►
From YouTube: IETF99-NETSLICING-20170717-1330
Description
NETSLICING meeting session at IETF99
2017/07/17 1330
https://datatracker.ietf.org/meeting/99/proceedings/
A
Okay,
it's
1:30,
so
please
everyone
take
a
seat,
we're
gonna
be
starting,
so
welcome
to
net
slicing
both
as
I
said
before
we
have
a
very
full
agenda,
so
we
will
try
to
go
through
the
church
lights
rather
quickly,
and
then
we
will
be
getting
given
ten
minutes
loss
to
the
presenters
and,
as
we
have
said
before,
we
will
be
quite
straight.
We
have
a
one
minute
warning
sign
here
for
presenters
and
we
will
cut
it
ten
minutes
after
you
start
so
note.
Well,
as
you
know,
this
meeting
is
governed
by
the
relevant
documents.
A
If
you
haven't
read
them,
please
go
ahead
and
read
them
and
that's
important.
So
this
is
a
known
working
group
forming
both
when
it
was
approve.
It
was
approve
like
that,
and
we
want
to
thank
our
mini
takers,
so
sue
Kieran
and
eNOS.
Thank
you
very
much.
Do
we
have
a
jabber
scribe?
The
idea
would
be
to
take
questions
from
the
jabber
room
and
relay
them
to
the
mic.
I
could
do
it.
Ted
can
do
it.
Thank
you
very
much
Ted
and
then
the
blue
sheets.
A
A
You
have
their
the
agenda.
We
will
be
showing
it
later,
but
you
can
take
it
there.
We
uploaded
all
the
materials
to
the
IPF
meeting
material
site.
You
can
download
the
presentations
there
if
you
want
to
watch
them
in
your
laptop
and
we
will
have
an
ether
pad
for
note
takers,
so
you
can
go
there
and
check
the
notes
being
taken.
The
jabber
room
is
net
slicing.
Please
note
that
is
not
net
slices.
A
A
Having
said
that,
this
is
the
agenda.
We
will
first
basically
explain
what's
the
purpose
of
the
boss,
so
we
all
understand
that
are
on
the
same
page
on
expected
outcomes,
and
we
will
explain
also
how
the
ietf
approaches
this
type
of
work.
So
we
all
understand
where,
where
we're
coming
from
then
as
I
mentioned
before,
we
will
have
a
set
of
speakers,
and
we
have
asked
them
to
address
four
main
questions.
A
We
will
be
talking
about
them
and,
as
I
said,
we
will
be,
or
we
will
try
and
be
quite
strict
with
time
and
we
have
assigned
10-minute
slots
and
we
will
try
to
enforce
that
and
then,
at
the
end
of
the
day,
at
the
end
of
the
book,
we
will
be
answering
the
typical
questions
that
you
know
any
buff
needs
to
to
answer.
We
have
a
slides
about
that.
A
The
purpose
of
this
book,
as
we
said
before
this
is
a
non
working
group
form
involved.
So
the
purpose
of
this
book
is
not
to
form
a
working
group
is
to
have
discussions,
gather
information
and
educate
the
whole
community
into
the
net
slicing
area.
In
particular,
we
ask
all
presenters
basically
to
address
the
following
four
questions
when
they
are
presenting.
What
do
you
mean
by
network
slicing?
We
have
heard
a
lot
of
definitions
and
people
don't
seem
to
be
on
the
same
page
when
they
basically
say
network
slicing.
A
We
want
to
basically,
you
know,
dig
into
that
a
bit
more.
What
are
the
main
use
cases
they
have
for
net
slicing,
whatever
their
definition
is,
what
idea
of
work
or
idea
well,
what
I've
idea
of
work
is
is
needed
either
new
or
idea
of
working
progress,
and
then
what
non
idea
of
work
is
relevant
and
our
our
idea
actually
asked
us
to
state
that
the
fact
that
these
working
group
this
book
actually
is
in
the
ops
area
doesn't
mean
anything.
Special
is
just
that.
A
B
Lots
of
you
most
of
you,
are
RIT
of
old
handers,
and
so
this
is
apple
pie,
but
some
of
you
have
been
attracted
in
by
the
prospect
of
this
new
work.
So
it's
it's
worth
looking
briefly
at
how
the
ITF
might
approach
this
work,
so,
firstly,
the
ITF
works
on
the
internet
and
it's
protocols.
If,
if
you
have
worked
at
something
else,
then
it's
not
ITF
work,
we
work
best
with
focused
working
groups,
clearly
defined
problems
in
their
charters,
achievable
deliverables
and
not
working
groups.
B
That
span
span
multiple
areas
with
wide
scope
that
that
has
basically
not
worked
in
the
past.
Also
note
that
the
ITF
is
not
a
research
organization,
so
we
are
looking
for
tractable
problems
for
I,
imminent
implementation
and
deployment.
The
whole
running
code
thing
is
is
key,
so
there
is
the
IRT
F
for
bigger
research
problems,
and
there
are
plenty
of
other
places
to
research.
B
B
Api
is
between
software
components.
All
inside
one
implementation
are
basically
out
of
scope
and
we
don't
have
a
good
history
with
api's
that
are
external,
although
it's
worth
noting
that
yang
models
fill
that
position,
so
we
we
do
have
experience.
We
have
external
API
is,
but
we've
also
had
some
history
with
with
external
API.
Is
that
have
fallen
very
flat,
so
be
a
little
careful
with
with
that
sort
of
thing.
B
Right
how
to
behave
inside
this
both
obviously
be
civil,
listen
carefully.
What
the
chairs
have
discovered
in
preparing
this
both
is
that
many
of
you
use
the
same
terminology
for
things
that
are
slightly
different
and
it's
very
easy
to
talk
past
each
other
when
you
use
a
term
and
assume
that
the
other
person
means
the
same
thing.
So
it
should
be
very
careful
to
listen
and
understand
that
two
definitions
of
the
same
term
you're
both
right
you're
just
using
the
term
different
differently,
stick
to
your
time
limits.
B
But
don't
do
the
deep
dive
questions
until
the
end
and
and
those
questions
that
are
taken
as
we
go
along
form
part
of
that
10
minute
slot.
So
if
you
believe
you
want
to
take
questions
in
your
presentation,
then
maybe
9
minutes
is
better
than
10
minutes
funny
when
I
page
down
on
my
screen.
It
doesn't
change
on
that
one.
B
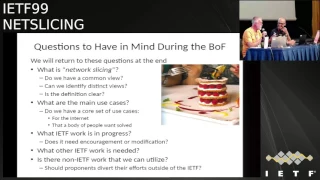
So
we'll
return
to
these
two
slides
of
questions
at
the
end
of
the
buff,
but
it's
worth
just
flashing
them
up
here,
things
to
have
in
mind
as
the
buffer
goes
forward,
so
those
were
the
bodies
Network
slicing.
What
do
you
mean?
Do
we
have
a
common
view?
Are
there
separate,
distinct
views
using
the
same
term,
but
they
are
very
easy
to
to
represent
as
different
views
and
all
those
definitions
clear?
B
What
are
the
use
cases,
so
we
should
not
be
chasing
absolutely
every
possible
use
case.
We
should
be
looking
for
killer
use
cases
and
use
cases
that
there's
a
good
body
of
opinion
behind
they
have
to
apply
to
the
Internet.
Otherwise,
why
be
here
and
people
must
want
them
solved,
not
just
agree
that
they're
interesting
then
we're
looking
for
what
I
ATF
work
is
in
progress.
Does
that
work
need
encouragement
and
tweaking
or
is
it
just
going
fine?
B
And
then
the
other
set
of
questions
are
more
formal
and
both
enthusiasts
will
have
read:
RFC
54:34,
that's
largely
targeted
at
working
group
forming
buffs,
but
we
can
reinterpret
those
questions
for
this
stuff
and
come
to.
Is
there
a
problem
that
needs
to
be
solved
and
is
the
ietf
the
right
place
to
solve
it?
Is
there
a
critical
mass
of
participants
willing
to
work
on
the
problem
and
work
on
the
problem?
Doesn't
just
mean
willing
to
put
your
hand
up
or
hum
in
a
buff.
It
means
willing
to
write
draft
review
drafts
actively
participate.
B
Is
the
scope
of
the
problem
well
defined
and
understood?
So,
do
people
really
understand
what
could
be
worked
on
and
what
might
be
out
of
scope?
And
if
we
were
to
list
deliverables,
could
we
could
we
be
clear
what
they
are
and
then,
lastly,
would
there
be
a
reasonable
chance
of
success
if
we
tackled
these
deliverables
and
then
doesn't
ad
want
to
say
anything,
the
ad
says:
we've
covered
everything,
so
we
will
move
on
to
our
first
presentation.
Perfect.
C
From
the
foot,
thank
you
very
much.
My
name
is
ski
of
Maya
I'm,
with
3gpp
and
I'm.
The
sweet
EVP
city
chairman
and
I
will
present,
but
after
the
last
net
slices
meeting,
we
had
a
lot
of
discussions.
Many
things
were
ongoing
during
the
last
three
four
months
and
one
of
the
major
questions
was
what
input
does
3gpp
like
in
its
official
documentation
that
it
has
at
the
moment
from
5g
perspective?
C
C
This
is
driven
by
many
people,
I
guess
and
tomorrow
there
will
be
at
lunchtime
a
presentation
where
we
go
deeper
into
these
issues.
So
this
slides
here
we
focus
on
network
slicing
and
tomorrow
then
I
will
keep
most
of
the
network
slicing
out
of
the
presentation
as
I
assume
people
interested
people
are
here,
I
have
too
many
slides.
You
will
stop
me
and
I
have
two
important
slides.
First,
can.
C
3Gpp
liaison
for
the
idea,
I
am
from
the
3gpp
side.
The
liaison
towards
idea.
Gonzalo
is
from
the
ITF
site,
the
liaison
to
3gpp
good
clarification.
You
thank
you
you're
welcome,
so
we're
talking,
maybe
talking
network
slicing
we
practically
talking
five
g
5g
is
a
project
that
we're
currently
pushing
forward
in
3gpp,
and
this
is
a
very
simplified
form
of
our
timeline
that
we
have
release.
14
has
just
been
finished.
Release
15
is
overlapping
with
it
it's
ongoing.
We
have
a
deadline
for
release
15
for
June
18
2018.
C
Then
we
will
grant
ourselves,
as
we
usually
do
three
more
months
to
complete
the
more
orders.
They're
still
open
issues,
so
we're
practically
speaking
about
September
2018,
where
we
will
have
to
have
a
first
workable
release
for
5g,
something
that
can
be
put
into
products
that
could
be
put
out
there
and
would
work
at
least
that's
the
plan,
the
deadlines
that
we
have
for
release
15
and
release
16.
They
are
rather
sharp
there.
We
always
have
sharp
deadlines,
but
usually
we
can
allow
ourselves
to
linger
a
bit
longer
for
these
two
releases.
C
That's
not
so
easy.
We
have
other
influences
from
the
outside
world,
where
we
really
have
to
make
sure
we
meet
these
deadlines.
