►
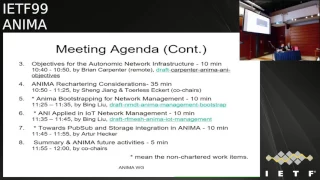
From YouTube: IETF99-ANIMA-20170719-0930
Description
ANIMA meeting session at IETF99
2017/07/19 0930
https://datatracker.ietf.org/meeting/99/proceedings/
B
A
C
A
B
A
It's
time
for
just
for
us
to
start
the
session.
This
is
the
animation
in
i99.
So
if
you
happen
to
be
in
the
wrong
session
wrong
room,
you
still
have
time
to
leave.
If,
if
you
are
here,
you
know
right
working
group,
please
make
sure
you
sign
your
they
blue
sheets
before
you
left.
This
is
not
waiver
ITF,
and
everybody
should
read
that
if
you
don't,
please
make
sure
you
with
that
afterwards
before
began
meetings,
we
already
Sinatra
plushies
and
we
need
a
job
scraper.
Anybody
weren't
here
well
job.
A
Okay,
who
could
be
right
here
for
me?
It's
taker,
P,
yeah,
I'm,
sure
this
will
watch
you
when
you
make
the
presentation.
Thank
you.
We
have
the
remote
participation.
There
are
four
on
the
remote
site.
Brian
will
makes
this
presentation
from
remote
and
our
side
of
the
earth,
New
Zealand
and
all
those
slides
have
been
uploaded.
Well,
he's
just
did
it
now
and
the
mailing
list.
We
have
the
minister
young
with
a
lot
of
discussions
and
decisions
here,
time,
machine,
John
and
theorists
acre.
A
A
We
started
to
put
in
more
time
along
by
Jefferson
and
we
are
going
to
talk
a
little
bit
regarding
to
the
objective
for
the
a
I
parameter
to
its
remotely
and
the
I
actually
assigned
35
minutes
to
myself
for
the
animal
chattering
considerations,
and
after
that
we
have
three
topics
which
never
be
discussed
in
a
a
working
group.
Yet
so
that's
new
work
proposed
animal
trapping
for
network
management
and
apply
a
I
island
at
work.
A
A
E
A
F
A
So
we
plan
to
send
the
document
to
is
G
by
the
probably
next
week
and
the
two
partition
use
case,
which
was
a
true
for
for
a
while,
but
waiting
for
the
grasps
will
get
clear
so
the
profit
management
past
working
coke
last
call
this
mas.
It's
in
Shefford
letting
up
and
the
staple
connectivity
draft
him
is
currently
in
working
class
Co.
A
G
G
G
So,
as
Shane
said,
the
remaining
discuss
palettes
have
been
cleared
for
version
15
I
apologize
that
version
15
was
only
posted
this
week
that
the
deadline
quarters
we
already
have
multiple
are
assigned
caught.
7017
now,
I
think
that
the
multicast
addresses
will
be
assigning
the
right
away.
As
soon
as
the
is
gia
approval
notice
goes
out
which
I
guess
it's
need.
Someone
to
press
a
button
and
just
the
other
comment
is
that
there
are
two
normative
dependencies
on
drafts
in
the
document
which
will
have
to
be
cleared
before
the
RFC
can
actually
come
out.
G
G
From
a
practical
point
of
view,
the
most
important
thing
was
the
first
one,
which
is
the
testing
that
bill
Atwood
was
doing
remotely
at
home,
told
me
that
there
was
some
issues
in
the
details
of
the
discovery
timeouts
that
needed
to
be
better
specified.
So
that
was
the
important
change
in
from
a
practical
point
of
view.
Then
we
basically
rewrote
the
a
lot
of
the
security
text
and
the
text
about
transport
layers.
G
G
There
are
three
related
drugs
and
the
API
draft
and
the
draft
on
guidelines
for
writing
essays,
but
they're
issues,
I
think
for
the
recharter.
But
we
really
need
people
to
read
them
and
comment
them.
Guess
I
think
they
will
be
very
helpful
to
implementers,
even
if
they
don't
become
standard,
strapped
documents,
and
the
third
related
draft
is
on
the
agenda
later,
so
I
won't
spend
any
more
time
on
it.
G
There's
one
prototype
which
I
moved
recently
to
get
up,
but
with
the
real
next
step
is
we
need
production
quality
code
and
we
need
interrupts
testing
I'm
sure
that
when
we
do
that,
we'll
find
some
errors
and
some
extensions
that
we
need
in
gross.
But
we
can't
do
that
until
people
start
using
it.
So
really,
that's
that's
my
most
important
point
that
we
need
people
to
write
code
and
come
to
a
hackathon
in
future
to
test
it,
and
next
slide.
I
think
is
where
I
asked.
If
there's
any
discussion.
E
Hi
Brian,
it's
Michael
Richardson
about
your
ni
objectives
document.
My
understanding
is
that
the
purpose
of
this
document
is
to
kind
of
collect
some
of
the
objectives
and
some
of
the
things
into
a
single
place,
so
that
people
can
kind
of,
compare
and
contrast
them
and
see
both
the
consistency
of
them.
Some
other
people
have
been
treating
it
as
canonical
versions
of
what
the
documents
actually
should
have
and
I
thought
of
it,
as
the
other
way
around
is
that
the
documents
have
stuff
in
them
and
this
simply
collects
them,
can.
F
D
Good
morning,
working
group
glad
to
see
my
co-author
max
is
on
online.
Keep
me
honest,
so
this
is
the
update
to
the
voucher
draft
next
slide,
please
so,
as
recap,
at
ITTF
98,
we
presented
the
voucher
document
so
having
just
a
few
open
issues
remaining
with
an
expectation
you
ready
for
last
call
within
a
few
weeks.
Of
course,
that
dragged
on-
and
here
we
are
now,
but
we
are,
as
just
mentioned
post
last
calls.
So
hopefully
this
will
go
through
very
quickly.
D
D
Okay,
so
also,
this
version
opens
the
possibility
that
alternative
sure,
artifact
signing
structures
may
be
signaled
by
external
mechanisms.
So
currently
the
the
document
says
it's
pkcs7
or
CMS,
but
in
the
future
it
may
be
desired
for
it
to
be
JD,
JD
s
or
CD,
WS
and
and
the
so
the
document
language
was
reworded.
So
as
it
wasn't,
you
know
exclusively
saying
it
had
to
be
pkcs7
next,
it
I'm
sorry
I'm
in
number.
Three
number
three
introduces
it.
This
version
introduces
a
flag
for
the
voucher
to
signal
the
pledge
that
it
must
fail
close
so.
D
When
the
voucher
itself
may
have
stapled
to
it
and
I
think
actually
it
might
be
number
six
here
stapled
to
it,
a
all
the
intermediate
certificates
that
it
was
signed
by
and
and
also
number
seven
it
has
the
relic.
Also,
potentially,
the
revocation
objects
stapled
to
it
or,
alternatively,
the
pledge
could
dynamically
fetch
the
revocation
objects.
D
But
the
question
here
is
for
whether
or
not
what
does
the
pledge
do
if,
in
the
case,
that's
not
able
to
get
the
revocation
objects,
does
it
fail
open,
fail,
close,
and
so
here
we
have
introduced
a
flag
to
state
definitively
that
it
must
or
not
they'll
open
or
close
for
we
added
the
proximity
assertion
type.
So
previously
he
was
always
verified
or
logged,
and
now
we
have
proximity.
So
proximity
was
added
specifically
to
support
the
notion
of
the
voucher
requests.
D
We
did
also
remove
the
domain
certificate
identifier,
because
now
the
pen
domain
certificate
is
used
exclusively,
meaning
that
we
no
longer
have
this
potential,
like
an
algorithm
for
having
to
discover
which
of
the
sub
certificates
are
CAS,
are
being
used.
That
can
be
verified.
Sorry,
that's
not
very
easy
to
express
alright,
so
I
already
talked
about
6
&
7,
so
we
can
go
to
the
next
slide
already.
D
There's
only
one
open
issue
and
I
mean
I
know
we're
post
last
call,
but
this
is
on
github
so
and
maybe
max
who's
online
can
speak
to
this
as
well,
but
the
the
github
issue
is
whether
or
not
we
should
have
mandatory
or
optional
fields.
So,
currently
the
the
voucher
structure,
you
know
it's
being
defined
using
yang
and
in
yang
there's
certain
Leafs
that
are
mandatory.
D
True,
so
the
value
is
always,
you
know
they
must
be
specified
all
the
time,
but
when
the
voucher
structure
is
being
used
for
requests,
those
fields
don't
make
much
sense
like
you,
wouldn't
necessarily
you
know
they,
you
wouldn't
propagate
them,
necessarily
from
pledge
to
registrar.
So
what
do
we
do?
So
we
have
a
few
options.
One
is
to
fill
in
dummy
values
for
the
mandatory
fields.
D
E
Let
you
finish
your
sentence:
was
it
any
thoughts?
Well,
I
have
thought
on
this
topic,
but
I
can't
she
seems
microphone
on
a
different
topic.
So
my
question
is:
is
it
possible
for
us
to
write
in
a
yang
extension
that
then
marks
them
as
as
optional
like
an
enclosing
or
a?
What
is
it
whatever
the?
What
was
the
thing
we
changed
it.
We
changed
the
anger
that
we
could
include
it
as
it
include
an
augment
and
stuff
like
that
right,
a
grouping
we
added
the
grouping,
so
we
could
do
that.
E
D
E
E
Okay,
that
I
think
that's
what
we
have
to
do,
which
is
unfortunate,
because
I
think
it
means
that
we
can't
use
as
much
of
the
yang
structure
to
say
whether
or
not
it's
valid
or
not
right,
because
we
want
to
reuse
the
object
twice
and
it
has
different
rules
in
each
place.
Right
I
mean
it's
not
my
preference
personally.
D
E
B
It's
not
fully
specified
there
and
we
kind
of
finish
that
specification
in
Bruschi,
because
that's
the
only
place
it
seems
we
need
it.
While
we
think
that
reusing
the
voucher
itself
across
you
know
multiple
protocols,
so
you
know
whatever
gets
it
out
fastest
and
I.
Think
I,
like
the
idea
to
be
you
know,
use
as
much
of
the
yang
structure
to
indicate
what
what
needs
to
be
in
something,
and
you
know
if
we
make
everything
you
know
optional,
then
it's
you
know
by
far.
Not
you
know,
semantically
as
strong.
D
E
E
F
Cross
group
involvement
is
pretty
important.
I
would
think
you
to
do
another
working
loop
group
last
call
I
think
is
sensible,
but
and
if
it
happens
quite
often
actually
in
the
IETF,
where
working
groups
do
multiple
last
calls,
it
gives
the
opportunity
for
those
other
areas,
those
other
working
groups,
to
be
made
well
aware
that
you're
doing
it
again,
because
you
found
significant
issues
and
you
really
really
really
want
the
feedback
from
those
groups.
So
please
do
another
one.
E
A
F
D
E
Next
slide,
please:
no,
the
rent,
monitor
works
first
time,
so
in
April
max
did
a
whole
lot
of
heavy
lifting
and
essentially
took
80%
of
the
document
and
threw
it
into
an
appendix,
and
then
then
we
garbage
collected
right.
