►
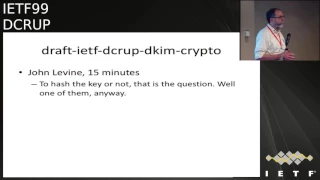
From YouTube: IETF99-DCRUP-20170720-1040
Description
DCRUP meeting session at IETF99
2017/07/20 1040
https://datatracker.ietf.org/meeting/99/proceedings/
A
E
F
B
C
B
B
Please
note.
The
note
well
well
is
very
likes
to
say
you
have
the
right
to
remain
silent.
Anything
you
say
can
be
used
by
the
ietf.
You
have
the
right
to
consult
with
your
attorney
about
your
obligations
and
other
privileges
about
intellectual
property.
This
is
the
formal
version
note
that
the
RFC
numbers
have
changed.
A
new
version
of
BCP
79
is
issued.
That's
the
RFC,
eight
one,
seven
nine,
mostly
it's
a
boiler,
plays
the
same
note.
G
We
seem
to
have
one
open
technical
technical
question.
Please
in
the
original.
The
this
is
part
of
the
Charter.
That
I,
don't
think
we
have
changed,
is
to
add
new
and
add
new
signing
techniques
to
D
Kim
and
the
first,
and
there
have
been
two
and
perhaps
three
of
them,
one
is
to
add
hash
keys
for
RSA,
because
we,
as
we
all
know
there,
are
bugs
in
DNS
provisioning.
G
That
makes
it
foolishly
difficult
to
publish
a
key
that
doesn't
fit
in
a
single
256,
byte
next
spring
and
and
RSA
key
is
bigger
than
one
K
bits.
Don't
do
that
so
right,
so
the
thought
is
we
could
do
what
other
crypto
protocols
do
and
publish
a
256
bit
hash
and
put
the
key
itself
in
the
signature.
That's
technically
straightforward,
as
far
as
I
can
tell
there
is
no
disagreement
about
that
and
Scot
says
he's
working
on
implementing
it.
I
think
Murray
said
he
would
look
at
it.
G
I
know
I'm
looking
at
it
for
the
girl,
stuff,
okay,
the
second
thing
is
to
add
elliptic
curve
signatures
again.
I,
don't
think,
there's
any
any
disagreement
about
that.
We
seem
to
agree
that
we're
doing
what's
called
pure
IDI
DSA,
which
is
ev2
five.
Five,
one
nine
without
an
extra
level
of
hashing
and
the
signature
is
that's
okay
and
the
contentious
question
is:
do
we
also
want
to
add
a
hashed
or
instead
we
want
to
add
a
hashed
version
of
of
V
V
DSA
signatures?
Now
the
hash
in
this
case
there's
no
operational
advantages.
G
Electrical
curve
algorithm
had
keys
twice
as
big
or
written
four
times
as
big.
It
would
still
fit
in
a
single
expert.
So
my
personal
preference
is
that
since
the
hash
key
says
a
hashed
elliptical
curve
key
adds
no
operational
advantage
and
since
Indy
Kim,
since
there
is
no
signature,
since
there
is
no
negotiation
between
the
sender
and
the
receiver,
a
receiver
must
implement
every
possible
crypto
scheme
that
any
sender
might
use
to.
Interoperate
I
would
rather
minimize
the
number
of
schemes
and
just
add
two
other
than
three.
H
So
Mountain
Thompson,
so
there
is
actually
potentially
a
security
benefit
to
hashing,
and
that
is
that
when
you
hash,
you
end
up
putting
the
public
key
in
the
message
that
you're
sending
and
as
a
consequence
of
that
that
public
key
is
then
covered
by
the
signature,
and
there
are
various
ways
in
which
signatures
are
used.
But
one
of
the
less
obvious
properties
of
signatures
is
that
if
you
generate
a
signature
over
over
something,
then
it
is
possible.
H
It's
certainly
in
RSA
and
maybe
in
in
some
of
the
elliptic
curve
variants,
to
generate
a
key
that
will
validate
with
that
same
signature.
