►
From YouTube: IETF99-LAMPS-20170717-1740
Description
LAMPS meeting session at IETF99
2017/07/17 1740
https://datatracker.ietf.org/meeting/99/proceedings/
A
So
on
the
mail
list,
Jim
shot
agreed
to
be
the
jabber
scribe
and
yolks
various
agreed
to
be
the
note-taker.
So
thank
you
very
much
for
that.
I
just
started
the
blue
sheets
around
so
I
just
sent
one
clipboard
because
it
looks
like
we're
probably
going
to
be
small
enough
that
we
can
fit
and
with
somebody
in
the
back
close
the
doors.
Please
there's
at
least
from
here.
It's
a
fair
amount
of
noise.
A
A
A
A
Okay,
so
next
item
on
the
agenda
is
we
have
four
documents
that
is
there.
All
of
our
chartered
work
is
now
with
the
ISG.
We
put
these
action
or
all
of
the
items
in
number
two
to
a
through
2d
to
deal
with
any
comments
on
those
documents
and
I
have
not
seen
any.
Is
anyone
aware
of
some
that
have
not
made
it
to
the
to
the
mail
list
yet.
B
We're
doing
slides
off
your
laptop,
yes,
hello,
I'm,
Phil
and
I
do
Pete,
so
this
is
next
slide.
So
basically,
the
situation
here
is
that
since
CIA
was
originally
specified
in
22:13,
we've
now
got
to
the
point
where
deployment
is
going
to
be
mandatory
for
web
PCI
certs
from
8th
of
September
and
when
certain
CA
started
implementing
it.
First
of
all,
people
started
saying:
well,
this
part
of
the
spec
is
ambiguous
and
so
I
said
well
right,
I'll
fix
it
and
then
after
I
clarified
it
people
said
well.
B
Actually
we
preferred
it
the
old
way,
and
yes,
so
basically,
the
orig
the
basis
here
is
that
the
original
intent
that
we
had
is
obsolete
in
that
we
were
trying
to
do
something
technically.
One
way
and
the
way
that
we
we
use
the
web
and
the
internet
has
changed
in
particular.
Cd
ends
have
changed
it
and
as
a
better
proposal,
so
I've
gone
to
the
next
slide.
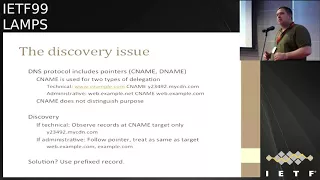
So
what
if
this
relates
to
is
the
discovery
issue?
B
Dns
has
this
pointer
mechanism
and,
as
you
all
know,
pointers
means
problems,
and
so
you
have
a
pointer,
there's,
actually
two
types:
e
names
and
D
names
in
terms
of
the
on
the
wire
protocol,
you
only
ever
see
C
names
unless
you're
doing
DNS
SEC,
and
it
turns
out
that
there
are
two
subtly
different
types
of
delegation.
These
are
used
for.
One
type
is
the
purely
technical
delegation
that
the
DNS
people,
conceived
of,
which
is
I.
B
So
originally
we
thought
that
the
type
of
delegation
that
we
were
supporting
was
this
administrative
delegation
of
I
have
a
large
portfolios
of
names.
I
want
to
port
them
all
point
them
on
the
same
direction,
and
if
you're
doing
that,
then
the
logic
would
be
that
you
would
follow.
You'd
follow
the
pointer,
and
then
you
treat
that
pointer
as
if
that
was
your
starting
point
for
your
search
and
traverse
the
tree
up
from
that
point.
B
B
One
of
the
things
here
is
that
we're
talking
in
terms
of
CAA,
but
obviously,
if
you're
doing
this
type
of
discovery,
anything
else
that
looks
like
CAE
should
probably
discover
in
the
same
basis,
so
we've
got
to
get
it
right
and
then
a
bit
of
text
to
justify
it
and
the
milestone
of
abyss.
Draft
of
684
for
April
2018,
which
I
think
is
very
doable
so
comments.
A
Any
other
comments:
okay,
I'd
like
to
kick
a
quick
comm,
just
to
get
a
sense
of
the
room
who
would
like
to
see
this
action
included
in
the
recharter,
yes
and
then
hum
No.
So
who
would
like
to
see
this
included
in
the
proposed
revised
Charter?