We
pulled
back
all
the
pieces
that
we
we
clearly
needed
and
move
things
around
into
a
different
order,
and
you
can
see
the
difference
in
in
the
URL.
If
you
want
to
go
to
the
diff,
it's
pretty
pretty
pretty
good
and.
E
That's
what
we'd
really
like
to
hear
and
there's
still
stuff
in
there
that
we're
how
we'd
say
we
have
some.
We
don't
know
what
exactly
where
to
put
yet.
Sometimes
documents
need
just
you
need
to.
They
need
to
percolate
in
your
head
a
little
more
next
slide.
Please!
So
a
little
bit
more!
You
know
kind
of
detail
what
we
did
previously
we
explained
you
know
we
had
these
sections
called
behavior
of
a
pledge,
behavior
of
a
this
behavior
of
that.
E
You
know
about
one
section
we
would
say
behavior
the
Registrar,
then
we'd
say
something
about
the
pledge
and
it
went
back
and
forth,
and
so
we
had
actually
already
violated.
That
kind
of
principle
of
you
know.
You
only
know
what
you're
doing
and
you
just
react
to
what
other
people
inputs
there.
So
that's
why
we
said.
Okay,
look
we're.
Obviously
we
want
to
write
the
document.
The
other
way
around
the
other
way
around
is
to
say
the
time
sequence
of
of
you
know.
E
First,
you
go
to
the
store
and
then
you
buy
your
groceries
and
then
you
walk
home,
and
then
you
do
this
stuff
as
opposed
to
the
store
experiences
a
customer
coming
in
and
leaving
right.
So
that's
why
we
rewrote
it
there.
Two
different
styles
you'll
see
them
both
in
the
ITF.
So
that's
the
new
protocol,
section
3
and
it's
organized
by
the
time
sequence
of
the
steps
that
I
need
to
occur
and
that
seemed
to
explain
to
most
too
many
people
much
better
as
to
what
the
flow
of
the
whole
process
is.
E
It's
probably
worse
off
from
the
point
of
view
of
somebody
who
has
been
assigned
the
job
of
writing
a
registrar
without
knowing
anything
about
any
other
pieces
right.
So
that's
a
worse
experience
for
them.
They
have
to
learn
what
everyone
else
is
doing
in
order
to
figure
out
what
they're
doing.
On
the
other
hand,
it's
much
more
clear
that
the
protocol
sticks
together
and
that,
if,
if
the
customer
wants
to
go
to
the
store,
the
store
is
willing
to
accept
the
customer.
E
That's
the
kind
of
process
so,
as
I
said,
shrunk,
454
pages
to
42
pages.
Most
most
people
think
shorter,
shorter
documents
are
better
and,
as
I
said,
I
actually,
in
the
left
hand,
side
I
actually
had
to
cut
out
quite
a
few
lines
of
the
table
of
contents
and
make
it
fit
on
the
slide.
Some
of
the.
So
that's
that
itself
should
tell
you
something
next
slide.
Please
technical
changes.
E
So
essentially,
prior
to
this
point,
you
would
send
some
if
you're
the
Registrar,
the
pledge,
you
would
say-
hey
I'm
a
pledge
and
here's
some
Jason
with
my
serial
number
and
if
you're
the
Registrar.
You
then
say:
oh,
thank
you
very
much.
I'll
talk
to
the
Massa
and
I'll.
Ask
the
Massa:
hey
I
had
a
serial
number
I'm
this
guy
and
what's
going
on,
and
then
you
get
a
voucher
response,
and
so
he
realized
this
was
a
kind
of
little
bit
disorganized
and
ad
hoc.
E
So
instead,
what
we're
doing
is
the
Pledge
actually
says:
here's
a
voucher
which
I
could
optionally
sign.
That's
my
key
if
I
have
lots
of
CPU
around
and
it
contains
yes,
my
serial
number
and
maybe
a
couple
of
things
that
matter
and
the
Registrar
says.
Oh
thank
you
very
much
and
actually
can
turn
around
and
say
to
the
massa.
Here
is
a
I'm
going
to
sign
this
voucher
like
object,
and
this
is
kind
of
what
I
want
I.
E
E
No
that's
right,
the
Registrar
may
send
a
new
voucher
could
be
signed
by
the
pledge
have
inside
of
that
voter
request
is
a
voucher
that
was
signed
by
the
pledge,
so
there's
a
kind
of
recursive
thing,
so
you
can
always
put
a
another
voucher
inside
of
your
voucher
when
you're
doing
a
vote
for
requests.
That
says
you
know
what
I
got
this
thing
previously
or
I
received
this
thing
from
the
pledge
and
you
from
the
syntax
in
the
yang.
E
We
can
go
as
deep
as
you
like,
and
there
may
be
some
logic
to
do
that,
although
semantically
I
don't
think
we
have
a
syntactically,
that's
allowed
a
semantically,
it's
not
clear
that
it
makes
sense
to
have
more
than
more
than
two
embedded
objects
there.
But
essentially
it
says
you
know
you.
Basically
what
you're
doing
is
you're
walking
to
the
passport
office.
You
say:
here's
a
reverse
certificate,
here's
my
stuff
and
here's,
my
previous
pass
or
in
case
that
makes
it
faster
for
you
to
look
up
my
details
and
issue
me
a
new
one.
Okay.
E
So
in
the
second
think
case
about
to
renewal,
that's
exactly
what
we're
doing
cuz.
What
we've
said
now
is
that
we
no
longer
expect
to
have
long-lived
vouchers.
Instead,
we
expect
to
have
rather
short
vouchers
that
you
can
renew
in
a
non-contiguous
fashion.
So
if,
for
some
reason
you
got
a
voucher
for
a
device
and
you
didn't
use
it
immediately
and
it
expired
because
it
was
only
good
for
20
minutes.
Let's
say
you
can
come
back
three
days
later
and
say:
here's
the
voucher.
E
You
gave
me
three
days
ago,
I'd
like
you
to
renew
the
same
thing
and
the
mass
is
gonna
say
yeah,
you
know
what
that's
pretty
good
I,
don't
see
any
things
changed
in
the
world,
so
here's
a
refined
thing.
It's
also
good
for
twenty
minutes,
go
for
it
and
that's
it
oh
and
I
validate
it
when
it
does
this.
E
Of
course
it
validates
all
if
make
sure
that's
no
revocations
or
anything
else,
that's
happened,
and
so
that's
why
that
the
period
of
the
voucher
is
relatively
short,
because
that
gets
a
round
of
us
ever
having
to
revoke
them.
They
expire
on
their
own
and
on
the
right-hand
side
and
the
voucher
signed
by
mass.
E
So
you
see
a
little
purple
box
and
that's
that's
the
registrar's
public
ID,
so
I
try
to
keep
the
colors
consistent
there,
so
that
essentially
means
that
the
the
voucher
now
has
pinned
the
identity
of
the
of
the
registrar
and
has
done
this
pretty
much
pretty
typically
by
the
last
certificate
or
in
my
I
would
like
to
say,
publish
I'll,
even
self
signed
certificate
of
the
registrar.
So
that
means
the
pledge
doesn't
have
to
have
a
big
long
chain
of
certificates
or
anything
else
to
it
to
validate
things.
E
That
is
doable,
but
we
realize
that's
not
so
easy,
so
this
business
now
of
having
the
Registrar
actually
signed.
The
voter
request
now
says,
and
the
Registrar
saying
this
is
the
identity.
I
want
you
to
issue
to,
because
this
is
the
signature
on
it.
So
that's
much
simpler,
it
doesn't
depend
upon
Els
client
certificates
in
particular.
It
also
means
that
the
entity
doing
the
the
entity
in
the
registrar
that
reaches
out
to
the
masa
no
longer
has
to
have
access
to
the
registrar's
private
key
to
make
the
tls
request.
E
E
So
we
did.
We
did
settle
after
a
long
discussion
through
mostly
the
winter
before
the
last
ITF
and
at
the
last
ITF
I
guess
we
were
really
still
sitting
on
the
fence
as
to
whether
or
not
we
were
going
to
jump
from
pkcs7
saw
seven
sign
Jason
to
JWT,
okay
and
I
would
say
that
we
decided
not
to
step
forward
on
that
at
this
time.
E
So
we
can
do
it,
so
we
could
move
to
a
Jose
signed
Jason
which
might
be
is
almost
but
not
quite
JWT,
or
we
can
move
all
the
way
to
JWT
and
we
can
move
all
so
we
can
move
to
two
CWT
caught
shot
and
caught
I
find
if
I
pronounce
them
shot
and
caught
for
people
that
never
heard
of
them.
They're
like
what
what
are
you
talking
about?
You
just
need
to
be
a
little
Welsh
to
understand.
W's.
E
Have
our
vowels
go
talk
to
those
guys,
I
think
it's
a
hilarious,
but
so
the
Registrar
needs
to
be
aware
of
all
the
formats
that
we're
going
to
create
okay.
If
the
Registrar
wants
to
audit
and
they'll
process
we've
we've
created,
it
has
the
Registrar
signing
these
objects.
The
Registrar
needs
to
know
what
they
are.
So
if
we
have
six
different
formats,
registrar's
are
going
to
have
to
support
six
different
formats.
E
Masses
and
pledges,
however,
which
are
created
by
the
same
vendor
manufacturer
support
one
okay.
So
if,
if
you
are
dealing
with
a
constrained
or
a
small
device,
you
don't
have
to
support
six
different
voucher
formats.
You
pick
one
okay
and
that's
it
and
as
the
Massa
as
the
manufacturer
you
decide,
my
pledges
will
have
JWT
s.
If
that's
what
we
move
to
and
the
Massa
says,
I
support,
JWT
s
and
that's
a
manufacturing
time
decision
that
you
make
and
you
hope
the
Registrar
support
them
before
you
deploy
I
guess
so.
E
The
Registrar
is
the
guy,
that's
in
the
hot
seat
and
the
rest
of
them
are
are
driving
or
can
you
know
have
to
wait
for
the
Registrar
support?
But
again
it's
not
a
negotiation.
There's
no
back-and-forth,
we
don't
say
oh
I
have
to
convert
this
and
that
pledge
supports
with
the
pledge
supports
and
the
Express
is
that
he
does
that
next
slide.
Please
I
put
a
questions.
Comments
here
and
I
have
a
couple
of
another
slide
after
that,
because
I
thought
it'd
be
good
to
stop.
Here.
E
F
H
E
A
E
Have
done
that
we've
stopped
using
your
design
team
mailing
list.
Okay,
so
you'll
see
it
all
on
the
main
list.
I
thought
the
contents
of
our
our
meetings
that
the
notes
we
keep
from
our
needs.
We
actually,
we
actually
lined
up
basically
arguing
text
in
the
ether
pad
and
then
we
wind
up.
You
know
summarize
that
the
the
summarize
the
reason
for
the
argument-
yeah.
H
A
B
It's
good
for
next
slide,
please
what
was
the
last
time.
Oh
yes,
maybe
maybe
just
a
one
one
thing
not
from
my
side.
Also
now
I've
started
Shepard
review
on
the
on
the
document.
We
haven't
been
able
to
put
that
all
back
into
the
latest
version
posted
but,
for
example,
the
Ani
objective
text
that
was
also
proposed
and
text
in
in
those
changes
right.
So
there's
this
outstanding
request
from
that
Shepard
review
right.
