►
From YouTube: IETF99-IPSECME-20170721-1150
Description
IPSECME meeting session at IETF99
2017/07/21 1150
https://datatracker.ietf.org/meeting/99/proceedings/
A
A
Yeah
well,
we
should
have
a
few
minutes
for
for
open
mic,
some
some
quick
status
on
our
existing
drafts.
We
have
a
number
of
drafts
in
in
the
editor
queue
that
I've
just
entered
the
queue
40
307
this
and
seven
three
two
one
dis
are
now
in
the
queue
TCP
and
cabs
has
entered
the
Edit
phase,
so
we
should
be
probably
hearing
from
the
RFC
editors
soon
and
we
recently
requested
publication
of
EB
DSA,
so
we
should
be
hearing
from
the
IHG
soon
on.
B
C
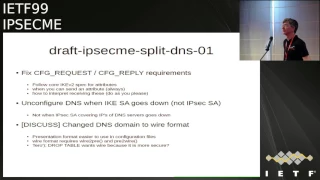
Okay,
I'm
so
speediness
there
weren't
that
many
changes,
it's
just
a
small
diff.
We
we
synced
up
the
document
for
this
if
she
request
reply
payloads,
because
we
had
come
up
with
all
these
smart
things
of
when
we
decided
when
we
wanted
replied
to
be
valid
or
not,
but
then
was
pointed
out
that
the
core
RFC
actually
tells
you
exactly
what
to
do
and
the
summary
base.
The
point
is
that
you
can
always
send
whatever
you
want
and
you
can
always
ignore
whatever
you
receive.
C
So
we
update
the
draft
to
say
that
then
Tara
came
up
with
an
interesting
use
case
where
we
wanted
to
limit
the
IP
addresses
reachable
by
the
DNS
server,
so
that
that
we
were
sure
that
you
were
using
the
right
technology
for
the
right
thing
and
I'm
Tara
came
up
with
his
funny
use
case.
Why
he
wants
to
do
this
on
demand.
So
he
wants
the
IKE
to
be
AC,
to
be
able
to
notify
the
DNS
servers
and
an
on-demand
when
sending
a
packet
to
the
DNS
server.
C
He
wants
the
childís
a
to
come
up,
so
we
changed
the
wording
to
say
only
unconfigured,
the
dns
when
the
I
guess
a
goes
down,
not
one,
and
if
the
IPSec
recite
goes
down
and
there's
no
more
limitation.
That
says
you
know
the
DNS
MUSC.
The
dns
must
only
be
accepted.
If
this
IPSec
has
a
is
up,
and
then
the
interesting
part
is
that
I
sort
of
reluctantly
agreed
to
change
the
presentation
format
to
wire
format,
based
on
the
suggestion
of
tarot
drop
tables.
C
And
and
and
I'm
actually
back
paddling
on
this
I
really
don't
like
this
I
really
want
to
go
back
to
the
presentation
format,
because
I
don't
really
want
a
DNS
parser
in
my
code.
I
know
that
one
other
implementation
has
the
same
thing
and
I
think
this
is
a
manageable
security
item
in
the
implementation
and
and
presentation
format.
It
is
much
nicer
to
have
in
configuration
files,
so
we
don't
have
to
deal
with
the
in
Isaiah
format.
No.
D
D
D
B
C
B
C
C
Most
penis
configurations
and
most
dns
administrators
are
really
used
to
presentation
format
when
they
type
in
redhead
comm.
They
don't
really
want
to
do
like
wire
format
in
commercials
and
and
that's
an
example.
If
you
now
use
a
strong
son
who
already
implements
these,
you
know
at
this
configuration
payload
put
that
from
it,
and
you
can
already
use
it
if
it
would
just
be
presentation
format,
but
it
doesn't
support
anything
while
you're
ready.
Yes,.
C
Today,
yeah
I
understand
the
DCP
argument.
I
also
talked
to
Paul
Hoffman
about
this,
and
the
only
reason
Paul
Hoffman
actually
caved
into
the
presentation
format
was
that
there
was
already
three
other
use
cases
in
DHCP
that
used
to
present
a
they
use.
The
wire
format,
so
only
for
consistency
was
an
agreement
to
again
use
wire
format,
but
we
have
no
precedence
here
right
now.
This
is
the
first
time
we're
doing
is
so
it.
The
depressant
here
could
still
be
disused,
presentation,
format.
E
Tommy
poly,
so
as
another
author
on
this
I
am
I'm
technically
fine
with
either
way
that
we
go.
I
do
also
definitely
prefer
the
presentation
format
to
the
wire
format.
Yes,
I
acknowledge
that
it's
it's
simple
to
convert
the
uncompressed
version,
it's
easier
to
read
the
traces
is
easier
for
people
to
already
configure
the
presentation,
format,
that'll
kind
of
works
by
default,
without
changing
any
of
the
code
for
many
implementations.
B
B
So
so
in
given
in
so
in
all
of
the
cases
were
actually
sent
something
we
sent.
You
know
one
item,
we
don't
we
don't
send
you
no
spaces,
they
separated
list
of
domain
names
or
fully
qualified
domain
names.
Actually,
when
we
are
actually
sending
an
email
address,
we
are
actually
sending
the
email
address.
Parkour
I
think
we,
actually
you
are
not.
We
are
not
allowing
you
to
have
you
know.
B
This
comment
feels,
and
you
know
this
all
of
the
other
things
that
is
actually
part
of
the
email
address,
I
think
it's
actually
saying
RFC
eight
to
two
of
the
address,
which
is
only
the
address
part.
Not
they
not.
You
know,
mother.
So
that's
why
I
was
saying
that
the
gay
we
are
not
sending.
You
know
convict
strings.
We
are
accessing
items,
its
have
a
very
good.
No
because
here
we
have
actually
have
a
multi-line
string
having
spaces
having
all
the
stuff
separated
or
space
separated
list
of
you
know,
items
and
no.
No.
No.
E
E
B
Yeah
but
I
mean
presentation,
format
can
have
actually
have
you
know
all
kind
of
other
things.
Also,
if
I
understand
correctly,
if
I'm
talking
about
same
thing
that
we
are
actually
having
in
you
know,
for
example,
you
have
you
have
a
you,
have
a
backslash,
you
can
have
a
bad
person
lives
in
there.
It's
actually
it
you
know
go
so
it
has.