Now
for
yes
hum
now,
for
no
that's
very
clear,
there
was
silence
for
now
so
alright.
Thank
you
very
much.
Thanks
for.
E
E
E
The
reason
for
me
to
propose
these
two
functions
over
the
char
trees,
because
they
can
do
only
Chaudhary
I
can
do
and
the
shake
256.
It
has
two
times
better
performance
and
like
one
of
the
same
performance
improvement
over
the
shot,
three
512
and
they
shake
one
per
day.
It
has
like
24
percent,
better
performance
than
the
shot
3
256.
E
D
D
E
And
one
more
advantage
for
using
the
shakes
over
the
SHA
threes
right
now.
Is
that
for
the
shake
you
can
do
the
one
pass
Mac
very
nice
way
so
is
this
would
be
very
efficient
in
in
macking
and
also
if
you
do
generate
a
random
number
generation,
it
would
be
the
same
thing
to
it.
One
single
pass
very
efficient
and
the
shake
is
build
based
on
random
permutation,
but
basically
going
to
be
random
functions
because
we
have
the
the
capacity
would
be
trunk
turn
off
from
the
output.
A
E
I
didn't
understand
the
question.
I
thought
you
asked
me
how
this
kind
of
thing
want
to
be
used,
because
you
asked
on
a
Mac.
Mac
is
a
possibility.
People
could
do
ashmac
with
any
hash
function,
but
with
this
construction
you
don't
need
to
do
H
Mac.
You
do
one
pass
and
you
gain
a
lot
of
performance
from
it
and
it's
proven
secu.
You
have
to
need
to
follow
the
D
structure
that
we
have
with
the
one
I-185
SP.
When
I
five.
D
E
E
D
E
E
So
currently,
if
you
use
sha-512
what
P
384
that
what
would
happen
and
it
will
happen
the
same
thing-
we
shake
to
512
/,
no,
shake
256,
last
fight
off
right
now
and
the
same
thing
with
shake
128
output
with
output,
256
bits,
that's
good
for
us
say
good
for
anything
else.
If
you
do
P
256,
that
would
be
fine
perfectly.
If
I
or
I
say
is
fine.
I.
C
C
E
As
well
said,
they
say
that
they
did
propose
I,
adopt
as
a
tentative
or
or
or
you
know,
alternative
just
in
case
something
happens,
and
people
don't
want
to
use
shall
to
and
sorrow
is
still
good
by
now,
I'm
not
saying
so
too
bad
but
whole
purpose
does
not
replace
you
out
it
just
alternative
to
saw
and
in
case.
If
we
will
want
to
use
it,
they
can
use
it
sure.
F
Yeah
I
mean
I,
think
we've
been
trending
in
security
towards
having
fewer
code
point
assignments
for
safer
alternatives.
They
don't
have
a
clear
security
rationale
and
it's
completely
clear
with
the
security
rationale,
for
this
is
so
I
guess
I
would
be
in
favor
of
heavy.
If
you
were
stuff
like
an
informational
core
points,
I
don't
like
a
not
recommended
marker
on
it.
F
Mean
that
the
only
two
divers
that
we
are
act
that
we're
actively
used
actively
using
now
are
a
ES
and
ChaCha
and
both
of
those
have
clear
security,
clear
rationales
for
why
you
use
one
versus
the
other
AES
because
of
AES
and
I
it
was
the
standard
in
cha-cha
box
is
much
much
faster
on
non
AES
and
I
systems.
So
what
is
the
rationale
for
this?
For.
E
Their
strong
rationale
for
this,
because
shake
design
is
weighted
from
from
any
a
Exodus
I
such
as
saw
to,
and
is
it's
very
secure,
the
security
margin
right
now
is
high
or
or
if
you
check
overall.
So
those
are
security
reason
for
for
for
for
the
shakes
and
short
three
to
stand
on
their
own
feet
over
here
and
internal
performance,
it
compatible
to
take
available
to
sha
204
now
Sherpa.
F
Shutter
is
like
a
giant
security
merchant
about
and
if
we
do,
if
we
thought
that
wasn't
true
than
we
had
and
we
shot
have
shot,
512
I
mean
so
I
I'm,
just
not
understanding
like
the
back
up
the
sha-256
and
sha-512
and
I
understand
this
Twins
lon
I
got
wanna.
Have
for,
did
you
shot
three?