So
you
can
generate
a
message,
sign
it
and
then
I
can
claim
to
a
sent.
That
message,
whether
or
not
that's
interesting
or
an
attack
that
actually
makes
sense
in
this
context
is,
is
something
that
will
require,
like
a
huge
amount
of
analysis,
but
I'm,
just
pointing
out
that
the
potential
here
for
us
to
gain
some
additional
defense
against
people.
Switching
switching
keys
out
for
messages
just
operationally.
G
H
I
J
K
So
just
two
I
take
what
I
think
Martin's
argument
was
on
Eric
rajala
on
about
the
potential
ability
which
I
also
don't
know
how
to
exploit.
Is
that
say
say
we
had
some
situation
where
a
message
was
referred
to
where,
where
you
have
an
existing
published
message
and
what
I
want
to
do
is
I
want
to
claim
ownership
of
that
message
and
I
can't
change
the
message
by
Ken:
I
can't
publish
mething
stuff
in
DNS.
K
K
But
you
know
at
some
point
arm
which
may
not
be
too
far
in
the
future.
We
may
at
the
point
where
people
simpler
that
world,
where
the
large
volume
messages
receive
have
two
signatures
on
them,
one
of
which
is
either
eec
or
hashed
RSA,
at
which
point
you
can
say,
I'm
tired
of
supporting
24,
10,
24
hours,
RSA
and
listener,
and
because
you
don't
have
to
accept
anything
in
particular
and
because
that
what
happens
in
receptors,
you
ignore
it.
K
Then
this
isn't
like
this
isn't,
like
you
know,
receiving
h.264
where
you're
like
don't
have
internet
video.
If
you
like
decide
on
what
they
uses
before,
is
it
matter?
If
you
don't
get
like
the
beacon
validity,
that's
what
so
it's
perfectly
easy
to
exam
in
the
market
and
say
well
we're
now
at
78%
of
my
messages
or
one
of
these
two
modern
things
and
I,
just
don't
care
about
twenty
fours
anymore.
So
so
I
have
to
process
the
long
tail.
K
So
I
think
what
I
would
have
a
key
for
is
simply
saying
we
are
consistently
hashing
and
then
at
some
point,
not
lawsuits
in
future
until
I
say
always
in
that
far
away,
then
you
can
just
throw
away
them
a
hash
code
path.
So
if
we're
finding
them
as
code
paths,
that's
axe.
Isn't
it
because
I
say
we
have
to
me.
If
we
think
anybody's
gonna
do
hashed
RSA,
then
we
have
to
have
passion
and
you're
talking
when
you
say,
but
using
the
term
hashing.
You
mean
like.
H
Yeah
not
until
some
weather
or
whether
or
not
the
signing
over
the
key
is
a
value
or
not.
I
think
the
we
have
to
consider
the
fact
that
the
future
is
much
bigger
than
the
past
and,
as
I
could
points
out,
we
have.
We
have
evidence
to
suggest
that
this
is
something
that
we
don't
have
to
worry
about.
A
long
tail,
I
agree
with
eken.
G
H
Is
that
fair,
so
I'm,
not
gonna
like
lie
down
on
the
road
on
this
one
I
think
if,
if
people
are
implementing
this
want
to
avoid
the
extra
step,
then
then
that's
that's
fine.
A
little
little
concern
about
the
signing
of
the
key
I
think
this.
That's
part
of
the
reason
why
we
signed
over
identities
in
in
TLS
and
various
other
protocols,
but
again,
like
I,
said,
couldn't,
couldn't,
pin
anything
to
it.
I.
K
I
guess
I
will
say
that
upon
consideration,
I,
don't
think
it's
worth
having
two
forms
of
the
EDD
essay,
so
I
think
why
I
would
prefer
to
hash
it
upon
and
be
clear
I
guess
there
to
be
two
here
pass:
the
key
all
the
time.
Thank
you,
the
public
key
all
the
time.
