►
From YouTube: IETF99-SIDROPS-20170717-1550
Description
SIDROPS meeting session at IETF99
2017/07/17 1550
https://datatracker.ietf.org/meeting/99/proceedings/
A
B
Afternoon,
if
you're
in
the
room
for
the
cider
ops
working
group
you're
in
the
right
room,
if
you
think
you're
at
something
else,
you
should
leave
now
or
stay,
be
quiet
and
listen.
You
might
learn
something.
I
know
I
will.
If
somebody
in
the
back
you
please
close
the
door.
That
would
be
great,
we'll
be
getting
started
in
a
moment
or
two
or
just
sorting
out
some
slide
problems.
B
F
B
All
right,
as
I
said
earlier,
come
on
computer.
This
is
the
cider
drops
working
group
at
IETF,
99,
I'm
Chris,
that's
K
yer,
and
we
have
a
presenter
a
mirror
after
I'm
done,
I
think
we
have
a
note-taker
Jared,
a
jabber
scribe
Joel
once
they
got
those
backwards
next
slide.
Please
note:
well
tiny,
tiny
font.
You
view
it
on
the
website.
It
hasn't
changed
since
last
time.
I
hope,
because
that's
what
I
copied
it
from
thanks.
B
It
changed
great
I'll
change.
The
slide
later
itu
already
know
that
it
changed.
So
you
didn't
have
to
read
it
okay,
so
the
agenda
is
relatively
long
relatively
full
this
time,
so
we
don't
have
a
lot
of
spare
time
so
in
case
anybody
wants
to
add
anything
else.
No
great.
We
have
the
following
set
presentations.
Their
mayor
will
be
up
next,
but
in
the
agenda,
bashing
thing
will
also
cover
current
documents.
Skipper
support
documents
on
the
tools
page
for
us
they're.
B
Still
the
same
four
documents
we've
had
before:
there's
some
progress
for
route
server,
RPK
light,
I,
believe
I,
think
those
folks
are
in
the
room
and
had
something
to
say:
I
can
hop
up
and
say
it
if
they
like
three
to
one
I,
think
they
have
some
updates
they're
working
on
since
they're
not
coming
to
the
mic,
and
then
they'd
like
to
ask
for
working
group
last
call.
So
maybe
in
three
four
weeks
we'll
have
our
group
last
call
message
for
RPI
light
or
about
server
our
PLA.
B
If
you
haven't
read
the
draft,
you
should
probably
go
read
it
now
or
after
other
presentations
serve
today
and
send
comments
along
to
the
author's
tree.
Validation
says,
is
coming
up
for
expiration,
but
I
believe
that
Tim
is
planning
to
present
today
about
it.
So
we'll
get
some
update
on
that
as
well.
That's
where
we
are
next
now.
It's.
I
K
L
G
M
M
N
So,
if
you're
stepping
out
of
the
box
okay,
so
it's
apical
deployment
status
challenges
and
the
learning
validator,
which
is
one
of
all
the
things
we
are
trying
to
do
to
help
applique
and
because,
okay,
this
is
joint
focus.
You
can
see
with
the
list
of
many
people
down
here:
oops
you're,
single
ad
Thomas
Albert,
which
is
here
your
film
Casa,
which
is
here
a
fig
birds
which
is
here
Michael,
Shapiro
and
fire
film,
on
which
not
you,
okay,
so
I
talked
very
briefly
about
a
PKI.
N
Well,
you
all
know
it's
a
just
skip
over
death
and
then
about
who
are
adoption.
The
trend
won't
Wars,
which
are,
in
our
opinion,
a
big
problem,
especially
for
validation.
So
we
talked
about
that
the
causes
of
the
damages
of
that
and
then
the
IV
adoption
status
and
the
challenges
facing
that
which
are
the
kind
of
thing
we
are
trying
to
solve,
the
impact
of
partial
our
V
adoption.
As
you
will
see,
adoption
of
our
V
is
almost
non-existent.
So
we'll
talk
well.
N
If
we
had
a
slightly
better
adoption,
would
it
help
short
answer
not
so
much?
We
need
significant
adoption.
So
what
do
we
do
and
we'll
talk
about
directions
that
we
are
pursuing
for
improving
the
deployment
of
all
that
which
is
Warner,
Tata,
very
simple
mechanism
for
fixing
or
identifying
incorrect
was,
and
then
the
smart
validator,
which
is
our
main
focus,
which
is
the
mechanism
for
improving
the
validator
or
an
improved
version
of
the
validator
and
that's
prototype
implementation
we
have.
N
We
are
hopefully
moving
soon
to
prototype
experiments
with
the
prototype
deployments
and
so
on,
and
we
are
looking
for
more
partners
to
discuss
this
with
so
I
hope.
Some
of
you
will
be
interested
in
in
that
code.
Okay,
hopefully
we'll
do
a
demo,
probably
not.
Actually
that
will
see
if
you
have
time.
Okay,
you
all
know
about
our
PK
I.
Don't
need
to
explain
about
that.
Essentially,
groups.
N
Essentially,
it's
a
linkage
between
the
IP
prefix
and
the
origin,
and
possibly
the
the
max
links
fault
for
that,
and
the
main
point
is
that
for
for
Africa
to
work
against
router
hijacking,
we
must
domains
must
the
vault
origin
validation,
our
V,
that
is
the
should
drop
BGP
announcements
which
conflict
with
or
without
that,
just
issuing
words
is
not
actually
very
interesting.
The
whole
question
is:
do
would
the
main
the
service
providers
would
the
actually
is
throwaway
BGP
announcement
which
contradicted
published
valid
wars?
Okay,
so
that's
really
our
focus.
N
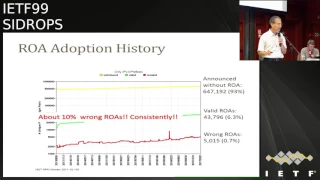
If
we
look
at
what
option
history,
there
is
a
progress,
as
you
see
in
the
green
line
to
his
progress.
There
are
more
novels
being
issued.
Of
course,
there's
also
progressing
the
Internet
in
general.
As
you
see
in
the
yellow
lines,
the
Internet
itself
is
growing,
but
walls
are
growing
in
a
slightly
higher
pace
than
the
general
internet.
So
that's
good.
However,
the
problem
is
the
red
line.
The
red
line
has
the
arrows
and
I.
This
line
of
arrows
is
kind
of
erratic,
and
it's
going,
you
know,
jumping
up
and
down
and
so
on.
N
It
is
pretty
consistently
10
percent
about
10
percent
of
the
issue.
Doors
are
incorrect,
10
percent
arrows
is
a
lot
and
that
really
can
be
a
problem.
Ok
and
now
what
happens?
If
we
have
an
incorrect
such
a
mistake
in
the
wrong
work,
and
we
do
our
V
like
we're
supposed
to,
then
we
drew
drop,
correct,
bgp
announcements,
that
is,
we
are
going
to
lose
some
good
traffic.
How
many
domains
then
are
actually
doing
it
are
doing
the
LV,
and
the
answer
is
assumed.
One
would
expect
if
the
situation
very
very
few
okay.
N
So
why
would
we
even
have
one
growers?
So
this
is
a
real-life
example
of
France
Telecom
I,
don't
know
it
may
be
recently
it
was
fixed,
but
until
quite
recently
it
was
not
faced
those
all
we
did
ask
them
to
fix
it,
and
there
had
this
pretty
large
block,
perfect,
okay,
/
witch-king
prefix
out
of
which
web
some
customers,
you
always
distress,
24
and
so
on.
Like
many
providers
do
now,
France
Telecom
are
good
guys.
They
are
issued
their
own
laws.
N
The
only
problem
is:
is
a
provider
they've
not
made
sure
that
the
customers
will
also
issue
worse
as
a
result?
If
my
internet
service
provider
will
be
filled
during
our,
we
will
be
featuring
announcements
which
contrary
is
wrong.
Then
he
might
supermarket
chain
using
it.
We
not
be
able
to
contact
them
on
our
website
or
domain
and
I
will
not
get
in
your
word
and
I
love
you,
oh
good,
okay,
so
this
is
really
a
problem.
Ok,
well,
you
may
not
care
about
your
goals,
but
I
do
so.