E
So
I
just
mentioned
something
about
appendix
D.
Really
do
people
need
people
to
read
the
document
who
haven't
read
the
document
and
then
say,
did
I
understand
everything
and
then,
if
the
conclusion
is
I,
there
was
pieces,
I
was
didn't
understand.
Please
go
read
appendix
D
and
see
if
there
was
some
text
there
that
helped
you,
because,
as
I
said,
we
ripped
good
lot
out
and
Tallis
has
more
proposed
text
that
we
haven't
figured
out
how
to
fit
in.
E
We
I
was
in
the
process
of
filling
out
the
my
registry
templates
and
I
realized
that
we
kind
of
have
a
bit
of
I
think
a
bit
of
a
mess
in
our
mind.
Types
and
I.
Don't
really
know
what
the
right,
what
the
right
answer
is.
I,
don't
know
if
there
are
any
mime
experts
in
the
room.
Now,
if
not
I'm
gonna
have
to
go,
find
I
sent
a
couple
emails
to
a
few
of
the
mime
type
people
as
to
what
we're
supposed
to
do.
We
had
a
+
CMS
and
it
turns
out
the
+.
E
I
Oh
yeah,
hi,
Elliot
Lear
first
III
did
a
mime
type
for
the
mud
stuff.
So,
if
you
catch
me,
offline
I'll
share
my
experiences
with
you
on
that
I
think
what
it
boils
down
to
Michael
is
if,
if
this
is
meant
to
be
an
interplay
specifically
for
this
particular
particular
application,
and
you
can
use
the
same
mime
type
or
subtype
complete
with
plus,
by
the
way,
because
that's
what
I
did
with
mine,
so
I
can
I
can
go.
I
can
work
with
you
offline
on
that
and
we're
gonna
propose
something
back
to
the
working
okay.
E
I
Okay,
I
mean
yeah
if
you,
if
you're
comfortable
with
using
one
of
the
existing
types,
but
I
was
counseled
and
and
again
I
can
go
into
this
offline
to
go
ahead
and
create
one
of
those
nice
little
plus
e.
Like
things
for
a
good,
and
if
you
want
to
to
do
the
same,
we
can.
We
can
have
the
same
conversation
with
the
same
people
to
see
if
we
get
the
same
results.
Okay,.
E
That
actually
would
work
the
best,
so
we
do
meet
at
this
point.
We
we
have
been
meeting
weekly
at
1400.
We
tend
to
use
either
appear
in
or
WebEx
Tuesdays
at
1400.
Let
if
you're
gonna
join
us.
Let
us
know
so.
We
know
expect
you
and
it's
usually
a
audio,
mostly
with
some
screen
sharing
with
a
lot
of
etherpad
for
stuff
I
and
we
I
I
would
expect
that
we'd
be
ready
for
working
group
last
call
by
around
September.
First,
nothing
ever
gets
done
in
August.
E
At
least
you
never
get
any
reviews,
but
we're
still
working
on
it.
So
that's
why
I
wouldn't
want
to
start
a
working
group
last
call
August,
15th
or
something
cuz.
No
one
would
notice,
and
but
I
would
expect
to
weebly
be
finished
by
the
next
ITF,
be
in
the
in
the
queue
anyone
anyone
planning
to
implement
any
of
the
pieces.
Read
registrar,
massa
pledge
any
good
Facebook
postings
out
there,
yeah
okay
hands
up
there,
that's
great
to
know,
okay
other
than
us
all
right.
Thanks.
A
E
A
B
Next
slide,
all
right,
so
after
Chicago
the
last
version
I
post,
it
was
oh
seven.
So
let
me
quickly
summarize
the
changes
from
oh
seven.
We
have
this
connection
to
legacy
equipment
in
the
NOC
that
cannot
speak
the
ACP
natively
that
section
I
overhauled
and
made
it
a
lot
more
explicit
after
a
bunch
of
questions
came
in
how
that
works.
So
please
read
that
so
right,
so
you've
got
your
ACP
interface
without
encryption
into
these
device,
and
then
you
have
your
old
data
plane.
B
Don't
want
to
go
into
too
much
detail
for
time
reasons
next
slide.
So
then,
basically,
what
came
out
of
Chicago
was
the
discussion
about
this.
This
negotiation
of
the
secure
channel
in
an
extensible
fashion
and
the
you
know
thing
that
we
never
completely
worked
out
was
kind
of.
How
would
we
negotiate
that,
for
example,
with
grass-
and
there
was
also
the
point
being
brought
up-
that
ikely
to
is
actually
meant
to
negotiate
arbitrary
protocols,
so
in
conclusion
of
that,
I
basically
moved
that
whole
section
out
of
the
normative
part
of
the
document
into
an
informative.
B
You
know
kind
of
possible
next
decks
brought
in.
You
know
that
I
CLE
too,
should
do
it,
but
also
wrote
that
it's
not
clear
whether
I
quit
you
would
successfully
get
amended
to
negotiate
something
like
80
or
180,
or
other
hardware
encryption
schemes
that
people
wanting
to
implement
ACP
in
layer,
2
environments
might
want
to
use.
So
from
that
perspective,
I
think
this
is
a
section
documenting
that
more
work
needs
to
be
done
and
certainly
would
be
very
interesting
to
come
up
with
the
grass
negotiation.
B
So
there
is
a
lot
more
terminology
in
there
right
so
now
the
field
in
the
certificate
that
has
the
ACP
information.
There
is
the
term
ACP
information
on
that,
and
that's
also
the
field
that
we're
using
to
authenticate
a
neighbor
certificate
in
before
the
oh.
You
was
used,
but
then
there
was
all
this
text
in
the
document
that
was
saying.
Oh,
we
would
like
to
be
able
to
also
authenticate
certificates
from
other
domains,
so
you
never
know.
B
What's
in
the
certificate,
we
want
the
certificate
to
be
reusable,
so
we
want
to
make
sure
that
whatever
we
do
for
the
ACP
does
not
depend
on
anything
that
some
other
use
of
the
ACP
some
other
existing
functionality
in
the
devices
would,
you
know,
have
in
a
way
that's
incompatible,
so
the
only
dependency
against
certificates
other
that
you
know
they
need
to
be
valid,
and
you
know
you
check.
The
authentication
is
anything
checking
against
the
ACP
information
and
it's
also
made
extensible
I
have
a
slide
for
that
next
slide.
B
B
That's
in
another
part
of
the
message,
so
in
the
text
now,
there's
the
complete
message,
the
flood
message
through
which
you
basic
basically
find
on
a
link,
ACP
neighbors
and
the
main
part,
was
also
that
we're
going
to
have
a
parameter
in
there
that
lists
the
type
of
security
training
channel
protocol
supported
in
this
case
IP.
To
could
be
DTLS
as
well.
Those
are
the
two
options
and
that
basically
also
means
that,
because
we
learned
this
right
now,
I
adopted
the
text.
How
the
secure
channel
negotiation
works.
B
You
find
the
neighbor
you
know
which
protocol
it
supports.
Those
are
the
ones
you're
trying
nextslide
the
protocols
that
basically
at
the
grasp
level
are
negotiated,
are
reduced
to
I'd,
v2
and
DTLS,
so
I'd
be
to
itself
it's
going
to
negotiate
between
native
IPSec
and
IPSec
over
GRE
and
those
are
the
ones
mandated
to
be
required
by
standard
autonomic
devices
and
D.
Tls
is
kind
of
the
test
balloon
and
we'll
see.
B
If
we
have
any
more
problems
in,
you
know
getting
that
through
security
review
in
terms
of
complete
specification
and
other
aspects,
but
certainly
it
would
be
good
to
have
at
least
one
test
balloon
to
see
how
you
know.
Extensibility
works
both
for
us
and
for
the
idea.
There's
no
need
for
port
assignment
right.
Grassed
negotiates
the
port
as
well
next
slide.
Okay.
B
So
then,
basically,
in
the
last
two
weeks,
I
heavily
worked
on
the
ACP
posted,
oh
eight
today,
and
so
the
idea
was
that
the
text
would
now
be
code
complete
in
terms
of
all
the
pieces
that
people
ask.
How
does
this
and
that
work
should
be
in
there
right
now.
There
was
a
bunch
of
things
missing,
so
hopefully
we'll
get
a
shepherd
review.
Working
group
last
call
fairly
soon
on
that
there
is
now
a
terminology
section
with
all
these
terms.
There
is.
B
So
the
first
thing
that
was
missing
was
the
whole
section
on
you
know:
okay,
we've
got
certificates.
How
do
we
maintain
them
in
terms
of
certificate
renewal
that
basically,
that
section
was
added
then
the
whole
section
about
neighbor
discovery
that
was
straight
down?
There
is
now
only
what
we
really
want
to
use,
which
is
dull
grass,
all
the
other
stuff
that
we
discussed
is
now
in
the
informative
section.
B
Then
security
Association,
as
we
said,
iq2
DTLS,
then
how
to
use
grasp
in
the
ACP,
so
I
basically
revoked
that
into
two
main
subsection,
the
one
explaining
why
we
really
consider
grasp
in
the
ACP
as
a
core
part
of
the
ACP,
and
that's
really
because
the
core
services
for
connectivity
are
unicast
and
service
discovery.
Graph
does
more.
But
those
are
the
two
key
pieces.
I
think
that
really
are
at
the
lowest
level
of
autonomic
connectivity
right.
So
you
can't
get
away
with
just
unicast.
B
You
need
service
discovery,
that's
basically
one
part
of
that
grass
does
and
then
the
second
part
is
the
reversal
and
that's
what
we
kind
of
worked
out
through
the
review
of
grass
in
inland
is
three
and
that's
basically
that
we're
saying
grasp
always
needs
something
like
a
security
and
transport
substrate.
Some
you
know
underlying
function
that
defines
how
grass
messages
are
sent
and
secured.
B
That's
basically
what
Michael
was
suggesting
with
256,
so
8-bit
of
virtual
addresses
not
doing
the
zone
and
a
comparison
between
these
two
I
reworked
on
Monday,
with
a
Pascale
the
ripple
profile
to
meet
that
profile,
template
from
Michael,
with
with
a
lot
more
detail
and
also
defining
the
protons
I
have
a
slide
for
that
and
then
on
the
way
on
the
button
here,
some
other
PDF
conversion
killed
that
there
is
now
in
this
general
consideration.
There
is
a
subsection
about
ACP
interfaces
and
that
came
back
to
the
discussion
that
you
know.
B
Brian
always
was
asking
ok.
So
now,
we've
got
these
link
local
messages
in
the
ACP,
so
where
are
they
sent
and
they're
sent
into
interfaces?
Interfaces
are
mapped
to
secure
channels.
You
can
map
them
one
by
one
is
point-to-point
or
you
can
map
them
multiple,
secure
channels
into
a
single
multi
axis
virtual
interface.
So
that's
now
documented
pro
and
con
a
point-to-point
versus
multi
access
in
that
section.
Next
slide,
then.
B
Basically,
this
whole
description
of
you
know:
how
do
we
do
acp
on
layer,
2
switches
and
that's
one
of
the
reason
actually
why
we
selected
grasp
instead
of
mdns,
that's
in
its
own
normative
section,
because
one
of
the
key
points
is
also.
We
want
to
say
that
layer,
2
switches
need
to
run
acp.
