►
From YouTube: IETF99-HRPC-20170721-0930
Description
HRPC meeting session at IETF99
2017/07/21 0930
https://datatracker.ietf.org/meeting/99/proceedings/
A
B
B
Hello,
everyone
welcome
very
much
to
the
human
rights
protocol
considerations
meeting
Friday
morning.
July
21st
also
welcome
to
remote
participants.
We
got
quite
a
full
agenda
here
and
a
bit
different
schedule
from
normal.
We
made
two
changes
in
the
schedule,
as
discussed
on
the
list
is
that
we
have
a
longer
session,
then
normally,
because
we
often
ran
out
of
time
and
instead
of
having
three
or
four
speakers
for
inspiration.
We
took
one.
So
we
would
have
more
time
for
discussion.
You
would
go
into
a
bit
more
depth.
B
I'm
also
happy
at
the
end
to
see
whether
you
think
this
is
a
useful
model.
We
should
revert
back
or
we
should
go
out.
Otherwise
they
are
the
administrivia.
We
have
a
note-taker.
Do
we
already
have
a
volunteer
for
the
different
scribe?
We
have
a
jabber
scribe,
excellent
thanks.
So
much,
please
join
the
main
list.
If
you
haven't
done
so
already,
poor
requests
for
drafts
are
welcoming
github.
You
can
find
the
intros
the
minutes
and
a
website
there.
I
said
we
have
quite
a
full
agenda.
B
Does
anyone
have
any
other
points
for
the
agenda
agenda
bashing
one
to
approved
here?
We
go
so
this
is
the
note.
Well,
if
you
haven't
noticed
it
well,
then
you
haven't
noted
so
well
during
this
whole
week
because
it's
Friday
morning,
so
if
you
have
any
IPR
claims
you
would
like
to
make
or
you
have
any
IP
are
things
for
anything
you'd
like
to
present.
Please
tell
us
now
because
else
it's
too
late.
B
So
as
always,
it's
very
important
that
you
review
documents,
not
only
because
then
we
have
a
man
can
have
a
more
informed
discussion,
but
also
the
quality
of
the
IETF
documents
depends
on
your
reviews.
So
please
review
documents,
your
own
working
group
also
in
other
working
groups,
and
then
we
will
also
review
your
documents.
B
So
the
step
research
group
we
have
been
we've
been
quite
Britney.
We
have
been
working
on
the
topic
since
ITF
91
we've
been
a
proposed
research
group
since
ietf
92,
and
you
see
we
have
a
pretty
consistent
production
of
work
actually
with
a
smart
increase
in
a
number
of
drafts
and
also
continuously
new
things
coming
about
which
you
also
see
things
in
the
presentation
of
it.
B
So
what
we're
trying
to
do,
as
is
in
our
Charter,
is
to
expose
the
relationship
between
protocols
and
human
rights,
with
an
initial
focus
on
the
right
of
freedom
of
expression
and
the
freedom
of
assembly.
We've
tried
to
propose
guidelines
and
also
see
how
those
guidelines
could
work
in
practice
and
also
to
increase
awareness
of
the
human
rights
community
and
the
technical
community
about
the
importance
of
technical
workings
of
the
internet
and
its
impact
on
human
rights,
and
then
we'd
like
to
start
off
with
a
presentation
and
Q&A
with
wilt
Milton.
B
D
Well,
thank
you
I'm
pleased
to
be
here
I'd,
particularly
like
to
think
I've
and
Niels
for
inviting
me
I
think
it's
very
interesting
that
they
were
so
eager
to
have
the
discussion.
I
do
want
to
say
that
the
idea
for
this
paper
was
in
fact
Farzin
s
and
she
couldn't
be
here
today.
She
has
a
bit
of
a
human
rights
problem
being
Iranian
and
living
in
the
u.s.
she's
afraid
to
leave,
or
at
least
was
until
the
Supreme
Court
settled
that
issue.
D
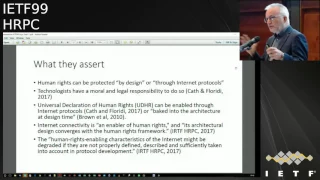
Just
to
give
you
a
brief
summary
of
the
somewhat
provocative
points
we
want
to
make
yeah.
First
of
all,
we
want
to
subject
the
belief
that
we
can
promote
and
protect
human
rights
through
protocols
and
standards
or
architectures
to
some
critical
assessment
and
I
in
particular,
have
a
very
long
background
in
an
old
guy
in
science,
technology
and
society
studies
and
history
of
Technology
and
you'll
see
the
intersection
of
that
discipline
to
what
you're
doing
here.
D
Fundamentally,
we
believe
that
human
rights
are
primarily
a
political
and
institutional
accomplishment
and
cannot
be
reduced
to
a
matter
of
technical
design.
Although
we
of
course
believe
that
technology
dis,
equilibrate,
s--
existing
institutions
and
alters
the
way
society
works,
it's
not
simply
a
matter
of
technical
design,
and
there
are
also
some
disturbing
aspects
of
potentially
negative
aspects
of
the
trying
to
make
policy
or
protect
or
enable
rights
through
your
tech
designs.
D
So
let
me
first
try
to
characterize
the
views
boom
that
we
are
criticizing
and
the
fact
of
the
matter
is
we
quickly
discover
that
there
is
not
a
simple
or
uniform
statement
here.
That
is
some
clearly
theoretically
derived
position.
We
have
a
spectrum
of
views,
so
at
one
extent
some
people
are
asserting
that
human
rights
can
be
protected
by
design
or
through
the
internet
protocols,
and
given
that
technologists
have
a
moral
and
legal
responsibility
to
do
so.
D
Not
what
I
don't
know
whether
to
call
in
RFC
or
not?
Yes,
I
think
it
is
so
it
talks
about
Internet
connectivity
as
enabling
human
rights,
in
other
words,
taking
a
technological
or
creating
a
technological
capability
that
advances
freedom
of
expression
and
there's
a
statement
in
there
that
the
architectural
design
of
the
Internet
converges
with
the
human
rights
framework,
which
we
frankly
don't
know
what
that
mean.
D
There's
another
statement
that
the
human
rights
enabling
characteristics
of
the
Internet
might
be
degraded
if
they
are
not
find
described
and
sufficiently
taken
into
account
in
protocol
development,
so
that
is
again
a
step
back
from
the
harder
position
that
human
rights
can
be
protected
by
design.
What
they're
saying
here
is,
let's
be
aware
of
impacts
or
potential
impacts
when
we're
developing
protocols.
D
One
of
them
is
a
stronger
claim,
the
the
famous
claim
at
least
made
famous
by
Lessig
but
developed
by
others
before
him.
That
code
is
law
and
then
there's
a
somewhat
weaker
and
we
think
more
accurate
claim
that
the
technology
mediates
rights,
that
is,
it
is
a
kind
of
an
intermediary
between
the
accomplishment
of
Rights,
on
the
one
hand,
and
the
the
technical,
the
the
efforts
by
people
to
use
it
in
ways
that
either
compromise
or
advance
human
rights,
and
that
latter
point
is
I,
think
articulated
in
Laura
denardis
work.
D
The
infrastructure
is
in
place
and
people
are
trying
to
do
things
to
it
that
either
compromise
human
rights
or
advance
human
rights,
for
example,
denardis
and
others
have
frequently
focused
on
the
famous
SOPA
and
PIPA
laws
which
we're
trying
to
use
domain
name
system
blocking
to
to
enforce
copyright
or
prevent
copyright
infringement
in
the
United
States.
Now
this
is
clearly
not
a
design,
a
really
a
redesign
of
Internet
protocols
that
was
an
ex
post
attempt
to
use
the
capabilities
of
the
infrastructure
to
block
or
filter
certain
kinds
of
things
that
were
perceived
as
violating
copyright.
D
So
with
that,
characterization
sort
of
the
theory
and
practice
will
now
go
into
our
critique.
Well,
the
first
thing
that
we
notice
and
again
this
point
is
certainly
contestable
at
some
point,
but
for
a
very
large
extent
the
Internet
is
already
designed.
Its
basic
architecture
is
in
place.
This
is
not
to
say
that
it
doesn't
change
that
there
aren't
marginal
adjustments
and
changes
that
there
aren't
new
standards,
but
any
kind
of
protocol
development
that's
going
on
now
and
the
IETF
is
not
going
to.
E
D
An
immediate
and
major
impact
on
the
way
things
work
much
less
on
the
degree
to
which
human
rights
are
enabled
over
the
Internet
and
there's
something
also
interesting
about
that
is
you
know
if,
indeed,
new
standards
or
new
processes
within
IAAF
are
needed
to
protect
human
rights?
It
seems
that
seems
to
indicate
that
its
current
architecture
does
not
necessarily
protect
human
rights
that
this
again
is
more
of
a
site
of
struggle,
rather
than
baked
into
the
architecture.
