►
From YouTube: IETF99-TEAS-20170720-1330
Description
TEAS meeting session at IETF99
2017/07/20 1330
https://datatracker.ietf.org/meeting/99/proceedings/
A
C
B
Good
afternoon
this
is
the
t's
Working
Group
hosting
the
joint
young
session
with
C
camp
MPLS
and
PC.
You
can
access
the
agenda
for
today
and
the
slides
using
the
pointers
on
the
slide.
Itf
note.
Well,
this
is
Thursday
afternoon.
You
should
be
well
versed
by
this
by
now,
lou
has
presented
the
recent
changes
to
this
note.
Well,
a
couple
of
times
this
week
this
was
presented
in
the
appeal
of
working
group
and
also
in
the
routing
area,
open
meeting.
D
B
You
miss
those
two
presentations.
Please
do
with
you.
This
read
as
far
as
session
logistics
are
concerned.
This
session
is
being
streamed
and
recorded
so
pleased
to
speak
only
using
the
microphones
and
to
state
your
name
before
speaking
for
the
pen
bit
of
remote
participants
as
usual
you'll
be
taking
the
minutes
using
etherpad,
so
pleased
to
participate
in
it
and
we'll
be
on
jabber
as
well
as
far
as
agenda.
For
today
goes.
We
have
three
slots
dedicated
for
T,
specific
crafts.
B
E
E
So
here's
the
last
this
type
of
changes
we
have
made
since
last
IGF
session.
So
now
we
allow
multiple
instances
of
interim
they
unlock
IDs
and
we
added
missing
TTP
ISM
to
Mandalay
and
the
way
I.
Just
some
attributes
to
the
link
termination
point
and
talent
ownership
wants.
So
we
also
import
handling,
aqua
connectivity,
metrics
labeled,
and
we
were
sharing
of
the
tea
types
between
our
protocol
and.
E
E
Then
here's
a
some
of
the
changes
mentioned
earlier,
so
he
is
into
the
internal,
a
anak
ID.
So
we
fixed
the
situation
for
multiple
loci
disease,
each
particular
Commission
points.
Here
we
changed
the
interlayer,
lock
ID
from
live
to
live,
so
this
were
accommodated
this
situation
back
here
for
the
case.
Here
we
have
to
be
peacefully,
you
have
to
lock
IDs
1
&
2.
Then
we
are
requested
by
some
implementers.
We
added
a
few
attributes
to
the
information
content.
E
Sometimes
we
need
to
specify
the
unerring
confirmation
points,
so
we
added
in
the
model
here
so
that
we
can
specify
such
conduct
requirements
then
for
the
connectivity
matrix,
labor
handling,
we
were
raised
by
situation
there
or
one
region
of
the
involved
with
a
table
from
one
and
maybe
change
at
the
other
end.
So
for
the
modeling.
We
need
mode
and
label
relationship
sites
label,
rejection
from
the
matrix
entry
to
each
termination
points.
E
Recently
we
have
found
was
three
copies
here:
path:
constraints
of
optimizations
and
computed
passed
properties
for
those
things
they
are
now
in
the
gene
types.
Proprietary,
we'll
talk
more
on
roles
in
the
tunnel
model
presentation,
then
for
the
Pend
Oreille
is
modeling.
We
had
this
have
been
discussed
before
and
the
recorded
comments
from
she
come
people.
He
is
also
some
more
comments.
E
Can
also
suggest
that
we
should
do
more
detailed
modeling,
so
here
we
have
inside
of
a
generic
screen.
We
now
have
routines
have
that
a
better
model
here
and
then
we
had
the
model
will
be
able
to
buy
the
young
doctor.
So
we
traced
all
the
concerns,
including
present
continuous
terminology,
consistencies
and
some
cookies,
then
the
bigger
issue.
He
is
a
DA
style
and
we
have
been
discussed
this
for
quite
a
bit
time.
We
all
know
that
this
is
that
you
actually
want
more
tool
and
this
would
be
provided
better
structure
and
better
features.
E
So,
but
the
question
is
how
and
one
which
we
commute
with
this
kind
of
architecture.
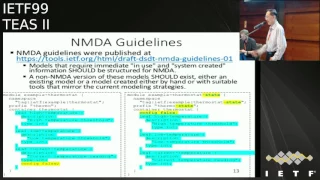
So
now,
a
couple
month
ago
we
have
the
published
an
MPA
guidelines,
so
this
is
what
we
were
trying
to
move
from
current
models
now
student
late.
So
the
proposed
the
Caroline
is
like
this.
So
if
we
need
I'm
the
in
use
the
state,
which
is
the
case
we
are
having
not,
then
we
can
have
an
MVA
module
of
life
and
also
companion.
F
G
E
So
the
module
name
is
appended
with
the
state
and
in
the
namespace,
also
change
a
little
bit,
and
it
was
more
here
because
everything
is
a
config
fault
on
the
right
side.
So
this
is
a
at
a
glance,
though
the
change
is
not
a
match.
We
can
reuse
pretty
much
but
depending
on
the
model
complexity.
So
this
is
a
trivial
case.
It's
easy,
but
a
soft
case.
It's
not
that
easy.
We
need
for
some
restructuring
and
here
so
we
have
had
many
discussions,
so
she
won
and
how
about
motor.
E
So
we
want
to
hire
while
modeling
capability.
We
need
to
maintain
our
state
and
configure
all
those
speech
capabilities
from
the
modeling
perspective.
They
also
need
to
ring
King.
The
protocol
and
application
features
recipe.
We
don't
want,
have
a
model
delayed
and
though
we
also
don't
want
to
have
them,
they
impact
communications.
E
So
now,
since
we
after
that
many
discussions,
we
decided
to
move
this
as
quick
as
possible
so
because
we
are
depending
on
the
partly
based
model,
which
is
I
advise
to
target
model,
so
we
have
described
it.
I
tries
to
find
a
lot
of
people,
and
so
the
advice
model
has
screen
to
update
to
MTA
and
they
thanks
for
Alex.
E
This
happened
down
so
then
we
we
calcified,
we
it's
possible
for
us
to
move
to
an
NP
also,
so
we
have
made
change
so
I
did
move
our
model
to
the
main,
an
MTA
translation
mode
module
under
man.
They
also
added
a
state
module
the
same
idea
because
we
have
used
a
lot
of
defects
which
contains
XPath,
so
it's
a
not
led
to
simply
very
other
go
P,
so
we
had
to
do
something
to
stop
it
now
they
structured
according
opens.
E
This
may
not
be
the
same
case
for
every
model,
so
we
receive
a
found.
Some
augmentations
could
be
easier.
So
in
our
case
the
nmda
model
and
the
befallen
and
the
amount
of
pretty
much
stay
inside
the
same
model.
They
hire
some
duplications,
but
it's
tolerable.
Here
we
have
like
fifty
percent.
The
things
need
to
be
repeated,
so
basic.
E
You
have
used
to
have
music
container
and
still
continue.