If
people
don't
think,
we
see
that
then
I
think
the
answer
is
to
do
hashed,
RSA
and
unhatched,
so
my
rank
order
will
be
hashed,
hashed
key,
always
hash
hash
key
for
RSA
on
hash,
key
free,
DVD
essay.
G
K
K
G
G
C
K
As
far
as
I
can
tell,
what
we
are
primarily
arcing
about
is
the
is
speculative
future
future
simplicity
of
the
code
paths
depending
on.
We
think
what
we
think
is
gonna
happen
in
the
future
and
if
we
think
in
the
future
we're
gonna
end
up
having
to
have
hash
keys
in
its.
You
have
always
hash
keys,
I'm
thinking
the
future,
we're
gonna
having
largely
unhatched
keys
that
it's
you
start
always
on
hash
keys.
K
B
I
C
I
F
C
C
H
I'll
provide
text
and
before
you
disappear,
John
because
oh
I
was
just
about
to
ask
you:
are
you
done
the
I?
The
review
that
I
wrote
of
the
draft
hit
the
list
I
may
have
mentioned
that
I
preferred
hashing
in
it
and
that
caused
an
enormous.
It
wasn't
just
you
rat
hole,
yes,
I,
don't
know
who
started
the
particular
thread
through
your
Apollo.
G
H
Or
didn't
work
for
Belarus
that
that
would
be
fine,
oh
yeah.
The
more
verbose
thing
is
a
problem
that
I'll
get
to
later,
but
the
there
are.
There
were
some
comments
in
there.
That
I
think
are
pretty
pretty
crucial
and
I
want
to
make
sure
that
those
don't
get
lost,
particularly
when
we
get
things
moving
between
documents,
yeah
I'm,.
G
J
G
J
K
So
I
also
just
since
I'm
just
a
list
a
few
minutes
ago,
but
the
names
of
these
things,
so
is
it
as
well
yeah,
both
the
DNS
and
the
okay
good.
So
if
anybody
I
I,
think
anybody
V
Malia
Josh
the
suggestion
that
the
name
should
say
to
55.9,
where
other
than
her
256
and
not
just
better
than
they
should
discuss
it.
But
if
not
people
remind
us.
C
B
We
are,
we
have
extra
time
too,
so
we're
little
heads
good,
just
as
we
start
at
10
minutes
early,
so
you
can
ignore
it
to
some
degree.
The
time
limits
on
these
all
right,
so
the
dekum
usage
document
is
supposedly
and
probably
the
simplest.
These.
The
changes
as
I
recall,
are
that
we
are
deprecating
use
of
sha-1
entirely.
We
are
increasing
the
floor
as
a
part
and
put
it
for
the
number
of
bits
and
keys
that
we
should
be
accepting
to
1024
and
there's
a
third
thing
that
I
escapes
me
at
the
moment.
B
But
essentially
this
is
a
an
update
to
deke
him
directly
that
doesn't
add
anything
but
simply
tightens
up
base
requirements.
Sorry,
so
Mike
should
I
talk
about
that
one.
So
yes,
that's
all
this
is
Seth.
Who
just
mentioned
something
is
going
to
be
shepherding.
This
document
I
think
we're
pretty
close
modulo.
What
we're
about
to
talk
about
too
less
calling
this
it's
it's
a
very
simple
update
document,
so
glad
Martin.
So.
H
Martin
Thompson,
though
there
are
a
number
of
things
that
I
had
concerns
with
this
document,
I
mean
what
you
have
on
the
slide
is
exactly
it
I
think
we
should
not
do
PSS
in
this
document.
Absolutely
okay,
that's
so
that's
a
no-brainer!
Then
we
have
two
things
and
what
you
have
right.
There
is
almost
the
sum
total
of
the
document,
yet
it
somehow
manages
to
be
five
pages
and
two
of
those
are
in
our
fault
but
yeah.
H
Well,
yes,
but
I
think
you
might
be
able
to
get
it
down
to
two
and
I
think
that
simply
means
providing
some
rationale
for
why
the
document
exists
and
then
saying
must
not
use
char.
