►
From YouTube: IETF99-TSVWG-20170718-1330
Description
TSVWG meeting session at IETF99
2017/07/18 1330
https://datatracker.ietf.org/meeting/99/proceedings/
A
A
A
B
A
C
C
So
we've
identified
note
takers
and
jabber
scribes
diverse
crowd.
Thank
you.
Thank
you
all
very
much.
We,
as
always
when
the
reviewers
were
working
group
drafts,
will
ask
as
we
go
to
this
session.
People
take
a
look
at
things
and
a
reminder.
Please
use
TS
UWG
with
before
and
after
as
part
of
the
name
of
draft
submitted.
If
you
want
us
to
notice
it
we'll
say
that
that's
what
we
look
for
in
trying
to
figure
out.
What's
what's
relative
the
meeting
a
standing
document
view
request.
C
Doctor
quality
relies
on
reviews,
please
review
documents
in
your
working
group
and
at
least
one
of
the
DUP
for
another
working
group
in
general.
If
you'd
like
documents,
you
care
at
review,
please
put
the
effort
to
review
other
documents:
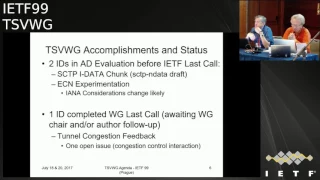
ok,
collards
and
status.
We
got
four
RFC's
published
between
1987
97
98
between
seoul
and
chicago,
so
we've
had
no
our
sees
published
since
then
they
seem
to
coming
back
in
in
waves,
we're
working
on
creating
next
one.
C
There
are
turner
drafts
in
the
RFC
under
queue
diffserv
and
with
rtq
OS,
and
the
details
in
Kappa
CTP.
Both
of
these
are
in
miss
rep
state
for
the
SCTP
end
data
draft,
about
which
we
have
good
new
good
good
news
report.
There
are
no
IDs
and
ietf,
but
no
no
drafts
on
ie,
less
Club,
post,
ITF
class
call
processing,
but
we
hope
to
see
that
change.
C
So
the
end
data
draft,
which
is
two
drafts
the
arcs
and
are
waiting
for,
is
now
in
ad
evaluation
before
IETF
last
call,
as
is
ecn
experimentation
and
within
in
just
a
little
bit.
We'll
talk
about
some
minor
changes.
Committee
EC,
an
experimentation,
there's
been
some
discussion
about.
Will
they
do
about
I,
Anna
duration,
attract
Tom,
Josh
and
feedback?
We
have
an
open
issue
with
that
draft.
Leaburg
last
call.
We've
talked
to
the
area.
Directors
will
need
to
go
talk
to
the
authors.
C
We
think,
unfortunately,
that
significant
changes
that
draft
are
going
to
be
required
to
to
to
resolve
that
open
issue
or
anything.
The
time
due
to
feedback
draft
draft
offers
here
today,
we'll
take
it
up
with
them
offline,
but
some
significant
changes
are
coming
are
going
to
going
to
your
card
that
draft
Spencer.
D
So
yes,
mr.
Dawkins
responsible
area
director,
the
I
did
a
chunk
draft
I'm
about
halfway
through
idea,
evaluate
the
evaluation
on
and
I
really
like
it.
I
am
I'm
generally
a
decent
number
of
comments
that
most
of
them
are
questions
about
clarity,
the
easy
and
experimentation
one
versus.
Do
we
closed
on
the
on
what
that?
Really?
What
that
one
really
needs
to
say?
Yes,.
C
Won't
you
that
know
it
seems
parent
ation
is
going
to
do
what
releasing
instrumentation
draft
does.
Is
it
D
it
documents
the
end
of
the
ECM
knots
experiment
and
provides
the
rationale
for
making
are
the
ECM
naughts
RFC
of
chars
thirty
five,
forty
historic
we're
going
to
add
one
line
to
that
that
removes
the
registration
of
the
flag
in
the
TCP
header
that
was
used
by
the
by
the
ECM
knots.
Accurate
ecn
needs
that
flag.
The
TCP
M
working
group
will
figure
out
how
to
use
that
flag
for
accurate,
accurate
to
easy
end.
D
C
C
C
E
C
C
C
That's
here
we're
gonna,
do
that
today
and
the
Tim's
got
a
few
slides
on
what
he's
going
to
do
about
it.
The
good
news
is
the
mappings.
The
code
point
mappings
are
stable.
All
the
changes
and
all
the
discussion
is
around
is
Ron
traffic
conditioning
text
and
what
what
you
do
is
sort
of
class
the
traffic,
but
not
not
the
base
mappings.
We
are
hoping
to
get
through
the
serious
open
issue
on
the
diffserv
Laura
effort.
C
Ph
be
draft
today,
which
is
which
DSC
PDUs
once
we
get
through,
that
money
should
be
ready
to
go
to
work.
The
last
call
and
we've
got
eight
more
working
groups
drafts
all
the
tool
will
will
get
covered
today
and
Thursday
a
couple
for
one
and
two
are
eating.
Encapsulation
three
and
four
more
SVT
piece
of
four
five.
Six
and
seven
are
l4s.
Eight.
Is
you
the
options
draft,
but
wait.
There's
more
as
note
of
the
mailing
lists,
we
are
announcing
the
adoption
of
the
these
two
FEC
for
two
error
correction
drafts
Vincent.
C
Our
workers
been
working
on
these
I
have
not
had
time
to
update
these
slides.
The
agenda
is
updated.
These
are
now
working
group
drafts.
I
will
probably
might
cope
with
spare
time
for
use
of
v3
of
these
slides.
That
gets
these
draft
names
updated
to
the
to
the
correct
draft
names
for
the
working
group.
Grass
reason
for
doing
this
is
th.
Dwg
is,
among
other
things,
the
home
of
a
maintenance
work
on
transport
area
protocols
that
doesn't
justify
for
me
its
own
working
group.
C
C
Interested
right
so
offline
discussions
here,
you
may
seem
to
come
back.
There
are
three
drafts
related
to
TC
BG
that
are
over
on
the
inch
area
agenda
this
time
around.
The
interior
tunnels
draft,
which
we
talked
about
here
number
times
of
four
MTU,
is
a
particular
particularly
important
topic
in
that
draft,
and
it
does
does
a
good
job
on
that.
A
draft
on
a
network
multipathing.
I
was
initially
target
qwg.
It
sure
looks
like
it
is
it's
it's.
C
It's
a
more
appropriate
draft
for
inter
area
because
mostly
about
how
to
send
packets
down
down
network,
has
in
parallel
and
there's
a
version.
Six
draft
of
the
sun.
Sorry,
a
draft
for
version
6
the
sox
protocol
again
also
being
active
discussing
in
Terraria
and
on
their
on
on
their
agenda.
If
you
interested
in
any
of
these
three,
please
go
to
the
interior
meeting,
which
I
think
is
on
Thursday
before
our
second
session.
A
C
C
C
We
do
status
updates
we're
going
to
quick
cover
to
month
or
two
three.
