►
From YouTube: IETF98-IPSECME-20170329-1300
Description
IPSECME meeting session at IETF98
2017/03/29 1300
C
Okay,
let's
start,
then
the
should
be
already
going
around,
and
this
is
that
this
ipsec
Amy
rocky
group
meeting
and
if
people
are
still
talking
they're,
going
to
be
minutes,
takers,
Oh
Michaels,
will
entail
and
right
yeah
wait.
So
this
happy
second,
even
working
group
I'm
take
one
of
the
chairs
that
up
giving
in
this.
D
C
Wall
Trier
next
are
to
have
larger
slice.
Ok,
this
is
the
note.
Well
I,
guess
all
you
will
note
it
already.
So
next
one
so
we
have.
The
blue
seats
are
actually
one
blue
sheet,
calling
around
they'd
put
the
other
one
with
the
shirts.
So
few
of
us
here
and
tell
you
like
it.
No
takers
and
my
clothes
already
saying
yes
right,
the
note-taker,
how
it
could
anybody
else
want
to
help
Michael
it
all
right,
good,
okay,
then
I
think
we
already
have
a
chopper
scribe:
okay,
okay,
all
right!
So
next
one!
C
So
so
these
are
our
chinta
I
had
with
modified
it,
since
they
I
posted
his
first
time.
There's
got
to
be
a
little
more
discussed
about
the
algorithm
documents
and
there's
going
to
be
perhaps
the
minimal
ESP
stuff
in
the
end,
depending
if
you
have
time-
and
we
should
have-
because
we
have
half
an
hour
more
time-
demurrer
origionally
supposed
to
have
any
comments
or
changes
or
something
that
any
other
items
people
want
to
put
in
the
end.
C
Okay,
go
to
the
next
slide,
all
right,
so
I
question
to
monitor,
implement
algorithmic.
There
is
no
issues
in
ganar
door
of
the
ER.
There
was
some
minor
needs,
insecure
and
the
IST
was
actually
reading
relevant
because
they
notice
that
there
is
an
inconsistency
there.
It
says
the
triple
disease.
The
text
says
it
should
not
and
the
table
same
a
and
I
think
they
may
is
actually
the
correct
one.
C
This
is,
it
has
been
may
originally
that
the
should
not
text
was
editor
in
the
way
back
there
in
a
text,
and
we
test
I
think
it
was
because
you
know
we
added
get
the
same
text
today.
You
know
other
document
at
the
same
time
and
it
is
suit
not
in
in
for
ipsec
the
ESP,
because
there
is
a
problem
with
the
IV's
which
I
question
too.
It
doesn't
matter
whenever
condition
that
much
data
editor
the
good
bit
short.
C
You
know
blockcount
actually
matters,
so
we
actually
can
keep
it
as
a
may
here
and
that
reasonably
I
think
values.
Okay
is
because
it
was
the
mandatory
implement
before
that,
so
moving
it
from
monitor
to
implement
too
much,
they
should
notice
actually
something
that
this
bit
to
trouble.
There
is
no
reason
to
be
anything
of
them.
So
if
anybody
has
any
comments
on
this.
F
G
C
So,
okay
go
to
the
next
slide.
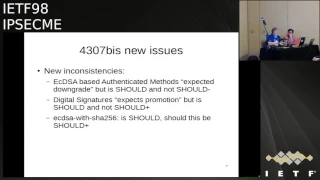
Okay,
these
are
new
issues
and
I
removed
one
of
those,
your
new
issues,
because
I
don't
think
it's
nice
and
there
was
also
text
about
saying.
Cha-Cha
20
isn't
ensued,
but
it's
not
enough
for
should
plus
at
that
divorce.
No
I
have
said
an
email
about
that,
but
anyway,
so
you
have
some
inconsistencies
there.
That
sucks,
I
think,
are
all
of
them.
Are
international
I
think
there
are
supposed
to
be
this,
but
we
can
actually
talk
about
those.
So,
first
of
all
is
this
ecdsa.
C
It
text
says
that
they're
expect
to
be
downgraded,
but
they
still
suit
and
it's
not
suit.
My
nose
and
I
think
that's
actually
is
correct,
but
it's
something
that
we
say.
Yes,
we
are
going
to
be
in
the
future.
We
are
going
to
be
a
grainy,
but
you
are
not
wrong
creamy
that
yet
because
we
don't
know
what
is
going
to
be
going
happen
with
them,
and
that's
that's,
of
course,
one
of
the
things
we
can
discuss,
but
but
I
so.
E
C
I
think
I
think
the
current
I
think
the
current
view
is
that
there
is
no
there's,
no
hash
negotiation
there
and
the
other
thing
is
that
people
are.
If
everything
goes
fine
and
we
start
using
EDD
SI,
then
we
are
going
to
be
their
abilities,
but
if
we
don't
move
to
the
ecd
EDD
SI
tell
me
I'm.
Actually,
sorry!
Next,
if
you
don't
move
to
do
know
the
curve
top
photo
593,
not
EDD
SI,
but
there
you
know
safe
curves,
then
the
enemy.
C
This
is
this,
is
this
is
easy,
the
other
catching
it
on
ecdsa.
Yes,
sir
yeah
yeah,
so
so
so
that's
why
I've
actually
think
that
they
should
be
still
okay
because
I
we
don't
have
a
you
know
what
this
code
to
be
replacing
it.
Didn't
we
don't
see
what
is
going
to
be
replaced,
but
we
can-
and
we
can
see
that
there's
people
saying
that
these
are
not
so
good.
C
I
J
Right,
I'm,
fine
with
either
should
we
perhaps
rather
than
I,
should
look
at
the
text
again.
The
rather
than
saying
just
expected
downgrade.
Should
we
mentioned
specifically
what
we
think
is
replacing
like
we
mentioned.
If
EDD
sa
is
being
used,
if
the
safe
curves
are
being
used,
that's
likely
path
is.
C
Maybe
would
be
the
working
class
go
yes
if
we
would
be
in
a
working
group.
Last
call.
Yes,
we
would
modify
that,
but
many
of
you
are
pasta.
Tell
us
what
I
used
to
have
to
approve
it.
I
don't
want
to
do
any
extra.
You
know
the
text
changes
that
are
not
mandatory.
You
know
you're
not
really
needed
they.
You
know.
The
Triple
S
is
clearly
inconsistent
in
the
document.
C
This
is
it
it's
us
we
are
saying
sued
and
let
me
say
that,
yes,
this
might
go
down
it,
but
it's
not
in
a
day
and
then,
for
example,
for
the
next
one,
the
digital
signatures
it
says,
expect
to
be
promoters
promoted
in
the
future
from
suits
to
shoot,
plus
or
subtract.
That
reason
why
it's
not
suit
plus
now
is
that
we
don't
have
enough
implementations
to
actually
see
if
it's
it's
going
to
be
gaining.
You
know
it
updates.
It's
the
same
thing
with
the
shot
chart
20
it's
it.
C
C
C
K
C
That's
right,
that's
why
it
should
show
the
meaning
that
the
s
you
should
implement
it
and
it
most
likely
might
be
it
might
be
the
marsh
mandatory
implement
argument
all
then
we
call
the
ad
DSA
I'm,
not
sure.