Escaping
mechanism
is
exactly
it's
kind
of
things
in
there.
You
need
even
inside.
C
B
That's
true,
I
was
also
saying:
okay
format.
Also,
you
are
saying
it's
easier
to
understand,
but
if
you
do
what
you
think
that
what
they're
looking
for
the
you
know
the
frames
anyway
losing
Wireshark
Wireshark,
already
knows
how
to
you
know,
decode
their
bar
format,
so
the
actually,
though
so
you
very
nicely,
but
what
the
NSA
my
format
looks
like
inside
it,
and
even
if.
B
E
A
C
F
D
G
C
A
A
A
B
A
J
J
So
the
only
thing
we
added
is
a
reference
to
beast,
which
is
somehow
the
veneer
Britta,
never
abilities
that
has
been
subject
to
in
TLS
and
well.
That's
was
all
the
comments
from
our
former
Eric,
so
this
is
the
only
comment
free.
We,
we
add
and
I
think
we're
done.
So
for
those
who
don't
remember
the
content
of
the
draft,
we
can
have
it
in
15
seconds
or
so
Eric.
This
is
your
comment.
J
A
A
K
Yeah
very
quick
background,
just
in
case
anyone's
missed
it
we're
talking
about
music
by
the
problem
with
with
with
I
guess
it
is
now
is
that
if
someone
has
a
product
computer,
they
could
break
both
of
helmand
there'll,
descriptively,
Hellman
and
Reed.
We
all
secrets,
we
don't
have
a
needs
one
with.
No
one
has
a
non
toy
to
computer,
yet
my
ones
concern
is
that
they
might
be
recording
traffic
now
and
then
decrypting
them
later
5-10
years
when
they
have
a
real
computer.
Next.
K
Now
there
are:
what
do
we
do
about
this?
The
short
term
strategy
is
to
simply
just
have
both
sides
have
a
shared
secret
and
stir
that
in
drag
key
does
security.
Secure
secret
is
strong;
they
can't
dive
it
that
we're
secure.
A
long
term
strategy
is
to,
of
course,
to
attempt
I
to
talk
up
to
actually
you
that
post
quantum
key
exchange
cerium
protocol.
K
K
A
L
Valerie
Spencer
for
those
plus
hair
insert
about
these
ones.
This
particular
approach
I
think
that
there
is
one
consideration
that
might
be
significant.
So
in
this
approach,
Deepika
BBK
is
used
as
an
additional,
an
additional
credential
to
to
reach
quantum
security,
so
it
doesn't
replace
an
ordinary
credentials
like
certificates.
L
K
L
K
L
L
That's
not
good
if
they
use
null
authentication
for
I
can
say
for
first
I
can
say
establishment
and
then
immediately
do
Ricky
with
PPK
you'll
get
authentication
to
get
authentication
to
say
that
it
will
means
that
the
first
I
can
say
will
be
using
null
authentications.
It
is
okay,
but
it
has
some
drawbacks.
First,
it
is
not
acceptable
to
ddos
attacks.
Well,
it
has
a
lot
of
drawbacks.
L
K
C
Yeah
a
week
we
can
simply
say
must
not
be
used
with,
like
no
sorry
with
OAuth.
No,
because
there's
no
point
anyway,
like
you
Yuki
like
earth
null
is
supposed
to
be,
you
don't
know
this
person
and
you
will
never
authenticate
them
and
so
having
a
out
of
bound
PPK
negotiated
already
makes
no
sense
in
the
context.
So
we
should
just
simply
say
must
not
and
then-
and
this
danger
will
be
limited,
I.
B
N
Dan
Harkins,
so
I
noticed
when
the
the
PPE
ID
is
fixed.
It
says
both
the
PPK
and
the
PPK
ID
are
limited
to
be
base64
character,
set.
So
I'm
wondering.
Why
are
you
imposing
the
requirement
on
what
the
PPK
itself
is
and
I
can
see
if
you're
gonna
limit
with
the
ID,
if
not
a
fixed,
ID
you're
specified
with
the
character
set
is,
but
what
do
you?
Why
are
you
imposing
this
on
the
shared
secret
itself.
K
B
So
so,
in
last
meeting
we
had
this
discussion
and
people
were
saying:
okay,
having
one
format,
data
to
try.
Everybody
is
easier
than
you
know.
Otherwise
you
have
a
hex
format.
You
have
binary
format
if
you
have
an
ASCII
format
and
then
people
can't
in
the
insert
spaces
or
or
or
noodles
there,
so
having
base64
encoded
stuff
in
there
configuration
file
and
in
the
excel.
You
know
data
and
it
doesn't
really
matter
right.
N
Well,
no,
it
does
because
it
says
it
has
to
be
a
base64
character
set,
so
it
doesn't
matter,
but
my
recollection
of
that
conversations
that
people
wanted
a
way
to
a
standard
way
to
distribute
the
PPK
and
it
does
actually
talk
about
RFC
60,
which
I
believe
was
my
suggestion
in
the
last
meeting
to
use
just
the
symmetric
key
envelope
that
PKK's
came
up
with
and
honor.
He
talks
about
doing
that.
So
that
being
the
case,
why
do
you
care
what
the
formative
the
PPK
is
about?.
C
Is
I
thought
one
of
the
consideration
was
as
well
that
based
on
experience
with
PSK
is
that
people
are
afraid
that
they
will
limit
themselves
to
the
ASCII
set
to
avoid
problems
of
incompatibility
of
misinterpreting
the
format
of
the
PPK,
and
so
people
stick
to
a
low,
entropy
ASCII
version.
Instead
of
using
the
full
range
of
randomness
we
have
and
that
using
basics.
The
first
sort
of
makes
it
easier
that
everybody
can
use
a
better
entropy
based
people
case.
O
O
E
Cut
the
line
after
this
comment
go
so
just
to
try
to
Claire
Tommy
Polly,
clarifying
and
adding
on
to
those
you're
right,
I
think
what
we
want
is.
It
should
be
easy
to
configure,
but
also
taking
in
the
direction
of
making
it
a
strong
key.
That's
not
just
some
set
of
ASCII
characters
and
I
like
the
current
encoding
and
it's
up
to
the
implementations
to
make
sure
that
you
can
easily
distributed.
G
Hi,
my
name
is
CJ
next
slide.