That's
not
our
problem.
Oh
I
mean
I,
guess
I
feel
like
I
feel
like
this
keeps
coming
by
and
saying
like.
Why?
Don't
you
have
shot
three
and
like
they
keep
getting
the
same
answer?
Which
is?
Why
did.
E
F
E
B
Disagree
with
Acker
here
I
think
that
it's
important
for
every
cryptographic,
primitive
that
we
have.
We
should
have
exactly
two
algorithms,
one
that
we
can
use
for
current
deployment.
That
is
hopefully
both
should
be
supported
everywhere,
but
one
should
always
be
a
backup
algorithm,
because
the
thing
is
that,
if
you
are
once
you
know
that
something
is
weak
and
you
want
to
get
away
from
it,
it
is
too
late
what
they
tell
you
to
start.
B
Yet
it
takes
us
over
ten
years
to
change
an
algorithm
I
warn
people
when
Shah
to
came
out
I
said:
we've
got
to
start
deploying
it
now,
and
everybody
said:
oh
now
we
don't
and
then,
when
sure
people
decided
that
sha
Wan
was
about
to
be
broken.
Suddenly
they
come
to
camp
form
and
say:
okay,
we
got
to
phase
out
shall
warn
before
certificates
that
have
been
already
issued.
Our
own
use
will
expire,
so
it
went
from
okay.
We've
got
plenty
of
time
to
okay,
stop
using
it
now.
B
So
that's
a
data
point
of
no
I'm
not
satisfied
with
there'll,
be
time
to
deploy
something
else
in
the
future.
I
think
that
we
want
to
have
two
algorithms
for
each
cryptographic,
use
that
are
based
on
distinctly
different
cryptographic,
primitives
so
for
public
key
we've
got
RSA
and
we've
got
the
elliptic
curve
alternative
for
for
symmetric
crypto.
We've
got
a
EES
and
we
got
cha-cha
now
and
I.
B
D
D
F
Wait
so
I
I'm,
I,
guess
sort
of
okay
with
a
Mac
out
rhythm.
Here,
though,
likes
not
clear
to
me
what
setting?
What
setting
do
people
do,
knocking
enough
data
that
this
performance
issue
is
important.
This
always
comes
up
and
like
in
all
in
all
in
all
the
semantic
settings
we
have
so
so
in
every
setting
where
you
want
in
cypher,
you
should
be
using
an
AED
algorithm,
and
so
what
setting
do
people
do
enormous
size
max?
So.
F
No
time
right,
that's
my
point
and,
and
it
has
to
be
a
finicky,
did
it
not
the
original
in
Acadia
force
using
a
deal.
No,
that's
that's
off
envelope,
but
I
I
know
I,
understand
I'm,
just
saying
like
that
in
any
setting
where
you
want
to
been
using,
we
want
both
both
properties.
You
should
be
using
AGC
I'm,
not
using
absolutely.
G
From
gondwana
I
just
wanted
to
respond
to
Phil's
idea
that
you
have
exactly
two
algorithms,
one
of
which
you're
using
and
one
of
which
you
aren't
that's
the
same
as
having
exactly
one
algorithm.
The
problem
with
upgrading
is
that
there's
broken
implementations
in
the
field
or
implementations
that
don't
support
your
new
thing
and
they
all
need
to
be
upgraded
before
you
can
use
the
new
thing.
If
it's
not
being
used
at
all,
it's
not
going
to
be
tested.
It's
not
going
to
work
when
you
suddenly
have
to
switch
to
it.
B
A
data
point-
I,
don't
think
that's
been
raised
here-
is
that
if
you're
going
to
do
add
four
four
eight,
you
have
to
do
char
three
anyway.
So
it's
not
like
we're
adding
another
module
to
the
crypto
environment.
We're
just
saying
here
are
the
code
points
to
use
it
as
a
backup?
I
I
saw
two
responded
to.
A
E
Two
to
two
comments:
if
you
had
a
backup
some,
some
people
are
probably
going
to
use
it
not
like
everywhere,
but
it
doesn't
mean
that
it
just
sitting
down
nobody,
you
use
it.
Some
people
might
might
want
to
use
a
short
three
because
it's
ready
and
they
have
some
reason
to
do
so.
We
just
I
can't
conclude
that
you
know,
for
example,
like
sha-512,
is
a
kernel,
a
backup
for
sure
to
very
sick,
for
example,
for
example.