D
The
second
problem
is,
we
have
some
difficulty
understanding
the
extremely
strong
linkage
that
is
asserted
between
the
UDHR
and
international
law
and
the
technical
architecture,
that
is
to
say,
if
you
say,
I
am
trying
to
protect
through
my
protocol.
The
confidentiality
of
data
I
know
what
that
means
very
clearly,
if
you're
saying
I'm,
trying
to
protect
the
right
of
privacy
as
defined
in
the
UDHR
I'm,
not
sure
I
do
know
what
you
mean,
if
you
say,
I'm,
trying
to
protect
the
entire
set
of
human
rights
and
enshrined
in
this
standard.
D
It
was
formulated
in
fairly
imprecise
terms,
they're,
not
all
of
the
rights
in
there,
for
example,
the
right
to
a
job,
I'm,
not
sure
you're,
going
to
help
that
with
your
protocol
development,
maybe
the
right
to
developers
to
a
job
might
be
in
some
way
advanced
by
what
you
do
here,
but
some
rights,
as
the
the
committee
here
recognizes
in
their
document,
are
not
that
relevant
to
ICTs
or
connectivity.
So
again,
that's
that's
a
big
step
back
from
the
general
claim
about
human
rights.
D
Now,
even
the
rights
that
you
consider
to
be
the
most
relevant
to
the
Internet
contain
serious
internal
conflicts,
so
one
of
the
obvious
ones
is
free
expression
versus
privacy.
The
human
rights
declaration
says
that
everybody,
you
know
the
famous
article
19
after
which
I
think
Neil's
has
tattooed
on
his
forehead
somewhere
says
that
you
know
freedom
of
expression.
Everybody
has
a
right
to
seek
and
impart
information
regardless
of
frontiers.
D
It's
great
it's
one
of
my
fav
formulations
of
the
right
to
freedom
of
expression,
but
then
later
on
it
says
everybody
has
the
right
not
to
be
defamed
to
not
have
their
reputation
besmirched
by
others,
and
so
those
two
things
can
obviously
clash.
So
how
do
you
do
that?
In
a
protocol?
Free
expression
versus
intellectual
property?
Is
intellectual
properties,
actually
recognize
human
rights?
D
Obviously,
human
rights
puts
great
emphasis
on
due
process,
but
it's
also
a
human
rights
issue
that,
if
you
don't
catch
bad
bad
people
who
do
evil
things
so
there's
a
tension
there.
Now
again
the
the
HPRC
people
are
not
naive.
They
recognize
this
in
their
documents.
But,
to
my
mind,
the
response
is
quite
lame,
they're
sort
of
saying.
Well,
you
need
to
balance
them.
D
Okay.
How
are
they
balanced?
How
are
they
balanced
in
a
protocol?
This
is
not
clear
to
me:
decisions
on
design
and
deployment
need
to
take
rice
conflicts
into
account.
Okay,
what
does
that
mean
to
take
them
into
account?
How
do
you
reconcile
them?
How
do
you
make
these
rights
into
the
architecture
when
you
are
that
when
you
have
these
conflicts
and
needs
or
balances?
D
So
that
is
what
we
consider
to
be
one
of
the
major
issues
with
the
the
linkage
that's
being
forged
problem.
Three,
probably
this
won't
be
too
controversial.
Code
is
not
law.
Okay,
and
to
understand
this,
you
simply
have
to
ask
yourself:
where
does
code
come
from?
It's
not
purely
exogenous.
It
doesn't
drop
down
from
the
sky.
Whoever
writes
code
is
responding
to
economic
incentives,
almost
certainly
probably
political,
doing
it
in
a
political
environment,
and
there
are
certain
kinds
of
legal
and
political
constraints.
D
So
there's
a
reciprocal
relationship
between
what
code
gets
written
and
the
surrounding
society
and,
in
fact,
code
and
architecture
can
be
and
often
are
overridden
by
laws
and
regulations,
and
so
a
good
example
of
this
comes
right
here
from
the
IETF
and
the
famous
interaction
that
this
group
had
with
the
kaliya,
which
is
in
the
u.s.
called
the
communications
assistance
for
Law
Enforcement
Act.
D
Now,
if
you
remember,
is
sometime
in
the
early
90s,
the
telephone
systems
started
getting
digitized
and
the
wiretapping
technologies
of
the
law-enforcement
agencies
and
Intel
agencies
realized
that
their
techniques
were
not
able
to
capture
information
in
the
same
way.
So
a
law
was
passed
in
1994
and
this
is
really
before
the
internet
was
a
big
thing
perceived
as
the
widespread
mass
medium.
So
they
passed
a
law
forcing
us
telephone
companies
to
redesign
their
network
architecture
to
facilitate
wiretapping
of
telephone
calls
by
law
enforcement.
D
And
then,
of
course,
the
internet
became
a
big
thing
and
the
law
enforcement
agencies
noticed
that
they
didn't
have
any
such
capabilities
for
the
Internet
and
when
the
IETF
was
working
on
standards
for
voice
over
IP
and
related
things,
somebody
suggested
to
them
I've
seen
assertions
that
the
FBI
asked
the
ietf,
but
I've
never
found
any
verification
of
this
request.
But
certainly
there
was
discussion
of
what
to
do
about
whether
their
standards
or
voice-over-ip
should
be
made
Kalea
compliance,
and
so
they
formed
the
famous
Raven
working
group.
D
I
think
it
was
in
October
or
November
of
1999
and
it
concluded
in
May
of
2000
and
the
IETF
basically
said.
No,
no
thanks.
We're
not
going
to
write
rewrite
our
standards
to
make
them
compliant
with
a
US
law,
as
you
probably
remember,
the
main
reason
for
that
was
not
so
much
human
rights
per
se.
Although
the
the
tenor
of
the
group
was
very
very
Pro,
privacy,
Pro,
individual
rights
and
anti-government
anti-surveillance,
but
they
basically
said
we're
a
global
standards
organization
and
we're
not
going
to
write
standards
to
the
specifications
of
one
government.
D
So
did
that
settle
the
matter.
Did
we
have
successfully
protect
privacy
on
the
Internet?
Well,
of
course,
what
happened
next
is
that
in
2004
and
five
all
of
the
law
enforcement
agencies
went
before
the
US
Federal
Communications
Commission
and
filed
a
petition
to
expand
kaliya
to
broadband
providers,
voice
over
IP
telephony
and
instant
messaging.
Of
course,
this
laws
would
only
apply
to
us-based
providers
or
people
with
the
major
jurisdictional
Nexus
in
the
US
and,
of
course,
the
civil
rights
civil
liberties
groups
oppose
these
requests.
D
The
Electronic
Frontier
Foundation
in
particular,
was
in
the
forefront
of
the
opposition,
but
this
was
post,
9/11,
America
and
surveillance,
one
politically
over
privacy
and
individual
rights.
So
we
got
a
kaliya
compliant
broadband
providers.
However,
the
technology
of
the
internet
was
sufficiently
diverse,
complex
and
changing
that
there
was
continued
to
be
this
struggle
over
surveillance
and
privacy,
as
you
all
well
know.
Indeed,
in
this
period,
the
FBI
and
the
NSA
continue
to
claim
that
they're
going
dark
and
privacy
advocates
continue
to
worry
about
the
massive
scope
of
surveillance
on
the
Internet.
D
So
what
lessons
would
I
grow
from
the
Kalia
case?
Well,
one
of
them
obvious
ones-
is
that
the
so-called
bad
guys
or
the
anti
human
rights
forces
can
use
a
standards
process
to
they
can
specify.
You
know,
let's
get
into
the
IETF
and
try
to
urge
them
to
do
something.
Let's
get
go
to
the
regulator
and
tell
them
to
pass
new
standards
that
were
a
compulsory,
so
there's
no
nothing
about
doing
things
via
standards
and
makes
it
throw
human
rights
it.
D
The
other
conclusion
is
that
code
was
code
in
law
was
law.
The
ietf
refusal
to
make
its
architecture
modifications
did
not
settle
the
matter
by
itself
and
after
the
FCC
intervention,
there
were
some
law
dictating
code,
and
then
we
saw
norms,
code,
law
and
markets
working
together
as
elements
in
a
political
struggle
over
privacy.
D
It
doesn't
seem
outlandish
for
me
to
imagine
that
if
indeed,
you
find
yourselves
actively
shaping
human
rights
in
a
way
that
really
tilts
the
social
environment,
in
the
way
that
you
want
that
you
might
find
governments
knocking
on
your
door
and
saying
well,
maybe
you
should
have
some
representatives
of
our
point
of
view
in
your
committees.
Forget
about
technical
expertise.
You
guys
are
in
the
policy
business.
Why
can't?
D
D
Dissident
groups
like
Protestants,
to
disseminate
their
views
in
in
mass
form
in
ways
that
gave
them
a
competitive
advantage
over
the
old
stodgy,
Catholic
Church,
but
and
kings
and
princes
were
also
challenged
by
this.
So
what
happened?
Well,
the
government
started
to
clamp
down
on
printing
presses
through
various
mechanisms.