So,
following
on
what
Scott
said,
so
basically,
this
is
sort
of
a
long
term
solutions
to
the
threat.
When
who
knows
quantum
computer
becomes
available,
and
if
you
were
in
the
in
a
talk
where
Kenny
talked
about,
you
should
lover
the
first
line,
then
we
should
add
perhaps
a
big
engineering
problem
and
then,
when
it
happens,
obviously,
then
there
are
different,
obviously
will
be
vulnerable
and
then
there
are
also
works
already,
mainly
research
in
the
area
of
quantum
safe,
Oh,
post,
quantum,
algorithms
and
Mesa.
G
We
believe
that
I,
they
still
a
fix
compliant
next
slide,
please.
So
what
we
sort
of
a
proposed
was
that
to
do
optional,
key
exchange
so
having
another
key
exchange
in
additions
to
the
diffie-hellman
and
then
a
goal.
Basically,
we
want
to
keep
the
minimum
as
possible
on
the
only
modification
to
IV
to
we
want
to
maintain
the
compatibility
but
IV
to
and
also
if
needed,
in
the
future.
Who
knows
we
may
want
to
face
out
those
keys
that
are
vulnerable
next
slide,
please.
So
this
is
the
current.
G
The
format
of
of
the
qsk
payload
is
very
similar
to
a
DK
payload
next
slide,
so
obviously
backward
compatibility,
it's
a
something
that
needs
to
be
addressed.
So
we
thought
up
the
following.
Let's
say
once
need
to
implement
a
policy
where
we
want
to
do
a
format
to
allow
a
classical
sort
of
a
si
to
be
a
to
be
established.
G
So
basically,
the
initiator
will
send
a
set
of
proposals,
some
of
them
offering
ke
and
some
will
offer
a
combination
of
ke
and
and
post
quentin
crypto
and
then
obviously
one
needs
to
mark
the
qsk
payload
as
non
critical.
On
the
other
hand,
if
you
want
to
have
a
policy
where
only
sort
of
a
quantum
safe
channel
to
be
established,
then
on
the
si
payload,
we
only
offer
proposals
that
support
qsk
in
combination
with
K
and
if
needed
then
that
you
escape
a
lot
can
be
much
critical.
G
And
you
know
we
have
received
a
number
of
emails,
unique
as
to
us
people
said
there
are
in
the
actual
implementations.
This
might
not
be
the
case
and
also
said
that
potentially
might
not
be
a
good
idea
to
introduce
a
new
payload,
but
I'll
come
to
that
later
next
slide.
Please
I'm
gonna
go
through
this
very
quickly
in
internal
si.
Obviously
it's
a
quite
straightforward.
Now
it's
the
computation
of
a
key
map.
It's
basically
now
requires
a
concatenation
of
the
new
element
and
the
same
with
the
khemsa
rekeying
of
hlsa.
Next
one
please.
G
Likewise
under
each
key
in
the
ICS
a
we
when
there
is
a
quantum
say
for
key
exchange,
then
we'll
have
a
new
element
in
it:
okay,
so
next
one
please
now
that
was
the
easy
part
all
right
and
the
difficult
part
is
these
things.
The
trouble
with
the
key
is
using
condom.
Safe
sort
of
payload
is
that
it
is
very
large
and
question
for
thanks,
but
do
what
is
large?
A
very
good
question.
Welcome
to
that.
So
so
we
accented
with
a
number
of
them
the
Latisse
based
system.
G
G
B
G
G
So
we
have
consider
number
of
methods
to
me
to
get
fermentation
the
first
one
we
consider,
for
example,
is
that
okay,
we
will
use
out
of
c7
383
apologies
if
I've
got
the
number
wrong
to
use
the
fragmentation
over
there.
So
that
means
we
send
a
qsj
payload
as
part
of
a
key
or
unfortunately,
after
some
consideration.
G
We
recognize
nor
good
idea,
because
then
by
then,
if
quantum
computer
becomes
available,
people
be
able
to
decrypt
part
of
the
I
key
oath,
meaning
that
URI,
you
reveal
your
identity,
so
we
ditch
that
and
the
next
one
we
thought:
okay,
in
fact,
quite
similar,
the
first
one.
Why
do
you
know
why?
Don't
we
just
sort
of
a
immediately
reach
EDSA
once
you've
got
the
I
key
of
vision
again,
the
same
problem,
the
other
one
is
that
we
pick
you
as
a
payload
that
has
got
a
small
public
key
size.
G
I
mean
one
of
them,
one
of
them
that
we
considered
is
this
SI
d
H,
which
Kenny
is
not
to
invest.
Yesterday
is
a
very
new
scheme,
a
drop-in
replacement
to
defeat
Helmand
and
that
one
we
experimented
with
that
and
the
key
size
only
six
hundred
six
hundred
bytes
and
that
you
could
send
it
as
part
of
the
AI
is
and
then
and
then
you
sort
of
a
do
more
on
the
channel
si
the
other
one.
G
P
Every
scroller,
so
TV,
encapsulation
or
not
I
I,
would
encourage
you
out
to
let
their
best
be
the
enemy.
Is
it
good
here,
you're,
familiar
tempting
to
I
mean
this?
Is
a
hedge
you're
from
rarely
attempting
to
protect
these
your
data,
if
in
a
post
quantum
world
the
user
identities
are
revealed
for
these
are
data
is
corrected?
That's
a
lot
better
than
nothing,
and
given
that
I'm
worried
that
all
the
other
things
adjusting
are
impractical,
one
won't
work.
Mm-Hm.
P
Like
the
likely
as
easy
a
likely
outcome
of
not
doing
one
of
these
earlier
ones
that
you
say
there's
an
perhaps
these
are
identity
is
nothing
will
happen
at
all
which
don't
we
strictly
worse,
they're.
Not
these
are
entity,
except,
as
you
can
find,
an
elegant
way
to
protect
everything.
I
was
just
practicing
giving
up
an
user
identity
and
pressing
other
things.
Okay,
thanks.
G
C
B
All
right,
so
one
of
the
things
we
had
when
we
were
at
a
villain,
there's
actually
think
about
this
previous
document.
One
of
the
idea
we
had
there
that
you
could
actually
use
that
to
plug
in
real.
You
know
chemically
access
methods
in
of
in
future,
which
would
mean
that
they
we
have.
