interface
type
is
sonnet
and
you
start
showing
those
that
object
on
Ethernet
or
or
or
any
other
interface
type.
The.
E
H
E
E
We
talked
a
bit
so
the
next
issue
is
applied
in
rest
comp
and
after
talking
about
it
a
bit,
we
decided
that
that
wasn't
an
issue
we
were
going
to
take
on.
We
were
going
to
push
it
off
to
the
networking
group
in
in
general.
I
just
want
to
remark
that
there's
a
still
a
disagreement
about
the
goals
of
rest
comp
is
it:
is
it
a
another
means
of
getting
to
net
comp,
or
is
it
some
sort
of
easy
button
for
programmers
who
want
an
easy
button?
E
C
D
C
A
Hi
Dan
Bogdanovich,
on
behalf
of
the
design
team,
presenting
the
work,
the
update
on
the
thing
they've
been
working
since
the
Berlin
IDF.
Since
then,
we
added
three
new
members
to
the
design
team,
urban
areas,
jus
Fangio
and
Ian,
Jenn
zoo
so
kudos
to
them
into
the
new
work
and
energy
they're
bringing
to
the
team
next
slide.
Please
give.
A
A
So
the
what
when
we
started
originally,
we
started
with
a
metamodel
for
the
whole
device
and,
as
we
were,
building
that
we
were
realizing
that
the
elements
that
we
have
to
build
inside
this
one
graph
was
in
or
getting
too
complicated,
and
we
split
it
up
into
three
drafts.
So
the
basic,
essentially
draft
the
device
model
draft
how
to
organize
is
essentially
a
very
simple
draft
which
says
just
the
basics
of
the
model
and
then
the
logics
of
that
are
in
the
eleanii
and
in
the
NI.
A
A
Okay,
so
on
that
part
is
when
we
were
creating
the
LME
model
and
the
NI
model.
The
idea
there
is
that
you
get
a
basic
object
and
then
you're
assigning
resources
to
that
object,
because
we
have
to
assign
multiple
and
we
don't
know
what
the
user
within
the
administrative
the
domain
wants
to
run,
what
protocols,
what
interfaces
have
to
be
assigned
and
not
all
Ella
knees,
are,
you
know,
created
the
same.
A
We
had
to
find
out
how
to
mount
external
modules
into
that
module
that
has
been
created
for
that
we
have
been
using
scheme
amount
and
for
most
of
the
use
cases,
the
scheme
amount
is
answering
the
requirements,
but
for
some
of
them
we
had
to
come
up
with
some
new
ideas,
and
for
that
we,
you
know.
We
have
a
here
proposal.
A
A
After
that,
the
administrator
of
that
device
is
adding
resources
like
interfaces
to
that
is
having
hard
resources
like
interface
and
QoS
capabilities
to
that
lme,
and
then
the
administrator
of
that
lme
is
starting
to
mount
network
modules
that
they
need
inside
that
L&E.
That
means
they
have
a
mount
protocols.
They
want
to
use
and
other
network
services
that
they
need
for
that
one
and
they
don't
want
to
administer
by
themselves.
A
So
the
problem
there
is
that
it
works
nicely
for
Network
for
most
network
services,
except
for
hardware,
specific
resources
like
interface,
and
we
had
to
figure
out.
How
can
we
map
scheme
amount
and
interface
without
because
that's
a
shared
resource
and
then
how
to
figure
out
how
to
share
that
resource
between
two
administrative
domains?.
I
You
go
back
to
the
previous
slide
17
because
you
skipped
over
the
thing
about
our
PC
operations
and
I
was
just
going
to
point
out
that
actions
and
nested
notifications
will
just
work.
They
just
you
know
it's
just
a
different
path
to
the
node
in
it.
They
can
still
work
in
there.
They're
relocatable,
our
pcs,
are
always
at
the
top
level
and
they're
always
going
to
be
a
problem
because
the
top
level
you
want
to
shift
down
into
the
eleanii,
but
actions
if
you.
J
A
To
the
ideal
that
they
would
be
all
available
but
from
the
real-life
use
cases
dead
folk,
definitely
we
will
have
to
see
how,
because
people
might
add
modules
later
after
the
eleanii
has
been
accentuated
and
then
how
to
add
those
new
modules
that
has
been
created,
because
the
question
is
how,
once
you
create
an
eleanii,
and
you
have
a
new
service
that
you
want
to
add
to
that
eleanii?
How
will
you
add
it
to
it?
Will
it
be?
