►
From YouTube: IETF99-TOKBIND-20170717-1550
Description
TOKBIND meeting session at IETF99
2017/07/17 1550
https://datatracker.ietf.org/meeting/99/proceedings/
A
All
right,
so
do
we
don't
like?
We
didn't
actually
include
any
any
updates
on
our
existing
core
documents
on
the
yonder.
That's
because
there
isn't
actually
as
much
to
talk
about
the
core
documents
or
waiting
for
chair
right
up
and
we're
gonna
get
that
to
do
get
to
that
this
week,
and
then
it
goes
into
the
eyes
GQ
and
hopefully,
in
a
couple
of
months
they
will
sort
of
fall
out.
The
other
end
authorities.
B
Yeah
there
are
some
myths
that
I
just
sent
to
the
authors
and
we'll
have
a
meeting
and
make
sure
that
all
the
document
number
is
actually
line
up.
So
the
glue
is
giving
versions
of
all
the
documents.
The
references
actually
corrected.
So
just
a
little
bit
of
cleanup
to
hopefully
make
the
later
part
of
the
process
easier,
epi
est.
A
C
C
D
G
C
Part
of
it,
okay,
so
briefly
for
token
binding
on
TLS
one
point:
three
connections
with
one
or
two
key
connection:
guys
yes,
token
by
nu
for
one
are
TTLs
one
point
three
connections
in
TV
to
go.
We
limited
this
to
TLS,
1.2
and
earlier,
but
like
to
support
TLS
1.3.
There
are
some
really
minor
changes
to
make
I
just
wanted
to
get
feedback
from
the
group.
Should
we
write
up
a
separate
talk
to
be
a
pretty
short
draft?
C
Thank
you
cover
the
changes
needed
for
supporting
token
1.3,
or
can
we
just
roll
it
into
the
existing
draft
that
I've
been
working
on
for
0
Itt
connections?
The
changes
are
on
the
server
side.
The
token
attention
goes
in
encrypted
extensions.
Instead
of
in
server
hello,
we
can
clarify
the
language
that
the
signed
value
is
using
TLS
1.3,
section
7.5
exporters
instead
of
using
the
RFC
4705
language,
and
then,
if
this
is
a
separate
draft,
I
would
just
include
language
that,
since
TLS
1.3
requires
all
new
extensions
to
define
your
interaction
with
0
RTT.
A
J
C
C
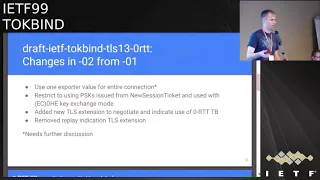
Okay,
next
slide,
so
in
the
tls
1.30
RTT
draft.
The
changes
from
the
previous
draft
are
right.
Now
it
uses
the
same
exporter
value
for
the
entire
connection.
I,
don't
think
this
is
an
issue.
That's
been
resolved
on
the
list
or
in
discussion
here,
so
I
have
a
slider
to
at
the
end,
so
that
we
can
continue
to
discuss
this
issue
in
hopes
of
approaching
consensus
at
some
point,
probably
not
here.
C
I
have
restricted
the
use
of
Zorc
show
combining
two
PS
K's
that
have
been
issued
from
a
new
session
ticket
and
also
the
PS
K
has
to
be
used
with
the
EC,
tht
and
key
exchange
mode.
The
reasoning
here
is
that
a
gasket
from
the
accession
ticket
is
limited
in
time
that
it
can
be
used
for
and
with
the
ECB
s
th
e
key
exchange
mode.
This
means
that
we
should
have
separate
that
we
should
have
a
new
export
value,
that
they're
being.
K
C
On
every
single
connection
we
also
get
out.
I
am
then
there's
a
now
a
TLS
extension
to
negotiate
and
indicate
use
of
0
r
TT
token
binding.
So
it's
just
to
make
it
very
explicit
when
we're
doing
0
r
TT
so
combined
versus
to
a
normal
totem
binding
and
there
was
an
altar
of
after
say
we
play
education.
Extension,
that's
been
removed,
so
next.
L
J
C
C
C
Okay,
so
this
slide
is
basically
an
overview
of
what
the
initial
handshake
looks
like
when
doing
0rc
token
binding
the
client
advertises
token
binding
in
its
client
hello,
the
server
in
its
response
when
it
issues
the
new
session
ticket
I.
This
is
a
server
that
supports
cor
TT
token
binding
issues.
A
new
session
to
go
to
the
early
data
extension
also
issues
the
ticket
with
the
early
token
binding
extension.
C
And
if
the
client
doesn't
support
the
aurochs,
you
show
combining
it's
just
going
to
ignore
the
early
token
binding
extension
in
that
new
session
ticket.
