►
From YouTube: IETF99-HOMENET-20170717-1330
Description
HOMENET meeting session at IETF99
2017/07/17 1330
https://datatracker.ietf.org/meeting/99/proceedings/
A
B
B
C
C
D
C
C
You
got
it.
Thank
you,
Thank
You,
Lee,
yeah,
I.
Think.
If
anything,
the
volume
is
now
a
little
too
high.
Does
anybody
it's
good?
Okay
sounds
very
loud
from
up
front.
Okay,
we
have
the
usual
why
she
say
not
so
usual
note.
Well,
there's
been
a
slight
update.
We
couldn't
tell
you
where
it
is,
but
you're
expected
to
read
this
and
know
how
to
know
how
to
perform
with
it.
I
should
leave
that
there
for
a
minute.
If
you
are
unable
to
comply
with
the
note.
Well,
please
depart
the
room.
C
C
We
then
got
tired
of
talking
about
the
naming
architecture
and
service
discovery
documents
that
we
have
and
sort
of.
The
three
latter
drafts
shown
there
draft
a
CTL
on
our
factory
home
net
documents,
but
they're
they're.
They
are
related
and
relevant,
but
I
think
the
main
thrust
will
be
on
the
CLD
end
document,
and
then
it
has
going
to
continue
to
talk
about
some,
the
NCP
security
and
summation
CP
experiences.
C
Sorry,
yes,
yeah
at
Ed's
request,
we'll
probably
put
the
density,
P,
security,
nation
and
CP
documents
actually
before
the
name
and
architecture
ones
so
that
some
one
of
Ted's
collaborators
can
actually
and
be
in
the
room
flat
thanks
around
210,
okay.
So
yes,
working
Hopkins
update
had
a
minor
update.
They
will
profile,
which
do
this
talk
about
Ted
sock
and
also
than
we
talking
about
home.
It's
also
nine
as
you'll,
hopefully
recall.
Just
over
a
week
and
a
half
ago,
I
started
a
sort
of
final
one
week,
work
and
route
past.
C
All
on
this
I
had
a
couple
of
comments
come
back,
so
those
will
need
to
be
incorporated,
but
I've
had
a
group.
I
are
a
director
that
we
will
then
push
that
directly
to
ITF
last
call
through
his
ad
review
and
that
we
will
kill
off
the
whole
net
with
a
co
three
documents,
as
there's
no
longer
any
need
for
those
two
doctrines
to
go
together
as
a
pair
with
basically
everything
that's
needed,
being
incorporated
in
the
previous
home
at
dot
o
nine
document.
C
We
do
still
have
another
other
documents
which
is
still
technically
around
and
part
of
the
working
group.
The
latter
three
in
particular,
hybrid
proxy,
is
still
waiting
on
DNS
SD
work,
front
enemy
delegation
in
Roman
architecture,
eh
the
options
still
probably
necessary,
but
I'll
waiting
on
what
we
decide
as
a
group
to
do
with
the
name
in
architecture
as
a
whole,
make
sure
that
those
actually
are
they
fit
in
a
consistent
that
all
group-
and
it's
a
big
question
on
this.
First
one
in
the
sect
which
isn't
actually
working.
E
G
Hello,
so
I'm
Julia,
scrubber,
Trek
and
I'd
like
to
just
a
few
words.
Six
lies
about
the
draft,
so
it's
a
very
simple
draft
that
has
two
parts:
a
first
part
that
tells
you
how
you
parameterize
babble
in
a
home
that
it
says,
look
if
you
have
a
Ethernet
link,
use
metric,
96,
okay,
so
babble
doesn't
tell
you
what
kind
it
just
tells
you.
You
have
16-bit
metric
values,
and
here
we
are
saying,
look
an
Ethernet
in
the
home
that
is
metric
96
or
you
must
do
ipv6.
G
You
should
do
ipv4,
because,
obviously,
if
you
have
two
implementations
of
Babel,
one
is
ipv6,
only
one
is
ipv4
only
they
will
associate,
but
they
won't
exchange
any
useful
words.
So
all
of
those
parameters
have
Babel
are
written
down
here
and
there
is
a
second
part
which
is
somewhat
more
technical
because
it
requires
understanding
of
both
h
and
CP
and
Babel.
This
speaks
about
the
interaction
between
H
and
CP
and
Babel.
So
it
tells
you
things
that
are
pretty
obvious
that
you
think
about
it
like.
G
If
you
announce
an
external
ipv6
prefix
over
H
n
CP,
then
you
must
ensure
that
it
can
be
routed
to
next
please.
Now,
this
draft
is
almost
ready.
It
has
just
two
issues.
One
is
that
it
still
refers
to
the
old
version
of
the
source,
pacific,
routing
extensions
that
you
will
tell
you
a
few
words
about
that
later
and
the
other
issue
are
the
security
requirements.
Next,
please
so
in
versions
there
zero
zero,
zero,
one
and
I
think
that's
a
typo,
because
the
current
version
is
zero,
so
that
should
be
0
1.
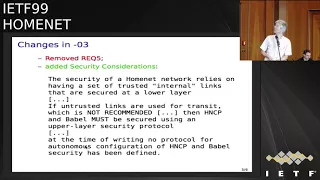
G
However,
what
was
not
obvious
to
me
at
the
time
is
that
this
requires
defining
a
new
sub
protocol
in
H
NCP,
a
protocol
that
negotiates
keys
between
H
and
CP,
routers
and
so
on,
and
defining
a
new
sub
protocol
for
H
and
CP
is
out
of
scope
for
this
document.
So
in
Chicago,
I
asked
for
this
requirement
to
be
removed
from
this
document
and
asked
to
differ
security
to
a
different
document
of
which
I
would
not
be
the
editor.
G
G
The
working
group
today
is
that
we
wait
until
the
source
specific
routing
draft
until
make--the
draft
is
adopted
by
the
data
working
group.
So
I
don't
know
when
it
will
happen,
because
the
Babel
group
is
meeting
is
later
today
and
as
soon
as
it
is
adopted
to
update
the
reference
in
this
draft
to
the
new
version
to
have
somebody
review
the
security
considerations
that
I'd
written
not
sure
I've
done
my
best
I've
written
them
in
good
faith,
but
I
am
NOT.
G
E
Ted
lemon,
this
isn't
actually
a
question.
I'm
gonna
be
doing
a
presentation
on
the
HNC
P
piece
of
this
in
a
minute
which
we
haven't
talked
about.
Sorry,
it
would
be
good
if
we
could
talk
if
we
could
actually
have
a
conversation
about
how
that
ever
like
what
your
reaction
is
to
that,
which
I'm
sure
will
happen.
H
Hi
so
much
abou
T,
so
I
will
just
present
use
the
new
version
encoding
of
the
source,
specific
routing
in
Babel.
So
just
a
few
background
about
the
way
in
Hammett
Babel
is
currently
the
mandatory
routing
protocol
to
implement
for
Annette
and
the
source.
Specific
extension
is
required,
so
the
draft
has
been
written
a
long
term
a
long
time
ago
in
2005
and
the
current
Lisa,
but
the
working
group
has
introduced
mandatory
bits
which
gives
a
really
better
draft
simpler,
but
incompatible
with
the
previous
definition.
H
So
here
was
the
previous
encoding,
where
we
have
three
new
TL
reason
for
update
route
request
and
sec,
no
request
pushing
the
sauce
prefix
at
one
volt
at
random
parts
in
the
message
and
the
new
encoding
is
just
to
have
one
source.
Prefix
meant
that
we
sub
T
re.
So
you
see
it's
really
cleaner
and
the
results
in
better
code
simpler
and
yes,
so
because
it's
a
theory
is
mandatory.
This
extension
is
not
compatible
with
6126,
but
of
course,
the
base
protocol
remains
compatible.