D
One
of
the
most
simpler
ones
was
simply
to
arrest
dissidents
and
put
them
in
jail
or
kill
them,
which
goes
on
today,
of
course,
but
sometimes
they
try
to
exert
more
systematic
economic
control
over
the
printing
press,
for
example,
by
licensing
presses
and
awarding
monopolies
to
particular
publishers
to
publish
specific
kinds
of
books,
particularly
in
England.
The
printing
press
was
highly
licensed
until
I
think
the
early
18th
or
19th
century
mmm-hmm
case
abroad.
A
radio
broadcasting
is
equally
interesting.
D
D
Indeed,
not
so
much
because
of
specific
technical
architecture
made
them
promote
freedom,
but
because
they
were
new
technologies
in
a
state,
didn't
know
how
to
control
them
yet-
and
this
is
particularly
true
of
the
internet,
where
we
had
you
know
just
kind
of
burst
onto
the
scene,
unexpectedly
by
passing
telecom
monopolies
and
bypassing
national
barriers
to
censorship
and
control,
and,
of
course,
later
on
states
learned.
How
can
we
control
this?
How
what
can
we
do
to
stop
this?
What
can
we
do
to
stop
that?
D
So
you
really
have
to
pay
attention
to
the
historical
trajectory
of
the
technology.
It
is
important
to
understand
how
and
why
these
technologies
broke
out
of
the
chains
of
previous
technologies,
but
it's
also
important
to
understand
that.
Inevitably,
those
who
want
to
control
will
discover
new
ways
to
control,
just
as
people
who
want
to
evade
control
will
discover
new
ways
to
evade
control.
So
that
leads
to
one
of
my
final
points,
which
is
that
design
is
ex-ante.
D
It
happens
before
the
fact
and
rights
violations
are
really
ex-post
and
knowledge
of
how
they
occur
and
where
they
occur,
is
really
after
the
fact
so
true,
assessment
of
human
rights
impact
of
various
technical
developments
can
only
occur
after
the
fact
and
standards
are
protocols
that
seem
to
be
secure
or
protective
at
the
moment
of
design
may
actually
have
unintended
consequences.
They
may
be
exploited
in
ways
that
you
don't
anticipate
or.
D
D
The
one
of
the
objectives
that
we've
heard
from
people
involved
in
the
HRP
see
is
that
they
want
to
change
the
language
that
you're
using
to
describe
the
technologies,
but
we're
not
sure
that
simply
changing
language
will
have
any
actual
impact
on
human
rights
on
the
Internet.
Again,
it
might
make
you
more
aware
of
certain
things,
but
by
itself
the
change
of
language
will
not
have
much
of
an
effect.
D
So,
to
conclude,
we
don't
want
anybody
to
go
away,
thinking
that
we're
against
human
rights,
we're
in
favor
of
human
rights
and
in
particular,
I
mean
I,
can't
have
to
qualify
that
statement
I'm
very
much
in
favor
of
freedom
of
expression,
privacy,
the
classic
civil
and
political
rights.
I,
don't
know
about
all
of
those
things
that
are
classified
as
human
rights
under
human
rights
law,
but
the
idea
that
you
all
are
in
a
very
powerful
position
to
advance
those
rights
through
Internet,
Protocol,
design,
I
think
is
needs
to
be
moderated
and
looked
at
soberly.
D
So
the
idea
is
not
to
discourage
you
from
being
aware
of
human
rights
or
to
believe
or
or
to
in
any
way
divert
you
from
a
commitment
to
those
rights,
that's
simply
to
challenge
unrealistic
expectations
that
could
in
fact,
backfire
in
certain
ways
and
otherwise
might
lead
you
to
to
waste
a
lot
of
energy
on
things
that
are
not
really
where
the
action
is
so
open.
It
up
to
discussion.
F
G
Hi
there
my
name
is
Andrew
Sullivan,
so
I
I
guess
it
probably
won't
be
too
surprising
that
I'm
somewhat
sympathetic
to
this.
To
this
description
of
the
issues
and
in
particular,
I
think
some
of
us
were
a
little
nervous
during
this
work,
because
the
problem
I
think
for
that
you
mentioned
about
you,
know,
sort
of
involving
the
standards
process
directly
in
in
in
political
tussles,
but
I
wonder
whether
there
is
a
more
generous
reading
of
the
not-quite
RFC
and
that
is
to
to
read
it
as
just
an
exhortation
to
protocol
designers.
G
If
you
think
about
the
consequences
of
potential
technical
trade-offs
they
make
for
any.
Given
you
know
right
situation,
and
and
and
if
it's,
if
it's
just
that,
that
seems
a
little
less
a
little
less
controversial
that
you,
you
can
make
decisions
that
can
have.
You
know
potentially
rights,
enabling,
if
you
believe
in
rights,
rights,
enabling
consequences
or
rights,
disabling
consequences
and
and
and
maybe
part
of
the
difficulty
is,
there's
there's
a
little
bit
of
a
tension
in
the
text,
sometimes
between
the
more
exhorted,
Tory
kind
of
version
of
it
and
more
optimistic
version.
G
D
I
wouldn't
have
wanted
policy
makers
or
international
lawyers
to
have
any
kind
of
a
gatekeeping
function
over
that
I
think
the
great
thing
about
what
the
internet
community
did
was
they
created
this
capability
and
didn't
worry
about
the
consequences.
You
know
they
just
did
it
and
and
that
advanced
human
society
greatly.
But
whenever
you
create
a
capability,
you
don't
really
know
how
it's
going
to
be
used
completely.
It
could
be
used
by
people
for
purposes
that
you
don't
really
know
and
we're
certainly
learning
it
now
about
the
Internet.
D
So
in
terms
of
the
awareness
of
possible
impacts
and
again
you
have
to
be
modest
about
your
ability
to
know,
I
think
it's
great
to
encourage
the
considerations.
The
aspects
the
awareness
I
have
no
problem
with
that
at
all,
but
again
just
be
modest
about
the
ex-ante
versus
ex-post
problem
and
realize
that
things
that
you
do
now
might
actually
be
used
in
ways
of
just
really
appalled.
You
later.
E
Hi
Bob
Hinton
been
a
little
while,
since
we
chatted
last
so
two
things
the
thing
at
the
beginning
where
you
said
that
the
you
know
the
Internet
is
basically
static,
so
so
that
there's
a
there's
a
lot
of
truth
in
that,
but
it's
not
the
whole
truth.
I
mean
I.
Think
the
recent
worth
the
ITF
has
been
doing
on.
E
You
know
ubiquitous
encryption
and
privacy.
I
think
you
know,
isn't.
It
seems
very
in
line
with
human
rights
to
make
it
harder
for
people
to
look
at
traffic.
You
know
I
mean
there
was
there's
a
big
tussle
going
on
right
now
with
TLS,
with
the
new
version
of
TLS
as
to
whether
how
easy
or
hard
it
is
for
middleboxes
to
look
at
the
encrypted
traffic.
So
I
mean
that
that's
a
very
active
discussion
here.
So
there
is
still
a
lot
of
things
that
I
think
affect
human
rights
going
on
here
today.
E
So
it's
not
completely
static.
Obviously
it's
the
basic
package.
Switching
architecture
hasn't
changed
too
much
and
the
other
thing
I've
always
thought
for
a
long
time
that
when
you
design
technology
or
in
this
case
protocols,
you
are
making
policy
decisions,
you
may
not
be
quite
aware
of
it,
but
what
the
capabilities
you
build
in
those
protocols
or
the
capabilities
you
don't
build
in
effect,
what
can
be
done
with
them
and
that
that's
very
much
a
policy
I
mean
it
starts
from
the
creation
of
packet-switching
was
a
giant
policy.
E
E
Packets
are
more
distributed
than
they
used
to
be
so
you
know
if
they're
I,
think
policy
and
technology
choices
are
not
these
two
separate
domains.
There's
not
the
policy
people
and
then
the
the
protocol
designers.
There's
a
lot
of
overlap
here
and
I
agree.
It's
good
that
when
we
do
design,
we
give
this
some
consideration.
You
know
it's
hard
to
know
exactly
how
it
applies,
but
you
know
it's
worth
thinking
about.
E
D
I
think
the
the.
By
the
same
token,
you
say
that
you're
making
policy
decision.
Do
you
want
policy
makers
looking
over
your
shoulders,
you
make
those
decisions
or
do
you
want
to
be
solving,
let's
not
even
to
call
it
solving
technical
problems.
Do
you
want
to
be
creating
technical
capabilities,
and
you
want
a
free
hand
to
do
that?
Or
do
you
want
governments
and
politically
representation
to
constrain
you
in
those
in
those
choices.
H
I
Kkeok
Maya
I
have
a
few
comments.