So
I
guess
one
of
my
major
messages
that
I
want
to
convey
to
you
today
and
tomorrow
is
if
ITF
starts
work
on
anything
that
is
intended
for
these
releases,
then
ITF
should
make
sure
that
you
meet
these
deadlines
right.
So,
if
you're
saying
you're
working
on
something
that
is
related
to
five
cheese
slicing-
and
you
mean
something
that's
meant
for
release
15,
then
you
need
to
meet
meet
this
deadline
else.
C
We
have
lingering
drafts.
We
have
lingering
drafts
in
other
working
areas
like,
for
example,
with
IMS
and
zip
there
it
works
sort
of,
but
for
this
project
5g,
the
deadlines
are
really
sacred
and
we
shouldn't
touch
them.
So
please
keep
that
in
mind.
Where
do
we
go
under
work
in
related
to
slicing
in
3gpp?
What
you
see
here
is
the
3gpp
structure,
so
we
have
done
the
high-level
requirements
already
in
essay
1.
C
So
this
is
for
the
whole
5g
project
right,
but
also
for
and
what
you
see
here
with
the
bubbles
is
the
slicing
related
ones.
The
work
is
currently
under
quite
good
progress
in
the
architecture
group.
There's
a
document,
23
501.
You
will
hear
this
again
and
again.
You
can
read
this
there's
a
lot
about
slicing
India
there.
The
work
is
in
progress
in
progress
means
these
requirements
can
change
and
they
will
change
for
sure
to
a
certain
extent.
C
So
the
question
I
think
that
was
asked
to
me
and
several
people
are
asking-
is
that
sweet
EPP
currently
have
dedicated
requirements
for
any
kind
of
IOT
of
protocol
or
activity
related
to
network
slicing
and
you're,
asking
at
the
moment
currently
right.
So
it's
something
that
we
have
in
our
spec,
something
where
I
can
without
any
doubt,
tell
you.
This
is
there
and
for
that
the
answer
at
the
moment
is
no.
There
is
nobody
in
suite
EBP
that
could
guarantee
you
that
any
specific
ITF
solution
would
be
needed
or
would
be
taken
for
network
slicing.
C
Why
is
that
that
way?
We
are
just
starting.
Are
we
in
the
middle
of
the
architecture,
work
architecture,
work
normally
doesn't
look
too
much
or
too
closely
into
the
protocols
and
everything
on
protocol
Security
orchestration
related
that
either
studies
ongoing
or
is
just
about
to
start
so
I
don't
want
to
speculate.
I
hope
you
don't
speculate
on
what
3gpp
is
needing
what's
foreseeable?
Well,
there
are
several
scenarios:
foreseeable
I
mean
Yui,
2,
core
core
internal
run,
and
so
on.
Many
groups,
as
you
saw,
will
work
on
slicing
in
3gpp.
C
But,
of
course
we
don't
know
the
outcome
yet
so
seeing
this
I
just
want
to
say,
please
don't
shoot
the
messenger
I'm
not
saying
you
shouldn't
work
on
network
slicing
I'm,
just
telling
you
at
the
moment,
I
can't
give
you
any
concrete
requirements,
at
least
not
core
requirements
on
the
level
that
you
would
need
to
start
off
your
work,
but
usually
how
the
work
is
done
is
that
ITF
goes
ahead
with
protocol
work
and
then,
when
3gpp
finds
their
requirements,
they're
looking
around
and
see.
Are
there
protocols
that
fulfill
our
requirements?
C
So
in
essay
2,
the
architecture
group,
we
define
the
network
slice
as
a
logical,
end-to-end
network
and
it's
dynamically
created
and
when
we
mean
end-to-end,
then
we
really
mean
like
it's
the
core
network,
but
it's
also
the
radio
access
network
that
can
be
sliced
and
there
can
be
given
either
to
a
dedicated
customer
or
for
very
specific
service.
As
an
end-to-end
network.
It's
a
standalone
network
like
from
from
a
different
operator.
C
It
includes
the
the
cod
control,
as
well
as
the
user,
plain
radio
access
network
anyhow
and
also
non
3gpp
access
networks
such
as
fixed
networks,
yeah
and
then
si5.
The
orchestration
work
is
done
in
essay
5
or
will
be
done
in
essay
5.
They
are
just
started
their
work.
If
you
want
to
follow
their
work,
there
is
currently
they
finish.
The
work
on
the
study
work
on
a
TR,
a
TR
is
always
for
us,
a
technically
recommendation.
It's
a
study,
it's
nothing
normative,
but
it's
good
to
look
at
it.
It's
28,
801
and
they're.
C
Now
starting
the
normative
work
in
several
specifications.
So
this
is
not
the
only
one,
but
twenty
one.
Twenty
eight
five
three
one
might
be
one
that
you
would
be
interested
in,
so
you
find
those
on
our
webpage
and
I
would
encourage
you
to
follow
our
work
also
on
these
specifications
in
the
specifications.
You
find
what
we
really
agree
on
in
3gpp,
so
as
a
five
again,
because
this
was
sort
of
an
input
that
I
got
I
have
one
minute.
Okay,
then
I
just
jump
over
these
slides.
C
You
have
you
have
more
slides
in
here
where
I
try
to
summarize
the
different
cases
that
we
for
the
moment
foresee
and
I
hope.
This
is
sort
of
a
background
information
where
you
get
an
overview.
If
you
want
to
follow
our
work
once
more,
you
have
to
look
into
the
related
specifications
and
need
to
find
out
what
what
the
requirements
are.
Of
course,
we
can
also
work
more
closely
together
on
a
expert
to
expert
basis.
Thank
you
very
much.
Thank.
A
F
You
very
much
for
coming
to
this.
Both
I
have
half
or
some
part
of
the
presentation,
from
the
both
proponents
point
of
view,
which
was
very
hard
in
the
last
three
months
to
build
up
five
separate,
but
interrelated
drafts
and
I
will
attempt
to
answer
some
of
the
questions,
not
all
of
them
as
addressed
by
the
chairs.
However,
after
me,
there
will
be
two
other
presentation
covering
the
other
parts
of
the
both
proponents.
There
are
plenty
of
slides,
however.
F
I
would
like
to
use
only
three
to
convey
the
messages
after
that,
I
will
accept
questions
with
a
viewer
clarification,
but
also
substance.
Now,
slicing
is
happening
now
in
a
big
scale.
All
the
operators,
to
my
knowledge,
all
the
manufactures
and
all
the
key
research,
industrial
or
academic
research
establishment,
are
working
on
it
in
prototype
software
development,
as
well
as
open
source
and
designs.
F
So
it's
a
time
to
understand
that
this
is
coming,
and
the
main
emphasis
now
should
be,
in
my
view,
to
bring
together
all
these
energies
in
order
to
ensure
that
there
is
no
chaos
at
least
slices
will
be
compatible,
interoperable
and
usable.
That's
a
main
message.
That's
reason
why
I
am
presenting
a
few
elements,
rated
slicing
and
other
end.
The
these
proponents
group
decided
that
the
one
definition
which
could
be
useful
to
be
realized
is
a
container
of
network
resources
of
network
functions.
F
Some
of
them
are
virtualization
next
period
in
large
numbers
service,
but
also
management
and
probably
exposure
functions
which
will
make
this
container
very
much
usable
in
a
context
of
delivering
all
the
results
is
a
necessary
function
for
one
at
least
supporting
one
service.
Well,
the
issue
is
not
to
go
for
creating
an
overlay
which
supports
all
the
services.
F
Similarly,
and
in
that
sense,
this
concept
is
has
a
long
history,
but
currently
it's
hot
topics
in
industry
as
I
understand
all
the
standard
groups,
including
sue
GBP,
are
working
on
it
or
starting
to
work
on
it.
There
is
a
major
gap
in
the
wireline
area
with
a
view
of
different
aspects,
but
all
emphasize
what
is
important
and
anyway,
these
are
references
which
I
believe
that
will
help
the
the
activity.
G
F
F
This
is
where
we
believe
that
will
add
more
value
and
obviously
has
to
be
done
to
include
orchestration
and
many
other
functions,
but
it
has
to
be
dynamically
created
in
such
a
way
that
will
not
interfere
to
each
other,
obviously
has
to
have
an
operator
and
tenants
may
be
multi
tenants
very
slight,
but,
very
importantly,
this
concurrent
deployment
of
this
isolated
network
have
to
have
capability
to
support.
Well
at
least
one
service.
F
There
is
no
point
to
do
it,
otherwise
there
will
be
services
from
non
IP
type
of
service
deployment
to
many
other
types
of
services
deployed
on
a
same
share
infrastructure,
the
infrastructure
might
change,
and
we
need
to
support
all
the
needed
isolation
infrastructure.
So
for
clearly
in
our
mind,
there
are
a
number
of
problems
which,
as
high
priority,
should
be
able
to
be
sought
out
into
an
emerging
working
area
in
ITF,
and
we
selected
10
out
of
20,
which
we
identified
as
the
one
which
should
make
a
lot
of
sense.
F
Obviously,
we
have
a
little
architecture
which
basically
says
that
at
the
bottom,
you
have
the
infrastructure
and
that
changing
and
should
not
be
precluding
the
work,
which
is
a
main
working
in
network
sizing,
which
is
in
the
middle,
which
is
basically
management,
dynamic
manager,
embedded
management
operations
and
functions
or
subsidy,
and
also
the
interface
and
Inter
working
with
services
and
the
tenant
and
the
orchestrate
the
problems
which
you
select
it.
We
have
done
in
such
a
way
to
ensure
that
we'll
have
interoperability
at
the
highest
level
between
slices
in
the
future.
F
Even
they
are
defined
differently
by
different
manufacturers
or
different
operation
in
the
operators
network,
which
will
happen
anyway.
For
as
such,
the
middle
part
of
the
scenes
which
want
to
solve
other
management
functions
related
to
lifecycle,
management,
monitoring
and
discovery.
This
large
number
of
service
networks
with
autonomic
capability
and
critically
with
end-to-end
orchestration
by
the
way
orchestration
includes
coordination
of
around
a
hundred
separate
other
functions
which
need
to
be
put
here
to
in
order
to
ensure
that
this,
these
things
are
done
and
all
of
them
could
be
developed
through
new
protocols.
F
However,
the
rather
key
importance
in
related
to
the
how
this
will
face
the
services,
therefore,
a
slice,
the
we're
young
model
to
allow
that
to
happen,
as
well
as
operational
slices
to
happen.
It
will
be
including
composition
as
I
see,
is
absolutely
essential
and
a
key
to
it
is
to
ensure
isolation
at
the
bottom,
but
also
at
the
top
of
this
stack
and
that's
coming
to
one
point.
Also,
there
are
many
definitions,
I'm
always
similar.
F
What
is
needed
to
be
standardized
module,
a
uniform
slice
template
which
includes
component,
which
should
be
then
used
similarly,
rather
than
semantically
disjunctive,
and
in
such
a
way
the
slice
is
producing.
Let's
say
in
C
GBP
in
a
radio
part
sooner
or
later
could
be
compose
with
slices
in
this
area.