We
run
this
side
method
of
generating
the
keys,
and
then
we
configure
them
as
as
a
PPK
and
PPK.
B
B
You
advocate
actually
might
be
using
Coptic
something
it
right
using
TCP.
It
might
be
using
something
because
I
mean
it's
it's
something
that
this
you
know
think
that
you
need
to
do
beforehand,
but
depending
on
how
much
actually
you
trust
and
what
kind
of
protocol,
because
some
of
those
methods
actually
can
get
a
rate.
You
know
you
know
multiple,
you
know
I,
don't
this
you
can
use,
so
you
don't
have
to
necessarily
to
be
run
it
on
every
single
you
know
exchange.
You
can
actually
do
something
that
you
create.
B
You
know
ten
of
these
identities
you
can
use
in
the
future
or
something
like
that
and
and
then
run
out
before
you
run
out
of
that
you
do
the
exchange
again
or
something
like
that.
But
it's
it's
it's
one
of
the
ideas
out
of
that
and
actually
I
think
the
fragmentation
ruin
the
fragmentation.
It's
actually
good
thing,
because
Rex
one
of
the
things
we
have
I
think
if
I
run
correctly
tape,
I
guess
a
payload
yeah
length
is
32
bits
yeah
only
the
UDP
I
know
kind
of
that
things.
B
L
L
G
L
Simplify
all
the
situations
and
be
more
compatible
backward-compatible
and
during
the
reason
you
have
both
Korea
and
Chris
kept
notice.
Only
reasons
again,
I
can
think
of.
Is
that
you
don't
trust,
then
you
don't
trust
the
security
that
is
the
new
key
exchange
method
gives.
So
you
combines
both
exchange
most
traditional
difficult
man,
and
this.
L
G
It's
at
a
moment
of
every
seed,
as
you
know,
it's
still
in
the
transitional
process.
I
mean
obviously
existing
equipment
that
uses
ke,
payload
people
cross
certification
and
things
like
that,
I,
don't
think
we
can
throw
that
out
anytime
soon,
next
slide,
so
after
receiving
a
lot
of
these
unique
as
to
us
on
this,
so
no
so
that
meant
to
answers
on
your
point
is
that
we
also
consider,
if
it's
possible,
to
to
fragment
I,
say
in
it.
G
So
one
thing
we
came
up
with
is
to
use
these
things
on
the
initial
sort
of
a
exchange
you
send
sort
of
a
notify
paler
to
tell
the
other
side.
Do
you
support
that?
If
they
do,
then
they
come
back
with
a
cookies
and
and
also
to
respond
with
this
a
qsk
notify,
basically
that
contains
sort
of
a
indication
that
they
supports
it.
So
we
didn't
BSA
a
payload,
then
there'll
be
number
of
proposals
sort
of
a
indicates
in
there.
G
In
this
payload,
as
I
mentioned,
this
is
very,
very
new.
We're
so
exploring
these
things-
and
it's
not
even
in
draft
form,
is
something
that
we
work
on
after
receiving
a
number
feedback
on
this
next
slide.
Please.
So
we
also
got
a
source
source
code
on
this
thing,
so
we
use
a
strong,
chuan
and,
and
people
who
are
interested
and
obviously
is
there
I
mean.
B
If
we
decide
that
we
are
so
good
to
work
under
that,
I
think
we
are
going
to
be
deciding,
because
there
seems
to
be
lots
of
interesting
this,
but
anyway,
so
so
I
think
it's
too
early
to
start
talking
talking
about
what
kind
of
fragmentation
and
TCP
and
whatever.
Where
do
we
put
those
things
sort
of
great.
M
Makovsky
NCSA
yeah
thanks
EJ
for
his
draft
I.
Think
it's
a
good
all
the
document
Thanks.
The
one
comment
I'd
like
to
make
is
I
notice.
In
the
draft
you
make
mention
of
specific
algorithms
for
perfectly
exchange
and
you
you
know
you
have
certain
values
listed
for
them
and
public
key
sizes.
I
think
it's
probably
premature
to
be
doing
that
or
I
think
it's
probably
not
appropriate
for
this
particular
draft
I.
G
C
So
during
sag
we
just
heard
like
a
optimistic
estimate
of
like
this
will
take
seven
to
ten
years
before
we
figure
out
which
algorithms
were
going
to
use
so
I'm
wondering
if
this
work
isn't
a
little
bit
premature,
like
I
like
experimenting
and
I.
Think
that's
a
good
thing.
But
where
do
we
draw
the
line
like
and
I'm
just
looking
at
working
group
chairs
and
the
80s?
For
that.
B
So
actually
we
do
design
our
programs
our
protocol
so
that
they
have
a
crystallographer
ability.
So
we
need
to
do
that
here
too,
so
we
actually
I
prefer
to
mix
what
makes
what
our
system
is
so
that
we
can
actually
run
multiple
of
these
mechanisms.
So
we
can
actually
do
experimental
and
see
what
what
works,
what
doesn't
and
so
on
and
yes,
I,
agree
that
I,
don't
know
when
we
actually
going
to
be
designing
bits
of
those
algorithms
are
going
to
be
the
mandatory
to
implement.
C
B
Some
big
plop
to
that
and
another
one
send
some
to
serve
some
calculations
and
simply
big
block
that
then
we
have
a
shared
secret,
I
guess
most
of
these
are
this
kind
of
blocking
replacements,
fortify
Hellman
if
it,
if
there's
some
algorithmic,
that
requires
you,
know
seven
round
trips
and
doing
some
weird
things
in
the
middle,
that's
something
that
is
not
going
to
be.
For
example,
the
current
mechanism
is
I,
think
works
with
every
every
kind
of
this
kind
of
plug-in
algorithmic
for
the
film
on
which
has
one
economist.
C
B
Q
Q
Can
hear
me?
Yes,
even
he
Phillip
LaFrentz
I
serve
a
population,
so
I
just
want
to
express,
because
this
problem
is
something
that
we
donated
some
resources
and
we
essentially
came
up
to
pretty
similar
conclusions
and
crucians,
as
you
guys
did,
but
we
would
love
to
help
out
with
this
trance
and
really
catch.
So
we
don't
think
it's
a
good
idea.
It
is.
K
Okay,
I
just
want
to
basically
doesn't
mean,
there's
been
complaints
about
the
complexity
of
it.
There
are
basically
two
complex
questions
here.