N
This
is
really
a
problem
and
therefore
we
are
all
here
together
to
make
sure
that
I
get
the
steady
supply
of
your
votes.
Okay,
okay,
so
the
question
is
how
many
of
the
service
providers
great?
What
is
the
risk
for
me
if
not
getting
Yahoo,
and
for
that?
It's
not
trivial
to
measure
it
initially,
we
did
is
very
indirect
imprecise
but
very
easy
to
do.
Experiment,
which
is
we
just
look
at
the
different
collector
of
BGP
announcement
where
we
go
all
the
monitors
we
could
have.
N
You
know
public
availability
that
we
could
check
and
we
checked
which
of
them
get
all
of
these
incorrect
roles,
because
if
you,
if
you
get
one
of
these,
it's
incorrect
BGP
announcement,
because
if
you
get
it's
not
really
linked
with
your
hands
right,
it's
a
digit
pronounces
which
contradict
one
of
these
actually
kind
of
incorrect
like
France
télécom.
So
if
you
get
these
BGP
not
so
that
means
that
the
entire
airspace
does
not
enforce
or
Yohe
okay.
N
So
that's
what
we
check-
and
we
could
learn
by
this
sum-
is
that
we
not
appealed
almost
like
him.
We
also
do
not
deploy
our
V
and
that
gave
us.
You
know
that
at
least
eighty
of
the
top
hundred
a
ESPYs
do
not
enforce
our
V,
which
is
pretty
bad,
as
you
will
see
in
a
moment,
it's
actually
for
deployment
for
the
value
of
RPI
is
very
bad.
Is
reality
like
this?
So
can
we
measure
more
precisely
to
make
sure
if
this
is
correct?
Incorrect?
N
Maybe
it
is
reality
is
better
or
maybe
reality
is
even
worse.
So
we
did
some
more
competitor,
IV
measurements
actually
Thomas
here,
which
is
sitting
over
there.
I
can
I
can
give
you
some
okay,
so
Thomas,
which
is
just
a
guy,
going
blind
now
also
NDA
gifts,
so
he
ends
the
basic
result.
I
don't
have
time
to
go
over
it.
We
did
use
three
different
measurement
meadows
and
so
on
the
basic
answer
we
are
still
doing.
N
Some
of
this
experiment
with
the
basic
answer
is
only
a
handful
like
on
one
hand
or
at
most
two
hands
domains
or
providers
enforce
our
V,
so
this
is
almost
non-existent.
Okay
in
in
real
life,
which
is
not
surprising,
if
you
consider
the
result,
if
you
do
it,
you
will
lose
about
your
10%
of
the
traffic
for
domains
which
are
doing
the
rowers
will
be
mistakes,
you
will
be
losing
some
significant
amount
of
traffic
and
the
Randi,
and
quite
a
few
others
have
done.
N
Also
some
similar
measurements
I
believe
is
for
what
I
understood,
they're
pretty
similar
results,
but
we
didn't
see
it
completely
tails.
So
we
have
to
see
exactly,
but
probably
it
seems
like
there
is
a
very
similar,
so
okay,
so
the
climate
is
very,
very
limited,
extremely
limited.
What
is
the
impact
of
this
partial
deployment
of
our?
We
may
make
if
we
want
or
send
deployment
we
still
one
percent
benefit,
maybe
more,
maybe
if
we're
5%,
we'll
get
five
percent
benefit,
or
even
more
and
so
on.
N
So
that's
a
question
like
what
is
the
impact
so
before
I
could
present?
The
actual
is
that
that
me
explain
why.
Essentially,
situation
is
bad,
that
is,
if
we
have
one
percent
deployment,
we
are
expecting
to
have
less
than
one
percent
benefit
and
the
basic
reason
is
collateral
damage.
What
we
call
it.
Let
us
look
at
this
example:
okay
and
the
main
swings
in
green
or
s3
is
in
green
because
he
is
actually
deploying
our
way.
N
So
that's
a
good
omen,
but
the
main
two
is
not
deploying
now
here
is
our
attacker,
and
here
is
a
good
guy.
Okay,
what
they
do
they
both
announce,
one
one,
one
perfect
one
1/24.
Actually
the
good
omen
is
announcing
one
one:
zero,
zero
16,
which
is
a
super
prefix,
but
Delta
K,
of
course,
is
doing
a
sub
prefix
attack,
because
this
is
the
most
effective
attack.
What
is
happening
now
is
affected
domains.
Flea
has
adopted.
Our
our
read
does
not
help
the
traffic
because
the
traffic
will
still
be
sent
to
the
attacker.
N
The
traffic
to
the
sub
prefix
is
still
sent
to
the
attacker
because
of
the
sub
prefix
attack,
they're,
mainly
a
lot
immensely
rpki
does
solve
the
sub
perfect
attack.
Don't
misunderstand
me,
however:
here
it
does
not,
because
we
have
here
a
domain
on
the
way
which
does
not
enforce
and
therefore,
with
the
traffic
hitches
domain,
two
as
it
would,
it
would
actually
be
misrouted
and
sent
to
the
attacker,
so
the
attack
still
works.
Although
domain
3
is
adopting
lov
okay.
So
now
we
have
to
check
you
know
how
when
does
it
happen
and
so
on?
N
We
did
simulations
in
the
standard
technique,
which
is
very
problematic.
I
know,
I,
I,
agree,
don't
tell
me
it's
problematic,
it
is,
but
that's
the
technique
so
far
known
it's
important
to
find
a
better
technique.
Yes,
but
not!
This
is
not
our
topic,
so
we
pick
we
use
the
quedagh
internet,
topology,
mapping
of
the
inter
different
domains,
ESS
and
their
relationship,
and
so
on.
N
We
pick
at
random
and
victim
domaine
in
attacking
domain
in
the
victim
domain,
of
course,
is
assumed
to
publish
Aurora,
and
then
we
are
checking
which,
in
the
selecting
time
to
be
which
domains
by
the
percentage
of
that
we
are
testing
at
that
time,
our
doing
our
v
randomly
and
then
we
are
just
computing
which
domains
will
actually
send
to
the
victim
and
it
remains
we'll
send
to
the
attacker.
That
is
the
percentage
success
rate
for
tactic.
What
are
the
results?
N
Okay
results
are
essentially
that
if
you
have
almost
all
the
network,
it
should
be
here
the
winner.
If
owners
of
the
network
is
adopting-
and
here
just
a
100,
proper
ISPs
and
let's
see
which
of
them
are
adopting,
we
see
that
as
long
as
is
only
a
few
of
them
are
adopting,
then
that
leg
actually
succeeds,
even
if
all
the
rest
of
the
network
is
adopting
except
to
handle
tapas
tapas,
which
we
are
still
losing.
Essentially
always.
This
is
exactly
because
of
the
phenomenon
I
described
earlier.
N
Okay,
and
only
most
all
of
them
are
not
things.
Then
we
get.
You
know
to
the
subject:
twenty-something
percentages,
that's
the
basic
topic.
A
I
can
get
to
okay,
but
again,
if
a
lot
of
them,
if
the
1200
are
not
the
fact
that
all
the
rest,
all
the
rest
of
the
Internet
I,
don't
think
does
not
help
us
remember.
We
are
not
anywhere
close
to
this
now.
Let's
look
at
the
reverse
situation,
supposes
that
we
convince
all
the
hundred
topping
SS.
N
Oh
actually,
suppose
it's
the
rest
of
Internet
does
not
adopt
what
happens
if
or
didn't
happen,
I.
Don't
you
see
it
doesn't
matter
much?
Okay,
we
doesn't
matter
a
little
bit,
but
you
see
if
all
the
top
100
the
dog
but
the
others,
don't
then
we
are
also
doing.
Therefore
our
V
does
require
very
significant
adoption.
In
order
to
be
meaningfully
does
not
mean
that
it's
not
going
to
help
us,
but
we
do
need
significant
adoption.
N
Okay,
so
we
must
work
on
adoption
if
we
want
to
get
anywhere
adoption
here
in,
as
in
many
other
internet
standards
indefinitely.
Many
security
standard
is
a
huge
problem
and
we
should
really
work
very
strongly
to
do
it.
So
these
are
our
suggestions.
We
can
try
to
improve
deployment.
