►
From YouTube: IETF99-INTAREA-20170720-0930
Description
INTAREA meeting session at IETF99
2017/07/20 0930
https://datatracker.ietf.org/meeting/99/proceedings/
A
C
D
Morning,
everyone
so
we're
gonna
get
started
on
interior
welcome
at
IETF.
Ninety
nine
blue
sheets
are
going
around
both
sides,
so
please
make
sure
you
register
your
agenda.
Your
your
church
was
him
and
myself
hello.
Everyone
there's
a
new
note,
well
that
you
have
already
learned
by
heart
at
this
time
of
the
week,
so
we
encourage
you
to
keep
reading
it
and
be
aware
of
the
differences.
Basically,
you
have
to
disclose
any
IP
are
related
to
any
discussion,
communication,
etc.
That
happens
during
this
meeting
that
you
may
be
aware
of.
D
B
D
Anyone
that
it's
willing
to
stand
up
yeah
yeah.
Thank
you
thanks.
We
got
perfect.
Thank
you
very
much,
all
right.
So
moving
on
to
the
agenda
we're
going
to
give
you
a
quick
update
on
the
working
group
documents
and
where
we
stand,
then
Ron
is
going
to
give
us
his
speech
about
probe,
which
is
a
apink
all
Deeping.
Now
it's
called
probe
and
it's
been
accepted.
D
Congestion
notification
tunnels
with
Bob
towel
is
going
to
talk
about
the
islands
in
your
packet,
discovering
provisioning
domains,
Eric
an
amputee
network
layer
from
grabber
and
Sox
v6
from
blood
on
our
status,
update
the
privacy
considerations
for
IP
broadcast
and
multicast
protocol
designers.
Well,
if
you
remember
that
that
document
got
accepted,
so
our
Shepherd
has
been
assigned,
that's
myself.
Actually
so
I'm
going
to
be
shepherding
the
document.
No.
On
the
generic
UDP
encapsulation,
it's
been
updated
to
version
4,
but
the
authors.
D
Sorry,
so
they
all
only
update
this.
It's
moved
from
version,
one
to
version
4,
no
presentation
plan
for
this
time
on
the
IP
were
intentionally
partition,
aliy
partially
partition
links.
We
adopted
the
document
as
last
time,
so
it
now.
It's
now
a
working
group
document.
Again,
no
no
presentation
probe
got
adopted,
but
we
Hira
an
update
from
ron
directly
and
they
be
tunnels
in
the
internet
architecture.
B
E
Okay,
welcome
to
Thursday
morning
in
a
cold
dark
room,
I'll
try
to
wake
everybody
up.
You've
heard
this
presentation
before
under
different
names.
First
time
I
came
here,
it
was
called
leaping.
Then
we
had
to
change
it
to
expain.
Then
we
found
somebody
else
have
used
that
so
now
it's
called
probe.
One
thing
that's
changed
significantly
is
the
name.
A
feature
has
been
added
and
just
to
make
sure
that
you're
all
awake
in
this
cold
dark
room
on
Thursday
morning.
When
you
see
the
new
feature,
raise
your
hand
and
then
I'll
know
people
are
awake.
E
Anyhow,
let's
dive
in
probe
is
a
utility
that
feels
something
like
ping,
but
a
little
bit
better.
Let's
go
on
to
the
first
slide
and
let's
talk
about
your
old
buddy
ping
ping
test,
bi-directional
connectivity
between
a
probing
interface
and
a
probed
interface.
Probing
interface
sends
an
ICMP
echo
request
to
the
probed
interface.
If
the
probed
interface
gets
the
request,
he
sends
back
an
ICMP
echo
reply
and
if
the
reply
makes
it
all
the
way
to
the
back
to
the
probing
interface,
we
declare
success.
Otherwise
we
declare
failure
now
something
about
ping
ping.
E
Doesn't
always
exercise
the
probed
interface,
the
echo
request
may
come
in
the
probe
node
through
a
different
interface,
and
if
the
echo
reply
may
leave
the
probe
node
through
an
interface
other
than
the
probed.
So
what
first
thing
you
have
to
disavow
yourself
is
the
know
that
were
exercising
the
probed
interface
next
slide.
E
Ping
has
two
failures,
not
two
failures:
it
does
what
it
does.
It
has
two
shortcomings,
though
one
is.
It
can't
distinguish
among
the
following
failures:
maybe
the
echo
request
got
lost
on
the
way
to
the
probe
note.
Maybe
the
probed
interface
is
down.
Maybe
the
probed
interface
is
up,
but
the
echo
reply
got
lost
on
the
way
back
to
the
probing
interface.
In
any
case,
when
you
look
at
ping,
all
you
know
is
that
the
echo
reply
didn't
make
it
back
to
you.
You
don't
know
why.
E
The
other
is
that
ping
requires
bi-directional
reach
ability
between
the
probing
and
the
probed
interfaces.
So
there
are
some
times
when
you
just
can't
use
ping,
for
instance,
when
the
probed
interface
is
unnumbered,
when
the
probing
interface
is
ipv4
only
and
the
probing
is
ipv6
only
or
vice
versa.
So,
with
probe
we're
gonna
try
to
overcome
the
shortcomings
you
see
on
this
slide
next
slide.
E
So
let's
talk
about
probe.
What
makes
probe
different
is
it
distinguishes
between
a
proxy
and
a
probed
interface?
What
happens
here
is
the
probing
interface
sends
an
ICMP
echo
request
to
a
proxy
interface.
That's
a
new
ICMP
message.
The
extended
ICMP
echo
request
identifies
the
probed
interface
by
address
if',
name
or
if'
index,
so
we're
making
a
distinction
here.
E
There's
a
probing
interface,
the
guy
who's,
sending
the
echo
request,
he's
sending
it
to
a
proxy,
and
the
echo
request
has
in
it
in
its
payload,
something
that
identifies
the
probed
interface,
the
proxy
and
the
probed
interfaces
are
different
from
any
one
another.
The
proxy
interface
receives
the
extended
echo
request,
determines
the
status
of
the
probed
interface
and
returns
an
ICMP
echo
reply
and
the
echo
reply
reports
the
status
of
the
probed
interface.
Now
this
probed
interface,
it
can
reside
on
the
same
node
as
the
proxy
interface.
E
So
say,
the
proxy
is
the
loopback
on
a
on
a
router
and
the
probed
interface
is
any
other
interface
on
the
router.
It
can
also
be
directly
connected
to
the
node
upon
which
the
proxy
interface
resides.
So,
let's
say
for
a
moment
that
you
send
your
your
echo
extended
echo
request
to
the
loopback
on
a
PE
router.
You
can
ask
for
the
status
of
a
seee
interface,
that's
directly
connected
to
the
PE
router.
B
E
Next
time,
I'll
have
fireworks
next
slide.
Okay,
how
do
we
determine
the
status
of
the
probed
interface?
Well,
if
the
probe
interface
is
on
the
same
node
as
the
proxy
interface,
it's
easy.
You
do
exactly
what
you
would
do
to
determine
the
IFR
status
and
mid-to
if
the
probed
interface
is
directly
connected,
if
it's
not
local
to
the
proxy
interface,
what
you!
What
you
do
is
take
a
look
in
either
your
ARP
table
or
your
neighbor
cache.
If
the
address
appears,
then
you
say:
oh
yep,
that
that
interface
must
be
there.
E
If
the
address
that
it
doesn't
appear,
you
assume
that
the
interface
does
not
exist
and
you
send
that
kind
of
response
back
next
slide.
So,
let's
take
a
look
at
some
of
the
differences
between
probe
and
ping
probe
tests,
two
things.
First,
a
test
bi-directional
connectivity
between
the
probing
interface
and
the
proxy.
If
you
don't
have
that
probe
won't
get
a
reply.
The
next
thing
it
tests
is
the
status
of
the
probed
interface.
If
the
probed
interface
is
down,
you
get
a
reply,
and
the
reply
says:
the
probed
interface
is
down.
E
E
Okay,
we've
talked
about
this
mysterious
new
ICMP
message.
Here's
a
few
details
about
it
like
any
ICMP
message.
It
has
an
IP
header.
The
destination
address
is
the
proxy
interface.
You
always
send
the
packet
to
the
proxy
in
the
ICMP
body.
The
type
is
to
be
determined
by
iana
there's
a
code,
a
checksum,
an
identifier
in
a
sequence
number
and
they're
all
the
same
as
the
traditional
ICMP
echo
request.
The
only
difference
is
that
the
sequence
numbers
only
eight
bits
long
and
that's
to
make
room
for
an
L
flag.
E
The
L
flag
tells
you
whether
the
probed
interface
is
local
to
the
Box,
are
directly
connected
to
the
box,
and
it
has
an
extension
structure
that
identifies
the
probed
interface
next
slide.
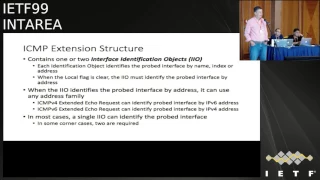
Okay,
the
identification
structure
has
one
or
two
interface
identification
objects.
They
identify
at
the
probed
interface,
either
by
name
address
or
I
F
index,
and
if
it
does
it
by
address,
it
can
be
any
address
type.
So,
let's
say
for
a
minute:
you
sent
a
I,
see
MP
v4
packet
to
a
IP
v4
only
loopback
address.
E
You
can
be
asking
about
a
interface
that
is
ipv6
only
and
identifying
it
by
its
ipv6
address.
Maybe
it's
ipv6
link
local
address.
Now.
This
link
local
thing
brings
up
the
kicker.
You
might
have
two
interfaces
with
the
same
link:
local
address
on
a
box,
so
sometimes
you
need
to,
inter
facial
identification
objects
to
uniquely
identify
a
probed
interface.
Next
slide.
E
The
extended
echo
reply
returns
exactly
two
pieces
of
information,
operational
status
and
what
protocols
are
active
on
the
interface.
It
doesn't
return
anything
else.
This
isn't
meant
to
be
an
SNMP.
Yet
on
the
all
the
attributes
of
the
Box,
it
just
returns.
Two
things:
it's
a
ping.
Look
like
next
slide:
okay,
use
cases.
Why
did
we
go
through
all
this?
Well,
the
use
case
I
was
thinking
about
when
we
started
this
as
I
wanted
it.
People
to
use
more
probe
on
numbered
interfaces,
and
the
reason
I
wanted
to
do
that
was
to
reduce
the
attack.
E
Surface
of
a
router
also
wanted
to
make
provisioning
easier.
So
you
don't
have
to
manage
all
these
addresses.
That
was
that
was
the
driving
one,
but
then
more
things
came
up,
for
instance,
what?
If
the
probing
and
probing
probit
know
what,
if
the
proxy
and
probed
interfaces
are
in
different
address
types
ones,
ipv4
ones
ipv6
or
what?
If
you
just
don't,
have
a
route
to
the
probed
interface,
you
only
have
a
route
to
the
proxy
okay
next
slide.
Ok,
here's
what
this
looks
like.