That's
actually
one
of
the
things
I'm,
not
sure
cool.
This
one
is
going
to
be
the
next
to
mandatory,
implement
our
business.
Edd
essay
or
you
know
the
digital
signatures
right
in
just.
J
C
J
C
C
C
Okay,
if
people
agree
on
that
and
that
denied
exactly
just
these
are
just
something
text
at
web
and
if
it
would
be
last
call
yes,
we
could
actually
text
and
think
about
this,
but
when
we
are
this
far
far
away-
and
we
hopefully
are
going
to
be
issuing
this-
you
know
as
a
new
proposed
algorithms
or
monitoring
rambro
algorithms
faster
than
you
know
what
it's
ten
years,
that
they
take
it
for
the
last
time.
So
hopefully
the
you
know
in
five
years
or
three
years
we
actually,
but
we
come
back
to
this.
Oh
so.
E
C
D
A
C
Let's
go,
the
next
issue
is
said:
ESP
algorithm,
so
there
is
also
same
things.
You
know
we
have
some
reviews,
nothing
stuff,
some
minor
needs
and
so
on.
But
this
is
the
issues
in
from
the
is
T.
So
diversity
is
that
is
obsoletes.
The
cemetery
to
one
in
cryptographic,
communists
only
and
I
think
agree
that
the
cryptographic
is
completely
obsolete.
Where
there
are
a
mix
of
trucks,
remove
it
appear,
so
they
are
happy.
Then
the
Manoir
Keating
is
something
that
actually
needs
to
be
having
some
texted.
That
actually
is.
C
The
current
text
is
they're,
saying
that,
okay,
if
you
use
bonded
manual
keys,
you
must
use
a
yes
CBC
mode
and
I
think
that
section
of
us
a
little
bit.
It
is
just
trying
to
say
that
okay,
that's
value
it's
Monday
through
tu
no
use,
but
but
the
pundit
reduce
that
monitor
tune.
You
know,
implement
it's
not
supposed
to
do
its
monetary
use,
so
that's
actually
something
that
we
need
to
fix,
and
it
there
is
also.
C
E
To
be
very
close
to
a
target,
all
he
did
yes,
okay
here
we
go
so
yeah
I
already
have
to
effect
on
and
you're
right.
Basically,
we
just
concluded
at
CBC
was
the
only
one
you
could
use
so
we
set
must,
but
we
should
really
say
these.
These
alligator
cannot
use
because
of
manual
keating
and
guaranteed
counters
and
ID's.
You
cannot
use
these
algorithms,
so
if
you've
I
have
texted.
C
To
flip
it
around
yeah,
but
actually
I,
don't
know
what
would
be
the
difference
between
the
Blowfish
ESP
or
you
know:
ASC,
pcs,
prophecy,
ABC
or
ASC
busy
yeah,
but
anyway
anyway
meet
me
yeah,
yeah
yeah,
but
anyway.
So
I
would.
I
would
say
that
you
know
the
monetary
monarchies
visit
uni
and
we
should
actually
not
say
any,
but
you
squeezed
oj
implementations.
That's
what
other
thing.
L
L
L
C
L
C
Currently,
it
says
that
the
monarchy
is
is
not
to
be
used,
as
is
inherited
dangerous
and
I.
Think
the
axe
actually
say.
Let's
talk
about
you
and
I
think
that
actually
is
good
for
single
use,
because
actually
there
is
people
are
going
to
be
implementing
man.
Work
is
anyway
because
it's
some
cases
useful
for
debugging
and
so
on,
and
you
know
testing
type
of
thing.
So
I
don't
know
two
people
to
say
that.
Ok,
you
are,
you
are
not
confirmed
confirming
too,
you
know
this
RFC.
C
If
you
happened
to
implement
man
working
and
it's
actually
sometimes
people
actually
use
it
to
plug
into
different
key
marysville
protocols,
but
anyway,
so
so
I
think
it's
very
such
a
that
it
should
use.
It
should
not
be
used
to
it's
correct
there,
but
then
it
we
know
which
algorithm
is
actually
very
difficult.
I
think
we
actually.
This
is
something
that
we
can
solve
here.
I
think
we
actually
should
come
to
back
to
the
list
and
talk
about
having
textin
in
front
of
it
right.
I,
just.
M
Recalled
one
question
and
going
down
and
would
like
to
ask
the
working
group
to
see
if
it
would
be
a
good
choice.
We've
been
thinking
about
duplicating
chippa
desk
and
we
know
that
there
are
some
places
is
still
being
used
and
we
wonder
if,
if
we
do
gasps,
would
anybody
having
a
hot
burn
for
that
policy
option
now.
C
We
already
say
for
ESP
it
should
not
and
for
I
question
two
is
going
to
be
May,
so
we
don't
care
if
you
deprecated
it
at
me,
people
can
actually
remove
it
if
they
duplicate
means
like
no
use.
That's
that's
fine
for
us
that
have
you
already
say
it's
made
major
implementing
Iike
first
one
and
it
should
not
be
used
in
should
not
in
and
I
in
ESP.
So,
okay.
O
So
Danielle
I
think.
The
reason
we
said
must
not
for
the
manual
king
is
not
only
it's
a
bad
idea,
but
only
one
of
the
streets
in
is
mentioning.
Yet
you
must
not,
but
the
other.
The
other
two
suites
are
not
so
clear
about
the
most
nuts
sir,
so
I
think
in
DCM
I
think
that's
the
same
but
I'm
saying
GG.
C
M8
and
for
Paula
tata
tata,
20
are
or
actually
any
of
the
counter
mode.
Ciphers
are
inherently
dangerous
with
you
know,
man
work
is
because
in
man,
work
is
actually
means
that
you
type
in
the
case
interconnect
file
and
when
you
reboot,
you
started
sequence
number
from
you
know
from
the
strats,
and
you
actually
have
you
know,
but
a
strictly
everyone.
K
What
Mary,
King
I
think
beside
the
testing
and
debugging
poppers
lectures
as
a
realist
case,
which
is
in
using
the
OS
ppl
spp
of
p3
authentication,
which
relate
to
use
it
for
the
multicast
colors
view
package,
melon,
multicast,
packets
and
there's
no
Kurds,
there's
no
practical
way
to
do
any
any
anything.
Otherwise
beside
emoji,
a
many
p,
but
that's
a
real
use
case.
I,
don't
think
we
should
say
we
must
not
use
money
pit,
because
this
really
skeezer.
E
C
E
C
Alright,
so
there's
a
couple
of
other
suitors
this
out
null
and
out
non
non
toxic,
no
and
out
none.
There
is
some
text
about.
We
have
talked
about
the
Nala.
You
know
how
dedication
when
we
are
supposed
to
be
out
soon
on
and
so
on.
Others
monsters
text
about.
We
change
it
in
a
renaming
summer
girl,
because
we
are
now
using
today,
algorithms
as
they
are
in
our
registry,
at
the
cemetery
to
one
actually
use
them.
You
know
in
the
clerk.
C
Some
kind
of
you
know
formula
to
serve
about
the
same
that
iono,
but
not
the
same.
So
these
are
something
that
I
think
we
are
already.