Then
we
have
moved
all
those
attributes
from
the
containers
inside
this
config
and
State
moved
to
the
tyrants
and
remove
those
containers.
So
this
is
a
simplified,
not
show
you
what
we
have
been
doing
and
then
pretty
much.
We
have
the
current
state
of
a
model,
so
we
think
it's
pretty
much
stable
and.
F
E
E
They
are
three
key
to
pocket
model
which
is
referencing
poster
advice.
They
are
straight
apology
and
the
teeth
part,
so
they
also
have
been
updated
to
the
nmda
style
because
they
are
little
bit
different
right
for
the
augmentation
cases.
You
see
here
and
put
my
some
data
points
for
the
moving
to
90s.
So.
F
E
F
D
F
Try
to
optimize
the
size
of
them,
which
is
fine.
That's
that's!
Okay,
but
just
as
a
general
observation
here
is
the
expectation
is
you
can
produce
these
very
very
easily,
but
just
by
taking
a
copy
of
the
ending
and
then
da
ma
Joel
copy,
it
change
its
name
to
state
change.
The
name
say
sir
state
and
re-shared
type
this
and
keep
the
group
being
separate,
and
then
the
intention
isn't
to
make
that
state
model.
Very
short,
it
is
to
make
it
very,
very
easy
to
produce
throat
in
the
appendix
and
you're
done.
E
Sizes
of
one
factor
also,
we
don't
want
to
have
duplication
right.
So
there's
some
maintainability
issue,
the
one
who,
however,
changes
here
and
there,
because
if
you
only
try
to
search
and
replace
all
names
its,
we
have
like
hundreds
of
cases
right.
So
whenever
you
change
this
config
model,
we
need
to
do
the
same
thing
again
at
the
state
model.
Yeah,
so
we're
we're,
hoping
you
have
the
tool
which
can
make
it
a
fully
automated.
You
know
you
don't
have
this
and
we
don't
want
to
have
these
duplications
there.
F
D
F
Defensive
for
transformation,
yeah
and
I
think
again
just
an
observation
to
the
room
that
if
the
state
watches
here
a
temporary
thing,
so
this
is
not
a
long-term
plan
for
these
state
modules
hang
around
once
the
nmda
complying
implementations
come
along,
the
state
modules
are
automatically
replicated
and
are
not
required.
Yeah.
E
Yeah
yeah
and
another
observations
that
are
run
in
a
structure
unless
we
hit
a
limitation
for
the
coping
cutter
coping.
You
cannot
pass
predator
to
that.
So,
even
though
we
have
simple
differences
between
the
two
structures,
my
little
namespace
team,
otherwise
such
a
mistake.
So
if
it
can
do
some
simple
see
kind
of
micro,
this
would
easily
can
be
reduced.
But
this
is
not
possible
here.
H
My
name
is
tarick
Francisco,
so
the
proposal
of
adding
a
module
with
the
state
and
my
understanding
is
to
hold
the
applied
configuration
or
a
state,
and
that's
my
my
understanding.
Yes,
there
is
a
third
argument
to
this
or
it's
another
state
which
is
a
automatic
or
dynamic
state.
What
is
the
thinking
that
we
will
have
a
dynamic
module
there,
and
the
second
part
of
my
question
is:
if
augmentation
other
modules
will
augment
your
your
model,
they
will
have
to
augment
both
the
model
and
the
state
models
and
maybe
the
dynamic
model.
F
Robertson
siscaly,
so
this
state
module
serves
two
purposes
one
is
it
allows
you
to
report
the
before
the
nmda
implementations
come
out.
It
serves
two
purposes
one
is
it
allows
you
to
report
the
applied
configuration
value,
the
other
case
where
it's
used
in
the
case.
That
probably
matters
here
is
system
created
interfaces.
A
system
created
state
effectively,
so
it's
required
in
that
particular
scenario
and
to
address
the
other
comment
about
dynamic.
No
there's
no
intention
will
ever
be
a
/,
dynamic,
I.
Think
intention
there
is.
H
I
I
K
Blueburger,
any
hat
just
to
be
clear.
The
recommendation
that
came
from
the
ADEs
and
that
is
being
follow
through
in
all
these
different
working
groups
is
that
state
create
the
state
model.
The
one
that
goes
in
the
appendix
include
both
applied
and
system
created
information,
so
system
created,
could
be
dynamic
for
a
particular
model
if,
for
some
reason,
that's
insufficient
and
there
needs
to
be
a
representation
of
a
third
thing.
We
should
talk
about,
and
that's
specific
case,
but
at
this
point
no
one's
identified.
L
Sioux
hairs,
I
think
in
this
hat,
I
RS
chair
with
the
topology
dynamic
piece,
the
the
benefit
of
the
topology
model,
with
the
ending
MMD
a
well
that's
a
tongue.
Twister
some
days
is
that
it
can
be
loaded
in
that
dynamic,
ephemeral,
davis
store
without
problems.
The
dynamic
data
store
is
a
unique
definition.
I
think
you
need
to
be
careful
to
disambiguate
between
dynamically
created
stuff
and
the
dynamic
data
store.
E
Yeah,
for
that
know
that
the
same
thing
we
did
for
the
I
saw
and
I
saw
two
pocket
models.
We
also
know
that
into
an
NDA
compatible
modules,
and
so
in
this
case
this
is
a
poorly
augmentation,
so
which
is
similarity
formed
convention
infidel.
It
gives
5
2003
I'm,
one
of
which
is
we
don't.
In
this
case
we
don't
have.
L
Are
you
into
we're
working
to
make
the
you
know,
there's
a
point,
not
an
MD.
A
BGP
model
was
which
hopefully
is
a
basis
for
this
s
are
additions
to
BGP,
and
but
we
are
working
rapidly
toward
an
M
and
D
a
model.
Are
you
anticipating
data
coming
from
a
BGP
nmda
based
model,
plus
an
augmentation
for
service
routing,
to
be
put
in
to
be
linked
to
your
T
srte
topology,
modeling,
defense
right.
E
L
Will
be
moving
to
empty
I
have
heard
I
have
heard
my
80s
and
I
am
the
chair
and
I
got
obey
yeah,
we
go
there,
okay,
but
the
quest
is
more
for
technology
bases.
It
looks
like
as
a
guiding
share.
I
must
make
sure
that
it
all
who
use
the
right
types
and
all
the
stuff
if
we
do
an
SR
extension
to
put
to
look
at
stuff,
I
need
to
make
sure
the
models
align
carefully
and
they
all
should
align
based
on
an
NMDA
did
I
understand
that
yes,
yep.
That's
right.
Thank.
L
B
H
Hello:
everyone,
my
name,
is
dark
exactly
and
I'm
with
Cisco
Systems.
Can
you
hear
me,
okay
in
the
back
I
hope
so
I
can
come
closer,
so
I'm,
given
a
quick
update
on
the
modeling
effort,
forty
an
RSVP
models
that
are
described
in
three
drafts.
At
the
moment
the
latest
yang
code
sets
and
github
at
the
location
you
have
there.