Once
we
get
done
the
agenda
bash
and
then
Tim's
got
a
few
words
to
say
about
the
the
802
211
diffserv
draft
we've
noted
these
drafts
as
being
related
interest.
Then
the
bulk
of
today's
meeting
is
diffserv
ecn
and
l4s
draft
CC
and
respect
recent
cat
encapsulation
drafts
and
then
on
Thursday
we're
gonna.
Take
a
look
at
a
couple
of
SCTP
drafts.
C
Any
comments,
questions
requests
all
right.
Consider
the
agenda
bash.
Let's
quick,
knock
off
items,
two
one:
two
one:
three,
two
three
we've
basically
done
two
one.
We
I
think
we
based
on
that.
You
want
to
to
interview
on
congestion,
draft
Tom
session
feedback
draft.
The
outcome
is
that
we
it's
going
to
need
some
significant,
more
work
in
particular,
I
think
we
want
to
see
a
worked
example
in
it
and
we'll
take
this
up
directly.
The
draft
authors
eating
experimentation.
C
F
Okay,
sorry
so
Tim
Sogeti,
Cisco
Systems
I,
just
like
to
review
where
we
are
with
the
diffserv
to
802
11
mapping,
the
mappings,
the
the
reasons
behind
this.
Of
course,
we
have
so
much
more
traffic.
Now,
that's
Wireless.
In
fact,
this
balance
is
shifted.
There
is
now
more
IP
traffic
that
is
sourced
from
wireless
devices
and
wired
that
happened
this
year.
That
trend
is
going
to
continue
by
2021
is
expected
at
63%
of
tropical
resource
from
wireless
devices.
However,
QoS
policies
are
not
aligned
because
we
have
two
independent
autonomous
standards
bodies.
F
Administering
this
not
administering,
but
administering
the
standards.
Pardon
me
and
then
the
goal
is
to
maintain
that
consistency
of
treatment,
regardless
of
whether
the
traffic
is
on
a
wired
or
wireless
network.
The
next
slide,
please,
as
David
mentioned,
the
mappings
themselves
have
been
stabilized.
We've
had
two
years
of
discussions
really
good
discussions
on
the
group,
and
so
this
is
now
good
to
go.
The
couple
areas
that
we
are
going
to
talk
about
have
to
do
with
the
scavenger
class
or
the
le
PHP.
F
That
Roland
will
be
discussing
all
return
to
that
in
a
moment,
but
then,
if
we
could
just
take
a
look
at
the
next
slide,
I
want
to
make
the
point
to
is
that
these
are
already
in
wide
use
on
millions
of
devices
from
Cisco.
We
wanted
to
get
with
this
whole
initiative
started
by
getting
our
own
house
in
order,
and
then
we
realized
look.
F
Why
do
we
have
so
much
disparity
from
one
platform,
one
software
version
to
another,
and
then
we
wanted
to
do
a
greater
service
to
the
Internet
community
at
large
by
arriving
at
a
consensus
consensus
recommendation,
so
that
would
have
that
consistency
across
all
vendors
across
not
only
the
makers
of
APs
and
wireless
infrastructure,
but
also
wireless
endpoint
devices,
so
I
think
I
tallied
this
up.
It's
like
about
800
million
devices
are
already
using
the
recommendations
put
forward
in
this
proposed
standard.
F
What's
remaining,
you
may
some
comments
from
David
coming
from
a
security
background,
even
though,
in
the
terminology
and
section
1.6
of
this
document,
we
outlined
the
context
of
the
word,
trust
and
non
trusted.
These
are
used
extensively
in
RFC,
45
94,
which
is
what
we
draw
heavily
from.
However,
we
do
recognize
very
clearly
that
these
have
very
strong
definitions
outside
of
Kos.
So
to
avoid
that
confusion,
we
will
make
the
changes
to
the
wording
and
avoid
the
use
of
the
wording
Trust.
F
F
In
turn,
that
will
have
an
effect
on
ours,
we're
very
happy
to
make
those
changes
once
they
are
finalized
and
we'll
do
that
and
then.
Finally,
just
some
wording
knits
have
been
suggested
and
I'm
welcoming
anymore
during
this
working
group
last
called
number
two.
What
we're
asking
for
the
final
slide
is
that
we
will
make
all
the
changes
per
your
comments
for
your
reviews.
I
want
to
say
thank
you
for
everyone
that
has
done
a
review
on
this.
C
I
believe
we're
good
last
call
is
now
is,
is
now
closed,
but
of
course
somebody
has
any
last
minute
comments
get
them
in.
We
would
like
the
chairs
share
Tim's
sense
of
urgency,
we'd
like
to
move
this
draft
sooner
rather
than
later,
and
so
we're
gonna
do
on
the
issue
around
Ellie
is
let's
see
where
that
DSP
discussion
that
we're
about
to
have
goes,
and
if
it's,
if
we
have
a
pretty
clear
consensus-
and
we
know
where
we're
going,
we
can
update
this
draft
to
encompass
the
Ellie
draft.
A
C
H
Whoo
at
Tom
Jones,
University
of
Aberdeen,
and
we
have
a
working
implementation
on
top
of
FreeBSD.
We
would
love
to
speak
to
anyone
who's
interested
in
running
our
code
or
anybody
who's
interested
in
doing
an
implementation
or
another
operating
system.
So
we
could
do
some
interoperability
and
probably
best
if
you
wanna
talk
to
this.
You
talk
me
down
mm-hmm.
C
And
what
running
codes
kind
of
important
for
this
draft,
because
it's
taking
advantage
of
otherwise
unused
space
that
turns
up
if
the
IP
packet,
length
and
unity
packet,
lengths,
don't
met,
don't
match,
and
so
interaction
with
existing
plantations
that
aren't
expecting.
This
is
is
of
major
interest.
C
I
Comment
when
you
change
the
FreeBSD
code,
did
arts
Dave
Wilson
sideline?
Did
you
notice
if
the
old
code
would
have
been
okay
with
the
options
it
sounds
like
he
made
freebsd
support
the
UDP
options.
Was
the
old
code,
a
problem,
so
what
an
old
FreeBSD
version
trip
over
the
the
options
in
an
incoming
packet
and.
C
J
C
K
K
The
ANA
section
was
little
bits:
cleaned
up
and
I,
also
edit
multicast
traffic
as
a
potential
use
case.
So
multicast
traffic
usually
has
a
problem
that
multicast
traffic
can
suddenly
appear
in
your
domain
as
soon
as
a
branch
is
newly
created,
and
in
that
case,
if
you
want
to
avoid,
let's
say
traffic
sources
that
can
cause
severe
condition
in
your
ISP
Network,
you
may
be
better
off
using
Kali
in
order
to
avoid
that,
so
that
could
actually
help
in
deploying
little
bits
multicast
and
on
a
more
global
scale.
K
I
also
added
text
about
implementations
using
a
QMS
and
UCM
usage
for
Ellie
and
I,
also
revised
text
and
security
section.
