►
From YouTube: IETF114 I2NSF 20220726 1730
Description
No description was provided for this meeting.
If this is YOUR meeting, an easy way to fix this is to add a description to your video, wherever mtngs.io found it (probably YouTube).
C
C
A
A
D
A
Screen
yeah,
it's
kind
of
annoying.
In
a
way
I
heard
people
have
waited
years
for
them
to
finish,
and
so
we
have.
A
couple
of
drafts
need
to
be
discussed
whether
we
should
finish
the
last
call
sent
to
iesg
for
review,
or
should
we
abandon
it?
So
I
hope
this
meeting
we
can
discuss
them,
that's
it
and
then
so,
let's
go
back
to
the
any
other
questions
want
a
suggestion,
any
discussion.
No,
then,
let's
go
to
this
first
thing
on
the
agenda
about
the
consumer
interface
data
model.
Okay,.
E
So
can
I
tackle
during
my
speaking?
Is
it
fine,
I
think
if
I
okay,
otherwise
it
didn't
hurt
yeah.
So
hello,
everyone
welcome
to
i2
nsf
session,
I'm
very
excited
because
we
have
on
on-site
meeting
two
and
a
half
years
right,
so
I'm
very
happy
having
you
guys,
especially
roman
and
our
chairman,
europe
and
linda,
and
our
yeah
itunes
members.
E
F
E
E
So
basically
this
time
we
synchronize
a
consumer-based
interface,
the
way,
the
other
nsf
pacing
and
capability
young
model
and
monitoring,
because
we
passed
through
three
data
young
model,
the
thorough
the
review
and
evaluation
of
isc
in
the
meanwhile,
we
also
updated
the
in
parallel
consumer
phase
interface
and
the
resurrection
interfaces.
So
we
believe
these
two
drafts
are
well
synchronized
next
slide.
Please.
E
E
So
I
think
this
is
cleared
next
slide,
please
and
yesterday
dr
johnson
park
from
actually
he
gave
several
comments.
So
I
addressed
her
last
night
and
I
updated
and
I
submitted
the
version
22.
I
believe
all
his
comments
are
cleared.
Okay
next
slide,
those
are
editorial
comments
and
also
security
directorate.
He
gave
he
reviewed
and
overall
looks
of,
I
think,
is
fine,
and
then
he
gave
one
a
niche
typo
so
interruption.
So
we
collected
next
slide.
Please.
E
The
second
young
model
is
a
resurrection
interface.
This
is
importing
capability,
young
data
model,
so
capability
young
data
model
is
passed
as
rfc,
so
this
is
borrowing
a
major
component
from
capability,
so
the
only
some
picture
or
isolation
is
some
excess
information
and
the
performance
capability.
E
E
E
So
the
previously
we
had
some
transport
some
layer
information,
but-
and
now
our
young
model
focus
on
the
access
in
the
the
same
data
center.
So
in
that
case
ip
address
and
portal
number
enough,
because
this
access
information
for
some
security
controller
can
access
network
function
nf
to
computer,
so
usually
netcomp
or
leicester.
Conf
are
used
so,
which
means
the
tcp
is
used
so
in
bristol
tsp
is
a
transporter
layer.
So,
as
a
result,
ip
address
and
the
proton
number
for
on
nsf
is
good
enough.
E
E
E
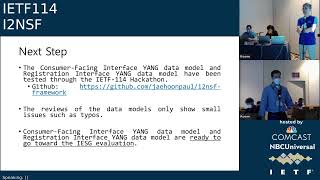
So
next
step
we
got
okay
through
a
review
from
people
outside
the
authors,
so
I
believe
also
the
one
thing
I
want
to
say
last.
Actually,
the
hackathon
is
already
almost
seven
years
during
seven
years,
except
the
one
hackathon
because
of
copied
yeah
the
happening
at
that
time.
We
couldn't
participate
in
itf
hackathon,
except
that
so
we
kept
participating
and
itunes
hackathon.
We
demonstrated
also
we
implement
our
own.
Also
we
implemented
with
at
three
people
we
so
we
had
have
two
implementations
and
consumer
pacing
legislation.
E
F
C
C
E
C
Yeah,
no
and
it's
great
that
he
did.
I
just
didn't
see
anyone
else
from
the
working
group
saying
that
they
read
it
and
reviewed
it.
I
mean
the
director
reviews
are
great,
but
we
asked
for
those
that's
coming
from
the
outside.