Otherwise
we
can't
do
auto
configuration
autonomic
services
on
layer,
2
switches,
so
that's
elevated
to
its
own
type
of
additional
normative
section
right.
Why
do
we
want
it
and
how
do
we
do
it?
B
Yes,
I
mentioned
the
ACP
connect
that
that
was
done
better
and
then
basically,
the
section
of
how
do
I
turn
all
across
non
autonomic
places.
I
modified
that
into
2
section.
So
the
standard
one
is
tunneled
right,
so
you
basically
built
the
whatever
tunnel
manually
and
then
you
run
the
ACP
across
it.
Just
grass
discovery
everything
fine,
but
you
end
up
with
two
layers
of
encapsulation:
whatever
your
configured
tunnel
is
and
then
the
secure
Channel,
so
that's
not
really
ideal.
B
So
I
added
the
section
to
say
you
just
configure
a
remote
endpoint
for
your
secured
channel
association
like
okay
here
is
your
remote
I
could
be
to
peer.
Please
talk
with
him
and
build
your
IP
set
connection.
So
that's
a
lot
more
efficient
security
side.
So,
through
the
review
with
grass,
we
we
got
a
lot
into
those
details.
So
I
added
a
subsection
against
the
text
from
the
inside.
Everything
else
in
before
was,
of
course,
about
the
wonderful
property
of
the
ACP
that
it
very
nicely
protects
everything
against
attacks
from
the
outside.
B
But
what
happens
if
a
device
is
compromised,
so
I
basically
added
that
section,
and
that
was
also
one
of
the
outcomes
why
the
ACP
now
has
one
inconsistency
with
what
we
finalized
and
grasped,
which
is
that
basically
we're
now
saying
in
the
ACP
that
the
transport
substrate
for
grasp
really
even
inside
the
ACP
grass
unicast,
should
rely
on
TLS.
Even
though
there
is
an
outer
IPSec-
and
that's
really
about
you-
know,
mitigating
attend
attacks
from
the
inside
by
notes
that
happen
it
as
ACP
notes
that
have
been
attacked.
B
Ok,
so
then
all
the
stuff
that
was
initially
upfront,
so
basically
the
domain
certificate
provisioning
in
Rome,
and
that's
a
section
that
was
discussing
brewski
and
the
stuff
that
has
been
moved
out
down
because
it's
really
just
informative.
As
far
as
it
comes
to
the
ACP,
the
whole
discussions
about
why
not
LD
TM
DNS
and
ultimately,
why
dial
grass,
so
that
was
just
moved
on
just
the
text.
B
You
know
verbally
somewhat
improved
that
what
I
mentioned
the
extending
ACP
channel
negotiation
via
grasp,
something
which
we
never
finalized
is
now
in
that
informative
section
and
then
all
the
way
at
the
end.
To
some
you
know,
restatement
we
summarization
of
how
about
these
domains
subdomains
and
certificate
authorities.
How
does
it
come
together?
Because
these
pieces
were
kind
of
scattered
in
the
normative
text,
necessarily
because
they
go
through
multiple
steps
like
the
certificate
and
the
addressing?
So
that's,
basically,
what
I
thought
restating
this
for
people
to
read
up
is
very
helpful.
B
Next
slide
right
so
as
far
as
the
main
certificate
is
concerned,
so
I
was
trying
to
for
clarity
for
modularity
to
make
brewski
not
mandatory
by
the
ACP
but
make
it
optional
and
saying
the
really
prerequisite,
and
we
had
that
in
the
text
is
you've
got
to
have
this
magic
certificate
in
the
devices
that
basically
has
the
ACP
information.
However,
you
create
that
we
don't
really
care.
B
As
far
as
ACP
is
concerned,
sure
we
want
to
recommend
brewski
but
could
use
net
kanjiru
touch
or
you
could
manually
type
the
bits
in
with
peek
and
poke
right.
So
as
far
as
ACP
is
concerned,
it
doesn't
matter,
but
then,
of
course
comes
the
point.
Okay
and
if
you
don't
do
brewski,
how
do
you
do
certificate
renewal?
We
want
to
do
certificate
renewal,
so
that's
actually
the
section.
So
now
in
the
ACP
document,
the
maintenance
section
is
basically
about
renewal.
You
must
run
EST,
you
must
have
in
the
ACP
and
EST
server
or
more.
B
These
can
be
discovered
by
grasp.
So
there
is
also
the
grass
objective
to
discover
the
est
objectives
and,
oh
by
the
way,
brusque
is
just
an
extension
to
est
for
the
first
bootstrap
stuff,
and
one
of
the
reasons
to
explicitly
write
out
est
in
the
ACP
is
also
that
when
we
started
writing
ACP,
our
understanding
was
that
brewski
was
the
all-inclusive
document
about
everything
that
the
certificates
needs,
and
you
know
the
more
I
was
participating
in
the
design
team.
B
The
more
it
became
clear
that
brewski
really
only
cares
about
the
initial
bootstrap,
not
about
renewal
or
everything
else.
That's
part
of
est.
We
want
to
refer
to
that
and
that's
basically
what
the
documents
now
does.
As
far
as
obviously
one
wasn't
one,
you
have
a
and
I
autonomic
network
infrastructure
devices.
They
must
support
brewski
and
ACP,
but
of
course
you
can
just
build
a
device
that
only
has
ACP
but
not
routing.
So
that's,
basically,
the
clarification
I
think
the
structural
improvements.
That's
now
in
the
text,
with
all
the
details
needed
next
slide,
a.
A
B
Know
it
EST
is
mandatory
procedure.
Brusque
is
not
mandatory
procedure.
Brewski
is
an
extension.
A
superset
of
est
brewski
adds
the
initial
bootstrap
how
you
initially
get
a
certificate,
and
even
in
that
initial
getting
of
the
certificate,
it
does
rely
on
EST
right
and
when
you
do
renewal,
you
don't
need
anything
from
brewski.
You
really
only
need
EST,
and
so
because
we're
saying
okay,
the
prerequisite
that's
been
in
there
since
day
one
is
you
have
the
magic
certificate.
B
The
assumption
was,
of
course
you
get
it
from
brewski,
but
what
you
do
afterwards
for
a
new
land
for
renewal
est
is
sufficient.
That
was
totally
unclear,
so
this
is
now
completely
clear
that
you
know
as
soon
as
the
our
ACP
is
able
to
start
up,
because
it
has
a
certificate.
What
happens
from
there
on
with
the
certificate
is
est
and
of
course,
also
things
like
a
certificate,
revocation
list
and
so
on.
So
nothing
that
would,
you
know,
require
a
brewski
like.
E
H
E
A
bunch
of
other
other
ways
of
doing
that,
it's
and
and
I
think
that
it's
entirely
appropriate
that
the
certificate
lifetime
considerations
be
within
the
ACP
document,
because
it
is
the
ACP
document
that
actually
makes
use
of
them.
Just
just
as
a
I
haven't
read
this
part
of
the
text.
I
think
it's
very
new
from
this
week,
even
right
today,.
E
This
sounds
great,
it's
it's
surprising,
but
it's
but
it's
while
you've
been
busy
this
week.
So
that's
great
but
I
wanted
to
say
that
so
one
of
the,
for
instance,
one
of
the
considerations
in
itv2
that
we
had
long
conversations
about
was,
for
instance,
are
you
allowed
to
build
an
IEP
to
si
that
whose
lifetime
exceeds
the
certificate
lifetime
yeah
right
and
one
of
the
conclusion
was.
E
B
E
So
that's
yeah!
So
so
that's
that's
exactly
why
I'm
saying
that
this
has
to
be
there,
but
but
in
case
we
actually
need
to
think
about.
We
need
to
say:
okay.
Well,
you
know
that's
a
consideration
and
that
also
that
you
need
to
make
sure
that
you
renew
your
certificate
sufficiently
in
advance
that
fifty.
E
You
if
some
other
part
dies
because
it
didn't
do
this,
then
your
you
may
get
cut
off
right
and
not
being
able
to
renew
and
have
to
go
through
some
bootstrap
again
right,
because
because
some
other
parts
have
the
network
we're
not
as
observant.
So
it's
not
just
for
yourself
that
you
need
to
keep
things
up,
but
for
the
fact
that
other
devices
need
to
renew
so
I'll
read
this
document
this
part-
and
it
sounds
great
and
and
I
think
that
this
is
really
progressing.
So
that's
people.
B
The
the
other
important
detail
about
the
renewal
is
so
now
I
put
the
stake
in
the
ground
of
saying.
Okay,
you
must
support
crl
our
CDP
to
get
a
crl
over
https.
Just
for
the
generic
case
that
you
have
the
I,
don't
know
what
bootstrap
and
what
no
certificates
and
then
in
the
informative
section
about
brewski
I
put
your.
B
Me
just
finish
that,
basically,
the
preferred
model,
of
course,
is
to
use
brewski,
that's
in
the
informative
section.
That's
also
where
it
explains
this
wonderful
model
of
the
short-lived
certificates
and
the
fact
that
we
can
even
do
with
the
equivalent
of
renewal
with
brewski
after
short-lived
certificate
has
expired,
the
stuff
that
we
kind
of
worked
out
in
the
bootstrap
team,
because
we
can
instead
of
doing
renewal,
we're
doing
just
re-enrollment
through
the
brewski
infrastructure
right.
So
that,
obviously,
is
the
preferred
solution.
B
B
B
Model
document
there
is
actually
no
change
in
the
intention.
What
we're
doing
here
at
all-
it's
just
you
know
where
is
stuff
written
up
right
and
I
think
that
all
the
certificate
management
that
was
just
you
know,
I
think
as
as
acp
authors,
initially
expected
brewskis
taking
care
of
everything,
but
obviously
brewski
is
only
up
to
the
first
time
when
you
get
a
certificate.
So
it's
really
our
responsibility
and
we've
just
haven't
hedged
up
to
it,
but
reference
wise.
There
is
nothing
new.
B
Right,
so
these
are
the
details
in
terms
of
the
ACP
thing:
how
do
you
find
your
closest
est
server
and
if,
basically,
their
trust
point
is
in
the
cert?
So
there's
a
bunch
of
detail
and
out
of
time
that's
yeah
recommendation
to
the
renewal
after
less
than
50%
of
lifetime
has
expired.
So
let
please
please
read
the
text
and
and
NP
definite
next
slide.
Okay,
what
was
this
right
so
this?
This
was
basically
a
bunch
of
the
details
that
has
led
me
in
terms
of
their.
B
There
was
kind
of
suggestive
text
where
I
wouldn't
I
couldn't
understand
it
all.
How
would
implement
it
about
subdomains
and
how
to
recognize
subdomains
and
basically
way
too
many
references
to
intend
will
solve
the
world
and
I'm
getting
concerned
that
you
know
we
may
not
get
intend
anytime
soon,
so
I
wanted
to
try
to
figure
out.
What's
the
most
easy
thing
we
can
do
about
subdomains-
and
you
know
for
example,
especially
when
you
use
Michels
the
aid
addressing
space,
we
don't
have
the
zones,
we
can
use
different
UL
A's,
so
basically
next
slide.
B
So
this
is
now
the
format
of
this
wonderful
acp
information.
So
we
have
the
ACP
address.
We
have
the
domain.