So
next
slide
yeah.
So
one
aspect
that
came
a
little
bit
more
clear
in
this
version
is
that
one
essential
characteristic
of
Ellie
is
that
it
has
there's
no
harm
to
best-effort
traffic
property,
and
so,
if
a
provider
actually
decides
not
to
support
nowhere
effort,
then
it
cannot
take
advantage
of
these
features.
K
So
they
must
be
aware
that
they
may
be
side
effects
on
on
this
Airport
traffic
if
they
carry
the
war
effort
within
the
beste
for
a
grenade,
and
currently
the
draft
discuss
discusses
two
types
of
users:
one
is
the
element
user,
which
means
the
user
doesn't
care
whether
lower
effort
traffic
is
actually
better
treated.
Then
the
intended
so
remarking
best
effort
is
okay
for
them
and
the
other
uses
the
the
L
a
strict
user,
which
means
he
doesn't
want
to.
K
K
So
currently
the
draft
proposed
only
to
use
the
le
Minh
semantics
and
maybe
to
use
some
kind
of
lower
if
for
transport
like
like
that,
if
you
want
to
make
sure
that
no
traffic
is
really
pushed
in
the
background,
so
one
question
is:
have
we
means
to
detect
any
remarking
using
I,
don't
know
arm
the
the
connection,
establishment
of
TCP
or
something
so
we
usually
need
been
some
kind
of
DHCP
feedback.
There's
right
now,
at
least
to
my
knowledge.
No
no
means
for
doing
that
next
slide.
K
So
next
steps
I'm
not
sure
whether
people
like
the
semantics
of
a
liminal,
a
straight
I,
don't
know
I
mean
for
me.
Le
Minh
is
fine,
but
it
seems
that
people
made
some
comments
in
the
past
that
they
have
any
strict
semantics
in
mind
and
I.
Don't
think
that
we
need
actually
two
years
apiece
to
support
this
so
yeah.
K
K
So
there's
only
a
small
set
of
potential
choices
left
in
the
current
ESP
stand,
a
pool
and
yeah
so
I
guess:
Gauri
has
more
input
data
just
in
a
few
minutes,
and
so
yeah,
more
reviews
and
feedback
appreciated
and
yeah
I
think
we
are
nearly
ready
for
going
to
work
in
group
last
call
except
the
fact
that
we
may
have
to
think
about
updating
the
arrow,
2.11
mapping
draft
or
the
web
RTC
draft
after
they've
been
published.
I,
don't
know.
C
A
L
L
So
a
really,
this
talk
is
about
what
would
be
the
best
choice
for
a
code
point
for
early.
What's
the
state
of
this
discussion?
First
of
all,
I
received
forty
five.
Ninety
four
specified
CS
one,
but
is
understood
that
this
is
not
a
good
choice.
It
would
be
zero,
zero
one,
zero,
zero,
zero
and,
by
the
way,
now
the
analyzer
sorry
for
to
simplify
this
discussion.
L
So
the
binary
of
this
code
point
so
that
there
is
consensus,
SE,
not
not
a
good
choice,
because
we
will
create
a
priority
inversion,
so
we
should
select
something
that
start
with
zero
zero,
zero
and
then
something
in
the
top
down
and
the
bottom
three
bits
in
the
current.
As
we've
seen,
the
carbon
suggestion
is
zero
one
zero,
so
our
experiments,
our
measurement,
were
meant
to
really
see
if
it
would
work
in
today's
network
and
it
it's
a
good
starting
point,
because
we
saw
that
at
least
it
has
good
survivability
in
the
internet.
L
Sense
that
using
this
Co
point
it
in
the
a
large
number
of
parts
it's
if
we
color
the
pocket
with
the
this
dscp
can
get
to
the
other
end.
That's
right!
So
first
let
me
spend
a
couple
of
words
about
what
experiment
we
did.
We
developed
this
this
tool
called
path
scope
which,
as
the
same
as
looks
inspired
by
trace
route,
it
was
a
traffic
generator
that
use
a
syn
packet
to
send
in
packet
to
a
target
and
increase
the
time
to
live.
L
Each
time,
then
I
collect
all
the
ICMP
the
because
of
the
time
to
lead
the
expedition
at
the
the
traffic
at
the
sender,
and
it
does
an
analysis
of
what
I
see,
starting
with
different
coupon.
So
it
changed.
The
point
is
scriptable,
so
you
can
decide
which
compiler
to
start
with,
and
it
does
this
automatically
and
we've
done
this
with
several
point
from
three
vantage
point
in
this
open
network,
all
digitalocean
from
300
point
towards
300
targets
chosen
randomly
from
the
Alex
that
1
million
lists
using
TCP
and
UDP,
and
that's
right.
L
So
one
pathology
that
we
saw,
starting
with
several
code
point,
is
that
the
top
three
beats
are
some
time
bleached.
We
call
this
a
toss
bleaching,
because
these
three
bits
correspond
to
the
ole
toss
semantics,
and
this
means
that,
for
example,
what
you've
seen
that
several
compile
like
a
f11
f12
3
1,
&,
4
4
1,
that
all
of
this
strip
bit
non
zero.
But
the
bottom
tributed
0,
1,
0
after
resetting,
are
mapped
to
the
SCP
2.
L
Similarly,
for
a
F
1
2
F
2
2
3
3
2
&
4
2,
we
have
known
that
the
top
tribute
non
zero
and
are
mapped,
but
the
bottom
3
bit
1
0,
0
M
and
on
map
to
yes
it
before
and
the
same
story
for
a
F,
1,
3,
F,
2
3.
So
our
friend
Bowie
series.
That's
the
question
for,
or
with
all
these
900
the
unique
search
destination
pay.
L
We
see
that
70%
of
parts
of
the
SCP
modify
so
the
fee
at
the
end
of
the
part,
wasn't
the
same
day
as
the
one
that
we
started
to
start
with,
but
in
10%
we
are
the
this
pathology
to
us
bleach.
So
you
understand
what
is
that
the
track
here
is
that
some,
for
example,
if
you
choose
the
SCP
2
nd
freeze
start
with
the
I
priority
class
like
a
f11,
it
would
be
mapped
to
the
SCP
to
next.
L
So
then
we
done
some
other
of
this
measurement
in
we
develop
another
tool
called
edge
traced
that
it's
collect
rates
because
it
wants
to
do
exactly
the
opposite
of
this,
so
it
starting
from
a
pool
of
of
sorts
at
the
edge
of
the
network,
and
we
selected
we
had
control
of
177
nodes
distributed
across
the
network,
then
more
on
this
was
on
the
map
algae
presentation,
using
this
tool.
We
can
see
also
looking
at
this
webpage
here
at
the
bottom.
L
We
saw
that
when
we
send
a
probe
from
one
of
these
point
to
one
central
send
server,
we
saw
that
this
pathology
of
tos
bleaching
was
non
insignificant.
We
had
is
70%
and
also
we
had
the
other
measurement
using
a
mobile
network
in
a
protocol.