H
So
before
I
describe
the
changes
we've
done,
let
me
give
or
recognize
the
efforts
by
Sergio
it
Aloha
Carlo,
Francesco
and
others
who
reviewed
our
model,
gave
comments
and
I
hope
we
addressed
and
we'll
continue
to
address,
open
comments
from
them
and
for
the
team
for
continuing
to
show
up
weekly
on
the
discussions
to
cause
on
the
modeling
so
that
high
level
changes
we've
done.
We
moved
some
attributes
that
are
packet
specific
to
the
packet
module.
H
The
first
update
we're
adding
a
probably
a
year,
shifted
the
order
in
the
previous
slide.
But
this
is
the
operational
state
we're
introducing
in
the
LSP.
It's
basically
a
state
machine
of
the
LSP
state
as
it
progresses
from
path
computing
to
computation,
okay
or
failed
and
then
setting
up
and
it
closes
up
with
a
state
up.
So
it's
incremental
state
as
it
progresses.
H
Right,
the
second
update
we're
adding
computer
path
properties,
which
will
hold
the
accumulative
metrics
of
the
path.
There
are
multiple
metrics
that
the
path
can
carry.
We
have
it
as
a
list
and
we
have
a
metric
type
metric
types
that
we
defined
RTE
metric,
IGP
metric,
latency,
hop
count,
average
delayed,
actually
latency
and
average.
They
may
be
the
same.
H
H
H
The
fourth
update
we
added
some
bounds
on
when
doing
path,
computation
or
assigning
some
constraints
on
your
path,
so
the
bounds
again,
we
have
different
metric
types,
it's
a
list
where
you
can
set
the
metric
type
and
and
the
bound
that
you
want
upper
bound.
So
you
can
basically
set
multiples
of
those
in
the
list.
H
The
fifth
update
in
terms
of
optimization
or
objective
function
or
optimization
criteria,
we
try
to
model
what
was
defined
in
our
C
55:41
in
the
PCE
space.
So
we
have
an
objective
objective
function
there
as
well.
We
have
some
more
elaborate
way
of
defining
an
optimization
metric
that
you
want
or
multiples
of
those
that
you
want
to
optimize.
For
so
there
were.
There
was
some
vendors
that
thought
that
we
could
do.
We
they're
interested
in
optimizing,
multiple
metrics,
although
some
had
concerns
with
that.
H
But
so
we
have
these
two
ways
of
optimizing
for
a
picking
a
path
and
applying
an
objective
function.
Either
you'll
say:
oh,
this
is
my
objective
function.
I
want
you
to
give
me
the
optimal
path
or
you
define
your
own
objective
function
by
producing
a
list
of
metrics
and
you
close
off.
If
you
have
multiple
paths
that
you
compute
engine
produces
you
want
to
break
the
tie
between
those
and
pick
one
of
them.
You
are.
H
H
So
there
was
a
the
sixth
update
we
did
was
with
respect
to
constraints,
basically
to
realize
what
was
mentioned
in
RC
3209,
and
it
was
specific
to
the
bitmap
and
not
the
the
name,
think
they
named
way
of
computing
computing
affinity
paths.
So
we
added
the
usage
leave
there
to
allow
for
exclude
any
include
any
include
all
so.
We
support
in
the
model
these
three
that
are
listed
in
RC
3209.
Now.
H
H
L
L
H
H
H
H
H
We
have
multiple
modules,
external
modules
defined
in
other
drafts
and
in
other
working
groups
as
well,
that
are
augmenting
our
models.
So
if
we
go
ahead
and
make
a
change
to
the
nmda
style,
we
want
to
coordinate
with
them
as
well
and
notify
them
that
we're
doing
this
and
they
will
be
impacted,
so
their
models
need
to
be
updated
and
synchronized
as
well.
H
We
have
one
last
point,
which
is
the
dynamic
created
tunnels,
which
is
a
system
generated
tunnel.
So
far,
we
in
our
discussions,
we
were
attributes
of
those
tunnels.
We're
going
to
show
up
under
the
state
leaves
so
we
branch,
config
and
state
to
show
the
applied
and
their
intended
on
a
fight
as
well
as
captured
the
dynamic.
So
far.
This
was
the
thinking.
Now.
H
If
we
migrated
to
the
dash
state
module,
we
were
not
sure
if
we're
okay,
to
continue
showing
the
dynamic
attributes
of
tunnels
of
dynamic
tunnels
under
state
or
should
we
have
two
lists,
a
list
for
an
applied
configuration
and
another
list
for
dynamic,
created
tunnels.
So
we
have
a
case
where
in
NT
tunnels
where
tunnels
are
created
dynamically
by
the
system,
an
example
is
auto
bypass
tunnels
or
back
up
tunnels
or
automesh
tunnels.
These
are
created
by
the
system
and
we
wanted.
F
To
model
those
ok,
Rob,
Wilson
Cisco,
say:
if
you
to
move
to
nmda
style,
then
when
you
have
an
endgame
Oh
Joel
we've
had
the
confidence
state
in
a
single
tree.
The
operational
state
data
store
would
show
you
these
dynamically
created
entries
because
they're
not
coming
from
the
Dino
datastore
they're
just
coming
from
the
system.
That's
fine
and
you
can
create
them
there.
So
when
you
create
a
separate
state
version
that
module
again
you'd
put
the
dynamic
entries
in
the
same
one,
there's.
F
If
you're
running
in
an
MVA
on
an
existing
device,
you
create
an
extra
state
tree
to
serve
that
purpose.
I
haven't
state
module
and
you
write
it
there
so
effectively
the
state
modules
you
could
think
that
is
being
like
the
short
hormones.
Implementation
of
a
dynamic
data
set
of
an
operational
data
store,
yeah.
F
H
L
H
Stuff,
thank
you
yeah.
Definitely,
we
want
some
clarification
on
it,
so
we
want
to
move
with
the
working
group
consensus
on
this,
so
the
tea
topology
model
is
is
is
doing
the
or
state
module
we
could
migrate
as
well
to
be
aligned
once
we
chat
offline
and
clarify,
although
knishes
in
terms
of
next
steps
like
I
mentioned,
we
need
to
grow
close
on
an
MVA.
We
need
to
continue
on
working
with
other
team,
defining
our
pcs
for
the
tunnel
and
the
path
computation
in
terms
of
RSVP
base
and
extended
draft.
It
is
stable.
H
M
M
It's
also
for
path
computation.
So
in
particularly
for
young,
our
PC
of
data.
We
are
the
redefine
as
an
augmentation
of
the
eternal
LTC,
so
they,
our
our
disease,
is
provide
as
an
augmentation
of
the
eternal
PC
we
align
our
grouping
in
in
younger
EA
types,
common
grouping
and
other
support
for
multiple
paths.
Computational
requests
using
more
or
less
the
same
concept
as
vector
in
this
era
with
the
synchronization
list.
M
Okay
here
is
the
there
is
the
G
table,
support
with
the
link,
and
we
use
this
support
for
tracking
young
model
for
state
officiant
to
track
also
issue,
and
we
track
some
opening.