First
is
is
raw
layer.
So
actually
I
will
talk
about
this
quickly.
N
Mechanisms
is
a
wallet
which
is
the
mechanism
to
identify
incorrect
or
us,
and
if
you
didn't,
try
it
yet
I
recommend
you
do
you
can
enter
it.
You
can
try
your
own
network,
you
can
try
whatever
network
you
like,
but
domain
name
or
by
IP
address,
and
you
can
see
who
are
protected
or
not
protected
who
are
issuing
was
in
which
of
them
are
correct,
which
are
incorrect.
Of
course.
N
Okay,
and
then
we
are
developing
the
smart
validator,
which
I'll
talk
about
them,
maybe
a
demo
and
if
we'd
not
have
time
for
the
actually
not
really
demo
but
video
for
the
sake
of
time.
But
if
we're
not
have
time,
even
for
that
or
if
you
just
want
to
see
more
details
come
to
us,
we
can
show
you
the
the
real-life
demo
you
can
play
with
it.
It's
very
nice
and,
of
course,
talk
with
us
if
you
are
interested
in
experimentation
and
deployment.
N
Okay,
so,
first
of
all,
the
toilet
is
a
simple
website
and
web
service,
which
is
identifying
these
incorrect
wrong
wars.
And
then,
when
we
are
going
on
to
fight
them,
we
actually
try
actively.
We
have
to
be
in
fact
or
practically,
but
anyway
we
send
emails
to
all
the
operators
that
we
can
identify.
Currently,
we
are
not
doing
the
best
job
of
identifying
your
operators.
We
should
improve
on
that
actually,
but
of
the
ones
that
we
did
locate
and
were
able
to
contact
them
about.
N
40
percent
actually
fix
the
error,
so
we
actually
conclude
from
the
like
a
very
simple
thing:
if
it
was
me
serious
organization
like
wipe
etc,
will
take
this
very
simple
walk
of
wallet
and
will
actually
do
it.
Officially,
then
probably
will
get
even
higher
percentage
rate
and
will
improve
significantly
reduced
error
rates.
It
is
a
very
simple
thing
to
do
so.
That's
one
thing,
and
this
should
help
a
lot
also
to
add
the
our
V
deployment,
because
it
seems
that
they
indeed
this
risk
of
blocking
a
file.
N
Drawer
is
probably
one
of
the
biggest
reasons
for
people
not
to
deploy
our
V
okay.
But
then
we
are
coming
okay,
supposing
or
even
that
we
do
it
and
we
still
get
percentage,
maybe
will
be
a
bit
lower
but
will
still
be
significant.
How
can
we
fix
this?
They
are
of
a
perspective
from
the
validation
perspective,
and
then
we
are
developing
the
smart
of
the
learning
validator
and
we
are
planning
now
experimentation
with
Cisco,
with
LinkedIn
with
few
others,
and,
of
course,
whoever
of
you
is
interested
and
love
to
talk
with
your.
N
We
will
love
to
talk
with
you
about
doing
more
of
this.
Ok.
So
what
is
this
smart
validator
doing?
It
has
3
modes.
Essentially,
the
first
one
is
the
manual
and
learning
modes
which
together
doing
it's
a
manual
mode,
allowing
the
operator
to
define
exceptions
to
the
regular
our
voice.
These
are
we
ignore
these
are
we
apply
and
so
on
and
learning
at
the
same
time?
What
is
it?
N
What
is
it
learning
it's
trying
to
identify
this
incorrect
words
and
when
the
operator
also
wishes
it
can
move
to
one
of
the
two
conservative
modes
and
the
conservative
most
of
the
ignore
mode.
The
ignore
modes
mean
means
that
the
validator
simply
completely
ignores
all
these
incorrect
ones.
So,
for
example,
when
I
say
incorrect,
I
mean
stuff
like
France
télécom.
Well,
they
may
argue
so
there
were
is
correct,
because
this
is
the
prefix
or
ever
notice
that
if
we
adopt
it,
then
the
customers
will
show
been
announcing
for
years.
N
The
perfect-sized
will
be
coming
in
filing.
So
that's
what
we
define
as
an
incorrect
run.
We
can
argue
about
that.
I
agree,
but
from
the
point
of
view
of
deploying
the
system,
it
is
not
desirable.
Okay,
maybe
we,
let's
not
call
it
incorrect
if
you
don't
like
it,
but
it's
problematic
for
deployment
okay
and
therefore
we
will
just
so
the
first
mode
simply
completely
ignores
them.
N
The
second
mode
of
the
assessment
conservative
mode
is
an
auto
extent
mode,
which
means
it
is
adding
as
if
we
had
our
ways
for
these
long
lived
long
pop
announced
announcements,
which
are
we
in
this
world.
That
is,
we
kind
of
automatically
fix
in
a
sense
or
if
you
like,
the
let's
say,
France
Telecom
example.
So
we
are
issuing
the
raw
the
de
Nonna
should
have
issued
so
said
they
will
not
be.
N
Okay-
and
there
are
two
other
ideas
that
we
didn't
actually
yet
implement.
You
are
still
it
mo.
Is
the
alpha
plus
plus,
is
a
mechanism
to
reduce
the
collateral
damage
it
gives
incentive
to
deployment,
but
that's
a
long
story
and
still
in
research
level
and
the
person
validation
is
a
mechanism
to
give
more
benefit
to
rpki
by
handling
additional
attacks.
Essentially,
some
of
the
attacks
that
are
currently
only
handled
by
BGP
SiC
completely
and
a
lot
of
them
will
actually
be
is
prevented
by
employing
that
and
it
was
in.
This
were
a
paper.
N
This
was
in
the
seek
home,
a
conference
become
of
last
year
presented
and
we
will
probably
incorporate
it
with
Indus,
not
validate
Oh
soon.
Okay
and
I
love
to
give
details
of
that.
But
of
course,
I
don't
have
time
for
that.
So,
just
to
explain
a
bit
this
logic
of
actually
permitting
BGP
announcement,
even
if
they
are
contradicting
with
a
warrant,
but
they
have
been
published,
for
you
know
a
few
weeks
and
so
on.
N
If
we
look
at
the
it's
a
passive
hijacking,
as
reported
by
BGP
stream,
you
see
that
most
almost
all
of
them
have
been
within
two
weeks
or
less.
So,
if
you
go
further
than
that,
you
only
get
a
very
small
percentage
of
the
attacks.
Why
is
that
that's
a
good
question,
but
I
think
there
I'm
sure
that
each
of
you
can
understand
some
of
the
very
good
reasons
for
that.
But
the
bottom
line
is
very
simple.
Reality
is
that
most
of
the
hijacking
across
for
very
short
periods.
N
Therefore,
by
adopting
this
very
simple
rule
for
at
least
for
the
initial
deployment
of
the
system,
we
will
actually
not
know
so
much
in
its
effectiveness.
We
will
lose
a
bit
we'll
have
more
false
negatives.
Yes,
some
attacks
will
escape
the
system,
but
not
much,
really,
very,
very
okay.
So
that's
the
logic
of
the
system.
This
is
the
architecture
of
the
system
well
and
not
go
over
it.
It's
pretty
straightforward,
it's
going
back.
N
They
are
contradicting
the
rewards
of
course,
and
here
you
see
they
are
essentially
a
disappeared
because
of
we
apply
this
conservative
mechanism.
Okay,
and
now
we
have
time
or
not
one
minute,
you
want
to
do
a
demo
in
one
minute,
okay,
so
yes,
so
your
film
will
try
to
do
the
demo
in
one
minute,
we'll
see
how
that
will
go.
How
do
I?
Do
it
actually
I
think
you
click
on
the
link.
P
N
P
N
Q
N
L
What
any
number
song
suppose
is
very
interesting
presentation.
First
I
just
wanted
to
come
back
and
win
the
beginning
of
the
presentation.
You
say
there
is
10%
persistence,
the
wrong
way
race
and
you
give
France
télécom
as
an
example.
I
just
wanted
to
focus
on
that
point.
People
most
of
the
time
believe
that
I
Jax
I'll
trust
you
no
bad
guys
stealing's
Internet's.
Actually
it
can
also
happen.