H
So
as
conclusion
for
this
working
group,
so
the
specific
routine
in
Babel
will
use
the
new
format
which
gives
a
much
simpler
extension
but
which
is
incompatible
with
6126.
So
we
will
need
a
flag
day
to
say
now.
We
use
only
the
new
version,
as
gyro
says
this
may
way.
We
may
wait
for
the
barbel
working
group
to
adopt
a
c-stand.
You
draft
thanks
for
your
attention.
C
C
It's
been
five
years,
I
think
now,
I
think
office,
wouldn't
route
session
was
Quebec
in
two
thousand
or
maybe
six
no
six
years,
2011
so
yeah
time
to
move
on,
hopefully
get
some
new
blood
into
the
group
and
maybe
actually
get
some
reiteration
going
because
we've
burnt
out
it's
been
a
long
difficult,
slob
Terry
is
still
interested
in
hearing
from
anybody
who's
interested
in
volunteering
as
a
co-chair
and
still
be
talking
to
people
this
week.
If
you
are
interested,
please
email,
Terry,
but
also
mark
and
I
look
available
after
the
meeting.
C
G
E
There
isn't
actually
a
document
associated
with
this
yet,
but
it's
my
intention
that
there
will
be
if
the
working
group
agrees,
that
this
is
the
right
way
to
go,
which
remains
to
be
seen.
So
the
motivation
here
that
what
triggered
me
to
get
started
on
this
was
actually
the
conversation
that
that
julius
just
referred
to.
E
I
as
Julia,
said
completely
misunderstood
what
it
was
that
he
was
asking
me
to
do
in
our
last
meeting
and
that's
really
part
of
I
think
why
the
the
work
didn't
go
anywhere,
but
I
actually
got
motivated
to
to
dig
in
deep
to
this
about
a
month
ago
and
so
I.
You
know
reread
all
the
documents
and
stuff
like
that,
and.
E
E
Potentially,
it
might
be
useful
to
be
able
to
do
dns
sex
signing
it's
not
clear,
exactly
how
that's
all
going
to
work
yet,
but
but
basically
the
key
thing
is
that
so
and
the
other
motivation
is,
is
I
mean
the
other
aspect
of
this?
Is
that
we
don't
really
know
that
we
need
this,
but
we
I
think
we
do
need
this
or
I
think
we
will
need
this,
and
if
we
don't
do
it
now
we're
going
to
be
in
trouble
later.
E
E
It
tries
to
nominate
the
best
key
or
the
it
chooses.
One
key
out
of
a
selection
of
shared
secret
key
is
presented
by
various
DNC
D
participants.
And
again
you
know
it's
a
it's
a
shared
secret,
so
sharing
the
secret
is
not
really
giving
you
much
security.
So
I
think
that
maybe
partially
my
fault
that
it's
this
way,
because
I
argued
for
this
years
ago
and
didn't
really
get
involved
in
writing
the
document
and
so
I
get
what
I
paid
for.
E
But
here
we
are,
we
need
something
that's
secure,
and
so
this
is
what
I
propose.
What
I
propose
is
that
every
node,
that's
participating
in
H
NCP
should
generate
a
public/private
key
pair
and
each
node
should
share
its
public
key
is
a
TL
v
NH
NCP,
it's
pretty
straightforward!
It's
really
no
different
than
any
of
the
other
things
that
h
NCP
is
doing
so
now,
because
every
node
is
sharing
its
public
key
in
h,
NCP
every
other
node.
Every
node
has
every
other
notes
public
key.
E
That
means
you
can
do
DTLS,
because
now
you
have
identifiers
for
every
node.
You
have.
You
have
a
key
for
every
note.
So
so,
if
a
if
a
node
connects
to
you,
the
DTLS
handshake
can
occur
using
your
key
and
the
key
that
you
know
that
that
node
has-
and
this
is
a
way
that
you
can
identify
which
nodes
you're
talking
to,
and
this
works
not
only
for
for
Babel,
but
it
also
works
for
h,
NCP.
E
You
essentially
have
a
tofu
mechanism
for
distributing
keys,
which
isn't
great,
but
what
it
gives
you
is
the
ability
to
both
notice
that
that
a
host
to
know
which
host
you're
communicating
with
and
to
to
communicate
secretly.
So,
for
example,
if
you
wanted
to
diffie-hellman
now
you
have
a
basis
for
doing
that.
E
E
So,
if
I
think
that
this
is
useful,
I
would
like
to
have
this
I
get
the
impression
that
you
know.
Julius
asked
us
to
write
this
up
and
so
I
think
that,
at
least
in
principle
Julius
agrees
that
this
is
worth
doing.
I'm
hoping
that
others
agree
that
this
is
worth
doing
and
I'm
willing
to
write
the
spec.
If
somebody
else
wants
to
participate,
I'm
happy,
they
have
helped.
I
E
G
To
the
idea,
Robert
Reich
that
so
if
that
is
successful,
it
is
much
more
interesting
that
you
make
it
I
think
we
all
have
this
problem
of
having
a
actually
determine
trust
answer
in
a
helmet
and
if
agency
P
can
provide,
can
provision
cheese
to
everyone
in
the
network
distribute
public
keys.
That
would
be
really
bad
big,
not
only
from
the
point
of
view
of
the
routing
protocol
and
agency
P
itself,
but
especially
for
all
the
application
layer
protocols
that
we
want
to
secure
in
the
helmet
yeah.
E
One
of
the
other
things
that
I
really
feel
motivated
to
have
security
for
is
the
TLS
key,
that's
used
by
the
user
interface
of
your
home
net
right
now,
when
you
talk
to
your
HTTP
server,
you
aren't
using
TLS
or
if
you
are
you're
clicking
through
some
kind
of
warning,
and
it
would
be
nice
if
we
could
figure
out
a
way
to
make
that
work
as
well.
Although
that's
not
entirely
clear
from
what
we're
doing
here,
because
we're
not
actually
sending
certs
around,
we
could
also
have
a
cert
TLV
though,
and.
I
E
E
Yeah
well
right,
you're
right,
we
could.
We
could
just
have
that
TLD
and
maybe
that's
the
right
thing
to
do.
I
don't
know
I
mean
there
is
a
point
to
be
made
that
we
could
be
using
Acme
to
get
keys
for
each
of
these
devices
that
are
actually
signed
by
a
PK
by
the
PKI,
and
then
your
browser
wouldn't
even
pop
up
a
warning
message.
When
you
try
to
talk
to
your
web
tier
to
your
UI
on
the
on
the
device,
which
would
be
great
so
yeah.
E
C
Positive
feedback,
yeah
I
have
a
couple
questions,
but
I'm
starting
up.
Can
you
go
back
to
your
first
slide?
Please
Ted
to
first
slide
yeah.
Yes,
this
one,
so
it's
quite
clear
from
the
presentation
how
this
would
authenticate
subsequent
messages
between
H
and
ours,
but
not
quite
sure,
I
can't
see
how
this
addresses
the
first
issue
of
how
you
limit,
which
a
channels
can
participate.
It.
E
Provides
a
thing
that
you
can
identify:
hnr
is
with
the
process
of
limiting
which
H
NRS
Connect
is
out
of
scope,
but
that
is
to
say,
I
haven't
I'm,
not
interrupt.
Well,
I,
don't
know,
I
mean
it
might
be.
It
might
be
worth
putting
that
in
this
graph
too,
but,
but
you
know
it
essentially,
it
gives
it
gives
whatever
or
whomever
is
managing
the
network,
a
handle
to
use
to
identify
bad
actors
and
to
also
or
alternatively
and
a
handle
to
use
to
identify
truck
trusted
actors.
So
the
more
reactive
and
proactive
prevention
well.
C
E
Know
the
we
haven't
gone
down
the
path
of
defining
the
user
interface
of
the
home
and
that's
what
this
does
is
it
basically
allows
all
of
the
routers
in
the
network
to
to
prove
that
they
are
who
they
are
and
to
repudiate.