We
have
some
open
issue,
but
we
solve
some
sudden
open
issues
with
respect
the
last
IDF
and
we
there
are
other
five
that
are
being
discussed
jointly
with
the
TA
tunnel
model.
M
This
is
the
basic
open
issue
that
we
have.
We
are
still
in
discussion
with
that,
yet
with
the
eternal
guides,
the
first
one
is
that
for
topology
D
we
solved
the
problem
of
what
is
the
meaning
of
topology.
It
is
clear
so
with
track,
but
the
follow-up
question
is
how
to
use
this
topology
D
in
the
sense.
How
can
be
chosen
this
topology
G's
to
be
used?
And
if
it
is
the
case
that
among
DSC.
M
Can
decide
that
request,
ta
tunnels
at
ARPA
in
topology,
1
or
2,
depending
of
path
computation
that
has
been
provided
before
so
this
is
us
to
be
discussed
with
with
the
other
guys.
So
other
issue
is
related
to
the
request
for
to
shrink
a
little
the
tunnel
parameters,
config
list
of
attribute
that
we
should
we
cannot.
It
is
useless.
No,
it
is
not
used
to
use
a
full
to
use
for
us
because
there
are
a
lot
of
thought.
M
M
Then
there
is
a
residual
bandwidth
of
an
issue
that
there
has
been
provided
at
by
Daniel
a
presentation
about
this
in
PCM
PC.
This
is
for
us,
his
general
T
concept,
not
just
for
a
preceptor,
and
we
think
that
is
a
new
metric
for
a
minimum
salvadore
several
bandwidth
and
can
be
help
to
minimize
the
number
of
odd
computation
requests.
M
Then
there
is
the
request
to
have
a
relaxed
about
constraint
concept
so
in
in
in
TCP.
There
is
already
this
feature
and
that
that
providing
the
fact
that
the
path
computation
must
must
fail
if
a
constraint
is
not
met
or
in
cases
a
taxable
constraint
can
be
relaxed
at
Assad.
The
path
competitions
not
fail
so
needed
again,
some
needed
also
for
Pat,
computationally,
DC
and
and
as
to
be
discusses
that
can
be
bring
into
the
context
of
the
eternal
model.
M
M
M
M
M
Obviously
needed
to
have
further
comments
and
feedback
from
working
group
so
that
there
is
the
the
the
basically
an
issue
that
issue
discussion
regarding.
Then
they
needed
to
reduce
the
number
of
part
computational
requests,
but
we
think
that
it
is
is
an
implementation
issue
is
not
a
problem
of
standardization.
M
I
Holy
I
think
a
surgeon
for
summarizing
all
these
issues.
There
are
some
very
important
one
and
useful
like,
for
example,
the
lack
of
order
of
relaxation
of
constraints.
That
is
definitely
missing
and
it's
quite
easy
to
address.
There
are
some
issues
that
I
think
is
just
misunderstanding
like,
for
example,
the
last
one
that
you
said
about
protection
I,
don't
think
that
we
actually
are
related
to
signaling
in
any
way.
So
we
model
cheat
on
our
model.
I
We
do
not
assume
that
it
would
be
signaled
by
some
protocol
and
protection,
local
protection,
entrant
protection-
it's
not
only
important
parameter
for
in
tunnels,
but
also
for
Park,
complication
and
stuff.
Like
that,
so
some
of
these
things
is
just
we
could
just
figure.
You
know
talked
and
started
yeah
the
the
think
about
it.
Apologize.
M
L
L
Many
one
of
the
things
the
anchors
asked
us
is:
were
we
doing
our
pcs
or
were
we
doing
just
reads
and
writes
this
one
seems
to
focus
on
our
pcs
along
a
train.
My
understanding
is
the
base
model
needs
to
be
able
to
do
reads.
Rights
and
our
pcs
did
do
I
understand
that
in
your
in
your
work-
and
that's
just
a
excuse
me,
it's
a
point
of
question
because
it's
part
of
the
standardization
process
of
the
base
given.
B
L
B
We
typically
don't
gauge
the
interest
for
a
document
in
the
joint
session,
but
given
the
overlap
of
the
topic,
but
PCE
we're
gonna
make
an
exception.
So
I'll
do
a
quick
poll.
How
many
of
you
have
read?
The
latest
version
of
this
document
can
I
get
a
show
of
hands.
Please
a
few
of
those
who
read
the
document.
How
many
think
that
this
is
ready
for
an
option
see
a
few
more
hands
than
last
time?
C
Shirt
commandment,
so
in
the
interruption
working
group
we
adopted
practice
to
reveal
document
externally,
twice
one
when
its
process
of
being
adopted
and
the
content
before
working
or
plus
code.
So
rather
than
waiting
till
working
group
last
columns
and
going
to
young
doctor,
you
might
want
to
review
it
with
external
party
while
it's
going
through
working
reproduction.
So
you
don't
want
to
focus
on
something
that
might
be
changed
very
close
to
the.
B
K
D
K
O
Honestly
is
all
woozy
from
away
and
para:
maybe
we
can
share
the
document
with
PC
because
we
have
got
the
questioners
in
the
past
that
we
need
to
keep
a
PC
working
group.
Inform
that
since
there
is
some
say
common
expertise
to
be
addressed,
I
don't
I
think
it
could.
We
can
do
that.
So
it's
not
a
problem.
K
K
A
really
good
point
to
raise
while
we're
running
these
joint
meetings.
It
makes
it
easy
to
just
keep
this
discussion
in
in
here,
I'm,
not
sure.
If
we're
gonna,
you
know,
we
say
this
meetings
in
experiment,
so
we'll
see
what
happens
and
we'll
make
sure.
Thankfully
we
have
the
PC
here
so
make
sure
to
cortex
them.
Okay,.
N
J
Actually,
we
try
to
augment
the
pasty
topology
model
on
this
particular
update.
That's
a
major
update
and
we
claim
that
it
is
an
MDA
compliant,
as
the
apology
claim
that
they
are
named
a
compliant,
but
I
think
we
found
some
issue
when
some
it
compiles
well
until
they
topology
update
was
taking
place.
So
we
have
some
glitches
here
for
the
namespace
on
I.
Think
some
of
them.
You
know
after
Network
types
we'd
have
a
/w
sent
apology.
I
think
we
probably
need
some
prefix
on.
J
So
this
is
update
and
I.
Think
we
need
to
continue
to.
You
know,
make
some
efforts
online,
the
theater
policy
and
then
kind
of
copy,
whatever
you
choose
to
do
and
really
kinda
reflect
put
some
of
the
appendix
issue
as
well.
But
this
is
simple
model,
so
I
don't
know,
I
need
to
talk
to
ship
and
how
to
do
that.
J
There's
a
good
question:
actually
we
don't
have
impairment
validation,
a
model
here,
although
in
doubles
and
Jim
police
work,
we
actually
have
that
aspects.