So
next
slide,
we
see
what
this
looks
like
when
the
client
does
not
support
the
ort
token
binding,
but
the
server
possibly
does
the
client
is
going
to
send
so
for
this
example.
C
The
client
includes
token
binding
because
it's
willing
to
negotiate
over
money
for
this
extension
that
has
earlie
data
in
this
example,
because
it's
resuming
a
session
where
token
binding
was
not
previously
negotiated.
So
the
client
has
the
option
of
I
can
resume
a
connection
with
no
token
binding
and
I'm
willing
to
do
that,
because
the
connection
of
the
session
I'm
resuming
had
no
type
of
mining
previously
or
I
can
negotiate
to
a
combining
without
zero
RTT.
C
C
Try
to
do
early
ort
token
binding.
They
would
have
to
have
several
bugs
in
its
implementation
to
do
that.
One
would
have
to
assume
what
mining
parameter
was
being
used
for
that
early
for
that
sorority
token
binding,
and
it
would
also
have
to
ignore
the
must
and
the
spec
of
it
can
only
send
the
early
to
a
binding
extension
if
the
client
completed
its
client
glow.
C
Okay,
next
slide,
so
getting
into
the
tough
that
we
started
discussing
in
Seoul
and
had
a
little
bit's
discussion
on
mailing
lists.
It's
about
searching
exporters
right
now
and
the
dock.
The
current
design
is
that
we
don't
search
any
exporters.
This
is
a
very
convenient
before
doing
HTTP,
because
we
have
a
request
response
pattern
where
and
that
initial
request.
We
have
about
token
that
we
want
there.
C
C
C
J
K
J
J
A
reasonably
low
bar
for
the
canal
system
and
thankfully
we
have
HTTP
and
all
future
protocols,
can
consider
this
in
their
token
binding
use.
It's
not
something.
That's
it's
not
gonna
be
particularly
onerous.
Well,
it's
not
like
there's
a
ton
of
them
out
there
already
using
cloaking
running
and
they
have
to
retrofit
the
zero
ICT
anybody.
Everyone.
J
J
J
C
This
is
sort
of
discussing
the
different
options
for
which
exporter
to
use,
when
the
first
option
in
here
is
what
the
factor
currently
says,
which
is
that
use
the
hey.
If
you
successfully
negotiated
CRC
token
binding
use
the
early
exporter-
and
this
is
one
two
V's
roughly
equivalent
to
using
client
certificates
with
resumption
in
that
the
proof
of
a
possession
of
the
private
key
is
effectively
that
the
client
had
possession
of
a
private
key
at
the
beginning
of
the
initial
session.
You
don't
gain
much
meaningful
contribution
passed
at
that
time.
Point
which
is
fine
certs.
C
One
of
the
other
options
that
have
been
discussed
is
require
that
the
full
strength
exporter
be
used
for
all
children,
binding
messages
that
are
sent
after
the
handshake
is
completed.
This
sort
of
yeah
yeah.
It
still
has
the
early
exporter
in
use
for
the
first
flight,
when
this
pushes
things
as
close
as
possible
in
the
direction
of
security
and
team.
Makoto
Hayden
had
the
biggest
issue
that
I
have
with
this
is.
This
is
both
very
difficult
to
define.
You
could
have
to
a
binding
message
that
is
lit
across
early
data.
C
That's
somewhere
before
and
somewhere
after
they've
covered
some
of
this
and
preachy
presentation,
and
it
also
is
very
difficult
to
open
with
this
do
tubes
layering
of
protocols,
and
then
we
could
also
have
some
sort
of
middle
ground
for
this,
where
the
the
exporter
is
switched
at
some
convenient
time.
That
might
not
be
exactly
when
the
handshake
completes
in
Seoul
I
was
discussing
that
the
clients
wishes
as
soon
as
possible
or
as
soon
as
reasonably
convenient
aid
issue
that
was
brought
up
with
this,
as
the
server
has
no
good
way
of
enforcing
it.
C
A
slight
variant
of
that
could
be
that
the
server
post
handshake
if
the
early
exporter
is
used,
could
just
send
sort
of
a
soft
childhood
at
application-layer.
Reject
it
and
say:
please
try
again
and
then
my
input
is
the
correct,
excellent
past.
That
I
think
some
of
the
switching
exporters
is
something
that
could
move
in
to
win
to
switch
exporters,
someone
that
can
be
moved
into
the
application
for
Ohio,
and
that
would,
in
this
case,
with
the
HTTP
case
of
if
we
use
the
402
early
code,
that
Mark
Thompson
is
proposing
for
zero
RTT.
C
That
in
the
application
profile
of
how
to
do
that
or
if
the
application
is
such
that
there's
no
early
data,
if
there
is
no
bount
opinion
early
data,
then
it
just
says
you
always
use
the
full
strength.
Exporter
I
think
that's
another
option
of
sort
of
move
that
to
the
application
profile.