Sorry,
all
of
ya,
all
the
road
to
repudiate
routers
that
are
not
identified,
and
then
those
routers
can
show
up
in
the
user
interface
and
the
end
user
can
say
well,
I,
don't
recognize
that
Robert
right,
you
know
the
routers
can
actually
have
like
something
printed
on
the
box.
E
That
says
this
is
the
idea
of
this
router
and
then,
when
you
go
into
the
user
interface,
you
could
identify.
That's
the
router
that
you
wanted
on
your
network
and
if
you
see
a
router
that
you
didn't
want
on
your
network.
Well,
you
can
check
the
box
next
to
it.
That
says,
don't
allow
this
one
yeah,
but
it's.
C
Looking
very
useful,
you
know
about
wavin
aside,
I
participate
in
a
monthly
in
SF,
Coordination
called
various
other
DNS
vendors,
and
you
know
folks,
and
on
our
last
call
good
half
of
that
call
was
taken
up
in
the
discussion
of
how
you
would
dispute
things
like
DNS
SEC
trust
anchors
within
a
home
scenario
happens
at
lot.
C
of
my
area
and
Steve
prophet
was
around
in
that
discussion,
and
this
is
exactly
something
we've
talked
about
meeting
for
that
right.
J
Thanks
David
scan
Ozzy
Apple,
so
first
off
this
is
really
cool.
I
would
really
love
for
the
trust
anchor
or.
However,
we
want
to
call
it
the
trust,
establishment,
the
first
step
to
not
be
out
of
scope,
because
every
as
we've
seen
with
most
of
the
security
issues.
This
is
one
of
the
sharp
edges
and
if
we
just
say
oh,
we
pump
that
down
the
road.
Then
everyone
will
just
not
implemented
and
at
the
end,
it'll
be
just
pointless,
because
anyone
can
just
roll
new
public-private
key
pairs
anytime.
They
want
to.
E
C
J
I
said
holy
I
totally
agree.
I
wasn't
recommending
that
we
enforce
say
this
particular
hardware
solution
by
that
I
mean
this
particular
radio
of
this
particular
button
do
I.
However,
the
laundry
list
approach
is
the
one
way
to
guarantee
that
no
one
will
do
any
of
them,
or
that
two
vendors
will
do
different
ones,
and
also
this
really
does
impact.
What
you
were
talking
about
earlier.
Do
we
use
Rockies
versus
x.509
I,
don't
feel
strongly
about
either
of
them,
but
it
impacts
this
so
going
forward
on
this.
E
What
I
would
suggest
we
do
is
actually
write
out
that
laundry
list
anyway,
not
because
we
think
it's
definitive
or
the
final
thing,
but
because
it
gives
us
something
to
work
with
and
then
sit
down
and
think
about
like
well.
Can
we
come
up
with?
Can
we
can
we
draw
a
circle
around
parts
of
this
laundry
list
and
say
if
you
implement
any
one
of
these
plus
that
one
that's
enough
or
I
mean,
can
we
come
up
with
something
that's
reasonable
to
require?
E
E
E
The
implementations
that
I
had
to
choose
from
or
agent
H
net
D,
which
I
could
not
get
to
build
on
a
bun
too
for
more
money.
Hi
Simha,
which
looked
in
interesting
but
wasn't
didn't,
have
any
documentation
and
shn
CPD,
which
had
some
documentation.
But
the
main
thing
that
was
great
about
it
was
that
the
code
was
very
readable
and
so
I
was
able
to.
It
was
it's
relatively
small,
so
I
was
able
to
just
kind
of
grok
it
and
I
was
able
to
get
it
to
build,
and
that
was
great.
E
E
The
documentation
was
sufficiently
detailed
to
get
me
through
it,
but
I
had
to
really
think
about
what
was
being
said
and
I
had
to
really
build
a
mental
model
before
I
could
get
it
working
like
I,
couldn't
just
kind
of
flip
a
switch
because
you
wind
up
having
to
actually
change
sort
of
the
default
interface
layout
of
of
open
wrt,
which
is
a
real
pain,
obviously
in
production.
We
would
like
that
not
to
be
that
hard.
E
E
E
The
open,
wrt
router
Deacon
figured
all
of
its
ipv4
addresses
on
all
of
its
interfaces,
and
my
host
then
lost
its
IP
address
and
ipv6,
for
whatever
reason
wasn't
working
and
it
really
sucked-
and
it
took
me
kind
of
a
while
to
get
my
network
back
like
I,
had
to
go
around
and
like
go
to
the
serial
console
of
my
open,
wrt,
router
and
I
had
to
like.
You
know,
turn
on
my
TV
and
switch
it
to
the
console
of
my
my
Ubuntu
box.
It
was
kind
of
a
pain,
Julius.
E
Yes,
so
I'll
get
to
that
in
a
minute,
so
this
is
actually
not
the
last
slide,
even
though
it
says
conclusions
so
I
don't
really
feel
like
this
is
quite
ready
for
demoing.
If
you're,
if
you're
a
true
believer,
you
can
get
it
working
if
you're,
not
a
true
believer
chances
are
you're
not
going
to
get
it
working.
E
E
E
There
are
some
things
in
the
in
the
specification
and
that
would
particularly
include
the
thing
that
Julie
has
just
referred
to,
which
caused
the
part
of
the
problem
that
I
saw,
which
is
that
I
couldn't
even
talk
to
my
routers
over
over
my
ipv4
local
mattad
addresses.
That's
broken.
That's
got
to
get
fixed.
That's
that's!
Not
the
right
default
behavior.
E
Another
reason
that
it's
broken
is
because
we
don't
have
a
naming
architecture,
and
so
even
though
I'm
pretty
sure
that
I
actually
had
ipv6
I
can't
it's
been
a
month
and
a
half
since
I.
Did
this
I,
don't
remember
the
details,
but
my
recollection
is
I.
Did
a
by
vb6
but
I
couldn't
figure
out
what
the
ipv6
address
of
the
router
was,
and
so
I
couldn't
get
to
the
user
interface
so
I
had
to
anyway.
So
getting
a
working
naming
architecture
would
really
help
with
this.
Because
then
I
could
have
just
said.
E
You
know
connect
to
the
because
there's
a
there's,
a
default
name
for
the
router
that
you
can
connect
to
that's
supposed
to
be
guaranteed
to
work,
and
when
my
IP
before
routing
was
working,
it
was
working.
So
if
we
had
naming
working
better
than
that,
would
work
and
there's
just
a
bunch
of
integration,
work
to
do
and
I
think
this
is
not
a
hard
thing
to
do,
and
I'd
really
like
to
do
it.
E
E
So
one
of
the
challenges
I
ran
into
is
the
spec
is
like
you
have
to
read
the
whole
spec
and
then
you
form
your
mental
model,
and
then
you
read
it
again
a
couple
of
times
and
then
eventually
you
understand
how
it
works.
I
think
that
could
probably
be
improved
and
I
think
it
would
be
worth
doing
that
it
might
be
that
it
gets
improved
in
HNC,
P,
Biss,
spec
or
it
might
get
improved
in
a
informational
document,
a
table
stock
or
something
like
that.
But
we
got
to
do
something
about
this.
E
I
think
that
the
way
it's
done,
the
amount
of
work,
that's
involved
in
understanding
the
network,
to
the
point
where
you
can
debug
it
is
too
much
and
and
I
think
that
in
h,
NC
p
actually
isn't
that
complicated.
So
it
shouldn't
be
that
hard
to
understand,
so
we
should
do
something
to
help,
and
that
is
my
last
slide
comments
or
tomatoes
or.
H
H
E
Report
so
I
was
in
kind
of
a
hurry,
and
so
so
I
have
not
done
all
the
documentation.
I
would
like
to
work
with
you
on
on
actually
solving
these
problems.