Now
there
is
a
routing
sub
domain
field
which
is
optional,
and
so
the
whole
idea
is
the
hash
you
calculate
of
the
concatenation
of
the
routing
sub
domain
in
the
domain
by
domain
is
example.com.
Routing
sub
domain
would
be
area,
51,
dot
research,
so
the
edge
of
string
from
which
you
generate
the
hash
is
area
51,
research
or
example.com.
So
now
you
can
create
basically
different
UL
a
s
and
also
by
using
multiple
subdomains.
B
If
you
have
an
ACP
connection
to
appear
in
a
different
sub
domain,
you
can
start
doing
intelligent
tricks
and
future
stuff,
like
grass
negotiating.
What
are
you
doing
on
the
routing
side
differently
right
now,
it's
purely
in
this
standard,
the
ability
to
create
different
ula
s
there.
You
can
use
that
to
create
multiple,
disconnected
networks
that
you
can
connect
whenever
you
need
to.
B
But
it's
really
really
just
a
stake
in
the
ground
to
hopefully
do
in
follow
up
work
very
easily,
more
changes,
an
improvement
in
routing
and
aggregation
other
things
without
having
to
wait
for
intent,
I
think
that
would
be
high
level
a
way.
To
summarize
this,
for
the
time
being
next
slide
yeah-
and
this
is
also
yeah.
There
was
this
other
text
that
was
saying.
B
Okay,
if
you
want
to
basically
start
you
know,
bringing
together
different
domains
into
the
a
CPU
cross,
sign
the
certificates
and
I
was
thinking,
oh,
my
goodness,
how
much
effort
does
that
take
to
get
from
existing
certificates
over
certificates
that
are
cross
sign,
and
so
basically
I
changed
that
over
to
you
just
want
to
distribute
the
other
networks
CA
as
another
trust
anchor
that
basically
in
your
certificates
check.
You
are
accepting.
So
that's
the
much
easier
solution
next
slide
yeah,
so
that
I
talked
about
that.
B
So
the
whole
ACP
neighbor
discovery
that
was
all
just
moved
down
and
and
refined
in
the
text
to
be
hopefully
easier,
readable
for
part
yeah
next
slide
yeah,
so
I
talked
about
the
I,
don't
have
the
the
actual
format,
but
we
had
these
threads.
Certain
bits
of
you
know
routing
sub
domains
that
we
reserved
and
and
didn't
use,
and
then
we
only
got
16
bits
for
different
devices
from
a
registrar,
so
Michael
was
proposing
a
an
optimized
addressing
scheme.
So
now
the
document
has
both
of
these
address
schemes
in
there
so
going
forward.
B
B
B
B
E
B
B
Know
it's
a
German
word
Israel,
because
I
would
love
to
pontificate
over
that.
Okay
right.
So
then,
the
key
part
which
I
also
laid
out
in
more
detail,
is
exactly
the
discussion
that
we
had
in
Chicago
also
about
the
fact
that
ripple,
ultimately
to
have
all
the
flexibility
of
its
feature
would
need
to
have
things
in
the
forwarding
plane.
I
was
afraid
to
raise
the
bar.
B
It
networks,
like
you,
know
typical
service
provider,
enterprise
networks
that
never
had
these
forwarding
plane
requirements,
which
is
also
why,
in
the
Cisco
implementation,
we
didn't
do
this,
and
so
ultimately,
the
profile
that
we
have
right
now
doesn't
require
any
forwarding
changes
ripple
is
just
establishing
a
destination
prefix
based
routing
table,
like
you
know
any
other
lame
routing
protocol,
and
it
quickly
converges
and
updates
these,
as
you
expect
from
any
other
routing
protocol.
So
what
it
now
gives
you
is,
there
is
only
shortest
path:
route
to
a
single
knock
right.
B
B
If
people
figure
out
that's
not
good
enough,
yes,
then
we
can
go
back
and
create
another
profile
that
adds
all
the
IP
and
IP
and
capsulation
the
RPI
header,
and
this
forwarding
plane
stuff
but
I
think
now
at
least
it's
it's,
it's
very
clear
what
we're
doing
that
it
works
and
how
we
could
expand
it
next
slide,
so
grasping
the
ACP
right.
So
I
think
I
initially
mentioned
that
already
transport
security,
substrate
mandate,
TLS
1.2
for
grasp
unicast.
You
know
attack
vector
from
the
inside
and
effectively.
B
We've
moved
the
Spanish
Inquisition
about
TLS
parameters
from
grasp
over
into
ACP
and
I'm.
Happy
to
take
that
on
and
see
that
we
have
all
the
details.
Erik
was
giving
me
a
bunch
of
references,
I'm,
not
sure
that
I've
gotten
through
all
the
details,
but
hopefully
we
got
sha-256
and
to
bid
sighs,
and
so
these
things
so
we'll
see
that
you're
in
security
review
next
slide.
So
we
are
the
all
the
layer,
2
stuff,
I.
Don't
think
need
to
go
into
more
details
on
that
yeah
next
slide
right.
So
all
everything
was
a
appendices
there.
B
When
we
had
the
discussion,
there
was
kind
of
nobody
reads
beyond
the
author's
names.
So
that's
why
all
the
what
we
had
in
appendices
before
is
this
section
further
consideration
just
directly
before
ini
considerations,
and
so
what
do
we
have
in
there
now
I
think
we
already
went
to
that.
So
the
whole
kind
of
discussion
about
brewski
ripple
unchanged
the
GLS
stuff
yeah.
So
we
talked
about
all
this
already
Thanks
next
slide.
Yep
normative,
informative
next
slide.
B
Right
so,
as
far
as
the
the
the
security
properties
right,
so
the
the
whole
idea
that
we
have
encrypted
channels
right
because
we've
seen
you
know
in
implementation,
history,
a
lot
of
people
always
pushing
back,
who
needs
security
right,
were
just
in
a
secure
data
center
in
other
places.
So
I
just
wanted
to
kind
of
be
a
lot
more
clear
about
these.
Two
main
reason
why
we
do
it.
B
One
is
really
all
these
bad
existing
protocols,
whether
it's
DHCP
DNS
radios,
NTP,
all
the
stuff,
that
you
do,
a
network
management
that
isn't
self-protecting
and
the
you
know
ability
to
protect
against
packets
being
injected
into
the
management
plane
and
forwarded
through
that,
but
also
pointing
out
that,
obviously
any
new
stuff
being
built
inside
the
ACP
should
or
must
use
end-to-end
encryption.
You
have
the
certificates
from
the
acp
don't
rely
on
the
secure
channels
alone,
yeah
I
think
that's,
that's
the
key
part
next
slide
right.
Okay!
So
that's
what
we
are
as
I
said.
A
With
my
working
group,
tear
her
down,
I
have
to
company,
impose
you
and
Michael
Richardson,
because
when
I
sent
out
the
call
for
agenda,
none
of
you
guys
replied
to
me
how
long
time
you
need
it,
and
each
of
you
actually
used
25
minutes
for
for
the
time
now
we're
half
hour
behind.
Is
that
it
all
right?
You
you
guys
are
you
know
computer
for
they
working
Google
milestones?
That's
why
you're
getting
priority?
Okay,
but
please
you
from
what
how
much
time
you
need
next
time.
A
C
A
A
A
So
next
page,
please,
this
is
a
change
from
Australia
to
all
four
draft.
We
actually
added
more
explanation
about
the
solution
and
make
it
more
readable
and
we
added
the
ipv4
options
and
we
actually
removes
the
DHCP
PD
a
flag.
However
way
to
add
some
text
say
this
mechanism
could
working
together
with
the
HTTP
PD,
also
it's
clear
and
in
the
document
that
this
document
is
not
a
complete
function
specific,
so
that
not
all
details
are
included.
A
This
is
just
a
informational
document.
The
main
pepper
is
used
to
describe
the
architecture
framework
utilized
the
component
of
a
drunken
network
infrastructure.
Its
base
base.
This
just
a
reminder
for
what
the
scenario
we
try
to
solve
and
that's
in
the
appear
on
a
network
way.
I
try
to
assign
the
autonomically
assign
the
profits
according
to
the
Lobos
in
this
IP
run.
Network
next
wait,
please
Alka
so
that
next
page-
and
this
is
what
they
were
added
for-
ipv4
extension
it
we
proposed
the
edge
profits,
objective
options.
A
There
are
two
options:
the
profits
manager
object
could
be
extended,
support
ipv4
by
adding
an
extra
flag,
all
the
option
to
a
separate,
but
similar
objective
could
be
defined
for
ipv4
yeah,
and
so
that's
something
still.
You
know.
The
working
group
may
need
a
little
bit
more
discuss,
but
I
guess
I'll.
Take
that
to
the
main
list
not
to
discuss
here.
Yeah
yeah.
B
Just
I
think
it's
good
to
give
you
know
an
idea.
You
know
how
to
do
it
with
before,
because,
ultimately,
before
it's
so
crooked
that
you
would
I
think
it
makes
a
lot
lot
sense
to
you
know
before
it's
in
much
more
need
of
all
this
automation
than
v6,
but
I'm
not
sure
that
in
an
informational
document,
we
need
to
figure
out
all
the
details
right
so
I
think
the
the
whole
idea
of
these
of
this
document
was
as
a
validation
and
give
an
idea
on
how
you
do
it.
A
A
A
A
It
describes
a
DHCP
deployment
module
without
a
central
DHCP
server
and
wizards
central
DHCP
server.
It
also
adds
a
Prophet's
management
with
the
grasp
proposed
deployment
module
using
the
grasp.
So
that's
more
scenarios
descriptions
here
and
to
describe
how
to
deploy
them.
Explain
please,
that's
all
for
now
and
this
taper
I.
A
B
Just
sit
here
and
make
it
fast,
I
got
to
hit
by
my
co-chair,
so
okay
next
slide
right,
so
yeah
yeah.
So
this
is
a
just.
You
know.
Through
the
you
know,
Chang
did
a
great
detailed,
Shepard
review,
so
many
small
textual
changes
more
detailed
to
what
stable
connectivity
means.
You
know
also
meaning
that
it's
meant
to
support
managing
ipv4,
even
though
it
by
itself
only
does
ipv6,
and
then
we
find
the
challenges
in
the
mutation
section.
B
That
was
a
I
think,
most
confusing
to
read
for
first
rushing
and
trying
to
emphasize
on
the
fact
that,
from
my
experience
you
know,
the
biggest
remaining
challenge
for
ipv6
is
really
that
ipv6
support
in
an
MS
systems
in
the
NARC,
like
you
know,
configuration
servers,
even
Sdn
controllers,
other
type
of
service
that
you
need
to
provision
the
network
and
so
having
work
with
customers.
They
really
said:
okay,
you
know
in
an
enterprise
right
we're
you
know.
B
A
lot
of
the
software
often
is
a
lot
older
and
they
don't
want
to
buy
a
new
licenses
and
that's
you
know
why
there
is
this
crazy
section
of
doing
v4
to
v6
net
as
a
workaround
for
these
customers
and
I.
Think
it's
so
ugly
that
nobody,
who
really
don't
need
it
temporarily,
would
you
know
ever
want
to
deploy
at
longer
term.
That's
also
I,
don't
see
it
as
a
risk.