I,
don't
say
this
is
the
very
case
here,
but
it
can
happen
that
some
not
dedicate
customers
just
to
live
with
their
IP
block.
L
So,
for
instance,
in
this
very
case
it
could
be.
You
know,
Dannon
yogurt
manufacturer
living
with
IP
blocks,
which
was
first
allocated
by
France
Telecom
to
some
other
ISP,
and
then
it
becomes
very
complicated
for
an
HP
to
get
the
block
back
because,
for
instance,
the
customer
can
be
also
customer
for
some
other
services.
L
N
L
N
L
N
Right
yeah,
what
you're
saying
is
in
the
completed
is
in
the
current
situation.
We
don't
have
our
PK
eyes
and
customers
could
kind
of
walk
away
with
the
prefix
and
nobody
noticing
so,
and
we
have
a
Miss
in
this-
does
happen
current
in
the
internet,
yeah,
but
I
think
this
is
a
bit
of
saga
not
to
the
whole
issues
that
I'm
discussing
I
completely
agree
that
current
situation,
without
you
know,
proper
mechanisms
like
applique
allow
this
mess
to
happen,
and
we
are
now
trying
to
clean
up
the
yeah.
L
N
R
S
R
Email
address
and
they
will
be
notified
about
anything
infinite
amounts.
That's
helped
improve
the
data
quality.
Also
my
colleague,
Alex
bond
have
been
has
been
contacting
people
quite
well,
assertively,
say
in
the
beginning,
and
definitely
he
did
get
the
answer
back
at
times
that
most
specific
announcements
were
actually
unwanted,
so
that
does
exist.
I'm
was
my
last
point.
I
had
one
more
point,
but
it
slipped
my
mind.
Well,.
O
T
George
Telecom,
the
point
I
would
like
to
make
is
for
successful
deployment.
We
need
well
okay,
there
is
actually
a
large
space
where
additional
tools
and
monitoring
services
are
required
and
well
the
question
whether
we
have
the
full
tooling
available
at
by
definition
or
by
implementation
or
deployment.
I
would
like
to
come
back
to
the
example
from
our
French
colleague
Anthony.
T
My
dumb
question
would
be
well
assuming,
assuming
that
one
of
your
customers
with
delegated
address
space.
Actually
you
would
agree
that,
yes,
that
delegation
should
work.
Do
you
have
the
tooling
available
in
your
current
rpki
deployment?
That
would
allow
that
customer
to
get
the
delegation
and
then
maintain
the
Aurora,
or
do
you
have
the
mechanism
and
the
processes
in
place
that
allows
your
support
to
continually
update
what
the
customer
needs
kind
of
the
current
the
current
the
current
model
of
using
rpki
is
essentially
a
single
level
hosted
service.
T
U
V
Want
to
make
a
very
quick
comment
that
if
the
customer
gets
let's
say
is
a
customer
would
have
not
created
the
raw,
the
ISP
would
have
forwarded
the
traffic.
So
if
the
customer
now
announces
the
law,
then
the
raw
gets
maybe
or
throughout
gets
not
elected,
but
the
traffic
still
goes
to
the
to
the
ISP
and
the
ISPs
still
would
forward
to
traffic
to
the
customer.
So
I
don't
think
that
you
wouldn't
be
able
to
order
your
cheese.
You
still
would
do
it
there's
trust
the
problem
is,
there
was
no.
W
B
X
B
S
Hi
everyone
so
I
represent.
How
looks
you
can
be
used
to
secure
the
location
of
IP
other
system.
It's
perfect
C's
first
I
will
make
a
short
introduction
to
the
blockchain
and
then
I
will
explain
the
using
this
context.
We
would
like
to
remark
that
this
is
not
a
substitute
to
the
RPG
I.
It
just
preliminary
analysis
of
how
it
might
look
like
using
the
blockchain.
So
we
are
just
seeking
feedback
from
the
group
so
first
of
all
a
short
box
in
the
glory
all
for
those
who
are
not
familiar
with
it.
S
In
short,
the
blockchain
is
a
decentralized,
secure
and
reduce
database.
It
can
also
be
seen
as
a
token
tracking
system
to
know
who
has
what
it
is
built,
adding
blocks
of
data
one
after
another,
and
it
is
protected
by
two
mechanisms:
team
signatures
which
ensures
the
ownership
of
the
tokens
and
the
condition
algorithm,
which
ensure
that
data
integrity,
the
first
one
optional
built,
was
Bitcoin,
which
is
used
to
change
money,
and
this
exchange
is
between
two
parties
and
it
doesn't
require
an
intermediary,
but
other
applications
are
possible.
Thanks
to
its
properties.
S
This
figure
shows
the
blockchain
workflow.
The
basic
unit
of
blockchain
all
transactions,
they
have
three
elements:
data,
signature
and
the
public
key
associated
with
the
signature
transactions
are
broadcasted
to
a
pitbull
Network
and
at
some
fixed
intervals
in
time.
One
of
the
nodes
in
the
network
collects
all
transactions
into
a
block.
It
then
calculates
the
conventional
rhythm
which
enforcing
the
sort
of
rules
a
great
among
wall
note,
and
then
he
podcast,
this
blog
back
to
the
network
upon
the
rest
of
the
notes
receive,
is
no
work.
S
They
verify
the
control,
algorithm
and
the
signatures,
and
if
they
are
correct,
they
are
it
to
the
blockchain
since
blocks
of
data
and
at
12:30
model,
and
it
is
called
a
blockchain.
So
this
design
provides
seven
testing
properties
among
them.
We
remap
the
following:
it
is
a
centralized
because
all
nodes
have
entire
chain
which
makes
it
resilient.
S
The
data
with
its
public
key
I
should
also
be
noted
that
the
content
oven
does
not
allow
sang
in
several
times
the
same
public
key,
because
you
would
be
giving
the
same
token
to
several
entities,
and
this
is
not
possible.
It
is
usually
known
in
Bitcoin
as
double
spending,
so
also
a
few
words
about
the
content
algorithm.
The
content
is
no
algorithm
is
the
central
part
of
any
blockchain,
because
it
controls
addition
of
blocks,
so
it
basically
finds
what
these
consensus
and
provides
the
notes,
a
set
of
rules
which
help
them
reach
the
same.
Reach.
S
So
working
on
a
slight
pro
work
is
relative,
professional
power
and
to
add
the
block
notes
have
to
perform
a
large
amount
of
calculations,
for
example
in
become
the
cache
of
the
block
has
to
start
with
a
fixed
amount
of
zeros.
This
is
quite
hard
because
the
only
long
way
to
do
this
is
by
brute
force.
It
also
means
that
if
someone
wants
to
change,
they
take
us
to
redo
the
probe
work.
S
So
this
setup
makes
that
if
we
want
to
notify
the
loop
chain
may
be
changing,
the
last
block
would
be
quite
easy,
but
the
mark
watch
we
go
will
go
back
the
harder
he
gets.
Another
site.
Pristiq
takes
a
different
approach.
Improvers
take
all
participants
cannot
a
block,
but
we
take
into
account
the
number
of
tokens
I
have.
S
S
S
S
Regarding
the
Pantages,
it
is
a
centralized,
so
there
is
no
hierarchy,
no
certification,
Authority,
sorry
I
need
it,
which
makes
management
more
simple
and
also
Hakeem
is
very
simple.
It
only
requires
a
limited
amount
of
player
tourists
and
it's
unreadable
because
we
can
always
go
back
in
the
history
book
chain
to
serious
transactions.
It
also
censorship
resistant,
because
a
data
cannot
be
modified.
Of
course
it
has,
but
also
the
most
important
one
being
that
it
doesn't
provide
tips
or
Africa
and
dislike
PGI
greater.
It
remain.
S
S
We
want
to
store
the
a
block
of
IP
addresses
in
its
holder,
the
scene
of
allocations
and
allegations
of
IP
addresses
and
the
meaning
of
these
virtual
fallacies
to
alias
numbers.
So
we
say
well,
we
can
see
IP
addresses
as
points
they
share
similar
properties.
They
are
unique,
so
two
parties
cannot
hold
the
same
block
of
addresses
these
blocks.
A
father
has
come
either
straight
or
party,
and
they
are
divisible
because
I
can
split
block
of
others.