E
We
have
an
implementation
and
it
looks
strangely,
like
ping,
you
know
the
word
is
probe
here,
we're
querying
by
name.
So
it's
interface
and
the
name
of
an
interface
and
the
10-10-10
is
the
proxy
address
and
you
get
something
back.
That
looks
like
a
ping
next
slide
here.
Another
one
we're
querying
an
interface
by
its
link.
Local
address
next
slide.
Ok,
lots
of
security
possibilities
here,
lots
of
security
considerations.
You
can
use
probe
to
discover
things
about
a
box.
E
For
instance,
you
can
use
it
to
discover
if
you
find
that
it
has
an
interface
called
GE,
0
/,
0,
/
0.
You
can
infer
a
lot
of
things
about
that
box
like
who
the
vendor
is
maybe
what
version
of
code
it's
running.
Maybe
what
the
bandwidth
or
MTU
of
the
interface
is.
So
you
may
not
want
to
open
probe
up
to
anybody
next
slide.
E
So
what
are
the
mitigations
well
for
a
node
by
default?
It
doesn't
honor
ICMP
extent
extended
echo
requests
if
it
does
honor
them.
The
query
types
are
enabled
one
at
a
time
by
default,
they're
all
disabled,
so
you
would
have
to
enable
ICMP
echo
requests
and
only
queries
by
address,
not
queries
by
name.
If
that's
what
you
want
and
further
for
each
type
that
you
enable
you
can
specify
which
source
addresses
you
will
accept
the
query
from
so
that
way.
E
E
Okay,
the
status
we've
had
many
rounds
of
this
many
comments,
thanks
to
Jeff
Haas,
so
Nene
Jonathan,
Looney,
Carlos,
Pena
Tarot.
We
have
a
new
feature
thanks
to
med,
Boudica
Boca,
dare
med.
You
didn't
jump
up
when
you
heard
your
own
feature
I'm
heartbroken
and
we
have
a
working
prototype
thanks
to
Reggie
Thomas,
which
brings
us
to
our
next
slide.
I
think
we're
probably
weren't
ready
for
working
group
last
call
what
other
folks
feel,
but
first
questions.
F
So
comment
on
the
if'
name,
hand,
wing
one
thing:
I
was
trying
to
look
up
and
didn't
have
a
chance
to
you
before
you
got
there.
Is
that
I'm
inferring
an
answer
based
on
the
text
of
the
document
which
says
that
it
can
be
utf-8?
Yes
by
that
I'm
inferring,
that
it's
not
constrained
at
a
ASCII
character
set.
Yes,.
F
What
that
means
is
that
your
draft
is
currently
under
specified
and
it
does
not
guarantee
Nierop
ability
and
it's
easy
to
fix.
Alright,
now
that
says
utf-8,
but
it
does
not
discuss
normalization
for,
and
so
you
need
to
do
one
of
two
things
or
perhaps
both
you
need
to
either
say
that
the
sender
has
to
normalize
and
put
it
in
a
particular
normalization
for
them
like
NFC,
or
you
have
to
say
that
the
receiver
must
accept
anything
and
do
normalization
itself.
Otherwise,
the
lack
of
interoperability
happens.
F
If
the
sender
just
puts
it
in
whatever
its
natural
normalization
for
them
is
the
sender
does
a
byte
for
byte
comparison
against
its
internal
up
representation
and
they
use
different
normalization
forums
and
you
get
a
failure
and
that's
what
can
happen
today
and
your
confirm
it
to
the
specs.
You
got
it.
You
got
to
solve
that
problem.
I
get
interoperability,
okay,.
F
Second
part,
which
is
a
variation
of
the
same
things.
You
say
if
the
if'
name
was
longer
than
255
octets
you
truncate
at
255
octets.
Yes,
a
problem
with
that
is
when
you
truncate
a
UTF
string
at
255
octets.
What
you
get
is
a
non
utf-8
string,
because
you
can
be
truncating
right
in
the
middle
of
a
character,
and
so
you
can't
do
that,
and
so,
if
you're
going
to
truncate,
you
have
to
Krunk
8
on
a
character
boundary
which
is
not
a
255
octets.
It's
at
255,
octets,
truncated.
H
B
J
Hi
there
alright
I
was
here
about
a
year
ago-
we're
not
here
here,
but
in
this
working
group.
This
is
a
draft,
that's
being
fast-tracked
through
TS
vwg,
intended
to
go
to
law
school
working,
great
law
school
in
October
now,
so
we
want
eyes
on
this
because
it
actually
updates
interior
protocols
next.
J
So
this
is
what
the
problem
is.
I've
now
labeled,
this
problem
number
one
because
there's
another
problem,
but
the
main
one
is
that
when
you're
tunneling
IP
headers,
you
ACN
is
unlike
any
other
field
in
that
not
only
does
it
have
to
go
down
the
layers
as
you
encapsulate,
and
not
only
can
it
change
once
it's
down
the
layers,
but
then
you
also
have
to
propagate
the
change
back
up
the
layers
right,
and
there
is
no
other
field
like
that.
J
As
far
as
I
know,
and
so
at
the
egress
shown
in
that
little
table,
that's
deliberately
too
small
to
read
is
a
matrix.
That's
already
in
RFC
6040
of
what
the
outer
header
is,
what
the
inner
header
is
and
how
you
calculate
the
forwarded
header.
Then
the
problem
is
on
the
last
bullet
main
bullet
of
those
three.
J
If
the
D
cap,
as
shown
where's
the
if
the
decap
here
shown
in
Y,
does
not
support
that
function,
you
must
zero
the
UCM
field
before
you
put
it
into
the
tunnel,
because
otherwise,
if
you
have
just
copy
the
ecn
field-
and
there
are
ACN
capable
machines
network
elements
along
here
that
market,
those
markings
will
not
get
propagated
back
up.
They'll
just
get
dropped
on
the
floor
when
it
D
capsule,
eights
and
then
all
hell
breaks,
loose
and
all
hell
breaks.
J
So
the
problem
with
this
is-
and
we
only
realize
this
recently-
that
we
specified
that
tunnel
behavior
for
nodes
that
want
to
comply
with
EC
n.
But
the
problem
is
this
requirement.
Is
for
knows
whether
or
not
they
comply
with
ec
n?
All
all
tunnel
nodes
have
to
do
this.
This
is
not
just
if
you
want
to
comply
with
e
CN,
and
so
what
we've
had
to
do
is
make
this
a
requirement
for
operators
to
configure
it
not
just
for
implementers
right.
J
L2Tp
tunnels
treat
that
as
a
toss
bite
and
the
configuration
of
diffserv
behavior
can
be
configured,
but
it
treats
the
two
bits
in
the
six
bits
as
just
eight
bits,
and
it
can't
treat
them
differently.
So
we've
put
a
very
strong
requirement
in
their
implementations,
must
D
capital
e
CN
and
diff
surco
point
configuration
because
otherwise
operators
can't
even
do
that.
So,
as
you
know,
potentially
the
problem
here,
not
a
problem
at
all.
If
there's
nothing
inside
the
network,
that's
actually
marking
ecn,
but
those
sort
of
nodes
are
now
appearing.
J
J
Now
what
this
draft
was
originally
trying
to
solve
was
the
problem
that
RFC
64
Tiye
that
defines
the
behavior
of
tunnels
and
ECN.
It
wasn't
potentially
clear
what
the
scope
was.
It
said
all
IEP
in
IP
tunnels,
and
this
update
clarifies
that
that
includes
IP
and
IP,
with
stuff
in
between
with
shims
with
layer,
two
and
shims
and
so
on.
So
the
outer
is
on
the
bottom
here,
I'm
going
to
call
this
IP
shim,
possibly
layer,
two
and
possibly
IP
inside.
J
But
if
you
don't
necessarily
know
whether
ip's
inside
I
feel
you
don't
have
to
look
that
deep.
But
if
you
don't
know
you
have
to
zero
the
outer
IP
in
case
there
is
an
IP
header
inside
right,
so
we
have
a
look
through
and
surveyed
what
standards
track.
Rfc's
we've
got
that
I
like
this
IP
shim,
IP
or
IP
simulator
IP
and
your
guys
have
obviously
been
busy.
J
Obviously
there
are
differences.
You
know
it's
a
broad-brush
statement,
but
so
what
this
quickly,
what
this
table
does?
We've
had
to
ignore
anything:
that's
not
widely
deployed
or
standards
track,
so
anything
with
a
cross
there.
Where
we're
there.
We
know
other
entry
in
the
table.
A
okay
means
it
specifies
what
to
do
with
the
ecn,
headers
and
we're
fine
I'll
come
unto
what
the
exceptions
mean.
J
No
K,
not
okay,
there's
two
possibilities.
One
is
that
this
draft.
We
have
written
update
text
into
this
draft
and
the
other
is
that
it's
not
an
ITF
tunneling
protocol,
it
maybe
there's
an
IETF
RFC,
but
we're
not
in
control
of
it.
So
I
want
you
guys
to
look
if
we
can
just
pop
back
to
the
last
slide:
Teredo
Gerry,
lttp
v3,
the
lttp
guys
are
reviewing
that.
J
J
The
three
questions
I've
got
in
that
table,
it
says
SFC
is,
is
not
applicable
because
they
haven't
defined
an
actual
end
cap
relation
is
that
true,
and
the
second
question
is:
is
it
true
that
there
are
no
automated
GRE
tunnel
set
up
protocols
because
I
can't
find
any,
but
you
guys
should
know
where
there
is,
and
no
one
in
TSP
knew
this
and
Turay
do
I'm
dealing
with
that
with
Praveen
in
Microsoft.
So.
K
Tom
is
Rahim
Oval,
so
there
was
some
discussion
about
this
in
the
NGO
3
mailing
list,
mainly
regarding
the
X
line
in
Geneva
and
correct
me.
If
I'm
wrong,
the
way
I
understand
it
is
that
actually
each
RFC
that
defines
an
encapsulation
over
IP
and
IP
encapsulation
will
need
to
define
to
have
a
section
that
says
what
happens
in
terms
of
EC
and
propagation
right,
and
so
my
question
is:
would
it
be
possible,
in
this
draft
to
define
a
small
set
of
options
like,
for
example,
the
way
to
propagate
ecn
is
option?
J
J
Already
in
the
base
set
this
up
just
updates
that
to
say
this
is
basically
this
defrost.
It
exists
merely
to
put
update
text
in
for
protocols
that
legacy
protocols
that
all
need
to
be
updated
to
point
to
that
spec
and
say
what
you
have
to
specifically
do
for
those
legacy
protocols
like
lttp
GRE
things
like
that
in
the
original
spec
there's
two
modes
and
exactly
what
you
want.
This
compatibility
mode
and
normal
mode
in
the
compatibility
mode
is
the
zero
in
the
outlaw
and
that's
what
we
need
to
do
so.
Actually.
K
J
L
L
We'll
do
look
at
all
of
these
protocols.
Control
protocols
see
what
we
have.
You
know.
We
have
considerations
on
how
to
create
GRE
tunnels.