E
B
About
I'm
I
just
wanted
to
give
you
know
one
example
of
a
stupid
way
to
get
the
old
before
knock
stuff
working
and
that's
the
stuff
that
in
a
lab,
I
tested
out
and
my
working
on
routers,
so
I
know
it
works
and
I
didn't
want
to
spend
too
much
time
on
it,
but
I
think
I
wanted
to
show.
You
know
that
you
can
adopt
the
stuff
now,
even
when
you
are
faced
with
this,
you
know
legacy
not
equipment.
That
was
basically
it.
Okay,
I,
don't
like
it
any
more
than
than
you
right.
So.
B
Yeah
and
then
also
the
the
description
of
you
know,
when
do
you
use
the
data
plane
when
to
use
the
ACP
to
talk
between
NOC
devices
and
and
device
in
the
network
and
Shane
was
concerned
about
why?
Why
am
I
mentioning
dns,
and
my
experience
is
just
in
a
NOC
everything
that
you
manage
is
managed
through
names
for
the
devices
and
whether
they
have
you
know
localhost
table
or
use
dns.
B
And
then
whenever
one
of
these
server
fails
and
you
had
get
one
with
a
different
IP
address-
and
people
haven't
considered
that
upfront,
they
have
a
thousand
devices,
they
need
to
change.
So
that
would
be
an
actual.
You
know
standard
strike
outcome
that
could
follow
up
from
that
and
then
architectural
II.
You
know,
we've
we've
done
the
stable
connectivity
for
stable
enough
to
do
management
operations
across
it.
B
But
one
of
the
things
we've
started
to
learn
is
that
in
the
Sdn
environment,
people
are
also
starting
to
build
out
really
very
closed-loop
systems
throughout
event,
management
channels.
For
example,
in
data
centers
they're
iGPS,
where
instead
of
doing
hop-by-hop
negotiation,
you
use
the
out-of-band
management
network
to
actually
you
know
flood
your
LSAs
collect
information
about
links
up
and
down,
and
you
know
would
be
cool
to
figure
out.
What
would
we
need
to
do
in
an
ACP
performance
and
recovery?
K
So
this
is
Jasmine
Aubrey,
and
this
is
just
a
chart
presentation
on
the
change
from
the
oh
three,
two,
oh
four
of
the
reference
model.
So
I'm
I
think
it's
just
a
couple
minutes
so
at
first
that
there
is
some
changing
in
the
wording
in
some
place
of
the
draftees.
For
example,
we
have
before
work-in-progress
and
now
AM
phase,
one
and
other
things
like
that-
some,
for
example,
out
of
scope
for
a
Neiman,
not
part
of
phase
one.
K
Finally,
there
is
some
updated
reference,
some
editorial
stuff
by
Michael
and
that's
kind
of
thing
next
slide.
I
think
that
the
biggest
change
in
the
the
draft
is
the
security
consideration
sessions,
and
this
is
almost
a
new
session
in
the
work.
The
title
had
changed
another
things.
So,
for
example,
there
are
a
couple
of
comments
that
are
taking
that
and
talk
how
to
change
the
text
into
to
improve
the
concepts
that
are
described
in
the
draft.
A
A
G
That's
its
purpose.
It's
not
intended
to
do
the
jobs
of
the
infrastructure
documents,
so
there's
a
working
group
choice,
which
is
whether
to
publish
this
as
a
separate
document
or
to
simply
put
the
material
in
the
main
drafts
that
it
that
they
belong
to,
which
other
and
risking
a
CPM,
stable
collectivity,
so
I
would
suggest
we
discussed
that
point
at
the
end
with
Michaels
question
earlier.
G
So
just
a
quick
look
at
the
objectives:
don't
propose
to
you
for
brewski.
There
are
two
objectives:
one
for
the
join
register,
r1
for
the
proxy.
The
objective
for
the
join
registrar
is
used
by
a
proxy
that
wants
to
discover
a
registrar,
so
we
can
do
a
standard
cross
discovery
process
and
then
obtain
details
from
the
registrar
about
what
options
it
provides.
G
The
connection
by
doing
standard
grasp
synchronization
and
the
other
one
is
the
join
proxy
objective,
which
a
proxy
uses
to
announce
itself
to
all
the
pledges
and
that's
restricted
to
the
linked
local
instance
of
cross,
also
known
as
dull.
So
the
proxy
effectively
joins
the
registrar
to
the
pledge,
and
that's
why
you
know
you
notice:
the
proxy
is
the
principal
no
it
mentioned
in
both
of
those
descriptions.
So
next
slide
please.
G
So
this
is
just
an
example
of
the
join
registrar,
objective,
I,
don't
think
I'll
go
into
the
syntax
details,
but
it
looks
you
know
this
is
sort
of
Python
desk,
notation
and
there's
the
join
proxy,
also
Python
esque
notation.
What
I
would
say
is
that
at
least
writing
in
an
object-oriented
language.
It's
extremely
easy
to
define
these
things
and
also
extremely
easy
to
play
with
the
definition
find
out.
If
it
does
what
you
want
change
it,
if
you
don't
like
it.
G
So,
although
I
think
the
actual
code,
something
like
a
brewski
will
almost
certainly
be
written
in
C
for
experimenting
with
the
model
by
which
we
in
which
we
build
brewski
as
a
gross
pewter.
A
high-level
language
is
some
a
great
way
to
do
it
and
pretty
much
anybody
with
five
minutes
studying
of
the
basics
of
can
understand
what
is
it
all
about?
I
guess
it
all
worked
in
several
other
languages
as
well.
G
It's
similar,
the
ACP
announces
itself
to
modes
which
are
potentially
joining
the
ACP,
so
each
no
than
the
ACP
can
announce
itself
to
link
local
neighbors,
and
this
is
designed
exactly
like
the
join
proxy
objective,
so
that,
in
fact,
an
optimized
mode
could
send
both
the
same
flood
message.
In
other
words,
the
piece
of
code.
G
B
Yeah
you
know
I
and
and
I
mentioned
that
inside
I
read
that
from
Ani
objective
and
brought
that
also
as
an
option
to
the
ACP
draft
when
I
copied
it
and
but
also
noted
that
if
I'm
having
a
separate
a
CPA
essay
from
brewski
proxy
a
si,
then
obviously
you
know
it
would
be
probably
more
work.
Trying
to
coordinate
that
into.
B
G
That's
why
they're
separate
objectives,
but
they're
so
similar
that
you
could
probably
write
a
common
code
base
that
could
handled
of
them.
If
that's
what
you
want
me
to
do,
and
the
last
one
in
the
document
is
actually
a
little
bit
speculative,
it's
one
for
the
stable
connectivity
drove,
but,
as
some
I
think
tell
us
is
just
illustrated.
There
are
quite
a
lot
of
open
questions
about
mountains.
Big
stable
connectivity
mechanism
would
actually
use
grasp.
So
I
would
regard
this
subjective
at
the
moment
as
a
placeholder,
rather
than
as
a
firm
definition
and.
C
G
But
I
would
comment
that
if
you
define
a
grass
projective
as
a
negotiation
objective,
it
turns
out
that
you
can
use
it
as
a
two-way
communication
channel,
because
you
know
they
go.
Eight
messages
go
backwards
and
forwards
on
each
each
one
contains
a
new
version
of
the
value
of
objective
Epsilon
ago.
She
ation
works,
so
it's
very
easy
to
turn
that
into
the
general-purpose
messaging
protocol.
If
you
want
to
do,
there's
no,
in
fact,
I
wrote
a
messaging
system
using
grass
for
a
few
weeks
ago,
just
for
fun
took
about
an
hour.
G
B
Maybe
just
just
a
comment
right
I,
so
the
the
negotiation
capabilities
of
of
grass
but
I'd
love
to
explore.
You
know
for
this
negotiation
of
ACP
secure
channel
with
you
know,
different
preferences
kind
of
trying
to
emulate
Ike
v2
and
seeing
how
we
can
bring
other
objectives
like
performance
in
there.
I
think
that
would
be
a
great
exercise
as
far
as
learning
about
NOC
services
right
I
mentioned
in
the
stable
connectivity
that
I'd
rather
see
a
lot
of
separate
services.
B
Like
you
know,
a
DHCP
server
DNS
all
these
different
servers
as
individual
objectives
being
announced,
I
haven't
figured
out
how
I
would
use
a
you
know,
coalesced
a
and
NOC
objective
through
which
something
would
be
negotiated.
But
if
you
have,
you
know
any
further
idea
on
how
this
you
know
could
be
leveraged
to
do
something.
G
G
F
As
someone
who
reads
an
awful
lot
of
drafts
and
reviews,
an
awful
lot
of
drafts
every
two
weeks
for
the
ballot
process
and
approval
of
documents
going
out
to
it,
and
yet
another
document
for
information
is
always
a
pain.
If
it's
germane
to
a
particular
topic,
I
would
I
personally
would
prefer
to
see
it
in
the
document
in
either
a
section
or
an
appendix
for
very
easy
reference,
rather
than
going
to
hunt
down
something
else
that
that's
my
personal
opinion.
F
E
Michael
Richardson,
so
I
thought
this
was
a
useful
document
to
have
in
the
working
group
so
that
we
could
easily
and
quickly
compare
the
style
grammar
if
you
like,
of
the
different
objectives
that
people
are
had
and
that
the
print
was
to
copy
and
paste
them
from
other
documents
into
this
document,
and
that
allows
people
to
kind
of
get
a
flavor
of
things.
And
then,
conversely,
when
someone
is
saying,
okay
I'm
trying
to
write
a
new
objective
and
they
go
to
this-
and
it
collects
a
whole
bunch
of
them
together
and
they
can
go.
E
B
B
B
B
I'd
love
to
ask
the
question
to
the
mailing
list
also
with
with
a
proposal.
Then
you
know
not
to
use
it
as
a
reference.
You
must
copy
the
text
in
your
document
of
the
objective
that
you
depend
on,
but
we're
collecting
all
the
objectives
in
a
consistent
fashion
in
this
document
for
reference
for
cross,
that's.
G
A
A
A
By
that
time
we
actually
those
who
twenty
force
working
of
proposed
chatter
text.
So
all
those
chart
X
actually
has
their
meanings
every
words,
but
some
of
them
may
be.
You
know
out
of
date
that
why
we
went
to
the
rich
other
way,
I
need
to
update
some
text
next
page.
Please
here
are
the
important
message
from
the
country
charter.
We
don't
want
to
boil
the
ocean
that
why
they
can't
charter
is
quite
respect
to
the
milestone
we
set
up
from
the
very
beginning.
A
We
only
add
one
milestone,
work
item
as
for
last
three
years:
that's
water
and
we
would
like
to
improve
the
progressive
in
tracking
of
autonomic
functions
and,
and
we
want
to
work
on,
only
the
reusable
components
and
they
we
want
the
autonomic
network
infrastructure
to
be
reusable.
So
keep
that
in
mind
and
the
working
group
views
folks
on
the
affair,
professional
image,
the
network-
that's
I'm
by
the
word
it
could
include
in
the
IOT
network
as
well,
but
definitely
the
home
network,
which
probably
managed
by
the
users
scrappers
themself,
is
out
of
scope.
A
That
will
remain
next
page,
please
yeah!
For
the
trunk
networking,
we
divide
reference
to
the
self
merging
characters
of
this
property,
the
network
element,
but
we
are
not
really.