I.
Think,
though,
that
the
base
year
RTG
token
by
new
craft,
should
have
some
amount
of
guidance
of
what
must
do
at
least
this
much
before.
C
G
It's
about
anger,
I
think
providing
too
many
options
provides
ways
to
screw
this
up
like
even
further,
which
is
just
like
one
I'm,
for
just
using
the
same
mix
for
same
one
for
same
exported
for
zero
are
to
be,
and
one
rqp
data
yeah,
because
you're
you're
willing
to
accept
the
risk
for
Zaraki
data
like
it
doesn't
seem
very
convincing
to
me
that
you
wouldn't
be
willing
to
accept
that
risk
from
one
our
debaters.
Well,
if
you
didn't
want
that,
then
you
would
reject.
F
J
J
J
B
J
Logic,
no,
not
because
there's
something
was
but
because
the
analysis
that
he's
done
and
I've
reached
the
same
conclusions
independently
myself,
which
is
that
this
is
exactly
what
I
coming
a
client
certificate
and,
if
you
think
about
it
in
the
same
terms
as
client
certificates,
you
can
convince
yourself
that,
well,
if
client
certificates
are
busted,
we're
screwed,
if
this
is
positive,
we're
screwed
in
exactly
the
same
way,
there's
been
some
pretty
pretty
good
analysis
of
using
five
certificates.
Thank
you,
and
if
this
is
as
good
as
concert,
if
Achatz
then.
J
Using
blind
certificates,
it's
using
the
one
on
se
to
exporter
is
roughly
equivalent
to
using
a
concert,
difficut
view
provided
from
this
connection.
This
one
is
the
client
certificate
was
provided
on
the
previous
connection,
and
we
have
analysis
of
all
of
these
things
with
TLS
that
works,
and
if
my
equivalence
is
correct,
let's
not,
let's
not
commit
to
that
with
money
or
anything.
C
N
And
Draper
for
Microsoft,
so
the
analogy
with
certificates
is
interesting,
but
I
don't
think
it's
correct,
at
least
in
two
ways.
First
of
all,
client
certificates
authenticate
the
user
where
the
token
binding
just
prevents
replay
of
tokens
hopefully,
and
secondly,
with
client
certificate.
You
know
with
the
client
certificate.
There
is
not
a
replay
problem.
The
way
it
is
the
way
it
exists
was
token
finding,
like
the
reason
we
use
token
binding
is
we
want
to
prevent
replay
and
if
the
play
is
not
prevented,
then
token
binding
is
meaningless.
N
C
L
C
You
know,
second,
is
that
the
using
0rc
joke
mining
isn't
sort
of
prevented
planting
replay
of
minding
doubles,
so
I
think
for
the
authentication
thing
we
don't
have
like
a
find
certificate
that
has
like
a
subject
name
in
it
to
say
who
these
are
is
but
yeah
it
does
say
this
is
the
bed.
This
is
the
public
key.
That's
uses
it
to
use
the
public
key
as
the
ID
I'm
going
to
say
some
server
can
say.
C
Yes,
this
is
the
same
person
that
I
saw
last
time
with
this
public
key,
which
is
sort
of
the
amount
of
identity
that
token
binding
is
dividing
for
replay.
There
is
the
concern
that
0rz
data
can
be
replayed
and
but
I
don't
think
that
token
binding
two
days
took
mining
with
zero.
Rct.
Isn't
designed
to
prevent
this
you're
elected
to
replay
concern
over
TLS.
It
is
what
gets
replayed
is
the
exact
same
application
data?
It
still
prevents
that
token
being
replayed
at
with
other
application
data.
O
And
I
believe
the
reasoning
here
the
same
as
our
or
customer
reasoning
about
the
termination
of
the
TLS
handshake,
which
is
to
say
that
once
the
any
data
which
is
received
using
the
keying
material
after
the
after
the
TLS
handshake
is
completed,
you
have
you
can
retroactively
Lee,
okay
and
that
and
in
any
case,
that
wouldn't
be
fixed
by
changing
the
exporter,
because
the
logic
is
double
same.
So.
A
Q
D
D
D
There's
a
lot
of
proxies
out
there
that
provide
some
meaning
of
communicating
the
concert
if
again
to
the
back
end,
but
they're
all
a
little
bit
different,
and
that
makes
application
development
and
deployment
with
respect
to
trying
to
do
sniffing
it
off
behind
the
front.
End,
really
difficult
or
I
might
say
kind
of
a
pain
in
the
ass
so
and
it
just
happens
to
be
I've,
been
dealing
with
someone
recently
here
and
dear
to
my
heart,
trying
to
solve
that
problem
here.
So
a
little
bit
of
confirmation,
bias
I've
been
out
spreading.