D
J
In
scheme
amount
in
general,
we
assume
that
there
will
be
use
cases
similar
to
pier
mount
very
really.
The
schemas
is
supplied
dynamically
at
runtime,
okay,
great.
What
I
was
wondering
whether
it
is.
It
could
be
also
this
case
or
if
you
really
assume
that
you
can
just
you
know
everything
in
advance.
We.
D
J
A
Based
on
how
the
based
on
administrative
decisions,
how
many
interfaces
will
be
assigned
to
a
particular
eleanii,
is
it
one
or
one
hundred
we
never
know
that
depends
on
the
device
you
know
capacity,
so
we
have,
you
know
essentially
some
ideas
how
to
solve
that.
We've
been
looking
into
the
HTTP
protocol
in
order,
you
know
how
how
to
do
that,
it's
the
mod
rewrite
and
if
somebody
else
have
some
other
ideas
how
to
do
that
it.
This
would
be.
You
know
for
discussion
and
we
discussed
the
de
la
de
edad.
J
Kosh
I
think
that
there
is
some
confusion
about
terminology
here,
because
even
if
you
use
absolute
xpath
like
xpath,
it
means
that,
even
if
it
is
absolute
that
it's
really
confined
to
them
mounted
itit
rewrite
so
that
the
route
that
address
by
by
a
slash
in
XPath
expression
is
is
just
the
mount
point.
So
there
is
no.
J
All
right,
so
what
we
are
talking
about
is
to
either
and
then
some
notation
how
to
get
out
of
this
mouth
jail
so
to
say
and
reach
something
that's
outside
or
which
I
think
is
maybe
but
approach
that
Lou
suggested
to
invent
some
way
how
the
mounted
betatry
can
borrow
stuff
from
like
some
kind
of
symbolic
link,
or
things
like
that.
So
we
have
to
really
discuss
this
so.
A
We
have
to
always
there
are
some
complications
there,
because
we
have
to
think
about
the
administrative
rights
to
access
this
information
as
you're
going
down,
because,
if
you're
passing
you're
creating
administrative
domain
within
the
administrative
domain.
But
it
doesn't
then
also
pass
the
administrative
rights
from
the
upper
domain
to
the
lower
domain.
The
lower
box
can
be
completely
black
box
and
you
have
them
to
make
sure
that
the
you
cannot
read
from
one
to
the
other
and
what
you
essentially
do
code.
A
So
on
the
Upstate,
we
are
essentially
tracking
what
the
net
mod
design
team
is
doing.
In
many
places
we
are
leaving
the
Upstate,
you
know
as
the
placeholder
and
based
on
that,
what
the
the
design
team
will
come
up
with
the
recommendations
and
how
will
they
not
do
that?
We
will
essentially
follow
up
on
that.
So
on
the.
A
A
Okay,
so
in
that
case
you
know,
based
on
this
new
recommendations,
you
know
when
they
come
out.
We
will
end
with
the
you
know.
If
this
will,
as
the
work
world
process
on
that
part,
will
be
upgrading
between
the
versions
the
drafts
that
we
are
working
on
so
on
the
conventions
this
is,
you
know
the
kudos
to
the
new
guys
that
have
joined
us
and
they
have
been
working
on
that
on
that
part.
A
I
am
a
little
bit
weak
because
I
be
no
read
it,
but
on
going
into
details,
if
you
ask
me,
I'll
have
to
ask
the
if
somebody
from
the
troupe
of
Shiva
he's
here,
so
he
would
be
able
to
know
to
give
you
more
information
and
provide
you
with
more
details
on
that
part.
But
essentially
you
know
what
we
have
done.
Is
we
initially
or
what
the
team
did?
Is
they?
A
K
One
on
a
previous
one:
it's
a
very
good
item.
Don't
try
to
make
it
perfect,
we
need
types
now
the
value
will
be.
One
of
us
will
be
reused
by
older
fan,
yang
models.
One
more
thing
we
created
in
the
hackathon
yang
model,
search
in
which
you
can
have
like
any
field
search
certain
a
typedef.
You
can
search
type
that
on
the
entire
set
of
young
models
that
I
know
of,
and
make
sure
that
you
have
the
consistent
set
of
the
of
types
that
would
be
great
work.
L
K
I
typed
that
for
multicast
this
is
just
one
one
of
the
examples.
While
I
was
reviewing
a
document
in
which
I
was
a
multicast
type
death
and
then
I
was
relating
to
to
your
draft.