Otherwise,
there'll
be
a
problem,
but
the
other
elements
which
are
important
which
are
listed
on
the
bottom.
So
this
is
my
three
important
slides
I
have
many
details
that
could
stop
now,
if
you
have
verification
questions,
if
not
I'll
continue,
I
think.
F
F
One
group
of
problems
related
to
the
fact
that
management
becomes
their
essential
means
by
which
this
will
be
achieved.
That
includes
lifecycle
management
of
slicing
in
terms
of
creation,
also
when
they
are
deployed
as
instances
when
when
they
have
to
be
switched
off
and
they
have
to
release
the
results,
is
the
network
functions
and
others
to
for
other
use
dynamically?
In
such
sense,
this
problem
becomes
an
essential
tools
to
do
it
and
protocols
to
achieve
it
are
needed
to
ensure
cohesion
be
severe,
how
slices
are
creating
worldwide.
F
Very
importantly,
as
I
mentioned
before,
in
addition
to
lifecycle
management,
the
subject
of
control
at
different
level,
as
maybe
a
hundred
level
of
granularity
of
control
function,
which
need
to
be
covered
and
I
exemplified
in
in
in
the
diagram
on
one
side,
and
the
first
diagram
shows
how
this
could
be
created,
which
is
now
very
important.
This
has
to
be
done
with
monitoring
and
discovery
functions
in
in
mind
autonomically.
F
F
I
will
just
end
to
say
that
the
key
across
all
these
problems
will
be
a
uniform
model
of
dealing
with
slicing,
in
particular,
the
slice,
template
and
the
management
capability
and
exposure
which
will
make
this
concept
not
only
a
reality
but
protocols
to
be
used.
Thank
you
very
much.
These
are
the
25
minute.
Well,
do
I
have
to
thank,
because
they
work
very
hard
in
the
last
23
months,
not
only
to
produce
the
slides,
but
also
in
a
weekly
discussion
to
tease
out
that
what
is
important
and
what
is
not
important.
Thank
you
very
much.
F
F
H
This
presentation
is
going
to
talk
about
the
main
use
cases.
The
energy
analysis
for
natural
sizing
here
is
a
la
identified.
The
network
is
rice
use
cases
if
we
regard
the
network
size
the
service,
the
network's
testing
can
provide
the
natural
customization
for
some
use
case,
such
as
the
ritual
customer
premise,
equipment
from
3gpp
perspective.
The
network
starting
working
ITF
can
provide
the
result
assurance
for
some
use
case,
such
as
the
EMV
BER,
camtc
and
AMC
apps,
and
the
network
pricing
also
can
support
the
implementation
of
new
technologies
such
as
the
ICN.
H
This
is
the
use
case
of
vcp
autonomic
om
of
Astra's
can
make
existing
customization
better
I
saluted
the
traffic
engineering
and
flexible
for
mission-critical
service.
The
network's
pricing
had
provided
dedicated
physical
Maidan
lingaiah,
provided
a
flexible
control
of
status,
tribal
management.
That
means
the
network
slice
can
enhance
the
reliability,
security
and
the
flexibility
and
for
the
implemented.
The
new
technology,
such
as
the
ICN
ICN,
is
the
long
IP
param
based
technologies,
the
network's
pricing.
He
enabled
the
icy
and
work
together
with
the
traditionally
based
the
service
and
provide
the
proper
result.
H
I
solution
between
them
and
that's
considering
the
whole
procedure
of
the
Natural
History's
at
first
assist
the
system
need
to
expose
the
natural
resource
and
based
on
the
exposed
to
network
resources.
The
Italians
who
can
describe
the
what
kind
of
network
is
rising
requirements
you
want.
This
requirement
is
always
the
end
to
end,
so
it
will
be
negotiated
a
month,
a
foreigner
demands
and
then
to
construct.
H
They
are
isolated
and
the
Kopelman's
quarantine,
Network
recites
the
instance
and
each
instance
instance
also
need
to
provide
a
certain
of
OAM
for
state
monetary
or
restore
treachery
tracker
that
mang
from
the
whole
procedure.
We
can
elicit
four
key
requirement.
They
are
thrice
realizing
resource
requirement,
description,
trust
on,
and
coordination,
performance,
grantee
and
I
solution,
as
well
as
the
natural
catalyzing
om
for
the
foster
requirement.
As
the
natural
beast
rising
domain
controller,
it
should
be
able
to
describe
the
net
was
naturally
resources.
It
has
learning.
H
Why
captured
the
requirements
from
the
talent
include
the
performance
metrics,
the
protection
requirement,
I
solution,
Custer
in
the
path
restriction
and
so
on
related
world,
such
as
the
young
death
model,
the
CPP
templates,
the
tiers
based
and
tears
could
be
used
here
for
some
of
them
later.
The
response,
obstruction
and
management
are
less
repress
and
some
of
them
need
the
extension
of
specification
of
advanced
state
service
function
to
be
invoked
and
their
invocation
orders
for
the
stating
the
requirement.
H
The
cross
nominal
coordination
differ
in
the
common
controller,
always
need
to
coordinate
with
each
others
for
the
resource
of
configuration
ourselves
under
informations.
Some
related
work
provide
a
hierarchical
common
platform
solution
for
this
kind
of
cross
domain
coordination,
but
consider
a
more
general
scenario
that
made
different
it'll
not
belong
to
different
owners
or
administrators.
So
we
sink
flood
of
flats
of
peering.
H
Trust
of
non
coordination
solution
is
needed
in
this
situation
and
besides
this,
the
extension
or
network
slicing
space
to
the
behaviour
and
the
object
are
needed
for
the
third
requirement
of
the
performance
guarantee
and
I
solutions.
Different
networks,
slice
should
be
isolated
for
the
performance,
security
or
manager
meant
reasons.
There
are
a
lot
of
relative
work
here,
such
as
the
VP.
The
segment
shooting
is
not.
We
sing
the
title
coupling
between
the
underlay
and
overlay
and
the
enhancement
two
different
and
contributed
not
needed.
The
last
requirement
the
natural
slicing.
H
Okay,
I
am
actually
the
OEM
ATF
has
nothing
new
identifying
so
far,
but
the
problem
is
the
network.
Slicing
has
totally
changes
the
regularity
of
oh
yeah.
We
need
to
provide
the
postal
I
am
for
different
talent.
Meanwhile,
since
each
slice
with
may
cross,
multiple
demands-
and
this
demand
may
be
wrong
to
different
providers,
not
means
we
also
need
to
consider
the
poor
tomorrow
a.m.
and
another
possible
use
a
jury.
There
is
a
lot
of
surveys
implemented
on
:
slice,
so
we
still
need
to
consider.
H
The
personalized
Oh
am
I
already
said,
there's
nothing
new
here
for
oh
yeah,
and
that
means
the
technology
space,
because
I
am
tours
the
overlay
om
and
some
other
solution
could
be
reused
to
here.
But
we
need
to
carefully
considering
the
customer
customized
granularity
of
network
slicing
I
am
here
is
our
conclusion.
We
list
the
four
key
requirements
in
the
horizontal
in
the
vertical
direction,
for
the
first
requirement
is
the
slicing
result
and
a
requirement
description.
H
We
thank
a
detail
at
first,
a
digital
network
slicing
specification
such
as
the
performance
metrics
protection,
how
availability
guidelines
are
needed
and
then
accompanying
a
model
need
to
be
defined
for
cross
domain
coordination.
A
lot
of
protocols
such
as
the
BGP
grasp
could
be
used
here,
but
we
need
complemented
models
for
flat
crossed
online
coordination
for
the
performance
guarantee
under
I
solutions.
The
ex
nation
work
best
on
the
defi
technologies
such
as
the
Libyan
MPs
and,
secondly,
routing
an
ad
for
the
last
requirement.
H
The
network
slicing
om
in
order
to
perform
the
personalized
for
domain
and
first
list
om,
we
need
to
add
some
additional
information
to
traditional
om
packages.
That
means
we
need
to
consider
how
to
define
how
to
generate
a
recycle
manager
there's
additional
informations.
Meanwhile,
we
need
to
consider
how
to
perform
the
OEM,
our
material
resources,
how
to
autonomically
discovery,
the
service
functioning,
instant
and
the
capability
and
the
network's
rising
instance
basada
ISM.
We
need
to
design
a
new
working
flow
for
the
network's,
rising
OEM
and
the
redefine
the
repository
two-story.
H
H
B
A
J
Get
often
my
name
is
Daniel
King,
so
I'll
be
presenting
the
applicability
of
abstraction
and
control
the
traffic
engineer.
Networks
to
network
slicing
I
will
certainly
attempt
to
keep
within
my
assigned
ten
minutes.
So
we
are
talking
about
a
collective
of
engineers
have
been
working
on
abstraction
and
control
of
traffic.
Engineer
networks
now,
essentially
a
framework,
that's
derived
from
a
set
of
requirements
and
a
problem
statement
for
solving
traffic
engineered
problems.
These
are
providing
network
virtualization
and
network
virtualization
in
some
cases
could
be
synonymous
with
network
slicing.
J
So
when
we
started
seeing
sort
of
network
slicing
being
discussed
and
Alex
mentioned
that
the
the
cohort
of
of
engineers
and
academics
have
been
working
on
network
slicing
now
for
at
least
22
months,
we
thought
it
might
be
good
to
write
an
applicability
document
that
kind
of
shows
or
demonstrates
how
a
CTN
might
be
used
in
order
to
solve
some
of
the
network
slicing
with
requirements.
So
what
do
we
mean
by
network
slicing?
And
these
are
the
sort
of
the
actn
protagonists?
J
Network
slicing
is
a
transport
network
slice
construct
which
provides
an
end-to-end
logical
network,
often
with
compute
functions
and
utilizing
shared
underlying
physical
or
watch
or
virtual
network
resources.
This
logical
network
is
separated
from
other
often
concurrent
logical
networks,
each
with
independent
control
and
management,
and
each
of
which
can
be
created
or
modified
on
demand.
So
essentially,
these
are
our
traffic
engineered
connectivity
with
function
that
may
be
compute
or
storage
of
contents
or
network
specific
function.
J
That
is
bound
to
a
set
of
reliability,
performance,
latency
and
service
capabilities,
and
we
may
also
add
a
chain
as
sort
of
determinism
as
some
kind
of
traffic's
during
our
traffic
flow
in
order
to
visit
particular
functions
in
a
very
specific
order.
How
did
we
derive
and
the
overall
requirements
for
network
virtualization
or
network
slicing?
Well,
we
have
a
set
of
requirements
documented
in
specifically
in
a
requirements
document,
but
also
a
problem
statement.
These
are
associated
across
a
number
of
dimensions.
J
So
in
the
AC
TN
framework,
you
would
find
at
this
particular
example.
On
the
right
hand,
side
essentially,
we've
got
our
customer
network
controller,
which
is
the
consumer
of
the
network
slice.
The
network
slice
is
provided
by
the
multi
domain
service
controller,
which
is
our
super
controller.
Our
Orchestrator
and
the
type
of
network
slice
is
dependent
on
the
type
of
service,
the
type
of
application
that's
actually
running
on
top
so
sort
of
the
client
layer.