Moreau
were
really.
This
is
used
mobile
nodes
in
different
operators
across
wireless
operate
across
Europe,
where
we
have
bought
control
of
the
sender
and
the
receiver.
It
will
accentuate
experiment
using
two
two
nodes
and
we
have
the
opportunity
to
probe
the
many
many
tests.
L
Many
many
parts
across
in
this
work
and
yeah
we
saw
various
other
pathology,
but
still
that
us
bleaching
was
detectable
because
we
are
at
least
for
quest
point
7
when
we
went
to
see
the
pathology
specific,
oh
of
a
certain
ruler.
So
how
did
ESET
changed
from
the
input
to
output
in
4.7
percent
of
the
routers
presented
this
this
pathology?
Next?
L
So,
okay,
that
set
up
the
the
the
question
is:
what
is
that
is
the
SCP,
the
best,
the
best
choice,
because
we
can
see
this
issue
of
resetting
the
top
tribute
and
so
I've
this
priority
inversion?
Of
course,
it's
important
to
to
consider
that
if
it
was
mapped
to
something
like
is
like
this
F
wouldn't
be
a
problem,
but
because
the
uniqueness
of
this
code
point
that
is
lower
than
be
safer,
then
we
don't
want
this
priority
inversion.
A
So
thanks
Ruffalo
for
setting
up
naturally
getting
some
measurements,
so
we
can
see
what's
happening
for
real
I.
Think
it's
important.
We
talk
about
this
now
because
all
the
other
diffserv
classes,
we've
created
all
the
other
ph
bees
are
actually
being
pH
bees
which
could
live
with
the
best
effort
service,
but
we're
being
elevated
by
the
diffserv
mechanism.
This
particular
pH
B
is
one
that
seeks
to
be
worse
than
best
effort.
So
we
don't
want
other
traffic
mapped
above
it
by
accident
or
below
it
by
accident.
We
don't
want
this
inversion.
M
Baker
you've
only
got
eight
options
and
actually
for
that,
you
can
use
in
your
collapsed
dscp
and
the
reason
being
that
the
least
significant
bit,
if
puts
it
in
a
special
use
class.
So
it
pretty
much
has
to
be
zero
for
any
public
vscp.
So
that
leaves
you
a
grand
total
of
three
values.
So
if
you're
gonna
argue
against
using
to
Fred.
A
A
M
C
A
M
So
what
are
we
ready
to
talk
just
carry
on
okay,
so
the
values
that
value
you'd
like
to
wind
up
with
zero,
the
value
that
you're
arguing
you
could
wind
up
with
and
not
like,
would
be
two
or
four
or
sex
and
I'm,
not
sure
I
see
the
real
difference
in
them.
You
know
from
that
perspective.
I
would
really
like
to
go
back
to
these
people
that
are
doing
cosplay
Qing
and
tell
them
that
that
was
25
years
ago.
The
Internet
has
been
different
for
a
really
long
time
throw
up.
A
H
Tom
Jones
University
of
Aberdeen,
and
just
so
just
another
argument
against
SSH
is
squatting
on
core
points
for
encode
points,
for
friends,
right
of
traffic
and
for
a
bulk
traffic,
so
bulk
copies
over
SSH.
If
you
use
the
core
point
might
end
up
with
the
early
treatment,
which
is
probably
not
what
they
want.
N
Michael
Abramson,
so
the
seventeen
seven
percentage
points
can
we
go
back
to
the
okay?
Did
you
observe
any
when
he
says
modified
the
DHCP
was
this
like
all
of
those,
so
the
17%
includes
the
10%
of
the
total
aging,
or
is
this
in
addition
to
okay?
So
we
have
7%,
where
it's
not
doing
only
toss
bleaching
its.
It
is
all
that
it's
setting
it
to
zero,
or
did
people
do
even
other
things,
but
most
of
it
is
to
zero
okay,
but
how
much
of
it
is
not?
L
I
guess
it's
a
small
percentage
and,
for
example,
we
can
see
it
from
the
last
slide
where
we
had
yeah.
We
had
like
the
main.
The
main
the
dominant
pathologies
are
really
bleaching
and
toss
bleaching
in
different
proportions,
and
then
we
have
the
small
number
of
other
good
point
that
we
detect
at
the
end
that
are
related.
If
you
want
to
the
one
that
we
set.
N
A
It
may
be
that
some
of
these
code
points
are
intentional
policies
within
the
diffserv
domain
that
are
admissible.
The
issue
I
think
that's
on
the
table
is
the
marking
of
packets.
That
is
not
probably
intentional
and
is
disruptive
to
the
use
of
this
code.
Point
yeah
once
a
disruptive,
because
it's
intentional
apparently
okay,
yes,.
N
K
O
Okay,
I
can
go
get
me
well.
No!
So
no,
it's
pretty
clear
from
from
even
from
here
that
there's
a
few
things
that
there's
basically
probably
one
or
two
a
SS
that
are
actually
leaking
out
like
weird
you
we're
using
a
for
dscp
for
actual
engineering
inside
our
network
and
inch
leaks
out
right
and
they
don't
bleach
it
on
the
out.
On
the
other
end
or
somehow,
her
story.
O
The
question
that
I
came
up
here
to
ask
was
actually
so
you
said,
tens
of
a
s's
are
doing
things
that
might
make
beat
the
two
four
and
six
code
points
not
works
of
bleaching,
the
top
three
great
how
many
S's
were
in
the
sample.
So
we
had
ninety
two,
oh
two
unique
source
destination
pairs
monroe
has
an
access
network
diversity
of
like
nine
different,
a
isatis.
So
if
we're
looking
at
tens
of
a
s
is
in
thousands
of
a
s,
is
that's
different
than
ten
two
bases
and
hundreds
of
asses?
O
L
Yeah
I
mean
with
the
one
that
we
traversed
and
really
we
consider
all
we
discussed
some
some
sample,
because
if
the
dscp
was
changed
that
quite
early
along
the
path-
okay,
maybe
it
wouldn't
be-
it's
not
longer
significant
for
the
the
one
that,
for
example,
if
it
was
bleach,
you
can
infer
anything
from
the
next
measurement.
So
we
had
many
as
assets
that
were
Amina,
reachable
from.
O
O
O
But
how
many
different
yeses
is,
that
is
the
question
and
what's
the
proportion
yeah
so
I
would
I
would
suggest
going
going
back
and
I'm
gonna.
Look
at
that
I
mean
it's
pretty
clear
as
input
to
the
discussion
that
we
should
start
having
here
that
two
four
and
six
are
bad,
and
now
we
get
to
go
fight
about
one
three,
five
and
seven
right.
O
But
but
I
mean
like
so
from
from
a
measurement
standpoint,
it
would
be
really
interesting
to
know
what
the
denominator
of
the
number
of
a
s
is.
He
said
they
were
like
tens
of
a
s.
It's
like
it's
tens
of
tens,
then
we're
screwed.
If
it's
tens
of
all
of
them,
then
it's
phone
calls
all
right
all
right.