I
think
it's
a
bit
too
straightforward
to
think
like
the
IP
revolution
or
internet
revolution
is
like
a
radio
or
the
free
press,
because
we're
much
more
flexible
and
I
understand
that
on
the
on
the
lower
layers,
maybe
the
technology
isn't
changed
that
often,
but
when
you
look
now
at
what's
going
on
in
terms
of
clarifications
on
higher
layers,
where
also
human
rights
most
likely
need
protection,
we're
changing
the
architecture
every
few
years
you
know
ideas
come
in,
but
I
think
there.
I
I
That's
my
understanding,
my
feeling
and
from
that
I
see
that
the
ITF
has
light
momentum
to
use
its
capabilities
to
bring
human
rights
issues,
whatever
issues
into
their
protocols
to
make
sure
they
are
there
and
the
other
bodies
simply
have
to
live
with
that,
at
least
at
the
moment
and
I
think
this
is
something
we
should
take
into
consideration.
We
should
keep
in
our
mind
that
the
ITF,
from
my
perspective,
can
really
make
a
difference
here.
Thank
you.
D
I
D
Yeah
I
don't
have
any
fundamental
disagreement
with
that
I
think
I
would
just
emphasize
that
maybe
you've
made
a
bunch
of
technical
decision
incremental
ii
over
the
last
10
years
that
have
enabled
this
movement
to
the
cloud
and
this
movement
to
the
cloud
is
going
to
have
a
number
of
policy
competition
implications
that
there's
no
way
you
could
really
design
for
in
your
protocols
there.
You
know
you
need
to
massive
levels
of
concentration,
which
requires
some
kind
of
regulatory
response
by
antitrust
or
competition
policy.
I
Just
want
to
say
I
I
understand.
Did
you
say
it's
not
our
our
task,
but
when
you
see
the
discussions
that
were,
for
example
in
when
it
came
to
TLS,
this
is
sort
of
made
our
task,
because
some
people
want
certain
things
that
others
don't
want.
So
the
maybe,
if
you
say
it's,
not
our
task.
Yes
from
a
technical
point
of
view,
maybe,
but
the
confrontation
is
brought
here
anyhow,
so.
D
I
totally
agree
that
when
it
comes
to
TLS
issue,
what
you're
doing
is
saying
we
are
designing
for
confidentiality,
which
is
a
classic
part
of
the
triad
of
information,
security
and
I'm.
All
for
that,
the
question
is,
you
know
there
are
going
to
be
countervailing
forces.
You
know,
maybe
the
the
TLS
mechanisms
you
come
up
with.
Well,
some
states
will
say
you
can't
use
those
and
they'll
try
to
regulate
their
infrastructure,
to
prevent
that
others
might
find
new
ways
to
get
around
it.
That's
all
I'm
saying
is
that
you're
not
settling
the
issue
by
I?
B
Of
beating
the
mic
thanks
so
much
Milton
Ron
I,
thanks
also
for
the
reference
to
the
movie,
a
requiem
for
a
dream.
I
I'm
I'm
afraid
that
this
now
slowly
starts
to
become
a
more
of
Inception,
because
I'm
going
to
tell
you
to
wake
up
from
your
dream
and
then
you're
going
to
tell
me
wake
up
from
your
dream.
So,
let's
see
how
how
matter
we
can
get.
B
But
let
me
go
back
to
the
last
time
when
I
thought
I
was
awake,
you
know
as
a
reference,
and
that
was
at
the
previous
ITF
and
that's
where
we
had
a
talk
from
from
Dave
Clark,
who
said
are
the
author
of
the
famous
hustle
paper
and
said
there
is
a
tussle,
and
that
is
something
that
you
seem
to
seem
to
acknowledge
here
as
well
and
I.
Think
what
we've
been
saying
in
a
draft.
We
need
to
make
the
tussle
more
explicit.
B
So
my
question
would
be
here:
what
are
you
adding
to
that
discussion
because,
as
others
have
said,
there
are
already
policy
makers
here?
There
are
already
nation-states
here
pushing
their
influences
with
the
Raven
process,
so
you
that
you've
seen
we
have
also
seen
Wheaton
of
crypto
standards.
We've
seen
also
the
explicit
request
for
the
weakening
of
crypto
standards.
B
We've
also
been
other
requests,
so
I
think
the
that
you
seem
to
describe
the
policy
layer
as
a
separate
layer,
whereas,
whereas
it's
integrated
through
the
whole
stack
and
I'm
a
bit
surprised
that
you
as
a
Science
and
Technology
scholar
haven't
mentioned
the
concept
affordances,
because
network
and
the
technology
always
has
specific
characteristics
which
inhibits
or
stimulates
or
enables
or
disables
a
certain
behavior
and
you're
completely
rights.
That
you
cannot
completely
predict
that,
but
it
doesn't
mean
you
cannot
think
about
it,
and
it
doesn't
mean
you
cannot
model
it.
B
That
doesn't
mean
you're
going
to
be
right
or
you
can
take
that
into
account.
In
your
your
analysis
and
with
the
internet.
There
is
also
not
so
much
an
ex
post
and
an
ex
ante,
but
it's
a
it's
an
ex
to
Dante.
You
know
we
are
continuously
evolving
the
the
network
and
we
have
no
idea
how
it's
going
to
be
used.
B
There
was
sudden
uptick
of
decentralized
bit
BitTorrent
protocols,
and
then
it
seems
that
distribution
was
going
to
be
much
stronger,
but
now
we
see
a
very
big
tendency
towards
centralized
a
on
many
different
layers
of
the
stack.
You
said
it's
not
your
problem.
Well,
it
is
our
problem
if
that
leads
to
a
less
resilient
network,
and
so
that's
when
we
start
thinking
what
can
we
do
about
that?
B
So
I
think
it
definitely
has
influence
on
what
we
do
here
and
then
your
reference
to
the
printing
press
and
the
radio
I
was
very
surprised,
but
also
it
was
great
because
the
printing
press
initially
was
embraced
by
the
Catholic
Church
because
then
finally,
they
did
not
depend
on
monks
to
copy
to
copy
and
they
could
distribute
and
they
thought.
Finally,
now
everyone
is
going
to
have
a
Bible
and
we're
going
to
have
ultra
dominance.
B
So
everything
has
specific
affordances
and
you
see
different
ways
in
which
control
is
possible
and
which
control
is
harder,
so
we've
seen,
for
instance,
the
possibility
of
shortwave
radio
made
the
distribution
of
news
much
easier,
but
then
there,
of
course,
was
jamming,
but
jamming
was
a
very
large
economic
investment
to
do
so,
you're
also
making
it
harder
for
people
to
censor
the
deads.
Also
work
we're
doing
here
and
we've
seen
now
the
discussion
on
deck.
B
D
I'm
not
sure
what
your
point
about
the
historical
things
are
to
reinforce
my
point
that
there's
an
ongoing
struggle
on
the
site
of
these
technologies.
The
Catholic
Church
thought
printing
press
was,
you
know
they
assumed
we
control
things
and
but
the
economic
affordances
of
the
printing
press.
You
know
almost
anything,
make
one
of
these
things
and
start
cranking
stuff,
and
now
you
connect
that
to
a
dissident
movement,
Protestantism
and
suddenly
you've
got
something
under
control,
and
then
you
start
yet
a
more
systematic
institutionalized
regime
of
press
control
which
lasts
for
200
years.
D
The
same
thing
with
brought
just
Brecht
apparently
didn't
know
that
I
guess
he
was
thinking
about
only
about
broadcasting,
but
broadcasting
was
preceded
in
pioneered
by
you
know:
early
1900s
hackers
known
as
radio
amateurs,
and
they
were
talking
to
each
other.
That
was
the
whole
point.
They
were
using
short
waves
to
bounce
signals,
around
publish
contact
with
people
all
over
the
world
and
it
was
the
radio
amateurs
who
suddenly
just
got
this
brilliant
idea
of
connecting
their
record
player
to
their
transmitter
and
start
broadcasting
music.
D
B
So
I
say
that
there
are
different
affordances
to
the
different
technologies,
a
way
in
which
the
internet
is
governed
makes
it
harder,
and
that's
also
part
of
the
later.
This
political
is
that
the
the
process
in
which
we
can
be
controlled
and
can
be
influenced
our
difference.
Then
we
get
back
to
the
tussle
that
here
we
can
take
the
tussle
more
explicit
and
can
seek
to
counterbalance
it
right.
I.
D
Gotta
say
something
about
the
tussle,
so
I
I
was
there
when
he
did
this
paper
at
the
telecom
policy
research
conference
in
what
way
about
2002,
or
something
like
that
and
to
us
that
was
like,
oh
so,
the
the
engineers
have
discovered
policy
struggle.
Well,
it's
like
what
you
want
to
call
it.
That's
cute
that
resonates
with
the
engineers,
but
this
is
what
we
do.
This
is
what
we
talked
about
for
the
last
200
years.
This
is
political,
so
of
course,
there's
tussles
over
technology.
D
J
Allyson
medkit
I'm,
the
I
work
for
Salesforce,
RI,
r,
TF,
chair
and
I,
don't
want.