We
have
to
look
at
those
look
at
the
text
and
say
how,
to
you
know
whether
the
text
is
you
know
goes
with
you
know,
or
further
updates
on
me
right
now.
Okay,
thanks.
M
N
Ccwg
chair
you
ever
going
to
last
call
this
wherever
it
is.
What
I
got
to
say
was
that
the
earlier
discussion
about
options,
let's
just
double
check-
that
we've
got
all
the
right
text
on
this
and
the
options
in
the
tunnels
draft,
because
people
aren't
gonna
come
looking
for
this
easy
enough
when
they
put
in
the
next
tunnel,
but
we
hope
they're
gonna
go
we'd
the
tunnels
BCP,
and
so
we
need
to
make
sure
that
they're
that
that
their
I
think
I'm
pretty
sure.
N
E
J
K
Okay
thanks:
my
name
is
Tom
Mizrahi
I'm
from
Marvel,
and
this
draft
defines
guidelines
for
specifying
packet
time
stamp
format,
its
joint
work
with
your
team
Fubini
and
without
morton,
and
actually
this
draft
is
submitted
to
the
interior
working
group.
It
was
also
presented
this
week
in
tick-tock
and
NTP
will
talk
a
bit
later
on
about
which
working
group
is
the
right
place
for
it.
Next,
please.
K
So,
when
general
time
stamps
are
pretty
useful
in
the
RFC
series,
they've
been
used
in
a
lot
of
our
FCS,
we
distinguish
between
two
main
types
of
time:
stamps,
text-based,
time
stamps
and
packet
time
stamps.
So
here
is
an
example
of
a
text-based
time
stamps
for
a
net-net
account
for
our
PC
in
this
case,
and
there
is
also
an
example
of
a
packet
time
stamp.
This
is
the
ntp
packet
format.
The
main
difference
is
the
text-based
time.
Stamps
are
intended
to
be
more
user
friendly.
They
don't
necessarily
have
a
fixed
length
and
packet
time.
K
Stamps
have
a
fixed
length.
They
need
to
be
compact.
They
need
to
fit
into
a
packet
header.
Next,
please
so,
like
I
said
text-based
time,
stamps
are
used
in
a
lot
of
our
FCS
and
they're.
Their
format
is
defined
in
RFC
3
3,
3
9,
and
these
are
a
few
examples.
There
are
a
lot
of
other
examples
of
RFC's
that
use
these
text-based
formats
packet
time
stamps
are
also
very
widely
used.
K
This
is
again
a
short
list
of
some
of
the
our
fees
that
use
it
next,
please,
and
there
are
also
a
lot
of
internet
drafts
that
are
currently
in
progress,
which
also
use
packet
time
stamps.
Now
the
main
issues
that
we're
trying
to
address
here.
First
of
all,
there
is
no
common
time
stamp
format
for
the
packet
time
stamp
variant.
That's
one
issue,
and
the
second
issue
is
that
a
lot
of
these
drafts
are
RFC's,
define
their
own
back
a
time
stamp
formats.
K
Another
problem
is
that
the
way
these
formats
are
defined
are
sometimes
very
different
from
each
other
and
in
many
cases
the
time
stamp
is
the
in
somewhat
unclear
way
or
ambiguous.
So
these
are
the
main
problems
we're
trying
to
deal
with
next,
please
so
the
goal
of
this
draft.
First
of
all,
to
define
a
relatively
small
set
of
recommended
packet
time
stamp
formats
and
also
to
define
guidelines
of
how
to
specify
new
packet
times
and
formats
next,
please.
K
So.
These
are
basically
the
recommended
time
stem
formats
that
were
currently
presenting
in
the
draft.
So
we
have
two
formats
which
are
based
on
NTP
64-bit
format
and
a
32-bit
format,
and
there
is
also
a
64-bit
format
which
is
based
on
PT
P,
and
the
idea
is
that,
if
you're
going
to
use
a
timestamp
in
network
protocol,
that
typically
runs
on
a
PC
or
on
a
server,
you'll
often
want
to
integrate
that
with
NTP.
K
And
then
you
often
want
to
use
an
NTP
based
format
and,
on
the
other
hand,
if
you're
going
to
implement
a
network
protocol
that
typically
runs
on
hardware
or
sometimes
PGP
is
used.
It
makes
more
sense
to
use
the
PTP
base
timestamp
format.
Next,
please,
okay,
so
expect
that
in
most
cases
the
timestamp
formats
we
saw
in
the
previous
slide
will
fit
most
scenarios
most
requirements.
However,
in
some
cases
we
understand
that
people
will
have
different
requirements.
K
Another
aspect
that
is
discussed
in
this
draft
is
an
optional
control
field.
So,
in
a
lot
of
cases,
if
you're
using
a
packet
time
stamp,
you
will
need
some
control
information
about
that
time
stamp.
So,
for
example,
that
control
information
can
include
what's
the
time
stamp.
Format
is
what
is
the
precision
or
resolution
of
the
time
stamp?
What
is
the
epoch,
the
era
and
we're
actually
looking
for
feedback
about
what
kind
of
control
information
you
believe
may
be
required
in
this
aspect?
K
Next,
please,
okay,
so
this
draft,
the
first
version
of
this
draft
was
submitted
in
the
last
month
or
so
submitted
it
to
the
internet
area
working
group.
One
of
the
things
we
were
looking
for
is
feedback
about
what
is
the
correct
working
group
to
consider
the
this
draft
and
the
feedback
we
received
from
Suresh
was
that
probably
the
best
way
or
the
best
place
to
discuss
this
would
be
in
tick,
tock
and
NTP.
K
J
J
In
ttpm,
there's
currently
work
on
just
starting
on
redefining
the
TCP
timestamp
or
at
least
agreeing
on
various
timers
at
either
end,
and
then
you
have
to
agree
the
clock,
granularity
and
things
like
that.
So
the
units
you've
got
there
is:
are
you
using
a
standardized
format
for
that
or
you're
having
to
invent
a
format
for
units?
Because
that's
the
big
problem?
It's
it's!
What
resolution
is
each
end
talking
about.
K
J
Cuz,
because
you
know
clock
out
a
lot
of
the
timestamps
in
the
past,
we
rent
of
a
millisecond
so
granularity
and
we're
now
needing
something
nanosecond.
You
know,
and
so
you
you've
got
a
one
problem.
Is
you
need
more
bits,
because
the
wrap
is
is
greater
because
you
got
more
packets
on
the
wire
any
one
time,
but
the
other
problem
is:
what
is
the
resolution
that
you're
talking
about
it?
Be
Jen
right.
J
O
Korea
Montenegro,
so
I
did
notice
that
you
had
on
the
list
of
existing
work
document
out
of
six
slow
working
group
and
I'm
wondering
if
you're
going
to
operate
in
sort
of
like
mid
doctor
and
be
packet,
for
you
know
time
stamp
doctor
that
thing
cuz.
So
I
would
like
to
to
ask
you
for
review
for
that,
as
working
group
co-chair
of
six
though,
and
it
would
be
good
to
have-
you
will
be
on
that
document.
On
the
six
document
it's
already
listed
there,
six
low
lie
Joe
six
thought
spiration
time
whatever.
O
K
P
P
P
So,
basically,
in
the
legacy
world,
which
means
you
know
the
stuff
called
ipv4
with
dotty
teresa's,
you
select
one
interface
only
and
you
go
and
you
use
that
to
ensure
that
the
traffic
is
coming
back
through
the
same
network,
but
typically
that's
not
what
we
want
to
do
in
v6.
Next,
in
the
case
of
20
roaming
for
v6,
you
will
get
provide
equitable
or
provide
you
assign
addresses
from
all
service
providers.
P
So,
in
the
case
of
the
previous
slide,
you
will
get
three
prefixes
and
you
can
select
as
many
addresses
among
those
three
prefixes
and
again
is
bare
minimum
3,
some
reference
there
now.
The
question
is
that
all
the
application,
all
the
hosts-
can
select
one
of
several
in
the
case
of
multiple
CCP
addresses,
which
is
the
next
stop,
which
is
the
DNS
resolver,
I'm,
using
and
so
on,
and
so
on.
So
there's
basically
the
problem
we
are
trying
to
solve
here.
Next
and
interestingly
enough,
this
issue
has
been
raised
multiple
time
this
week.
P
P
So
now,
if
you
have
in
the
branch
of
Microsoft,
both
connectivity
through
I,
guess
some
MPLS
VPN
or
VPN
whatever
and
connectivity
to
a
local
service
provider,
the
holes
there
will
receive
two
prefixes
one
from
the
Microsoft
IT
one
from
the
service
provider.
Source
address
selection
in
this
case
will
work
fine
if
you
want
to
go
to
the
Internet.
P
But
if
you
want
to
go
to
the
Internet
to
reach
any
cloud
services
in
Azir,
guess
what
you
will
select
the
address
to
go
to
the
corporate
level
and
then
you
want
to
type
nothing
can
be
fixed
really
easily
there
next
another
one
and
that
you
are
here.
You
presented
this
when
you
have
to
interface.
I,
know
to
to
interface
you
receive
through
array
or
DHCP
or
whatever
DNS
resolvers
addresses.
You
need
to
be
sure
that
you
are
sending
a
request
to
a
DNS
resolver
from
that.
P
The
address
associated
to
this
interface
else,
you
will
receive
a
reply
which
is
not
correct.
Think
about
the
geolocation
right
I'm
connected
to
the
VPN
of
my
employer.
Right
now.
He
believes
I'm
in
Amsterdam
and
as
far
as
I
know,
we
are
proud
right
so
that
there
ask
an
address
to
my
VPN
provider.
I
will
be
redirected
to
a
Tamiya
plots.
They
are
in
Amsterdam,
not
in
fact
there's
a
problem
next
another
one
and
Cristiano
is
here,
don't
know
whether
Fernando
is
here.
What
about
an
application?
P
I
am
as
a
client
that's
kind
of
easy,
but
if
I
am
the
listener,
the
server,
if
I,
do
a
bind
and
I
want
to
listen
to
all
addresses,
but
should
I
listen
to
all
addresses
or
only
part
of
the
addresses
open,
I've
selected
this
we
need
to
expand
there
as
well
next,
so
in
short,
I
wanted
to
prove
you
that
they
are
use
case.
Real
problem,
I
mean
I
was
not
aware
that
Ted
and
Christian
other
who
be
presenting
this
this
week.
So
that's
a
real
problem
to
be
addressed.
P
P
The
set
of
information
into
the
array
is
limited,
but
you
know
to
get
more
information
like
pricing.
Is
there
a
cactus
porter?
Is
there?
Is
it
a
walled,
garden
network
and
so
on?
And
so
on?
Come
back
on
this
and
a
el
flag,
which
is
main
that
you
can
build
this
visits
information
with
some
ipv4
information
you
get
through
DHCP
before
so
how
does
it
work
next?
P
The
client
on
the
Left
starts
and
you
receive
a
rotted
attachment,
including
this
option.