Thanks
right.
C
And
the
to
the
point
where
we're
gory
and
I
were
sort
of
equivalent
quibbling
with
with
thread
it's
roughly
up
on
the
screen.
This
is
the
int
registry,
and
the
important
point
is
that
the
code
points
in
pole.
Three
that
end
in
zero
one
were
tagged
as
maybe
utilize.
Your
future
standards
action
if
necessary.
So
we
did
warn
people.
However,
running
code
wins
this
one.
Every
time.
A
K
Thanks
for
for
these
measurements,
I
think
just
bleach
is
maybe
a
misnomer.
It
should
be
IP
president's
bleach
also,
so
it's
more
precise
exactly,
for
instance,
please,
yes,
so
yeah
I
think
we
should
stop
around
so
I'm.
Basically,
a
second
threats
comments.
We
should
stop
working
around
broken
implementations
and
also
I'd
like
to
get
this
SSH
stuff.
Fixed
I
mean
why
are
they
using
KO
point
to
its
its
allocated
for
standard
section
or
not?
A
C
Core
point
right,
although
I
think
my
Michaels
comment
was,
is-
is
quite
wrong
with
a
lot
of
what
we're
dealing
probably
dealing
with
here.
It
operates.
You
have
equipment
that
ain't
broke
and
they're,
not
critically
clear
on
what
all
the
details
are
of
what
it's
doing,
but
but
the
traffic
seems
to
flow
through.
C
Your
co-chairs
about
to
earn
their
absorbance
salaries.
Okay,
we're
gonna!
Do
this
we're
gonna,
do
this
via
show
of
hands.
This
is
a
straw
poll.
This
is
a
straw
poll.
Not
a
final
decision
can
I
see
from
a
show
of
hands
how
many
people
in
the
room
think
how
many
people
think
they
understand
the
issue.
C
Okay,
the
decision
trying
to
make
here
is
okay,
so
the
decision
when
I
set
up
here
is
Dooley
stick
with
dscp.
Thank
you,
Bob,
good,
good,
good
good.
Do
we
stick
with
dhcp?
That
is
currently
the
draft,
or
do
we
pick
another
dscp,
which
is
probably
gonna,
be
an
odd-numbered
one,
because
in
essence
this
says
that
the
site
looking
at
here
that
says
the
two
is
bad.
We'll
also
apply
two
four
and
six.
C
So
if
we
accept
the
argument
here,
the
two
is
bad
four
and
six
go
away
and
we're
gonna
be
looking
at
odd-numbered
dscp.
So
the
decision
being
the
decision
that
we're
looking
at
is
to
be
simple
or
we
go
to
one
of
the
one
of
the
odd
numbers.
Odd
number,
DCPS
cps
and
the
question
I
want
to
ask
is
how
many
people
think
who
understand
the
issue
think
we
have
enough
information
to
make
the
decision
now.
C
C
P
C
C
I
think
I
agree
with
you,
which
is
that
this
this
this
slide
not
not
lame,
demolishes
to
blossom
masters.
For,
if
you
believe
this
slide
is
a
reason
not
to
choose
to
it's
also
a
reason
not
to
choose
four
and
six
and
will
wind
up
with,
will
wind
up
having
to
deal
with
the
process
consequences
of
using
an
odd
one
and.
G
Q
Q
C
C
Q
K
R
Q
O
O
A
O
O
J
A
O
H
R
C
C
C
C
F
F
C
J
C
C
And
part
of
the
reason
this
slide
exists
is
when
I
look
at
our
set
of
milestones,
I
discovered
we
had
5
September
crafts
due
in
September
I,
knew
that
wasn't
going
to
happen.
Ok
now
we
need
milestones
for
the
of
the
remaining
drafts.
Bob
September
2018
is,
is,
is
a
swag
for
out
for
for
for
l4s.
Do
your
better
swag.
A
G
E
A
C
Udp
options
making
a
guess:
I
guessed
after
the
spring
meeting
next
year
that
that
gives
us
gives
us,
gives
us
two
meeting
cycles
and
I.
Think
I
I,
don't
think
the
spec!
That's
gonna
change,
much
I
think
it's
mostly
at
an
understanding
of
of
implemented,
bility
and
of
and
effect
on,
implementations
that
don't
support.
C
S
E
C
E
So
we've
done
liaisons
on
this
and
in
the
process
of
writing
this
the
normative
text
in
it
being
a
PCP,
we
decided
to
pull
it
out
into
a
another
standard
track
document,
so
the
ticket
update
of
a
standard
track
drafts
which
I'm
going
to
come
up
to
right
things
that
been
going
on
recently.
This
this
draft
has
been
tabled
for
quite
a
while
it's,
but
that
stuff
is
happening.
One
very
important
thing
going
on
in
3gpp
is
a
proposal
from
Ericsson.
E
In
fact,
number
reference
number
one
down
there
to
try
and
make
ACN
visible
of
the
RLC
low
in
the
3gpp
stack,
because
the
IP
header
is
compressed
both
both
time
to
get
there.
If-
and
this
is
for
architectures
where
the
BBC
P
layer
is
distributed
from
the
RLC
layer,
so
so,
and
so
that
that
would
require
this.
This
draft
it
was
proposed
in
the
June
meeting,
and
there
were
counter
proposals
to
because,
because
it's
sort
of
that
they've
already
got
this
technology
called
Ram
based
codec
at
that
adaptation.
E
That's
just
for
one
application,
it's
basically
for
voiceover
LTE,
and
so
there
was
some
people
saying.
No,
we
don't
want
to
do
ACN,
because
we've
got
this.
I
was
saying:
well,
let's
do
both
and
I
was
saying
not
and
all
the
rest
of
it,
and
when
you
look
at
the
minutes,
everyone's
quite
confused
about
what
the
differences
are
between
them
and
what
their
scope
isn't,
all
the
rest
of
it.
E
So
in
the
end
of
the
decision,
was
deferred
until
August,
but
I
would
encourage
any
3gpp
delegates
to
understand
the
implications
of
this
decision,
mainly
because
the
the
proposal
from
Ericsson
was
primarily
to
like
a
support
l4s
with
very
low
latency,
without
having
to
jump
back
in
the
stack
to
another
node
to
report
ecn.
So.
C
C
C
E
E
C
E
E
E
E
C
E
Me
tell
you
what
that
slides
about
on
yeah.
So
this
the
scope
was
of
RFC
6040
was
IP
and
IP,
and
it
never
said
anything
that
I
IV
has
to
be
directly
on
IP,
but
some
people
assume
it
did
and
some
people
zoomed
in,
so
that
this
updates
make
it
clear
that
includes
a
shim
and
that
shim
might
be
extended
with
a
layer,
two
header
as
well
before
you
get
the
other
IP
header
and
it
could
even
apply
where
you
don't
know
whether
the
you
know
is
IP
or
not.
E
So
there's
text
in
the
draft
to
make
this
all
clear,
I
won't
go
through
the
text.