You
know
against
some
function
to
be
centralized
well,
the
autonomic
functions
should
be
able
to
adopt
into
unpredictable
changes,
so
that
will
be
flexible
and
the
closed-loop
control
is
important.
We
don't
want
to
have
some
open,
API
eyes,
which
we
don't
know.
You
know
how
to
close
the
rest
procedure
if
the
rest
procedure
after
we
move
API
is
lead.
You
know
visual
input
from
human
being.
A
A
We
actually
touch
at
least
five
of
them.
Those
black
phones
actually
goes
well.
We
touched
a
little
bit
the
common
way
to
identified
node,
but
we're
not
to
worry
or
to
identify
the
notes
in
the
topology
of
the
network
or
fun.
You
know
express
itself
to
be
more
understanding
by
they.
You
know
other
elements
of
the
network,
so
we
maybe
cook
working,
keep
working
a
lot
and
for
the
last
worker
components
are
consistent.
Autonomic
management
module.
A
A
This,
what
we
we
have
done
so
far
for
the
animal
autonomic
network
infrastructure.
We
have
really
used
super
components.
We
have
the
put
drop
key
infrastructure.
We
have
the
autonomic
control
player.
We
have
the
generic
autonomic
of
signal
protocol,
which
is
used
by
other
two
components
as
well,
and
all
those
together
to
become
the
autonomic
network
infrastructure
and
beyond
them.
We
have
the
autonomic
of
source
agent,
which
way
I
think
could
be
consider
other
applications
within
the
network
devices.
A
For
the
campus
charter,
we
haven't
opened
to
do
those
days,
as
we
just
have
to
validation
use
case
which
actually
informational
stators,
but
hopefully
in
the
future.
We
would,
you
know,
be
more
open
as
us,
but
we
still
working
on
the
great
years
of
which
we
suck
aces
could
be
you
know,
except
for
standardization
it.
It's
not.
Offices
should
be
standardized
next
page,
please
yeah.
This
is
the
working
group
milestone
again,
this
all
disparity.
We
have
four
milestone
working
called
documents.
A
It
should
be
definitely,
you
know
finish
by
the
next
meeting
next
page
and
loss
way.
Hopefully
we
we
think
we
could
send
them
to
ISD
before
the
next
item
meeting
but
maybe
steal
some
work.
You
know
for
the
updating
or
the
address
the
comments
from
ISD
by
saying
those
that
means
actually
will
almost
complete.
The
are
cont
milestones
by
next
eight
meeting
that
why
we
need
to
discuss
with
chattering
next
page,
please,
the
procedure
today
just
relax.
A
A
Actually,
for
last
two
and
half
years,
every
idea
of
meeting
we
had
two
sessions
for
anima
most
of
time
in
the
second
session
is
open
for
day
long
chartered
work
items
so
that
why
we
already
have
a
very
good
foundation
to
for
our
each
other.
However,
we
also
had
some
materials
of
booting
for
our
work
item.
A
B
B
I
think
we've
seen
over
the
last
three
years,
especially
on
the
Friday
on
the
Thursday
Friday
sessions,
a
lot
of
cool
ideas,
but
when
we
want
to
take
on
things
for
a
charter-
and
you
know
the
reminder,
24
revisions-
that
we
had
to
get
through
the
first
round
of
the
charger-
and
that's
really
always
coming
down
to
a
bunch
of
points
that
I
wanted
to
it
to
remind
folks
are.
But
we
need
active
contributors
to
the
work
right.
B
So
if
you
propose
something
that's
best,
when
you
can
contribute
it
to
yourself,
then
that
doesn't
actually
solve.
You
know.
Customer
problems
that
you're
aware
of
right.
Will
the
resulting
document
be
necessary
and
sufficient
for
interval,
implementations
I
think
that's
always
for
the
ITF,
the
most
important
things
they.
We
love
in
the
ITF
protocols
that
interoperate
instead
of
you
know
only
things
that
you
know
could
be
done
for
pride
really.
Does
it
leverage
chart
around
one
work
right,
so
the
a
and
I
was
meant
to
be
reused,
so
anything
that
actually
uses.
B
It
is
a
cool
thing
for
us
to
also
validate
what
we
have
done
and
to
prove
it's
useful.
Can
it
proliferate
the
work
into
more
deployments
now?
I
guess
not.
Necessarily
all
of
that
needs
to
happen
here
right.
All
the
related
work
happening
in
sixty
is
cool
as
well.
So
this
may
not
be
a
good
criteria
for
our
working
group
alone.
That
could
also
have
in
other
groups,
then.
B
Is
it
necessary
and
helpful
to
improve
deployment
of
charter
on
one
work,
and
you
know
I
when
we
discussed
a
little
bit
about
additional
grass
details
and
a
bunch
of
the
other
things
that
we
have
been
following,
slides,
I,
think
through
the
work
on
the
Charter
items,
I
think
we
learned
a
bunch
more
details,
extension
other
things.
That
would
really
be
helpful
to
me
happen
and
yeah.
Ultimately,
you
know
global
warming
right,
don't
boil
the
ocean,
and
also
consider
you
know,
is
this
something
that
enema
should
be
doing
as
opposed
to
other
working
groups.
Okay,.
A
A
A
We
had
the
in
stock
items,
which
explains
how
is
I
should
use
the
Bing,
I
and
cross
API.
You
know
to
provides
the
API
is
for
the
is
a
to
invoke
usually
and
AI
ni
deployment
document
could
help.
You
know
to
understand
how
deploy
in
various
environment
and
it
may
feedback
some
requirements
or
modification
to
our
eyes
and
the
infrastructure
information
distribution
over
across
actually
extends
the
crust
ability
a
little
bit
also
the
open
source
reference
implementation
for
a
I'm.
B
A
A
A
Last
was
one
of
the
potential
work,
generic.
Who
is
a
specification?
If
the
you
know,
if
some
ASA
is
generally
enough,
you
know
to
be
a
white
use
for
every
automatically
devices
as
something
definitely
good
and
should
be
standardized
the
specific
places
based
on
the
specific
scenarios
for
which
one
not
decided.
Yet
if
we
can
work
out,
you
know
good
quit
here
us
to,
you
know,
decide
whether
they
should
be
standardized
or
not.
Then
we
may
be
working
on
some
of
those
specific
phases.
A
B
Maybe
just
terminology
wise
I
think
one
of
the
things
we
missed
in
this
life
I
think
when
it
when
it's
about
how
do
we
build
software?
That's
how
when
we
think
about
a
SaaS
software
modules
right
if
we're
thinking
about
some
particular
service,
our
terminology
is
the
autonomic
function
right.
That's
basically,
something
that's
done
by
a
bunch
of
aces
together,
and
so
we
don't
have
that
term.
But
if
it's
about
what
we
do,
that
would
be
you
know:
do
we
want
to
work
on
this
autonomic
function
or
not
yeah.
A
A
You
know
possible,
then,
beyond
that
we
could
add
the
autonomic
functions
to
you
know
over
it
for
the
network's
lesser
management
and
say
sl4
load-balanced,
based
on
the
device
negotiation
that
could
be
some
generic.
Who
is
a
switch
applied
to
every
a
at
home
keynote
and
out
software
update
management,
I
think
another
fundamental
functional
for
Asia,
also
towards
perhaps
up
and
storage
integrating.
We
have
one
rotation
today
and
the
left
management
and
naptime
management
of
Asia
Alma's
discussed
expect.
Please.
A
We
also
has
several
draft
submit
to
animate
during
a
master
at
half
years,
but
nobody
really
present
already
asked
the
working
group
timeslot
for
that.
So,
but
you
know
we
mean
if
they
were,
there
are
computers.
We
may
retake
that
next
big
fish.
Ok,
this
is
the
last
page.
The
next
after
discuss
with
our
ad
and
get
permission
from
ad
to
reach
Hatter,
okay,
ready.
E
E
I
wasn't
entirely
sure
that
we
haven't
done
the
red
things,
although
I
realized
there's
no
actual
document
about
how
to
address
nodes
or
how
to
name
them,
but
it
seems
like
we
could
fit
that
in
somewhere
with
a
little
bit
of
work
and
I
finished
those
those
things
off.
I,
don't
think
it's
that
hard,
but
maybe
I
missed
the
list.
The
complexity
somewhere.
E
We
have
a
really
good
job
of
not
boiling
the
oceans
by
never
speaking
the
words
intent
unless
it's
an
a
quiet
little.
You
know,
you
know
you
know
kind
of
thing
right,
yeah,
so
that's
really
good
I,
don't
know
how
soup
was
doing
I
think
they've
kicked
intent
out
of
their
working
group.
I
I
know
that
I
tried
to
pay
attention
at
one
point
and
I
just
was
my
eyes
glazed
over
because
I
there
was
too
many
too
much
abstractions
for
me.
E
E
B
You
know
yang
model
for
X
and
I
said
cut
off
line,
yeah
metaphor
for
managing
the
network,
the
grass
objectives,
so
a
couple
of
things
around
that
which
I
think
would
very
much
help
actual
implementations
of
the
a
and
I
so
I
think
there
is
there's
a
bunch
of
good
things
to
do.
As
far
as
the
intent
is
concerned,
I
think
it
would
be
good
to
keep
the
discussion
going.
B
I
like
the
drafter
and
much
I
kind
of
started
to
talk
to
the
ATS
a
little
bit
in
my
impression
is
that
the
best
thing
we
can
probably
do
about
intent
is
come
up
with
a
different
name,
because
I
think
what
we've
been
thinking
about
really
is
more
like
a
northbound
network,
wide
interface
to
provision,
services
and
policy,
and
you
know,
whenever
you
know,
we've
been
asking
people.
What
do
they
think
is
intend?
We've
got
different,
different
opinions
right
so
yeah.
J
Oh
my
voice,
the
fact
that
this
work
has
to
continue.
Let's
don't
forget
that
other
language
working
starting
45
years
ago
was
the
first
paper
on
sync,
and
it
is
supposed
to
continue
is
not
something
what
you
do
it
once
and
finish,
because
this
will
be
a
disaster,
and
I
would
like
to
suggest
that
maybe
part
of
the
work
in
the
next
area,
though
animal
to
be
concentrated
on
the
emerging
professional
networks
which
are
appearing,
namely
the
software
networks,
if
you
like
it
or
not,
this
is
going
to
be
a
trend.
J
Now
it's
related
to
the
autonomic
networking
of
virtual
systems,
obviously
slices,
but
also
with
all
the
other
tools
which
I
needed
to
integrate
to
the
Reston.
For
this.
In
my
view,
it
should
be
at
least
a
high
priority
for
for
this
working
group,
rather
than
to
just
add
more
or
in
addition
to
adding
more
elements
whose
existing
thing
all
the
concepts
of
are,
are
applicable
to
non
virtual
elements.
It's
a
time
to
move
that
element,
this
ecosystem,
which
is
happening,
Thank,
You,
P,.
L
Morning,
everyone
this
draft
just
mentioned
by
shown,
it
belongs
to
the
category
of
leverage.
The
current
a
lie:
okay,
next,
please.
So
the
problem
is
when
we
want
to
utilize
the
current
ni
into
some
existing
traditional
systems,
such
as
network
menu
server.
There
are
some
gaps.