If
the
client
doesn't
know
this
option,
this
fare
will
get
the
array
and
will
use
it
as
usual,
that
we
know
the
option
and
if,
in
the
option
there
is
the
age
standing
for
HTTP,
it
will
simply
go
and
to
the
specific
URI
we
use
the
PVD
ID,
which
is
in
the
array,
dot,
well-known
/pv
and
get
the
information
next
by
this
HTTP
connection,
and
we
use
HTTPS
on
purpose
here.
P
P
The
bundles
are
the
prefix,
the
route
information,
the
next
of
the
DNS
search
phase
and
the
DNS
server,
because
then
we
solve
that
problems
right.
We
always
go
by
an
interface
using
this
address
to
go
to
this
DNS
server.
We
make
those
windows.
There
are
this
kind
of
Venn
diagrams
here
and
it's
up
to
the
host
or
Motorama
to
the
application
to
select
whether
you
use
any
of
those
like
the
firefox
and
safari
here,
or
you
use
only
the
red
bindle
like
Skype,
or
you
use
the
green
vendor
like
VLC
here
next,
where
are
we?
P
This
is
actually
very
easy
to
implement.
This
is
just
another
array
option.
You
need
to
change
the
semantics
into
the
stack,
which
is
a
bit
more
complex.
There
are
open
source
code,
so
Pierre
and
myself
are
working
on
this
with
another
guy
in
Paris,
where
basically,
we
work
on
manage
so
the
Linux
client
receiver
is
there
with
patches.
We
have
big
a
wash
rag
dissector,
so
we
can
display
all
those
option
of
the
were
shocked.
We
modified
IP
route.
We
modify
our
a
DVD
and
in
this
ayat
II
have
a
curtain
over
the
weekend.
P
P
That's
what
we
did
and
Tom
Jones
into
the
new
project
and
Doreen's
there
as
well.
I
made
some
integration
with
the
need
project,
which
is
kind
of
middleware
at
the
transport
layer.
Next
and
tonight,
at
the
bits
and
bytes
please
come
and
see
us,
ok
and
myself
will
be
there.
We
can
show
you
there
or
we
make
something
working
with
the
captive
portal.
Next.
P
Ok
last
slide
next
step
for
us,
we
see
very
useful
feedback
during
the
Akata,
so
peer
is
currently
working
on
it
to
upload
the
0
things
like
using
a
well-known
URL
rather
than
something
else.
Now
we
really
really
welcome.
It
is
one
of
the
reason
why
I'm
here
in
this
room
today,
we
really
want
to
get
feedback
so
who
read
it
by
the
way?
Oh,
oh,
so
something
like
the
ten
people.
So
all
of
you
please
comment
on
the
list
on
all
three
yeah.
L
Three,
so
the
question
is
in
myth
working
group
we're
a
couple
of
time.
Pvd
documents
right,
one
was
MVP,
one
was
DHCP,
those
were
working
real
documents,
so
I
asked
what
changed
they
were
killed.
They
didn't
move
forward
and
suddenly
veer
what
words.
What's
the
disconnect
here
between
the
two
I
won't.
P
L
A
that's
too
much
of
a
detail
right,
but
but
but
the
key
thing
is
they're
very
high
level.
Those
drafts
tried
to
solve
this
problem.
I
think
that's!
That's
you
know.
As
a
co-author,
you
know
at
least
two
of
those
documents
right,
I'm,
usually
they
take.
Those
documents
forward
are
somehow
consolidate
that
work.
That
would
be.
You
know,
I'm
not
objecting
to
this
I
like
this
world,
because
prefix
coloring
is
something
that
I
started.
Actually
I
introduced
that
term
okay.
Q
Q
So
the
whole,
the
network
needs
to
pick
a
prefix
for
the
host
if
it
doesn't
support
pvd's
I,
don't
think
that
that
means
that
I
think
that
this
can
go
forward
independently
of
what
I
just
said,
I,
don't
think
the
two
things
are
that
there's
a
cross
requirement
there,
but
I'd
like
to
see
work
happen
on
that
as
well.
We
just
make
sense.
Thank.
R
You
Lorenzo
clearly
two
trees,
partly
in
response
to
three,
so
there
are
a
few
things
that
weren't
wrong
with
myth,
one
of
them,
of
course,
being
that
the
working
group
was
shot
in
the
head.
I
still,
don't
know.
How
is
how
that
happened
because
it
was,
it
basically
happened
overnight.
An
ITF
I
wasn't
there
as
like.
Okay,
the
working
group
has
been
closed,
have
a
nice
day,
all
right,
fine.
So,
but
the
really
I
think
this
is
a
contra
nation.
That
story.
R
Another
thing
that
I
have
to
say
against
address
that
came
out
of
Memphis
that
they
tried
to
do
way
too
much
with
way
too
little
OS
spender
support,
and
that
is
not
the
case
for
these
current
efforts.
I
think
we've
got
a
line
of
sight
to
actual
implementers
building
this
stuff.
So
you
know
the
running
code.
Part
of
it
is
is
way
more
true
here
than
it
was.
Then
there
was
an
IPR
claim
that
we
all
stayed
away
from
which
was
sort
of
I.
R
Don't
know
if
that
was
part
of
the
reason
why
the
working
group
was
closed,
and
so
there
there
are
a
number
of
things
wrong.
That
we
think
we
did
learn
from,
and
so
these
efforts
are
in
some
sense,
a
continuation
of
those
a
little
bit
d
scoped,
but
probably
more
more
realistic
in
terms
of
actual
implementation,
d-dave
nodding
his
head,
so
he's
I
think
we
have
I
forget
who
the
authors
are
here.
I
know
it
doesn't
include
any
of
us,
but
I
think
Apple,
maybe
is
the
north.
Are
you
is
that
right
now.
P
P
M
M
M
S
Berni
volts
I
want
to
just
follow
up
on
Ted.
That
I
think
you
do
need
to
consider.
You
know
either
doing
what
Ted
suggested
or
at
least
documenting
what
the
impact
is
of
sending
these.
These
are
raised
with
pvd's
to
devices
that
don't
understand
them
right
that
that
will
just
process
them
as
normal,
Ras
or
I.
Forget
I
think
that's
what
I.
P
S
G
P
G
P
G
P
Kind
of
true,
but
when
you
say
the
age
I,
don't
remember
the
explicit
wording
we
use
into
the
draft.
We
say
when
you
see
the
age,
you
should
get
back
the
additional
information.
The
additional
information
is
not
really
critical
compared
to
routing
or
to
addressing
but
you're
right.
If
we
cannot
get
the.
G
T
U
Didn't
understand
the
problem?
Well,
let
me
take
another
take
of
Bob's
problem
statement,
a
Christian,
Rita
ma
what
you
have
there
is
a
signal
that
says
to
the
host:
go
to
that
website,
connect
to
it
and
go
fetch
a
page
if
you
do
that
with
a
normal
HTTP
stack,
you'd
end
up
carrying
cookies
and
all
that
kind
of
stuff
know
you
might.
In
any
case,
you
get
a
signal
that
you
have
this
connectivity
and
having
an
outside
connectivity
like
that.
When
doing
it
a
core
of
all
Internet
is
not
it's
not
free.
U
It
has
a
privacy
implication.
Okay,
so
there
is
a.
There
is
a
very
different
spice
it
Monsieur
between
go
fetch
information
remotely,
which
means
that
you
will
have
lots
of
traces
all
over
the
network
and
finding
in
your
DHCP
server
in
or
something
like
that,
which
is
local.
So
there
are
policy
implication
on
anything
like
that.
It's
it
looks
cool.
It
looks
easy,
but
I
I.
U
P
U
Go
you
don't
go
it's
it's
in
practice.
It's
not
something
that
the
user
is
going
to
decide
on
a
connection
by
connection
basis.
It's
easily
fit
us
turn
on
or
turn
off
and
I
mean
I.
Dare
you
explain
that
to
your
family
that
hey
where's,
this
new
nominee
OS
that
lets
you
choose
between
multihoming
and
privacy?
Right
it'd
be
better
if
this
was
more
local,
okay,.
P
But
su
got
the
point
here,
but
it
was
the
difference
if
you
receive
into
a
normal
array.
Please
use
this
DNS
server
as
a
recursive
DNS
server.
You
will
also
go
to
the
Internet
to
this
recursive
server
resolver
and
basically
you
will
also
invade
your
privacy
right.
That's
the
same
thing:
I
don't
see
sending.
U
Request
that
is
not
actually
true.
I
can
configure
my
DNS
software
to
always
go
to
a
trusted.
Dns
resolver,
whatever
the
network
says,
can
you
explain
this
to
your
family
member?
Oh
yeah,
you
use
private
DNS
and
that
way
you
will
not
be
snooped
off
by.
You
is
V,
that's
as
very
easy
to
explain.
Okay,.
V
Tommy
Poly,
so
as
author
I
mean
thank
you
for
bringing
up
that
point,
I
think
it's
good
to
considering.
We
should
probably
clarify
it
stuff
around
that.
A
couple
things
one
like
a
lot
of
this
is
seems
similar
to
what
we
already
do
with
a
captive
portal
today,
I
join
a
network
in
general.
The
system
on
your
behalf
does
an
HTTP
probe
and
it's
being
redirected
and
that's
how
you're
getting
all
this
information
you
have
no
idea
what's
happening
there.
V
The
goal
with
this
is
to
try
to
improve
that
experience
that
the
the
resource,
you're
fetching,
ideally
in
a
lot
of
cases,
would
not
actually
be
over
the
Internet.
It
could
just
be
locally
hosted
and
probably
should
be,
and
the
idea
is
that
at
least
this
will
be
a
secure
connection
rather
than
the
completely
clear
text
Pro,
but
your
systems
doing
on
your
behalf
pretty
much
any
time
it
joins
the
network
anyway,.
F
Hey
Dave,
Taylor,
Rena
and
I
got
up
at
the
same
time
because
I'm
gonna
segue
and
let
him
cover
at
the
part
that
he
was
gonna
talk
about
the
I
was
gonna
sort
of
rephrase.
What
I
think
Bob's
question
is
Bob's
question
is
not
about
the
identification
part
which
I
think
is
the
part
that
learns
oh,
is
going
to
talk
about,
but
but
how
you
get
the
sort
of
the
bag
of
properties
that
you
showed
and
in
order
to
get
that,
that
means
that
you
have
to
be
able
to
do
things
like
resolve
the
fqdn.
F
You
have
to
be
able
to
route
to
the
set
of
IP
addresses,
that's
there
and
in
order
to
correctly
wrap
in
the
set
of
IP
addresses,
and
you
correctly
resolve
that
you
might
need
to
have
the
bat
that
may
give
information
to
make
the
correct
decision,
which
is
a
little
bit
of
a
circular
dependency
and
that's
where
bob
was
coming
from
now.
That's
the
question:
if
you
have
a
good
answer
to
that,
please
answer
it,
but
I
think
that's
what
bob
was
worried
about.
Is
it
more
or
less
circular
dependency?