But
Debbie
will
you
start
off?
It's
not
like
I
sitting
there
there's
nothing
yeah.
G
I
just
want
to
replace
the
idea
that
some
people
trying
it
occasionally
is
enough.
There
will
be
implementations
that
don't
support
it
correct
and
nobody
will
discover
until
it's
too
late
and
you
need
to
upgrade
to
it
at
which
point
their
implementations,
that
don't
you
drop
right
anymore.
You
need
to,
if
you're
going
to
specify
something,
then
it
needs
to
be
a
tested
configuration.
It's
used
enough
that
everyone
will
be
testing
with
it
before
you
before
it
becomes
your
only
option.
Yes,.
E
Oh
yeah
so
hope
that,
if
it,
if
it
were
to
be
adopted-
and
some
vendors
here
would
have
some
coal
burning
and
tested-
that's
my
hope,
but
it's
up
to
people
here
if,
if
they
they
want
to
use
it.
The
reason
and-
and
the
reason
is-
are
excellent
to
me.
But
people
might
disagree
with
what
what
I
think
but
I
I
see.
The
reason
is,
is
various
very
strong
and.
H
A
Okay,
let's
do
a
hum
is
in
doing
the
recharter.
Do
we
want
to
include
this
in
the
proposed
text
to
the
is
G?
Yes
and
no
okay.
Do
we
want
to
include
the
shake
part
of
the
specification
for
P
kicks
and
s/mime
in
the
recharter
hum
now,
for
yes,
come
now
for
no
that's
pretty
clear,
okay!
Thank
you.
Quinn
thank.
B
B
They
said
when
I'm
looking
at
the
Civic,
because
you
know
that
if
you're
on
a
site
and
the
certificate
is
like
six
months
old,
if
that
site
is
much
less
likely
to
be
fraudulent
than
one
that
is
five
seconds
old,
because
you
know
it's
not
being
taken
down
and
with
certificate
transparency.
This
means
it
becomes
even
more
so
because,
presumably
there
are
people
looking
at
the
certificate,
transparency
logs
or
pay
people
to
look
at
them
to
detect
fraudulent
or
confusing
registrations.
B
So
all
the
certificates
are
evidence
of
longevity,
and
so
the
solution
that
was
proposed
then
was
this.
Member,
since
extension,
you
know
see
like
you
have
on
your
American
Express
card.
If
you
have
an
American
Express
card,
it
says
how
long
you've
been
with
the
company
and
so
anyway,
so
that
next
slide
please.
So
why
now
well?
Short-Lived
certificates
are
coming
back
onto
the
agenda
and
the
other
reason
is.
We
started
to
get
issues
together
with
user-accessible
safety
and
Meishan
in
that
one
of
the
problems
with
the
current
internet
and
web.
B
That
is
a
piece
of
information
which,
when
they
see
it,
actually
conveys
useful
data
to
them,
because
they're
used
to
judging
the
you
know
in
meatspace,
you
look
at
you're
going
to
affirm,
it
says,
established
2019
97,
and
that
tell
you
something
so
and
we
were
looking
at
this
for
us
a
browser
project.
So
next
slide
objections
that
I've
received
back.
One
of
them
was
well.
We
owned
the
browser
houses,
the
only
browser
that
counts
and
we're
in
where
the
other
people
are
going
to
decide.
F
B
B
Do
have
a
browser
we
do
have
you
know
a
few
million
users
and
another
objection
was
that
well,
revocation
doesn't
work,
Peak
extent,
work,
CAS,
don't
work
and
I.
Don't
think
that
that
you
know
if
you're
doing
web
PK
are
you
doing
P
kicks,
and
one
of
this
is
a
piece
of
information
that
the
CA
can
put
in
a
certificate
in
an
auditable
fashion.
B
The
main
issue
that
has
come
up
that
is
tricky
is
this.
Information
is
in
certificate
transparency.
So
why
didn't
just
look
there
and
the
there
are
two
ounces
I've
got
to
that.
Why
is
that,
if
you're
going
to
say
okay,
that
information
is
in
certificate
transparency,
you
just
go
look
well,
then
somebody's
got
to
write
a
draft
to
explain
how
to
look,
and
that's
probably
going
to
be
a
lot
more
complicated
than
a
draft.
That
says
here
is
the
extension.