That's
not
working
group
energy,
I
mean.
Is
it
possible
to
get
more
reviewers?
I
mean
there's
folks
in
this
room
I
mean:
are
they
committed
to
reviewing
it
and
saying
it's
ready
to
publish
that's
what
I'm
looking
for?
C
Yes,
yeah
yeah,
I
mean
that's
what
I
mean
we
need
the
church.
I
mean
what
I'm
looking
for
is
the
transparency
that
you
know
folks
have
looked
at
it
and
kind
of
read
it,
and
if
we
could
do
that
for
both
of
those
to
get
to
the
point
that
we
have,
I
mean
this
isn't
a
voting
thing.
It's
not
a
numbers
thing.
We
could
have
three
to
five
independent
people
that
aren't
document
authors
that
aren't
the
direct
reviews.
C
E
C
Yeah
I
mean
I,
I
mean
sue
and
I
kind
of
talked
about
this
since
you
kind
of
mentioned
her,
I
mean
I
think
we
have
a
little
bit
of
I'm
trying
to
focus
us
on
the
process,
because
the
hackathon
is
is
wonderful,
but
the
hackathon
is
not,
unfortunately,
our
document
process.
So
what
we
would
expect
just
to
level
set
to
level
set
everyone
from
working
for
last
call
is
that
we
have
a
document.
There
is
an
author
team.
C
One
would
expect
that
the
team
of
authors
has
been
folding
in
what's
happening
from
the
working
group
and
they've
already
done
everything
that
needs
to
get
done.
What
I
think
gives
working
group
the
chairs
confidence
and
me
confidence
that
we,
this
is
a
consensus-based
thing
that
the
people
that,
in
the
the
people
that
participate
in
the
working
group
put
everything
they
needed
in
this
document
would
be
for
folks
from
the
working
group
to
positively
confirm
to
us.
We
looked
at
it.
C
E
C
A
A
C
Yeah,
in
a
sense,
this
is
the
check
to
kind
of
exactly
the
point.
Getting
reviews
is
hardened.
I
fully
kind
of
recognize
that,
but
this
is
in
a
sense,
is
the
check
if
we
do
not
have
enough
energy
to
have
people
review
the
final
thing,
then
we
probably
don't
have
enough
energy
to
publish-
and
this
is
the
check
that
there's
consensus
in
the
working
group
to
do
this
and
there's
energy
to
kind
of
finish.
C
G
Just
for
full
transparency,
this
is
diego
lopez
in
some
cases.
I
must
confess
my
in
my
case
that,
for
example,
I
have
I
have
reviewed
the
document.
It
seemed
okay
and
simply
you
feel
like
you,
don't
you
don't
have
the
time
to?
I
mean
the
time
I'm
talking
the
ten
seconds
to
say.
Well,
it's
okay,
just
because
you
have
all
the
other
things
that
that
distracts
you,
but
but
that's.
C
Yeah,
I
mean
the
there's
different
ways
to
kind
of
get
to
the
consensus
process,
but
my
concern
in
measuring
that
consensus,
because
that's
what
the
working
group
chairs
are
doing
is
the
only
evidence
we
have
is
the
meetings
and
the
mailing
lists,
and
so
we
don't
have.
I
mean
my
assessment
and
I
think
I've
put
this
on
the
mailing
list
before
my
assessment
is
we
haven't
met
in
a
while,
which
again
is
perfectly
fine.
C
Certain
working
groups
have
a
different
tempo,
but
if
you
take
a
look
at
the
working
group
mailing
list
from
the
last
two
years
three
years
there
are
no.
There
is
no
discussion
of
the
documents.
It
is
the
document
authors
which
is
great.
It
is
the
director
reviewers,
but
the
work
group
is
entirely
silent
on
all
of
the
edits,
and
so
from
my
perspective,
I
can't
tell
that
there's
consensus.
What
I
see
are
the
document.
C
Authors
are
being
incredibly
responsive
to
the
reviews,
but
the
working
group
is
not
at
all
commenting
when
we
were
talking
two
plus
years,
where
we
don't
see
that
at
all
and
so
on.
This
way
out,
I
really
want
to
make
sure
that
we've
double
checked
the
consensus,
especially
how
long
it
took
for
some
of
those
others,
which
is
where
this
consensus
kind
of
concern
kind
of
came
from
that.