D
D
This
is
your
general
ideas
about
how
to
how
to
convey
the
information
one
is
you
expose
the
token
binding
IDs
to
the
backend
application?
The
other
is
that
you
exposed
the
ekm,
maybe
a
little
other
stuff
to
the
back
enough
occasion,
and
let
it
do
its
thing
I
my
sense
in
the
room
and
soul,
and
maybe
I
was
wrong.
Maybe
it
was
the
the
weather
who
knows
was
that
people
were
preferring
the
ekm
exposure
approach.
So
a
few
weeks
later,
I
wrote
this.
D
This
first
draft
that
did
that
expose
dkm
and
a
couple
other
things
to
the
back-end
application
as
an
HTTP
header
during
that
time
somewhere
to
hide
this
was
nice
enough
to
coined
the
acronym
T.
Trp
will
save
me
a
lot
of
time
typing,
because
I
was
getting
tired
of
finding
TLS,
terminating
reverse
proxy
and
copying
and
pasting
appreciate
ya.
Doing
that.
D
Also
around
that
time,
I
received
some
pushback
both
on
the
list
and
in
person
and
sort
of
asynchronously
office
from
people
that
were
not
really
too
happy
with
the
approach
to
expose
in
the
a.m.
and
and
having
the
backing
up
occasions
do
the
actual
work
of
verifying
the
token
binding
signature,
and
this
was
not
from
theoretical
people.
This
was
from
people
that
were
working
on
plugins
for
systems
that
are
commonly
deployed,
as
reverse
proxies
on
Ingenix
and
Apache,
to
be
specific
and
in
IETF
98
in
Chicago.
We
almost
round
on
the
time
Lafe
lost.
D
My
slides
and
I
gave
a
very
rushed
actually
Bob
still
feels
terrible
of
nervous
and
shaking
rushed
and
incoherent
presentations
in
the
last
five
minutes
of
the
token
body
deception,
and
it
was
also
cut
off
short.
There
wasn't
really
time
for
questions
and
answers,
but
after
that,
I
did
have
a
open
side
meeting
later
that
week
and
we
sat
down
with
a
smaller
group
and
kind
of
talked
to
the
issues,
and
there
was
a
clear
preference
amongst
that
group
to
do
the
other
approach
where
the
TLS
terminated,
reverse
proxy.
D
Little
bit
more
detail
about
how
that
works
defines
HP
headers
that
enable
a
TT
RP
and
a
back-end
server
to
function
together
as
a
single,
logical,
server-side
deployment
of
HTTP
token
bucket.
What
happens?
Is
this
TT
RP
validates
the
total
binding
message
from
the
sect
of
mining
header
that
we're
all
know
and
love
and
removes
it
from
the
dispatch
requests
to
their
back-end
application,
assuming
that's
all
valid
and
all
good?
It
takes
the
provided
token
binding
ID
based
before
URL
encodes
it
and
adds
it
as
a
new
HP
header.
D
D
R
L
L
S
D
A
lot
of
easy
ways
she
accommodated
from
just
writing
it
down,
like
I,
said
before
I'm
also
trying
to
facilitate
something,
that's
very
easy
to
use
a
deploy
in
C
and
that's
to
be
a
profile
that
allows
for
each
vs
token
binding,
which
is
which
is
the
document
that's
about
to
go
up
RFC.
That
only
has
definitions
around
sending
and
receiving
providers.
B
S
D
T
U
U
D
U
D
U
D
O
D
Approach
and,
furthermore,
that
it
wouldn't
it
doesn't
make
sense
to
define
a
security
mechanism
between
these
two
systems,
specifically
for
this
particular
header.
When
there's
other
security,
there's
other
headers,
other
information
being
passed
with
it
too.
That's
already
the
responsibility,
the
front
end,
the
Doosan
sanitation
other
work
and
to
introduce
a
new
share
key
or
some
other
security
function
around
this
particular
portion
seemed.
O
D
The
argument
is,
it's
explicitly
called
out
as
a
must
in
the
standard.
So,
if
you're
going
to
deploy
this,
you
have
to
follow
the
must
I
realize
there's
a
possibility
that
sanitation
you
mess,
but
there's
a
possibility
to
any
security
requirement
in
any
of
these
standards
would
be
missed
and
a
bunch
of
other
people
in
this
room
I
does
at
least
in
my
view,
as
I'm,
trying
to
write
this,
so
it
can
be
deployed
and
used
by
application
providers,
and
it
is
that
that's
consensus.
Okay,.
S
K
A
O
D
K
T
T
O
Suggestion
was
to
establish
a
shared
key
and
Mac
the
data,
or,
for
that
matter,
establish
a
shared
key
and
shove
it
in
the
header
right
in
front
of
it,
so
that,
like
so
like
presents,
the
key
is
required
right
anything
there.
Anything
that
requires
active
participation
by
this
by
this
device,
rather
than
through
how
sue
passenger.