That
they're
trying
to
address
one
is
is
how
to
to
actually
have
8a
both
a
traditional
and
quantum
algorithm,
because
we
don't
necessarily
trust
a
push
quantum
out-of-the-box
fact
I've
said
I
would
advise
asking
allowing
multiple
most
quantum
algorithms.
The
other
question
is
is
how
to
do
fragmentation
other
than
those
questions
that
the
problem
is
completely
trivial.
S
Hello,
this
is
kind
and
almost
everything
said:
I
don't
want
to
waste
time
on
motivation
and
solution.
We
did
some
experiments
with
my
Kelly's
some
years
ago
and
the
key
size
of
McAleese
is
way
beyond
64k.
By
the
way.
Last
year
the
New
Hope
algorithm
showed
up
and
there
was
an
implementation
and
strong
Swann,
and
we
also
did
some
experiments
with
that.
S
We
did
some
measurements
and
anybody
who
is
interested
in
some
comparison
numbers
I
love
to
share
that,
and
so,
but
these
are
PQ
only
mechanisms
and
what
we
heard
today
and
yesterday
and
what's
the
common
solution
at
the
moment
from
the
crypt
cryptographers
is
said-
to
have
a
combined
weight
on
mechanism
by
classical
th
and
by
AP
q
and
next
slide.
Please,
as
we
heard
there
is
no
simple
drop
in
solution.
S
We
have
this
fragmentation
issue
that
has
to
be
solved
and
if
we
use
the
TCP
thing,
then
yeah
that's
the
page,
but
it
it
was
my
purpose
to
use
Ike
over
UDP.
We
have
some
pros
and
cons
to
move
the
quantum
JFK
exchange
into
the
Eickhoff
exchange,
that
that
makes
the
I
guess
a
not
quantum
safe
but
as
being
already
discussed
or
heard.
This
might
not
be
a
problem
because
it
doesn't
address
active
attacks
at
the
moment
and
yeah.
The
other
thing
is
the
signalling
issue
that
is
also.
S
We
have
may
be
more
difficult
to
solve.
Where
to
put
this
combined
exchange,
we
can
use
a
new
transform
type
for
post
quantum
safe
agreement.
Then
we
can
combine
these
transforms
and
then
si
payload.
But
what
I?
What
I
see
is
that
the
key
exchange
payload
is
currently
cannot
refer
to
a
specific
transform
type.
S
It
only
refers
the
traffic
transform
ID,
so
we
cannot
easily
combine
different
key
exchange
payloads
in
the
in
the
exchange,
or
we
can
have
a
transform
type
for
combined
methods,
so
that
act
that
explicitly
says
I
want
to
combine
two
method
to
key
exchange
variants,
and
maybe
we
need
both
to
face
out
non
PQ
agreements
in
the
future.
So
but
that's
something
that
I
love
to
discuss
on
in
the
working
group.
If
the
working
group
is
going
to
adopt
this
problem,
thank
you.
P
So
I
have
to
apologize
for
not
like
a
koala
but
yeah.
If
you're
not
gonna,
ask
if
you
can
specify
it
as
if
it
were
alternative
to
diffie-hellman
right,
you
want
to
be
sure
you
signal.
I
can't
use
this
alone,
so
I
don't
know.
Is
it
that's
the
point
of
the
second?
The
second
point,
which
is
that
combined
usually
how
you
would
say:
I
won't
use
this
road
if
the
almond
yeah
and
he's
like
it's
cut,
it's
like
really
bad.
If
you
just
use
the
vq
thing
without
the
V
element.
N
Dan
Harkins,
so
it
seems
to
me
that
moving
this
QE
payload
or
you
know,
ke
payload
or
whatever
to
the
icon
exchange,
solves
two
problems
right.
It's
gonna!
It's
gonna
fix
the
fragmentation
problem
because
there's
already
an
RC
for
doing
vitamin
and
it
addresses
the
backwards
compatibility
issue
because
you
can
in
the
I
guess
and
negotiation.
You
can
send
some
notify.
N
That
says
you
know:
I
do
quantum,
but
by
the
I,
do
the
PC
to
PC
ke
thing
and
the
other
guy
will
either
if
he
doesn't
send
it
back,
then
you
know
that
you're
you're
unable
to
send
the
the
the
PQ
ke
and
the
and
the
DI
Karthik's
exchange,
so
I
think
I.
Think
there's
really
no
argument
for
putting
that
in
the
in
the
I
cough
exchange.
It
just
causes
two
problems
that
that.
N
C
Okay,
so
oh
do
you
have
still
comment
about
this?
Just
quick
because
because
post
this
presentation
or
previous
on
our
mumbling
about
transform
type,
so
I
do
want
to
make
my
point
about
transform
types
that
if
we
add
a
new
transform
type,
you
basically
do
doubling
the
proposals,
because
you
have
that
list
of
proposals
we
have.
We've
already
did
this
once
for
a
a
DS,
and
so
now
we're
gonna
have
four
proposals
for
each
thing.
It's
gonna
get
silly.
It's
it's
going
to.
B
Get
I
question
one
again
which
had
250.
Actually
it
was
limited,
256
proposals,
that's
why
we
couldn't
propose
everything
so
anyway.
So
this
is
something
as
I
said.
Our
current
Charter
says
that
we
do
about
the
same
post,
quantum
protection
about
having
accurate
and
one
meaning
the
preset
key
type
of
thing.
This
is
out
of
our
current
charter.
We
are
going
to
be
recharging
anyway
in
Singapore,
because
we,
our
charter,
ends
in
2017
December,
so
we
are
at.
This
is
something
that
I
think
there
is
clear
you
know,
I
would
actually
want
to
get
hung.
B
If
you
think
that
we
should
actually
include
this
in
charter,
so
we
can
actually
get
ready
to
invited
by
the
Singapore.
That's
our
during
discussion
so
who
are
in
favor
of
adding
some
kind
of
you
know
not
be
not
preset
keep
based
on.
You
know,
first
quantum
crypto
algorithm
thing
in
Ike
version
in
India
charter
for
the
it
for
the
next
charter.
Not
yes,
sir.
B
V
A
U
U
U
That
looks
better
so
once
again,
minimal,
tip2
client,
the
draft
that
is
linked.
There
is
not
ours,
but
the
original
geography
to
draft.
Yes,
you
can
just
stay
there,
and
so
how
far
is
it
minimal?