Maybe
we
don't
have
enough
eyes
on
it
as
it
exits
the
working
word.
E
E
Actually,
we
actually
worked
hard
in
terms
of
young,
some
fixing
something
at
that
time,
working
with
people.
I
think
it's
hard
to
give
some
specific,
so
tom
pets
also
young
doctors,
so
we
got
a
lot
of
you
know
comments
we
yeah
so
at
moment.
Maybe
somebody
else
yeah,
maybe
also
we
approved
using
the
the
implementation,
so
I
think
yeah
so
but
yeah.
So
if
you
think
we
need
more
comment,
maybe
we
can
looking
for
so,
but
yeah.
A
Well,
so
roman,
is
I
find
it's
interesting.
I
went
to
this
open
source
gathering
today
at
lunchtime
for
many
of
the
extensions
in
the
routing
area,
they're
required
to
render
implementations
right
so
there's
some
proposals
in
bgp.
For
example,
you
look
at
the
code
and
then
you
run
the
code.
They
have
test
configurations
so
that
if
you
can
run
through
the
test,
then
you
are
okay,
because
some
of
the
features
like
can
be
encoding
so
integrated
details
like
people.
Don't
care
like.
A
C
It
should
be
all
yang
experts
with
the
domain
expertise
to
kind
of
model,
and
if
not,
then
then
we
actually
in
fact
do
need
outside
help,
which
I
don't
know
whether
we
need
but
like
what
we
need
is
review,
which
is
the
yang
experts
that
gathered
in
this
room
need
to
put
eyeballs
on
and
said.
I
looked
at
it
and
I
am
comfortable
with
it
or
I
have
feedback.
So
it's
not
so
much.
We
need
comments
as
in
we
need
to
find
issues
with
the
document.
I'm
not
saying
that
at
all.
D
F
Yeah
hello,
my
name
is
tanyan
joshua
kim
from
seongyoung
university
in
korea.
Let
me
start
my
presentation
today.
I
am
going
to
present
about
guideline
for
security
police
translator
in
itunes,
itunes
framework,
this
presentation,
based
on
based
on
draft
young
alternative
secret
polish
translation
version
11..
Next,
please.
F
F
F
B
F
F
So
little
relationship
between
cfi
and
nfi,
cfi
and
nfi
have
almost
one
to
one
mapping
relation
the
young
tree
of
cfi
and
nfi
have
similar
structure
based
on
itunes
capability
young
data
model.
With
this
characteristic,
the
attribute
of
cfra
young
module
can
be
mapped
to
an
api
young
module
by
determining
deterministic
mapping
algorithm.
There
is
a
zhang
algorithm.
F
F
F
F
F
F
So
the
high
level
policy
finally
translates
to
those
two
low
low
level
policy.
First
is
low
level
policy
for
prior
secondary
support
web
filter,
as
you
can
see
there,
that
kind
of
in
this
build
employee
translate
to
the
on
I
project
bonded
to
exterminate
and
the
web
sns
website
translates
into
facebook
and
instagram.
F
For
the
next
step,
this
draft
explained
the
relationship
between
cfi
and
nfi
as
guideline
for
security
translation,
it
helped
the
audience
to
understand
how
to
link
the
cfi
data
model
and
an
nfi
data
model
is
not
just
on
exemplary
architecture
and
procedure
of
security.
Secretary's
translator,
with
this
threat
put
on
implementer,
can
design
and
implement
it
on
spd
that
can
work
in
the
itunes
ecosystem.
F
E
Yeah
this
is
jean
paul,
john
from
skku,
so
the
this
draft
I'm
one
of
an
author
of
this
draft.
Let
me
briefly
explain
this
motivation,
so
this
is
the
raptor
explain,
relationship
between
cfi
and
nfi
for
guideline.
So
without
this
draft
it
is
a
very
hard
implementer
to
figure
out
how
to
translate
cfi
xml
high
level,
young
and
low
level
young
based
on
nfi.
E
So
we
focus
on
this
relationship
between
two
data
young
models
and
then
let
the
audience
can
understand
easily
how
to
link
to
each
other
and
the
implement
and
also
as
appendix
we
can
suggest
the
exemplary
architecture
and
procedure
rather
than
some
implementation
detail,
some
direct
normal
mentioned.
So
we
just
focus
on
the
relationship
about
two
data
models.
Okay,
that's
it!
Thank
you.
A
Thank
you
very
much.