T
D
My
expectation
is
that
that
is
the
case
and
that's
spelled
out.
The
security
considerations
is
that
some
mechanism
there
it
has
to
be
done.
What
I
think
the
argument
is
that
that's
too
passive
and
that's
something
active
specifically
around
these
headers-
should
be
employed
to
make
sure
that
the
TCR
TV
it
doesn't
inadvertently
left.
D
V
J
O
Real
origin,
server,
and
so
but
then
then
the
consequence
is
because
this
is
some
random
new
header.
The
teacher
P
like
T
Derby's,
our
configure
if
they
simply
pass
it
through,
and
so
now
you
the
problem
getting
this
configuration
whatsoever.
This
doesn't
feel
safe
and
so
it's
not
solved
by
having
a
TLS
conditional
if
it's
all
by
its
having
some
mechanism
where
the
T
therapy
specifically
attest
these
headers.
Now
I
hear
you
say
it's
a
V
it'll
be
a
specific
solution
to
this
header,
but
this
is
a
general
problem.
O
O
It
is
to
make
a
generic
generic
fix
for
it
and,
like
so,
to
go
back
to
like
maybe
design
the
microphone,
but,
like
you
establish
a
shared
key
and
then
it
comes
in
a
header
that
is
a
list
of
all
the
headers
that
you
that
you
insert
it
I
mean
like
this.
Is
it
hard
to
solve?
If
you
actually
want
to
solve
it,
suppose
you
want
to.
D
D
But
I'm
just
trying
to
I'm
trying
to
provide
a
workable
solution
within
the
context
of,
what's
already
provided
and
in
around
around
sanitizing
the
specific
header,
the
server-side
deployment,
either
No
about
token
money
or
a
dozen.
And
if
it's
gonna
be
configured
to
do
this,
then
it
has
to
support
this
and
sanitize
these
headers
like.
If,
if,
if
it's
not
doing
this,
then
the
client
can
send
these
headers
and
it
won't
strip
it
and
the
whole
system.
O
D
D
D
D
B
So
I
have
a
question:
is
there
another
working
group?
That's
actually
focusing
on
these
sorts
of
reverse
proxies
where
some
general
solution,
because
this,
whatever
solution,
would
equally
apply
to
TLS
certificates
and
other
things
that
you
currently
are
using
the
method
that
Brian
is
is
recommending
that
I
think
from
a
deployment
point
of
view,
I
get.
What
you're
saying
is
that
for
getting
f5
and
ping
and
everybody
else
who's
making
these
things
to
actually
support
it.
There
should
be
some
general
mechanism
for
H
smacking,
these
headers,
that
this
could
fit
in.
O
Or
something
else
we
invent
well
I,
guess:
I,
guess
I'm,
just
like
I
I,
don't
think
I,
don't
think
I,
don't
think
it's
a
reasonable
answer
to
say
that
it,
because
all
this
all
about
some
other
problem
like
we're
a
problem,
we're
just
gonna,
go
ahead
and
say
that
we
know
it's
not
good.
That's
like
not
like.
D
D
A
Right
I
mean
there
yeah
and
I
was
about
to
alter
that
question,
sir,
so
that
how
many
people
are
on
the
floor
right
now
want
to
talk
about
this
specific
issue
right,
everybody,
okay,
how
about
it?
But
you
know,
let's
keep
we're
gonna
close
to
light
my
clients
after
the
people
who
are
standing
up
and
cleared
or
clearly
indicating
they're
interested
in
to
talk
Mike.
R
Jones
Microsoft
I
failed
to
identify
myself
before
I
was
going
to
respond
to
something
that
was
said
know
15
minutes
ago,
which
is
the
HTTPS
draft.
Only
defines
provided
and
preferred,
which
may
be
true,
but
protocol
defines
sec
token
binding
in
a
way
that
you
could
pass
multiples
and
I
just
want
that
to
be
preserved
through.
D
K
W
Know
just
to
talk
about
that.
Just
to
save
one
thing:
I
think
that
it
is
a
problem.
I've
seen
many
systems,
you
know
not
sanitized
header,
not
this
particular
yet,
but
you
know
this
certificate
header,
it's.
It
is
a
problem.
I,
don't
know
that
you
should
solve
the
described,
but
it's
a
problem.
I
would
like
I,
think
I
think
would
be
good
to
solve,
but
it
would
be
an
improvement
for
the
community
itself.
E
William
Dennis
Google,
all
right,
I
guess
I,
don't
quite
understand
the
concern
here,
because
if
you
have
a
terminating
cellists
proxy
that
doesn't
support
recombining,
it
does
really
not
because
it
doesn't
support
X
money,
I,
just
reverts
to
whatever
we
had
previously.
Where
is
it?