The
first
one
is
because
in
the
ACP
and
the
all
the
addresses
and
generated
automatically
and
in
the
traditional
way,
the
addresses
are
mostly
panda
risk
very
restricted
by
the
administrators.
L
So,
even
if
the
central
management
server
can
connect
to
the
autonomic
nodes,
the
server
cannot
figure
out
which
one
is
which
the
second
question
is.
The
autonomic
node
itself
also
doesn't
know.
Who
is
the
server?
And
the
third
one
is
the
just.
The
management
server
also
don't
know
the
topology
of
the
autonomic
network.
So
because
of
these
gaps,
it
will
be
impossible
for
the
traditional
system
to
utilize
the
ini.
L
Next,
please,
okay,
here's
some
very
initial
ideas
of
how
to
solve
these
problems
to
the
issue.
One.
We
need
a
naming
mechanism,
just
as
mentioned
by
Michael,
Richardson
and
I
explained
it
a
little
bit
in
the
next
slide
and
the
second
one
is.
We
need
simply
need
a
discovery
mechanism
for
the
management,
server
or
controller
for
the
topology
discovery.
L
We
need
a
Maxim
to
report
the
topology
information
to
the
server
okay.
Next,
please,
for
the
naming
we
proposed
a
conceptual
technique
called
a
structure
name
and
the
essential
thing
is
the
naming
element,
that's
key
information
or
hints
of
a
device
name,
and
some
of
the
elements
are
mandatory
for
device
name
and
some
of
them
optional.
L
So
when
also
need
to
define
the
semantics
and
a
pattern
of
name,
so
the
semantics
could
be
include,
but
not
limited
to
the
device
type,
the
ownership
locations
or
functions
etc,
and
a
pattern
I
just
asked
you
the
example.
We
can
compose
the
name
by
location
and
device
time,
functional
role
and
a
distinguishing
number
to
make
sure
the
name
won't
be
conflict
with
each
other
and
the
don't
come
in
of
the
device
next,
please
so
how
we
can
compose
that
kind
of
structure.
Name
autonomically
in
general,
there
are
several
approaches.
L
Sorry
I
just
forgot.
The
English
word
some
some
word
generally
by
the
device
itself
that
can
teach
finish
with
each
other,
and
we
can
also
allow
some
specific
hardware
interface
to,
for
example,
we
can
oh
okay.
The
hardware
will
use
some
USB
key
to
in
input
such
kind
of
information
and
and
the
network
interface
as
well.
L
L
Ldp
is
always
useful
too,
and
what
we
need
to
define
the
grasp
objective,
to
reported
to
apology
to
the
central
data
server.
Okay
next,
so
the
Trotter
is
at
a
very
initial
stage.
We
just
want
to
give
some
ideas
and
to
see
whether
these
direction
worse
to
be
explored
in
as
a
future
work
Adam
in
this
working
group,
okay,
the
next
one.
L
So
we
can
have
multiple
gateways
and
each
gateway
normally
only
attached
with
our
Y
network
and
the
meter
knows
you're
a
very
resource
constrained,
for
example,
a
one
typical
mode.
It
only
has
110
8
kilobyte
of
RAM
and
512
kilobytes
roam
and
the
Gateway
is
much
more
resource
rich,
and
these
small
nose
only
need
to
connect
to
the
Gateway,
and
normally
it
doesn't
need
to
directly
connect
beyond
the
Gateway
to
the
server
and
in
this
reproduction,
the
youth
repo
and
they
also
utilized
ipv6.
L
L
L
Next,
please.
So
there
are
also
some
existing
solutions
and
their
specification.
The
first
one
is
the
call
me
the
engine
interface
develop
the
place
down
co-op.
It
is.
There
are
several
craft
and
there,
the
core
network,
a
core
working
group
and
in
a
nutshell,
this
solution
is
just
a
LT
version
of
Netcom
young.
H
L
And
the
other
one
is
called
led
with
machine
to
machine
is
developing
another
sto
called
OMA
and
management
protocol
is
also
based
on
Co
app,
but
they
don't
choose
the
yon
data
model.
They
use
defending
ourselves,
oma
objects
and
all
mod
objects
is
in
a
flat
organization,
rather
than
a
young
tree
style
organization
connects
place
so
giving
we
already
have
existing
solution.
Why?
We
consider
use
grasp
for
this
scenario,
because
the
cost
of
itself
has
provided
enough
capability
to
support
of
functions.
The
minimal
requirement
is
just
we.
L
We
utilize
the
request,
the
message
and
the
synchronization
message
passed.
The
flood
message
can
fulfill
the
current
requirements
and
the
question
is
very
lightweight
and
the
cost
base
is
really
small
and
actually
the
other
team
is
now
developing
the
prototype
for
for
the
product
and
the
is
established.
The
cost
base
should
be
within
3
K,
but
of
course,
is
for
the
minimal
requirement,
not
the
whole
question.
G
L
M
Hi
next
one
please
so
we
traded
some
discussion
on
the
mailing
list
about
you
know,
rethinking
how
we
actually
distribute
messages
in
the
anima
infrastructure.
So
in
a
nine.
So
why
is
that?
Because,
as
you
know,
the
reference
model,
and
also
some
drafts
are
actually
already
mentioning
that
so
as
a
possible
rich
authoring
item,
so
information
distribution
might
be
necessary,
for
example,
for
the,
unlike
you
know,
indents,
but
also
for
some
other
things.
M
If,
for
example,
several
others
need
to
somehow
communicate
together
to
establish
some
service,
for
example,
it
would
be
probably
a
good
idea
to
provide
some
kind
of
information
distribution
which
is
more
structured
than
what
we
have
today,
which
essentially
boils
down
to
flooding
the
whole
network
thanks
slide,
please
so
we
have
several
wise
I
will
not
go
into
all
details
of
that.
But,
as
we
just
did
it's
a
guiding
example,
we
can
think
about
a
bunch
of
sensors
in
the
room
that
need
to
agree
on
some
network
wide
value.
M
So
this
value
is
not
local
to
a
sensor.
Let's
say:
temperature.
The
physicists
will
tell
you,
you
know:
the
temperature
is
not
what
the
one
node
is
reading,
but
rather
some
kind
of
average
value
of
all
nodes.
So
if
this
is
an
average,
what
needs
to
be
established
by
consensus,
essentially,
you
would
need
not
only
to
distribute,
let's
say,
an
intent,
whatever
switch
off
the
AC,
when
the
temperature
is
23
degrees
Celsius,
but
rather
you
would
do
something
like
okay,
I
am
measuring
20.
M
But
what
do
I
know
what
temperature
is,
so
you
would
need
to
probably
flood
and
refund
and
refile
until
you
actually
get
the
consensus
okay.
So
this
is
also
true
for
some
other
possible
scenarios,
which
I
will
not
go
into
all
details
too
much
light.
Please
so
point
is
that
if
you
look
at
the
current
four
point,
seven
section
in
the
reference
model
draft
it's
kind
of
confusing
the
information
distribution
requirement
in
the
sense
that
I
want
to
reach
all
notes
or
I
want
reached
all
nodes
of
that
type
with
the
specific
realization
of
that.
M
Being
you
know,
unconstrained
broadcast
so
essentially
flooding
over
the
network
actually
grasp,
which
is
then
used
over.
The
API
is
using
some
kind
of
multicast,
but,
as
we
know,
the
you
know
that
most
of
networks
do
not
really
support
multicast
in
that
way,
and
that's
what
level
multicast
repeatedly
failed
in
principle?
Probably
it.
M
You
know,
there
are
better
methods
to
do
this,
maybe
on
the
application
layer
and
as
one
of
these
methods
has
emerged
in
the
literature
century,
this
pops
up
this
publication
subscription
service
right,
where,
which
is
an
implementation
of
an
you,
know,
application
layer,
multicast,
where
essentially,
they
subscribers
and
the
publishers
are
decoupled,
and
that
allows
you
for
some
kind
of
a
synchronous
method
of
communication
which
then,
however,
achieves
almost
all
properties
of
the
most
infamous
flooding.
You
know,
especially
for
bigger
scales.
M
Specifically,
the
problem
is
that
in
the
AC
t,
if
you
read
it
currently,
for
example,
the
intern
distribution
is,
by
definition,
going
to
the
whole
80s
or
the
autonomous
domain,
because
this
is
how
they
are
known,
as
the
main
is
define.
The
scale
of
that
is
not
constrained.
The
you
know,
sparsity
of
the
network
is
not
clear,
so
that
would
lead
with
this
flooding
and
repetitive
flooding,
essentially
to
message
explosions.
M
We
believe
so
that's
why
something
like
that
something
more
structured
provided
from
the
a
and
I
or
maybe
some
kind
of
special
si
would
be
probably
a
good
thing.
So
the
pops
up
ins
realization,
however,
very
often
relies
on
storage.
Why
that
usually
at
least
for
the
repetitive
you
know
resending
or
for
this
so-called
backlog,
so
for
error
handling
and
so
on,
but
it's
it's
really
profitable
to
use
some
storage.
Okay!
Next!
Thank
you.
So
then,
essentially,
the
idea
becomes
very
simple:
we
could
introduce
a
closed-loop
support
for
storage
in
anima.
M
That
would
be
general
support,
so
Shang
and
sister
than
that
before.
So
this
is
not
some
kind
of
function.
That
is
only
you
know
helpful
for
somebody,
because
the
you
can
see
the
the
calls
would
be
something
like
put
and
get
of
some
information
objects,
data
objects,
let's
say,
and
that
would
work
more
or
less
the
same
work
like
the
routing
works
today.
So
if
I
want
to
route
today,
I
do
not
actually
have
necessarily
zero
to
the
end
node.
What
they
do
is
I
ask
you
know
some
next
hop
to
actually
deliver
the
message.
M
So
the
same
would
or
could
work
for
the
storage,
and
there
are
known
proposal
for
that.
Essentially,
you
do
not
know
where
to
store
it,
but
you
would
very
simply
give
it
to
the
next
hop
and
the
next.
What
would
find
it
and
so
on
and
so
on
it
can
be
structured
okay,
so
that
would
work
in
a
way
where
we
will
just
start
with
some
from
some
state
and
then
you
know,
do
a
specific
deterministic
procedure
and
end
up
storing
these
data
somewhere,
okay,
more
or
less
the
same,
like
you
do
with
body.
M
Okay
next
slide,
please.
So
it
can
be
implemented
done
in
different
ways.
We
can
see
it
as
some
kind
of
non-mandatory
additional.
A
si
I
mean
the
ACP
itself
is
in
a
si,
but
probably
the
lower
level
of
si
souls
that
that
is
probably
the
second
point,
but
it
could
be
some
kind
of
mandatory.
They
use
a
level
a
si
mandatory
or
not
mandatory
could
be
decided,
but
would
be
probably
quite
easy
to
integrate.
M
In
the
current
structure
of
the
you
know,
documents
drafts
our
C's
and
so
on
from
it's
less
than
that
cost
is,
let's
say:
okay,
probably
or
maybe
it
would
be
less
interoperable.
So
that's
why
we
could
also
consider
that
as
a
basic
service
of
a
and
I
and
introduce
that
kind
of
a
si
at
the
same
level
as
a
CP
or
may
be
integrated
within
the
new
version
of
a
CP
or
something
like
that,
so
both
can
be
considered
next
slide.
Please
and
then
just
for
an
overview.