I
do
have
questions.
It
seems
like
almost
like
a
dns,
the
name
to
the
address
the
the
high
level
name
or
context
to
the
low
level
mapping.
So
with
that,
you
will
need
some
kind
of
external
database
to
rely
on
right
to
do
the
translation,
so
it's
showing
here,
I
didn't
see
it
like
like,
for
example,
I
want
the
entire
group
to
do
something,
but
this
group
information
has
to
be
represented
in
some
kind
of.
E
Okay,
so
you
can
see
we
have
the
nsf
database,
so
we
can
populate
some
employee
information
name
and
their
ip
address,
based
on
the
dhcp
and
also
url
case.
Some
sns
website
case
instagram
youtube.
Facebook,
like
that
kinds
of
populated
into
nsf
database
linda
mentioned
dns
database,
so
we
can
so
actually
the
popul
population
of
that
database
case
a
kind
of
current,
our
consumer
patient.
Also,
we
export,
as
I
remember,
patrick
right,
so
we
consumer
phase
interface
also
dealing
with
the
population
that
kind
of
database
entries
with
those
information.
E
G
H
Yeah,
hello,
everyone,
my
name
is
patrick
from
sunglass
university.
So,
basically,
in
our
current
draft,
we
are
proposing
like
a
the
relationship
right
between
the
two
data
models.
We
have
the
high
level
policy,
which
is
the
cfi,
and
then
we
have
the
low
level
policy,
which
is
the
nfi
and
in
these
two
data
models,
so
in
the
nfi
we
designed
it,
we
designed
it
to
be
have
more
details
right.
H
C
Hi,
roman
daniella,
wearing
no
hat
just
as
cardigan
man
university.
I
think
I
have
two
interrelated
kind
of
questions:
how
how
do
folks
that
are
using
iqsf
now
bridging
the
gap
between
the
two
models
and
then
my
related
kind
of
question
is:
is
that
secret
sauce
of
the
implementers
I
mean?
Is
there
I
mean?
Do
we
need
standardization
in
that
mapping.
G
This
general
case
that
the
as
I
said
before,
if
we
consider
here
precisely
the
correspondence
between
the
different
instances
of
the
of
the
different
models
and
how
they
are
related
and
the
the
how
the
extensions
could
be
could
be
linked,
I
think
I
think
that
would
make
sense.
I
mean
when
we
talk
about
extensions,
because
it's
important
thing
that
a
vendor
comes
with
extensions
and
how
you
connect
one
to
the
others
and
how
you
connect
the
instances.
I
think
we
we
should,
or
we
could
explore,
that
space.
E
So
a
woman
comment
is
this
draft
explained
some
linkies
between
two
model
because
almost
a
one-to-one
mapping,
but
not
exactly
one
tool-
mapping
patrick
yeah
mentioned
so
certain
some
detail
is
missing
in
a
consumer
face
interface
such
as
users
group,
just
the
user
could
write
letters
than
ipv0006
ipv4
addresses,
and
so
those
are
can
be
translated
using
nsf
database
can
be
handled
by
that.
So
this
document
is
filling
that
gap
between
consumer
pacing
and
energy
facing
interfaces.
E
Without
this
document
it
is
very
hard
to
figure
out
how
to
link
to
each
other
because
the
I'm
editor
for
those
data
model,
I'm
well
aware
of
that,
but
other
people,
no
idea
so
translator
is
a
very
important
piece
of
our
itunes
app
and
with
this
one
and
the
people
can
easily
understand
their
young
models
and
then
they
can
make
it.
So
that
is
the
purpose
of
this
document.
F
C
So
so,
if
I'm
kind
of
summer,
to
summarize,
I
guess
my
question
was
primarily:
why
would
I'm
not
saying
that
the
translation
didn't
need
to
happen?
I'm
asking:
why
does
that
has
to
happen
in
a
standardized
way
and
you're
saying
that?
Is
it
fair
to
say
that,
because
you
could
have
an
ecosystem
of
different
kind
of
extensions?
You
need
to
kind
of
guide
that
translation,
because
there
is
heterogeneity
like
the
the
models
be
kind
of
different,
so
we
need
to
provide
more
guidance,
so
we
can
in
fact
do
the
translation.