B
The
other
thing
is
that
I'm
not
sure
that
anybody's
talking
about
writing
their
browser
in
such
a
way
that
the
browser
is
going
to
proactively
grumble
through
the
CT
logs
and
obtain
this
information,
and
so
they
can
present
it
to
the
user.
I,
don't
think
that's
going
to
happen
and
the
sort
of
the
particular
context
in
which
I'm
thinking
about
using
this
is,
if
I
get
a
certificate
that
says
that
it's
been
around.
This
key
has
been
around
or
this
subjects
has
been
around
for
five
years.
B
Maybe
then
I
don't
insist
on
getting
the
revocation
information.
However,
if
I
get
the
certificate-
and
it
says
okay-
this
was
issued
in
the
past
five
hours-
then
maybe
I'm
going
to
be
very
particular
and
check
before
I
take
the
user
to
that
site.
So
it's
not
a
question
about
getting
access
or
blocking
access
to
the
site.
It's
a
question
of.
Is
this
a
part
of
the
internet
where
the
browser
wants
to
make
additional
checks?
B
So
if
you
go
to
the
next
slide,
so
this
is
the
proposed
Chartist
text
saying
examing,
so
you
know
basically
we'd
have
to
look
into
this
a
bit
further
before
deciding
whether
to
go
on
it.
Perhaps
in
that
it
might
one
of
those
things
that
when
you
actually
try
it
out
in
practice,
it
turns
out
not
to
be
such
a
good
idea,
but
that's
a
chat
attached
I.
J
Feel
Robin
Wilson
from
Internet,
Society,
I
I
know
you
thought
this
through,
but
I
wanted
to
kind
of
test.
One
angle
of
it
from
the
user
experience
perspective
and
particularly
about
short
lived,
serves,
I.
Think
I
mean
you
and
I
have
talked
about
this
before
at
night.
Yes
about
the
number
of
warnings
that
I
get
from
a
browser
plug-in
that
says
this
certificate
has
changed
right.
J
You
might
want
to
worry
about
it
and
actually
there's
there's
a
there's,
a
long
random,
looking
prefix
in
the
URL
of
the
certificate
points
to
and
at
the
time
I
had
a
privacy
concern
about
that
because
it
appeared
to
me
that
might
be
a
linkable
value.
You
reckoned,
it
was
probably
actually
more
likely
to
be
an
artifact
of
things
like
server
farms.
J
B
Yeah-
and
here
we
come
to
a
problem
with
UI
and
web
browsers,
and
one
of
the
problems
is
that
the
security
UI
community
has
basically
done
a
bad
job
all
right.
We
had
this
with
s/mime,
where
you
send
somebody
assigned
s/mime
email
and
what
would
come
out
was
warning.
This
message
is
signed
and
it's
kind
of
like
you
know
the
security
UI
people.
Basically,
the
pathology
has
been.
They
tried
something
that
bombard
the
user
with
a
lot
of
useless
information.
They
then
conclude:
oh,
this
is
impossible,
because
our
crappy
approach
didn't
work.
B
Therefore
nobody
can
do
it
and
so
because
they
did
something
that
we
told
them
wouldn't
work
and
because
they
kept
doing
it
and
because
they
weren't
ever
asked
us
how's
a
way
that
might
work
we're
in
this
cycle
of
they're,
saying:
oh,
you
can't
just
usable
UI.
You
can't
present
the
user
with
safety
information
that
makes
sense
to
them
it's
impossible
and
now
I,
don't
think
it's
impossible.
But
maybe
the
solution
requires
a
garbage
collection
on
certain
institutions,
security,
usability,
people,
Robin.
J
Wilson,
just
very
one
one
very
quick
comeback
in
the
normal
run
of
events,
just
using
my
browser,
I
wouldn't
see
any
of
that
stuff
at
all,
even
legitimate
warnings.
It's
only
because
I've
got
a
third-party
plugin
that
I'm
seeing
any
of
it
right,
even
though
it
may
be
presented
in
ways
that
you
think
are
or
poor
UX
which
I
agree
with,
but
that
my
point
is:
how
do
we
avoid
the
bad
pots
that
UX,
given
what
you're
trying
to
achieve
here?
Okay,.
B
Well,
the
other
question
here
since
you're
from
Internet
Society
and
since
you've
just
made
the
acquisition
of
OTA.