I
mean
that's
actually
what
I'm
alluding
to
here,
I
think
you
know
I'm
not
saying
somebody
else
should
go
off
and
do
this
integration
work.
I'm
saying
I
would
like
to
do
this.
Integration
work
and
I'm
happy
to
hear
that
you're
interested
in
yeah.
H
I
appreciate
a
lot
that
you're
working,
we
are
really
all
testing
it.
I
have
to
admit
that
the
implementation
is
a
bit
old.
That
said,
the
way
you
present
it
you're
discussing
the
validity
of
the
protocol
based
on
your
failure
to
make
it
run
in
your
network
right,
and
that
disturbs
me.
Quite
a
lot
like
in
front
of
90th
audience
you
come
I
was
not.
Actually
we
got
students,
students
like
19
years
old-
they
can
make
it
work,
so
I'm,
sorry
to
be
that
ours,
but
you
were
on
the
slide.
G
E
Not
sure
that
that
makes
me
feel
any
less
insulted,
but,
but
so
so,
just
just
to
quickly
speak
to
that
point.
What
I'm
getting
at
is
not
that
so,
of
course,
I'm
perfectly
capable
of
getting
this
stuff
working
and
not
speaking
for
myself,
I'm
speaking
for
the
actual
end
users,
who
are
the
targets
of
this
technology,
the
people
that
we
actually
want
running
it
for
them,
it's
just
too
hard,
even
for
a
reasonably
knowledgeable
network
person,
unless
they
really
really
want
to
get
it
working
or
it's
their
assignment
or
they're.
E
A
student
who
has
a
lot
of
spare
time
which,
as
looking
back
as
a
student
I,
remember
having
like
an
amazing
amount
of
spare
time
which
I
didn't
think
I
had
at
the
time.
But
anyway,
those
are
in
our
target
audience,
and
this
has
to
work
for
our
target
audience
and
that's
what
I'm
getting
at
it's
not
again.
Really.
My
point
is
not
to
say
that
you
did
a
bad
job.
You
did
a
great
job,
it's
just
that
we
aren't
done
yet
and
there's
a
lot
more
work
to
do
right,
I,
just.
H
Want
to
point
that
yeah
home
that
is
running
is
not
running
out
of
the
box
of
the
open,
the
village
routers,
because
when
you
install
one
well,
it's
not
a
day
enabled
by
default,
so
you
have
to
explicitly
enable
it,
which
is
already
too
much
for
an
end-user.
Second
point
is
that
your
use
case,
if
I
understood
it
right,
was
with
10
L
upstream
interfaces,
which
is
not
exactly
the
base
audience
either.
So,
if
sorry
with,
you
used
tunnel
interfaces
right,
I.
E
L
I
think
you
should
look
at
icmpv6,
known
information,
queries,
ping,
6,
W
or
just
pinging.
The
all
nodes
multicast
address
will
make
it
very
easy
to
learn,
although
v6
nodes
and
then
you
could
have
gotten
the
address
of
the
router
so
I
get
get
sounds
to
me
like
getting
the
V
being
able
to
to
local
v6
communication
you'll
be
able
to
when
v4
breaks
again
you'll
be
able
to
then
get
to
your
router
and
reconfigure.
It
yeah.
D
Tells
least
speaking
as
a
participant
I
regarding
who's
our
target
market,
it's
good
to
keep
the
end
user
in
mind
so
that
we
can
create
something
that
really
someone
else
can
put
together
and
make
deliverable
the
the
target
market
for
this
group
should
be.
You
know,
arrow
and
apple
and
Belkin
and
d-link
I
think
I'm
doing
that
in
alphabetical
order.
Yes,
but
all
you
know
in
you
know
somebody
that's
going
to
sell
it
and
support
it,
not
to
mention
service
providers
as
well
that
have
their
home
gateways,
so
it
doesn't
have
to
be
perfect.
D
E
Perfect,
if,
if,
if
our
target
market
is
somebody
like
ubiquity
or
Google,
then
I
agree
with
you.
But
unfortunately,
if
our
target
market
is
some
of
the
smaller
router
vendors,
they
aren't
going
to
do
that.
Integration,
work
and
the
way
that
you
address
that
market
is
that
you
put
the
code
and
open
wrt
and
make
it
work.
You
have
an
open,
wrt
distribution.
That
out
of
the
box
is
doing
the
right
thing.
They
still
gonna
skin
it
with
something,
of
course,
yeah.
E
D
There
we've
been
doing
that
since
the
very
first
day
of
trying
to
get
it
working
well
and
hope.
The
wrt
just
don't
set
your
sights
so
high
that
you
can
never
reach
it.
They
can
do
a
little
bit
of
work
as
well
and
it
might
start
with
ubiquity
and
Google
and
Apple,
and
then
the
other
guys
follow.
Who
knows?
That's
all.
M
Hi
George
Michaelson
a
penny,
so
Ted
I
actually
think
what
you
had
was
an
extremely
real
experience
and
I.
Don't
think
it
should
be
disregarded.
I
think
that
sense
that
something
should
be
intuitive
and
you
should
be
able
to
construct
from
scratch.
It's
understood
to
have
components
you
build
from
the
standard
component
and
then
you
hit
a
moment
where
it
doesn't
work.
I
actually
agree
with
you.
M
That's
a
very
strong
signal,
something
isn't
baked
yet
and
it
might
be
as
simple
as
there's
a
wiki,
that's
not
being
kept
up
to
date
ascribing
some
of
the
stepping
stones
you
have
to
bridge
over
or
it
might
be
diagnostic
elements
I'm
going
around
in
my
head
thinking.
If
I
were
building
systems
than
they
had
potential
to
become
unreachable,
I'd
want
a
heartbeat
signal
coming
out
of
the
router
and
some
packet
form
on
the
wire.
M
Saying
me
me
me
me
me
so
that
you
could
have
at
least
on
low-level
TCP
dump
or
something
and
seam
packet
flows
on
an
unbound
interface
discovered.
What
you
wanted
I
mean
sure
it
zeroconf
dns
SD,
something
would
have
been
great,
but
even
primitive
things
should
have
been
there.
So
I
personally
think
what
you've
had
is
a
very
real
and
valid
experience
and
I
go
to
it's
not
quite
baked.
Yet
it
should
be
possible
to
do
what
you
tried
to
do.
N
D
N
It's
really
we've
moved
on
to
other
things:
okay,
I'm
just
it
sounds
like
Ted
saying
that
hey
there's
still
more
to
do,
and
maybe
we
do
need
to
wait
till
we've
got
the
naming
stuff
at
least
suspect
and,
and
that
would
be
you
know,
room
for
more
implementations.
I
also
I
could
imagine
doing
an
interim
hackathon.
Maybe
at
Ed's
house.
E
N
E
Doing
it
doing
it
at
an
IETF
really
is
going
to
work,
because
it's
not
a
it's,
not
a
you
know,
that's
not
where
you
run
into
the
real
problems
right.
It's
when
you're
it's
when
you've
got
a
raw
network,
that's
that
you
have
to
cram
it
into
as
opposed
to
you're
building
a
hypothetical
Network
Julius
I.
Just.
G
If
you
are
locally
connected,
you
do
have
the
full
topology
in
H
and
CP,
and
you
do
have
the
names
of
every
single
of
your
nodes
in
HNC
P,
and
here
there
are
two
issues
issue
one
is
we
don't
have
the
tools
you
would
like
to
be
able
to
launch
a
command
on
your
local
node
and
get
the
full
topology
and
by
the
way
yes
roots
are
here.
It's
green
because
you
sweat
it
over
H
and
CP
that
the
green
Rooter
is
called
whatever.
G
So
we
haven't
built
such
a
tool
last
year
with
the
students
but
the
tool
never
reach
production
quality,
because
there
are
two
kinds
of
students:
there's
two
bring
their
stuff
to
production
quality
and
those
who
disappear
immediately
after
they
got
their
grade
right
and
she
happened
to
be
the
second.