H
H
Okay,
so
basically
I
want
to
talk
to
you
about
the
the
new
draft
that
we
are
proposing,
which
is
the
previously
we
called
it
application
interface,
and
we
received
a
comment
that
this
name
can
be
confusing
and
because,
for
that
reason
we
we
changed
it
into
analytics
information
and
analytics
interface,
that
it's,
the
naming
itself,
is
much
more
clearer
and
you
can
clearly
know
what's
the
meaning
of
analytics
interfaces.
Okay
next
slide,
please.
H
H
Yes,
now
we
call
it
analytics
interface,
as
you
can
see,
it's
much
more
easier
to
understand
that,
what's
the
purpose
of
it,
instead
of
saying
it's
an
application
right
now,
it's
analytics
interface,
yeah
next
type,
please,
okay,
so
the
in
here
now
we
added
a
new
component,
which
is
the
i2nsf
analyzer.
This
analyzer
is
purpose.
Is
we
collect
monitoring
data
from
those
nsf's?
That's
working,
they
collect
all
of
the
important
information
all
of
the
data
and
try
to
analyze
it
and
the
analysis.
H
H
Okay,
so
to
provide
those
analytics
data,
we
we
propose
this
analytics
interface,
so
this
interface
is
between
the
security
controller
and
the
analyzer.
So
after
the
iterative
analyzer
analyze
those
monitoring
data,
it
will
try
to
provide
a
new
information
or
the
configurations
like
what
how
to
solve
the
what's
issue
in
the
current
network
right.
So
we
propose
this
analytics
interface
so
that
that
analyzer
can
send
information
to
the
security
controller
next
slide.
Please.
H
H
So
it's
very
important
that
we
have
some
sort
of
analyzers
that
what's
what's
happening
in
our
system
right
now,
so
the
analyzer
can
collect
the
data
and
those
monitoring
data,
and
then
we
basically
try
to
make
sure
everything
is
okay
and
then
by
analyzing
those
activity
and
performance.
Basically,
we
can
create
a
closed
loop
security
control.
H
This
is
this
is
used
so
that
we
can
enhance
the
network
security
through
the
analysis
of
those
monitoring
data
and
by
adding
the
two
components
and
basically
one
component
and
one
interface.
We
allow
what
we
call
security
management,
automation
and
this
is
supports
automatic
adaptation
and
also
we
can
support
adaptability,
basically
yeah
next
slide.
Please.
H
Okay,
so
in
this
analytics
interface,
there
are
two
roles
that
we
are
we
needed
to
provide
an
enhancement
of
this
network
security.
The
first
one
is
the
the
policy
configuration.
Second
one
is
the
feedback
information.
Basically,
on
both
of
these
roles,
we
provided
three
fields,
which
is
the
nsf
name,
the
problems,
which
is
the
issue
that
we
are
having
currently
and
then
we
have
also
the
solutions.
What
is
the
possible
solutions
for
the
issue
that
we
are
having
currently
next
slide?
Please
so
the
first
one
is
the
policy
configuration
the
purpose
of
this
policy.
H
Configuration
is
basically
when
we
are
having
an
nsf,
that's
working
all
the
time,
and
then
we
collect
those
information.
What's
going
on
what
is
happening
in
our
network
and
then
when
we
analyze
those
data
and
then
we
can
provide
some
sort
of
a
reconfiguration
or
a
configuration,
because
we
want
to
enhance
what's
happening
in
the
network
right.
So
if
we
find
out
something
is
terribly
going
on,
then
we
need
to
reconfigure
those
configurations
on
those
nsfs.
H
H
And
we
have
a
feedback
information
which
is
a
different
kind
of
information.
That's
delivered
from
the
analyzer.
In
this
case.
It's
not
really
a
configuration.
For
example,
if
we
in
our
network
system,
we
have
some
hardware
failure
or
any
hardware
overloaded.
So
in
this
kind
of
things
we
cannot
handle
it
with
just
a
security
policy
right.
H
H
So,
with
this
new
interface,
we
created
the
closed-loop
security
control
that
improve
the
and
enhance
the
security
policy
and
also
the
network
security
itself
and
in
the
young
module.
This
is
based
on
the
nsf
facing
interface
and
monitoring
interface,
and
also
this
draft
facilitates
both
the
report
and
query
for
security
management
automation,
and
we
want
to
propose
this
draft
as
a
working
group
item
in
the
next
nsf
recharging.
A
E
E
So
that
is
a
kind
of
lever,
so
it
just
the
user.
So
yeah
your
life
yeah.