I
was
asking
a
question:
should
we
include
that
there
now
I
don't
have
the
answer
to
that
you
decide,
but
whatever
you
do,
make
sure
it's
consistent
across
all
yang
models,
if
not
consistent,
discuss
with
the
author
white,
not
and
publish
vast.
M
Michael
far
away
and
just
the
same
question
about
matic
has
two
young
type.
We
defend
this
medical
station
high
winds,
a
generic
la
om
Yamato
since
we
need,
is
a
semantic
asked
to
you
note
to
using
the
CC
and
the
series,
our
pcs,
but
we
didn't
founder
the
same
definition
to
young
type,
I
underst
Yun
type,
so
we
just
friended
I
know
we
don't
want
to.
The
final
is
in
danger:
I'm,
not
a
strong
feeling
to
deciding
to
find
is
a
18
choose
a
lime
module,
but
we
will
also
want
to
reuse
another
young
world's.
D
M
M
N
Cylinder
ma
cisco
systems
and
routing
a
design
team
yeah.
I
think
what
then
was
said
is
for
this
to
be
useful.
We
have
to
move
fast
on
it
so
that
we
can't
make
it
be
a
bottleneck
for
the
other
models
that
we
want
to
get
in
the
initial
set
and
standardize
them,
but,
but
if
so,
if
you
could
move
fast
on
what
things
you
think
would
be
common
to
others
and
send
them
to
us.
M
D
Great,
thank
you.
So
one
interesting
thing
here
is
to
note
that
this
document
is
well.
It's
coming
from
the
routing
yang
design
team.
Their
product
is
aimed
at
the
routing
working
group.
So
that
means
that
there's
some
common
types
that
are
headed
there
rather
than
here
from
my
standpoint,
I
just
want
them
defined
and
I.
Don't
it's
not
so
important
to
me
where
what
model
they
come
in,
but
I
want
to
make
sure
that
the
group
is
aware.
C
A
A
There
is
a
draft
that
this
past
the
discuss
mode,
no
classification,
but
that
was
just
you
know,
giving
basic
guidelines
and
the
idea
there
was
that
the
developer
of
the
modules
are
able
to
classify
because
they
know
the
intention
of
the
module.
So
they
can
do
a
basic
classification.
Is
the
device
model
or
is
it
the
service
module?
A
There
are
some
different
thoughts,
but
some
of
them
is
to
be
completely
no
just
on
structured
string
and
the
other
one
is
to
put
at
least
you
know
some
guidelines
on
how
to
do
it.
But
allah
leave
majority
of
the
of
the
attack
to
be
privately
constructed
because,
as
you
know,
each
librarian
might
have
in
their
own
way
how
to
do
structuring
of
the
of
the
books
or
the
data
what
they
are
keeping.
So
for
that
reason
you
know
we
are.
A
D
A
L
Hi
I'm
mischief
Emilio.
This
draft
is
by
Helen
chin
and
she
cannot
be
here
today,
so
I
justá--
to
the
print
edition
instead,
and
so
we
have
some
become
specific
specification
requirement
here.
Each
namespace
in
the
model
need
to
be
unique,
color,
blue
and
also
the
module
name
and
the
sub-module
names
I'll
need
to
be
unique.
So
what
do
we
do?
Is.
L
Yeah,
so
this
is
a
the
draft
was
up
attended
here
before
and
also
called
comments.
So
there
are
some
revisions
and
updated
after
that,
so
the
the
drives
trying
to
solve
the
issue
about
how
do
we
do
the
naming
so
currently
and
many
companies
are
writing
their
own
enterprise
models
and
with
the
different
ways
some
YouTube
URL,
some
user.
You
are
in
and
each
has
its
own
convention,
so
there's
a
risk
to
hide
the
name
conflict.
So
here
basically
we're
trying
to
define
a
top-level
name.
L
So
then,
after
this
top-level
names,
and
that
each
organization
can
refine
the
name
and
define
the
sub
system
for
their
own
naming
convention,
so
the
whatsits
top-level
name,
we
can
still
discuss
and
can
come,
but
here
the
proposed
kind
of
Apollo's
18s,
reverse
it
penis.
So
here
the
grammar
would
be
like
this,
so
I
top-level.
L
L
Example
would
be
say:
some
company
you
can
I
become
company,
want
to
have
their
own
ospf
model,
so
what
they
do
would
be
after
there's
a
top-level
name.
They
put
com
example
and
then
put
the
young
name
there.
That's
my
only
so!
Oh
that's
it.