We
have
some
time
I
interested
to
know
how
people
at
room,
especially
you
think
of
the
Kerala
effort,
that's
going
on
about
values
and
bias
in
algorithms,
and
there
too
there's
a
very
funny
ring
component
to
the
discussion
and
the
kind
of
neat
alliance
among
parties.
It's
not
just
a
dominant.
It's
not
just
policy
folks
got
folks,
but
also
say
journalists
and
I
think
there's
place
paid
for
that.
The
Fourth
Estate
here
too
so
I
thought.
B
D
You
know
you
create
a
capability
right
and
then
you
find
what
it
does
and
some
of
the
things
that
it
does
are
unanticipated
and
whether
may
be
bad
and
some
of
them
may
be
fantastic,
and
then
society
starts
just
the
abilities
based
on
what
had
lurked
out
what
happened
with
your
first
pass,
and
this
is
was
a
state
right
now.
You
know
we
had
this
great
Google
search
algorithm
and
then
we
covered
various
ways.
D
It
could
be
gamed
or
various
ways
in
my
discriminatory
results,
and
so
now
people
are
wanting
to
take
that
was
in
make
them
more
transparent
and
the
possibility
or
capabilities
of
regulate
algorithm
needs
to
be
also
tempered
by
the
the
concept
of
you
know,
reward
innovations.
So
if
you
develop
this
great
algorithm,
there's
wonderful
things,
but
then.
D
It
to
everybody,
you
have
no
sort
of
intellectual
property
protection
for
it
that
I
deterred
from
developing
other
algorithms.
So
there's
no
free
lunch
in
terms
of
regulating
ability.
You
have
to
be
very
careful
how
you
do
that.
That's
my
perspective,
I
think,
there's
probably
people
here
who
know
more
about
them
than
I.
Do
we
haven't
really
focused
on
the
out
connect
regular
much
in
our
research.
C
Phillip
oddly
I
just
wanted
to
follow
up
on
the
earlier
comment
about
how
the
architect
has
changed.
To
me
with
a
big
thing,
that's
changing
was
maybe
unexpected
15-20
years
ago.
We
thought
it
would
be
we'd
end
up
with
something
that
was
highly
distributed
and
lots
of
people
in
there
Garrard
advising
applications,
and
we
actually
ended
up
with
huge
economies
of
scale,
see
we
sent
it
up
with
monopoly.
Basically
or
that's
the
big
trend.
Isn't
it
have
them
not
the
particular
application
area?
C
D
D
In
it,
but
it
does
have
a
very
important
point,
which
is
that
all
of
these
knowledge
ease
go
through
this
phase
and
then
in
the
early
stages.
There's
lots
of
small
innovation
going
on
it's
a
very
free
environment,
and
then
the
basic
structures
are
discovered
and
works
and
what
doesn't
work
discovery
get
some
solid
ation.
Then
you
get
institutionalization
and
some
kind
of
ties
to
the
government
and
more
rigid
regulation.
And
then
maybe
somebody
comes
along
with
the
disruptive
innovation
that'sthat's
equilibrium.
D
D
D
F
You
I
think
that's
a
great
note
to
end
on
Thank
You
Milton
for
coming
and
talking
about
a
paper
that
you're
still
working
on
I,
really
appreciate
you
coming
in
speaking
to
to
this
group
about
it
and
look
forward
to
reading
the
paper
when
you
in
person
any
or
Farzana
have
completed
it.
So
thanks
a
lot.
Okay,
moving
on
okay,
so
the
next
thing
we
have
is
I
guess
you're
talking
about
Neos
your
paper
on
well.
B
We
talked
about
this
draft
in
the
last
meeting
and
it
was
me
actually
setting
up
a
structure
about
things
we
talked
and
then
some
people
wanted
to
take
it
on.
There
is
not
a
new
version
out
I
wanted
to
check
in
with
room
if
anyone
interested
in
working
on
whether
we
should
pursue
this
further
and
if
people
are
interested
in
working
on
this.
K
F
B
L
L
This
started
like
thought
out
like
that,
because
apparently
there's
a
consensus.
The
eight
human
rights
were
tokens
considerations.
Research
group,
the
denial
of
service
attacks-
are
no
to
be
promoted
by
the
ietf
because
they
damage
the
intern
architecture.
So
we
were
wondering
how
this
does
the
internet
architecture
enable
and
or
inhibit
freedom
of
association
assembly,
including
protists,
that
is
encompassed
by
this
right,
along
with
many
other
rights
like
freedom
of
speech
and
even
privacy,
so
very
quickly.
The
difference
between
assembly
and
Association.
L
That
was
the
concept
of
forest
association
that
has
echoes
with
the
internet
architecture
itself,
because
these
rights
are
envisioned
as
freedoms,
which
means
that
nobody
is
supposed
to
be
forced
to
join
a
group
or,
if
even
forced,
to
leave
a
group.
It's
just
a
freedom.
You
can
either
join
or
leave
whatever
group
you
choose
either
temporary
or
permanent.
L
Also
another
thing
that
we've
been
discussing,
we
haven't
quite
reached
consensus
and
it
would
be
super
interesting
to
see
when
you
think
is.
If
the
internet
itself
was
an
association
and
assembly
or
an
association,
let's
just
treated
as
synonyms
right
now,
because
if
it
is,
it
should
be
protected
by
these
rights,
and
that
has
other
impacts
on,
let's
say,
other
kinds
of
networks
right.
So
if
the
Internet
is
the
network,
an
association
and
an
SM,
we
are
also
essentially
networks.
L
So
we
were
wondering-
and
we're
still
wondering
if
this
is
something
that
we
can
definitely
assert
next,
please
well,
just
as
a
side
note,
the
IETF
is
an
assembly.
We
could
even
consider
an
association,
even
though
not
in
an
association
doesn't
have
to
be
a
corporation
or
it
doesn't
even
have
to
be
legally
constructed.
It
can
just
be
a
bit
more
formal
and
a
bit
more
more
permanent
and
RFC
3233
defines
the
IETF
said:
an
open
global
community
of
network
designers
operator,
vendors
and
researchers.
L
So,
in
this
sense,
IETF
is
definitely
an
assembly
Association
protected
by
these
rights.
Next,
please,
even
the
mere
discussion
of
RFC's
would
not
be
possible.
Without
these
human
rights
and
justice,
an
historical
side
know
the
work
protocol
find
its
way
into
language.
Is
computer
networking
because
of
this
need
of
collective
agreement.
L
Next,
please,
so
we
mapped
out
a
bunch
of
cases
and
examples,
but
I
really
want
to
emphasize
the
difference
between
free
association
and
forced
Association,
because
I
think
it's
one
of
the
most
interesting
ones
that
we've
been
able
to
come
up
with,
starting
by
the
text
of
the
ICCPR
on
the
UDHR
and
then
taking
it
to
the
internet
architecture
and
see
how
it
won,
impacts
the
other
and
how
the
text
impacts
could
be
interpreted
in
terms
of
inner
architecture.
So
free
association,
it's
very
easy.
Let's
just
think
about
mailing
lists.
L
You
join
a
mailing
list,
you're
tired
of
mailing
lists.
You
just
unsubscribe
the
peer-to-peer
preppy
protocol.
It's
also
a
an
association
and
assembly
issue
because
it
allows
for
collective
collaboration.
Ideally,
it
would
be
without
the
need
for
centralized
servers
and
but
there's
very
different
models
of
that,
and
this
took
us
to
a
next
question
that
I
will
talk
in
a
couple
of
talk
about
in
a
couple
of
minutes
and
then
the
issue
of
forced
Association,
we're
thinking
about
denial
of
service
attacks.
As
I
said,
there's,
apparently
a
consensus
within
the
human
rights
protocol
considerations.
L
Research
group
that
there's
some
denial
of
service
attacks
that
are
legitimate,
there's
some
that
are
not,
but
the
IETF
should
not
be
making
those
distinctions
in
terms
of
content.
That's
from
free
speech,
free
speech
perspective,
but
taken
from
an
association
and
assembly
right
perspective.
We
can
we
ask
ourselves
two
things.
First,
if
the
denial
of
services
attacks.
L
Putting
race
the
entire
internet
architecture
so
to
speak.
Could
this
be
an
illegitimate
form
of
association
because
they,
and
given
that
the
Internet,
it's
an
association
itself,
if
we
are
able
to
concede
that
if
we
put
at
risk
the
Internet
as
an
association?
Could
that
be
an
illegitimate
association
form
that
should
not
be
promoted?
In
terms
of
like
your
architecture?
That's
one
question,
and
then
the
other
must
be
taken
into
consideration.
L
That
DDoS
attacks
are
also
a
form
of
forced
assembly
and
Association,
because
some
most
times,
and
sometimes
they
are
done
without
the
agreement
or
even
the
knowledge
of
the
in
both
parts
and
the
Internet
of
Things,
has
brought
interesting
discussions
regarding
that
with
ISPs.