And
if
you
do
then
the
draw
correctly,
then
you
get
to
me,
it
seems
like
yeah
I
would
also
like
to
say
that,
like
from
a
developer
point
of
view,
it's
good
to
create
something
that
I
think
it's
usable
by
pelvis
and
easily
consumer
lines.
E
What
I
really
like
that?
What
your
proposal
is
as
opposed
to
income
share
key
thing,
is
that
it's
actually
gonna
be
easier.
Application
of
all
this
can
actually
get
to
combine
these
so
I
think
that's
a
win
and
I
think
if,
if
there
is
always
a
more
people
deploy
to
our
mining
with
a
mile
risk
that
if
the
scene
seems.
G
D
B
X
All
talk,
Mike,
I,
think
eckers
comment
about
well,
you've,
already
trusting
this
server
with
your
private
key.
You
should
therefore
be
willing
to
just
have
a
shared
secret
with
it.
I
think
that
shows
the
impedance
mismatch.
These
entities
behind
these
accelerators
and
off
loaders
are
trusting
their
private
key
they're
having
somebody
else.
Do
all
the
nasty
work
for
them,
so
they
can
just
concentrate
on
the
business
thing
and
they'll
do
IP
level,
routing
and
IP
level
access.
And
yes,
it's
not
great,
but
I
think
this
as
suspect.
X
A
Was
that
an
argument
that
you
know
so
I
guess
the
question
I
was
gonna
I
wanted
to
ask
you
know
both
occur
as
a
DM
and
implementers
of
proxies
is
whether
you
know
a
you
know.
If
you
were
given
the
choice
of
saying
you're,
you
know,
because
you
know,
as
I
I
think
Ecker
is
telling
us
as
ad
that
there's
okay,
you
know
all
right.
A
Oh
that's,
fine!
All
right!
Fine.
What
I
heard
was
that
there
is
significant
risk
in
the
IDF
process
for
food
for
this
thing
going
forward.
If
we
don't
provide
enough
security
to
protect
the
habit
right
and
if,
if
that's
true,
we
might
wind
up
in
a
situation
where,
as
implementers
you'd
be
to
be
presented
with
the
choice
of
either
implementing
a
shared
secret
scheme
to
protect
the
other
or
parsing
the
parsing,
the
ECAM
all
right.
O
A
J
Thomson
I
think
a
lot
of
this
is
sort
of
concentrating
on
the
the
challenge
of
doing
this
and
you're,
making
it
a
lot
harder
than
it
actually
needs
to
be
so.
The
load
balancer
is
already
doing
this
till
I
say
export
of
thing,
and
it
does
have
a
shared
key
with
the
back-end
server,
which
is
the
shared
secret
that
I
negotiated
with
the
TLS,
and
it
can
use
TLS
exporters
and
use
that
to
protect
these
things,
and
there
is
no
way
that
the
the
client
could
produce
anything
on
its
leg.
J
D
X
Do
any
right
dog,
it's
all
to
you,
yeah
many
people
do
do
this,
but
most
people
buy
these
things,
so
they
don't
have
to
worry
about
that
and
they
put
the
boxes
or
the
reverse
proxies
in
their
DMZ
and
they
have
IP
firewalls
and
they
trust
that
that's
going
to
be
enough
to
Munsen.
Once
the
TLS
connection
is
terminated,
plaintext
in
the
backend,
it's
really
not
great
your
mom,
it's!
We
would
all
find
it
really
really
horrible
and
stupid.
G
B
G
G
L
O
I
mean
William
asked
how
you
in
this
situation,
it's
really
quite
simple:
you
have
a
network
of
load
balancers,
some
of
which
support
this
wrapping
so
quickly.
Not
it
will
conserve.
Risk
all
would
support
this
draft
and
the
servers,
your
confusion,
think
the
old
web
else
and
that's
Hagen
this
trick
and
like
I
I,
can't
tell
you
many
conversations
we've
had
in
TLS
about
about
about
like
data
centers
are
partially
configured
in
odd
ways
and
like
we
just
were
into
exactly
the
situation
like
you
know.
O
Maybe
I
want
been
a
half
ago
with
a
descended
over
surfing,
like
half
bogus
OCSP
responses.
So
it's
like
incredibly
easy
to
get
in
the
setting
where
your
datacenter
is
partially
misconfigured,
so
I
mean
I
mean
again
like
you
know,
it
may
be
the
case
that
this
consider
decision
does
not
work
going
with
this
case,
but
it's
like
not
the
cases
can't
happen
so.
A
Let's
see
if
I
can
dig
us
out
to
this,
so
so
so
if
I
interpret
Brian's
sort
of
position
is
that
we've
got
security,
consideration
language
that
says
you
must
solve
this
in
some
way
your
Morton
saying.
Well,
there
is
an
easy
solution.