One
must
use
keys
of
1024
bits
or
higher,
or
you
know,
maybe
we
can
make
it
a
little
higher
than
that
even
I.
Think
1024
is
perfectly
reasonable
at
this
point
in
time.
The
document
currently
includes
a
whole
chunk
of
text
from
the
DK
MRC
verbatim.
Without
modifying
it,
it's
very
confusing.
We
need
to
stop
doing
that.
H
Yep
and
the
other
thing
is.
We
don't
need
to
modify
the
a
B
and
F,
which
is
say
have
to
tell
people
not
to
use
those
code
points
and
modifying
the
ABN.
F
makes
this
document
bigger
and
more
complicated,
and
we
have
iona
considerations
and
all
sorts
of
other
things
that
really
don't
advance
things.
We
just
need
to
tell
people
just
stop
using
that.
B
B
K
I'm
just
trying
to
think
about
what
the
security
properties
of
all
this
are,
so
the
existing,
so
I'm
just
gonna
use
for
a
second
of
people.
Indulge
me
so
these
visiting
attacks
on
sha-1
or
all
collision
attacks,
and
we
don't
have
any
free
image
attacks.
Yet
maybe
we
never
so
the
the
collision
attacks
on
the
so
engine
egg
about
like
how
do
you
support
a
collision
in
this
system?
K
I
think
the
way
you
exploit
the
collision
in
this
system
is
and
or
no
you
say
like
why
it
can't
because,
like
the
produce,
it
is
all
produced
by
via
pop
by
the
center.
But
if
the
way
you've
put
occlusion
in
the
system
is
that
say
you
have
like
a
mere
relay
that
just
spin
filtering
and
now
what
I
do
is
I.
Give
you
two
messages,
one
of
which
and
I.
K
Can
you
throw
any
of
the
input
right,
but
I
give
you
two
messages,
one
of
which
one
for
you
to
sign
that
is
innocuous,
and
is
it?
Is
it
full
my
pornography
or
whatever,
and
then
I
take
this
inter
off
and
I
shovel
to
my
party
traffic,
one
on
so
I?
Don't
know
like
it
anybody's
written
down
what
you
might
actually
be
ideal
to
do
with
a
collision
attack
on
deacon,
but
I'm
I
birthed
someone
thinking
about
that.
I'm
I
don't
know
the
system
wanted
that
right
now
on
the
on.
K
It
might
be
nice
in
these
documents
to
say
something
about
what
we
think
the
times
appropriate
time
scales
were
phasing
out
acceptance
of
sha-1,
which
I
understand
that
we
can't
do
for
quite
some
time,
but
I
know
I
mean
that
the
browser's
made
a
lot
of
noise.
Remember
I
stopped
accepting
sha-1
certificate,
so
I,
wonder
I,
wonder
if
we
should
I
wonder
if
we
should
say
something
at
least
about
these.
You
know
we
expected
to
some
point
in
future
with
some
big
time
scale
ways,
but
they
actually
say
you
stopped
accepting
them
as
well.
K
D
G
B
H
B
M
This
is
very
I
know
some
of
the
security
related,
some
of
the
crypto
related
registries
have
things
like
should
and
should,
plus,
and
something
like
that
or
whatever
that
says
that
the
status
is
likely
to
change
to
be
stronger
in
the
next
version.
Let's
not
go,
there
says
Martin
okay,
nevermind,
like
if
it
said.
Thank
you
yeah.
G
John
the
meeting
at
mean,
as
far
as
when
do
stop
except
accepting
them
that's
sort
of
more
of
a
mug
issue,
is
its
most.
Let
me
for
ten
years
we
told
people
sha-1
is
bad
and
it's
most
in
its
appears
to
be
largely
a
matter
of
figuring
out
who's
still
signing
with
sha-1
and
beating
up
on
the
disiike.
We
can
persuade
them
to
change,
which
is
not
really
the
I
ATF's
remit.