You
have
some
of
these
already
in
there.
So
these
are
the
changes.
I
wouldn't
be
doing,
but
I,
so
the
Mon
working
text.
We
come
back
to
the
mailing
list
about
having
some
paragraph
there.
It's
one
per
ography
I'll,
go
to
the
free
thing
and
and
I
think
molded.
Others
are
fine.
Okay,.
E
And
then
the
last
one
I'm
not
sure
if
it's
needed,
but
we
came
back
from
ISD
refute-
is
that
they
wanted
some
more
explicit
entry.
That
said
that
anything
not
listed
may
be
used
and
I
think
we,
we
sort
of
argue
that
we've
already
explained
this
in
the
introduction
or
the
abstract,
and
we
don't
need
it
again.
C
C
All
right
next,
one
in
EDSA,
so
actually
now
so
this
is
the
we
have
a
big
group
last
call
done,
and
there
was
this
question
about
to
be
used
0
or
should
we
use
something
else
for
identity
and
I?
Think
the
most
people
in
the
listing
to
be
favoring
of
using
new
number
and
I
just
wanted
to
see?
If
there's
anybody
here
actually
want
to
stop
using
JIRA
instead
of
don't
see
anybody
or
you
have
a
comment.
P
Comment
about
the
EDSA
I
lack,
if
you
curve
in
casa,
but
are
too
concerned
about
it,
EDSA
on
the
way
to
push
it
first
is
not
certified
agreed
or
something
about
official
Authority
about
crypto,
which
can
be
a
problem
on
second,
which
more
comment
for
me:
there
is
no
idts
occurred
available
in
openness,
openssl
or
GCS.
11
is
awesome.
I
You
have
no
well,
we
have
to
have
standard
both
here
and
in
TLS
that
are
specifying
the
use
of
EDSA
before
it's
worth
opens.
It
sells
well
to
actually
implement
it,
and
I
have
heard
from
riches
nothing
but
that
they
are
working
on
it.
They
plan
for
some
next
release,
that's
coming
out
next
year,
I
think
so
it
will
be.
A
thing
thing
is
the
algorithm
that
we're
using
in
Ike
is
a
generally
decided
by
the
certificate
that
we're
using
and
as
long
as
the
major
ca's
are
issuing
only
our
essay
or
ecdsa.
I
That's
what
we're
going
to
use
but
we're
making
these
documents
in
expectation
that
at
some
point
we
will
be
able
to
use
EDD
essay
and
open.
The
cell
code
is
coming.
There's
many
other
libraries
that
already
have
such
code.
So
I
don't
see
that
as
a
problem.
As
for
the
identifier
for
the
hash,
well,
zero
is
already
called
none.
It's
no
hash
is
sort
of
sounds
like
it,
but
I'll,
because
some
people
might
use
zero
for
special
value
than
it's
fine,
to
use
a
the
next
available
number
and.
C
J
Probably
Apple
so
just
I
mean
to
the
point
of:
is
it
ready?
Should
we
do
it?
Sadly,
our
implementation
isn't
open,
but
we
have
implemented
EDSA
and
Ike.
It's
working,
it's
good.
We
definitely
want
to
move
ahead
with
it,
so
I
don't
want
to
hold
it
up
for
any
reason
internally
right
now
we're
using
five,
because
that's
the
next
number
we
haven't
deployed
that
yet,
but
it'd
be
great
to
get
number
five
out
there.
So
we
don't
do
bad
things
to
get
number
five
out.
The
outers.
C
Need
to
make-
and
you
know,
request
from
iono
it's
expert
review
as
the
document
register,
which
means
that
when
you
make
the
read
number
for
a
requester
iono,
I
never
said
it
to
me
and
I
will
lucky
the
number
we
could
talk
to.
Do
you
explain?
No,
no,
you
have
to
go
through.
Iono
expert
can't
give
the
numbers
directly
so.
C
Six
because
nobody
said
anything
about
the
chi-rho
expert
and
he
would
say
yes,
okay,
so
I
think.
Actually
we
are
going
to
be
with
the
five
and
that
the
current
text
in
the
document
is
okay,
so
I
think
activation
after
this
document.
We
should
start.
Actually
we
have
done
the
last
call,
but
so
we
should
actually
make
you
know
start
the
publication
requested
for
this.
So.
I
C
C
E
Artists,
microphones,
much
better,
ok,
so
we've
removed
the
request,
limited
domain,
so
the
client
could
send
the
list
of
domains.
It
only
was
interested
in
and
we
talked
about
this
and
we've
removed
that
feature.
The
sidh
every
internal
dns
domain
option
for
the
sender
is
Sarah
sighs.
We
added
some
local
policy
clarifications
and
we've
removed
the
requirement
for
the
childís
rate
to
be
up
for
any
dns
IP
addresses
that
percent.
E
So
previously
we
said,
if
you
send
an
IP
address
than
one
two
three
as
a
dns
name
server
for
one
of
the
domains,
then
you
must
make
sure
that
there's
a
child
I
say
up
for
that
appear,
dress
and
after
talking
previously
in
a
working
group,
was
decided
to
remove
that.
So
those
are
the
issues
we
changed.
The
last
version
that
was
like
the
00
document
after
adoption,
so
the
open
issues
are
there's
two
items
aware
we
had
consensus
about.
E
So
my
opinion
is
the
case
where,
if
I
connect
to
read
calm-
and
I
want
to
talk
to
bugzilla,
overcame
I'm
getting
the
internal
IP
address
and
if
I
cash
that
and
if
then
disconnect
my
VPN,
then
I
need
to
go
back
to
the
public
IP
address
of
the
server.
So
I
need
to
flush
my
cash
and
so
for
me,
it's
important
that
that
that's
in
the
protocol,
it
says
you
know
flush
the
cache
for
these
entries.
If
you
reconnected
or
disconnect
your
domain,
anantara
has
a
different
opinion
on
that.
C
Document
inside
secure,
so
I
think
it's
actually
it's
something
I
don't
want
to
be
late
there.
You
know
cash
interest
immediately.
When
you
have
you
know
a
child
SI
going
down
or
like
I
said
you're
going
down,
but
I
mean
that
would
actually
you
know
course
troubles
if
you
have
it,
because
what
you
usually
do
you
just
recreate
it
immediately,
but
if
you
tear
down
and
then
you
have,
you
know,
love
your
connection,
sir.
You
know
failing
because
the
dns
name
isn't
funny.
That's
actually
not
very
funny.
C
C
No,
that's
what
that's
the
idea
when
you
have
a
non-routable
address,
you
see
what
happens
there.
Then,
when
you
send
the
traffic
it
will
drinker
type
a
sec
to
create
it
again
and
then
you
have
it
back.
That's
that's
the
basic
idea,
because
I
mean
you
have
that
you
have
the
treatment
rules
that
are
still.
L
L
I
think
that
you
should
have
either
two
different
names
or
something
that
that
that,
because
if
there
is
some
risk
of
disclosing
traffic-
and
you
would
go
publicly
if
the
link
was
down,
then
obviously
there's
no
risk
of
disclosing
traffic
right,
because
you
would
be
happy
to
do
it
in
the
clear
then
you
should
just
do
what
who
cares?