But
what
we
do
is
just
reduce
the
protocol
to
a
subset
required
to
get
a
si
and
maintain
it,
and
the
result
can
be
seen
here
so
different
to
the
normal
equity.
We
have
got
a
communication
between
a
constrained
client
and
a
key
server.
U
So,
additionally,
you
send
a
group
ID
which,
which
size
you
wish
to
join
that
group
and
the
key
server
authenticates
you
decides
if
you
are
allowed
to
join
a
group,
then
answers
here
with
its
own
authentication
and
identity
and
the
SI
properties
and
the
corresponding
keys
and
keys.
I
ricky
looks
pretty
much
the
same
as
the
response
to
cheese.
U
I
off
as
you
get
authentication
cheese,
a
properties
and
the
corresponding
keys
and
there's
two
sets
of
keys
the
transport
keys
and
key
encryption
keys,
one
which
you
used
for
the
communication
in
the
group,
the
second
it's
used
for
the
wreaking.
So
next
slide
please.
So
our
implementation
is
built
on
ride.
U
For
the
other
two
we
took
some
time
measurements
next
slide.
Please!
So
what
you
can
see
here
from
the
left
to
right
are
the
steps
in
a
protocol,
the
preparation
of
the
SA
inert
processing
of
DSA
in
the
preparation
of
G
off
and
processing
the
earth,
and
what
you
can
see
here,
the
big
one
is
the
diffie-hellman
shared
secret
calculation,
which
is
quite
big
compared
to
the
rest,
but
actually
a
quite
good
result
like
under
L
on
the
right
side.
U
U
So
again,
how
did
the
minimization
we
just
took
up
I,
optional,
payloads
and
reduced
it
to
all
you
need
to
get
through
the
essay
and
to
maintain
it,
and
it
would
actually
be
interesting
to
specify
I
a
server
configuration
as
a
main
problem,
or
the
biggest
messages
we
had
handled
were
the
server
messages
which
included
a
lot
of
vendor
ID,
payloads
notification
alerts,
and
so
on
next
slide.
Please
we
will
release
our
implementation
on
github
I
guess
it's
gonna
be
somewhere
around
next
week.
U
Q
Hi,
my
Cisco,
so
just
for
the
sake
of
people
who
aren't
familiar
with
this.
This
geography
is
a
draft
that
Valerie
and
you
of
and
I
have
this
meant
to
protect
multicast
IP
SEC.
It's
there
say
we
weren't
looking
at
the
constrained
case,
but
it's
really
quite
interesting
to
see
that
it
it
looks
like
it
could.
At
least
the
group
member
side
can
run
on
the
constrains
case
and
can
run
worth
a
commercial
version
of
a
key
server.
W
W
U
B
B
U
B
C
B
Issue
here,
but
so
so
I
have
one
question
here,
because
we
actually
support
area
director
also
so
wake
up
yeah
yeah.
So
so
this
is
again.
This
is
the
not
minimal
version,
but
this
normal
equation
to
a
group.
You
know
Kim
and
I
spend
the
right
person
to
is
craft
that
has
been
out
for
starting
for
2010
or
something
like
that
and
it
because
em
sector
a
group
is
dead.
It
can't
go
there
and,
of
course,
never
start
discussing
about.
Should
we
actually
have
it?
You
know
ad
sponsored
or
should
be
taking
the
working
group.
B
P
B
Right
but
so
I
have
a
question
for
the
croup,
then,
who
would
think
that
this
actually
would
be
useful
to
document
this
in
to
have
this
GDL
GI
person
to
to
go
through
the
working
group
and
and
to
be
able
to
item
or
attitude
the
Charter,
so
we
can
actually
working
at
this
book.
This
would
actually
be
this
specific
trust
going
through,
but
the
back
pocket
gets
changed
control
if
you
to
be
able
to
contain
so
those
who
are
who
actually
think
that
we
can
actually
answer
that
Kirsten.
B
Groups
group
teammates
it
because
we
have
to
have
that
done
before
we
can
have
a
mini
monolithic.
The
minimal
actually
belongs
to
the
LV
IG,
not
in
here,
because
it
be
here.
We
only
do
things
that
are
you
know,
modifying
the
protocol
or
the
minimum
ones
try
to
stay
within
the
protocol,
but
just
specify
what
you
need
to
implement
so
I
wonder
if
you
can
actually
make
a
ham
here
or
no
I.
Let's,
let's
make
a
home
here.
B
L
F
F
L
Please
so
this
is
this
picture
just
shows
how
karma
backwards,
just
as
an
example,
so
first
it
says,
established
its
its
oversimplified,
but
some
things
are
left
out
by
extension
since
are
shown
so
I
could
say
anything.
I
calls
exchanges
it
both
when
I
post
PS
indicates
it
is
if
they
support
my
bike
and
when
initiator,
want
to
change
its
IP
address.
It
sends
update
to
say
there
is
identification
using
new
address
in
this
example:
IP,
double
I
and
so
responding.
L
L
So,
if
not
is
in
between
then,
depending
on
the
not
behavior
original
respondent
may
not
initiate,
update,
may
or
may
not
initiate
update
because
not
can
block
incoming
connection
without
previously
seen
packets
going
outside,
and
if
original
respondents
multihomed
zone
it
may
not
be
able
to
instruct
in
shelter
to
switch.
You
say
to
another
address,
even
if
you
want
to
so.
My
boy
can
general
permit
initially
responded
to
to
try
address,
update
procedure,
but
a
in.
L
L
World
because
Knights
are
not
so
almost
everywhere
currently
and
next,
please
so
the
concepts
of
limitation
is
the
network
asymmetry
introduced
by
restricted
cannot.
This
is
just
an
example.
So
if
respondent
address
is
changed,
some
response
to
change
s
address
to
IP
Double
R,
it
tried
to
send
information
exchange,
but
with
no
mapping
this
packet
will
probably
drop
by
net
in
between.
So
as.
L
L
And
perform
switching
to
and
others
Oh
next,
please
so
proposed
solution
is
as
follows.
So
respond
to
requests
in
jet,
initiator
to
move,
say
to
a
new
address
by
initiated
informational
exchange
inside
this
exchange,
and
you
notification
switch
to
IP
address
which
contains,
and
you
responders
address,
address
and
to
do
with
middleboxes.