That
is
not
a
part
of
this
problem.
I
think
belongs
in
ITF
space,
because
ICF
has
said
that
he
doesn't
want
to
do
user
experience,
but
the
OTA
has
done
user
experience
and
in
onal
way,
is
all
about
user
experience.
So
that
will
probably
be
a
part
of
the
problem
to
take
that.
K
Well,
Hofmann,
so
you
said
at
the
beginning,
you
hadn't,
given
us
a
draft,
so
I
think
it's
way
too
early
for
us
to
look
at
charter
tax,
because
I
have
no
idea.
What
first
issued
means
first
issued
by
this
CA
first
issued
by
NECA
first
issued
by
a
CA
who
trusts
another
CA
to
have
issued
it
earlier.
I
would
really
want
to
see
a
little
bit
more
definitiveness
on
what
the
intent.
You
know
what
what
the
intended
extension
semantics
would
be
before
we
considered
a
charter
issue.
F
B
B
F
Yeah
I
mean
it's.
It's
certainly
true
that,
like
that,
when
you
click
on
the
pack,
padlock
icon,
you're
clicking
off
things
like
eventually
we'll
show
you
like
the
entire
certificate
right
but
like
which
I
guess
my
website.
Sorry
things
that
been
that
sense,
I
suppose
it's
true,
but,
like
my
question,
I
suppose
was
it
was
really
which
seat
which
relying
parties
do
you
think
are
interested
in
being
real
with
this
information
of
the
user
in
some
way.
Well,.
B
Right
now
we
have
all
these
projects
to
try
and
explain
to
people
how
to
be
safe
online,
but
we
don't
have
an
ability
to
tell
them
how
to
be
safe
online,
because
I
mean
like
the
UI
is
all
over
the
place.
Alright
yeah
one
browser
has
changed
its
certificate
UI
for
us
to
sell
what
is
it
five
times
in
the
past
year?
Sure.
F
No
I
understand
that
yeah
I
mean
like
control
your
cars
earlier,
like
those
decisions
were
made
based
on
security
research,
not
based
on
just
like
the
idiots
it
was
announced
by
the
way,
so
I
guess
I.
Just
don't
understand
like
like
who,
like
the
that
my
impression
is
that
most
of
browsers,
that's
all
major
browsers.
Every
er
said
nothing
arrived
no
interest
in
this,
so
I'm
trying
to
figure
out
like
who
the
consumers
are
so.
L
I
have
an
answer:
rich
solves
I
think
it
would
be
useful
in
email
or
other.
We
decrypting
or
verifying
signatures
that
were
generated
a
while
ago
and
you've
got
a
cert,
and
then
you
can
see
that
yes,
this
was
the
same
thing
that
happened
back
when
it
was
first
time
to
encrypted.
That's
that's.
That's
a
more
useful
use
case
to
me
than
the
web.
Dki.
C
So
hi
this
is
Sean
Turner
again,
so
realizing
that
you
started
your
presentation
off,
but
you
wanted
to
start
off
with
some
fireworks
and
we
have
the
internet,
so
I
went
and
did
a
search
for
what
happened.
Last
time
and
the
summary
from
the
me
nuts
from
726
and
O
7
was
that
there
was
three
things
you
proposed.
The
list
discussion
was
not
deference
proposals.
C
M
M
N
B
Well,
you
have
a
validation
criteria,
but
in
this
case
I
mean
like
enact
me.
We
now
have
the
ITF
specifying
validation
criteria
as
a
technical
level.
I
was
thinking
that
the
validation
criteria
would
be
purely
technical
now,
obviously,
with
anything
that
ITF
does
in
this
area.
If
you're
going
to
use
in
the
web,
peek
yeah
it's
going
to
have
to
be
considered
at
cab
forum
at
some
level.
N
B
D
Channeling
sean
leonard
I'd
like
to
see,
or
at
least
compare
with
the
date
the
organization
was
established,
the
point
being
that
that's
probably
more
actionable
for
an
end
user
or
for
a
computer.
If
continuity's
desired
a
pointer
to
the
prior
cert,
our
private
key
would
be
more
actionable
private
key,
it
does
say
private
key.