Do
it
in
the
clear
or
whenever
it
changes,
doing.
Look
here,
clear
or
whatever,
but
Tarot's
use
case,
I
think,
is
that
you
know
you
have
a
bunch
of
these
internal
things
that
you
want
to.
L
E
That
would
be
based
on
the
TTL
of
those
dns
records
in
your
cash.
That
is
really
sketchy,
so
you'll
end
up
like
with
half
the
time
it
not
working
anyway,
because
did
dns
record
happen
to
expire
and
you're
just
typing
in
names
that
aren't
part
of
the
public's.
Actually
you
don't
know
if
you'll
get
the
internal
dress
or
an.
L
Rn
annex
domain,
one
of
the
reasons
why
I
think
the
split
dns
is
fundamentally
broken
actually,
but
but
assuming
that
that
you've
pinned
some
things
to
have
some
domains
be
internal
okay,
that
should
not
expire,
even
if
the
TTL
of
the
rest,
so
you've
just
said,
I've
got
some
configuration
that
means
domains.
I
look
up
internally
through
this.
These
other
places
that
stuff
should
probably
have
its
own
TTL.
L
So
so
that's
that's
part
of
the
question
that
I
have
and
I
think
that's
fundamentally
broken
and
I
think
that
we
have
better
solutions
in
DNS
that
most
people
and
live
in
a
v4
only
world.
Don't
understand
that
that
would
permit
this
to
work
very
well.
That's
right!
So
so
I
realize
you
guys
live
in
this
real
world
of
administrators
that
think
they
own
ten
net
and
there's
only
one
ten
net
and
they
only
have
one
VPN
up
right.
L
So
I
know
that
I
know
that
those
those
people
I
mean
I,
think
they're
idiots
but
and
we're
supposed
to
help
them
out
right.
So
I'm
saying:
if
we're
going
to
help
them
out,
then
we
need
to.
We
need
to
have
that
some
kind
of
pinning
so
so
that
those
things
have
to
have
a
time
to
live
and
every
time
you
bring
up
your
VPN,
then
I
think
you
get
essentially
new
records
and
new
ttls
and
everything's
good
right.
I.
L
Think
you
can
make
that
work,
but
I,
don't
think
you
want
to
flush
the
cache
when
that,
when
connections
go
down,
that's
what
I'm
trying
to
say
right
or
if
you
do-
maybe
your
Paul's
right.
Maybe
you
want
to
flush
at
every
single
time
because
you
want
to
do
it,
make
a
consistent
experience,
which
is
that
the
user
learns?
L
E
D
J
I
mean
I
think
dude.
The
kind
of
the
real
world
perspective.
That's
driving
this
I
I
think
we
need
to
leave
in
something
about
flushing
the
cash
I'm,
fine,
softening
it
and
saying
like,
depending
on
what
your
implementation
does.
You
may
flush
the
cache
or,
if
you
expect
these
DNS
names
to
be
truly
global
and
managed
correctly,
and
you
don't
have
a
broken
split,
dns
configuration
or
your
enterprise,
then
you
cannot
flush
it.
I
think
we
can
just
iterate
that
I
don't
think
it
needs
to
be
solved
in
this
document.
J
This
doesn't
need
to
solve
the
world's
problems
on
split
dns
to
the
point
of
triggering,
so
I
may,
at
least
on
our
end,
we're
not
going
to
trigger
based
on
the
address
once
the
VPN
has
gone
down.
Oftentimes
oh
I
mean
what
solutions
to
do
now
is
that
they
trigger,
based
on
the
fact
that
the
host
name
cannot
be
resolved
anymore,
and
so,
rather
than
treating
us
an
address
you
trigger,
based
on
something
about
the
name
of
the
DNS
failing,
and
you
realize
that
oh
dang,
it
I
got
screwed
up.
L
J
E
J
Does
the
I
don't
know
if
the
expectations
really
matter
all
that
much
because
it's
really
just
a
local
client
policy
about
what
it
does
so?
I
me
to
the
point
of
where
we've
gone
in
the
draft
of
saying
that
you
know
the
client
is
no
longer
specifying
to
the
server
here's,
the
ones
that
I'm
willing
to
accept.
Essentially
the
clients
already
potentially
trimming
down
the
list
of
domains.
That's
going
to
be
doing
split
DNS
for
it's
making
its
own
local
policy
decisions.
R
Yeah
Kyle
Bekker,
its
Facebook
I,
have
seen
some
issues
where
people
want
to.
Basically
when
you're
on
VPN
redirect
people
on
that
VPN
to
say
some
like
release
candidate
version
of
your
website
and
then,
if
you're,
on
not
against
public
internet,
go
to
a
different
site
and
then
the
release
candidate
for
sending
for
whatever
it's
only
available
on
to
VPN,
and
that
does
end
up
in
shoo
when
you
disconnect
from
VPN,
but
still
at
the
cast
entry
for
some
IPS.
C
But
the
current
takes
to
say
that
you
have
you,
must
you
know
first
plastic
ashes
and
that's
the
most
is
what
I've?
Actually
you
know
say
you
could
say
that,
yes,
you
you
should
be.
You
know
you
should
remove
the
cash
she
immediately.
Many
you
know
fear
that
you
are
not
going
to
get
be
in
the
VPN
anymore.
That
would
be
actually
much
better
decks
or
stuff
like
that.
But
I
think
we
got
it
from
back
to
the
least,
and
you
know
it
discussion
there
and
go.
Oh.
C
E
E
C
C
S
S
I
should
hopefully
go
ok.
This
is
both
con
crypto
I,
I
I'd
be
too
next
slide.
This
is
a
next
slide.
A
brief
summary
right
now,
with
the
kekeke.
That's
pretty.
We
depend
on
diffie-hellman
occurred
for
Helmand
for
our
protection,
a
sullen
stores
tend
traffic
for
ten
years,
the
bill
on
computer.
They
can
then
go
back
and
read
all
their
craft,
that
traffic
that's
a
good
thing
next
slide,
and
what
we
going
to
do
about
it
that
the
obvious
solution
would
be
to
come
with
a
post
quantum
key.
S
I
key
exchange
a
good
idea,
but
there's
nothing
that
we
really
like
right
now.
This
is
going
to
have
a
comp
tech
contest,
which
role
might
be
in
seven
five
or
seven
years
come
up
with
something
I
don't
know.
We
want
to
wait
that
long.
So
let's
come
up
with
temporary
solution,
but
what
I'd
idea
with
our
strategy
here
is
actually
have.
S
Both
sites
have
a
shared
secret
and
basically,
they
stir
in
the
shared
secret
in
when
they
derive
the
keys,
and
so,
if
someone
someone
breaks
the
difficult
as
long
as
they
can't
break
that
they
shared
the
secret.
They
still
can't
be
able
to
redrive
the
keys
and
therefore
we're
safe
and
the
keys
need
something
ridiculous
valve
entropy,
but
exactly
achievable
next
slide
or
sorry.
Is
that.
P
S
What
we
talked
with
weed
mostly
agree
about
the
acquirement
such
algorithm
guild
is
important.
I
think
I
traffic
needs
be
protected.