This
exchange
is
initiated
from
old,
say
address
so,
but
initiate
a
response
to
an
you
responders
letters
which
is
inside
our
notification.
So
it
is
a
violation
of
section
2,
dr.
Mariner,
RFC,
72
96.
L
L
M
L
So
this
is
just
an
illustration,
so,
when
this
point
I
want
to
switch
it
to
move
existing
say
to
address
a
P
Double
R,
it
sends
an
affirmance.
It
starts
informational
exchange
from
old
address
in
blue
I
PR,
but
IP
Double
R
is
inside
information
mode,
so
initiator
gets
this
exchange,
so
it
comes
through
the
not
because
it
using
existing
mapping
and
after
that
and
shaker
responds
to
these
new
others.
Ip
table
double
are
in
green
and
it
creates
a
new
mapping
on
net
so
that
the
next
package
that
will
be
sent
so
the.
L
L
The
data
offer
notification
for
my
back,
supported
physically
currently
empty
and
must
be
ignore
it
for
unsupported
mobike
appears.
So,
if
you
we
can
add
here
similar
even
a
single
bite
or
some
pretty
fine
streams,
it
indicates
that
in
the
chance
to
support
this
extension,
so
next
please
so
thanks.
What
do
you
think
alright.
B
There
are
communion
I
think
it's
a
very
bad
idea
to
start
puffing
packets
to
send
packets
that,
from
the
IP
address
that
you
don't
own,
is
going
to
be
dropped
anyway,
because
I
mean
the
first
up.
First
hop
router
will
sector,
oh
I,
get
this
address
that
is
not
belonging
to
any
of
my
it
rephrase
it
shouldn't
be
coming
from
here.
Doing
source
address
validation.
It
actually
drops
a
pocket.
Well,
they
should
be
doing
that.
B
I,
don't
do
it,
but
they
should
be
doing
well,
but
but
but
I
guess
said
they
will
do
that
more
and
more
because
they
are
just
poof.
We
need
something
that
this
you
know
considering
the
attack
and
people
are
trying
to.
You
know,
protect
against
it
so
so
and
and
making
a
protocol
that
relies
on
being
able
to
send
spoofed
pockets.
B
Can
actually
do
that
already
in
a
more
bike
you
send
their
address,
update
that
you
delete
the
first
address
that
Wi-Fi
address.
You
only
keep
their
keep
the
3G
address
and
then
then
indicator.
We
notice
that
oh,
the
address
that
I'm
using
actually
got
lost
so
I
need
to
do
address,
update
now
myself
to
have
to
start
using
the
other
address,
so
that
actually
works
already.
B
The
only
case
very
doctor
unit,
which
doesn't
work
is
that
when
you
lose
the
address
completely
when
you,
then
you
don't
have
an
address,
the
pocket,
Civic
or
address
you
could
send
the
pocket
to
the
other
end.
And
if
you
lose
the
address,
then
you
don't
the
address
anymore,
so
you
can't
use
it
well.
L
That
will
probably
work,
but
it
doesn't
well.
It
doesn't
allow
responded
to
well
after
that,
after
that
procedure,
you've
explained
the
initiator
will
on
its
wheels
move
to
previous
address,
because
then
you've
set
up
datacenters
addresses
game,
I
think
so
you
cannot
control.
You
cannot
force
him
to
serve
each
Java,
one
particular
dress.
It
is
not
preferred
to
you
the
responder,
for
what
burns
games
is
very
important,
so
you
you,
you
will
probably
be
sweet
initiator
to
move
to
another
address,
but
once
again
you
will
update
the
cell
addresses
for
both
addresses.
B
This
is
still
as
a
mes
not
to
share
over,
but
yes,
in
that
case,
yes,
it
sweet,
seek
the
new
address,
telling
data
and
you
should
switch
lose
this
address
and
our
own
all
of
the
addresses
is
still
fine
and
that's
actually
one
of
the
things
we
got
can
specify.
But
having
found
something,
that's
saying
always
use
disproved
address
and
resend
pockets
been
from
this
proof.
Others,
that's
I,
think
they
will
get
quite
a
lot
of
discusses
in
a
you
know
from
iAds
anyway,
if
we
start
doing
that,
so
so
I
don't
propose.
B
F
B
Predict
but
I
need
a
prototype
old
because
there
is
mobile
is
still
related
to
IPSec,
so
it
actually
could
be
part
of
this
working
group
or
could
not
this
whole.
This
is
actually
something
we
have
to
decide.
It's
currently
isn't
in
the
Charter.
This
is
something
that
we
can
also
add
it
that
the
Charter,
if
you
want,
we
have
to
talk
with
the
area
director
about
that
and
because
it's
a
little
bit
more
further
away
than
you
know,
then
other
things
to
be
actually
I
think
I'm
able
to
talk
with
our
directors
first.
B
X
B
R
Hiya
Tobias
here
I
will
just
quickly
present
in
just
status,
update
on
diet.
Esp
next
slide,
please
so
for
those
who
don't
know,
we
discussed
it
quite
a
few
times
also
here
and
the
last
time
we
really
did
just
discussed.
It
was
in
Berlin
in
the
6lo
meeting,
because
it's
about
compressing
the
ESP
packet,
and
that
was
quite
some
support
that
people
wanted
to
use
IPSec
in
constrained
environments,
but
because
it's
more
IPSec
related.
We
were
asked
to
move
back
here
and
we
kind
of
redesigned
that
is
PD
sign.
R
R
So
the
idea
is
to
have
compression
rules
which
define
how
each
fields
of
the
ESP
packets
is
going
to
be
compressed
and
we
have
function
how
it
is
compressed,
for
example,
sent
value
just
means,
don't
compress
and
lead,
it
means
just
indeed
it
is
and
get
it
from
a
predefined
context
and
tidy
SP
is
one
strategy
just
saying
how
to
use
this
functions
next
slide.
So
just
some
oh
yeah,
the
title
is
kind
of
missing.
You
see
it
at
the
top.
We
can
say
for
an
IOT
VPN
scenario.
R
We
can
save
68
bytes,
which
is
quite
a
lot
if
you
consider
the
scenarios
of
IOT,
but
we
could
talk
about
maybe
128
bytes
of
MTU
or
even
less,
and
what
we
define
is
the
one
on
the
right
here.
Basically,
everything
in
the
red
is
pretty
ago.