G
But
you
know
it's
just
it's
you're
for
this
to
work,
the
way
it's
written
and
I,
don't
you
you
got
to
make
it
so
it
does
one
thing
not
make
it
all
optional
based
on
how
something
is
configured
and
well,
it
would
be
not
deterministic,
but
my
concern
is
this:
is
this
relies
on
all
kinds
of
mechanisms
to
work
correctly
or
not
be
subverted
or
for
this?
And
if
you,
you
should
maybe
think
about
some
other
ways
of
getting
this
information
without
relying
on
the
DNS
and
the
web
and
routing
and
DP.
G
F
Yeah
and
as
whoever
was
up
here
before
Bob
mentioned,
it
was
the
author
is
in
MIFF
right,
there
would
say:
well,
let's
just
put
it
all
in
the
RA
right
which
doesn't
have
the
problem
that
we're
talking
about
here
or,
let's
just
all
put
it
in
a
dhcpv6
response
or
whatever
else,
it's
just
embedded
on
one
place.
You
don't
have
the
extra
dependencies
you
just
have.
F
R
Lauren's
clearly,
I
think
a
couple
of
points
so
Christian
I
think
you're.
You
asked
the
wrong
question,
but
it
wasn't
that
it
was
close
to
the
right
question
and
I
think
I
think
the
question
was
not
like
why
it
is.
Why
are
you
doing
this
as
privacy
implications,
because
in
reality,
if
I'm,
if
I'm
a
reader
on
the
network
and
I,
want
you
to
connect
to
me
I
just
spoof
the
DNS
response
for
connectivity
checked:
oh
gee
static,
comm,
captive
door,
apple.com
and
whatever
is
that
Microsoft
uses,
and
you
connect
it
to
me.
R
Okay,
so
you
know
that,
let's,
let's,
let's
move
that
aside,
that
said,
we
do
need
and
I,
don't
think
we
I,
don't
think
you
do.
A
privacy
section
explains
how
this
is
no
worse
than
current
operating
systems
today,
because
I
do
believe
that
it's
no
worse
because
those
connections
are
going
out
as
soon
as
we
can
act
on
very
popular
operating
system.
So
we
do
need
to
show
if
we
want
to
do
this,
that
it
is
essentially
no
worse
than
we
have
today,
which
is
a
first
affirm
right.
So
we
do
have
to
do
that.
U
R
R
Reasons
the
reasons
we're
doing
something
bad
today
are
non
technical
reasons
that
are
not
gonna
change.
Yes,
we'll
have
private
DNS
I
agree,
and
this
is
gonna
be
authenticated
right,
but
those
probes
are
still
gonna,
be
there
and
they're
gonna,
be
there
approximately
forever
right,
so
I
don't
but
yes,
I,
like
I
said
you
asked
almost
the
right
question
and
the
questions
like
why?
Don't
you
have
a
privacy
section
and
that's
the
that's
I
think
the
right
course,
because
I
think
I
think
we
do
need
to
get
this
information.
As
for
like
being
tracked?
R
Well,
you
know
once
you,
you
know
you
contract
those
HTTP
requests,
even
if
them
some
magic
future
rolled
what
captive
portals
don't
exist,
we
stop
doing
those
HTTP
requests.
You
can
still
track
that
someone's
on
the
network
by
looking
at
their
packets
right.
It's
really
like
there
there
you
know
they're
there
right
so
and
to
respond
to
to
Bob
I.
Think
the
PVD
ID
gives
you
two
things
Bob.
R
It
gives
you
first
of
all,
it
gives
you
an
anchor
where
you
can
say:
look
this
thing
exists
and
if
you,
if
you
receive
other
information,
maybe
there's
another
Rooter
on
the
link
that
is
in
the
same
PVD,
maybe
you
have
existing
configuration
about
that
PVD,
like
a
mobile
network.
Name
like
you
know,
the
verizon
network
has
this
host
name.
R
Maybe
you
have
some
pre-existing
configuration
a
VPN,
client
or
something,
and
you
attach
those
with
that
ID
and
you
have
a
secure
way
of
authenticating
them,
so
you
can
merge
them
and
the
other
thing
that
it
gives
you
is
yes,
the
ability
to
use
that
ID
to
fetch
things.
The
nice
thing
about
putting
it
here
is
that
the
RA
gives
you
atomically
and
that's
very
important.
It
atomically
gives
you
all
the
bootstrapping
information
that
you
need
to
make
this
request.
It
gives
you
an
IP
address.
R
It
gives
you
a
DNS
server,
and
it
gives
you
this
this
name.
That
is
opt
that
you
can
optionally
use.
Even
if
you,
even
if
you
use
the
ID
to
merge
things,
you
don't
have
to
fix
the
metadata.
The
metadata
is
there.
If
you
want
more
information
about
what
the
network
provides
such
as,
is
this
network
metered
or
you
know,
does
this
network
provide
access?
Is
it
a
CAPTCHA
for
things
like
that,
so
it
serves
these
two
things,
I,
don't
know
if
this
is
explicit
in
the
drive,
but
it.
R
U
Christianism
again,
obviously,
we
need
some
privacy
consideration,
but
I'd
like
to
basically
make
sure
that
we
also
have
some
privacy
mitigations.
That
being
said,
there
is
another
issue:
okay,
what
prevents
the
coffee-shop
from
pretending
the
horizon
presently
what?
What
prevents
the
coffee-shop
water
from
preventing
that
pretending
that
they
otherwise
are
now
some
say
so,
and
this.
U
P
So
if
you
are
a
coffee
shop
somewhere
in
Prague,
and
you
pretend
to
be
Starbucks
in
u.s.
okay,
you
will
of
course
go
Starbucks
us
who
don't
know
the
TLS.
You
get
the
JSON
you
get.
The
router
should
be
this,
and
this
and
this
address-
oh,
it's
not
mingo.
You
refuse
it
or
whatever,
and
there
are
additional
techniques
as
well.
I
yeah.
G
Pop
hindering
I
am
Not.
Sure
I
may
be
misinterpreting
what
you
said,
but,
as
we've
learned
recently,
HTTPS
does
not
mean
that
who
you're
talking
to
is,
who
you
think
you're
talking
to
it
means
that
you
get
a
secure
channel
to
it
it.
You
know
we
saw
this
thing
with
free
certs
that
bad
people
can
get
them
to,
and
so
I
don't
think
just
because
it's
a
cheap
HTTPS
that
it
ensures
that
you're.
Talking
to
that
who
you
think
you
are.
V
Pommie
poly
Apple
again
I
just
want
to
tack
on
to
the
emphasis
that
we
should
look
at
the
kind
of
step,
one
and
a
step
to
separately
that
the
primary
goal
of
the
step,
one
is
to
say
that
when
I'm
in
a
situation
which
I'm
getting
these
multiple
sets
of
Ras
and
information
to
begin
with
and
I
have
this
plurality
of
information.
That's
provisioning.
I
have
multiple
previous.
V
This
I
have
multiple
DNS
configs
to
say
that,
yes,
the
network
knows
what
it's
doing
and
that,
at
least
within
this
scope
of
my
access
that
these
are
two
different
things
that
are
consciously
two
different
things:
I
can
use
separately,
and
that
is
the
only
thing
you
really
have
guaranteed
the
secondary
step
of
getting
more
information.
I
believe
in.
V
Q
Ted
lemon,
so
actually
to
speak
briefly
to
to
that
point.
There
are
security
implications
to
this
in
the
sense
and
I
I.
Imagine
I
haven't
actually
read
the
draft,
so
I
imagine
you've
already
addressed
these,
but
just
to
bring
them
up
to
the
mic
that
if,
if
you're
able
to
say
my
service
is
free
or
you
know
my
service
is
really
fast,
then
you
can
actually
convince
the
the
host
to
route
through
you
when
your
service
actually
isn't
free
and
and
thereby
deplete.
Q
T
Q
Yeah,
so
so
so
so
that's
a
that's
a
bit
of
a
concern
and
and
I'm
not
quite
sure
how
to
address
that.
The
other
thing
that
I
there's
two
other
points
that
I
wanted
to
make
one
is
that
in
terms
of
ops
in
terms
of
operations
and
in
dependencies,
if
you
actually
want
your
network
to
work,
you
have
to
make
this
work
like.
It
has
to
be
possible
to
reach
the
HTTP
HTTP
server
without
knowing
the
PVD
stuff,
because
otherwise
it's
not
going
to
work.
Q
You
you
just
learned
a
valuable
lesson
and
the
actual
point
that
I
wanted
to
make
is
that
one
of
the
things
we
talked
about
in
myth,
which
I
think
was
actually
kind
of
important-
is
that
it's
it's
because
we
have
to
deal
with
the
case
of
with
the
use
case
of
hosts
that
don't
support
multiple
pvd's,
which
you
know
may
or
may
not
be
most
hosts.
I,
don't
know,
since
we
have
to
support
that
use
case.
Q
What
we
had
talked
about
doing
in
myth
was
actually
wrapping
the
prefixes
that
are
not
the
default
prefix
in
in
the
option,
so
that
a
host
that
doesn't
know
about
the
option
will
fail
to
parse
it
and
then
they
won't.
They
just
won't
see
those
prefixes.
So
actually
you
would
have
just
a
general
RA.
The
host
wouldn't
actually
have
to
identify
itself
to
the
network
as
supporting
or
not
supporting
this,
it
would
just
see
the
RA.
You
would
see
the
stuff
in
the
RA
and
it
would
do.
W
Just
a
small
element
of
answer
why
the
that
option
was
removed
at
some
point,
I
think
it's,
because
one
of
the
reason
why
me
was
killed
like
trying
to
do
too
much
stuff,
so
I
I
have
no
issue
with
such
a
solution.
It's
just
like.
We
would
like
to
aim
for
simple
solution.
First,
like
not
try
to
do
everything
and
if
your
use
case
require
your
host
to
support
PVD
and
you
want
to
support
lumpy
video
where
hosts
as
well.
W
Maybe
you
cannot
use
this
solution
yet,
but
for
some
other
use
case,
this
solution
will
work
and
for
the
future
we
could
decide
to
have
another
container
option
for
arrays,
which
would
do
what
you
want
that
put
everything
in
the
single
documents.
It's
not
useful,
like
it's
just
going
to
make
it
more
complicated.
Q
So
tell
them
and
again
so
I,
don't
think.
That's
actually
a
good
reasoning.
I
think,
actually
that
the
ability
to
say
this
is
a
PVD,
the
MPM
PVD
aware
host
can
use
versus
this
isn't
is
actually
probably
the
most
important
thing
when
you're
talking
about
pvd's
and
so
as
far
as
I,
don't
think
like.
Maybe
there's
some
criminology
going
on
about
like
what
happened
with
the
myth
working
group
I
think
the
answer
to
that
is
is
probably
less
complicated
than
we
imagined
and
is
not
PR
just
said
so.
Q
I
think
that
we
should
actually
ask
for
what
we
want
and,
if
there's
a
reason,
why
that
isn't
the
right
thing,
then
the
consensus
process
will
deal
with
it
and
I'm
just
putting
in
a
plug
for
what
I
want
out
of
this
option.