I
traffic
is
less
important,
but
it's
that
seemed
to
be
a
bit
debated
available.
I.
Have
we
have
the
current
draft
right
here
and
there's
a
couple
of
points
to
that
were
brought
up
on
the
mailing
list
and
that's
go
through
them
next
slide.
S
N
E
C
Given
him
I
think
actually
that
I
have
proposed
a
one-way
also
earlier
very
early.
That's
why
I
think
I
think
the
key
Matt
only
is
has
the
problem
that
it's
a
it
has
the
properties.
If
there's
something
wrong,
if
the
key
Matt,
if
it's
wrong,
we
don't
know
this.
If
it
does
notice
it
all
the
ESP
traffic,
is
you
know
how
much
this
way
I
actually
want
to
do
something
in
the
ike
that
we
actually
notice
in
the
ike
that
ok
there?
C
You
know,
for
example,
the
authentication
fails
because
they,
you
know
Sergey
PPP
k
is
wrong
and
that's
why
that's?
Why
I
think
that
you
know
the
correct
solution
is
to
know
somewhere
in
the
volta
a
ski
day
T
which
actually
desk
ed,
has
a
good
property
at
that
they,
if
you
because
that's
used
to
when
you
are
doing
Ricky
of
the
ik,
say
it's
used
to
create
the
next
keys
for
their
weakest
Ricky,
so
that
will
offer
you
after
the
Ricky
you
also
the
ike
traffic.
Are
you
know,
PPK
protected.
S
Here's
a
suggestion
arm.
We
make
it
really
explicit.
Basically,
we
exchange
notifies
after
we
just
create
the
IKS
Isis
to
negotiate
that
we
actually
do
want
to
do.
This
would,
if
wanna
notifies
included,
say
a
hash
of
the
tpk.
Yes,
I
would
see
if
it's
the
wrong
hash
its
notice
to
notify
that
immediately
and
therefore
they
wouldn't
know
that
gee.
That
is
what
specifically
is
wrong.
That.
C
That's
one
of
the
problem
there
is
that
these
actually
knows
which
part
of
the
authentication
went
from
good,
then
we'll
be
able
to.
You
know,
attack,
authentication
and
the
ppk
separately,
because
you
get
the
different
error
message.
If
one
is
wrong
and
other
is
and
that's
why
I
think
that
would
be
better
to
have.
C
C
L
L
The
remote
guy
doesn't
know
which
one
I
was
wrong.
Okay,
local
guy
knows
what's
wrong,
so
can't
just
be
opaque.
Oops,
you
know
stuff
went
wrong
all
right,
not
that's!
What
happened
in
Mike
will
be
one
with
various
things
originally
with
with
pre
shared
secret
keys.
If
you
got
the
wrong
you
just
just
couldn't
decrypt
stuff
and
didn't
really
know,
what's
going
on
the
right,
we're
a
lot
better
situation
with
ip24,
a
lot
of
reasons,
I
think
that
some
people
in
the
list
are
in
the
room
if
they
think
this
through
may
ask
the
question.
L
If
we
don't
think
anybody
except
the
super
secure
people
are
going
to
bother
to
comply
it,
then
it's
not
going
to
be
on
customers,
checkbox
lists
the
vendors
aren't
going
to
produce
it,
and
the
end
result
is
that
no
one
will
use
it,
including
the
people
who
you
know
would
like
to
have
more
than
one
supplier
for
their
super
secure
stuff.
So
that's
an
issue
right,
so
if
we
really
wanted
to
do
it
and
I
think
we
need
to
make
it
a
little
bit
issue
and
I
was
very
surprised.
L
Several
people
said:
oh,
my
goodness,
we
don't
have
to
even
bother
deciding
what
the
format
of
the
ppk
is
printed
and
I'm,
like.
Oh,
my
goodness,
that's
like
the
most
basic
system
in
thing,
the
guy
can't
type
in
the
ppk
cuz
his
formats
different,
the
other
one,
and
he
doesn't
know
how
to
use
perl
unpack
on
it
right,
because,
just
honestly,
that's
Europe,
k,
labs,
told
me:
you
know
that
that's
the
level
of
administrator
we're
dealing
with.
L
So,
if
we're
not
going
to
make
it
easy
for
people
to
use,
then
actually
my
question
is:
why
bother
if
it's
only
going
to
be
used
by
the
NSA
to
secure
you
know,
US
government's,
you
know
what
they
can
just
go
to
their
two
preferred
vendors
tell
them
to
implement
your
protocol,
maybe
you're
one
of
those
preferred
vendors
already
and
we're
done
right.
We
hardly
even
need
a
standards,
action
right
Scott
you
decide
what
to
do.
You're
done.
Let
us
know
informational
draft,
how
it
went.
L
L
L
Okay,
because
that's
the
point,
the
point
is
to
get
that
PP
k
into
that
algorithm
now
such
that,
in
fact,
no
one
on
the
wire
will
be
able
to
detect
whether
app
redistributed
PP
case
or
I
have
a
proper
quantum
resistant.
He
agreement
algorithm
right
or
so
I
quantum.
My
green
book
he
agreement
valid
point
is
that
because
those
PP
case
can
come
out
of
the
other
thing
that
you
just
predicted
existing
right.
S
C
Yeah
better,
given
it
so
so
yeah
I,
think
I
think
actually,
because
that's
one
of
the
reasons
we
want
to
make
it
is
very
easy
to
implement
so
that
people
to
be
no
two
or
three
lines
of
code.
Then
people
are
going
to
be
adding
it
regardless.
If
it's
you
know,
if
they
think
it's
useful
or
not
it's
a
it's
useful
feature.
So
it's
always
useful
to
have
a
one
more
feature
in
your
feature
list,
because
that
might
be
something
that
customers
will
look
and
all
your
competitor
doesn't
have
that.
C
Oh,
that's,
that's
better
or
at
least
yeah.
He
has
73
pay,
you
know
lions
and
he
has
72.
So
this
is
better
because
had
one
more
so
that's
why
I
think
if
people
are
going
to
be
implementing
it,
but
it's
going
to
be
used.
That's
the
next
question
and
one
of
the
things
I
don't
want
to
be.
You
know
I'd,
say
I,
don't
think.
Actually
we
need
to
specify
anything
for
the
ppk
format,
because
it's
just
random
binary
or
bike
club
that
is
going
to
be
feed
into
their
critter
and
if
he
is
in.
C
Yeah,
how
do
you
type
in
Europe,
pre-shared,
key
pre-shared
key-
is
a
binary
club,
no
ascii
ascii,
usually
chaski
yeah
yeah
but
I
mean,
but
my
format
is
not
saying
that
he's
yeah
that
that
I
mean
I
mean
it's
good
yeah
in
here
we
actually
more
expect
it
to
be
binary
than
string
like
insert
key.
It's
actually
used.
Quite
often
they
are.
Actually
you
know.
C
Just
you
know
strings
it's
something
I
make
me
a
tasty
gold
yeah,
so
so,
but
with
it
here,
I
think
the
x-ray
expert
tend
to
be
more
like
a
binary
option
and
one
of
the
things
I
really
like
to
have
it.