So
it
could
be
a
fixed
slice
which
is
not
malleable.
J
You
know
there's
no
way
to
add
or
remove
endpoints
or
modify
or
request
additional
bandwidths
or
we
could
go
at
the
other
end
of
the
spectrum
provide
some
higher
layer,
slice
which
is
adjustable,
which
can
also
be
sort
of
controlled
by
some
recursive
functions.
You
could
run
a
controller
on
top
that
can
actually
change,
addressing
and
even
change,
topology
and
change.
J
The
way
that
the
flows
are
being
managed
on
the
slice
that
sits
on
top
of
some
sort
of
server
layer
or
underlay
resource
at
the
bottom
of
this
stack,
we've
got
the
physical
network
controller,
and
that
could
be
for
an
optical
network
technology.
It
could
be
for
some
packings
engineer
technology
but
in
both
cases
the
commonality.
Here
is
it's
traffic
engineer.
J
But
of
course,
a
CTN
was
not
only
developed
for
mobile
environments,
there's
also
a
number
of
other
use
cases.
These
are
addressed
or
all
these
the
problems.
The
scope
of
work
are
addressed
in
the
other
documents
listed
on
the
slide
here,
but
things
like
sort
of
inter
domain
connectivity
across
multi
sort
of
provider,
networks
into
a
data
center
connectivity
and
multi
layers,
client
over
server
layer,
orchestration
of
resources.
J
So
what
current
work
exists
for
HTN
and
this
listed
actually
is
almost
sort
of
harm,
filtered
or
a
shounen
list
of
stability,
so
we've
got
requirements
for
abstraction
control
of
T
networks.
Clearly
we
needed
this
document
relatively
stable
before
we
started
developing
the
framework
documents,
so
the
requirements
and
the
framework
documents
are
essentially
documents
that
will
that
will
move
into
last
call
to
or
are
already
in
lascall
have
been
sort
of
progressed
through
the
IES
G
and
towards
RFC
editors
q.
So
these
are
our
most
stable
documents.
J
Then
we've
got
a
number
of
other
pieces
of
work.
These
are
sort
of
ancillary,
as
we've
got
the
abstraction
methods.
Internet
draft
we've
got
our
information
model,
there's
a
yang
model
for
the
virtual
network
that
slice
itself
and
we've
also
started
thinking
about
the
OEM.
You
know
essentially
sort
of
telemetry
network
to
limit.
So
how
do
we
provide
a
feedback
loop
from
the
underlying
network
resource
in
order
to
have
some
kind
of
application
awareness?
It
may
be
SLA
specific.
J
We
might
have
to
modify
some
server
layer
resource
as
the
network
changes,
and
how
do
we
actually
record
and
use
that
information?
And
there
are
also
other
documents
as
well,
which
aren't
on
this
list
that
talk
about
what
type
of
existing
yang
model
could
be
used
combined
in
order
to
have
a
model
driven
approach
when
we
need
to
setup
or
teardown
or
modify
resources
from
that
underlay
slash
server
layer,
there's
a
question
at
the
mic:
no.
K
K
Earlier
you
mentioned
how
multi-domain
had
a
couple
of
different
meanings
and
one
of
them
seemed
to
be
across
administrative
boundaries
from
your
later
slide,
I
assume
what
you
meant
was
cases
like
your
multi
tenant
MVNO,
where
there
are
administrative
boundaries,
but
a
single
network,
but
I
wanted
to
ask
you
two
clarifying
question
of
whether
any
of
these
t
networks
that
you're
describing
with
a
CTN
are
multi
ASN,
I.
Think.
J
In
theory,
the
architecture
or
the
framework
supports
a
multi
provider
environment.
Whether
or
not
that's
something
that's
actually
going
to
be
deployed
in
the
near
term.
I
think
it's,
it's
still
an
open
question.
The
in
this
case,
what
you
could
have
is
each
PNC
could
be
operated
by
a
different
provider,
a
different
operator.
They
would
provide
a
slice
of
the
resource
to
the
mdac
that
could
be
a
broker
and
then
other
sort
of
application.
K
J
As
well,
yeah
cool,
okay,
I
think
I
think
I'm
almost
there
actually.
So
what
are
the
other
pieces
of
work
that
the
the
a
ctn's
Roo
team
are
working
on
and
the
various
participants
and
I
should
highlight
that
that
the
actn
effort
is
happening
in
the
t's
working
group
with
specific
ansari
work
occurring
in
the
relevant
or
subsequent
working
groups,
so
yang
models
very
important,
secure,
slicing
and
isolation
of
resources?
How
do
you
ensure
that
your
network
traffic
is
secure?
J
It
sort
of
partitioning
is
kind
of
an
open
issue
and
there
are
a
variety
of
technologies
that
we
could
use
in
order
to
do
that,
policies
who
is
allowed
to
request
the
slice,
but
that's
kind
of
been
out
of
scope-
that's
cnc
to
mdac,
but
that's
something
that
we
need
to
start
thinking
about
whether
or
not
we
need
some
imperative
language
to
decide
the
type
of
slice
or
when
to
kind
of
switch
in
the
event
of
some
kind
of
failure.
There's
a
working
group
in
the
ITF
called
super.
J
That
said,
there
could
be
some
policy
language
there
that
you
can
apply
and
then
the
final
point
that
I
should
quickly
make
is,
since
we've
seen
the
discussion
on
network
slices
and
this
sort
of
growing
interest
in
providing
and
managing
network
slices.
Clearly,
there's
a
need
for
requesting
compute
and
storage,
maybe
content
or
function
specific
when
you're,
making
the
topology
or
the
connectivity
requests.
J
A
All
right,
so
my
name
is
Jericho
I
was
asked
to
talk
about
how
slicing
and
IOT
relate
to
each
other
and
just
briefly
go
through
some
use
cases.
First.
So
talk
about
critical
services
that
the
police
or
a
power
station.
The
one
defining
feature
here
is
that
you'll
have
to
give
them
resources.
If
you
have
them,
those
services
are
so
important,
there's
also
a
bunch
of
services
or
use
cases
where
you
have
some
real
time
requirements,
latency
requirements,
for
instance
in
a
factory.
A
It's
like
a
in
a
local
area
and
then
here
in
the
middle
of
the
control
of
remote
equipment.
That
you'll
probably
have
some
latency
requirements,
but
they
are
across
one
in
environment
traffic
systems.
Probably
have
you
know,
components
of
these
previous
cases
to
some
extent
combined
and
then
one
final
example
here
is
the
mass
deployment
of
sensors,
which
both
implies.
You
know
scaling
to
very
large
numbers
of
devices,
millions
or
even
billions
and
then
possibly
also
being
able
to
again
prioritize.
A
But
maybe
this
time
say,
agricultural
sensors,
you,
you
might
not
need
to
have
them
like
on
this
millisecond,
it's
okay
to
get
them
in
a
few
minutes
time,
for
instance,
and
as
I
was
thinking
about
this.
What
can
we
do
from
a
network
access
network
perspective
to
help
some
of
these
distinct
use
cases
and
for
things
came
up
separation,
additional
control,
scaling
and
then
flexibility
I'll
talk
briefly
about
each
of
them.
A
The
separation
is,
first
of
all
could
be
like
traffic
isolation
between
different
domains
or
traffic
flows
or
users,
but
also
being
resource
guarantees
like
for
the
power
plant
or
whatever.
On
that
you
you
are
given
at
least
50%
of
our
resources.
Whatever
we
have
there's
some
control
issues
also
there's
some
desire
to
have
some
effect
on
how
things
are
done
in
the
network,
for
instance,
for
the
low
latency
cases.
One
example
that
I
think
is
is
the
fact
that
if
you
have
a
mobile
II,
the
endpoint,
you
have
mobility
service
provided
by
the
network.
A
A
I
have
one
example
here
up
is
kind
of
simple
to
understand,
but
down
that's
also
needed,
for
instance,
there's
lots
of
people
who
want
to
run
say
5g
or
other
types
of
networks
within
their
warehouses
or
factories,
and
then
it's
important
that
you
can
actually
bring
it
down
in
in
terms
of
practical
ability
and
then
a
commercial
ability
also
to
to
run
inside
a
factory
or
at
least
the
key
parts,
and
then,
finally,
flexibility.
You
need
to
be
able
to
tailor
services
to
a
situation
again
use
mobility
as
an
example.
A
Maybe
you
have
some
some
fixed
nodes
that
actually
don't
need
mobility,
so
maybe
you
can
just
dispense
that
for
for
the
purpose
of
those
particular
nodes
or
it
more
generally
allow
evolution
and
choice
the
u-turn
features
on
or
off
we
can
run
different
types
of
software.
You
can
run
different
type
of
networking
technology
to
some
extent
at
least
I
mean
fully
the
interface
through
the
devices
is
fixed.
What
you
actually
do
in
the
network
might
might
change
radically
as
people
innovate.
A
So
network
slicing
is
network
management
and
it's
not
not
like
us,
signaling
between
application
components,
but
it's
a
management
task
pertaining
to
the
treating
of
different
traffic
categories
in
separate
virtual
networks,
with
independent
resource
technology
and
topology
choices.
And
of
course
that
means
there's
some
dependencies
between
different
virtual
instances
and
reality.
Of
course,
like
you
can
provision
a
link
that
doesn't
exist.
A
At
least
I
mean
you
can
go
round
of
course,
but
you
can't
provide
direct
links,
for
instance,
when
they
don't
exist
or
low-latency
links
when
they
don't
exist,
but
that's
basically
a
very
simple,
simple
definition
of
this.
So
having
defined
like
the
requirement
or
having
looked
at
the
requirements
and
having
given
you
a
definition,
I
had
some
final
observations
to
make,
and
so
I
guess
the
the
question
in
people's
mind
is
what
is
needed.
I'll
just
point
out
that
not
everything
necessarily
needs
a
protocol.
A
I
mean
there's
different
things
here
in
this
space
and
much
is
doable
with
the
existing
tools
that
virtualization
management
tools,
Sdn
service
training,
a
CT
in
asthma.
So
the
question
is:
are
there
missing
ones
and
and
at
least
to
me
I'm
like
keeping
an
open
mind,
it's
not
immediately
obvious
to
me
that
yes,
I
absolutely
need
that
thing,
but
but
certainly
there
are
some
things
that
we
can
do,
and
this
always
need
to
do
more.
A
If
you
think
about
something
like
orchestration,
I'm
sure
we'll
be
working
on
that
20
years
from
now
and
still
improving
so
clearly,
there's
more
work
to
be
done,
but
there's
also
a
question
of
like
how
much
do
you
want
to
do.
We
heard
from
George
that
the
timelines
for
this
mighty
work,
for
instance,
are
quite
tight,
so
how
much
do
you
want
to
do
before
that,
and
you
know,
is
there
a
chance?
Perhaps
that
we
might
consider.
A
A
I
don't
have
time
to
go
through
much
of
that
right
now,
Jeff
Tantra
and
myself
wrote
this
draft
on
low
latency
services
for
applications
and
some
some
architectural
considerations
on
those
and
then
those
couple
points
to
make
they're,
like
you
know,
be
careful
with
your
assumptions
of
you
know.