The
logic
of
forced
Association
is
the
same
because
infinite
user,
the
edge
user,
needs
to
accept
the
policies
and
practices
of
the
edge
networks
that
provides
access
to
other
networks,
like
for
the
user,
to
connect
to
join
the
assembly
of
the
network
of
networks
of
the
internet.
L
If
we
are
ready
to
concede
that
they
always
have
to
connect
through
an
intermediary
and
while
connected
to
an
intermediary.
Well,
not
always
that,
let's
just
save
most
of
the
time
while
connecting
through
the
intermediary,
they
have
their
first
to
accept
the
policies,
practices
and
principles
of
this
network.
So
can
we
say
that
internet
connection,
thrice
peace,
is
a
form
of
force
Association?
L
Next,
please,
we've
also
been
discussing
which
model
is
better
for
freedom
of
assembly
and
Association,
centralized
or
decentralized,
and
why
both
things
have
to
seem
to
have
their
pros
and
cons
the
centralized
models
they
protect
anonymity
and
privacy.
They
are
usually
more
resilient
networks
and
more
resistant
to
censorship
mechanisms,
but
also
centralized
structures
have
enabled
people
to
group
together
to
identify
each
other
better.
They
recognizable
places
more
visible
and
also
in
some
some
other
cases.
L
They
enable
for
quicker
interactions
and
even
dissemination
of
information.
So
can
we
say
one
is
better
than
the
other?
Yes,
no,
and
why
I'd
love
to
think
I'd
love
to
hear
out
what
you
what
you
think
on
that
next,
please
so,
just
a
quick
set
of
preliminary
conclusions.
The
Internet
does
have
does
impact
the
ability
for
people
to
exercise
their
right
to
freedom
of
assembly
and
association,
and
then
can
we
think
and
assert
that
the
Internet
itself
is
a
form
of
Association
and
assembly
and
therefore
it
should
be
protected
as
such.
L
L
M
L
L
L
B
G
G
So
I
just
want
to
give
a
quick
outline
of
what
this
thing
is
about
and
what
we've
described
in
here
and
some
issues
that
have
already
come
up
in
discussion
on
the
list
and
then
we
can
maybe
have
some
discussion
here.
So
some
of
you
will
remember
that
I
was
one
of
the
critics
of
this
claim
that
protocols
are
political,
that
was
in
the
HR
PC
research
document,
and
there
was
some
back-and-forth
about
it
and
I
think
the
document
ended
up
a
little
bit
weaker
than
it
had
been,
but
also
on
it.
G
You
know
some
of
those
claims
are
still
in
there
and
I
think
that
there's
been
some
some
discussion
about
it.
So
we
wanted
to
understand.
Nielson
I
wanted
to
understand
what
the
possible
positions
are
about
this
and
then
try
to
distinguish
among
them.
So
at
least
we
could
understand
them
and
then
maybe
and
I
think
he's
more
optimistic
about
this
than
I
am.
But
maybe
we
could
answer
whether
there
really
is
a
political
dimension
automatically
to
two
protocols,
and
so
we've
got
some
described
positions.
G
G
Analogies
here
with
mass
media
development
or
traffic
or
dams
and
rivers,
that
kind
of
thing
where,
where
they
change
the
world
and
they
make
the
world
different,
there
is
some
say:
there's
been
some
suggestion.
Actually
that
because
of
this,
we've
got
some
category
mistakes
in
in
the
document
that
some
things
are
are
not
in
this
category.
That
should
be,
or
maybe
there
are
some
things
in
this
category
that
should
be
in
the
next
one.
G
The
the
last
of
these
positions
is
that
the
protocols
are
inherently
political,
so
this
is
the
position
that
was
controversial
before,
and
so
obviously
we
were
trying
to
make
it
as
clear
as
possible
here
and-
and
this
is
the
one
and
I
think
you
know-
Bob-
was
sort
of
suggesting
this
earlier
at
the
microphone.
I
think
this
is
something
that
Neil's
believes
that
the
protocols
are.
Fundamentally,
you
know
politics
by
other
means
you're
making
decisions
and
you're
making
political
decisions.
G
Fundamentally,
there
is
some
some
people
read
the
postman
things,
there's
there's
a
bunch
of
stuff
from
Neil
postman
in
here,
and
some
people
read
postman
actually
to
say
the
previous
category
of
stuff.
I
I
don't
know
what
postman
says
a
lot
of
the
time,
so
I'm
not
I'm,
not
too
keen
on
on
on
adjudicating
that
dispute.
In
any
case,
those
are
the
positions
that
we
were
trying
to
to
outline.
G
Now
we
identified
some
some
issues
in
the
zero-zero
we
hadn't
defined
politics
or
political,
and
it
seemed
that
there
were
a
number
of
cases
where
we
were
stumbling
over
that
so
the
zero
one
that's
already
out,
but
probably
you
haven't
read
it-
has
attempted
to
to
give
a
definition
of
that.
This
is
the
working
one
and
it's
there
on
the
screen
or
you
can
read
it
on
your
own
screens
later
if
you
would
like
on,
but
it
seemed
pretty
obvious
that
this
this
draft
is
gonna,
go
absolutely
nowhere.
G
If
we
don't,
if
we
don't
come
up
with
some
definition
here
so
so
we've
done
that
there
are
some
other
examples
that
people
sent
to
us
feedback
that
we
should
include.
We
didn't
include
the
Raven
process,
but
I
guess
we
probably
better.
Maybe
we
need
some
more
discussion
of
RFC
69
73.
Maybe
there
are
some
other
cases.
So
if
you
have
some
other
cases
that
we
ought
to
be
looking
at,
we
are
keen
to
hear
about
them.
G
Eliot
leer
had
a
really
interesting
set
of
remarks
about
how
the
document
says.
The
ietf
is
not
the
protocol
police
and,
of
course,
it
is
true
that
we
can't
go
out
and
force
people
to
use
our
protocols
or
anything
like
that.
But
there
is
a
little
thing
here
right,
so
we're
quite
aggressive
actually
about
about
our
IP.
Our
rules,
the
the
ITF,
is
extraordinarily
strict
about
what
you
may
and
may
not
do
so
much.
G
So
in
fact,
that
you
know
authors
of
documents
that
are
being
published
in
the
ITF
can't
put
them
under
different
under
different
terms.
They
have
to
go
into
the
IETF
terms.
They
can
put
that
they
can
put
the
document
the
same
document
under
other
terms
somewhere
else,
but
they
can't
publish
them
as
an
RFC.
G
This
has
come
up
several
times
because
people
wanted,
to
put
you
know
a
Creative
Commons
licenses
on
things
and
so
on,
and
it's
not
allowed
and
the
reason
for
that
is
because
the
ITF
s--
IP
our
position
is
that
it
wants
to
control
derivative
works
so
that
some
other
standards
organization
can't
come
along
swallow
the
thing
up
and
then
close
it.
You
know
with
with
a
change
or
something
like
that,
so
that
there's
there's
a
practical
reason
for
this.
G
Well,
that's
a
kind
of
protocol
policing
right
that
what
that
is,
is
an
attempt
to
enforce
certain
kinds
of
abilities
of
other
people
to
do
stuff
with
the
work
product
of
the
ITF.
So
so,
depending
on
how
you
interpret
protocol
police,
there's
a
potential
thing
here
and
I
think
we're
gonna
work
a
little
bit
harder
to
to
tease
this
out
some
more
I
think
in
the
in
the
document:
it's
not
there
yet,
but
it
it
would
be
interesting.
There
was
also
this
other
question
about
a
single
vendor.
G
End-To-End
thing
like
is
that
a
different
political
kind
of
situation?
We
have
a
lot
of
these
now
right.
There's
a
lot
of
stuff
deployed
on
the
internet
very
widely
deployed
on
the
internet,
that
is
end-to-end
controlled
by
a
single
vendor
and
and
maybe
that
changes
that
changes
something
about
it.
So
we
want
to
investigate
that
okay,
so
these
are
the
questions
that
we
have
anyway.
G
First
of
all,
whether
if
this
is
at
all
useful
or
maybe
it's
just
useless
and
we
can
stop
if,
if
we
updated
this,
you
know,
would
we
get
any
more
reviews?
Also,
we
want
to
know
if
people
think
this
is
actively
harmful,
because
there's
lots
of
stuff
that
you
know
you
can
write
down
that
you
shouldn't
and
obviously
there's
probably
stuff,
we've
missed
so
I
invite
you
to
tell
us
what
we've
done
well
or
badly
I
think
that's
it
right.
Yeah.
H
G
H
Oh,
this
is
Shanker
well
I.
Think.
Certainly
you
have
expressed
a
number
of
concerns
several
times
throughout
this
research
group
and
I.
Think
there
can't
be
anything
wrong
with
writing
them
down
in
a
structured
format
like
this
and
making
them
more
clear,
so
I
think
if
nothing
else
the
process
of
writing.
The
document
I
hope
is
helpful
for
people
observers.