S
S
So
if
you
want
to
do
tablet
chain,
the
first
question
that
comes
into
mind
is
which
contains
algorithm.
Should
we
use
the
typical
choice
is
prove
work,
it's
the
most,
the
one
that
most
merchants
used,
but
in
our
scenario,
sent
some
drawbacks,
the
first
of
all
being
that
the
the
party
that
had
plots
do
not
necessarily
use
the
blockchain.
So
that
means
that
in
some
cases
they
would
not
be
interested
in
its
correct
operation.
S
In
addition,
if
a
particle
holding
of
computing
power
it
could,
then
it
could
rewrite
that
blockchain
or
select
which
data
gets
added.
It
also,
in
some
cases,
it's
necessary
to
buy
a
special
hardware
to
perform
this
computation
and
in
these
compilations
also
very
inefficient,
because
you
have
to
do
a
lot
of
them.
S
On
the
other
hand,
approvers
take
appears
to
be
more
suitable
for
this
a
scenario
it
doesn't
require
special
highway
or
expensive
computations.
But
the
key
point
is
that
the
parties
that
control
the
blockchain
are
and
the
ones
that
have
no
computation
power,
but
rather
the
ones
with
known
IP
addresses
so,
in
other
words
the
people
who
use
the
blockchain
maintain
it.
S
So
because
of
this,
we
think
that
blood
chaney
a
prove
a
stake-
is
a
good
candidate
for
a
problem.
In
this
context,
so
I
will
end
up
with
a
small
example
of
how
this
might
work.
So,
first
of
all,
Ayane
would
allocate
all
the
perfect
sis
to
itself
and
then
it
would
start
allocating
perfect
sis,
to
example.
The
rears
here
we're
giving
one
as
logic
to
APNIC
and
in
the
reroute
allocate
them
twice
for
something
here.
We
give
one
dot
2/16
and
finally,
is
peace,
IRAs
box
to
the
alias
numbers.
S
This
way
anyone
can
download
the
bit
chain
and,
for
example,
check
which
a
his
numbers
link
it
to
a
fabric
analysis
and,
of
course,
we
can
always
go
back
through
the
entire
chain
to
see
if
these
perfect
was
only
by
Ana
and
just
to
finish,
our
use
case
is
wisp
in.
For
those
who
don't
know
it,
Elise
has
a
thing
called
mappings.
Are
there
bindings
of
IP
addresses
to
IP
addresses
any
kind
of
system
called
delegated
database
3,
which
is
et,
which
is
composed
of
several
nodes
that
the
table
you'll
find?
S
Z
AA
So
George
Michelson
AP
neg,
you
may
need
to
give
a
more
explicit
statement
of
what
happens
if
somebody
loses
their
private
key,
because
in
most
of
the
current
implementations
of
block
chains
losing
the
key
functionally
destroys
the
value
inherent
in
that
component
of
the
chain.
It
is
impossible
to
recover
without
some
process
which
functionally
reasserts
the
hierarchy.
You
said
on
the
slide
rekeying,
but
that
generally
means
consciously
rekeying
by
signing
over.
AA
AA
S
AA
Behavior,
so
the
second
thing
is
that
one
of
your
slides
talked
about
the
concept
of
public
verification,
and
there
is
a
concept
in
the
general
sense,
which
is
public
ledger.
The
sense
that
what
we
do
is
perform
transactional
change
in
a
way
that
other
people
can
observe
the
nature
of
your
transactions
and
that
can
include
cryptographic
proofs
that
concept
public
ledger.
That's
actually
a
really
interesting
concept,
but
the
important
observation
I
feel
I
want
to
make
is.
AA
It
is
not
inherently
tied
to
the
blockchain,
it
is
a
thing,
a
concept
in
itself,
and
so,
if
some
of
us
are
critiquing
blockchains
in
no
sense
are
we
necessarily
rejecting
transactional
logs
public
ledger
and
or
did
they
are
high
value?
The
problem
is
both
proof
of
work
and
proof
of
stake
as
models
of
the
computational
effort
or
the
evidence
of
participation
have
issues
when
you
apply
them
in
the
financial
domain
and
the
use
of
blockchain.
AA
The
etherium
model
includes
the
concept
of
a
contract,
a
digitally
encoded
transaction,
which
is
determined
in
time
and
sequence
because
of
the
encoding
of
that
contract,
nature
in
what
you
are
doing
and
that
that
has
some
interest
because
it
goes
to
aspects
of
the
public
ledger
behavior,
but
aetherium
itself
has
had
some
severe
information
crises.
They
have
had
people
use
faults
in
that
contract
to
achieve
distortions
of
the
value
inherent
in
aetherium,
and
it's
quite
a
difficult
problem
to
specify
what
a
valid
aetherium
contract
should
be.
S
AB
AC
The
draft
I
would
like
to
give
a
complementary
answer
to
job,
so
the
first
thing
is
that
we
are
not
claiming
that
this
is
better
than
LP
guy.
This
is
what
Georgie
said
at
the
very
beginning
of
the
presentation
we
plan
to
do
this
for
list
and
we
were
seeking
feedback
from
you,
the
experts,
because
you
know
very
well
how
to
protect
IP
delegations,
one
of
the
main
advantages
of
public
ledger
technologies.
AC
If
you
don't
want
to
use
the
word
blockchain
is
that
you
don't
need
you
don't
have
CAS
and
you
don't
have
all
these
management
issues.
If
you
consider
the
advantage,
that's
an
advantage,
then,
regarding
the
Rakim,
it's
true,
if
you
lose
your
private
key,
you
don't
have
any
capacity
to
change
your
allocation
sort
of
anything
with
your
other
six.
Now
the
advantage
is
that
it's
only
you
that
you
can
lose
your
private
key,
you
don't
depend
on
any
CA.
AC
You
are
only
responsible
from
your
parrot
key,
no
one
and
no
one
else
can
screw
it
up,
which
I
think
it's
it's
a
good
advantage
right
and
then
you
can
Rikki
whenever
you
want,
and
lastly,
I
think
that
the
presentation
could
have
I
think
that
the
semantics
we
could
call
it
a
public
ledger
and
it's
precisely
the
same
as
we
are
explaining.
Oh.
K
AD
So
the
question
I
had
whether
there
is
any
plan
that
you
intend
to
have
to
also
address
that
validation
advertisement
go
from
hop,
hop
hop
no
soon
as
the
prefixes
are
getting
transformed
from
one
folder
to
another
holder,
but
the
same
whole
advertisement
prefixes
like
how
it
works
in
the
internet
validating
that
path
would
be
very
useful,
so
that
could
be
one
second,
it
propels
useful
to
see
how
much
time
and
resources
does
each
proof
work.
Work
takes
sorry.
AD
If
you
look
at
the
current
set
of
algorithms,
despite
all
the
optimizations,
that
gone
have
gone
into
from
Bitcoin
into
the
blockchain,
whether
you
look
at
it
through
unknown
at
the
time
it
takes
to
construct
number
of
transactions,
invalidate
them,
and
that's
in
seconds
so
applying
this
technology
to
Rory
is
so
peaceful.
That
would
be
good
to
characterize.
How
long
does
it
take
for
every
transaction
that
going
another
transaction
going
abroad?
How
long
does
it
take
so
those
are
my
two
quick.
S
AD
G
Eyes,
Cisco
just
a
couple
comments
you
have
to
reply
to
them
the
with
thanks
for
your
clear
presentation
with
with
proof
mistake.
You
mentioned
that
your
attacker
is
basically
somebody
who
can
acquire
or
accumulate
a
large
number
of
IP
blocks.
I
would
just
point
out
that
in
in
the
structure,
there
are
some
of
those
attackers.
Of
course
it's
the
registries
at
the
top.
We
don't
think
of
them
as
attackers,
but
they
in
fact
have
the
ability
of
being
attackers
and
even.
G
What
people
were
talking
about
with
the
protection
of
the
private
key,
getting
their
private
key
instantly
becomes
an
attack
or
even
if
they
weren't
an
attacker.
So
that
would
be
important
to
think
through.
Also
I
would
point
out
that
that
means
that
the
the
control
of
the
plot
of
the
entire
address
allocation
and
its
course
still
in
the
control
of
the
same
people
that
it
is
with
with
rpki
today.