So
if
people
feel
we
need
to
add
our
impairment,
validation
for
linear
parameters
to
be
added
onto
here,
we
can
do
that
or
there
can
be
a
separate
young
model
and
augment
at
this
model
so
either
way
is
fine,
but
that's
something
that
we
need
to
talk
in
C,
careful
detail:
it's
not
this
year,
so
I
rather
not
talk
about
much
surer.
That's
after
this,
we.
J
J
J
We
have
both
containers
or
tunnel
configuration
internal
state
and
Alice
faith
and
device
configuration
quite
simple:
it's
not
complete
yet,
but
you
just
start
it
as
a
base
for
zero
zero
zero
one,
and
you
need
to
continue
to
line
with
the
latest
updates
from
T
to
no
and
any
comments
and
I
think
this
might
be
a
good
place
to
get
out
adopt
it.
Although
it's
a
sinister
version,
there
might
be
some
fiction
issue
in
September
I'd
like
to
have
this
model
adopted
and.
P
J
Yeah
I
think
you
know
when
I
when
you
started
this
one.
This
is
a
technology,
specific
connectivity
and
it
has
a
little
bit
different
implication
because
here
our
connectivity
is
an
old
connectivity
coming
inside
and
coming
out
interface
and
out
outside.
So
we
have
a
little
bit
different
implication
from
topology
connectivity
matrix,
that's
the
first
stage
and
also
I.
J
P
I
J
D
I
J
I
agree
but
I
think
a
charter
40
topology
is
generic
model,
so
I
think
you
are
actually
violating
those
a
multi-layer
assumption.
So
either
way
is
fine,
but
I
think
we
need
to
make
a
career
on
that
because
we
have
other
OTN
and
flexgrid.
Those
guys
are
defining
their
lair,
specific
topology
and
t
eternal
model,
so
I
think
Lou
is
here,
I
think
what.
D
I
K
Hi
Lou
Berger
this.
This
is
like
a
classic
discussion.
We've
had
in
C
camps
and
C
camp
started
where
we
come
up
with
something
that
is
technology
specific,
we
get
it
nice
and
polished,
and
then
once
we
have
the
solution
and
gone
through
all
the
the
difficult
details
to
solve
it.
For
that
one
case,
we
have
to
take
a
step
back
and
look
at
it
and
say
which
of
these
things
are
sort
of
generic
and
belong
in
generic
capability.
K
So
from
those
who
are
working
on,
it
absolutely
always
feels
like
they're
done
at
that
point
that
they
once
they
solve
it,
for
their
technology
they're
done,
but
from
the
common
and
from
the
the
way
we've
done
things
in
a
generic
way.
It's
when
they're
done
that
they
have
to
take
a
step
back
and
say
we
have
to
separate
this.
K
We
now
have
enough
understanding
about
how
to
abstract
the
piece
to
the
generic
and
and
it
is
it-
it's
always
tough
for
the
people
who
are
working
the
problem
because
they
feel
like
they're
done,
and
they
just
want
to
ship
it.
And
then
you
have
to
respect
that
they
they've
done
their
hard
work
and
they
want
to
have
a
solution
they
move
forward.
But
we
part
of
our
standard
process
is
making
sure
that
we
at
that
point.
K
I
have
the
aspects
that
are
generic
representative
generic
fashion,
and
this
is
a
constant
struggle
and
tension
in
NC
camp,
but
I
don't
see
it
ever
going
away
the
way.
Just
because
you
deal
specific
tech
technologies.
It's
a
tough
thing
for
the
working
group
to
manage,
but
it's
really
important,
because
if
we
don't
do
it,
we
don't
end
up
with
generic
capabilities
and
reusable
capabilities.
Sure,
okay,.
P
I
have
one
more
question
regarding
the
connectivity
matrix.
Typically,
the
connectivity
matrix
is
there
because
it
reflects
system
limitations
like
switching
capabilities
in
the
photonic
switching
fabric
of
a
w.zahn
switching
node.
My
question
is
now:
this
seems
to
be
a
configurable.
A
node
or
attribute
connectivity.
Matrix
is
already
writable,
so
my
question
is
shouldn't
that
be
a
read-only
attribute.
J
I
You
could
brew
scanner
so
to
answer
your
question
say
for
physical
raw
drops
that
this
is
probably
true,
but,
for
example,
you
can
see
a
node
as
a
representation
of
optical
domain,
and
then
you
actually
can
configure
the
desirable
connectivity
metric
okay,
so
you
may
administratively
limit,
for
example,
of
various
reachability
from
from
one
interface
to
another.
You
can
also
differently
optimize
the
connectivity
meters,
for
example.
Different
paths
could
be
selected
if
you
want
to
have
a
locker
different,
optimization
criterias.
I
J
N
Q
Q
Q
Balaji
model
that
focused
on
the
in
actual
layer
of
OD
n,
which
is
outer
layer
and
and
in
the
model
is
we
define
the
OT
ontology
and
for
times
when
the
network
type
is
o
TN
and
we
have
a
name
with
screen
type
for
networks
and
an
old
and
available.
How
do
you,
information
for
link,
link
actually
built
actually
and
also
audio
term
net
termination?
Q
Point
information
currently
is
under
being
termination
points,
but
in
the
main
image
that
you
call
suggested,
that
is
a
good
issue
would
be
in
the
tunnel
termination
points,
and
this
is
a
young
tree
from
the
from
the
quality
Emoto
and
for
the
link
attribute
the
country,
the
we
are
to
the
older
version
of
the
teeth
quality
model.
We
were
updated
this
model
and
the
changes
are
past
and
also
move
the
also
move.
Q
The
available
audio
information
of
all
to
the
Dinka
attributes
container-
and
this
is
a
termination,
audio
termination
point
information
and
including
the
adaptation
types
and
tributaries
throught
informations,
and
yes,
no
technology,
no
technical
changes
in
the
since
the
last
ITF
and
next
step.
We
will
address
the
audio
termination
point
issues
and
changes
a
model
tool
to
be
an
FDA
compliant
for
the
audio
for
the
OT
internal
model.
Q
This
draft
is
recently
adopted
by
the
working
group
version
version,
0-0
has
been
uploaded
and
the
distrust
contains
two
your
models
and
one
for
ot
and
tano,
and
there
is
also
our
Auto
for
transport
types,
including
signal
crime,
signal
types
and
tributary
protocol
times
and
the
OT
internal
model
also
Audient
Animoto,
augments
te
hono
model,
okay,
and
for
the
OT
internal
model.
We
have
a
tunnel,
we
have
attributes
for
tunnel
endpoints.
Some
of
the
attributes
are
for
actually
for
multi
domain
scenario
like
pillows
treatment
attribute.
Q
It
indicates
that
where
there
is
a
service
in
the
tano
is
transpose
through
this
domain
or
is
switched
to
another
tunnel
or
the
audio
dunno
in
the
nenes
domain
and
the
kind
source
current
signal
and
destination
you
know,
I
can
be
different
to
indicate
not
bookended
internal,
and
this
is
part
of
the.
This
is
a
cop
okay,.
I
Furthermore,
access
links
could
be
multifunctional,
the
dependent
on
configuration.