If
you're
actually
doing
T
less
on
the
inside-
and
you
know,
can
we
get
that
SPECT
out
somewhere?
You
know
in
a
venue
in
a
group
in
in
it
and
somewhere
in
the
iTap,
where
you
get
work
right
will
actually
get
good
review
and
good
feedback
from
implementers
I.
O
O
A
D
It's
not
normal
and
I
summarized
the
results,
and
if,
if
there's
another,
a
working
group
wants
another
solution,
I'm
happy
to
incorporate
that
I
personally,
don't
feel
it's
appropriate
or
necessary,
though
I
do
understand
your
concerns.
I'm
trying
to
keep
this
simple
and
deployable
and
I
would
like
for
it
to
be
available
in
a
time
frame
that
allows
for
adoption
somewhat
coincidental
with
the
actual
audit
open
body.
D
That's
my
goal
here
and
yes,
we
could
do
all
kinds
of
ukm
things
between
the
back
end
in
the
front
end,
but
it
turns
out
that
getting
access
to
an
exporter
isn't
actually
supported
on
a
lot
of
platforms
and
that's
one
of
the
difficulties
of
deploying
to
a
component.
So
if
you
move
that
requirement
to
the
backend
application
in
order
to
support
being
simple
behind
the
TLS
term
and
reverse
proxy,
then
you're
not
going
to
get
deployment
of
it.
D
A
We
were
gonna,
be
s,
we're
absolutely
gonna,
discuss
adoption
right
then
this
may
I
think
it
makes
sort
of
that
discussion,
maybe
a
little
bit
easier,
but
I
don't
think
it
really
matters
whether
this
is
a
working
group
document
or
not,
because
people
are
going
to
implement
these
kinds
of
things,
whether
we
like
it
or
not,
right
so
I
think
it's
about
sort
of
providing
them
with
the
good,
safe
tools
that
we'll
choose
to
make
make
good
choices.
I
mean
sane.
A
A
K
O
O
A
A
O
V
Kill
Chikara
cool
so
just
to
kind
of
advocate
this
patient.
Why
we
abundant
p.m.
since
I,
don't
need
friends.
One
thing
is
that,
with
this
approach
you
just
need
to
support
binding.
Then
you
know
three
or
four
proxies
and
not
another
welfare
evolves,
because
otherwise
science
need
to
do
it
and
beers.
V
L
E
Mean
to
me
that's
kind
of
a
bunch
draw
lap
and
I
guess:
I'm,
not
convinced
that
that
we
that
we
should
actually
add
complexity
to
sort
of
solve
that
and
I
think
the
cost
of
doing.
That
is
that
we
actually
make
it
a
lot
harder
on
the
people
that
will
implement
this
in
their
applications.
So
personally,
I'd
rather
see
all
the
complexity.
In
kind
of
you
operate.
E
Dhatus
and
operator
level
so
that
the
applications
have
the
easiest
time
possible,
integrate
and
I
know
for
us,
like
it's,
not
gonna,
be
a
problem
rolling
this
out
like
if
we,
if
we
do
roll
it
down
rolling
it
out,
everyone
go
to
the
entire
night
l7,
but
balance
of
class
I
don't
see
any
issue
with
that.
So
I
guess
like
if
even
tonnison
operate.
It
he's
at
risk
of
watching
this
than
the
risk
of
watching
it.
Maybe
they'll
watch
something
else
to
me.
That's
not
a
reason.
You
know
itself
to
make
your
sake
understand.
H
H
A
Absolutely
but
but
I
think
it
it
actually
helps.
If
we
have
concrete
proposals
on
the
table
and-
and
you
know,
Brian
has
a
point-
people
will
deploy
these
things
without
TLS.
It
doesn't
really
matter
what
we
say:
they
must
do
or
not.
I
think
I
will
do
it
and
I
think
the
best
way
again.
The
best
thing
we
can
do
is
to
provide
them
with
good
tools,
so
they
can
do
like
a
half.
Have
a
safe
deployment
of
these
things
right
and
to
me
it
sounds
like
Martin
has
proposed
it.
D
D
J
Thompson
I
agree
with
this.
If
it
can't
use
the
information,
don't
give,
it
is
basically
good,
I
agree
totally
I,
don't
think
anyone
if
someone
can
come
up
with
a
case
for
passing
more
information
than
you
should
make
more
fields
for
passing
more
information,
myk's
myk's
example
of
multiple
token
binding
ids
is
is
fine
and,
I
think
that's
a
reasonable
request,
but
he
is
asking
for
more
token
binding,
ids
he's
not
asking
for
division,
token
binding
message
or
the
extensions
or
anything
like
that.
J
U
So
just
this
formulation
that
makes
it
a
little
bit
word
Terp
required
to
sanitize
headers.