G
N
Chris
Newman
a
concern
I
have
about
the
document
is
I'd
like
to
see
actually
must
check.
The
key
size
of
the
key
is
at
least
twenty
four
now
I,
don't
care
how
you
use
the
result
of
that
that
can
be
up
to
policy,
but
you
must
check
this.
The
key
size
we
had
this
I
noticed
we
had
this
problem
in
TLS
implementations,
where
things
thought
they
were
generating
keys
of
the
right
size
and
they
weren't
and
and
it
created
Interop
problem.
So
I'd
really
like
to
get
that
check
in
early.
L
Kurt
Anderson
responding
to
John's
comment
about
people
accepting
sha-1.
Yes,
just
the
very
fact
that
this
draft
is
in
flight,
provided
a
lot
of
leverage
and
three
of
the
major
folks
that
were
still
actually
sending
sha-1
were
convinced
last
month
to
stop
doing
it
and
have
stopped
doing
it
in
the
month.
Subject.
So.
H
L
H
H
C
I
I
think
that
we
should
say
it
must
not
generate
on
the
acceptance
side
depends
upon
what
you're
going
to
be
using
foot
them
for,
if
you're,
using
the
signature
as
evidence
of
the
message
validity,
as
was
used
in
the
DNC
attack,
then
of
course
yes,
you're.
Looking
at
the
semantics
of
the
message,
and
it
really
does
matter
if,
on
the
other
hand,
all
you're
doing
is
doing
spam
filtering,
which
was
the
original
idea
of
deacon,
then
you
know
breaking
a
sha-1
hash,
breaking
an
RSA
key
that
that
looks
more
like
a
proof-of-work.
I
I
I
think
it
sends
a
bad
signal
to
ourselves
in
that
it's
tells
us
that
we
can
tell
the
the
community
to
turn
on
a
dime
and
one
of
the
things
I've
been
weighted
with
sha
Wan
was
that
I
was
telling
people
to
do
sha
to
like
a
year
after
it
was
published
by
nist
and
people
ignored
me
and
then
suddenly
we
have
kab
forum,
say:
okay,
we've
got
to
get
rid
of
char
wanna.
We
got
to
do
it
in
18
months
and
so
I.
B
In
the
future,
so
that
it's
interesting
you,
you
you're
like
an
interesting
counterpoint
to
what
we've
been
hearing,
which
is
the
community
asking
us
to
give
them
a
hammer
by
which
they
can
hit
themselves
over
the
head
to
move
for
it.
Look
there
there's
a
there's,
there's
a
certain
amount
of
inertia
that
a
must
not
accept
will
solve
and
so
you're.
Actually,
this
is
the
first
question
to
give,
which
is
it's
not
to
say
it's
not
valid
but
say
they've
been
saying.
B
O
Mill,
basically,
it
feels
like
we
said,
should
not
in
2010
before
and
there's
been
plenty
of
time
for
realize
it
to
do
that
and
the
must
2007
so
a
decade
and
the
must
not
language
is
what's
necessary
to
hammer
everyone
else.
It
worked
at
MOG.
Last
month
we
had.
You
know
there
are
three
major
ESPs
who
I
won't
name
in
shame,
but
who
were
still
signing
with
sha-1.
We
talked
to
them
and
they
all
said
with
the
threat
of
D
Krupp
and
must
not
were
just
deprecating
sha-1
language
saying
this
is
coming.
H
On
about
must
not
too
much
longer
about
go
ahead.
Mom,
Thompson,
I
think
in
response
to
these
comments.
The
the
key
thing
here
is
that
the
signature
still
exists
and
it
can
still
be
input
into
things
like
spam,
filtering
and
whatnot,
and
if
we
have
the
right
text
in
the
security
consideration
is
talking
about.
When
this
matters
having
the
headline
is
still
valuable,
I
mean
I.
Think
people
are
asking
for
the
headline
headline
thing
is
going
to
be.
The
body
of
the
document
must
not
blah
blah
blah
and
then
there's
gonna
be
some
deployment
considerations.