D
H
K
Stefan-Boltzmann
speaking,
why
I
have
to
concern
with
the
we
see
a
draft
one
is
that
it
seems
there
was
a
lot
of
overlap
with
HTTP
at
LPC
research
draft,
because
it's
our
protocols,
political,
is
already
is
a
basic
question
of
the
research
draft.
Maybe
one
way
to
solve
this
overlap
would
be
to
focus
on
explaining
to
people,
because
the
research
draft
is
very
harder
to
read.
It's
a
lot
of
things,
a
lot
of
discussion,
so
maybe
your
short
draft
focusing
on
the
ordinary
IETF
participant
and
explaining
why?
K
K
It's
not
clear
for
me
it
if
it
refers
to
volume
2
in
the
elaboration
in
the
creation
of
standards,
the
IETF
work
is
done
by
volunteers,
a
sort
of
thing,
oh,
is
it
about
adoption
and
implementation
of
stand
on
by
the
rest
of
the
world,
which
is
when
we
created
the
standard
with
people
have
to
deploy
it
or
not,
which
is
the
older
question
of
protocol
police?
So
it
seems
to
me
that
the
current
section
9
completely
mix
the
two
things.
Okay,
thank
you.
I
Thank
you
admire
speaking
I.
Think
on
the
protocol.
Police
I
would
think
we
you
could
extend
it
so
far
as
I
understand
you
say
it's
about
IPRs
and
who
creates
and
owns
the
protocol.
But
the
ownership,
in
fact
also
includes,
if
you
how
you
can
extend
the
protocol
and
we
had
issues
in
the
past
practically
from
an
outside
body.
G
I
I
We
were
able
I
think
to
99%
of
these
cases
to
resolve
one
way
or
the
other.
Some
things
like
charging,
lawful
interception
and
so
on.
They
will
stay
problematic
and
always
ray
give
phrase
for
discussion,
but
I
mean
we
have
a
way
of
of
resolving
that
and
I'm
don't
wanna
touch
whether
this
is
good
or
not.
I
just
say
the
fact
that
the
IDF
forced
us
to
practically
delay
our
work
for
quite
a
while
shows
how
powerful
the
IDF
is.
I
At
that
point,
it
was
painful
for
us
in
the
work
that
you
want
to
undergo
here.
It
might
be
a
factor
that
could
be
used
in
a
positive
manner.
The
other
thing
that
came
to
my
mind,
I,
was
I,
didn't
say
that
before
was
when
we
talk
about
such
things,
is
it
and
really
still
the
protocol
or
is
it
not
more
the
protocol
and
who
does
the
protocol?
G
M
M
One
one
way
like
one
way,
I
like
to
illustrate
this,
is
like
using
the
concept
of
like
muscles
hammer.
So
if
the
only
tool
you
have
is
a
hammer,
then
all
your
problems
start
to
look
like
nails
and
so
I
think
like
that,
that's
one
way
the
investor.
It's
why
it's
important!
You
cannot
only
consider
technology
by
itself
also
consider
it's
the
whole
set
of
its
users
when
determine
its
value
think
sit.
G
But
but
you're
not
you're,
not
disputing
that
there
are
people
who
think
that
the
technology
is
neutral
and
all
of
those
values
are
actually
in
the
humans.
I
think
those
people
are
wrong.
Yeah,
yeah,
III
think
the
I
think
the
extreme
position
in
the
other
direction
is
wrong,
but
I
lay
it
out.
So,
okay,
thanks.
F
N
N
G
Right
so
so
then
I
guess
the
question
that
I
would
have
is
is
what
would
you
say
to
Stefan's
point
before
that
the
research
document
is
actually
you
know
it?
It
tends.
It's
got
all
the
survey,
the
literature
and
all
the
rest
of
it
in
it,
and
so
for
a
lot
of
sort
of
IETF
participants,
it's
a
little
opaque,
and
so
maybe
this
is
a
the
you
know.
The
quick
and
dirty
guide
to
aimless
thinking
about
this
or
something
yeah.
O
N
I'm
not
saying
I'm,
not
saying
I'm
anti
decide,
say:
I,
just
don't
know
you
know,
I
mean
I,
don't
know
if
you
can
kind
of
lay
out
or
you
know
the
various
positions
different
people
have
been
aware.
It's
understandable
that
the
ITF
community
and
still
short
and
understandable
to
the
idea
community
right
and
I'm
fairly
clear
that
I,
don't
think
you
want
to
kind
of
pick
one
and
say
this
is
a
this
is
the
right
answer.
Yeah.
G
B
Shortly
speaking
to
the
overlap
on
between
the
research
draft
and
this
draft,
I
think
that
they
claim
that
we
work
out
in
the
research
draft
is
that
protocols
have
an
impact
on
human
rights,
which
is
a
very
different
claim
than
politics
are
political.
So
you
can
say
yes,
Human
Rights
are
political,
but
that
doesn't
make
it
the
same
and
I
think.
What
we
do
here
is
that
we
dive
it's
in
a
similar
way,
as
we
do
with
the
Association
draft.
B
B
G
B
So
here
we
get
to
the
presentation
of
the
hackathon
HTTP
status
code
451
and
there
we
have
the
combination
of
two
of
line
presenters
and
an
online
presenter,
olga
cruz
de
leyva,
al
poker.
Please
come
ahead
and
stand
in
the
purple
box
and
is
meet
echo
working
again
and
if
so
Siobhan,
can
you
put
yourself
in
the
queue?
So
we
have
you
on
the
screen.
Q
So
I
can
tell
that
some
of
you
are
quite
interested
in
implementation,
as
well
as
the
policy
and
perhaps
you've
been
waiting
for
a
bit
to
see
how
these
things
play
out.
So
we're
going
to
look
at
some
of
the
things
we've
done
to
monitor
and
track
the
success
and
the
implementation
of
RFC
seven
seven
to
five.
So
that's
the
HTS
code,
four
five
one.
So
we
were
at
the
hackathon
and
we
got
the
implementation,
so
I
mapped
oka.
Q
This
is
all
go
kristef
aber,
and
so
this
is
what
we're,
what
we're
doing
the
hackathon
we,
which
got
the
best
new
work,
so
it
went
quite
well
and
at
the
hackathon
we
built
tools
that
basically
track
that
they
crawl
and
detect
set
case
of
censorship
online.
So
it
was
a
matter
of
really
trying
to
see
if
this
RFC
is
in
use
its
deployed
its
way
of
declaring
incidence
of
legally
without
content
online.
Q
So
it's
also
quite
a
diverse
participation
from
groups
that
you
may
not
see
in
other
spaces
and
working
groups,
because
it's
represented
by
civil
society
and
I.
Suppose
part
of
the
goal
is
to
bridge
the
gap
between
policy
and
tech,
so
I
think
that
she
been
wanting
to
maybe
look
at
some
of
the
implementation.
Is
that
right?
Q
Q
Okay,
so
the
purpose
like
I
said
it's
three
to
add
some
transparency,
improve
tracking
and
also
to
understand
how
how
the
implement,
if
it
can
be
implemented
if
the
specs
commitment
said
and
used
in
practice
and
what
flaws
there
are.
So
you
find
that
HB
403,
for
example,
isn't
isn't
necessary
suitable
for
this
kind
of
task.
Q
So
the
implementations
there
were
I
think
five,
five
six
invitations.
In
total
there
was
a
crawler
which
scans
the
web
WordPress
plugin,
which
implements
the
actual
status
quo
and
daemon
that
collects
all
the
data
and
centralizes
it.
The
block,
collector
and
a
browser
extension,
a
chrome,
Chrome
extension
that
allows
users
to
report
incidents
that
they
detect
online
as
they
browse
and
also
an
alternative
Prada
which
validated
some
of
the
standards
or.
B
O
O
O
O
O
O
O
D
R
Guess
there
are
a
couple
that
are
more
relevant
than
others
or
more
concerning
than
others,
and
so
one
of
them
was
privacy,
privacy
and
anonymity,
because,
like
the,
if
the
user
tries
to
access
the
website
a
web
page,
that
is
blocked
the
he
or
she
often
would
get
a
four
five
one
response,
but
then
would
get
redirected
so
that
could
include
potential
privacy
breaches
and
it
it
can
mean
that
the
user
can
be
identified.
The
same
is
because
the
four
five
one
is
cached
by
definition,
so
there
is
a
trace
of
that.
R
The
user
tried
to
access
blog
content
on
his
computer.
So
if
the
computer
is
lost
like
it's
possible
to
retrieve
this
information
and
also
the
observers
of
the
network
have
access
to
to
see
who
try
to
access
the
blocked
content,
so
those
are
some
of
the
biggest
concerns
and
in
terms
of
censorship,
it's
it's
a
great
tool
of
censorship,
monitoring.
It
doesn't
solve
the
problem
of
censorship
and
we
make
we
want
to
make
it
to
a
point
that
it's
not
it's,
not
okay,
to
censor
using
four
five
one,
because
it's
not
okay
to
censor
point.