This
is
only
in
a
silo.
A
D
L
Okay,
thank
you
so
so
I'm,
a
plumber
and
I'm,
going
to
give
a
plumbers
perspective
on
net
slicing
when
I
were
interested
in
doing,
is
getting
the
bits
from
A
to
B,
according
to
the
characteristics
that
cleverer
people
than
me
have
already
set
up.
So
what
do
I
mean
by
network
slicing?
So
for
me
down
in
the
implementation,
lower
layers,
data
paint
layers,
it's
a
two
layer
network
where
the
underlay
provides
the
resources
and
the
overlay
service
is
the
tenant
tenant
can
have
the
degree
of
static
and
dynamic
isolation.
L
That's
needed
to
support
both
soft
and
hard
slicing
and
the
complete
spectrum
in
between.
So
what
do
we
mean
by
hard
slicing?
The
model
for
hard
slicing
is
that
it's
a
separate
physical
network,
but
of
course
you
wouldn't
want
to
you-
may
want
to
implement
it
like
that,
but
you're
doing
an
English
statistical
multiplexing.
So
the
trick
is
to
figure
out
how
we
give
majority
of
the
characteristics
of
a
separate
physical
network
to
a
virtual
network.
So
a
network
implanted
with
multiplexing
soft
slicing
is
very
similar.
L
L
The
underlay
provides
the
tenant
with
it
with
a
rich
instruction
set
to
specify
the
actions
to
be
performed
on
the
packets,
that
is
to
say,
we
instead
of
just
sending
a
packet
somewhere,
we
will
have
to
be
rather
more
precise
about
what
actions
happen
on
it.
Both
in
the
traditional
service
function,
Jam
model,
but
maybe
in
more
specific
terms
as
well.
L
So
what
are
the
main
use
cases
and
I'm
only
interested
again
I'm
introducing
on
the
infrastructure?
We
want
to
be
able
to
construct
bespoke
networks,
we
want
tenants
or
applications
to
get
the
type
of
connectivity
and
the
compute
topology
that
they
need
to.
So
it's
a
sort,
that's
a
sort
to
address
their
needs.
We
need
to
be
able
to
construct
assured
networks,
so
critical
applications
would
normally
need
a
private
standalone
network.
L
For
example,
emergency
service
networks
and
power
distribution
control
happen
on
bespoke
net
bespoke
private
networks
specifically
deployed
for
that
at
the
moment,
what
we
want
to
do
is
to
bring
the
scaling
of
that.
We
have
in
internet
type
technologies
to
those
applications
with
the
guarantee
that
we
get
with
private
networks,
deterministic
applications,
applications
that
are
among
that
require
something
to
to
happen
now
immediately
because
of
some
some
event.
L
So
what
do
we
need
to
do
is
to
transport?
Well,
we
also
need
to
consider
transporting
new
network
types,
so
I'll
put
some
pointers
into
this
later
on,
but
in
the
5g
space
people
have
been
talking
about
possible
replacements
for
IP,
for
example,
people
have
been
thinking
of
ICN
as
a
possible
replacement.
L
L
What
work
is
in
progress
within
the
space
that
I'm
talking
about
segment,
routing
service
function,
chaining,
deterministic,
networking
and
ACN
ents
are
critical
pieces
of
protocol
work
that
we
are
doing
that
can
act
as
a
tool
base
for
us
to
to
develop
things
going
forward.
So
what
new
activities
well
I
think
we
will
need
to
enhance
the
segment
routing.
We
will
have
to
give
it
more
instructions,
more
capabilities
to
address
different
objects
in
the
network
and
cause
different
things
to
happen
of
those
objects.
L
L
What
non
IETF
work
is
relevant
to
after
a
two-hour
deliberations
here.
Well,
flexible
Ethernet
is
one
that's
a
system
for
applying
a
hop
by
hop
TDM
instruments,
infrastructure
to
Ethernet,
and
that
is
certainly
a
candidate
for
the
underlay
for
network
splicing,
but
that
doesn't
have
the
properties
that
I
was
talking
about
earlier
on,
where
I
get
the
statistical
multiplexing.
But
if
you
want
to
build
something
at
the
extreme
end
of
hard
slicing,
that
is
a
good
platform.
L
Etsy
you've
got
this
project
called
NGP
next-generation
protocol
and
it's
an
attempt
to
redefining
both
the
the
network
layer
and
the
transport
layer.
I'm,
not
sure
if
it
will
find
traction,
but
if
it
does,
then
we
should
be
in
a
position
to
carry
it
and
since
one
of
their
concerns
is
that
TCP
gives
the
problem
a
one
of
the
properties
of
network
slicing
would
be.
You
could
stop
transport
types
that
would
interfere
from
bumping
into
each
other
information
in
it.
Centric
networking
was
hyped
as
a
the
way
that
5g
would
work.
L
L
That
would
do
many
other
things
as
well
and
indeed,
given
that
to
what
I'm
calling
alien,
Network
layers
have
been
put
forward,
slightly
new
ones
will
come
forward,
and
so
what
we
should
do
is
to
build
a
better
service
that
uses
IP
to
get
the
world
up,
uses
IP
to
manage
the
world,
uses
IP
or
MPLS
to
carry
things
around,
but
can
carry
these
new
types
so
we're
building
a
sandbox
relevant
drafts.
Really.
This
is
just
some
background.
L
G
D
B
L
In
a
hard,
isolated
or
a
hard
sliced
system,
I
think
it's
such
that
if
I'm
running
an
application
over
one
network,
I
can't
tell
that
the
other
network
exists,
so
we
have
static.
Isolation,
in
my
mind,
is
what
regular
VPNs
are
about,
but
dynamic
isolation
is
closer
to
what
deterministic
networking
is
providing,
that
is
to
say,
when
I
want
to
send
a
packet
I'm,
not
waiting
on
anything
else.
M
G
M
L
And
I'm,
trying
to
I'd
like
to
add
those
enhance
sort
of
guarantees
into
the
wide
area.
I
believe
that
is
the
piece
one
of
the
pieces
of
work
that
the
IETF
can
uniquely
add
deterministic
networking
as
the
start
of
a
platform,
but
I,
don't
think
deterministic
network
is
really
delving
into
what
we
might
do
in
the
underlying
network
itself
or
what
we
might
ask
it
to
do
for
us
in
order
to
do
better.
N
Alright
I'm
Hana
flink,
now
I'm
approaching
this
slicing
area
from
management
and
orchestration
part,
especially
motivated
to
work
about
what's
taking
place
and
treated
in
PSA
5,
and
it's
so
so
that
games
the
background
to
the
presentation
how
this
relates
to
the
gap
analysis
that
Christian
presents
a
couple
of
tens
of
minutes
ago.
The
presentation
and
related
draft
related
to
this
cross
domain
coordination.
Point
number
two
and
then
mostly
where
we
said
requirements
and
expectations
is
in
a
network
slicing
with
them.
N
So
because
of
multi-tenancy
and
multi
domain
aspects,
there
needs
to
be
something
new
there
for
filtering
various
types
of
KPIs.
So
answering
of
questions
that
were
given
to
us
if,
earlier
what
network
slicing
is?
It
is
a
tool
for
implementing
multi-tenancy,
sharing
net
resources
and
sites
sites
among
multiple
tenants.
It
is
a
tool
for
creating
dedicated
networks
for
for
vertical
markets,
will
very
special
type
of
networks
like
what
the
area
covers
mentioned
is
IOT
networks;
they
don't
need
necessary
or
everything.
N
What's
there
in,
there
might
be
network
site,
and,
and
finally
it
is
a
tool
for
service
optimisation
for
the
operator
to
construct
an
efficient
network
for
its
own
purposes
and
running
his
or
her
business.
So
what
we
do
we
take
as
a
starting
point
that
network
sizing
it
as
defined
by
next
generation
mode
mobile
network
that
was
also
adapted
by
3gpp,
si5
and
Etsy.
This
is
the
information
model
from
taken
from
3gpp
si5,
which
which
shows
two
domains.
We
have
the
common
connectivity
service
domain
and
then
the
network
operator
domain.
N
The
network
slice
provides
multiple
logical
networks
on
top
of
parcels,
earth,
seared,
networking
infrastructure,
a
slice
may
include
several
network
components
and
in
3gpp
terminology
they're
using
network,
so
I
submit.
So
one
slice
could
contain
these
network
sized
subnets
multiple
of
those
transport
network
in
this
model
is
one
of
these
networks,
wise
subnets
and
and
then
below,
that
we
associated
to
this
grouping
of
networks
or
subnets
network
functions
and
as
an
example
of,
of
course,
stemming
from
3gpp.
N
There
are
these
core
network
functions
and
access
network
functions,
but,
but
you
can
imagine
are
other
type
of
functions
there
as
well.
Also
traffic
engineering
functions
as
wise
may
be
deployed
or
operated
by
a
slice
provider,
meaning
the
network
operator
itself
or
the
tenant
who
requested.
That
depends
on
the
relationship
and
at
the
contract
that
has
been
made
regarding
the
multi
domain
prospects
of
see
that
there
are
two
layers
that
are
crossing
across
multiple
tenon,
multiple
domains.
N
One
is
the
service
instance
layer
and
then
the
network
slicing
layer-
and
it
is
these-
definitions-
are
taken
from
next
generation
mobile
networks.
The
service
instance
layer
is
in
the
scope
of
TM
4,
which
has
been
defined
certain
information
and
data
models
for
that
purpose,
and
it
is
also
providing
customer
facing
services
and
eight
years
as
well
as
resource
facing
services,
service,
api's
and
interfaces,
the
kind
of
northbound
interfaces
from
the
network,
slicing
manager
towards
the
service
instance
and
then
finally,
at
the
bottom.
N
We
have
these
domains
and
the
domains
may
be
technology
specific
that
it
is
working
there.
The
IETF
is
working
and
many
other
bodies
are
working
on
their
own
technology
domains,
recording
Penta
multi-tenancy,
how
it
impacts
it,
multiple
oscillating
in
to
record
notion
of
recursion.
Here,
the
picture
so
again.
This
communication
service
management
function,
network
slice,
management
functions
which
is
expected
to
come
from
the
network
operator
and
then
the
sub
network
slice
up
network
management
function.
A
question
is:
are
these
eight
years
one
and
a
be
ApS?
N
A
and
ABS
be
equal,
and
if
they
are
equal
again,
there
is
a
natural
recursion.
What
we
can
put
on
top
of
communicate,
okay,
some
service
money
management
and
on
other
layer,
so
orchestration,
creates
slices
and
associates
network
functions,
depend
and
setups.
The
connectivity
between
these
there
are
virtual
network
functions
as
well
as
physical
network
functions
and
their
lifecycle
management
differs
quite
a
lot,
so
so
that
makes
a
bit
of
a
difference
what
can
be
managed
and
under
eight
C
mono,
and
what
is
their
existing
management
systems?