R
R
This
is
mechanism
used
in
the
RPI
by
relying
parties
to
find
the
most
recent
a
the
most
recent
root
certificates
that
they
have
configured
and
the
way
it
works
is
you
have
some
your
eyes
listed
there
where
you
might
find
a
certificate
and
you
have
a
fingerprint.
So
if
you
get
this
ativy,
you
can
compare
that
matches
that
so
next
slide,
please.
R
We've
talked
about
this
in
the
Delta
protocol
document,
with
TLS
certificate
validation.
You
could
find
that
yeah
there's
so
many
CAS
out
there.
You
could
think
something
is
a
valid
certificate,
although
maybe
it
shouldn't
be,
you
could
also
find
that
people
have
made
configuration
errors
or
stuff
with
ciphers
and
what-have-you
that
can
be
misconfigured
and
well.
Essentially,
the
tower
already
contains
a
subject:
public
key
info
field.
So
essentially,
even
if
you
got
the
file
from
a
possibly
untrusted
source,
you
can
still
verify
that
it
matches.
R
So
we
probably
need
some
text
here
that
would
allow
you
to
maybe
warn
but
ignore
most
these
problems
next
slide,
please
so
to
wrap
it
up.
My
I
believe
this
is
the
last
line.
At
least
my
preference
would
be
to
move
forward
quietly
here,
actually
because
I
think
it's
trivial
for
CAS
to
to
publish
certificates
on
on
their
own
HTTP
URI,
rather
than
our
sink
and
I.
Think
it's
easier
to
scale
it
that
way
anyway.
Also
I
do
believe
that,
for
relying
parties,
if
you
supports
getting,
is
yes
as
an
optional
addition,
it's
it's
also.
R
You
know
it's
actually
easier
if
we
can
remove
the
need
for
our
sink,
because
it's
gets
us
one
step
closer
to
not
being
dependent
on
external
tool,
so
them
discussion
I.
Don't
think
we
need
to
have
that
all
here
right
now,
but
you
could
have
strategies
what,
if
you
have
multiple
you
arise
there
and
some
of
them
have
warnings.
Others,
don't
probably
something
to
talk
about
excellent
things.
R
So
first
question
would
be
and
I
guess
I
need
to
go
to
the
list,
but
is
the
working
group
interested
in
taking
this
as
a
on
as
an
item
and
discuss
further,
then
there
are
currently
six
mentions
for
our
sink
and
there's
HTTPS
validation
considerations.
So
I
think
probably
a
obsoleting
77304
than
doing
a
in
place
update
is
easier
or
may
well
make
the
thing
more
readable
and
then,
if
you
know
we're
all
good
with
all
this,
then
are
the
current
authors
of
7730
interested
in
following
up
or
a
needed.
AF
R
So
initially
you,
the
RDP,
your
I
is
included
in
the
certificate,
but
you
first
need
to
get
it.
So
when
you
first
boot
strap
you
don't
have
it.
You
would
have
to
do
an
arcing
fetch.
First,
then,
potentially,
you
could
find
it
a
root
certificate.
That
says,
has
a
notification
XML
in
there.
That
includes
the
certificate
itself
that
you
may
want
using
future
somehow,
but,
let's
think
of
it
poorly
defined.
R
AG
Trust
semantics
right:
well,
Boston,
DRL,
I,
agree
with
Tim
I.
Don't
think
that
RDP
replaces
the
need
for
this
I
think
Tim
is
on
essentially
the
right
track.
You
know
we
can
talk
about
details,
but
I,
don't
think
RDP
replaces
the
need
for
something
for
the
towel.
Fetch
Tim
I
know
is
aware,
as
one
of
the
co-authors
of
RDP,
but
I
want
to
be
careful
about
how
we
handle
TLS
valid.
You
know,
HTTP
validation,
failures,
I
think
we
essentially
want
to
handle
it
the
same
way
as
we
did
in
our
RDP.
AG
It's
good
to
try
to
do
the
HTTPS
validation,
but
I'm
not
sure
that
an
RPG
I
shouldn't
come
to
a
screeching
halt.
Somebody
screws
up
their
HTTP
server,
TLS
validation.
So
it's
essentially
the
same
kind
of
thing
about
you
know
failing
over
tea
and
secure,
because
the
data
themselves
are
secured
me
another
path.
Z
Job
Snider's,
NTT
I
do
think
it's
useful
to
standardize
on
a
transport
mechanism
within
the
whole
tool
chain
and
HTTP
might
as
well
be
the
one
standard.
If
you're
gonna
work
a
little
bit
on
the
tail
locator
file
format
field,
perhaps
consider
changing
it
to
Jason
and
perhaps
adding
a
version
number
so
that
the
next
time
we
add
anonymous
SCP
it
will
be
easier
than
forklifting
these
documents.
That's
just
a
very
small
suggestion.
Z
AH
R
So
I
think
there
are
two
benefits
here.
Even
if
you
make
it
like
an
optional
choice
or
you
know
still
allow
our
saying,
but
you
don't
have
to
use
it
as
a
CA
I
find
it
easier
to
do
skill
because
I
can
use
a
CDN.
I
can
offload
this
as
existing
technology
to
make
my
certificate
available
for
a
relying
party.
If
the
CA
also
chooses
to
use
the
Delta
protocol,
then
I
would
like
party
to
would
prefer
that.
R
So
if
we
have
HTTP
on
the
tail-
and
we
have
the
Delta
protocol
as
again
still
an
optional
additional
thing,
but
you
know
if
it's
used
then,
for
that
particular
part
of
the
RP
I
mean
it
could
change
with
dedicated
children
all
that
they
might
use
different
publication
points,
but
essentially
the
relying
party
tool
would
not
need
to
call
arcing
gets
all
them
and
I
think
that
has
performance
benefits.
It
makes
error,
reporting
easier
and
many.
R
B
B
R
It
is
okay,
miss
the
title,
so
the
next
thing
I
wanted
to
talk
about
was
basically
what
kind
of
related
to
the
the
previous
one.
So
if
we
change
the
your
eyes
on
on
a
on
a
single
locator
or
you
know
what
happens
if
I
want
to
rekey,
there
is
an
existing
deployment
of
relying
parties
out
there.
We
have
therefore
single
locators
installed
locally
and
I
can't
easily
inform
them
about
my
desire
to
either
publish
my
certificates
in
a
different
location,
for
example,
using
it
yes
or
him.
R
R
R
Y
R
Don't
really
know
how
to
solve
it
either.
It
would
be
great
if
you
could
solve
it,
I
suppose,
but
then
again,
I
wouldn't
want
to
stop
solving
other
issues
that
I
do
have
today
by
talking
about
that
solution.
So
moving
on
in
concept,
it's
really
simple.
What
I
would
propose
is
that
relying
parties
using
a
drawer
sink
a
locator.
They
can
find
a
trusted
certificate,
there's
a
whole
lot
of
things
that
are
published
by
this
certificate.
R
Essentially,
the
document
just
says
well
left
the
cross
anchor
published
a
new
towel
as
a
science
object
as
an
RTI
signed
object
of
the
new
type
and
when
the
relying
party
finds
that
basically
instructed
to
replace
the
trossingen
locator
that
had
with
this
new
one.
That's
essentially
all
there
is
to
the
idea,
but
then
worked
out
for
two
different
use
cases.
Yes,
next
slide,
please
so
for
a
key
role.
Now
here
it's
quite
aggressive,
actually
the
timeline,
but
that's
a
point
for
discussion
as
I
mentioned
earlier.
R
First
of
all,
you
would
have
to
prepare
your
new
key
settled
up
in
such
a
way
that
everything
is
there.
We
publish
everything.
You
were
publishing
only
your
old
key
and
then
we
can
publish
the
thrust
anchor
locator
on
the
old
key.
So
this
can
instruct
the
relying
parties
to
go
to
the
new
location
and
key.
Then
a
staging
period
seems
reasonable.
How
long
should
be
I
don't
know?
24
hours
is
kind
of
based
on
the
yeah.
R
AG
The
RFC
5
0
and
n
s
for
key
roles
at
the
root
I
think
there's
a
prior
right
there
we
might
be
able
to
reuse
I'm
sure
there
are
many
many
ideas
for
how
to
make
it
even
more
complicated
than
50
11
but
I
think
at
the
very
minimum.