I
would
like
to
what
you
are
saying
at
me.
I
need
to
have
something
now
in
a
protocol
that
we
can
plug
in
that
you
know
the
real
team.
C
You
know
quantum
key
distribution
reckon
it's
later,
so
we
can
actually
run
that
first,
then,
we
get
some
kind
of
binary
blobs
that
we
can
use
here
and
actually
I
guess
it
would
probably
be
something
that
we
run
it
once
then
they
get.
You
know
10,000
of
these
binary
blobs
and
when
you
use
these
PPK
is
in
you
know
in
some
kind
of
order,
and
then
they
have
some
internal
format
for
the
pp.
C
Might
be
there,
but
actually
one
of
the
things
is
there
as
it,
as
I
said,
is
it
they're,
usually
quite
large
yeah,
and
you
might
actually
want
to
run
them
all
over
tcp
or
something
like
that.
Instead
of
you
know,
you
did
leave
it
to
limit
that
packet
sizes,
so
I
think
it
might
be.
Actually
this
kind
of
free
generation,
the.
S
Other
advantage
of
that
Patera
key
exchange
have
that
we're
at
with
that.
We
don't
is
that
those
can
rerun
with
before
you'd
actually
know
the
idea
with
these
peeps
case,
because
you
have
to
know
the
identity
of
the
pier
you,
you
have
there's
a
chicken
at
a
bit
of
a
chicken
egg
with
the
pure
post
key
exchange.
There
is
no
not
and
and.
C
The
other
thing
I
was
think
about
here
is
that
in
Ike
we
always
assume
that
the
configuration
is
in
both
ends
you
actually.
This
is
actually
one
difference
in,
for
example,
pls.
We
assume
that
okay,
random
machine
somewhere
can
connect
to
server
and
they
don't
they
don't
share
any
configuration,
accepted
root
of
trusts,
but
I
mean
ends
it
with
ssh.
For
example,
you
I
don't
expect
to
be
able
to
associate
from
my
laptop
to
your
laptop.
C
C
The
comment,
if
I
don't
say
that,
but
if
you're
talking
about
you
know
normal,
you
know
authenticated
IP
secretary,
so
you
are
going
to
be
configuring
both
ends,
which
means
that
your,
if
you
are
not
using
some
kind
of
ppk
generation
from
either
from
you
know,
you
know
one
time
password
taking
slices
of
their
you're
doing
that
you
know
in
both
ends
anyway.
So
that's
why
I?
Don't
think
we
actually
need
to
have
any
kind
of
real
format
for
the
PDK.
J
Tommy
Polly
Apple
yeah
I
strongly
agree
with
tear
of
that
I.
Think,
first
of
all
that
the
format,
even
if
it
is
specified,
should
not
be
part
of
this
document
and
hold
up
this
document
through
from
going
through
because
it's
important
to
get
the
specified.
You
may
be
interesting
to
have
a
separate
one
about
what
are
different
approaches
to
sharing
PPK,
maybe
as
an
informational
thing,
but
yeah.
It's
probably
going
to
be
binary,
and
there
are
ways
that
servers
have
to
distribute
shared
secrets
now
and
they
are
different
and
they're
still
going
to
remain.
J
I
You're
here
and
I
want
to
push
back
on
what
Tara
said.
If
this
is
made
easy
to
implement
and
yeah,
it
could
be
three
lines
of
code,
but
that
doesn't
really
add
a
feature
to
my
product.
If
I'm
don't
solve
the
key
distribution
problem,
because
if
we
had
a
good
solution
for
the
key
distribution
problem,
we
would
never
reveal
certificates
for
authentication.
If
I
had
a
hundred
gateways
and
I
could
just
easily
distribute
the
9900,
the
pre-shared
key
is
that
they
need
for
good
authentication.
I
would
never
use
certificate.
S
I
I
U
Dan
Harkins
so
like
this
we've
got
kind
of
derailed
here
up,
but
as
far
as
distribution
of
these
things,
so
peak
X
defines
a
symmetric
key
package.
Now
we
could
it's
a
nice
format
to
distribute
things
and
if
you
have
mentioned
on
the
list,
if
you've
got
armed
guards
that
walk
around
distributing
these
things,
that's
that's
probably
what
you
got
to
do,
but
I
want
to
get
back
to
the
slide.
You
can
let
up
I,
don't
actually
remember
what
why
I
suggested
he
met
the
terrorists
suggested
something
else.
C
In
I
crossing
to
we
have
this
sk
seed,
which
is
going
directed
by
the
diffie-hellman
output.
Then
we
have
this
PRF
that
generates
a
bunch
of
this
sk,
something
there's
sk
d,
which
is
used
to
derive
the
derive
that
you
know,
keep
my
carry
on
sir
and
there's
a
I,
a
and
E,
and
so
that's
encryption,
authenticator
and
then
there's
this
skp
I
and
PR,
which
I
used
to
generate
the
authentication
hashes.
So
there
is
it's
used
in.
Let
me
see,
do
you
want?
You
want
to
mix
the
ppk
and
regeneration
of
all
of
those.
C
C
C
C
S
F
S
V
That
was
kind
of
what
happens
like
that.
It
might
not
be
simplified,
but
it
might
need
to
be
in
hybrid
with
a
whatever
the
desk
either,
because
we
have,
there
might
be
some
negotiation
parameters
required
people
to
start
thinking
about
formats
or
yeah.
What
they
hear.
The
protocol
cuz
look
like
for
the
birth
yeah
mixing
in
those
yeah.
H
Philip
lafrance
I,
Sarah,
ok,
so
it's
cotton,
I
talked
with
this
briefly
before
so.
I
think
we're
all
in
agreement
that
we
can't
wait
for
this.
We
should
do
something
now,
but
this
is
certainly
a
band-aid
I
think
we
all
agree.
So
my
concern
with
with
this
right
now
is:
it
doesn't
offer
any
forward
secrecy.
So
I'm,
pretty
concerned
with
you,
know
quantum
adversaries
so
I
think
forward.
Secrecy
is
a
really
highly
desirable
property
to
have
and
I
think.
H
If
we're
looking
forward
on
the
technologies
work,
hopefully
to
roll
out
eventually,
then
I
think
something
like
that
is
what
we
should
really
keep
in
the
back
of
our
minds
and
I
think
you
could
probably
achieve
it
with
some
sort
of
ratcheting
protocol
like
signals,
so
I
just
want
to
just
put
them
the
back
of
everyone's
mind.
Let
it
percolate
just
a
little
bit
that
this
is
something
that
I
think
we
should
really
really
try
to
get.
N
H
T
Just
told
you
up
to
the
point
about
Mandy:
this
is
definitely
a
band-aid
as
I'm
too
short,
I,
guess
so
the
Google's
algorithm
or
whatever.
So
as
the
color
computing
stuff
advances
the
I'm
crucial
that
well,
this
is
I'm
just
going
to
coach
a
mere,
but
it's
going
to
be
quantum
algorithm
that
lets
them
come
out.
So
it
might
be
good
for
now,
but
there
are
the
new
algorithms
that
will
for
the
weekend,
the
keys.
We
should.
S
T
C
As
a
chair,
I
think
we
need
to
have
a
separate
document
for
that
and
I
think.