N
Nonetheless,
because
of
the
recursion,
there
is
a
strong
need
for
service
food
meal
for
me
meant
and
monitoring
between
these
these
layers,
especially
what
comes
to
capacity
security,
quality
of
service
and
mobility.
It's
not
only
the
isolation
of
resources,
but
also
the
ability
to
the
operator
to
provide
correct
level
of
of
control
to
that
tenants,
and
we
foresee
at
least
these
crude
three
levels
of
control
that
network
operator
can
provide
to
the
size
consumer.
The
slice
cone
consumer
is
allowed
only
to
monitor
the
selected.
Kprc
is
like
a
dashboard
type
of
operations.
N
If
you
wish,
then
the
slice
consumer
may
have
a
limited
control
of
configuring,
the
given
network
functions
and
on
board
some
certified
network
functions
from
a
catalog
or
then
it
can
provide
a
full
control,
so
the
consi
slice
consumer,
which
is
running
possibly
its
own
monastic.
Of
course,
the
last
one
is
is
very
clear.
One
is
a
bit
of
exaggerated,
but
but
still
there's
a
possibility.
Nothing
excludes
them.
N
So
what
this
leave
us
leaves
us
to
is
is
that
paper
needs
to
be
some
management
entity
that
is
dealing
with
these
abstractions
and
consolidating
these
half
cups
to
the
sois
consumer,
and
it
is
one
what
we
are
sewing
in
the
draft.
We
are
introducing
networks
last
management
function,
which
is
setting
sitting
on
top
of
Etsy,
mano
and
and
then
on
top
of
network
management
systems,
and
these
network
management
systems
they
gradually
crawl
towards
these
virtual
network
management
functions
as
we
increase.
N
The
functionality
of
these
networks
lies,
subnet
management
functions
and,
and
the
here
you
can
see
their
dependencies
interfaces
and
possible
places
of
protocols
that
that
we
foresee
to
be
important
so
to
wrap
up
and
there's
a
lot
of
work
ongoing
in
the
non
IETF
area.
It
especially
on
management
aspects.
But
but
you
know
in.
G
N
To
ensure
whatever
work
idea
is
taking,
we
need
to
align
this
work
and
and
what
parts
need
to
be
aligned
the
other
abstractions
and
data
models
they
need
to
support,
multi
doorman,
a
multi-tenant
operations,
interfaces
between
the
relevant
functions,
support
for
records
and
varying
levels
of
export,
export
control
for
tenants
with
different
capabilities
and
and
then
then
we
pinpoint
that
that
there
is
this
need
for
functionality
that
consolidates
consolidates
the
OEM
have
caps
performance
indicators
that
slide
consumers.
This
is
the
concluding
slide.
D
D
With
this
picture
and
one
of
the
first
picture
we
saw
in
prim
statement
right,
were
you
spoke
about
template
management,
about
networks
like
Twitter,
in
lifecycle
management
and
to
an
orchestration
domain
orchestration
cross
domain
for
the
Fluke
domain,
right,
maybe
not
cross
operator?
And
what
do
you
want
to
do?
What
is
your
goal
here
in
the
ITF?
Won't
you
have
to
full
an
MS
versus
in
the
ideas.
No.
N
K
N
It
is
work
to
be
done.
This
is
both.
So
if
you
look
at
the
concluding
so
I
said
there,
there
I
stay
what
I'm
expecting
take
the
models,
combat
abstractions
his
interfaces,
support
of
recursion
and
and
then
means
to
consolidate
these
objects
right.
These
are
the
elements
in
order
to
implement
it
at
the
chamber,
but
what
I
was
sewing?
The.
N
N
N
Any
new
protocols,
possibly
extensions-
we
should
start
from
these-
that
that
we
are
able
to
support,
is
this
recursion
recursion
and
a
multi
domain.
Asli
multi
domain
create
some
some
policy
issues.
We
are
notated
supposed
to
be
released
in
very
sensitive
information
to
our
neighbor
and
we
need
to
be
able
to
encapsulate
the
data
more
links,
Thanks,
ok,.
A
Thank
you
very
much
honey.
Ok,
with
that,
we
concluded
our
presentations
and
now
we
we're
gonna
have
open
discussion,
so
I
will
be
showing
these
lights.
So
you
remember
the
questions
we
were
asking.
So
if
people
go
into
the
mic,
one
for
address
them
that'd
be
great
comments
on
the
presentations
we
saw.
They
are
also
welcome
and
please
keep
in
scope
and
be
concise,
because
we
don't
have
so
much
time
either
and.
B
O
Tell
Mizrahi
Marvel
so
I
have
a
question
from
the
first
speaker,
George
I.
We
understood
that
3gpp
is
not
really
waiting
for
our
work
and
they
probably
know
how
to
define
the
slicing
models
and
architecture
on
their
own.
So
my
main
question
is:
who
is
the
target
audience
of
the
work
that
we
discussed
today.
C
Yeah
good,
oh
hey,
maybe
I
can
quickly
respond
to
that.
So
I'm
not
sure
when
you
say
the
target,
whether
you
should
like
say
define
the
target
at
my
understanding
from
IIT.
If
so
far
is
that
you
have
enough
self-esteem
usually
to
start
to
work
on
your
own
and
then,
of
course
you
have
in
you,
you
got
a
lot
of
presentations
now
what
other
groups
are
working
on?
What
what
holds
need
to
be
filled?
C
Maybe
so
I
think
if
you
keep
these
things
under
your
radar
most
likely,
your
solutions
will
be
chosen
later
on
when
architectures
are
defined
in
more
detail.
I
can't
promise
you
that
these
solutions
will
be
taking
at
one
point,
but
at
least
if
they
are
there,
they
need
to
be
taken
into
consideration
and
we
have
the
evaluation
processes
where
we
do
such
things.
Thanks
yeah.
P
G
B
We'll
come
back
to
you
who
thinks
it's
nearer
a
hundred
okay,
you
don't
get
the
question.
So
non
was
asking
a
scaling
question.
How
much
are
we
slicing?
Are
we
slicing
in
the
order
of
ten
customers,
utilizing
a
limp
or
a
node,
or
are
we
looking
at
a
thousand
or
a
million
do
I'm
intense
yeah,
ten
slices
or
or
a
thousand
slices
or
a
million
slices?
So
ten
I,
see
of
the
order
of
twenty
hands?
Are
a
thousand.
A
F
To
address
it
before
VPNs
were
invented,
or
the
question
was
how
many
you
know
what
scalable
as
the
technology
to
implement
it
evolve.
The
now
is
not
the
norm
that
moved
from
few
too
many
I
think
that,
as
slicing
will
come
to
the
same
view,
namely
soonerlater
net,
to
be
properly
implemented,
mature
at
all
the
levels,
in
particular
management,
as
it
was
mentioned,
and
then
the
answer
will
be
very
many,
because
this
is
going
to
be
soon
or
later,
the
abstraction
we
don't
need
any
other
things
on
which
all
the
other
elements
could
happen.
I
Ericsson
I
would
like
to
try
to
make
a
summary
of
what
I
heard
in
this
90
minutes.
That'd
be
perfect.
We
then,
let's
see
how
many
people
agree
with
me,
adopt
that
we
have
different
types
of
domains.
Let's
say
radio
totally
out
of
our
business,
at
least
for
the
moment
transport.
We
have
different
requirements.
Someone
believes
they
are
almost
all
addressed
with
actual
tools
available
in
18,
ITF
personally,
I
agree
with
them.
Some
others
believe
something
is
missing.
I
We
can
work
on
that
I
wouldn't
say
there
is
the
need
for
new
huge
work,
but
probably
augmentation
to
what
is
already
there.
It
would
be
enough,
then,
the
club,
when
I
speak
about
how
they
think
of
an
FBI
packet
core
bucket
core
out
for
the
moment,
and
if
we
I
this
is
where
I
see
a
little
bit
more
meat.
We
have
a
lot
of
solutions,
but
Silas.
Maybe
we
could
start
working
too.
I
These
domains
work
together
again
personally,
I
believe
it's
just
a
matter
of
augmenting.
What
is
already
there,
I
see
a
city
and
as
a
perfect
starting
point,
to
use
the
young
models
we
have
in
a
city
and
topology
T,
topology,
augmented
with
NFV
information
and
FBI
things
like
that.
This
is
my
view
and
my
summary
of
okay.
Q
A
Q
Mobile
I
I,
don't
have
really
specific
questions,
but
I
would
like
to
share
some
of
my
observations
may
be
helping
the
room,
understanding
what
we
as
a
both
proponents,
understand
as
Network
slicing
and
what
not,
what
3gpp
really
think
now
is
slicing
aids,
so
in
in
3gpp
sa
it's
a
clearly
state
that
network
slicing
defined
by
3gpp
only
include
ran
access,
network
and
packet
core
network.
So
this
is
waiting.
What
has
been
writing
down
in
the
latest
version
of
3gpp
so
to
document,
and
also
in
I,
say
five.
Q
There
are
actually
requirement
in
a
specific
section
that
saying
the
network
slicing
management
system
defined
by
3gpp
sa
five.
There
are
two
options:
one
is
to
shoot,
relay
or
should
advertise
the
link
and
requirements
to
the
transport
network
system
management
system
and
two
to
actually
ask
the
transfer
transport
network
system
to
decide
which
transport
technology
or
technology
should
be
used
for
the
linkage
between
the
grant
are
a
n
and
core
network
and
option.
Two
is
assumed
that
the
3gpp
network,
slicing
management
system
has
an
approach
to
know
the
transport
information
to
decide
itself.
Q
So
that's
clearer
to
me
are
actually
considered
some
sort
of
requirement
for
the
transport
area
to
work
on,
of
course,
in
this
term.
In
terms
of
this
information
on
models
that
can
be
provided
between
these
two
systems
and
also
on
another
point
of
view,
I
would
like
to
share
in
responding
to
unhonest
presentation
and
we
can
discuss
this
offline
as
well.
Q
So
I
actually
don't
agree
regarding
transport
network
as
a
and
SSI,
which
is
network
slicing
studnet
instance,
because
here
I
quote
in
I,
say
5,
it
says
a
NSS
I
may
include
core
network
only
or
ran
only
or
both,
so
this
actually
aligned
with
the
definition
in
I
say
it
does
not
include
transport
network.
So
my
understanding
network
slicing,
this
word
in
3gpp
only
include
ran
and
packet
core
and
IETF
Network
slicing,
although
using
the
same
exactly
worse,
mostly
main
transport.
Q
E
Your
next,
so
with
regards
to
scope,
probably
talking
of
AP
Shepherd
for
the
book
I
think
focusing
on
3gpp
is
wrong.
Number
one.
There
are
no
requirements
coming
from
to
Jupiter's
yet
number
two.
If
it's
very
much
to
DPP
focus,
it
will
result
in
deficient
solution,
focused
only
on
radio
and
packet
curve
that
there
are
additional
things
that
lead
to
network
sizing.
It's
not
new.
We've
been
doing
a
run
with
PN
of
the
European
Ltd
on
quite
some
time.
However,
B
natural
size
definition
has
always
been
a
transport
there.