K
So
Paul
Hoffman
again
I
want
to
reiterate
what
I
said
before,
based
on
some
of
the
answers
you've
given
since
and
actually
sort
of
to
echo
what
Stephane
just
said:
I
don't
want
to
be
locked
into
my
CA
cuz
I
can't
find
another
CA
who
will
change
from
my
current
one.
I.
Don't
want
to
have
to
do
this
based
on
CSRs
and
I.
Don't
want
to
take
my
web
key
and
somehow
sign
something
else.
That
is
like
a
message.
So
I
really
want
to
see
a
lot
more
here
before
we
okay.
C
K
Go
forwards
on
that,
because
I
could
and
I
think
Stefan's
right.
If
this
is
something
that
CAS
want,
or
even
a
small
group
of
CAS
want,
let
them
say
this
is
sort
of
what
we're
thinking,
how
we
would
do
it
and
then,
and
then
just
do
the
simple
part
of
how
the
extension
would
go
in,
but
a
single
CA
could
could
easily
lie
about
this.
They
could
say:
oh
well,
I,
remember
that
you
did
the
first.
K
You
know
that
I
issued
this
first
for
you
a
lie
ago,
a
bad
CA
who
had
forgotten
that
could
either
put
it
way
in
the
past,
or
only
the
last
cert
you
did,
even
though
you
done
longer
so
I
think
that
we
need
better
information
on
how
this
would
go
before
we
actually
do
the
easy
part,
which
is
you
know,
what's
the
oeid
for
the
extension.
Yes,.
B
B
O
So
you
have
new
I'm,
not
ruling
anybody
else.
The
thing
is
and
well,
if
I'm
connecting
to
Microsoft
site
and
yeah,
they
should
have
a
key
since
95
Google.
Well,
they
should
have
a
key
since
98,
but
I've
just
found
this
store
that
sells
dog
food
on
the
Internet
one
month
is
fine.
Ten
years
is
fine,
I,
don't
know
how
long
they've
been
around
and
I.
Don't
I,
don't
think.
That's
really
a
good
signal
for
end-users.
O
B
It's
one
of
those
things
with
any
signal:
you've
got
the
problem
of
false
positives
and
false
negatives
right,
and
this
is
not
a
signal.
That's
ever
gonna
give
you
a
clear,
go
no-go
signal.
However,
if
you've
got
something,
that's
only
been
created
in
the
past
day
or
five
days
there
and
it's
present
presenting
itself
as
a
bank
that's
been
around
for
200
years,
then
maybe
you
want
to
look
at
this
second
time
before
you
hand
over
your
password
or.
F
Yeah
yeah
I
mean
I,
was
sort
of
persuaded
a
little
bit
by
Richards
point,
but
I
think.
If
you're
pidgin
is
as
for
the
web,
then
you
really
need
to
engage
with,
like
the
Weber
wine
party's
dangers
in
this
and
so
easier
to
present.
This
is
something
that
is
not
for
the
web,
in
which
case
then
you
make
a
separate
case
or
he's
like
engaged
with,
like
the
fact
that,
like
Chrome,
Firefox
and
I,
don't
see
Apple
and
I
either
they
want.
It.
I
mean
like
what
the
sort
of
natural
environment
I'm
sorry
yeah.
G
B
B
B
L
Rick
Sol's
yeah
I
have
a
problem
with
I
understand,
like
is
a
apple
pie
and
motherhood
kind
of
thing.
You
want
to
protect
users
and
keep
tell
them.
Oh,
this
is
the
good
part
of
the
internet
on
the
you
know,
you're
on
the
thoroughfares,
and
this
is
the
sketchy
part.
Some
of
us
live
on
the
wrong
side
of
the
tracks
and
the
problem
is
you
can't
define
that
and
you
can't
define
that
algorithmically
and
I,
don't
think
how
long
an
organization
has
been
paying
tithes
to
a
commercial
organization?
L
A
Okay,
we're
ready
for
the
hum
so
it'll
be
how
many
people
think
that
the
first
issued
extension
should
be
part
of
the
proposed
charter.
Yes,
and
no
so
how
many
people
think
that
the
first
issued
text
should
be
part
of
the
proposed
charter
hum
now
for
yes,
now,
for
no,
we
had
three
unanimous
homes,
but
not
all
in
the
same
direction.
All
right
that
was
our
last
charter.
Genda
item
we're
gonna
finish
a
whole
like
eight
minutes
early.
Thank
you
very
much
and
have
a
good
good
evening.