We
are
using
the
existing
nsf
facing
and
monitoring
interface,
but
not
exactly
same
so
that's
why
we
propose
and
also
this
purpose
is
we
provide
the
closure
security
control.
So
I
think
that
is
additional
required
piece.
Okay,
thank
you.
E
B
B
H
I
see
yeah,
so
this
collect
information
is
based
on
our
monitoring
and
our
monitoring
is
based
on
a
notification
based
or
report
base
right.
So
when
the
something
happens,
we're
going
to
report
it
to
the
analyzer
analyzer
will
realize
what's
happening
and
then
we're
gonna
give
some
sort
of
reconfiguration
to
handle
it
right.
Yeah,
that's
asynchronous.
C
Hi
roman
de
niro,
carnegie
mellon
university.
No
hat
could
you
in
the
kind
of
the
decomposition
of
what's
in
the
data
model?
There
was
this
box
of
problem
in
solution,
I'm
looking
in
the
draft
and
I
apologize.
I
didn't
read
it
so
I'm
as
smart
as
scrolling
through
it
and
kind
of
looking
kind
of
at
your
slides.
Can
you
explain
kind
of
a
little
more
about
what
gets
put
in
that
problem
and
kind
of
solution?
I
guess
I'm
not
exactly
kind
of
following
level,
though,
given
the
level
of
specificity
in
in
kind
of
the.
H
H
H
C
H
C
H
J
J
J
So
this
is
the
model
and
what
we
have
is
a
secure
session,
a
container
inside
of
the
bgp
piers.
That
would
make
a
lot
of
sense.
The
options
currently
we
have
are
ao,
md5
and
ipsec.
You
can
see
with
the
discussion
down
at
the
bottom.
Why
I
need
help.
I
had
a
long
talk
with
mahesh
and
who
chair
also
chairs
net
conf.
So
here
you
find
that
we
really
need
help
to
find
out
if
we've
got
the
right
grouping.
J
Paul
has
suggested
a
few
things,
but
this
is
why
I
don't
know
if,
if
we
have
a
right
now,
we
just
put
in
a
string
security
association
name,
but
I
really
need
to
find
which
group
is
is
going
to
help
us
with
that.
Next
slide,
you
notice
the
other
ones
have
key
chains.
So
one
of
the
thing
is
you
want
to
make
sure
that
you
can
have
a
security
association.
J
Perhaps
I
don't
know
operationally
people
seem
to
change
their
security
association,
some
very
rarely,
but
they
also
want
operational
state.
Okay,
so
that's
my
need.
What
I
don't
know
is
if
it's
i2n
i2
nsf
or
if
it's
ipsec
me
go
ahead
now
to
paul's
slides
that
he
helped
me.
This
is
paul's.
Suggestion
go
ahead,
linda
next
slide.
J
J
It
could
be
across
a
physically
secure
private
link
and
it
could
be
across
an
exchange
point
which
we'll
call
an
open
internet,
so
the
ipsec
can
be
used
any
of
those
cases
what's
good
about
it.
Is
you
really
need
to
have
some
sort
of
monitoring,
so
this
is
a
case
where
you're
seeing
I
to
nsf
work
in
the
model.
I
always
envisioned,
and
I'm
I
that's
a
where
the
i2
nsf
may
be
integral
parts
inside
of
a
larger
combinatory
box,
routers
and
security
devices.
Again.
J
J
Paul
suggests,
and
I
agree
that
it's
this
building
blocks
that
I
to
nsf
is
very
useful
because
we
have
some
of
the
same
things
inside
of
routing
places.
You
have
something
that's
controlling
the
security,
be
it
md5
or
be
it
ao
using
key
chains,
something
that
watches
it
and
gets
operational
state
and
then
something
that
is
a
configuration
backend,
which
is
really
the
development
management
system
and
a
user
which,
in
this
case
oftentimes
is
the
network.
J
J
That's
what
I
thought.
Initially.
I
had
debates
with
my
co-authors,
because
mahesh's
jeff
are
familiar
with
the
key
chains,
but
we
couldn't
get
to
a
a
solid
point.
So
paul
is
right.
You
can
either
run.
I
reckless
you
need
to
question,
but
what
I
really
need.
A
discussion
set
of
partners
to
to
ask
a
whole
bunch
of
questions,
and
this
is
a
bid.
Am
I
at
the
right
place?
I
I
pointed
my
co-authors
at
90
61
to
begin
with,
but
we
got.