Actually
we
have
to
check
out
the
verb
we
actually
make.
It
need
to
make
it
charter
change
for
that,
because
I
did
to
get
second
correctly.
Our
charter
to
do
children's
but
I
think
it's
actually
it's
very
doable
and
do
it
afterwards.
Yeah
I.
C
To
Berlin
and
roxrite
anyways,
so
yeah
so
I
actually
want
to
get
in
a
new
version
of
the
craft
and
I
think.
Actually
we
had
a
good
case
Arsenal.
If
you
actually
get
can
get
to
the
you
know:
agreement
with
their.
You
know
what
the
variax
are
going
to
feel
feeling
the
ppk
I
think
that
they
don't
get
any
version
out
and
then
it's
you
know,
I
think
this
I
have
a
lot
working
group
last
call
for
the
document
that
well.
U
If
you
go
back
a
slide,
I
think
I
think
Michaels
got
a
point
here,
but
I
it
seems
like
we
don't
really
need
to
define
how
these
are
distributed.
That's
out
of
scope.
We
just
deal
with
the
bits
on
the
wire,
but
because
of
that
I
think
we
should
define
some
sort
of
a
format
like
and
I
suggested.
The
EP
kick
symmetric
heat
format
that
you
have
to
adjust.
U
Allows
for
interoperability,
because
Michael
sandwich
base64
something
like
that,
so
we
should
just
have
some
well-defined
format
that
sent
text
to
container
container
of
these
things
that
you
can
do
well.
The
nice
thing
about
about
the
symmetric
key
is
it
you
can
have
a
it's
like
a
bag
right
have
a
bag
of
these
things.
You
can.
You
can
protect
the
bad
now
protect
with
what
is
a
problem.
U
E
Well,
I
do
think
it
would
be
good
to
define
some
sort
of
format
for
representation
in
ascii,
because
we've
seen
some
interoperability
issues
where
people
put
spaces
or
single
quotes
in
there,
and
they
appreciate
key
and
not
all
vendors,
accept
that,
and
so
you
got
like
weird
broken
vs
case,
but
also
don't
want
binary
blobs
in
my
config
files.
So
so
some
some
standard
might
be
nice,
but
it
should
be
really
simple,
like
indeed
like
base64
or
something
yet.
C
R
R
I
Charlie
turn
it
off
then,
on
again,
okay.
So
last
time
we
had
three
suggestions
of
how
to
negotiate
it
within
the
essay
structures
and
thing
we
finally
converge
on
using
a
new
transform
IDs
for
each
one
of
the
algorithm.
So
we
have
a
sec
em.
Now
we're
going
to
have
a
SCCM,
I
IV
same
for
GCM
same
for
patent
chhatrapati,
and
it
was
a
question
whether
we
want
one
for
just
playing
aes
counter
mode
and
no
everybody
thought
not
okay,
so
next
slide
and
okay.
I
That
was
the
last
thing
last
time
since
then,
we've
talked
to
occur
and
he
mentioned
that.
Well,
you
wondered
why
we
were
negotiating
like
negotiating
it
like
this,
because
it
seemed
inefficient
and
it
is
inefficient,
but
all
the
other
options
are
even
even
worse
because
of
the
way
unknown
had
attributes
are
handled
in
the
essay
payloads
so
that
it's
not
great,
but
it's
probably
better
than
the
other
alternatives.
I
Another
thing
he
mentioned
is
that
there
is
a
way
to
do
this
with
other
and
Griffin
algorithms
that
are
cbc
based
because
so
we
could
have
in
the
key
material
extract.
Yet
another
key
and
yet
another
say
AES
key
then
use
that
for
encrypting
countries
and
because
we
have
the
same
key
when
both
sides,
then
we
get
to
sing
encrypted
counter
and
that
can
be
used
as
the
actual
IV
for
cbc.
That
does
work.
We
actually
considered
it
at
some
point,
but
then
we
said
now
we
don't
really
want
to
do
that.
C
All
right
there
are
giving
it
I
think
I
think
the
keys
ago
actually
bet
best
way
to
do
it
in
with
the
different
ciphers,
because
one
of
the
things
we
are
here
talking
about
you
actually
modifying
the
cipher,
because
the
IV
is
part
of
the
cipher
and
you
we
are
removing
that.
So,
if
you
talk
about
the
crypto
context,
is
there
is
you
know
we
have
a?
You
know,
encryption
cook
function
that
gets
you
know
just
we
call
it
and
we
get
in.
C
C
Case
we
actually
need
to
make
modify
that
context
way
that
actually
how
to
cryptos
call.
We
have
to
keep
this
external
sequence
number,
and
actually
we
have
to
somehow
make
sure
that
the
crypto
algorithm
actually
understands,
as
it
actually
is
getting
different.
You
know
Ivy's
different
values
for
the
crypto
sequence.
Numbers
are
separate
for
our
son,
so
we
have.
This
is
like
this
is
why
I
actually
want
to
do
it
in
it?
It's
a
separate.
C
You
know
I
encryption
algorithm
so
because
it's
going
to
have
a
different
type
of
you
know,
for
example,
you
can
I,
don't
think.
Actually
you
can
actually
do
with
the
peeps
version
of
these,
because
I
mean
phipps,
where
I
think
it
actually
requires
the
IV
to
be
part
of
the
no
context
Iran,
and
here
we
actually
get
it
from
outside.
So
so
that's
why
I
were
to
get
it
might
be
better
to
have
it
this
way.
F
Moriarty
responsible
ad
for
this
group
for
few
more
hours
in
my
point
in
that,
maybe
some
people
might
not
know
who
Ecker
is
not
in
the
room
he's
in
another
session.
It's
eric
course
korlah
he's
the
incoming
sec
ad
and
we
shuffle
groups
I'll
be
sad
to
move
on,
but
I
will
continue
to
obviously
read
the
drafts
in
at
least
by
IETF.
Last
call
and
I'll
be
around
so.
C
We
actually
have
more,
how
many
people
actually
have
said
comments
and
reviewed
it
really.
You
know
only
just
which
I
but
last
time
ask
because
I
had
problem
that
it
was
like
one
or
two
and
it
they
were
routers.
So
now
we
have
a
much
much
more.
It's
actually
means
that
we
could
actually
start
going
to
do
home.
So.
K
I
Because
the
rules
for
handling
and
unknown
attribute
is
that
you
know
the
entire
proposal,
so
we
would
so
to
interoperate,
with
older
implementations
would
have
to
send
the
whole
proposed
other
proposals
with
the
indication
and
then
over
again
without
the
indication,
because
otherwise
the
proposal
is
no
good.
It
would
it's
just
inflate
the
size
of
the
essay
failed
much
more.
C
And
I
think
so,
as
we
seem
to
be
having
several
people
reading
this
document,
I
think
I've
actually
adjusted
and
starting
working
group
are
absent.
Another
angle
for
these,
so
so
we
have.
You
have
a
couple
of
weeks
time
to
comment
on
and
very
out
of
it
then
so
that
is
it
good
to
be
adopted
as
a
working
group
documents
and
then
we
hope,
look
it
going
forward
all
right.