R
So
it's
not
a
way
to
make
censorship
more
ethical.
More
than
anything,
it's
just
a
way
for
for
the
user
to
sort
of
see
why
they
cannot
access
certain
content
because,
as
we
mentioned
in
the
draft,
the
response
should
include
the
legislation
like
the
link
to
why
which
lies
applied
and
why
the
content
is
blocked
and
also
who
made
the
decision
where
there
was
a
court
decision
or
which
governmental
body
actually
asked
for
the
content
to
be
blocked.
So
I
guess.
R
R
And
read
it
in
Turkey
and
some
LGBT
content
appear
to
be
blocked
using
four
by
one,
and
so
we
are
currently
working
on
running
it
in
Russia
and
potentially
there
are
more
countries
where
we
would
like
to
try
it
in
to
sort
of,
monitor
and
measure
censorship
and
yeah,
we'll
gladly
share
them
with
you
and
the
next
item.
It
is.
Q
So
there's
always
balance
to
be
had
between
you
know,
encouraging
a
a
standard
and
and
putting
it
out
there
so
that
people
can
use
it
when
they
need
it.
So
that
might
be
one
of
the
things
that
that's
needing
clarification,
perhaps
in
a
revision.
So
we
do
have
a
few
resources
here
that
you
can
look
at
there's
the
code
on
lining
it
up
and
there's
a
live
demo
as
well
at
net
box,
org,
slash
dashboard,
which
is
an
outcome
of
this
work.
F
S
Spoon
uniting
speaking
I
just
try
to
understand
this
thing:
I
wrecked
the
RFC
just
right
now,
and
what
I'm
wondering
is
understand
that
also
intermediaries,
like
providers,
could
be
ending
out
this
kind
of
four
five
farm
code
to
block
content
on
behalf
of
government
or
whatever,
and
are
there
any
considerations
if
HTTP
is
used
or
the
NSA
kiss
use?
There
is
kind
of
thing,
doesn't
work
anymore,
so
well,
if
they
already
means
on
consideration.
If,
yes,
what
will
be.
Q
So
it
is
possible
to
inject
a
4-5-1
page
in
a
ISP
intercepted
page
page
load,
HTTP
resource
code.
If
it's
not
encrypted,
like
you
say,
with
TLS
HTTP,
there's
a
separate
set
of
problems.
The
content
isn't
visible
to
the
intercepting
party
at
the
moment
for
five
one
use
is
really
envisioned
for
used
by
the
entity
from
which
the
legal
block
has
been
requested
is
the
actual
publisher
which
which
restricts
its
own
content.
Q
So,
yes,
there
is
desire
in
cases
where
authorities
used
block
pages
already
to
have
them
delivered
with
a
4-5-1
status
code,
but
realistically,
there's
no
desire
or
plan
to
put
this
in
any
way
in
terms
of
intercepting
HTTP
content.
I
think
in
that
case,
it's
completely
up
to
the
it's
completely
up
to
the
publisher
on
how
to
do
that,
or
whether
to
do
that
and.
D
S
N
It's
just
a
question:
I
think
you
kind
of
mentioned
it
is
that
there's
you
know
if
people
start
using
this
and
then
you
go
off
and
measure
it
in
some
sense
that
could
distance
end
people
from
using
it
because
then
they
you've
measured
it.
You
might
report
on
that
right
and
have
you
thought
about
kind
of
ways
of
collating
results
are
not
anonymizing
them
necessarily,
but
maybe
you've
done
this
already
of
reporting
out
in
regional
or
functional
or
some
aspects
of
what's
worked
without
necessarily
calling
out
the
person
who's
publishing
before
five
one.
Q
Yes,
we
started
to
look
at
this
and
one
of
the
ideas
we
have
is
to
use
the
IP
anonymization
IP
address'
anonymization
work,
that's
going
on
at
the
moment
where
we
can
choose
a
kay-kay
sample
to
create
a
more
anonymous
grouping
or
because
we
don't
want
to
provide
the
actual
I
physical
IP
address,
but
we
do
want
to
give
an
idea
of
which
hands
which
regions
are
impacted.
So
in
terms
of
monitoring,
these
are
questions
that
we're
looking
at
and
we
need
to
answer
these
questions
so
that
we
can
publish
actual
useful
data.
Q
N
Q
Another
problem
I
mean
one
of
the
ideas
we
had
before
is
maybe
to
put
the
URL
in
a
image,
but
that
also
has
accessibility
issues
and
one
of
the
other
ideas
we
have
is
in
the
protocol,
perhaps
to
encode
the
URL
so
that
it's
not
in
clear-text,
so
there's
a
risk.
If
you
have
a
list
of
all
these
as
blocked
sites,
then
crawlers
are
going
to
consider
your
your
own
site,
which
hosts
the
transparency
report
as
a
dangerous
site.
Q
So
in
our
current
protocol
we
do
specify
and
encoded
an
encoding
of
URLs,
which
I
think
all
implementations
have
switched
to
at
the
moment.
So
the
probiotic
of
the
4.1
URLs
are
actually
base64
encoded
in
the
current
spec
of
the
vertical.
Simply
so,
they're
not
visible,
and
they
don't
become
a
problem
to
people
passing
around
the
data.
Okay,.
A
T
Let's
say:
I'm
part
of
the
fight
against
Internet
censorship
since
many
years
and
we're
trying
to
organize
you
know
if
this
is
just
joke
4-5-1
and
then
it
can
be
used
as
form
of
protest
right
in
the
internet.
So
if,
if
they
force
you
to
remove
something,
you
put
a
4-5-1
on
it
and
as
a
protest,
a
sign
of
protest
that
this
should
not
be
right
and
on
the
other
side,
if
we
start
to
take
serious,
then
we
are
kind
of
like
it
amazing
the
end
of
freedom
of
speech.
T
R
Well,
thank
you
for
your
comment.
I
think
we're
aware
of
this
I
guess.
The
idea
behind
it
is
that
they
are
already
doing
it
and,
for
example,
in
Russia
4-5-1
is
used
a
lot
by
because
there
are
different
laws
that
are
regulating
internet.
There
is
the
law
about
bloggers,
being
distributors
of
mass
information,
and
so,
if
you
don't
register
in
a
certain
registar,
your
site
can
get
blocked,
and
so
there
are
various
laws
that
are
for
a
like
a
citizen
who
is
not
very
much
into
tech.
It's
like
okay,
it's
blocked
by
law.
R
T
Maybe
I
should
add,
then,
as
an
answer
on
what
you
said.
Maybe
the
view
in
Russia
can
be
very
different
from
what
I
said.
I
don't
know
the
situation
there.
I
can
talk
about
the
view
in
Germany,
where
we
have
a
really
fighting
internet
censorship
and
it's
really
a
tough
one
because
they
really
wanted
the
government
wants
it
and
it's
also
a
discussion
even
in
Switzerland,
you
know
known
as
free
country
again
we
have
internet
censorship
on
the
table
politically
and
and
there
is
where
I
was
commenting.
Okay,
thank.
F
You
I
I
had
closed
the
queue.
We've
got
four
minutes
left.
So
really
it's
a
discussion
to
take
to
the
to
the
list
and
because
I
have
a
feeling
it's
gonna
go
on
for
a
bit
but
sorry
but
I
had
I
had
asked
to
close.
Thank
you.
Thank
you
very
much,
and
hopefully
we
could
continue
the
discussion
on
the
list
and.
F
So
really
good
thing
to
discuss
on
the
list:
okay,
just
a
quick
update
on
the
status
since
the
last
time.
Draft
irth
RPC
research
has
gone
through
the
IR
s,
G
review
and
I
guess
it
is
just
about
to
go
into
the
is
G
conflict
check
and
I
on
a
review,
but
Allison
is
coming
to
the
microphone.
So
can
we.
J
F
F
You
yes,
no
throughout
this
week,
nothing
new
came
up
that
needed
to
be,
and
even
through
today's
meeting,
nothing
came
up
that
needed
to
be
changed,
so
I
think
we're
fine.
Thank
you,
RFC
ahead.
Okay,
thank
you
very
much
whoo
and
with
only
two
minutes
left
I.
Don't
know
that.
There's
a
lot
of
time
for
open
discussion
of
the
drafts
papers
and
ideas,
so
I
would
just
like
to
say
that
submit
them
to
the
list
and
we'll
get
them
talking.
Did
anybody
have
a
quick
something
they
wanted
to
say
like?
F
B
F
Change
it
because
there
were
comments
last
time,
so
we
want
to
see
if
we
did
the
right
thing
and
changing
it
at
this
point,
seeing
nobody
at
the
mic
and
nobody
with
anything
to
say,
I
guess
we
had
a
whole
minute
extra.
That
I
could
have
let
people
talk
earlier,
but
thank
you
and
thanks
for
coming,
even
though
there
was
a
bunch
of
other
good
stuff
going
on.
At
the
same
time,
please
be
active
on
the
list.
Please
come
up
with
new
drafts,
Thanks
Oh.