We
want
to
look
at
some
of
the
timelines
that
are
used
in
50
11,
some
of
which
are
much
longer
than
what
Tim
is
talking
about
here
and
some
of
which
involve
pre
publishing
keys.
In
order
to
allow
you
to
do
something.
AG
AG
AF
B
R
R
Go
for,
loss
call,
publish
it
Randi
already
expressed
support
for
that,
so
that's
great.
Otherwise
we
just
publish
it
with
our
code.
We
say
thank
you
ITF,
but
we're
going
for
a
more
lightweight
way
of
documenting
this
I
see
some
married
in
a
but
basically
I
think
we
needed
a
decision,
a
move
on
and
that's
all
I
had
to
say
on
that
one
actually
really.
AF
AG
Rob
Boston
DRL
yeah.
This
does
not
need
to
be
a
working
group
document
just
published.
This
is
what
our
peek
at
this
is.
What
right
did
it's
useful
as
it
is
get
it
out
the
door
speaking
as
an
implementer
who
actually
read
the
document
while
implements
some
of
this
stuff?
It
is
extremely
useful,
but
it
doesn't
need
the
working
group
to
fiddle
with
it.
It's
just
it's
done.
R
B
The
the
suggestion
which
we
should
have
discussion
on
the
list,
but
is
just
push
to
work
for
last,
call
and
push
word
I.
Think
if
you
have
links
to
your
code
and
whatnot
in
the
document,
then
that
whole
Rock
process
continue
as
you
need
to
there.
So
all
right.
Thank
you.
Yeah
I'll
send
a
note
to
the
list
for
you
for
that.
One:
okay
and
sorry,
not
you
Randy's!
Next,
with
his
no
slides
tour,
ten
minutes
or
less.
AF
I
would
like
to
point
out
and
maiya
culpa:
RFC
60,
whatever
68:11
I,
think
clearly
was
not
clear
enough.
There
are
two
significant
problems.
One
is
when
I
make
an
announcement
to
Ruettiger,
no
matter
how
I
learned
that
route,
if
rüdiger
stock
has
to
call
me
and
tell
me
that
announced
an
invalid
prefix.
This
is
not
good.
AF
Ok.
The
second
problem
is
that
we
seem
to
be
well
know
via
draft.
The
RFC
says
the
operator
is
in
control
through
configuration
of
what
is
done
with
a
mark
1
with
a
route
once
it
is
marked,
not
found
valid
or
invalid
I
get
to
decide.
I
know
the
helpful
fatherly
vendors
excuse
the
sexism
or
think
they
know
what
should
happen.
You
don't.
AF
We
have
current
implementations
that
not
just
mark
the
route
but
drop
invalids
by
default.
Create
communities
by
default,
etc.
Stop
just
stop.
I
have
Steve
pehlivan,
a
security
researcher
as
a
customer.
He
only
wants
me
to
give
him
invalid
routes.
Just
stop
doing.
Gratuity
vaction
I
have
the
ability
to
do
it
all
in
policy.
AF
AF
T
Hi
Randy
Julio,
Deutsche,
Telekom
still
and
yeah
all
okay,
I
I
certainly
agree.
I
note
that,
of
course,
we
have
to
expect
that
not
everybody
is
using
this,
and
so,
of
course,
I
have
to
deal
with
the
situation
that
some
of
my
customers
may
not
do.
The
rpki
classification
and
I
still
need
to
tell
them
that
they
are
sending
me
junk
or
some
of
my
valued
peers
do
the
same.
T
AF
T
AF
If
they
don't
well
I'm
telling
them
not
to
do
I
should
have
some
way
to
signal
that
no
just
don't
do
it,
but
I
take
your
point.
If
I
by
policy
decide
to
drop
your
route,
maybe
it
would
be
nice
if
I
could
tell
you
and
now
we're
back
to
these
sophisticated
to
be
kind
signaling
mechanisms
which
are
not
my
fort
but
I
think
we
have
some
expertise
sitting
right.
There,
hi
job,
okay,
yeah.
U
Kate
patel
arcus.
I
just
wanted
to
add
that
I
think
the
last
time
I
looked
at
RFC
68
eleven.
It
doesn't
mention
the
rules
for
redistribute
redistributed
routes
to
say
how
you're
going
to
do
the
origin,
AAS
validation,
particularly
for
the
ones
that
you
originate
on
the
router.
So
if
you
can
offer
ask
working
group
to
do
this,
maybe
you
you
probably
want
to
issue
a
based
on
sixty
at
eleven
and
expand
those
okay.
AF
And
beat
me
up
about
this
out-of-band
he
is
correct,
but
let
me
rephrase
it
because
it
took
a
while
to
sink
it
to
my
head
and
it
may
take
a
minute
or
two
to
sink
into
yours.
If
it
comes
from,
if
I
am
originating
this
route
and
it's
coming
from
my
IGP
estatic,
it's
a
connected,
etc.
Then,
if
the
router
is
to
validate
it,
it's
got
the
prefix.
But
what's
the
AAS
number,
my
router
might
have
multiple
AAS
numbers.
AF
J
Z
Job
Snider's
entity
would
it
be
perhaps
useful
to
recontextualize
your
draft
as
an
update
to
four
to
seven.
One
two
very
clearly
indicate
at
which
step
of
the
conceptual
process,
the
validation
and
marking
takes
place,
because
if
the,
if
the
issue
is
that
implementers
get
it
wrong,
then
maybe
this
could
be
a
different
way
of
pointing
out
that
this
is
where
things
happen.
AH
Good
afternoon
everybody
I'm
Deema
from
Z
des
hommes
I'm,
aware
I
was
the
administrator
of
a
sort
of
a
Caroline
party.
Software
called
a
beast.
I
will
be
briefing
this
draft
and
responding
to
some
comments
from
many
lists
since
the
inception
of
this
walk
by
the
way
this
work
or
the
first
introduced
in
site
a
meeting
in
Banaras,
and
we
also
believe
we
also
like
to
move
it
on
inside
offs
working
group,
and
we
believe
this
work
is
in
alignment
with
the
charter
of
the
side
oops
in
terms
of
Caroline
party
thanks.
Why?
AH
Moving
around?
To
the
background,
the
fact
is,
requirements
in
Poland
are:
peas
are
scattered
throughout
many
IFC's,
so
this
makes
it
harder
for
a
implementer
to
be
confident
that
he
or
she
has
addressed
all
all
of
these,
that
your
eyes
requirements.
Subjects
like
the
faculties
know
that
software
engineering
calls
for
how
to
segment
zrp
system
into
components
in.
In
addition
that
you
should
be
aware
all
of
what
are
the
requirements
are
so
I'm
such
this
to
be
distributed
across
the
upper
head,
operational
timeline
of
user
and
granted.
AH
We
also
believe
the
taxonomy
of
a
generalized
RP
requirements
is
going
to
help.
That's
right.
Okay,
here
comes
the
overview.
Above
all,
the
most
important
thing
is
to
answer
the
reader
to
the
right
place.
We
are
RP.
Requirements
are
low
materially
to
find
bind
twinsies
by
doing
so.
It
aside
the
requirements
that
appear
in
several
documents.
AH
AH
AH
Only
the
describe
hearing
this
document
would
be
stable,
a
lousy.
Our
BK
is
standardized
as
a
way
we
see
today.
So
that's
the
reason
why
we
we
don't
make
a
local
transient
management
as
a
requirement
because-
and
we
won't
because
our
local
transient
Commandant-
is
a
kind
of
extended
IP
function
and
willing
to
make
any
difference
in
terms
of
the
integrity
aware.
Our
PC
channel
looks
like
is
easy
to
figure
out
to
the
outlier
of
the
document.
We
take
a
glance
at
the
catalogue
of
this
document.
AH
As
far
the
RP
are
designed
the
best
the
basic
function,
lantee
of
it,
it
could
be
divided
into
four
categories:
the
first
fashion,
the
cashing
the
applicator
policy
objects,
second,
processing
certificate
and
CIO
excite
and
then
processing
RP
carry
policy
center
objects.
Well,
my
way,
I
believe
the
diviner.
Manifestly
the
radio
tricky
part
so
I
hope
some
well.