P
Coonan
we
had
this
discussion
in
other
working
groups
also
operating
Saarinen,
and
in
most
of
the
case,
you
have
to
understand.
There's
two
different
things
we
are
talking
about
here:
there's
must
not
implement
and
must
not
use.
Those
are
very
different
things
implemented
or
actually
the
vendors
who
make
those
products
they
hate
must
not
implement.
People
task
means
that
they
immediately.
If
they
want
to
be
conforming
it
this
documentation,
they
have
to
remove
the
whole
code,
which
means
that
then
they
can't
have
a
backward,
compatible,
plat
flag.
I
said
oh
yeah,
but
yeah.
P
We
have
to
see
this
product
here
that
doesn't
support
it,
so
we
have
to
have
it
and
they
say
sorry,
we
can't
do
if
it
must
not
implement.
Then
you
can
have.
You
know
like,
for
example,
OpenSSH
has
this,
you
know
if
you
want
user
group
1
and
solve
one,
you
have
to
enable
these
flags
to
be
able
to
use
it,
but
you
can
still
use
it
must
of
use.
Is
okay,
I
think,
that's
that
that's
something
that
we
can
say.
P
But
of
course,
usually
we
don't
give
instructions,
but
you
can
use
because
we
say
that
it's
actually,
you
know
policy
policy
requirements
for
them.
You
know
these
people
who
are
using
it
must
not
implement
is
really
annoying
in
that
sense.
That,
and
if
you
say
oh,
we
can
burst
not
with
some
kind
of
oh,
you
can
use
it.
If
you
want
it,
it
should
not.
It's
not
much,
not
anymore.
Q
Q
L
Kurt
Anderson,
so,
given
that
we
all
realize
that
there's
a
certain
cadence
to
getting
documents
out
and
published
and
and
updated,
maybe
we
can
write
a
timetable
for
moving
through
these
phases
into
the
document.
So,
as
was
suggested,
we
start
off
with
a
must,
not
send,
then
we
add.
Maybe
we
put
a
deadline
next
year.
June
of
2018
must
not
accept
and
we
write
that
into
the
document
so
that
there's
essentially
a
tripwire
in
there
and
Ayana
changes
the
registration
in
June
of
next
year.
That
says,
must
not
accept
in
the
meantime.
C
What
I've
been
hearing
in
the
room
so
far
is
most
people
are
in
favor
of
just
making,
it
must
not
generate,
must
not
accept
all
right.
Let's
take
a
home.
How
many
the
question
is,
how
many
people
are
in
favor
over
the
documents
saying,
must
not
generate
or
accept
and
how
many
people
are
not
in
favor
and
how
many
people
don't
have
enough
info
to
decide.
So,
all
in
favor
all
those
opposed
all
those
who
need
more
information
that
seem
pretty
strong
and
favor
yeah
they're
great
yeah.
J
C
L
R
B
B
No
he'll
be
able
to
hear
that
and
see
the
notes
of
this
or
hear
the
transcript
and
figure
out
what
else
we
discussed,
but
I
I
do
plan
to
get
this
sort
of
last
call
this
fast
as
I
can
reasonably
get
it
done
without
missing
any
important
points.
There's
really
not
much
to
this
left,
the
ECC
I,
don't
think
Scott
is
here.
Is
he
Scott
Rose,
oh
yeah,
I'm?
Sorry,.
S
Hi
I'm
Scott,
Rose,
NIST,
basically,
I.
Don't
think
this
draft
is
needed
anymore
Amy,
because
this
is
for
there's
a
community
out
there.
That
needs
to
also
implement
FIPS
140
stuff.
Having
some
internal
discussions,
it
seems
now
that
there's
actually
a
roadmap
for
this
sort
of
thing
to
get
EB
DSA
into
FIPS
140,
so
things
are
kind
of
progressing
barring
any
kind
of
strange
management
stuff.
So,
in
effect,
the
actual
reason
this
draft
exists
is
gone.