So
this
is
a
the
request
for
this.
A
name
registration
was
written
in
another
draft,
so
also
revealed.
So
basically
we
come
to
the
working
group
trying
to
get
consensus.
So
we
need
to
have
this
because
many
informations
implementations
are
going.
F
L
So
those
are
for
the
vendor
specific
modules
buttery
from
vendor.
Trying
to
I'll
comment
is
a
standard.
Amodio
then
can
be
falling
into
the
disc
Academy
anyway,
so
they
said
your
own
augmentation.
So
if
you're
don't
want
to
standardize
nobody
or
care,
so
you
have
your
own
naming
convention.
Let's
hop
to
you,
okay,
so.
C
F
L
F
D
F
O
Mike
so
Tim
Carey,
just
to
let
you
know,
we've
done
the
same
thing
with
the
BBF
we've
and
I.
Are
we
standardized
what
we
put
for
yang
modules
for
our
templates
and
we
actually
just
do
it
a
little
bit
different?
We
we
use
the
we
used.
We
place,
we
don't
we
don't
do
yang,
then
the
company
we
do
the
company
than
the
yang.
So
we
just
kind
of
swap
those
two
positions
around
a
bit.
So
it's
you
RN.
You
know
BBF
yang,
then,
whatever
we
do
right.
L
L
After
you
are
in,
say
you
you
may
have
you
are
in
comm
the
cisco
and
another
people
was
some
other
organization.
You
think
you
are
an
income
dioxin
out
such
then
you
may
have
you
are
your
us.
You
are
a
dt,
the
whatever
its
sorted,
because
you
can't
do
anything
right
so
here
this
is
a
there's,
no
rules
here
so
I'd.
Here
we
only
trying
to
suggest
a
top-level
token,
so
you're
quibbling
to
your
PBS.
L
O
L
O
L
D
O
H
H
C
It's
going
to
have
to
be
a
recommendation
and
that
no,
in
fact
the
existing
namespace
using
HTTP
would
still
be
valid,
but
you
know
there'd
be
as
sixty.
Eighty
seven
is
is
that
would
you
know,
suggest
people
to
use
your
n
because
it
doesn't
have
the
appearance
of
a
URL
that
you
can
click
on
and
resolve
to
a
page.
It's
better
that
way,
yep
but
of
course
the
Cisco
or
others.
You
know
stos
are
using
your
ends
of
their
own.
C
F
F
L
D
C
E
P
C
L
L
D
Think
of
it
this
way,
the
proposal
is
for
the
case
that
you
are
using
a
namespace
that
begins
you
RN
and
it's
a
private
namespace.
Here's
a
format
that
must
be
followed
is
that
something
may
be
no
must
be
followed
if
you
start
with
you
RN
and
doing
private.
If
we
go
down
this
path,
that'll
be
a
must.
Is
that
something
that's
worthwhile,
so
you
can
still
start
with
HTTP
there's
nothing
wrong
with
that.
It's
because
you're,
not
viewing
aur
n,
I'm
not
I'm
not
advocating
I'm
stating
what
the
options
are.
E
D
It
seems
like
there's
a
class
of
people
who
care
about
this
and
there's
a
class
that
don't
okay,
that's
the
way,
I
read
it.
The
question
is:
is
there
enough
in
the
working
group
who
read
it
that
as
useful
that
we
should
pursue
it
as
a
working
group?
I
do
agree
that
we
shouldn't
we
shouldn't
end,
can't
break
current
usage.
Okay,.
F
D
I
agree
with
you,
but
that's
that's
my
personal
position,
not
chair
position
so
again
how
many
think
that
this
type
of
solution
is
something
we
should
be
good.
Excuse
me
working
on
is
this
a
problem.
We
should
be
worked
out
dressing
in
the
working
group,
so
it's
less
people
but
I
think
it's
still
a
reasonable
number
who
many,
how
many
think
it's
completely
useless.
I'm
gonna
ask
a
third
question
after
this
completely
uninterested,
so
it's
slightly
less.
How
many
think
that
it's
a
mistake
for
us
to
go
down
this
path?
D
This
one's
gonna
be
so
good
smell
this
one's
a
little
unusual
in
terms
of
what
we
normally
do.
This
isn't
a
proposal
but
more
of
a
report
on
some
experience
of
a
implementation
as
a
chair,
I'm
a
little
uncomfortable
that
the
culprit
name
is
being
mentioned
so
much,
but
I
still
think
it's
valuable
information
to
hear
about
an
implementation.