But
we
do
have
the
code.
G
G
Second
point:
we
want
those
tools
to
work
without
any
authentication,
I
think
so,
and
if
somebody
were
to
add
security
to
home
net
to
H
and
C
D.
It
would
be
good
to
think
about
this
use
case.
You
want
to
be
able
to
determine
the
topology
of
the
home
that,
even
if
you're,
not
authentic,
authenticated
anyway
yep.
H
H
The
topology
yeah
and
that's
one
of
the
things
that
we
presented
in
many
many
bits
and
bytes,
and
so
that's
why
yeah?
We
are
not
so
much
active
in
terms
of
demo
anymore,
because
we
have
been
in
the
past
a
lot
so
I
think
yeah,
the
color.
The
code
might
be
a
bit
rusty
and
yeah
help
on
maintaining
H
the
t's.
Welcome,
really
we
need
help
and
and
for
the
wiki
like
yeah.
H
O
Jordi
palette
I
am
a
user
of
open,
wrt
and
naturally
from
Lille,
which
is
the
revamp
name
of
open,
wrt
and
I
believe
it
was
about
nine
months
ago.
I
was
dead
testing,
they
have
meta
stuff
and
it
was
working
for
me
so
unfortunately,
because
it
was
working,
I
didn't
take
out
any
any
report
or
anything
because
it
was
working
right
so
we're
using
home.
That
is,
your
edge
router
I.
E
Tested
several
configurations,
yeah,
ok,
cool
I
heard
of
the
part
of
my
problem-
was
my
insistence
on
using
Ubuntu,
as
my
edge
router
makes
life
difficult,
I,
take
it
we're
being
chivvied
well.
Thank
you.
Everyone
for
that
discussion.
I
know
how
yet
another
thing
to
present,
and
this
is
a
lot
longer
so
sorry
about
that.
So
the
reason
this
is
long
is
because
I'm
not
actually
getting
a
lot
of
feedback.
That
tells
me
that
people
are
following
this
work.
E
I'm
just
curious
has
anybody
who
here
has
read
I
know,
there's
one
guy
in
the
back
and
there's
one
guy
up
here
in
the
front.
Who
else
has
read
the
the
relevant
documents?
Thank
you,
Tim.
Okay,
that's
not
too
bad.
Actually
so
I'm
gonna,
I'm
gonna
kind
of
give
an
overview
I'm
actually
going
to
skip
some
of
the
slides
there
here
for
completeness
in
case
somebody
wants
who
didn't
follow.
E
The
entire
presentation
wants
to
read
them
and,
of
course
you
can
ask
questions
and
I'll
go
back
to
them,
but
most
of
the
slides
some
of
the
slides
are
here
just
because
they
might
be
useful
for
answering
questions.
So,
first
of
all
the
goal
of
the
naming
architecture-
Billy,
you
look
up
names
on
the
Internet.
We
have
to
be
able
to
make
it
possible
to
look
up
names
on
the
internet
obvious.
E
We
want
to
be
able
to
publish
services
that
are
reachable
anywhere
in
the
home,
that
we
want
to
be
able
to
discover
services
anywhere
on
the
home
net
and
for
those
of
you
who
are
familiar
with
this
problem
space.
The
reason
why
I'm
emphasizing
that
is
because
mdns
does
not
work
on
an
entire
home
that
unless
the
entire
home,
that
is
only
one
link
so
non
goals.
These
are
things
that
we've
talked
about,
but
are
out
of
scope
for
this
document.
That
doesn't
mean
we
won't
ever.
E
Do
them,
publish
it
DNS
zone
for
the
home
that,
in
the
public
dns
make
service
discovery
available
off
the
home
net,
allow
off
home
net
devices
to
publish
services
in
the
home
net
and
secure
home
that
naming
and
service
discovery
using
DNS
SEC.
These
are
all
things
we
might
want
to
do,
but
not
in
this
document
name
resolution.
So
what
name
resolution
means
is
that
we
have
to
be
able
to
tell
devices
who
to
talk
to
in
order
to
resolve
names,
provisioning.
We
have
to
be
able
to
provide
resolution.
E
We
have
to
answer
the
questions
when
they're
asked
and
one
slight
challenge
is.
We
don't
actually
know
how
to
solve
this
problem.
What
if
your
multi
home
and
you
want
to
access
Netflix
and
you
look
up
your
Netflix
server
using
the
resolver
for
ISPA,
and
then
you
connect
to
the
Netflix
server
with
stream
on
ISP
II,
that's
going
to
suck
and,
more
importantly,
that's
going
to
generate
phone
calls
and
nobody
wants
phone
calls
and
that's
going
to
make
that's
going
to
limit
deployment.
So
we
need
to
figure
out
how
to
address
that.
E
The
idea
with
multi-home
fake
hosts
is
that,
if
you're,
if
you're
multi
on
faith,
then
you
get
prefixes
for
each
of
the
homes,
we'll
say:
there's
two
so
is
PA
n
is
P.
P
you'll
get
a
prefix
for
both
ISPs.
If
you're
capable
of
handling
it.
If
you're,
not
you
only
get
one
prefix
and
the
home
that
has
to
figure
out
which
one
that
is
which
is
a
problem.
E
So
if
you're
capable
you
get
one
prefix
and
you
get
a
list
of
DNS
resolver
IP
addresses
the
addresses
of
DNS
proxies
and
it's
a
different
list
for
each
ISP.
So
you
will
contact
a
different
IP
address
if
you're
looking
up
a
name
that
you're
going
to
use
to
connect
using
ISP
a
versus
if
you're,
looking
up
a
name
that
you're
going
to
use
to
connect
using,
is
P
P
and
the
reason
for
that
I'll
get
to
in
a
minute.
I.
Don't
think
we
really
need
to
solve
this
problem
for
ipv4.
E
We
don't
really
have
multihoming
for
ipv4
anyway,
so
you
know
we're
not
really
losing
anything,
but
it
was
one
of
the
one
of
the
key
things
we
wanted
out
of
this
out
of
the
home.
That
architecture
was
to
be
able
to
multi
home
and
if
we
can
multi
home,
but
multihoming
makes
your
life
miserable.
We
haven't,
succeeded
Andrew.
E
P
E
P
E
I,
don't
think
I,
don't
think
that
I
don't
think
it's
going
to
have
a
theory,
because
because
because
it
makes
sense
in
the
abstract,
I
think
it
has
to
have
a
theory
in
order
to
succeed,
like
so
think
about
your
Google
browser
right
for
your
your
Firefox
browser
or
whatever
right.
It
is
you
you
you
say:
go
to
netflix.com
when
it
goes
to
netflix.com,
that's
got
to
work,
and
so
because
it's
got
to
work.
That
means
that
the
browser
has
to
figure
out
which
is
P,
it's
talking
to
which
sucks.
P
This
this
feels
very
much
to
me,
like
the
economics
answer
of
in
the
long
run,
it
will
all
come
out.
Fine
in
the
long
run,
we're
all
dead
and-
and
the
same
thing
is
true
here
right-
that
the
if
every
application
has
to
start
knowing
oh
I'm,
making
this
connection
and
now
I
need
to
know
which
is
P.
I'm
going
to
use
multihoming
isn't
really
a
whole
lot
of
use.
So
it's
right
so
for
me
to
understand
them.
So
we.
E
Enter
I
mean
the
general,
the
general
expectation,
and
this
is
the
way
it's
been
implemented
in
Android
and
I.
Think
in
Mac,
OS
and
iOS
is
that
the
hosts
are
sorry.
The
application
just
says,
connect
to
netflix
comm,
and
then
the
operating
system
has
an
API
that
goes
and
does
all
of
the
math
that
I'm
talking
about,
and
so
from
the
application
perspective.
You
don't
do
anything
differently
at
all,
except
that
you
have
to
use
this
API.