You
can
read
the
draft
carry
on
next.
So
then,
when
I'm
had
a
look
at
how
many
specs
are
covered
by
this,
because
you
know
we,
we
covered
the
IP
and
IP
with
about
three
or
four.
But
then
I
discovered
that
the
interiors
been
quite
busy
and.
E
Also,
maybe
some
of
these
are
actually
routing
yeah
yeah.
So
what
what
these
columns
mean
ended
up
deciding?
Let's
not
let's
not
deal
with
anything
here,
except
standards,
track
stuff
or
widened
avoid
stuff,
so
the
first
column,
if
there's
a
cross
in
there,
there's
no
further
information
in
the
other
columns,
because
we're
going
to
ignore
all
that
when
I
say
first
car
I
mean
third
column.
Of
course
you
should
all
know
when
I
say
first
I
mean
third.
E
Then
the
the
a
okay
column
is
saying
that
it
refers
to
either
RFC
6040
on
tunneling
or
on
a
previous
compatible
to
a
previous
compatible
RFC
IRC,
3168
and
I'll
come
back
to
some
of
the
exceptions
like
the
SFC
one
in
a
minute.
I'll
just
explain
the
table.
First,
then,
the
two
in
okay,
not
okay,
columns,
they're,
two
different
sorts
of
not
okay,
one
there's
text
in
this
draft.
Now
that
makes
them
okay.
E
C
E
C
E
E
So
there's
two
l2tp
ones
for
the
very
old
b2
which
is
still
around
for
PPTP
point-to-point,
tunneling
protocol
and
then
l2tp
version
3,
which
is
often
used
for
Ethernet
and
other
other
layer,
2,
stuff,
tunneling,
and
then
there's
GRE
in
this
tirado,
and
these
are
all
significantly
different.
Actually.
E
E
Well,
this
is
sort
of
what
I
want
to
know
because
I've
been
asking
I
mean:
if
there
are,
they
must
be
automatically
configure
so
but
I,
don't
I
can't
find
any
protocol
that
does
it.
Ok
and
I
can't
find
anyone
who
will
sort
of
admit
to
looking
at
the
interior
main
unless
long
enough.
To
answer
my
question
right
so.
A
C
O
Okay,
so
I
actually
would
like
to
answer
that
question.
I
can't
say
yes
or
no,
but
I
can
say
that
if
banana,
which
had
AB
off
yesterday
is
chartered
and
they
decide
that
GRE
is
a
tunneling
mechanism
that
they
might
want
to
use
for
non
TCP
traffic
for
doing
multi
path
bonding,
then
they
will
find
or
define
a
configuration
provisioning
discovery
whatever
we
couldn't
go
over
the
word
that
that
not
like,
after
the
room
hated
protocol,
which
would
kind
of
qualify
as
automated
GRE
tunnel
setup,
so
I
think.
O
E
And
so
I'm
still
just
going
through
the
cat
why
these
things
are
significantly
different.
Then
of
course
tirado
is
generally
n
system
2n
system,
and
so
it's
it's
not
you
know,
network
configuration
and
thing
doesn't
apply,
so
I
see
Christian
there.
So
maybe
I'll
get
some
answers
out
of
Christian
as
well.
E
So
I'll
talk
to
him
later
so
going
one
level
deeper
on
each
one:
the
lttp
one
I've
proposed
and
in
consultation
with
Carlos
and
in
natio
a
new
actually
pairs
of
two
ends
from
the
go
she
ate
etn
and
that's
all
written
out
and
the
honor
I
on
a
registry
bit
is
written
up
and
who
or
how
it's
meant
to
work
for
GRE.
It's
just
manual
configuration
as
far
as
I
know,
so
there's
not
much
to
write
other
than
comply
with
6040.
E
If
you're
the
person
manually,
configuring
it
and
then
tirado
it's
sort
of
difficult,
because
the
spec
didn't
mention
ACN
and
there's
a
lot
of
tirado
out
there.
So
if
we
start
having
ecn
working
underneath
tirado,
it's
it's
good,
I,
don't
know
what
and
I'm
sure
Christian
can't
remember
what
the
code
looks
like
without
thinking
about
it.
But
whether
it
copies
the
ecn,
header
or
zeros,
it
is
important
because
if
it
copies
it,
then
it
will
be
black
holing
ACN
if
there's
any
easy
and
enabled
on
your
path.
G
A
S
Christian
we
tomorrow,
the
question
about
Teredo
is
that
there
are
two
parts
that
to
to
answer
your
question
there.
Is
it
conceptually
hard
to
have
a
support
for
easy
and
intuitive
and,
and
the
answer
is
no,
it
is
not
a
snow
particle
reason.
Why
not-
and
the
second
question
is
if
we
update
the
IFC
to
specify
that
support,
will
application
also
be
updated
and
data
is
a
much
harder
case
because,
as
far
as
I
know,
some
of
the
implementation
is
in
Hardware
yeah.
E
S
E
D
I
E
When
you,
when
you
move
in
two
aspects,
one
is
one
is
and
I've
got
slides
on
what
what
the
problem
is
next,
but
what
one
is
that,
if
there,
if
there
is
an
IP
outer
and
I'd,
be
here
somewhere,
then
if
you're
going
to
not
have
a
zero
in
the
outer
ecn,
you
should
first
check
that
the
other
end
of
the
tunnel
will
be
able
to
process
it.
I
guess:
okay,
all
right
and
and
so
it's
a
question
of
coordination
between
the
two
ends
of
the
tunnel.
E
E
Go
stay
on
this,
but
no
stay
on
this
one
a
bit
longer,
so
no
I
think
we're
done
on
that
yeah
other
than
to
thank
all
the
people.
It
acknowledges
in
the
various
working
groups.
I
have
been
beating
up
on
a
number
of
people
for
the
last
couple
of
months
right.
So
this
this
is
exactly
what
David
else
was
asking.
So
Sen
is
different
to
any
other
field
in
the
IP
header
when
you're
tunneling,
and
so
it's
a
given
example,
diffserv
gets
copied
down.
E
But
then,
when
it
comes
to
the
D
capsulation,
it's
just
thrown
away.
The
answer
is
just
thrown
away,
but
with
ECN
the
capability
goes
down
and
then
any
changes
to
it
have
to
be
propagated
back
up
again
right,
and
so
it
has
to
check
when
it's
doing
the
encapsulation.
Whether
the
D
cap
would
support
that
combination
of
the
inner
and
the
outer
before
it
gets
boarded
and
if
not,
it
should
zero
it.
So
the
problem
is,
if
it
does.
His
check
then
marks
it
ECT,
because
it's
come
in
as
ECT.
E
So
in
that,
like
in
the
Teredo
case,
then
you've
got
easy
and
capable
on
the
path.
If
you
go
through
say
oh,
if
you
call
upstream
on
your
trade-
oh
it
might
mark
it,
but
then
those
markings
just
get
dropped
on
the
floor
and
you
get
all
hell
break
loose
as
you
see
there,
and
so
what
that
will
mean
is
it
will
toggle
between
tail
drop
and
then
ACN,
and
it
will
give
you
really
bad
performance.