In
addition
to
what
you've
already
done
is
what
I
just
said
and
I
think
that
it's
eminently
doable
and
very
easy
to
specify.
I
don't
know
anyway,
I.
P
F
Dave
Taylor
I
just
wanted
to
comment
on
the
intersection
between
two
people's
comments
and
elaborate
on
that
so
I'm
going
to
go
back
part
of
Lorenzo
and
others
comments
are
about
how
actually
resolving
the
information
is
optional
right.
You
don't
have
to
do
it
if
you
just
can
use
the
basic
informations
in
the
RA
or
whatever
you've.
F
You're
not
using
it
as
sort
of
a
lookup
mechanism,
and
the
other
comment
was
Eric
when
you
were
responding
to
the
comments
about
security.
Well,
how
do
I
know
that
this
router
is
the
one
that's
actually
authorized
to
had
this
PVD
ID,
he
said:
well,
you
resolve
it
and
we
said
well,
but
resolving
is
optional
and
therefore
security
or
actually
trusting
is
completely
optional,
and
that's
why
the
vulnerability
or
whatever
the
chrismas
running
about
would
exist.
Now,
there's
a
couple
things
you
could
elaborate
on.
F
That's
you
know
better
than
nothing,
but
there
is
the
sort
of
issue
to
talk
about
there,
which
is
do
I
need
to
resolve
up
to
know
whether
I
can
trust
it
or
not.
Am
I
required
to
do
that?
Is
security
optional,
a
security
mandatory
and
so
there's
a
discussion
there,
but
the
notion
of
caching
previous
answers
is
actually
something
that
will
help.
P
U
F
P
One
thing
we
cannot
really
aim
I
do
agree
if
we
could
a
better
solution
which
is
100%
secure,
we
would
go
for
it,
but
we
know
we'll
never
reach
this.
So
if
we
can
get
at
least
to
prevent
miss
configuration
or
very
naive
attack,
that's
better
than
nothing
right
now.
Anybody's
can
send
you
arrays
and
their
little
protection
right,
because
if
you
do
NPT
behind
on
sweet
or
whatever
I'm
very
skeptical,
okay,
let's
look
maybe
on
meaning.
P
V
For
a
kind
of
like
the
bootstrapping
of
the
trust,
if
all
you
have
is
the
PVD
information
you
get
in
the
RA
or
the
other
direct
options,
and
this
is
just
an
identifier
at
that
point,
you
should
not
be
making
any
other
assumptions
about
how
that
identifier
is
connected
to
anything
else
that
you
have
known
previously.
This
is
the
only
things
you
would
be
possibly
trying
to
protect
the
validity
of
all
the
things
which
are
already
in
that
extra
information
dictionary.
You
fetch
so
there's
not
really
kind
of
a
problem
of
saying
so.
V
Yes,
if
they
claim
they're
Verizon
whatever
you
don't,
that
doesn't
really
mean
anything.
It's
just
saying
that
on
this
link,
this
is
one
consistent
set
versus
this
other
consistent
set
of
information.
So
you
should
not
make
any
other
some
based
on
that
until
you've
already
fetched
it.
So
there's
not
the
bootstrapping
problem,
because
you
only
care
about
resolving
once
you
have
resolved
and
you
want
to
say
what
do
I
think
about
this.
Other
information.
W
Am
I
still
trying
to
give
another
element
of
answer
to
a
Christian?
It
looks
to
me
that
what
you're
looking
for
is
a
way
to
trust
your
router
about
what
it's
telling
you
and
that's
quite
ambitious
problem
to
solve.
Unfortunately,
with
arrays
and
DHCP,
they
are
not
secured,
so
it's
complicated.
Maybe
what
they've
said
earlier
is
right
and
HTTPS
in
that
example,
is
not
a
way
to
make
sure
that
your
PVD
is
what
the
server
tells
you.
W
It
is
just
a
way
to
retweet
the
PVD
without
possibility
of
man
in
the
middle
attack
in
a
modification
of
the
PDT
object,
but
I
think
in
our
case.
Yes,
you
have
to
trust
your
router
and
the
information
that
it
gives
you
you
have
to
trust
it
as
well.
If
you
don't
want
to
trust
it,
well,
it's
optional.
You
don't
need
to
use
it.
You
don't
need
to
fetch
it.
E
Dear
it's
Ganassi,
app
or
also
touching
on
the
security
and
privacy
implications,
I
think
the
conceptually
this
is
similar
to
an
RA.
In
that
all
it
is,
is
an
advisory.
In
the
same
way,
you
are
a
could,
give
you
any
DNS
server
and,
as
you
were
saying,
you're
free,
you
configure
your
on
your
OS
may
want
to
do
that-
maybe
always
maybe
sometimes
you're
free
to
actually
do
that.
E
E
What
my
dns
was,
what
my
extra
routes
were
in
the
RA
here
are
a
few
other
related
information
from
there
and
also
I
can
guarantee
that
I
am
in
terminal,
2,
dot,
Prague
Airport,
C
Z,
if
they
source
it
from
there,
for
example,
and
that's
all
I
know
it's
just
a
string,
it
doesn't
mean.
Oh,
this
is
my
corporate
network.
Let
me
send
all
my
data
in
the
clear
now
you
don't
use
it
for
that.
I.
R
Learned
Zack
Lee,
the
other
thing.
Another
thing,
of
course,
that
is,
is
certainly
an
option
is
to
rely
on
a
given
that
this
is
partly
targeted
at
devices
that
might
also
have
multiple
interfaces.
You
can
always
use
an
other
interface
to
validate
this
PVD.
If
it's
on
the
internet
right
you,
you
have
that
option.
If
you
choose
to
do
that,
and
that
might
be
the.
R
It
doesn't
have
to
refuse
to
serve
you,
it
can
just
tell
you
I
mean
it
can
do
it.
The
thought
was
that
it
would
just
tell
you
these
are
the
POS
that
you
can
have
I.
Think
that's
what
that
was.
What
so
else
is
the
point
I
and
then
you
would
check
that.
But
my
point
is:
if
something
is
it
you
you
can
have,
you
can
have
a
model
where
you
could
choose
to
do
that.
R
R
P
P
M
Every
Hat
right,
so
the
interior
started
to
do
like
one
of
items
right
like
and
I
do
see
like
a
body
of
work
associated
with
this,
that's
going
to
happen
and
either
way
like
which
already
gonna
go.
We're
gonna
get
like
review
from
six
man
like
and
DHC,
and
probably
like
for
the
like
stuff
like
on
ipsec
knee
right,
so
I
would
really
say.
Like
you
know,
shooting
for
a
like
both
would
be
like.
The
best
thing
to
do
like
a
working
group
would
be
the
best
thing
to
do,
but
it's
really
your
call.
H
M
M
Q
Sorry,
that's
a
digression,
but
essentially
the
reason
I
came
up
to
the
mic
is
that
this
work
has
been
something
that
the
IETF
has
tried
to
do
for
quite
a
number
of
years.
The
myth
working
group
was
killed
off.
I
I,
don't
think
that
the
Met
working
group
was
killed
off
for
any
particularly
bad
reason,
but
nevertheless
it
was
killed
off
and
that's
where
the
work
was
happening
and
that
would
have
been
the
working
group
where
this
work
ought
to
have
been
done.
Q
Q
Q
If
you
think
what
ought
to
happen
is
that
a
working
group
out
to
do
this,
then
I
would
request
that
the
IAS
G
immediately
charter,
a
one-off
working
group
to
handle
this
work,
and
you
know
we
can
sit
down
and
and
and
write,
write
out
a
charter
and
do,
though,
do
the
IAT
IETF
consensus
process
to
make
sure
that
the
working
group
is
approved.
But
I
really
don't
want
to
see
this
wait
for
like
three
or
four
IITs
just
to
get
to
the
point
where
it
becomes
adopted.
Q
H
M
M
Q
Don't
know
I
don't
actually
know
why
Terry
closed
and
if
I
have
theories
and
and
I
don't
see
any
point
in
speculating
about
it.
Everybody
knows
that
reduces
mmm-hmm.
But
but
the
point
is
that
the
you
know,
I
I,
think
all
things
being
equal
yeah.
It
really
ought
to
be
its
own
working
group,
but
I
don't
want
us
to
wait
until
that
happens.
To
do
this
work.
That's
that's
what
I'm
getting
at
right
so
and
I
think
you
know.
There's
you!
Y
Mark
Kemsley
I
agree
with
a
large
large
part
of
what
Ted
said
when
myth
was.
You
know
quickly
closed.
If
I
recall,
there
was
a
message
from
Terry
that
said,
and
any
remaining
items
that
need
to
be
moved
forward.
I
will
you
know
ad
Shepard,
independently
and
I,
see
this
as
that
work
that
did
continue.
I,
remember,
meetings
that
happened
amongst
the
authors
and
other
people
after
the
IETF.
Y
Where
was
myth
no
longer
existed
where
we,
you
know,
but
got
together,
and
you
know,
started
working
on
the
what
you
see
here
right
with
full
expectation
that
yeah,
if
we
did
a
good
job
and
we
shopped
it
around
to
all
the
different
working
groups
where
it
affects
where
there
might
be
in
effect,
etc,
etc.
We
had
a
path
to
ad
Shepard
and
get
this
done
in
short
order.
I
would
like
that
promise
to
be
kept.
It
doesn't
have
to
be
by
it.
Y
Y
So
that
we
can
get
this
work
done
quickly
if
you
feel
like
you
need
a
really
short
term
working
group
in
order
to
put
some
chairs
in,
because
you
can't
scale
and
you
need
to
have
it,
you
need
to
have
a
chair
there
to
help
manage
it
cool
but
creating
a
both
plus,
both
plus
working
group
and
which
would
necessarily
end
up
like
opening
up
all
those
wounds
and
like
I
was
there
and
I?
Did
it
too,
and
it's
already
been
done?
Why
don't
you
do
it
that
way?
Y
M
L
Really
I
think
a
couple
of
points.
I
think
this
work
should
move
forward
quickly,
I
think
if
we
spend
too
much
of
time
creating
blobs
and
all
of
that,
that's
what
I'm
going
to
help
I
strongly
believe
it
as
a
strong
relation
to
some
of
the
Phi
Z
work
like
slicing.
So
in
that
sense,
there's
a
urgency
here.
I
think
it
should
move
forward
on
a
fast
track.
That's
my
one
comment.
Second
comment
of
the
movies:
I
completely
disagree
that
this
you
know,
I,
think
you
know
wounds
and
all
of
that.
L
Yes,
you
know,
I
I,
feel
that
you
know.
I
also
did
some
part
of
that.
But
but
one
comment
is:
it
doesn't
belong
to
me
feed
them
because
we
did
a
prior.
The
initial
publications
were
in
DHC
working
group.
We
just
called
it
class
somebody
denial
like
the
name.
They
came
out
with
some
structural,
symmetrical
changes
and
say
it's
something
new.
It's
not
the
fundamental.
The
core
ideas
were
introduced
much
before
that,
so
in
that
sense,
sniff
is
no
longer
no,
not
an
owner,
just
that
it
was
structured
work.