They
could
go
the
one
to
ten
different
layers
at
the
same
time.
Okay,
it
could
be,
it
could
be
Ethernet,
it
could
be
SDH,
it
could
be
F
corner
right.
So
again,
it
is
not
clear.
How
do
you
do
that?
So
what
we
started
working
on
and
what
we
seems
to
come
to
conclusion?
It
is
better
to
introduce
layer,
specific
types
rather
than
clear,
specific
admin
tations,
and
we
started
doing
this
by
defining,
for
example,
earlier
groupings
for
grantees.
I
J
R
However,
hard
I
think
to
provide
a
few
follow-up
to
egos
comments.
We're
trying
to.
We
really
hope
to
see
a
kind
of
stable
T
generic
attributes
and
including
both
the
parameters
augmentations
and
the
types
description
so
that
we
can
based
on
this
kind
of
generic
TV
parameters,
to
generate
those
kind
of
layer.
Specific
tactics,
including
Bo's
W
song
and
note
here.
I
So
your
person,
so
basically
what
we're
saying
is
that
it
is
fine
to
have
a
layer,
specific
augmentation.
For
example,
say
it
is,
it
is
fine
to
have
say
IP,
MPLS,
layer,
specific
augmentation
for
topology,
and
but
only
if
it
have
like
a
new
constructs
are
new
in
in
addition
to
what
we
produce
in
the
base
a
topology
model.
So
but,
for
example,
if
you
want
to
have
more
attributes
attributed
say
to
links
or
a
tunnel
termination
points,
it
is
better
to
basically
define
less
specific
types
and
not
to
use
augmentation
at
all.
I
Okay,
so
augmentation
again,
you
need
it,
for
example,
where
it's
like
FRR
kind
of
considerations
which,
which
is
specific,
say
to
take
it
layer,
but
not
other
layers,
but
say
if
you
want
to
have
again
layer,
specific
parameters
for
link
or
TTP's.
I
think
it
is
better
to
to
do
which
is
pretty
much
similar.
What
we
used
to
do
in
gmpls,
okay,
when
we
defined
a
layer,
specific
Elvis.
Q
D
N
D
D
Okay,
so
this
this
as
the
objective
of
increasing
the
programmability
of
network
devices
in
for
devices
model
with
with
young
we
found
one
one
particular
one
is
case-
is
related
to
flexible
transponders,
flexible
transponders.
What
multiple
rates
multiplication
formats
fact
particular
population
format
and
can
be
set
based
on
optical
or
physical
layer.
So,
for
example,
copy
s
key
is
more
robust
than
16
QAM
and
it's
possible
to
readjust
this
physical.
D
Yeah.
Thank
you.
So
the
the
the
scenario
we
we
are
continuing
is
is
referred
to
to
the
abnormal
architecture,
where,
in
particular,
we
have
an
SDN
controller
that
configures
and
configures
not
applying
devices
while
drawing
the
Mangler
receives
and
processes
alliance
in
case
of
birth
and
problems,
and
if
needed,
configuration
for
for
the
maintenance
of
of
the
services.
D
Okay,
so
considering
this
scenario
at
the
state-of-the-art
without
assuming
model
of
this
draft,
if,
let's
assume
to
have
an
active
service
connection,
then
we
have
a
decoration
of
the
physical
layer
implying
a
bitter
narrating.
Does
this
degradation
of
the
service
performance
are
detected
and
an
alarm
is
sent
to
the
on
demand
at
that
point,
new
transmission
parameters
are
computed
and
after
yes,
the
uncontrolled
goes
to
reconfigure
the
data
devices
so
the
transponder,
and
and
at
that
point
the
service
is
recovered.
D
So
you
can
see
that
that
this
workflow
implies
several
tasks,
so
can
be
time-consuming
next
slide,
please,
but
if
we
apply
the
young
model
in
draft
with,
we
can
do
something
something
different.
So
while
active
connection,
while
the
connection
is
ill
in
service,
the
SDN
controller.
Instructs
the
data
plane
devices
on
the
actions
to
do
to
perform
if
an
event
at,
and
so
for
example,
if
the
degradation
opens
the
Sdn
controller
instance
trucks
these
devices
on
how
reconfigure
that
itself,
so
that,
when
the
degradation
happens,
the
recovery
can
be
can
be
faster.
D
So
this
can
be
done
with
models
for
events
and
action
and
unfinished
state
machine
that
can
be
included
into
Matt
Kampf
messages.
Edit
concoct
message,
for
example,
next
slide.
Please
thank
you.
So
this
is
the
tree
of
the
young
model
for
for
event.
One
leaf
is,
is
the
attribute
event
that
that
is,
it
is
a
list.
So,
for
example,
we
can
have
the
event
bit.
Error
rate
increase
the
attribute
to
the
sub
leaf.
Filters
can
be
used
to
further
expressed
event.
So,
okay,
we
are
the
bit
error
rate
increase
but
which
which
impact.
D
So
this
filter
can
be
used
to
put
attraction
so
so
that
we
can
identify
if
the
bit
error
rate
is
higher
than
this
threshold,
so
can
be
a
problem
effectively
a
problem
and
the
area
area
should
be
done.
The
reaction
in
our
use
case
can
be
the
change
of
the
modulation
format
and
the
attribute
execute
actually
recalls
an
RTC
where
the
task
is
encapsulated.
So.
D
D
I
seem
to
have
an
event
of
bit
error
rate
increase
over
the
threshold,
so
we
have
to
take
the
reaction
of
the
up
adaptation
and
at
that
point
we
transit
to
the
new
state,
his
FAC
adapt,
but
from
this
state
we
can
come
back
to
the
steady
state
if
the
bit
error
rate
goes
returns
below
the
threshold,
and
in
that
case
we
can
reduce
the
redundancy
of
the
coding.
So
that's
it.
This
is
well.
We
can
stop
in
at
those
are
further
slides,
but
I
think
we
can
stop
here.
D
N
Linked
to
C
camp,
the
ops
working
group
and
the
supe,
because,
while
to
see
Kempe
because
it
started
from
from
an
optical
use
Kaiser,
but
it's
a
for
sure
this
is
something
that
can
be
can
be
generalized-
can
be
used
in
a
lot
of
different
contests.
So,
as
in
see
camper,
we
we
would
be
happy
to
see
technology
specific
extensions,
but
probably
this
work
that
needs
to
be
done
in
in
other
places.
I
don't
know
if
the
observer
working
group
is
the
right
place
or
net
mod
could
be,
could
be
one
Louis
contributing
moving.
A
R
D
R
D
We
can
see
that
the
performance
we
have
some
performance
parameter
to
monitor
this
performance
parameter
as
to
stay
inside
an
acceptable
range,
so
it
can
be
it
it's
enough
that
it
is
in
this
acceptable
range.
While
it
goes
outside
this
acceptable,
Ranger
becoming
critical,
so
creating
problems
to
the
service
problems
in
terms
of
quality
of
transmission
does
quality
of
service.