E
E
But
what
we
didn't
do
is
write
it
from
the
point
of
view
of
what
an
implementation
that
doesn't
apply,
whether
it
should
do,
and
in
this
one
case,
even
if
it
doesn't
comply
with
it,
it
has
to
do
something:
it's
like
a
requirement
for
all
things
that
use
the
Internet
Protocol
all
tunnel
endpoints,
whether
or
not
they
comply
with
RFC
six
deported
and
so
in
this
update.
Sixty
forty
I've
added
some
text
because
all
you
can
do
there
is
just
say:
the
operator
should
configure
it
to
be
safe,
right
and
I've.
E
Talk
about
those
words,
because
what
that
implies
is
that
the
implementation
gives
them
the
possibility
of
configuring
it
and
that's
why
there's
the
if
possible,
if
it's
not
a
big
herbal,
they
can't
do
it
if
it's
configurable
they
must
but
I
can
entertain.
Telling
an
operator
must.
It
is
sort
of
you
know.
C
E
S
The
operator
is
I
mean
the
tomato
setup
is
really
automated
and
we
do
effectively
as
an
explicit
set
up
with
a
system
of
ropes
and
all
that
so
I
have
not
done
the
work
and
I
don't
want
to
presume
of
the
way
it's
possible
to
specify
something
like
if
your
initial
set
of
probes
carry
the
bit
end
to
end,
then
you
notice
that
your
saga
is
capable
and-
and
you
use
it
wise
if
they
do
not,
then
you
did
use
it.
It
is
not
capable
and
you
zero
the
flag
yeah.
S
Matt
you
you
will,
you
will
be
in
a
way
it
which
basically
windows
like
if
I
will
always
send
me
to
zero
anyhow,
and
it's
not
windows
95
at
least
Windows
7,
but
but
they
will
send
a
bit
to
zero
and
and
they
will
not
acknowledge
it
when
you
send
a
probe
and
that
way
the
auto
system
will
notice
that
the
system
at
the
other
end
of
the
table
since
then
I
can't
do
it.
So
you
get
you
caramelize
it.
It's
possible
yeah,
okay,.
E
Right
so
yeah,
that's
the
end
of
that
slide,
so
spaces
make
steps.
There's
been
four
revisions
of
this
draft.
A
lot
of
works
gone
into
this
draft
to
try
and
meet
that
deadline
of
what
was
September
and
I.
Think
I
think
we
can
still
meet
it.
Hopefully,
interior
will
close
off
something
remaining
issues.
I've
got
a
session
with
Praveen
next
week,
because
I
thought
he
was
going
to
be
here,
but
he's
not
so
to
deal
with
tirado,
so
I
think
we're
in
good
shape
are.
A
C
C
E
A
There's
three
drafts
that
have
been
adopted
by
the
working
group
and
we
are
looking
for
people
to
actively
engage
with
this
process
and
the
whole
purpose
of
bringing
these
drafts
to
an
IETF
working
group
is
that
they
become
owned
by
the
working
group,
which
means
people
get
a
chance
to
change
them.
People
get
a
chance
to
implement
them
or
experiment
with
them
or
see
how
it
fits
their
architecture.
E
Was
okay,
Bob,
Alan
kitchenette
was
and
and
just
as
you
have
a
sort
of
state
of
the
working
group
slide.
One
of
my
slides
is
going
to
be
stage
of
but
l4s
across
all
areas.
You
know
because
because
it's
not
just
these
three
drafts
and
not
not
so
it's
sort
of
a
coordination
problem
within
a
coordination
problem,
if
you
like
and
and
that's
where
a
lot
of
other
people
are
putting
in
effort
and
things
like
that,.
E
E
Excellence
like
okay,
there's,
the
co-authors.
This
is
the
architecture,
one
first,
a
recap:
the
opera
architecture
is
three
parts:
the
aqm
with
the
dual
cues
to
protect
l4s
from
classic
and
but
to
still
check
out
the
capacity.
So
you
get
very
low
latency,
which
is
the
whole
point
very
a
queuing
delay,
I
should
say:
there's
a
classifier
which
I'm
going
to
talk
about
in
the
next,
a
draft
talk
which
is
ECT,
one,
that's
been
for
that
preliminary
early
decided
and
then
there's
the
congestion
control
on
the
host
next.
E
E
E
We
don't
have
to
do
all
of
performance
improvements,
because
it's
already
ten
to
hundred
times
better
latency
than
anything
else
so
we're
you
know
we
don't
have
to
make
it
even
better
to
to
do
that.
To
get
all
the
drafts
to
go
through
so
ya
know:
500
milli,
micro
seconds,
delay,
queuing,
delay
versus
the
best
is
about
five
milliseconds,
and
that
requires
fair,
queuing,
so
flow
queuing
so
yeah.
We
understand
this
holding
pattern
because
you'll
always
be
updating
your
transport
protocol
and
we
need
to
have
a
cut-off
point
next.
E
So
this
is
the
eye
test.
This
is
what
I
said
about
the
status
of
all
the
other
parts.
As
you
can
see,
all
the
red
bits
mean
work
being
done,
updated
bits
and
pieces,
pretty
cool
actually
in
the
IETF
specs
bullet,
which,
if
you
can
see
that
there's
only
now
one
of
those
specs
is
not
adopted
in
the
various
working
groups.
They
all
adopted.
The
only
one
that
isn't
is
the
quick
one
he's
getting
quick
and.
E
Oh
yeah,
the
3gpp
bit
I'm
gonna
talk
about.
Oh
no
I
just
talked
about
didn't
I
and
that's
coming
up
with
discussion
in
August,
oh
and
finally,
we're
still
trying
to
get
the
paper.
We
wrote
about
it,
the
research
paper
we
wrote
about
it,
accept
it
so
that
all
the
measurement
results
with
millions
of
scenarios
or
measurements,
but
this
one
got
rejected
by
sitcom
on
the
basis.
It's
not
novel,
because
they'd
heard
about
it
in
the
idea.
E
I'll
go
straight
into
this.
We
were
having
a
discussion
about-
or
this
is
written
into,
the
identifier
draft,
but
maybe
I
ought
to
call
it
out
a
bit
more.
We've
talked
about
ecn
being
the
identifier,
but
if
you
like,
that's
the
default
identifier
and
the
ever-present
identifier
for
the
end-to-end
service,
but
it's
possible.
E
We
or
we
don't
want
to
prejudge
how
this
gets
deployed
by
different
operators,
and
they
may
want
to
make
it
initially
something
that
they
do
only
in
their
own
network
or
only
for
certain,
like
business
customers
or
or
you
know,
in
a
you
know,
for
their
VPN
customers
or
whatever
you
know.
We
don't
know
so
it's
possible
that
this
will
be.
These
are
easy,
an
identifier
and
another
optionally,
and
so
that
may
be
the
address
of
one
end.