E
P
So
so
the
the
I'm
just
I
I
understand
that.
That's
that's
what
the
background
is
here,
but
I
I
think
that
I
think
that
you're
gonna
need
a
lot
more.
So
first
of
all,
the
document
doesn't
have
this.
You
know
stuff
in
it
right
right
now,
so
the
document,
the
document
is
not
up
to
date
with
the
slides,
so
it
this
is.
P
This
is,
at
the
very
least,
I
think
a
an
instance
of
the
thing
that
I
sent
to
the
to
the
list,
where
what
we're
doing
is
is
changing
our
scope
a
little
bit
in
order
to
make
it
simple,
and
that
might
be
the
right
thing
to
do.
But
but
this
is
probably
not
what
everybody
thought
they
were
gonna
get
of
out
of
out
of
our
plan.
So
that's
really
the
rock
on
me
yeah.
E
P
E
But
our
answer
isn't
G.
We
can't
do
that.
I
mean
we
had
a
working
group
which
unfortunately
got
closed
a
couple
of
years
or
a
year
ago
that
was
working
on
the
specific
problem,
and
so
so
our
answer
is,
you
can
totally
solve
that
problem.
In
fact,
their
existing
stacks
that
have
pieces
of
the
solution
to
that
problem
built
into
them
already.
They
don't
have
this
particular
piece,
because
this
is
actually
a
slight
enhancement,
so
the
piece
that
they
have
is
I've
got
two
interfaces.
E
P
I
So
I
mean
you
know,
this
goes
back
to
happy
eyeballs
and
things
like
that.
The
first,
you
know
you
need
to
figure
out
which
of
your
connections
is
going
to
work
better
and
I've.
Long
been
a
proponent
that
happy
eyeball
should
not
just
be
about
ipv4
versus
ipv6.
Happy
eyeball
should
be
about
what
is
the
best
connection
that
I
can
get,
and
so
that's
part
of
it,
and
then
you
know.
I
The
first
thing
you
do
with
any
connection
is
your
DHCP
query,
but,
and
that
gets
into
the
weirdness
you're
talking
about
I
mean
your
DNS
query.
Sorry
gently
ordering,
and
one
of
the
problems
that
you're
coming
up
to
is
that
different
domains,
different
networks
have
different
stuff
in
there
DNS
servers,
but
also,
even
when
they
go
to
the
authoritative
servers.
I
Having
different
private
stuff
within
their
DNS
servers
that
the
other
domains
don't
have,
and
it
seems
to
me
that
somehow
what
we
really
need
is
a
happy
eyeballs
with
four
DNS
so
that
you
can
find
the
right
domain
where
you're,
oh
happy,
eyeballs
doesn't
David
salt
everything,
I'm
gonna.
Let
him
talk.
J
Thanks
Barbara
David's
canaussie,
so
yeah
to
answer
these
points.
Happy
eyeballs
does
that
so
this
actually
like
Ted,
was
saying
we
stuff
a
bunch
of
work
in
this
working
group,
but
this
particular
problem
is
solved.
We've
had
this
for
a
long
time,
at
least
on
iPhones,
where
you
have
a
Wi-Fi
interface
and
a
cell
interface,
and
you
want
to
use
series.
You
want
something
to
go
really
fast,
because
users
don't
want
to
wait
and.
J
Well,
to
finish
what
I
was
saying:
one
of
the
things
it
does
is
that
it
does
DNS
for
each
interface,
because
indeed
the
answers
can
be
different
and
then
it
sends
the
query
over
that
elaborate.
Enhancing
that
to
use
the
multiple
source
addresses
that
you've
received
from
the
various
ISPs
on
your
home
network
is
by
no
means
a
stretch
right.
This
is
not
hard.
You
have
the
technology
yeah,
but.
E
I
totally
agree
with
you,
David
I
mean
from
my
perspective
the
this
looks
bad
because
it's
it's
it's
it's
like
when
you're
solving
a
quadratic
equation
right,
you
you,
you
multiply
everything
out,
you
get
all
of
these
terms
and
it
looks
really
messy
and
then
you
go
through
and
you
figure
it
out
and
by
the
time
you're
done
it's
like
really,
but
but
you
had
to
go
through
that
process
and
that's
all
this.
Is
it's
really
not
that
hard?
E
It's
it's
just
a
matter
of
doing
it
and,
as
David
has
said,
most
of
the
code
has
already
been
written.
It's
just.
We
need
a
couple
of
little
extra
pieces
of
shim
technology
to
get
the
information
into
the
stack
on
the
on
the
iPhone
or
on
the
you
know,
laptop
or
whatever,
so
that
so
that
it
can
do
what
it's
already
doing
when
it's
got
to
inter
fit
to
physical
interfaces.
It's
exactly
the
same
problem.
I
should.
E
C
H
Perfect
transition,
perfect
transition
for
another
draft,
which
is
happening
in
interior
or
6-man,
maybe
discover,
and
we
have
an
array
option
for
that.
It's
called
multi
provisioning
domain
discovery
of
looking
for
a
provisioning
domain
and
the
ability
to
get
some
more
information
for
I
mean
I'm,
repeating
stuff
that
most
people
here
already
here
this
morning
in
six-man,
there
will
be
another
presentation
in
interior
and
another
presentation
in
captive
portal
as
well.
So
please
come
and
comment
these
drafts
as
well
thanks
I.
I
Don't
thing
that
I
also
disliked
those
proxies,
the
DNS
proxies
and
I
really
don't
want
to
require
DNS
proxy
for
to
be
able
to
manage
my
different
domains,
even
though
the
home
domain
is
not
on
a
different
interface
really
than
the
other
interfaces,
and
so
I
think
as
we
allow
ourselves
to
have
multiple
DNS
servers.
We
also
need
to
get
away
from
this
idea
that
the
home
has
to
be.
You
check
the
home
before
you
check
anything
else
and.
E
I
E
I
E
E
M
E
F
E
Indeed,
that
that
distinction
is
part
of
why
I
think
that
company
we
were
having
the
confusion
we
were
having
in
the
conversation
so
yeah,
let's
move
on
a
little
bit,
so
this
is
just
some
more
text
about
how
to
how
to
how
to
provision
devices
I.
Don't
think
we
really
need
to
go
into
this
right
now.
Just
know
that
this
information
is
here.
E
If
you
want
to
talk
about
it
later,
we
can
again
I'm
calling
it
a
DNS
proxy,
because,
because
it's
it's
it's
DNS
proxy
is
like
a
switch
in
a
network
you
might
plug
directly
into
the
router
or
you
might
plug
into
the
switch,
but
the
switch
is
the
lowest
common
denominator.
So
that's
why
I'm
using
that
term
and
what
it
has
to
do
is
it
has
to
determine
whether
the
name
is
local
or
not.
E
If
it
is
local,
it
sends
it
to
the
local
resolver
if
it
is
not
local,
it
sent
at
the
ISP
resolver
and,
as
I
mentioned
earlier,
the
source
address.
The
reason
why
the
resolver
is
PA
has
a
different
source
at
a
different
address,
and
there
was
Oliver.
Her
is
BB
is
so
that
the
one
actual
piece
of
software
that's
sitting
there
listening
for
these
requests,
can
look
at
the
source,
address
and
say:
oh,
this
is
a
query
for
is
PA
or
oh.
This
is
query
for
is
BB.
E
E
Proxy
formally,
the
hybrid
proxy
I
have
written
a
new
draft
which
I
will
be
presenting
in
DNS
SD
on
I,
think
Wednesday
yeah,
and
this
is
Stewart
and
I
have
basically
been
conferencing
every
week
for
the
last
two
or
three
months
about
this,
and
so
we've
done
a
lot
of
work
and
so
Stuart's
got
a
whole
bunch
of
cool
stuff
which
you'll
see
in
here.
I've
got
this.
This
is
my
main
thing.