So
does
it
mean
that
there
are
no
way
for
the
application
to
know
securely,
that
the
information
comes
from
the
teat
ERP
and
not
is
something
forwarded
that
for
United
for
the
blind,
or
is
it
a
way
to
to
just
pass
information
in
Hawaii
that,
even
if
the
TTR
p
does
not
sanitize
anything
or
completely
messes
up
or
fails,
the
application
will
know
that
this
information
people
are
originated
from.
D
S
D
D
F
D
D
Know,
there's
there's
some
other
applications
on
this.
There's
an
area
in
go
off
where
the
top
combining
ID
itself
is
used
in
vaults.
Yeah
I
cannot
finish
the
feedback
that
that's
not
set
in
stone.
You
can
eventually
change,
but
the
ID
itself
seemed
like
the
most
appropriate
thing
to
expose
to
the
back.
Certainly
it
could
be
some
hash,
introduce
the
need
them
for
help
for
the
mobility
which.
B
Right,
so
it
seems
that
the
back
end
needs
to
know
the
token
binding
ID.
What
the
token
binding
type
is
provided
referred
or
some
extension
are
essentially
the
two
things
that
the
back
end
needs
to
know.
So
I
guess
the
discussion
with
Mike
is:
how
do
you
communicate
what
that
extension
is
because
it's
not
positional,
like
the
first
token
binding
versus
the
second
token
binding
in
the
header,
doesn't
actually
mean
anything.
There
is
some
sort
of
register
a
new
token
binding.
D
D
C
Nick
over
in
the
token
binding
message
you
can
have
token
bindings
different
types
like
provider
to
further
types
that
happen,
define
sure
that
you
can
have
a
type
repeated
multiple
times,
so
you
could
have
I
think
we
require
that
there's
only
one
provided,
but
you
could
have
a
list
of
multiple
referred
to
and
II.
In
that
case,
I
don't
know
if
any
mutations
care
about
the
positions
of
those
the
message
getting
back
to
Martin
some
like
earlier.
If
you
have
most
worker
types,
that
Hydra
could
just
be
those
IDs
separated
by
a
comments
to
support.
D
At
least
with
respect
to
multiple
refer,
I,
don't
recall
if
that's
allow
that
at
this
the
HTS
layer,
but
if
it
is
positionally,
there's
no
distinguishing
I
mean
there's
I,
don't
know
actually
to
be
honest,
I,
don't
know
I'm
happy
to
look
at
solutions
for
it
looks
and
help,
but
look
opposed
sucks,
but
I
really
want
to
avoid
complicating
the
it's,
not
the
80/20
rule.
It's
probably
the
99.
R
L
D
D
D
D
D
D
I
still
believe
that
the
problem
itself
is
very
important
for
us
to
provide
some
kind
of
implementable
solution
for
people
to
do
rather
than
leaving
it
up
to
themselves.
I
suppose,
there's
a
couple
questions,
whether
it's
this
approach
or
the
old
PM
approach,
I
feel
like
there's
consensus,
more
consensus
for
this
approach.
There's
considerations
around
additional
to
a
combining
types
which
I
think
we
can
get
to
in
in
whatever
approach
would
take
and
then
there's
questions
regarding
the
security
model
of
protecting
these
particular
headers,
which
I
don't
on
my
position.
D
A
I
mean
in
process
wise
core
adoption
is
you
know
it
means
you
turn
over
change,
control
to
the
working
group
so
and
we've
already
established
consensus
that
the
working
group
thinks
that
this
this
problem
space
is
worth
working
on,
and
so
we've
done
that
already
so
I
guess
it's
time
to,
and
it's
appropriate
at
this
point
also
for
adoption.
If
you
hear,
if
you're
comfortable
with
that,
we
can
do
that.
A
A
Alright,
so
who
hummmm
now,
if
you
believe
that
it's
appropriate
for
the
working
group
to
adopt
this
as
working
your
token,
all
right
now
now,
if
you
do
not
believe
it's
appropriate
third
of
this
document
as
a
working
you're
talking,
it's
pretty
is
pretty
straightforward,
so
resubmit
as
working
of
talking
until
Excel
fun
yeah.
We
can
do
that
and
we
will
will
confirm
on
the
list.
A
A
U
You
know
so
we
don't
have
many
minutes
left,
but
still,
as
we
talked
about
before,
is
the
considering
maybe
for
this
group
to
look
into
whether
to
combine
and
should
be
defined
for
sam'l
and
whether
that,
what's
the
best
place
to
do
it.
Yes,
if
it's
worth
doing,
will
it
be
implementing?
It
makes
sense
in
many
ways
to
do
to
combining
for
Sam
well,
instead
of
just
doing,
clients
authenticate
the
TLS,
which
is
done
in
many
of
the
higher
level
trust
my
word
for
sam'l
I
could
tow
combining
be
used
for
sam'l.