We
have
to
take
some
some
actions,
so
it's
something
the
use
case
finally,
is
something
more
related
to
to
the
to
the
to
the
maintenance
of
of
the
service.
In
my
opinion,.
S
You
Greg
and
then
deter
yes,
Greg
Norskies
City.
So
then
you
know
I
agree
with
your
statement
that
it
would
be
good
to
extend
and
look
at
the
generalization
of
this
I
can
pour
into
a
couple
things.
First,
probably
work
on
L
map
that
defined
their
framework,
and
it
has
an
informational
in
data
model
for
controller
that
performs
performance
measurement
and
then
passes
the
information
to
collector.
So
the
collector
can
be
the
one
that
monitors
quality
of
the
service
and
performing
measurements.
It
uses
new
performance
measurement
registry.
S
Another
thing
is
that
in
many
cases,
especially
if
we
talk
about
tacit
network,
then
it
would
not
be
only
one
metric
that
will
be
monitored
as
a
characteristic,
so
the
mechanism
probably
should
be
looked
at
extending
F
having
the
policy
that
combines
multiple
metrics
and
then
defines
an
ability
to
define
in
and
out
of
the
gradation
state.
Thank.
S
D
Our
as
I
said
two
days
ago
in
the
LPS
meeting,
yes,
that
the
work
started
with
optics,
but
finally,
we
tried
to
make
it
generic
and
yeah
for
sure
the
the
packet
networks
are
something
that
we
we
should
think
about
because
yeah,
because
it's
it's
it's
important
and
can
be
a
use
case.
So
yes
thanks.
We
we
will
think
about,
and
if
you
find
some
I
will
start
some
discussion
by
in
the
mailing
list.
D
If
you
any
contribute
contribution
and
any
comment
on
the
use
case,
cases
in
is
welcome
regarding
the
performance
monitoring
that
that
word,
that
you
cited
made
in
my
opinion,
can
be
parallel
in
part-
can
stay
in
parallel
to
to
this
to
this
work
because
we
are
not
defining
any
any
way
of
monitoring,
but
yet
the
our
system
will
exploit
some
monitoring
system,
so
they
can
stay.
I
can
go
in
parallel.
In
my
opinion,.
P
P
Typically,
when
the
signal
degrades
you
have
to
switch
to
a
modulation
scheme
that
also
has
an
impact
on
the
service
data
rate,
meaning
that
it's
typically
reduced.
Let's
assume
that
you
have
an
optical
transponder,
that's
capable
of
carrying
two
times
hundred
Gigabit
Ethernet
and
in
case
that
signal
degrades.
It
will
only
be
capable
to
carry
100,
Gigabit
Ethernet
or
not
two
times
hundred
keke
Gigabit
Ethernet.
This
means
that
this
has
an
impact
on
the
service
that
had
to
be
dropped
and
I
have
doubts
whether
this
should
occur.
P
Autonomously
I
would
prefer
that
an
SDN
controller
or
a
network
management
system
subscribes
to
receive
telemetry
data
from
this
optical
transponder
and
that
an
alarm
is
raised
and
then
in
case
the
signal
degrades
then
either
the
Sdn
controller
has
to
make
sure
that
the
traffic
that
cannot
be
carried
and
longer
by
this
optic
transponder
needs
to
be
rerouted
or
that
the
operator
takes
other
consequent
actions
rather
than
letting
the
optical
transponder
to
to
add
enormous
consequence
actions
that
may
impact
the
traffic.
Typically,
these
degradation
are
increasing
slowly
over
time.
P
D
D
Of
of
the
bitrate,
the
same
would
happen
if
we
work
at
fixed
bound
rate
and
we
increase
the
redundancy
consider
that
this
work.
This
use
case
comes
from
a
project
called
the
orchestra
were
involving
operator
and
also
bandage,
and
one
of
the
use
cases
of
the
of
the
project
to
consider
that
we
we
have
in
at
the
optical
layer
some
service,
a
service
class
that
admits
the
reduction
of
bitrate
in
case
of
specific
events.
D
So
if
we
look
at
the
literature,
we
can
find
the
justifications
for
that
despite
telecom
italia
and
which
is
in
in
this
project.
I
found
justifications
from
from
that
from
from
Nokia
in
in
a
paper
of
last
optical
fiber
communications,
comforts
and
which
is
also
in
this
Orchestra
project
Nokia,
and
there
is
also
some
other
justification
from
the
Deutsch
tile
del
telecom.
Another
paper
cited
in
the
one
by
by
Nokia
and
way
this
is
a
case,
is
just
a
use
case.
D
We
we
are
thinking
to
a
way
of
enlarging
the
filters,
because
if
we
need
to
keep
the
same
bitrate
we
will
we
would
need
one
carrier
more,
something
that
the
sliceable
transponders
admit.
But
we
will
need
to
enlarge
the
filters
along
the
path
and
we
are
thinking
to
an
execution
task
that
will
imply
also
the
enlargement
of
up
filters.
T
T
You
don't
have
to
help
the
interaction
with
control
or
management
Li,
and
so
this
is
a
point
that
I
could
announce
them,
and
the
second
comment
is
that
I
think
yes
mentioned
by
several
people:
I
think
in
this
case
it's
coming
up
some
generic
and
we're
also
working
on
the
microwave
radio
Ning,
and
it's
have
a
similar
feature
which
will
be
automatically
changes.
The
modulation
level
due
to
the
external
conditions,
so
there's
some
a
possibility
to
make
it's
more
generic.
Thank.
D
You
thank
you
for
the
comments
reg
on
regarding
your
first
comment.
So
sorry,
but
I,
don't
I,
don't
see
another
another
way
to
to
to
readapt
transmission
parameters
without
going
to
a
centralized
controller,
but
maybe
I'm
I'm
wrong,
but
I,
don't
I,
don't
see
another
method.
Currently
we
with
the
current
state
of
the
art
we
have
to
pass
through
a
centralized
controller.
This
is
time
consuming.
D
T
D
T
C
So
few
comments
and
extendibility
and
be
more
generic,
so
you
might
want,
rather
than
enumerator
use
cases
to
split
them
in
traditional
another
model
and
to
give
you
ability
to
scale
better
would
be
more
easily
to
consume,
especially
as
you're
going
to
packet
there
number
two
today
our
condition
is
binary.
If
you
go
to
packet
there,
it's
not
going
to
be
binary.
You
really
need
to
understand
what
it
is.
So
it's
not
just
also
true
number
three
and
back
to
Greg
comment.
D
D
C
You
going
the
layers
become
more
generic,
it
will
become
much
larger
space,
so
you
might
want
to
split
or
get
the
cases.
Okay
with
two
actions
today,
they're
binary,
it's
either
false
or
true.
Okay,
so
you
might
want
a
balloon
to
gradual
degradation,
number
three,
its
ability
to
combine
different
events.
B
G
U
Hi,
so
my
name
is
William
Lupton
and
I'm
speaking
here
for
the
broadband
forum
just
to
give
an
update
on
the
on
the
yang
work
that
that
we're
doing
and
how
it
relates
to
the
young
work,
the
idea,
okay,
so
there's
the
is
the
questions
I'll
try
to
answer.