She
ate
it.
The
rest
is
got
from
traffic
selectors
and
SAS.
We
already
have
next
slide.
We
also
try
to
be
more
open
for
other
use
cases
outside
IOT.
So
this
would
be
an
example
for
traditional
VPN
VPN,
so
we
could
compress
the
inner
IP
packet
of
a
VPN.
R
In
this
case
it's
ipv6.
We
can
also
do
ipv4
and
also
ipv4
and
ipv6
and
ipv6
and
ipv4,
and
also
just
defining
a
few
compression
rules.
Yes,
next
slide,
so
the
question
we
were
thinking
about
what
is
better
to
actually
have
better
compression
or
more
complexity,
because
the
better
the
compression
do
more
complex
is
to
negotiation.
And
the
second
question
is
how
to
move
forward
with
this
document.
E
Tommy
Polly
Apple,
so
I
guess
to
the
second
one.
I
think
this
is
really
cool
and
I'd
like
to
see
us
continue
working
on
it
and
get
specified
for
these
constrained
environments
to
make
sure
that
IPSec
is
a
viable
option
there.
So
I
think
we
should
continue
we're
kind
of
for
the
first
one,
I
guess
based
on
your
work
so
far.
Where
do
you
think
we
are
on
that
scale
currently
between
conversion
complexity?
So.
R
Currently
kind
of
strategy
which
we
at
the
moment
called
IDs
pivot,
so
sure
it
was
just
a
strategy
for
scenarios
and
the
complexity
of
negotiating
is
very
low
because
we
get
a
lot
of
stuff,
which
already
is
there.
If
you
consider
other
use
cases,
we
can
either
define
new
strategies
or
included
in
the
strategy,
making
the
strategy
more
complex.
So
at
the
moment
we
are
trying
to
minimize
the
complexity
but
maximize
the
compression.
That's
the
current
use
case
on
RIT.
That's
where.
E
J
So
I
think
one
of
the
the
balance
between
complexity
is
when
we
have
mostly
ipv4
in
ipv6
or
the
reverse.
It
is
currently
some
compression
is,
is
being
made,
but
by
you
Ray,
you
decompress,
by
taking
the
parameters
from
the
outer
IP,
which
doesn't
matter
if
they
are
not
the
same
darshan.
So
the
question
is:
should
we
add
some
complexity
at
that
point,
or
should
we
just
leave
it
uncompressed
for
the
regular
VPN.
E
B
I
have
question
I
understand
that
this
is
still
doing
exactly
the
same.
You
know
when
you
you
take
a
ESP
pocket,
you
compress
it
you
get
something
that
you
sent
the
other
and
you
decompress
it,
and
then
you
run
get
X
at
the
same
ESP
pocket
back.
Yes,
hopefully
exit
except,
of
course
you
know
the
sequence
number,
you
miss,
you
don't
change!
You
just
assume
it's
funny
bigger
than
the
previous
ones.
Yes,
true,
on
the
other
hand,
there's
also
sequence
number
compressions.
R
B
No
penance
talked
about
yeah,
that's
probably
one
of
the
things
that
they
actually
do
to
have
a
little
bit
more
complexity,
that
we
actually
want
to
recover
from
cases
per
sequence,
number
good,
okay,
so
the
question
is
now
is
tax
rate.
This
is
okay
in
something
that
has
been
tried.
Esp
has
been
here
a
couple
of
times,
and
this
is
again
it's
not
something
that
actually
modifies.
B
You
know
the
pail
of
payloads
in
the
or
actually
slice
pillows
in
the
wire,
but
not
actually,
the
original
ESP
pocket
is
going
to
be
same,
so
this
is
still
kind
of
somewhat
similar,
I
kind
of
think
that
food
calls
as
a
like
with
implementation
guidance
instead
of
the
year,
but
I
think
it
actually
might
be
better
here,
because
we
actually,
we
know
better
here
what
we
can
do.
No
that's
what
I
was
thinking
about
should
we
actually
add
this
also
in
the
Charter
for
the
Charter
discussion
for
Singapore.
B
Of
course,
all
of
this
needs
to
be
you
know
confirmed
in
in
a
list
and
also
in
Singapore.
We
have
to
get
the
80
and
80s
to
accept
those.
So
do
you
think
that
I'm
going
to
ask
for
hum
how
many
people
actually
think
that
this
should
be
included
or
should
not
be
included
in
he
in
here
some
kind
of
this
tsp?
Actually,
in
this
case,
it's
probably
going
to
be
this
draft
and
full,
of
course
modifying
it
as
we
go
forward.
So
how
many
people
think
that
we
should
include
this
in
charter
hum
now.
B
Y
Also
co-chair
of
Phi
2
and
s
F.
So
if
you've
been
following
the
mail
and
if
there
was
this
thread
on
both
lists
about
the
proposed
work
item
for
i2,
an
ACEF
about
having
Sdn
controllers,
configure,
IPSec,
endpoints
and
there's
seems
to
be
a
kind
of
a
disconnect
between
the
IPSec
people,
especially
the
P
n
people,
as
opposed
to
the
data
center
and
SD
n
people.
So
what
we're
planning
to
do
other
than
come
and
sabotage
the
I
to
NSF
meeting
every
time
is
to
hold
the
virtual
interim
meeting.
Z
Z
There
is
another
draft
that
is
a
four
three
zero
seven
bits
which
says
that
PSS
must
be
implemented
and
because
CAS
may
be
included,
but
even
then,
if
we
still
have
to
support
both,
we
need
to
know
how
we
should
tell
the
initiator
or
the
responder
that
we're
choosing
that
so
could
we
have
a
method
or
a
way
to
figure
out
what
the
other
person
is
using,
because
we
don't
know
and
to
read,
to
do
the
interoperability
test
right
now.
Strongswan
uses
pkcs
and
it
does
not
use
PSS,
as
mandated.
B
C
Like
probably
so,
no
I
I
do
think
it's
a
real
pronto,
because
deedie
hash,
the
de
notifying
Ike
in
it
for
the
the
signature
is
just
not
good
enough
for
us
and
we're
running
into
this
problem
now
and
we
suspect
it
will
run
into
more
problems
later
when
things
get
more
complicated
with
post
quantum
things.
So
I
do
think
it's
naughty.
We
should
consider
to
put
on
the
charter
all
right
so.