L
Z
Guri
so
gory
Fairhurst
and
we
have
a
vendor
code.
We
have
a
hackathon
open
source
code.
We
have
interested
in
the
draft,
that's
being
talked
to
her
in
multiple
working
groups
and
there
are
probably
other
working
groups
like
taps
and
the
PA.
The
path
aware.
Networking
research
groups
that
could
all
build
on
this
I
think
there's
a
huge
momentum
here
that
sorta
momentum
would
normally
create
a
working
group.
If
we
don't
need
a
working
group
unless
just
to
dot
the
draft.
If
we
need
a
working
group,
then
let's
adopt
the
draft
somewhere.
Z
G
U
P
Your
preference,
my
preference,
like
most
of
the
Oder,
get
it
as
soon
as
possible,
adopted
somewhere,
so
we
can
get
a
real
document
there
and
then
we
need
indeed
there
are
multiple
could
be
the
foundation
of
more
work.
So
when
we
can
get
a
working
group
there,
but
honestly
don't
wait
right
for
us,
I
mean
beside
the
privacy
thing
that
we
overlook.
To
be
honest,
we
can
finish
document
it's
true,
it's
true,
and
then
we
go
again.
The
code
is
there
right
so
like
the
reset?
Soon,
okay,.
Y
Mark
smart
totally
agree
with
what
what
Eric
just
said.
Let's
not
forget,
though
sometimes
we
do
I
think
an
AV
Shepherd
document
doesn't
need
a
working
group.
Okay,
there's
no
technical
I
mean
procedural
reason.
You
have
the
power,
you
can
take
a
document
and
put
it
straight
on
the
standards
track
in
front
of
the
iesg.
Now
again,
it's
up
to
you
in
terms
of
whether
or
not
you
need
the
hierarchy.
Y
You
know
in
the
group
to
help
you
do
that,
but
if
you
have
feel
like
you
have
sufficient
understanding
of
what's
going
on
here
and
that
you've
seen
because
you
know
all
the
authors
are
running
around
all
their
different
we're
and
making
sure
they
know
about
it.
That
distributed
approach
with
you
watching
very
carefully
might
be
all
that's
needed
right
and.
M
And
the
way
I
think
about
it,
not
right
like
whether
it
happens
in
interior
or
if
I
do
Eddie
Shepherd
I
follow
the
exact
same
process
right
here.
If
it's
in
some
other
group
right
like
there
is
a
difference
right.
So
if
it's
a
six-man
document
and
Eddie
Shepherd
like
I
I,
go
to
interior
and
like
the
relevant
groups,
but
it's
an
interior
I,
don't
see
a
difference
in
in
the
processor.
Also,
okay,
I,
don't
mind
things
either
way
right
like
so.
B
X
X
Hello:
everyone,
my
name,
is
major
discount,
our
CSR
dias,
Romania
and
I'm,
also
the
culture
of
the
drug
name
in
PT,
Network
layer,
multiple
library-
and
this
is
what
I'm
gonna
talk
to
you
about
today.
So
next
slide.
So
what
is
amputee
amputee
is
a
network
layer,
multipad
solution
which
provides
a
ton
of
or
multiple
paths
using,
the
GRE
in
UDP
encapsulation
RFC.
It
zero
eight
six
and
my
extension
is
also
different
from
both
MP
TCP
and
how
is
GRE
tunnel
bonding
protocol?
X
What
are
the
benefits
of
MBD
so
the
most
important
as
with
the
others?
The
path
through
put
capacity,
aggregation,
resilience
to
network
failures
and
our
contention
is
it
better
suits
real-time
traffic,
MP
TCP
X
like
this
well
aside
from
that
in
empathy,
can
also
be
used
as
a
router,
so
routing
packets,
amongst
your
own
networks,
between
the
tunnel
endpoints
and
also
as
an
ipv6
transition
technology,
because
the
tunnel
IP
version
can
be
different
than
the
path
IP
version
makes
light.
So
how
does
the
stack
look
like?
X
So
we
have
a
tunnel
interface,
that's
going
to
handle
the
application
TCP
UDP
head,
there's
an
IP,
headers
they're,
going
to
be
encapsulated
engineer
in
UDP
and
then
along
multiple
paths.
They
use
a
UDP
and
IP
next
up
with
so
as
I
was
saying,
conceptually
MPT
implements
a
tunnel
over
several
paths.
The
tunnel
packets
can
be
mapped
different
in
different
ways.
So
one
of
the
mappings
and
this
one
we
have
an
implementation
of
so
per
packet
based
mapping.
It
can
also
feed
role
based
mapping
or
a
combination
of
the
two.
X
So
the
a
packet
would
look
something
like
that:
we'll
have
the
application
later
to
know:
tcp/ip
TCP,
UDP
tunnel,
IP,
v4,
v6,
jaring,
UDP
and
then
the
path
headers,
which
okay,
so
the
port,
four
seven,
five
four
and
then
the
IP
version
of
the
next
type.
Of
course,
you'll
have
some
connection
specifications
which
can
contain
several
pads
and
we'll
have
some
parameters
for
that.
So,
for
example,
for
some
wasn't
a
no
attributes
like
name
permissions
tunnel,
IP
version,
etcetera
and
number
of
paths
for
the
path,
attributes,
number
of
paths,
definitions,
weights
and
so
on.
X
Next,
like
this,
so
in
terms
own
control
plane,
the
MPT
servers
are
started
automatically.
We
using
configuration
files,
of
course,
connection,
maybe
also
later
establish,
be
established
and
tear
down
dynamically.
The
paths
can
be
added
or
deleted
and
we
also
have
a
keepalive
mechanism
there,
except
so
this
was
a
quite
big
diagram,
so
we
spit
it
into
slides.
X
So
you
know
if
a
tunnel
interface
will
send,
the
packet
would
have
check,
checking
connection
specification
like
slightly
and
then
we'll
have
the
path,
selection
and
the
encapsulation
and,
of
course,
will
transmit
the
data
to
the
physical
interface
from
the
physical
interface.
The
data
is
checked.
Can
we
go
back
to
the
previous
slide?
Please
and
then,
because
of
different
delays
in
packet,
arrival
will
have
packet
reordering
and
then
the
packets
are
forwarded
to
the
tunnel
interface
back
so
okay,
so
the
packet
base,
mapping
as
I
was
saying,
was
already
implemented.
X
So
for
each
market
the
mapping
decision
is
made,
and
since
we
have
weights,
we
use
them
for
all
the
load
balancing
and
the
number
of
videos
or
bytes
sent
to
that
is
proportional
to
the
weight
of
the
pad.
And
for
this
we
have
precise
algorithm,
which
we
described
in
the
draft
and
also
there's
a
sample
C
code.
Okay,
so
this
wasn't
implemented.
This
is
something
that
we're
planning,
so
flaws
are
identified
by
the
usual
five
topple
and
then
all
the
packets
are
forgiven
flow
or
handled
the
same
way.
X
X
Okay,
since,
as
I
was
saying
earlier,
packets
may
arrive
because
it
because
of
different
delays
at
different
times.
We
have
to
do
package
or
thing,
so
we
came
up
with
all
the
right
delivery
and
it's
based
on
the
GRE
sequence
numbers
he's
done
at
the
receiver.
It
has
two
important
parameters:
the
order
window,
so
the
size
of
the
you're
doing
buffer
and
also
maximum
offer
delay
it's
working.
Well,
it's
interested.
X
We
are
still
kind
of.
We
have
still
these
open
questions
like
how
big
should
be
I
should
be
the
real
you're
the
window
and
like
what's
the
optimal
maximum
offer
delay,
so
these
are
still
being
beside
okay
next
slide,
please.
So
there
are
a
couple
of
academic
papers
that
were
written
on
this
subject.
If
you're
interested
in
this,
please
go
ahead
and
read
them
there.
Some
of
them
are
not
open
access,
so
if
you're
interested
in
reading
them,
please
contact
us
somehow
so
yeah.
X
We
we
tested
the
path
through
put
capacity
and
we
compared
it
to
NP
TCP
and
we
discovered
that
doable.
It
flows,
which
was
the
maximum
that
NP
tcp
supported.
We
have
different
or
we
we
have
better
performance,
also
tested
fast
connection
recovery
and
the
elimination
of
the
stalling
events
for
you
for
youtube,
video,
playback,
okay.
So
next
slide,
please,
if
you're
interested
in
this
draft,
please
support
it
so
in
the
academic
community
it
has
already
been
presented.
We
would
like
get
to
find
the
home
here
and
IDF
as
well.
So
yeah,
that's!
E
X
E
X
E
AA
AA
X
AA
X
AA
Z
X
Z
Y
Y
You
know,
there's
a
hundred
different
ways
to
tunnel
you've
picked
one
there's
hundred
different
ways
to
decide
how
to
put
packets
into
that
tunnel
for
whatever
use
case
that
you
have
and
you
reach
into
transport
area
for
sure
when
you
start
doing
that,
it's
really
fun
to
see
the
resurgence
of
B
channels
virtualized
and
bonding
all
over
again.
If
we
want
to
use,
if
you
want
to
use
IETF
standards,
track
documents
grab,
multi-link
PPP,
throw
it
over
an
l2tp
tunnel
and
you're
done.
You
know
it's.
It's
given
yeah.
Y
But
this
is
mostly
a
problem
of
deciding.
You
know
how
the
packets
go
in
to
the
two
tunnels
and
come
out
to
the
two
tunnels.
You
could
use
any
number
of
tunneling
encapsulations
and,
like
I
said,
we've
already
got
standards
track
RFC's
for
this,
so
please
continue
your
research.
Please
can
t
pub,
keep
publishing
I,
don't
think
we
need
another
standards
track
anything
for
this.
Okay.
Thank
you.
AB
So
hi
I'm
glad
and
I'm
going
to
talk
about
Sox
version
six.
So
the
motivation
behind
this
is
that
Sox
5
is
20
years
old
and
kind
of
needs
a
facelift.
It
makes
very
liberal
use
of
round
trips,
so
it
first
takes
around
data
round
trip
to
negotiate
the
authentication
method
that
it
that
the
client
and
the
proxy
are
going
to
use,
and
then
it
takes
one
round
trip
or
more
to
authenticate
the
client
and
then
the
client
asks
the
server
to
establish
a
connection
on
his
behalf.
I
mean
in
after
the
publication
of
Sox.
AB
Five
people
have
come
up
with
ways
to
do:
0,
RTG
authentication,
so
if
Gentiles
had
previously
communicated,
they
can
authenticate
in
0rt
tes
on
further
connection
attempts.
Now
we
have
a
hot
new
use
case
for
Sox,
so
mobile
mobile
devices
are
equipped
with
with
a
cellular
interface
and
also
Wi-Fi
interface.
In
case
we
want
to
use
both
of
these
interfaces
for
improved
throughput.
We
have
to
use
something
like
MP
TCP
now,
since
servers
typically
don't
deploy.