J
We
ended
up
with
some
debate,
so
next
slide
linda
and
then
I
think
I'm
done
I
need
to
find
out.
Am
I
in
the
right
place
to
ask
the
question
it?
It
look,
look
it
if
we
go
from
there.
The
question
is
whether
we
need
to
extend
it
or
whether
I
just
don't
understand
it,
and
this
is
another
one
of
the
those
cases
where
we're
pushing
at
models
outside
of
the
routing
world,
because
we're
not
sure
how
to
plug
into
them.
But
we
don't
want
to
invent
our
own
right.
J
G
G
G
We
we're
talking
about
bgp
reflectors
that
are
in
different
domains
and
that
are
going
to
be
submitted
to
to
a
common
controller,
and
that's
that
has
trust
implications,
because
is
that
the
autonomous
systems
are
going
to
put
trust
on
a
on
a
common
device
that
is
somewhere
the
we
have
to
be
careful
about
this.
The
my
understanding
of
rfc
1961,
when
it
was
conceived,
was
precisely
four
highly
centralized
environments
in
which
enterprises
that
were
willing
to
connect
their
branches
to
central
offices
or
the
branches
among
them,
etc.
G
This
is
a
totally
different
beast,
I
would
say,
because
it's
a
and
the
trust
model
we
have
to
understand.
Well,
the
trust
model
if
we
get
the
trans
model
right
well,
why
not
when
whether
in
the
interesting
conditions
of
this
is
that
it
would
support
whatever
the
kind
of
bilateral
agreements
between
the
different
bgp
domains,
I
mean
as
long
as
you
have
your
your
bgp
domain.
You
have
mine.
We
agree
that
we
trust
paul's
controller.
We
are
happy
but
again
is
can
be
tricky.
J
Thank
you.
Thank
you,
diego.
I
may
send
you
some
questions
on
the
background
I
realize
the
trust
model
is
is
in
some
cases
within
a
common
administrative
area
and
sometimes
very
tricky,
so
I
should
be
at
itf
I'll
try
to
track
you
down
what
I
need
to
know
from
roman
and
the
rest
is.
Should
I
continue
the
discussion
on
the
i2
nsf
list,
or
should
I
go
to
ipsec
me.
C
I
Yeah,
yes,
yes,
I
can
hear
you
job.
That's
why
so
a
couple
of
comments
regarding
the
what
I
can
say
is.
I
agree
with
the
paul's
view
about
using
rfc
as
it
is
because
in
to
me
to
me
basically,
we
have
two
nsf,
both
rveb
routers,
that's
fine!
You
can
use
both
models.
I
don't
see
at
the
first
side
without
any
additional
detail
and
you
need
to
extend
or
to
change
that
because
in
the
end
you
need
to
apply
a
security
association
between
two
two
end
points
and
that's
fine.
I
We
can
use
the
the
rfc
9061
regarding
diego's
comment.
Regarding
the
other
comment,
the
my
my
opinion.
There
is
if
two
bgp
routers
belongs
to
two
different
domains,
then
we
are
talking
about
two
different
controller
security
controllers,
managing
two
different
vgp
routers.
But
then,
here
what
we
are
saying
is
we
need
something
for
the
east-west
interface
between
both
security
controllers
to
finally
install
something
in
the
vgp,
but
the
northbound
interface
define,
I
mean
sorry.
The
southbound
interface
defined
in
the
in
the
rfc
9061
can
be
used
directly.
G
I
J
That
might
be
three,
but
I
I
see
the
point
I
think
graphing.
What
I'll
do
is
work
through
the
examples
I
had
done
and
send
them
to
you
and
and
copy
the
send
them
on
the
list
and
copy
and
make
sure
that
we've
got
the
right
concept
on
that
and
if,
if
I'm
not
bugging
you
guys
too
much,
that
would
be
helpful.
I
thanks.
C
D
J
J
D
J
D
And
it's
always
possible
to
bring
it
back
to
ipisa
me
and
dusk
again,
but
so
far
we've
never
done
really
ibiza
policy.
We
always
assume
that
it's
up
to
the
user,
to
make
the
configurations
match
and
defining
this
east-west
model
here
means
that
we're
somewhere
somehow
negotiating
between
the
controllers
and
coming
up
with
a
cohesive
policy,
and
that's
that's
a
difficult
thing
that
ibiza
me
has
never
done.