So
what
what
is
it
we're
working
on
and
what
would
we
not
work
on
because
we
would
regard
it
as
as
out
of
scope?
What
are
we
currently
working
on?
What
are
we
published?
What
are
our
sort
of
ongoing
projects?
U
How
do
we
publish
it
and
where
are
young?
What
about
drafts?
Because
people
probably
know
that
broadband
forum
is
a
member
organization?
So
you
know
the
work
does
not
take
place
in
public
and
what
about
the
yang
catalog?
Are
we
putting
our
stuff
in
the
uncataloged,
speak
to
your
guests
from
the
fact
the
question
is
there
that
the
answer
is
yes
and
then
also
just
a
bit
about
our.
You
know
our
practices,
our
ways
of
working.
You
know
what
what
rules
do
we
impose
on
ourselves?
What
about
using
external
yang
and
that
sort
of
thing?
U
U
U
It
might
be
mounted
on
a
power
pole
and
what
we
want
to
mostly
doing.
There
is
actually
publishing
some
it's
defining
some
yang
for
some
physical
air
interfaces
that
have
been
defined
in
itu-t,
so
these
being
the
physical
layers
that
are
used
for
these
this
type
of
device,
and
so
we
did
this
depending
on
the
ietf
interfaces
from
and
also
the
eye
net
and
ITF
yang
types
from
from
from
IETF
and
we're
now
working
on
a
new
version
that
sort
of
adds
some
more
stuff,
bonding
and
reverse
path.
K
K
K
K
U
Are
now
great,
thank
you.
We
are
now
and
I
think
the
certainly
ITF
interface
is
one
of
is
one
of
the
main
ones
that
will
impact
us.
The
other
one
which
is
not
currently
an
RFC
is
the
me
entity,
the
ITF
Hardware
bond,
which
also
has
that
same
state
separation.
So
absolutely
we've
got
to
go
back
and
decide
our
reaction
to
this,
but
I
believe
I.
Think
our
reaction
is
likely
to
be
similar
to
that
of
the
working
groups
within
IETF
I.
K
K
U
So
yeah
sorry
I
thought
you
were
just
distinguishing
an
RFC
and
an
ID
though
right,
okay,
so
yes,
so
absolutely
yeah.
We
have
to
definitely
consider
how
to
handle
this.
Some
thing
you've
just
Paul,
you've
thrown
at
us,
so
the
other
one
we've
published
is
I
mean
I.
Don't
necessarily
expect
you
to
be
able
to
read
that
it's
just
to
get
an
idea,
each
of
those
some
boxes
there.
Ism
is
a
module.
You
can
see
the
impulse.
You
can
see
that
the
blue
is
the
sort
of
general
areas,
the
general
topics.
U
You
can
also
see
the
external
dependencies
and
IETF,
which
this
time
does
include
the
dependency
on
when
IETF
hardware.
So
this
is
what
we
call
common
yang.
So
the
idea
is
that
this
is
it's
sort
of
roughly
equivalent
to
the
sort
of
thing
that
might
happen
in
that
mod
here,
but
goes
beyond
that
a
bit.
It's
some
really
young
that
we
see
being
used
across
multiple
of
our
work
areas,
even
if
some
of
it
is
actually
quite
I
mean
like
you,
can
see,
there's
some
forwarding
modules
in
there
and
some
and
that
sort
of
thing.
U
So
it's
not
all
just
pure
core
stuff
and
we're
working
on
some
new
stuff
too
now
and
you
can
I've
listed
some
of
the
things
we're
working
on
I'll
particularly
mention
the
one
at
the
bottom
alarm
management.
We
definitely
have
a
strong
interest
in
the
IETF
alarm
work
which
has
been
moved
to
C
camp,
but
the
draft
hasn't
yet
been
updated
in
sequence.
So
it's
not
on
the
agenda
in
any
way.
I
wouldn't
be
able
to
go
to
the
C
camp
meeting
because
it
conflicts
with
the
meeting.
So
since.
U
U
Please,
the
I
have
in
fact
done
that
one
of
them
sailing
and
the
other
one
isn't
here,
but
yeah,
okay,
yeah
but
I'm,
certainly
hopefully
before
the
next
meeting
yeah
and
actually,
if
the
alarms
is
something
we're
very
actively
discussing
internally
I
mean
we're,
definitely
want
to
build
our
work
on
top
of
the
so
called
Valene
draft
the
IETF
alarms
draft,
but
we
haven't
quite
decided
yet
so
what
it's
done.
We
want
to
purely
augment
it
versus
bringing
some
proposals
back
into
into
ITF
okay.
So
how
do
we
do.
K
U
We
have
some
ducks
to
get
in
the
row
in
a
row.
First,
though,
you
know,
because
we're
multiple
members
currently
discussing
various
options.
We
need
to
get
those
aligned
before
we,
even
those
individual
members,
as
contributors,
would
bring
that
into
ITF
I
think
but
yeah
no
I'd,
rather
I
do
rise.
That
the
thing
to
do
here
is
not
just
say:
B
be
effort
like
this.
Please
do
it
IIF.
We
do
absolutely
realize
that
you
know
that
doesn't
work.
We
realize
that
we
or
our
members
have
to
bring
the
proposals
in.
U
We
really
do
understand
that.
Okay,
so
how
do
we
publish
it?
We
we
have
our
luck
and
internal
software
release
registry,
which
is
just
a
grand
name
for
a
wiki
page
which
does
list
all
our
published
software,
which
includes
both
drafts
and
standard
yang,
and
we
publish
BB
F
yang
into
one
of
our
own
public
github
repositories,
but
with
draft
and
standard
areas
within
it,
but
we
also
have
that
linked
into
the
sort
of
de
facto
standard
yang
modules
area
via
the
singer
get
sub
module,
which
is
essentially
a
pointer
within
gate
to
another
module.
U
U
So
that's
mostly
a
plug
for
the
own
catalog.
Really,
we
don't
have
a
policy
that
that
our
modules
must
use
standard,
Ayana,
IETF
young
modules
whenever
possible,
and
we
do
by
that
mean
more
than
just
it.
Just
you
know
importing
them.
We
do
mean
using
as
they
were
intended
to
be
used
and
I've
already
mentioned
these
grunt
just
pulling
them
together
here.
So
the
ones
we're
currently
depending
directly
on
are
the
unit
types.
U
The
young
types,
I
have
type
interfaces
and
then
in
a
draft
the
hardware
and
then
also
system
and
I,
already
mentioned-
that
we're
also
in
progress
yang,
is
also
planned
to
depend
on
the
alum,
alarms,
draft
and
I
think.
Finally,
we
also
have
an
internal
sort
of
best
practices
document
which
is
sort
of
the
broadband
forum
equivalent
of
the
RFC
sixty
eighty
seven,
and
indeed
it's
based
on
that
and
it
here's
to
it
as
much
as
possible.