Maybe
we
could
to
sum
up
head
up
date
of
manufacture,
define,
okay,
the
last
part
alone,
Desdemona,
why
it's
delivering
value?
AH
Does
the
cash
data
into
the
peach
pieces
from
thanks
fine
I'm,
a
litel,
some
feedbacks
from
the
Middle
East
I'm
they're,
fulfilling
obliged
to
deliver
a
clear
message
here
that,
as
I
recall,
some
concern
from
should
happen
in
the
Middle
East?
Are
we
suggesting
that
implementer
should
skip
rate
raisers
I've
seen
for
know?
Anyone
who
wants
to
comprehend
can't
be
exempted.
AH
Looks
like
okay,
there
it
is
Russians
are
weather.
This
draft
is
a
read
out
in
the
to
the
existing
working
group
item
on
tree
validation
mean
our
defense
I
like
to
take
this
opportunity.
To
reiterate
our
point
of
view,
the
advocate
orientation
document
describes
how
you
know
the
ripe
ripe
conceived
an
interest
of
their
works.
While
this
document
is
more
Tareq
and
as
a
tree
foundation
document
is
expecially
a
description
of
one
particular
RP
implementation.
AH
Thus,
it
is
an
example
how
that
implementation
tries
to
meet
the
acne
requirements,
not
a
general
characterization
of
RP
primers,
so
I
hope
this
document
could
be
adopted
as
I
working
right,
X
right,
okay,
see
so
this
photo
is
taken
by
my
course.
You
can't
from
his
floor
either
fitted
sheet
last
year.
B
C
T
Well,
okay,
it
actually
it
actually
could
have
one
paragraph
that
says
an
implementation
should
come
with
a
documentation
and
Tim's
document
is
doing
that
for
is
implementation,
so
that's
very
easy,
and,
while
okay,
actually
putting
in
that
truth
into
this
document,
I
think
makes
a
little
bit
of
sense
just
to
make
clear
just
to
make
clear
that
this
you
is
important
and
we
have
a
thing
is
yes,
I
would
I
would
suggest
really
talking
about
relying
party
implementation,
because
I
am
a
relying
party
as
a
person
and
I
won't.
I
won't.
I
won't.
AH
V
I
try
to
be
quick,
so
at
IETF
97
we
gave
a
little
interoperability
demo
and
I
want
just
to
give
a
little
quick
update
about
the
reference
implementation
of
BGP
SEC
next
slide.
So
we
implemented
full
support
for
the
RFC
to
be
80
to
10.
What
is
the
68
and
this
9
I
think
at
this
point
we
allowed
to
receive
router
keys
directly
into
the
implementation.
We
also
updated.
The
BBC
capability
in
b2b
sig
has
attributes
to
these
ion
assigned
values.
V
This
gives
a
little
bit
of
a
problem
because
Bert
still
I
think
has
in
the
code
it's
the
old
values.
Therefore,
we
allow,
even
in
the
compilation
to
the
old
values
again
for
backwards.
Compatibility
next
slide,
then
for
everybody
who
there
was
a
discussion.
What
really
gone
I
had
many
many
years
ago,
but
I
think
four
or
five
IITs
back
the
problem.
V
This
the
time
when
the
validation
cache
sends
more
updates,
and
you
want
to
react
right
away
on
the
changes,
with
validation
of
your
updates
depending
how
there
was
come
in
it
might
be
the
reward.
What
was
well
an
update
that
was
valid,
not
becomes
invalid
and
then
next
one
becomes
valid,
and
that
brings
real
turn
on
the
router.
V
What
is
not
necessary,
so
we
implement
you
change
our
implementation,
it's
that
we
internally
do
these
processing,
but
we
notify
the
router
after
the
end
of
data
so
that
we
still
might
have
a
little
bit
of
a
churn,
but
because,
if
a
router
asked
during
this
update
it
gets
in
between,
but
nevertheless
so
we
reduced
run
dramatically
next
slide.
So
then
we
created
another
tool,
that's
called
bgp
Sakai
and
this
tool
allows
us
so
what
we
need
to
be
needed
between
the
traffic
generator
that
has
more
than
one
signed
hop
in
there.
V
V
So
what
we
did
in
the
video
is
that
all
it's
a
traffic
generator
that
creates
a
fully
signed,
p2p
sec
updates.
It
allows
to
store
these
updates
in
binary
files.
We
wanted
a
very,
very
simple
way
of
scripting
update,
so
the
prefix
alone
would
basically
mean
you
originate
it.
Then
you
can
just
look
at
this
different
speaks
for
itself
next
site,
then
the
crypto
tester
we
have.
As
I
said,
we
have
our
crypto
engine
where
we
only
need
to
be
to
be
SEC
path
attribute.
V
We
don't
need
the
whole
update
this
community
strings
and
so
forth
there.
If
you
implement
the
crypto
API
and
you
create
a
plug-in.
You
basically
can
test
this
plug-in
against
Russell
traffic
as
well
next
slide,
and
so
the
the
mother
was
another
thing
we
wanted
to
have
more
than
to
reference
implementation
of
BGP.
Second
self.
So
we
forgot
everything
what
we
did
and
we
started
had
and
someone
differently
implementing
b2b
zag
to
just
make
sure
that
what
we
do
does
the
things
right.
V
And
so
then
we
came
to
the
thing
that
the
problem
is
easy:
tsa,
P,
256,
it's
it's
non-deterministic
algorithm,
so
you
have
problems
that
the
signature
is
all
the
time
different.
So
we
went
to
our
c6
979,
which
provides
some
case,
and
we
allow
to
generate
signatures
using
this
case
so
that
you
can
basically
always
get
the
same
signature
for
the
same.
So
like
any
other
algorithm,
and
then
we
also
implemented
things
especially
for
testing.
What
happens
if
my
update
signing
fails,
for
example,
due
to
a
corrupt
key
or
a
missing
key?
V
So
we
allow
that,
if
you
have
now
an
MRT
file
feeding
in
and
there
might
be,
that
you
miss
a
key
either
you
drop
the
whole
update
or
you
generate
for
bactrim
days
for
update,
or
we
also
allowed
to
fake
a
signature
and
fake
an
S
ki.
Where
you
say
you
know
what
I
want
to
see
how
the
other
outer
reacts.
Even
if
I
give
him
a
real
SK
I,
but
never
the
fake
signature
that
they
don't
say,
hey.
That
is
well
it
so
exciting,
and
then
we
have
the
player.
V
So
then
we
generate
all
this
stuff.
We
store
it
in
bgp,
second
traffic,
in
a
binary
file
for
the
crypto
tester.
We
also
stores
the
public
keys
for
BGP
set
traffic.
You
have
to
pre
install
a
lot
of
keys
or
get
them
via
the
RC
to
be
8210,
and
you
can
play
them.
The
good
thing
on
this
is
especially
if
you
make
b2b
traffic
when
we
sign
all
these
updates,
we
create
it's,
it's
not
highly
performant,
so
we
want
to
have.
We
want
to
take
all
this
trip
to
overhead
and
generation
overhead
taking
out.
V
We
want
to
feed
into
the
router
as
fast
as
possible,
so
that's
why
we
allow
them
to
read
directly
the
binary
files
of
the
only
thing.
What
we
now
have
is
IO
time
from
reading
this
stuff
and
just
putting
it
as
it
is
on
the
wire
sending
to
next
slide
and
that's
our
printer
in
this
printer.
You
can
basically
also
use
PGP,
Zeca
or
just
as
a
sync.
It
doesn't
produce
any
traffic.
It
keeps
the
session
open
and
Treacy
speech.
V
If
you
see
it
insect
traffic
and
then
I
can
filter
on
everything,
I
can
filter,
Romeo
knees,
update,
show
me
the
open
from
a
notification
show
me
people
at
whatever
you
feel
like,
and
you
can
yeah.
As
I
said
you
can
have
it
on
the
receiving
site.
You
also
connect
on
the
sending
side
so
highly
good
for
for
debugging
next
slide,
and
that's
where
you
get
it
still
be
a
PS
or
X
or
att.net
orgoth.
So
source
is
open
source.
If
you
have
any
question,
come
to
me
I'm
here
all
week,
I
can
answer
questions.