So
next
time
you
do
an
implementation
report,
just
drop
off
your
company
name
from
melt
all
over
the
place.
B
P
Q
Okay,
so
the
problem
here
is
that
the
sequence
key
in
the
IETF
model
for
an
ace
is
the
alphanumeric
string.
Well,
it's
not.
The
problem.
Ietf
model
defines
it
that
way
in
iOS
XR
in
/
ace.
We
configured
the
ace
on
a
sequence
number,
so
we
had
a
problem
on
how
we
map
the
rule
name
to
a
sequence
number
now.
This
was
a
problem
because
all
our
data
structures
as
system
data
stores
everything
index
it
by
a
sequence
number,
and
then
we
have
to
change
things
to
accommodate
an
alphanumeric
string.
Q
It
really
became
an
issue,
so
we
came
up
with
an
algorithm
on
how
we
reuse
Cisco's
current
implementation,
and
we
accommodate
the
IETF
alphanumeric
string
as
well.
So
there
are
four
steps
to
the
high-level
algorithm.
The
the
first
step
is
that
when
we
get
a
Yank
data
tree
request,
an
edit
config
request,
we
first
look
up
the
MSS
DB
data
store
to
find
the
existing
ACL
and
we
create
a
on-the-fly
data
structure.
To
represent
this.
We
then
read
all
the
Edit
config
operations
in
the
yang
framework
data
tree
and
we
then
walk
through
the
data.
Q
Q
Q
C
Q
Sure
so
this
is
a
replace,
so
this
actually
just
tells
us.
The
algorithm
I
have
a
few
examples
on
this,
but
we
can
go
through
create.
So
let's
say
before
we
had
an
ACL
with
sequence
numbers
10,
20
30
and
the
alphanumeric
string
is
a
B
and
C.
So
on
the
right
side,
so
we
actually
have
an
algorithm
that
map's
10
to
a
22,
B
and
32
C.
So
now
let's
say
we
have
to
create
ad
so
because
the
default
operation
is
to
put
it
right.
Q
Replace
is
kind
of
interesting,
because
here
you
have
just
say
you
want
to
replace,
be
with
E
and
insert
after
a
so.
What
you
do
is
that
you
find
where
B
is
you
replace
it
with
E
and
also
put
be
in
the
delete
queue,
because
that
is
a
specific
delete
request
that
has
to
go,
and
you
insert
e,
giving
it
a
sequence
number
and
followed
by
see
whose
sequence
number
is
unchanged.
Q
Delete
is
fairly
straightforward.
The
last
slide
deals
with
how
Cisco
augmented
the
IETF
ACL
model.
This
is
a
fairly
simple
augmentation.
Where
have
in
the
ingress
and
egress
you
have.
You
can
have
a
v4
v6
and
esa
CL,
and
this
particular
example
only
allows
one
ACL,
but
I
think,
as
we
progress
there'll,
be
further
extensions
to
this,
because
different
platforms
and
running
XR
accommodate
different
number
of
acs
on
the
interface.
N
C
As
Sheppard
I
previously
pulled
for
IPR,
there
was
none
and
also
it's
okay,
cool
and
also
thank
you
for
showing
this
implementation
also
add
Andrew
pagana
vetch
also
had
mentioned
that
a
volta
had
done
an
implementation
of
the
ACL
draft.
So
two
implementations-
this
is
great
and
as
the
Shepherd
I'm
gonna
make
it
was
a
very
easy
right
up
for
me.
So
thank
you
very
much
and
oops
sorry,
Dan
126
again
well,.
A
We
found
out
in
the
young
model
that
we
could
do
optimization
in
the
ITF
packet
header
in
the
idea
packet
Heather
model,
because
the
we
matched
the
we
did
the
leaves
for
the
Heather
matching
instead
of
using
a
leaf
list.
If
we
would
change
from
leaf
to
leaf
list
it
would,
it
would
allow
us
to
create
entries,
AC
entries
about
say
terms,
but
it's
AC
entries
where
we
could
have
multiple
match
conditions
in
the
you
know,
single
line
with
an
action
at.
N
A
C
So
let's
take
this,
the
list
I
think
you
already
put
an
email
to
this
right
now
and
I
need
to
reply
to
that
as
Shepherd
and
decide
whether
or
not
we
need
to
pull
this
back
to
the
working
group
consideration.
But
to
my
impression
is
it
looks
like
its
effect
of
scalars
becoming
a
vector
and
it's
a
safe
change.