I
G
C
O
So
minimal
ESP
is
about
providing
guidance
to
have
a
minimal
implementation
so
to
make
well
to
help
developers
to
have
that
so
well.
It
does
not
update
nor
modify
the
standard
ESP
next
slide.
So
basically
we
go
to
every
fields
and
define
while
provide
some
guidance
and
how
to
implement
them
for
the
SPI.
We
we
recommended
implementation
generate
a
random
spi,
but
for
some
constraint,
nodes
random
generators
might
be
a
problem
so
where,
if
we
have
to
use
one
fixed
spi,
then
we
recommend
to
to
have
well.
O
We
would
like
to
mention
that.
Do
you
have
some
limitations
you
so,
and
one
of
the
limitation
is
that
you
need
to
be
able
to
identify
to
to
index
incoming
packets
to
sa.
So
what
we
recommend
is,
if
you
choose
to
limit
the
number
of
FSB
either
available
to
you,
you
should
be
have
at
least
one
per
session
/
host
you
have
if
you're
using
the
IP
addresses
one
of
the
question
we
had
is:
do
you
think
we
should
make
some
recommendation
and
how
to
perform
the
lookup
for
DSA?
O
O
B
U
V
O
However,
we
just
have
this
kind
of
recommendation
it
for
the
fix
SPI
a
little
bit
more
well
and
well.
If
you're
using
a
fixed
SPI,
then
of
course
you
get
some
privacy
considerations,
because
then
someone
monitoring
the
network
and
somehow
identify
the
device
or
even
to
yourself.
So
that's
thanks
for
you
commented
into
the
draft
well
in
any
case,
if
you
have
any
comment
pleased
to
provide
feedbacks
on
the
mailing
list,
next
slide
well,
SNP,
paiting
and
net
setter.
Well,
the
only
thing
to
mention
is
that
padding
is
not
mandatory.
O
O
S
C
C
Actually,
one
of
the
things
I
think
I
think
the
next
hitter
and
these
kind
of
things
are
actually
something
there's
this
there's.
This
beat
mode
of
type
of
things
like
wood
accent,
be
also
useful
in
this
kind
of
situation.
Where
you
have
this
in,
but
a
negotiated
I
que
si.
We
have,
you
know
all
kind
of
or
IP
circuits.
If
you
have,
you
know
the
source
and
destination
address
these
port
numbers
and
protocols,
and
that
kind
of
things
already
agreed
by
both
ends.
C
If
we
make
it
by,
you
know
very
specific
SI,
but
they're
still
sending
it
in
every
single
pocket,
and
we
always
verify
that.
There's
what
what
is
actually
supposed
to
be
coming
that
the
diversities
you
know
discuss
on
I
think
it
was
a
mechanic
understaffed
about
the
beat
mode
that
we
actually
know,
especially
going
to
talk
about
tunnel
McClatchy
tunnel
mode.
C
You
know
semantics,
but
the
absolute
transport
mode,
you
know
type
of
you
know
hitters,
so
the
axe,
I,
don't
have
an
extra
IP
header
inside,
because
we
can
reconstruct
a
in
our
heavy
hitter
from
day
and
that
actually
would
be
useful
here
at
Celtic
also.
But
it's
an
idea,
XO!
You
might
be
talking
to
think
under
about
taking
that
raft
off
right,
yeah.
C
Q
O
I
Says
that
you
had
the
plain
text
before
encrypting
and
if
you
have
to
pad
the
plaintiff
to
reach
multiple
of
4
at
least
even
if
you're,
the
CCM
or
GC,
even
if
you
aging
yeah.
Even
then,
you
have
to
go
to
a
multiple
of
four
that
doesn't
exist
in
st.
Els,
but
it
doesn't
exist
in
ESP.
Of
course,
you
can
say
that
you're
doing
a
modified
ESP
that
doesn't
require
this
alignment,
which
is
fine,
probably
a
good
idea.
But
4303
says
that
you
have
to
pad
to
a
multiple
for,
but.
D
S
I
O
What
I
was
stating
is
that
not
all
the
algorithm
as
men,
deterring
using
icv
and
as
as
a
result,
I
cv,
was
not
mandatory,
knit
whole
packet.
That
said,
every
time
you
do
in
an
authentication,
you
need
a
nice
EV
and
so
because,
while
the
algorithm
we
are
recommending
are
using
a
CV,
it
becomes
mandatory.
So.
O
O
O
And
so
well,
we
had
a
quite
long
section
on
the
cryptographic
sweet
just
to
explain.
Security
should
not
be
done
at
the
deep
end
of
other
things,
so
we
recommended,
for
example,
if
you
want
to
not
not
to
implement
some
specific
ash
function,
so
you
can
reuse
the
AES
daddy
in
this
draft
for
bandwidth
constrained
avise.
Then
we
provide
a
few
recommendation.
C
So
this
is,
if
I
dressed
correctly,
are
trying
to
still
be
exactly
standard
ESP,
but
just
telling
how
to
how
the
implementation
can.
Actually,
you
know,
make
things
easier
by
doing
some
tricks
like
if
you
go
back
a
couple
of
slides
ever,
let's
talk
about
the
next
terror
of
being
actually
better
for
work,
if
you're
talking
about
next
10
or
being
mandatory,
but
can
be
both
a
fixed
value
that
that's
what
I
saw
that
if
your
image
is
only
talking
UDP,
nothing,
yes,.
B
C
F
C
O
O
Basically,
the
idea
is
that
if
someone
is
implementing
its
own
ESP,
it's
not
a
ESP
base
or
not
base
I
mean
it
doesn't
break
anything,
that's
the
key
idea.
So
before
people
start
making
their
own
tricks,
it's
we
provide
them
some
guidance,
and
this
draft
is
not
expect
to
be
here,
but
it
was
here
in
order
to
get
feedbacks
and
wish.
While
we
expect
a
movie
to
forward
into
the
working
group,
lwi
g,
which
is
for
as
guidance
for
smaller
implementations,
so
watch
the
it's,
it's
not
the
working
group
craft
area.
C
Ok,
so
that
ever
actually
encourage
people
to
read
this
and
you
know
think
about
it
at
essen.
You
know
this
is
the
minimal.
This
is
how
to
implement
any
IPS,
be
in
very,
very
constrained
device
and
not
about
thing
about
it.
As
you
know,
this
is
kara
purpose,
ipsec
implementation.
That
is
doing
something.
This
is
like
a
I
had
a
minimal
I
question
to
document
their
text
explaining
how
to
do.
You
know
ETA
terse
I'd
of
that,
because
you
never
actually
never
want
to
be
under
sponder
there,
but
you're
sleeping
all
the
time.
S
C
And
I
actually
would
like
to
get
you
guys.
Send
a
comment
to
the
ipsec
email.
Is
that
when
you
have
read
it?
Even
if
there
is
nothing
you
know
wrong
with
it
to
go.
I
sure
you
can
find
something
wrong,
but
even
if
you
don't
find
anything
just
send
an
email
to
the
list.
I
say
that
you
have
read
it,
so
they
actually
know
that
somebody
has
been
ready.
Readings
so
I
think
that's
covers
everything
we
had.
Anybody
has
any
other
issues.