It
may
be
a
VLAN
ID.
E
Maybe
they
serve
Co
point,
maybe
a
local
one
or
a
global
one.
It
may
be
the
bearer
ID
and
a
mobile
network.
You
know
so
and
we're
we're
about
to
put
the
hooks
in
the
code
to
use
the
Linux
classifier
architecture
to
so
that,
so
that
people
can
just
add
another
classifier,
as
well
as
the
EC
n1,
and
really
just
just
what
I'm
discussion
about
this,
because
well
a
the
implications
for
diffserv
as
well,
but
but
also
just
the
business
implications.
E
Because
if
you
provide
this
flexibility,
it
will
probably
get
used,
and
that
could
delay
this
being
an
end-to-end
service
for
many
years
and
where
you
don't
provide
it
I
suspect
people
will
abuse
it
and
do
it
in
a
bad
way.
The
idea
of
doing
this
is
that,
at
least
when
you
take
out
the
optional
one,
it
becomes
an
end-to-end
service,
eventually.
C
Build-A-Bride
speaking
from
the
floor,
so
I
suspect,
Bob
and
I
have
a
Socratic
dialogue
in
our
future.
On
the
subject:
glass,
half
full
glass
half
empty
on
this
one
I'm
one
of
people
poking
Bob
on
this
for
a
couple
of
reasons.
One
is
that
at
the
very
least
dscp,
and
to
make
other
classifiers
that
that
Bob
mentions
help
enormous
amount.
When
you
think
about
incremental
deployment-
and
it's
it's
I-
think
that's
really
important
at
what
important
aspect
to
bring
out
and
I.
Think
beyond
that
in
general.
E
I
just
wanted
to
pick
up
on
the
point
about
incremental
deployment.
I
think
the
more
identified
you
add
together,
the
less
incremental
deployment
you'll
get
ACM
currently
goes
through
pretty
well
most
places,
although
we've
got
some
more
recent
measurements
on
mobile
network.
So
we're
going
to
talk
about,
but
the
next
idea.
But
you
know.
E
C
And
and
this
this
is
also
a
a
a
perspective
discussion
because
I'm
thinking
thinking
in
terms
of
this
being
and
enhanced
service
on
individual
networks
and
there
you're
going
to
want
networks
or
classifiers.
And
then
we
see
how
the
world
evolves
and
and
extent
which
we
can
get
this
to
become
to
to
become
in
end
to
end
and
the
I.
C
Works
I
just
didn't
wanna
make
make
it
make
the
other
the
problem
I
talk
offline,
there's
some
wording.
Changes
need
in
the
draft
it
to
emphasize
that
that
that
that
second
classifier
is
optional
and
quite
useful
and
important
to
are,
as
I
usually
would
support
the
deployment,
motivate
deploy,
motivation.
P
E
Okay,
it's
a
next,
so
we
had
a
bit
of
a
discussion
in
TCP
M
about
another
piece
of
this
jigsaw,
which
is
now
called
ECM,
plus
plus
plus
it's
the
file
name.
There
TCP
I
might
generalize
dcn,
which
is
about
making
sure
you've
got
AC
and
on
all
the
tcp
types
of
tcp
packet,
not
just
the
data
packets
and
the
point
was
made
there
as
it
has
been
before
that
this,
at
least
now
makes
everything
consistent.
E
So
you
don't
have
all
these
exceptions
in
your
low
balance
and
things
where,
where
these
load
balancers
another
thing
that
it's
broken
in
you
know,
as
fred
was
saying:
they're
still
working
on
the
internet.
Our
grandfathers
bill
they're
still
using
the
8-bit
the
toss
by
so
when
the
ecn
field
changes
they
they
load
balance
to
another
place,
so
at
least
having
all
the
packets
in
one
flow
at
the
same
CCN
field
can
be
useful,
but
I
just
wanted
to
point
it
out
here.
A
This
is
really
something
that
people
have
to
fit.
I
mean
we
saw
the
other
dscp
mess,
but
this
would
be
up
to
fiscal
soon.
As
you,
your
Reuter,
happily
marks
easy
to
you,
one
or
zero
to
see
II,
it
blows.
So
this
just
brokenness
we
big
headlines,
please
don't
use
the
whole
byte
called
Lata's
bite
in
olden
times,
use
only
dscp
field,
the
Lord
balancing,
because.
E
What
what
we've
been
finding
we
haven't
yet
found?
Any
correlation
is
because
there
was
so
much
they
said
bleaching
that
it
was
under
percent,
so
we
couldn't
correlate
with
something
that
was
the
the
ecn
field.
Bleaching
was
I
suspect
about
from
people
who
thought
it
was
the
toss
by
rather
than
trying
to
bleach
these
in
feel,
but
I
don't
know,
hey.
I
T
E
R
A
Q
K
Of
review
for
the
duo
queue
drafts
next
slide,
so
further
improvements
that
were
done
was
we
have
we
submitted
at
the
end
of
the
draft.
We
added
the
overload
handling
to
the
cola
for
it
also,
the
the
PI
heuristics,
which
were
removed
from
the
dual
PI
Square,
have
been
assessed
and
discussed
now
on
the
mailing
list.
K
K
Also,
solving
on
a
tail
drop
based
or
buffer
bloat,
it's
environment
where
you
have
big
used
without
a
QMS,
there
is
also
a
solution
and
evolution
which
is
which
is
okay,
because
we
can't
have
a
cramps
every
where
immediately,
but
on
the
other
hand,
all
the
aqm
work
that
has
been
done.
It's
is
actually
clashing
with
what
is
currently
in
the
linux
kernel
as
bbr
and
which
seems
to
be
deployed
already
extensively
in
the
next
slide.
K
K
So
it
will
induce
a
lot
of
drop
probability
which
has
an
immediate
effect
on
the
completion
times
for
the
short
flows,
even
for
bbr
in
themselves,
so
which
is,
of
course
not
good.
So
it
makes
the
situation
with
an
AKM
worse
than
without
an
atrium,
which
is
not
a
good
evolution.
Let's
say
it's
not
what
we
want
and
it's
not.
K
What
is
the
intention
of
the
work
done
in
the
aqm
working
group,
so
in
the
next
slides
question
is,
will
be
BR
as
is,
and
and
this
evolution
force
operators
to
disable
a
crimes
in
the
future
together
with
ecn.
So
that's
a
little
bit
concern
I,
think
and
in
the
next
slide
the
question
is
well.
We
we
proposed
actually
a
solution
in
ITC
RG,
which
probably
we
will
further
experiment
with
and
also
I
hope
to
be
BR
people.
A
K
A
Thank
you.
So
we
have
a
another
slice
of
TS
BW
g
on
thursday
and
it's
in
session
2
on
thursday
afternoon.
Please
come
along
and
that
will
also
condylar
liaisons
discussion,
the
SCTP
drafts
and
the
fake
frame.
So
please
come
along
to
that
also
otherwise
have
a
great
day.
Thank
you
ever
so
much
for
coming.