E
We've
never
looked
into
resources
right
if
you're
trying
to
do
LCVP
and
you're
not
losing
that
number
of
CPU
cycles
on
tear
out
the
difference.
Now
the
network
function
virtualization
brought
this
functions,
the
mobile
edge
computing
or
multi
access
requires
proximity
of
effort,
work
placement
which
requires
whole
notion
of
network
slices,
but
it
really
means
in
terms
of
resources,
networking
resources
to
place
or
cloud
to
reach
workload
to
deployed
rightly
so.
E
We
should
focus
really
to
adjust
industry
problem
rather
than
focusing
or
to
GDP
or
in
here
for
any
other
organization,
and
the
scope
should
should
be
as
such.
Not
really,
they
are
not
telling
us
anything,
so
we
are
not
doing
anything.
From
my
perspective
from
personal
perspective,
it's
wrong.
We
should
focus
on.
Industry
needs
nothing.
Particular
it's
just.
Ok,.
A
A
K
Of
the
things
we
want
to
avoid
I
think
is
the
mistake
of
conflating
all
of
the
requirements
of
network
slicing
as
needing
to
be
satisfied
by
all
of
the
network,
because
when
you
look
how
networks
are
built
right
now,
there
is
the
ran
component,
the
backhaul,
the
packet
gateway,
etc.
The
provenance
of
3gpp
technology
is
like
Sippi.
K
So
if
we
actually
think
we
are
going
to
extend
all
of
these
very
demanding
use
cases
ubiquitously
across
the
network,
we're
solving
a
problem
that
does
not
need
to
be
solved,
because
this
is
really
about
intelligently
arranging
the
deckchairs
to
address
things
as
much
as
anything
else.
Thank
you.
Dave
Shree.
N
Grand
Valley
Cisco,
so
hi
general
one
general
comment
on
provisioning
domains.
So
in
multiple
myth,
working
group
MIF,
there
was
a
one
work
item
called
a
multiple
reading,
domains
npvd.
So
a
lot
of
slicing
concepts
are
present
in
the
in
that
work.
Somehow
that
work
did
move
forward,
but
I
really
want
the
the
book
or
group
to
really
look
at
that
that
work.
That
was
done
in
the
past.
Okay.
R
Warren
so
Warren
Kumari,
maybe
what
Dave
said
clarified
this
for
me
somewhat
I'm,
not
sure
a
large
amount
of
the
discussion
seems
to
feel
as
though
it
sort
of
assumes
that
the
network
exists
everywhere
and
looks
the
same
everywhere.
So
it's
this
like
thin
layer
of
stuff
which
you
put
all
over
the
place,
and
it
doesn't
really
work
like
that
right
networks
get
built
so
that
you
have
more
capacity
where
you
need
it
and
it
get
built
sort
of
according
to
what
the
existing
uses.
R
If
you
expect
that
you
can
go
along
and
say,
I
would
like
some
network
capacity
from
here
to
here
with
latency
that
just
isn't
doable,
because
the
network
doesn't
look
like
that
or
more
with
sort
of
curious
type
profiles
that
look
like
this.
That
means
that
the
network
needs
to
be
built
with
way
more
capacity
than
currently
exists
or
with
the
ability
to
plan
some
set
of
people
off
when
this
comes
along.
This
I
think
means
that
things
are
gonna
end
up
way
way
way
more
expensive
and
I.
R
Think
that
a
lot
of
the
sort
of
we
would
like
to
be
able
to
do.
X
assumes
that
the
network
is
going
to
be
there
and
in
order
for
the
network
to
be
there,
you
need
spend
way
more
money.
So
if
people
are
okay
with
that,
you
know-
maybe
that's
fine,
but
I
suspect
providers
are
not
gonna
want
to
build
to
that
sort
of
level.
You
know
what
just
ubiquitous
capacity
everywhere,
because
then
it's
fairly
easy
to
be
removed,
my
competitor
and
then
suddenly,
you
know
I'm
left
with
this
extra
space.
S
S
Basically,
when
he's
saying
that
a
network
slash
in
his
public
concerns
the
packet
switching
layer
and
a
network
is
not
involved
in
the
that
slicing
I
disagree
with
that
this,
how
things
may
look
to
the
network
slice
user,
but
when
we
talk
about
network
slice,
isolation
and
all
kinds
of
constraints
and
like
benefits
and
delays,
reliability
software,
so
this
would
intimately
involve
management
of
network
network.
So
we
really
have
to
deal
with
that.
Thanks.
S
E
Yeah
chicken
from
Holly
I
have
a
similar
communion
as
a
ugurus.
We
are
expecting
the
requirements
from
the
GBP
and
metal
slicing
and,
at
the
same
time,
ITF
working
on
the
transport
that
network,
and
we
will
expect
this
capability
of
the
nurse'll
IC
to
provide
a
service
for
the
vertical
industries
afforded
more
general
use
cases.
Also,
so
I
think
this
work
should
be
useful
in
idea.
Okay,
thank
you.
D
Typically,
what
we're
doing
is
we're
dealing
with
networking
in
the
ITF
right
and,
and
there
I
see
like
the
network
slice
on
an
orchestration
and
I'm
wondering
if
you
want
to
have
all
these
done
in
the
ITF
and
if
not,
which
interfaces
to
come
back
to
the
orchestration
plantation.
The
gentleman
spoke
about
api's
for
service
functions.
So
what
actually
do
you
want?
You
have
here
from
the
ITF.
That's.
F
A
very
good
question,
first
of
all,
I
would
like
to
say
that
I
am
fully
in
agreement
with
Jeff
here
there
is
no
point
to
wait
for
requirements
from
outside.
To
start
working
very
remind
that.
The
slicing
activities
are
mainly
about
managing
the
transfer
network,
but
even
more
to
ensure
that
this
transport
network
is
supposed
to
carry
well
the
traffic
for
at
least
one
one
service
well
and
not
for
everything
unabated.
F
But
to
answer
the
question
is
that
we
are
talking
about
embedded
management
protocols
in
the
network,
and
that
includes,
in
my
mind,
new
ones,
who
tend
to
be
created
in
no
particular
order.
The
coordination
of
all
these
slicing
and
the
name
of
orchestration,
either
in
a
one
domain
or
multiple
domain.
It's
essential
second
protocols
related
to
discovery
and
monitoring
of
the
slicing,
which
is
are
the
very
dynamically
created
which
need
to
be
created,
autonomically,
not
behind,
and
so
on.
F
Also,
new
protocols
are
may
be
to
for
the
creation
of
the
resources,
the
network
functions,
which
and
other
elements
service,
functional
management
to
create
a
slice
and
then
instantiated,
which
means
that
traffic
then
had
to
be
directed
to
that
slice.
One
instance
aunty
new
protocols
are
needed
to
allow
elasticity
of
the
slices,
are
triggering
elasticity
when
the
service
requires
more
resource
or
less
resource,
more
or
less
network
functions
more
and
more
again
to
be
virtualized
anyway.
This
has
to
be
dynamically
created
and
enhance.
F
These
are
pure
management
of
the
transport
network,
which,
in
my
view,
it
is
part
of
the
essence
of
ITF,
and
this
is
where
this
work
will
add
value
of
substance.
I
think
that
also
it's
over
estimating
too
much
to
look
only
other
traffic
engineering.
This
is
beyond
traffic
engineering
to
some
extent-
and
this
is
probably
the
complexity
which
has
to
be,
though,
underneath
to
answer
your
question
about
isolation
or
others.
That
could
be
many
type
of
network
Sdn
like
knowledge
D,
unlike
many
guarantees
or
different.
F
We
should
cover
all
of
them,
because
I
have
slices
or
should
cover
all
these
parts
and
it's
a
time
to
find
out
what
is
material
in
terms
of
solution.
But,
in
my
view,
solution
for
these
problems
are
needed
and
next,
two
years
in
order
to
catch
up
with
the
industry,
which
is
working
in
parallel
anyway.
D
D
Right
so
I
be
involving
those
and
MS
OSS
at
least
those
respect
of
multi-tenant
cross
domain
cross
controller
part
of
earth
caps.
This
is
recon
Plex.
Basically,
what
you
want
here
is
a
full
kind
of
product
which
are
sold
to
do
if
I
think
example
of
an
l3
VPN
right.
So
this
is
what
you
want
to
have
by
adding
the
arrows
at
the
top
right,
because
whenever
you
start
to
go
between
the
slice
provider,
this
is
like
at
the
top
of
the
enemies
or
SSI
want
to
request
a
service.
D
It
should
be
much
it
turn
on
is
going
to
go
to
different
networks.
Somehow
it's
kind
of
easy
to
create
those
api's,
because
a
yang
model
is
an
API
right,
create
slots,
delete
slice
extensors
all
right,
I
can
do
that
very
easy.
The
hard
part
is
one
ago
you
have
to
map
this
to
the
different
technologies.
In
the
writing.
One
we
saw
segmenting,
we
saw
T's,
we
saw
a
VPN
plus.
D
We
saw
all
this,
but
this
I
mean
this
is
like
code
that
we
have
to
write
with
if
statement,
if
an
if
I'm
a
transport
network
and
by
the
way
the
destroy
definition
is
also
about
access
and
data
centers
of
if
data
center,
if
transport,
if
this
technology,
when
I
do
I,
do
all
this,
so
this
is
code
in
the
end.
That's
what
I'm
starting
to
say
that
it's
the
full
and
MS
OSS
you
want
to
have
here,
Sun
alarmist.
It's.
F
Could
be
standardized
in
order
to
allow
interrelated
and
operation
on
slicing
uniformly
a
much
smaller
than
big
process?
Second,
obviously
this
mapping,
which
I
mentioned,
has
to
be
done.
It's
probably
per
slice,
even
if
exotic
slice
has
to
compose
to
be
specific
to
one
network,
is
the
animal
like,
for
example,
like
does
or
not
so
this
mapping
have
to
be
multiple,
and
indeed
this
part
of
the
job
now
how
to
put
together.
All
things
is
part
of
the
process
which
I
call
the
template,
which
need
to
be
instantiate
and
use
uniformly.
F
A
E
The
key
success
factor
for
anything
are
consume
ability
and
press
ability
and
to
bring
it
directly
back
to
atf.
Any
solution
and
slicing
will
require
recursiveness.
It's
multi-layer,
multi
domain
by
definition,
which
will
bring
some
requires
regards
to
young
and
way
with
the
data
modeling,
and
this
should
be
discussed
about
now,
because
we
are
producing
this
model
number
two.
Our
advisors
are
with
us
our
data
models
which
brings
back
young
again.
E
T
We
have
a
seven
layer
architecture
from
the
OSI
from
the
deep
in
a
layer
we
can
be
a
definitive
in
the
slicing,
for
example,
from
CVP
the
most
focused
on
a
layer
to
slicing,
but
if,
on
the
ITF
remote
the
focus
on
the
slicing
after
three
layer,
3
layer,
I
think
you
example
in
CVP,
we
define
the
mobility
management,
the
based
on
their
to
technology.
Do
you
think
an
oval
by
in
the
item
use
both
of
you
before
aqua
six,
the
total
it
even
the
Khiladi
solve
the
same
problem
from
poverty
management?