E
E
F
I'll
refresh
your
memory,
you
actually
talked
me
out
of
doing
that.
Oh
we,
the
discovery
proxy,
let's
a
remote
device,
that's
not
able
to
multicast
on
the
link
reach
in
from
the
outside
and
say.
Do
these
queries?
For
me,
the
advertising
proxy
was
imagined
as
the
mirror
image
of
that,
which
is
a
service.
That's
remote
can
reach
in
and
say
advertise
this
for
me
using
multicast.
You.
F
Me
that
we
should
actually
try
to
be
moving
away
from
multicast.
We
should
not
be
encouraging.
More
use
of
multicast
occurs
as
expensive
on
Wi-Fi
it's
if
expensive
and
unreliable
and
hard
to
do
on
mesh
networks.
There's
a
number
of
reasons
why
multicast
is
valuable
for
certain
zero
configurations
in
our
ears,
because
the
network
gets
bigger,
it
rapidly
becomes
not
a
good
solution.
Thank
you.
So
so.
N
E
Okay,
so
so,
basically,
what
that
what
this
means
that
there
are
our
n
plus-1
zones
where
n
is
the
number
of
links
or
possibly
there
are
two
n
plus
one
zones,
because
actually,
after
the
discovery,
proxy
has
two
zones
for
each
length.
But
anyway
the
point
is
they're
purling
zones
and
then
there's
a
then
there's
a
zone
in
which
things
that
use
Stewart's
registration
protocol
will
register
their
names.
Hosts
browse
all
of
these
zones,
either
directly
or
through
a
discovery
broker,
which
is
another
thing
that
Stewart
has
a
draft
about.
E
So
the
required
infrastructure
here
is
that
every
home
net
writer
can,
if
needed.
So
every
every
hundred
router
has
to
have
the
following
things
on.
It
has
to
have
a
discovery
lease.
Actually
it
doesn't
really
have
to
have
a
discovery
broker.
It
has
to
have
a
discovery
process.
It
has
to
have,
as
it
has
to
have
the
software
to
do
a
authoritative
server
for
the
home
dot
ARPA
zone,
and
it
has
to
have
a
discovery
relay
every
home
net
when
it's
running
will
have
probably
a
discovery
broker.
E
This
is
the
problem
with
name
changes
and
inflight
should
have
an
authoritative
server
for
the
home
darpa
zone
and
every
link
on
the
home
that
will
have
at
least
one
discovery
relay,
and
ideally,
actually
it's
probably
better
to
just
have
one
but
anyway,
so
a
typical
home
that
might
have
it
might
look
kind
of
like
this
right.
It
might
have
home
DARPA.
That's
the
Agra,
the
authoritative
the
zone
for
which
there
is
an
actual,
authoritative
server
with
state.
E
It
will
have
the
link
one
homes
on
our
pizon,
which
is
the
zone
on
which
we
receive
mdns
stuff
for
link
number
one.
It
will
have
the
you
know.
It'll
have
three
links
like
that
and
then
home
DARPA,
assuming
that
we
have
a
discovery
broker
home
DARPA
will
be
listed
as
the
only
browsing
zone.
So
when,
when
you
want
to
browse
using
this
remember,
this
is
using
RFC
67-63
DNS
s
D,
so
it's
actually
using
DNS
to
do
service
discovery,
not
mdns.
So
when
you
do
dns
SD
you
go.
You
look
up.
E
E
E
Okay,
like
this
okay
and
then
the
answers
that
come
back
suppose
that
there's
one
one
of
the
printers
is
using
the
registration
service,
and
so
it
actually
registered
a
name
in
the
authoritative
zone
that
will
send
back
an
answer
that,
yes,
there
is
an
IP
p
t
CPM
DARPA
in
PTR
reg
printer
home
DARPA
I'm,
using
like
sort
of
geek
readable
names
here.
Actually
these
names
might
be
human,
readable
names
like
printer
space
at
space,
dead,
space
desk
or
something
like
that.
E
It
doesn't
have
to
be
reg
printer,
but
it's
just
easier
on
slides,
so
the
and
and
then
suppose,
there's
also
another
printer.
That's
only
doing
mdns
and
that's
on
link.
One
it'll
also
send
back
a
PTR
record
I'm,
not
putting
the
relay
proxies
in
here,
because
they're
just
kind
of
therefore
they're.
There
they're,
essentially
just
a
way
to
extend
for
the
advertising
proxy
to
ask
sorry
for
the
discovery
proxy
to
ask
questions
on
multiple
links.
E
So
so
the
broker
gets
back
answers
from
two
different
sources:
it
puts
them
together
and
sends
the
combined
answer
back
to
the
DNS
proxy
and
then
the
DNS
proxy
sends
the
combined
answer
back
to
the
host.
So
this
is
the
sort
of
topology
we've
got
here.
We've
got
a
number
of
different
places,
and
some
of
these
functions
might
actually
be
combined
like
it's
entirely
possible
to
have
a
discovery
broker.
That's
also
a
discovery,
proxy
and
and
just
kind
of
merges
those
two
functions,
and
you
know
you
could
have
in
principle.
E
You
could
have
the
discovery,
broker
the
advertising
proxy
and
the
discovery
proxy
all
be
one
piece
of
software,
that's
doing
all
three
tasks
or
they
can
be
completely
separate
and
be
speaking
DNS
protocol
to
each
other.
It's
it's
entirely
up
to
the
implementation.
How
to
do
this,
but
they
the
functions,
need
to
be
there
in
the
sense
that
it
needs
to
be
possible
for
the
broker
to
talk
to
a
discovery
proxy.
E
Actually
it
doesn't
really
need
it.
The
broker
could
just
be
talking.
The
broker
could
be
talking
to
its
internal
discovery,
proxy,
which
is
talking
to
a
relay
proxy
on
each
link,
and
so
there's
actually
no
need
for
an
explicit
break
between
the
discovery,
proxy
and
the
discovery
broker.
But
you
know
they
are
separate
functions
in
the
functional
chart.
I
am
gonna,
skip
these
slides
because
I've
already
explained
this,
but
they're
here
for
your
reference.
E
So
basically,
the
reason
I
put
these
slides
in
here
is
in
case.
Anybody
needs
to
drill
down
more
and
wants
to
ask
questions,
but
I.
Don't
think
that
we
need
to
go
into
detail
because
I
think
everybody
in
here
already
knows
this
stuff,
so
the
status
right
now
is
that
we
actually
have
a
lot
of
the
specs
written
they're
not
done
they're,
mostly
zero
zeros.
But
we
thought
this
through
pretty
thoroughly
and
I.
E
Think
that
we're
not
too
far
away
from
having
something
which
is
either
mostly
complete
or
entirely
complete
and
I
did
an
implementation
at
the
mdns
relay
right
after
that,
Stewart
and
I
changed
the
spec.
So
it's
not
in
sync,
with
the
current
spec
but
it'll
be
pretty
simple
to
update
it,
and
actually
you
look,
the
code
will
be
cleaner,
so
it's
great.
E
So
so,
if
the
working
group
is
okay
and
I've,
come
to
the
working
group
with
various
proposals
at
various
times
and
been
shot
down,
I'm
really
hoping
that
the
working
group
isn't
gonna
shoot
this
proposal
down,
because
I
think
it's
pretty
complete
I
think
it
does.
What
we
need.
I
think
it's
good
I'd
like
to
do
it
Julius.
Do
you
still
hate
me.
G
G
M
Hi
chose
Michaelson
from
aap
neck,
so
I
think
you're
right
to
say
that
this
is
something
that
should
probably
be
close
to
done
for
the
level
of
which
it
can
define
how
to
do
things
and
I.
Think
some
of
the
confusion
in
the
conversation
at
the
microphone,
at
least
for
me
as
I
understand
it-
is
that
I
think
people
are
wanting
to
see
much
higher
abstraction
of
behavior
and
talk
about
decision
logic
for
the
right
name
and
the
right
address
which
I
hold
naan
microphone
noise
to,
say:
that's
a
multi-dimensional
problem
and
I.