AB
Mp
TCP
network
operators
have
to
deploy
some
kind
of
proxy
in
order
to
terminate
the
MP
TCP
connection
and
open
of
vanilla
to
CP
connection
to
the
server
now,
since
mobile
networks
have
typically
have
high
latency,
we
have.
We
have
made
some
efforts
toward
the
shaping
off
as
many
RT
T's
off
of
Sox
as
possible.
AB
All
all
control
messages
have
TCP
like
options
and
we
plan
to
implement
our
clear
authentication
via
cell
options.
So
next
slide.
Now.
This
is
what
socks5
looks
when
Sox
6
looks
when
like
when
compared
to
Sox
5.
So
in
Sox
5
we've
got
the
method,
the
negotiation,
the
authentication,
then
then
the
request
and
finally
the
data
can
pass
through.
So
we've
taken
the
blue
bit
the
the
methods,
the
between
bit
part
where
the
the
client
specifies
what
server
it
wants
to
connect
to
and
the
red
bit
the
initial
bit
of
data
and
we've
tried.
AB
We've
tried
to
place
them
in
the
initial
data
exchange,
which
would
hopefully
fit
into
one
packet.
So
Sox
6,
so
Sox
6
in
our
Sox
6
client
sends
a
request
in
which
it
advertises
the
methods,
it's
known,
authentication
methods.
It
asks
the
server
to
initiate
the
connection,
and
it
also
provides
some
data.
AB
So
what
what
I've
said
up
to
this
point
applies
to
the
first
connection,
attempt
in
further
connection
attempts.
The
Sox
client
can
attempt
to
do
zero,
RTT
authentication,
which
case
the
server
replies
with
an
authentication
reply
and
and
requests
that
no
further
action
be
taken.
So
next
slide.
So
let's
take
a
also
look
at
what
the
request
looks.
Like
we've
got
version
numbers
made
a
major
number
and
a
minor
number
we've
got.
We
advertise
the
known
north
in
ossification
methods.
AB
We
tell
the
proxy
whether
we
want
to
use
here
for
or
not
we
tell
it
whatsoever
to
connect
to.
We
also
include
some
options
in
TLB
format
and
also-
and
at
the
end,
we
place
some
initial
application
data.
The
next
slide.
The
authentication
reply
is
your
authentication
reply.
It
basically
tells
the
client
whether
the
proxy
needs
further
authentication
or
not
so
in
case
zeroeth,
an
RTT
authentication
failed
or
was
not
attempted
the
server.
Basically,
the
proxy
basically
tells
the
client
that
such-and-such
method
must
be
followed
in
order
to
authenticate
the
client.
AB
In
case
your
Artie
authentication
succeeded.
The
server
tells
the
client,
via
which
authentication
method,
it
actually
authenticated
the
client
next
slide.
Please
and
finally,
we've
got
the
operation
reply,
which
tells
the
server
which
tells
the
client
whether
the
connection
was
successful
or
not
case.
It
wasn't
successful.
It
informed
the
client
whether
it
was
due
to
a
reset
or
because
the
connection
timed
out
or
because
the
proxy
did
not
did
not
refuse
to
connect
to
that
server
because
of
policies
or
whatever
other
reason.
I.
AB
AB
So
the
client
starts
by
size
by
initiating
a
three-way
handshake
with
us
with
a
server
with
a
proxy
after
one
proxy
after
one
client
to
proxy
RTT.
It
sends
the
request,
along
with
some
initial
data
for
the
server.
This
is
when
the
proxy
initiates
a
three-way
handshake
with
the
server
as
soon
as
that
three-way
handshake
is
completed.
It
sends
over
the
the
initial
application
data.
The
server
then
replies,
so
the
total
time
taken
to
for
the
client
to
receive
data
reply
from
the
server
is
to
RT
T's,
which
is
no
worse
than
vanilla.
AB
AB
AB
Thus,
the
the
initial
the
initials
in
hopefully
contains
both
the
request
and
all
of
the
data
that
the
server
needs
in
order
to
generate
the
response.
The
proxy
server
does
something
which
could
which
is
roughly
equivalent
to
stripping
stripping
the
request
it
sends,
and
it
sends
the
the
application
data
to
the
server,
the
server
replies
and
the
proxy
and
the
proxy
relays
that
they
touch
with
the
server.
In
this
case,
we
get
the
data
apply
in
one
RTT.
AB
AB
U
U
Oh
no,
basically,
well,
yes,
some
level,
but
basically
you
have
a
co-operative
process
in
which
you
can
send
his
initial
data.
Yes,
those
initial
data
can
be
replayed,
okay,
and
in
that
case
we
play
what
I
seem
to
consider
to
be
playing
answers.
Initial
data
will
trigger
the
connection
to
the
other
end
at
the
minimum,
anchoring
the
sending
of
data
so
I
I,
don't
know,
sou
have
analyzed
when
what
are
the
downside
of
eight
and
ordered
possible
mitigation?
Well,
yes,
so
so.
AB
Tft
four
also
has
the
same
issues.
That's.
That
is
why
TFO
is
optional.
The
client
can
choose
whether
or
not
to
use
UFO.
When
talking
to
the
proxy.
You
can
tell
the
proxy
whether
or
not
to
use
the
affor
when
talking
to
the
server
now
with
regard
to
authentication,
it
basically
depends
on
how
the
0rt
authentication
is
implemented.
So
if
you
just
use
some
kind
of
token,
as
in
TLS
1.3,
then
you
can
indeed
do
replays.
AB
But
if
you
use
some
kind
of
challenge
and
a
challenge
response
authentication
scheme,
the
proxy
can
just
issue
like
several
challenges
to
the
client
and
then
the
client
uses
the
map
for
connection
attempts
and
the
client
should
not
be
allowed
to
use
a
challenge
multiple
times
so
that
that
kind
of
handles
reap
replay
attacks.
So.
AB
AC
AC
So
I
want
to
be
both
more
positive
and
more
negative,
so
so
more
positively
I'm
really
enthusiastic
about
bringing
shadow
socks
into
into
the
IETF
and
trying
to
figure
out
a
way
to
basically
fix
that
protocol,
because
shadow
socks
is
a
widely
used
protocol
out
there,
it
needs
interoperability.
There
are
multiple
clients
and
servers,
it
does
not
have
good.
Interoperability
today
is
not
well
specified,
and
this
is
a
big
improvement,
/
socks5
and
overshadow
socks.
It
so
much
well.
The.
AB
AC
Protocol
I
understand
that
your
draft
doesn't
contain
shadow
socks,
but
it
seems
like
what
you've
done
here
is
you've
identified,
sort
of
why
they
were
unable
to
use
or
unwilling
to
use
socks
v
as
their
as
their
foundation.
And
you
know,
your
proposal
is
something
that
that
could
underpin
a
future
version
of
shadow
socks,
but
it
would
also
be
sort
of
potentially
more
more
compatible
with
with
IETF
approach.
I'm
really.
AC
About
that
I'd
love
to
collaborate
on
code
I'm,
my
team
is
working
on
shadow
socks
based
clients
and
servers,
and
we
would
love
to
have
a
better
protocol
foundation
so
feel
free
to
shoot
me
an
email
any
time
so
so
I'm
very
enthusiastic
about
this
from
that
perspective,
but
I
also
think
that
this
protocol
is
is
extremely
dangerous
and
should
not
be
allowed
at
the
idea,
because
what
you've
done
here
is
is
you've
taken
socks,
five
and
removed
RTT.
So
why
is
removing
RTT
is
important.
AC
Moving
RTT
is
important,
is
if
you're
speaking
over
a
high
latency
network.
In
almost
all
cases,
high
latency
networks
are
not
secure
networks,
they're,
not
networks
where
we
would
be
willing
to
trust
the
link
layer
with
our
security,
particular
they're,
usually
over
the
Internet
and
if
I
understand
correctly.
One
of
your
main
use
cases
here
is
is
for
channel
bonding,
where
you're
going
through
two
routes,
you're
definitely
going
over
the
public
Internet,
but
this
protocol
isn't
secure
and
although
you
mentioned
you
can
tunnel
it
over
TLS,
that's
actually
not
quite
true.
AC
AC
So
socks5
is
also
in
securable,
but
sonics.
Five
is
clearly
not
designed
for
use
over
public
internet
socks5
is
designed
for
and
and
I
I
spent
a
few
minutes.
Looking
through
the
history
of
this,
it
came
out
of
the
authenticated
firewall
traversal
working
group,
so
it
was
very
clear
to
the
people
who
designed
it
that
it
was
meant
for
use
inside
a
local
network
that
was
not
did
not
have
access
to
the
Internet.
So
that
was
a
trusted
network
and
it
was
a
low
latency.
Now
yes--that's
was
the
use
case
20
years
ago.
AC
Right
so
so.
I
agree.
I,
really
think
it's
really
important
to
have
good
standards
for
proxying
and
efficient
proxying
out
on
the
public
internet
on
high
latency
networks.
I
think
this
is
a
big
improvement
over
Sox
5,
but
I
really
wouldn't
want
anyone
to
to
actually
deploy
this
on
the
public
internet
because
it's
it's
insecure
and
also
because,
if
we're
going
to
rev
a
protocol
that
hasn't
changed
in
20
years,
we
should
take
that
opportunity
to
look
through
all
the
all
the
different
ways
that
we
can
see
if
we
can
improve
it
and
I.
E
E
The
fact
that
if
you
the
use
case
I
use
it
for
is
completely
unauthentic
ated,
because
well
people
before
I
was
saying
yeah,
it's
not
safe
at
all,
but
if
you
trust
the
underlying
network
and
it's
fine
and
when
you're
using
Sox
v5
in
the
non
authenticated
mode,
you
have
to
like
do
several
Archie
T's
to
say:
oh
I,
don't
support
authentication!
Oh
good
me!
Neither
let's
talk
not
very
useful,
so
Sox.
Do
you
think
you
could
really
streamline
and
do
these
things?
E
V
Tommy
Pauly
just
going
off
of
what
David
said
and
he
didn't
get
into
I
I
agree
that
yeah,
it's
not
safe,
but
I
think
there
are
now
probably
going
to
be
more
high
latency
links
in
which
the
RT
T's
matter
that
are
potentially
safe
or
trusted
thinks,
if
you're
looking
at
home
networks
or
IOT
type
networks,
and
so
this
would
be
very
useful
for
doing
proxying
there,
in
which
worse,
you
can
potentially
see.
Layton
sees
now
that
you
didn't
see
when
tox
was
originally
designed.
AC
Then
Schwartz,
thank
you.
I
just
want
to
respond
to
that
and
say
you
know:
we've
we've
been
burned
many
times
here
for
trusting
the
link
in
certainly
in
Wi-Fi,
over
and
over
we've,
we've
sort
of
been
told
that
we
have
a
trustworthy
link,
layer
and
we've
we've
learned
over
and
over
that
it
wasn't
true,
and
so
you
know
the
IETF
generally.
It
takes
the
position
that
we
either
need
basically
I
I,
P,
SEC
or
TLS,
or
a
moral
equivalent.