T
Also,
we,
if
we
sit
with
him
in
item,
we
have
at
least
a
differential
layer,
are
weeping
wine
snare
to
within
another
mystery
with
Ian.
Even
some
of
people
say
that
peer-to-peer
technology
can
be
used
to
create
the
IP
n,
a
VPN
on
the
break.
Everything
enable
like
sky
be
immutable,
a
torrent.
So
from
from
my
point
of
view,
if
we
start
slicing
when
personal
restricted
with
the
layer,
we
will
be
focused
on
even
there
have
a
deep
internal
review
and
a
requirement.
T
U
Aaron
Faulk
Akamai
I
just
like
to
point
out
a
piece
of
related
work
to
this
over
a
big
part
of
the
last
ten
years.
I
worked
on
a
National,
Science
Foundation
us
the
National
Science
Foundation
funded
our
research
network
called
genie.
You
can
find
it
a
genie
net.
It
is
a
national
scale,
collection
of
cloud
computing,
interconnected
by
layer,
two
networks
that
are
dynamically
assignable
resources.
U
So
this
stuff
has
been
around
in
the
research
and
education
network
for
a
while
turns
out
that
it's
really
hard
when
you
will
start
line
to
make
guarantees,
but
if
you're
trying
to
provide
best
effort
and
and
connectivity,
possibly
with
a
small
pool
of
reserved
infrastructure
for
special
users,
that
kind
of
thing
can
be
done,
and
it's
actually
running
now.
Okay,
just.
D
A
quick
comment
to
that
I've
been
around
the
same
community
since
worth
noting
that
it's
actually
never
seen
an
use
case
outside
of
experimentation
in
those
communities,
which
is
a
good
point
to
what
Warren
was
saying
that
you
know
it's
fine
and
good
and
fun
to
build
these
things.
But
you
know
you
gotta
actually
have
a
use
for
it.
Okay,.
I
A
VC
P
sub
product
as
a
whole
is
a
classic
case
of
slice
and
it
predates
the
3gpp
effort
by
years,
and
there
were
other
efforts
as
well.
So
especially
if
we
keep
this
as
an
IDF
work,
which
is
not
wholly
dependent
and
wholly
serving
3gpp,
and
if
we
keep
the
amount
of
wish
Lee
which
Alex
presented
I
cannot
call
it
anything
else,
we're
never
gonna
get
anywhere.
This
needs
to
be
cut
down
to
size.
Okay,.
A
Thank
you,
I
mean
just
to
clarify
before
we
go
into
Yeti,
because
there's
been
like
four
or
five
of
you
talking
about
that.
Obviously
this
is
not
about
3gpp
and
that's
why
New
York
made
the
statement
and
as
any
other
idea
both
if
we
find
work
that
is
relevant
for
the
Internet,
the
IDF
will
tackle
it,
regardless
of
whether
or
not
it
comes
from
3dep
brought
down
for
emmm
f.
A
What
have
you
so
I
hope
this
is
crystal
clear:
yadi,
yadi
ericsson,
so
I
wanted
to
respond
to
Lauren's
comment
earlier
about
the
costs,
and
you
know.
Obviously
you
can't
request
things
that
don't
exist
in
reality,
so
you
know
that
the
things
will
be
limited
by
that,
but
also
they'll
be
limited
by
the
useful.
You
know.
A
Market
behavior,
so
things
that
are
harder
to
get
by
are
gonna,
be
more
expensive
and
if
lots
of
people
request
that
and
they
actually
pay
money
for
that-
and
that's
great
you
know
if
lists
people
do
that,
then
you
know
it's.
You
know
more
more
resources
available
for
those
that
actually
do
require.
That
particular
thing.
So
I
don't
think
that's
a
major
concern.
A
I
would
rather
argue
that
the
you
know
if
there's
a
cost
concern
here,
it's
more
about
the
complexity,
as
pointed
out
by
the
previous
speaker
and
I
am
in
in
you
know,
it's
ITF
does
a
lot
of
great
work
in
this
space.
Also
others
do
open
source
organizations
and
so
forth.
I
think
we
need
to
continue
that
work.
Expand
on
that
work
figure
out.
A
What
are
these
small
pieces
we
need,
but
we
should
not
go
totally
crazy
and,
and
you
know,
attempt
impossible
and
and
this
or
that
and
all
the
possible
requirements-
that's
maybe
too
much,
in
my
opinion,
at
least
I
can't
fit
it
in
my
head.
Thank
you,
okay,
thank
you
Gary.
So,
with
this
week
we
close
the
mics
and
we
are
moving
to
us
Adrienne
mentioned
before
they.
You
know
54-34
questions
which,
even
though
they
are
basically
geared
towards
you
know
working
group
for
means
boss.
B
Let's
jump
to
the
third
bullet
here.
I
think,
which
is,
is
the
scope
of
the
problem
well
defined
and
understood
so
really
that
that
comes
back
to
do.
We
have
a
clear
understanding
of
what
net
slicing
is
now
do,
or
at
least
do.
We
believe
that
there
is
a
problem
called
net
slicing,
that
we
need
to
investigate
further
and
pin
down.
So
let's
have
a
hum
on
that.
Do
you
think
that
the
this
scope
of
the
problem
is
well
understood.
B
B
So
well,
let's
work
backwards.
Then,
if
we
were
starting
work
on
trying
to
nail
down
what
we
mean
by
neck
slicing
and
what
work
needs
to
be
done,
who
in
the
room
would
be
willing
to
actually
work
on
this
by
writing
drafts
and
reviewing
drafts
not
just
showing
up
on
a
mailing
list
or
or
so
on,
and
you
can
put
your
hands
up
for
this.
One
and
I
see
pushing
30
hands
to.
B
And
then
we
beg
the
question:
why?
Why
would
you
do
that?
Is
this
a
problem
that
needs
solving
in
the
ITF
okay?
So
this
is
an
ITF
scope
problem
and
a
problem
that
actually
needs
to
be
addressed,
and
you
may
have
on
this
one:
that's
a
pretty
quiet
hum
so
we'd
better.
Do
the
opposite!
Those
of
you
out
there
who
think
this
is
not
a
problem
that
needs
solving
in
the
ITF.
Please
hum.
C
Is
not
one
problem?
There
are
a
bunch
of
problems
and
we
can
look
at
each
of
the
problem
and
decide
whether
we
take
this
problem
but
take
that
problem,
because
if
somebody
asks
me
are
you
ready
to
take
that
slice
problem?
No.
But
there
are
a
lot
of
problems
that
I
will
be
interested
to
work
on
that
go
under
the
net
slices
and
then
being
clearly
stated
here.
A
I
I
think
we,
we
basically
know
had
the
questions,
the
answers
we
wanted
and
yeah
I
agree
with
with
you
actually
that
yeah,
it's
not
like
you
know
on/off,
but
but
we
cannot
have.
You
know
30
questions
now
in
in
10
minutes
so
well.
What
we
think
we
heard
is
you
know
we
we
get
a
few
use
cases
and
different
ideas,
I
think
the
conclusion
or
the
agreement
seems
to
be
like
people
agree.
A
This
is
a
complex
issue
is
clearly
not
you
know,
well
understood
still
by
the
hand
we
got
before
and
and
then
basically,
what
we
need
to
do
is
talk
to
our
IDs
and,
let
me
stress
again:
it's
not
only
benoit
an
ops
area.
We
will
talk
to
the
iesg,
because
this
goes
across
many
areas
and
basically
then
the
the
ball
basically
will
be
with
them
through
to
take
the
next
step,
so
to
be
very
clear.
D
So
the
hot
our
task
you
try
to
summarize
this,
so
I
took
some
notes.
What
I
want
to
do
is
what
we
do
at
the
end
of
the
week
is
that
we've
got
an
IAS
GI
a
be
meeting
in
which
we're
going
to
collectively
review
this
and
give
it
give
an
answer.
So,
however,
I
took
a
couple
of
notes
here:
okay,
we
noted
your
conclusions.
There,
there
abouts
right,
I,
see
lot
of
people
in
the
room.
D
That's
a
good
thing
and
by
the
way,
thanks
to
you
guys
can
start
drinking
so
network
slicing
has
got
a
specific,
specific
notion
in
5g,
but
we
heard
that
we
don't
have
any
5g
requirements
at
this
point
in
time.
I
heard
as
well
that
we
might
have
some
use
cases
that
are
not
5g
related
and
somehow
I'm,
not
surprised,
because
when
I
see
the
definition
of
network
slicing
in
the
prime
statement.
Well,
it's
so
large
that
basically
it
it
covers
everything.
D
So
the
location
is
access,
transport,
DC,
its
compute
storage,
networking,
it's
a
data,
plane
control,
plane
management,
plane,
it's
physical,
its
virtual,
so
I'm
sure
there
are
use
cases
that
are
non
non.
5G,
so
that
the
key
thing
is
to
find
a
one
that
we
want
to
solve
if
you
want
to
solve
them
here,
but
I
still
see
anyway,
different
definitions
of
network
slicing
I've
seen
the
one
print
statement
I've
seen
one
in
queue:
GPP
I've
seen
one
in
a
CDN
I've
snoring
rotting.
D
What
else
I
understand
that
and
I'm
come
from
up
so
I
will
mainly
speak
from
the
ops
point
of
view
in
this
case,
so
I
understand
we
want
to
have
slice
management,
and
that
makes
sense
right.
We
want
to
be
able
to
create
slide
to
extend
slide
to
to
delete
slides
slice.
Sorry,
we
want
to
have
the
ability
to
do
om
right
because
in
the
end
we
do
Network
slicing
to
have
a
service
with
specific
characteristics.
D
Now
on
the
NMS
OSS
part
I'm
confused
here,
because,
typically
it's
not
something
that
we
do
and
to
be
slightly
provocative
and
to
make
people
react
right
on
the
mailing
list.
So
keep
keep
working.
Is
it
seemed
there's
a
bit
of
I
want
a
pony
here:
I
want
a
button
which
says:
I
want
a
network
slice
and
because
I
got
these
API
that
says,
give
me
invite
bandwidth
and
packet
loss
of
zero
and
delay
of
zero.
D
I
will
get
this
automatically
right,
but
behind
this
NMS
OSS
as
I
call
it
there's
a
lot
of
things
that
must
happen
right
and,
as
I
mentioned,
creating
a
yang
model
to
say
creates
lives
is
like
piece
of
cake
right,
but
how
do
we
map
it
to
the
network
below
that
start
to
be
very
difficult
specifically
because
of
the
different
location,
the
core,
the
transport
data
center?
Because
not
forget
there
is
like
compute
storage
networking
and
maybe
the
run
as
well.
D
D
A
D
We
had
a
couple
of
discussion
here.
I've
been
also
provocative
to
make
people
react
right,
I
propose
that
you
use
this
week
with
the
proponents
and
actually
even
with
the
people
who
are
not
proponents
to
make
sure
they
agree
as
well
and
coordinate
on
the
point
of
him
discussing
this
week.
Ok,
thank
you.
Bye
now,
thank.