M
Think
saying:
oh,
we
solve
that
in
happy
eyeballs.
No,
you
didn't
what
happy
eyeballs
does.
Is
it
projects
a
single
dimension
of
problem
to
say
what
best
is
and
on
my
platform
of
choice?
Android
there
is
another
dimension:
there's
a
hit
knob
that
says
preference
Wi-Fi
over
cellular
at
all
times,
and
it
has
no
consciousness
that
my
cellular
provider
may
be
offering
zero,
zip
zilch
zero
charge
off.
Can't
access
the
high
bandwidth
TV
and
the
CDN
provider
that
I
get
from
DNS.
M
Lookup
may
well
say
no,
no,
no
use
this
Wi-Fi
binding,
go
suck
it
on
Wi-Fi
consume
my
Wi-Fi
limits
and
leave
me
unable
to
use
Wi-Fi
to
do
other
work.
It's
a
multi-dimensional
problem.
The
best
mapping
is
a
higher-order
question.
What
you
have
laid
out
here
is
an
architecture
for
saying,
based
on
coming
up
from
the
ground
based
on
being
multi
provider.
How
do
I
find
what
name
to
address
mappings
there
are,
and
you
introduced
actually
I
will
say.
I
think
Stewart
was
absolutely
correct.
M
To
say,
please
use
the
correct
labels
for
the
DNS
functioning
elements.
I
think
that
was
an
extremely
important
comment
and
you
do
that
and
I
respect
that
you
introduced
an
idea
called
a
broker.
I
like
that
idea.
I
see
brokerage
is
a
very
good
abstraction
for
what
is
the
best
choice
because
it
puts
it
into
that
multi-dimensional
question.
It
depends
the
best
is
not
what
happy
eyeball
says.
It's
a
complex
decision
that
you
are
describing
in
architecture
for
building
that
model
I
like
that
I
think
you
should
close
off
on
this.
It's
good!
Thank
you.
K
F
F
P
I'm
Andrew
Sullivan
and
my
employer
tells
me
that
I
don't
speak
for
them,
so
I'm
not
going
to
mention
who
they
are.
The
I
agree,
first
of
all,
with
what
I
think
what
Stewart
was
just
suggesting,
which
is
that
the
number
of
moving
parts
here
is
is
probably
actually
the
irreducibly
small
set
and
and
I
think
that
that's
okay
but
I'm
a
little
concerned
about
the
about
the
suggestion
that
we
heard
a
moment
ago
that
we
don't
really
have
requirements
because
we
do
write.
P
We
had
this
architecture
document
that
we
published,
and
it's
got
a
lot
to
say
about
this,
about
what
the
naming
thing
is
supposed
to
do
and
and
and
this
pozole,
as
I
said
to
the
list
and
I
said
I
suggested
earlier-
doesn't
entirely
meet
that
and
I
I'm
mostly
persuaded,
actually
that
that's
fine,
so
I
guess
what
I
want
to
ask
is
you've
got
this
last
bullet
here.
It
says
we
could
be
done
in
fairly
short
order
and
get
on
to
the
advanced
HomeNet
naming
architecture
and
I
want
to
ask
this
time
why?
P
E
So
you
know
the
problem
with
any.
This
is
the
reason
why
I
actually
sat
down
and
wrote
code,
because
the
problem
with
any
spec
that
we
theorize
about
is
that
it's
really
easy
to
theorize
and
you
often
miss
the
details
and,
unfortunately,
when
you
stop
theorizing
and
start
writing
code,
you
realize
that
there
are
complexities
that
you
haven't
thought
about
and
that's
what
you're
seeing
here
what
you're
seeing
here
is
that
is
that
this
has
actually
been
implemented.
The
implementation
is
not
big.
E
It's
like
2,500
lines
of
C
code,
which
I
would
really
rather
not
have
used,
except
that
it's
got
a
run
on
open
wrt.
But
so
it's
it's
it's
it's
really.
It's
really
not
that
hard
to
do
and,
of
course,
my
implementation
doesn't
have
all
of
the
stuff
in
it.
So
I
guess
I'm
exaggerating
slightly,
but
it
really.
It
really
isn't
that
bad.
The
thing
that's
that
makes
it
look
bad.
E
Is
that
all
the
details
to
the
best
of
my
ability
are
here
and
to
me
it
feels
like
we're
close
to
completion,
because
we're
kind
of
to
the
dregs,
we're
kind
of
like,
like
the
the
multihoming
thing,
is
kind
of
the
hardest
problem.
That's
left,
everything
else
seems
totally.
Tractable
I
have
a
specification
for
how
to
manage
the
interface
between
the.
If
you
read
the
mdns
relay
docket,
it
actually
has
a
specification
for
how
to
manage
the
interface
between
the
the
mdns
relay
and
the
discovery
proxy,
and
that
would
fit
very
nicely
into
hn
CP.
E
I
think
I
think
we
really
are
very
close
to
victory
here
and
and
it's
not
as
bad
as
it
seems,
and
therefore
I
think
that
if
there
is
interest
and
I
don't
know
that
there
is
I
mean
I
get
the
impression
that
there
are
a
fair
number
of
people
in
the
working
group
that
are
interested
in
the
advanced
hum
that
naming
architecture.
If
I'm
wrong
about
that,
then
absolutely
we
don't
need
to
do
it.
I
mean
I'm
interested,
but
one
person
being
interested
isn't
enough.
E
E
Yeah,
if
it's
really
up
to
the
working
group,
whether
to
do
whether
to
do
the
follow-on
work
and-
and
indeed
if
we
don't
do
the
follow-on,
if
we
decide
that
we
really
don't
want
to
do
the
follow-on
work,
there
are
some
simple
simplifications
we
could
make
to
the
simple
on
that
naming
architecture.
I,
don't
think
that's
worth
doing,
because
I
think
that
even
if
we
decide
now,
oh,
we
don't
really
want
to
do
this.
We
might
decide
in
five
years.
Oh,
we
really
do
want
to
do
this
so
I
know
I!
E
E
E
C
From
the
chair-
and
it's
not
necessarily
that
it's
not
fun,
this
I
think
longer
term.
We
do
need
to
do
this.
I
should
I'm
part
of
my
rationale.
Standing
down
is
that
I
would
actually
like
to
really
get
into
some
of
this
stuff
and
I.
Think
I
can
do
that
better
from
the
floor
rather
than
from
the
chair,
so
come
while
Singapore
or
later
I
really
would
like
Thunder
stuff
I
propose
that
actually
we
go
to
a
call
for
adoption
on
the
list
on
TLD
M,
sorry.
This
is
not
of
this
particular
draft.
C
C
One
of
my
concerns
from
the
chair
with
the
earlier
documents
we
had
around
naming
and
in
part
why
the
front
end
name
delegation
of
stuff
and
that
has
been
passed
so
long-
is
that
even
as
a
naming
guy
myself
I
hacked
I
couldn't
follow
the
end-to-end
resolution
process
both
for
internal
names
and
for
external
lanes
with
the
documentation.
We
had
I
think
it's
important
that
it's
clear
to
people
how
hosts
do
get
all
the
names
and
from
that
when,
if
you're
the
host
okay,
okay,
are
they
any
other
questions
on
lunch?
C
D
So
long
and
thanks
for
all
the
fish
and
yeah
it's
been,
it's
been
a
wild
ride.
Some
incredibly
good
work
has
been
done
and
I
appreciate
every
single
time.
Somebody
gets
out
there
and
tries
to
make
a
home
network
and
make
it
better
and
contribute
more
code,
because
that's
what
we're
all
here
for
I
can't
wait
to
go,
buy
one
of
these
and
install
it
in
my
home,
and
it
just
work
make
it
happen.
Guys
thanks.
I
got.
