►
From YouTube: IETF115-MOPS-20221107-0930
Description
MOPS meeting session at IETF115
2022/11/07 0930
https://datatracker.ietf.org/meeting/115/proceedings/
A
E
D
F
D
E
E
D
E
Right
yeah,
so
there's
plenty
of
reference
documents.
If
you
would
like
to
read
more
about
the
various
and
pertaining
policies
next
slide,
please,
yes,
and
we
are
going
to
be
using
the
meet
Echo
queue
to
run
all
of
the
cue.
So
please
make
sure
you
join
join
me
Deco,
either
in
the
in-room
tool
or
on
the
the
full
tool,
as
you
like,
and
if
you
have
a
question,
please
join
the
please
join
the
Medico
MyQ,
as
Kyle
said.
E
If
he
has
to
wear
a
mask,
we
all
have
to
wear
masks
so
we're
all
wearing
masks
unless
you're
actually
actively
presenting
or
eating
and
drinking
okay,
and
then,
additionally,
when
you're
joining,
please
do
make
sure
your
audio
is
off
unless
you're,
actually
in
the
queue
and
speaking
all
right
next
slide.
Please
yep.
We
have
the
agenda
and
all
the
other
information
available,
but
I
think
this
is
not
new
news.
Thank
you.
Next
slide.
Here's
the
agenda
for
today
do
we
in
fact
have
a
minute
Staker
volunteer.
D
E
G
E
E
A
H
A
A
So,
thanks
to
Colin
Jennings,
we
have
elaborated
the
techniques
to
acquire
a
model
of
the
real
world,
and
this
is
in
section
3.1.
So
we
already
had
an
annotated,
Point
cloud
based
model
description.
We
have
added
a
couple
of
lines
for
polygon,
mesh
and
texture
mapping
techniques,
and
we
have
added
a
model
based
on
light
field,
which
is
in
data
structure
terms,
a
table
called
environment
map
that
describes
the
intensity
or
color
of
the
light
rays
arriving
at
a
single
point
from
arbitrary
Direction.
A
The
first
is
the
parameters
of
the
traffic,
such
as
volume
of
XR
data
burst
time
idle
time
they
are,
they
could
be
widely
separated
in
time,
but
show
correlation
and
also
you'd
find
a
long
bursts
of
traffic.
So
the
operators
should
be
able
to
provision
net
server
so
that
they
can
manage
the
long
bursts
and
traffic
next
slide.
Please.
A
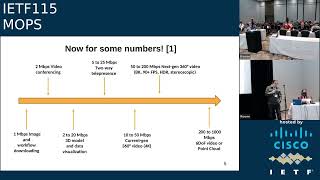
So
so
these
are
the
some
of
the
throughput
numbers
that
we
have
found
in
reference.
One
next
slide,
please-
and
here
is
another
set
of
numbers
here
we
have
included
the
expected
end-to-end
latency
values
as
well,
and
we
have
a
a
set
of
applications
arranged
in
taxonomy,
so
the
first
one
is
ar-based
remote
surgery
with
uncompressed
4K
120
frames
per
second
HDR
10
bit
real-time
video
stream.
A
So
for
this
the
expected
end-to-end
latency
is
around
750
microseconds.
The
expected
data
capacity
is
30,
gbps
and
possible
implementation.
Examples
are.
This
is
basically
a
newspaper
article
which
claims
to
be
the
world's
first
remote
surgery
over
5G,
then
the
second
application
is
mobile.
Ar-Based
remote
assistance
with
uncompressed
4K,
120,
FPS,
HDR
10-bit,
real-time,
video
stream.
The
expected
end-to-end
latency
is
less
than
10
milliseconds.
A
So
these
are
essentially
helping
in
the
workflow,
then
industry,
four
point
or
remote
maintenance,
remote
assistance
in
robotics
industry
with
those
references,
then
the
third
application
is
indoor
and
localized
outdoor
navigation
and
in
this
taxonomy,
from
reference
to
our
particular
AR
use
case
fits
in
that
category.
So
the
expected
end-to-end
latency
is
less
than
20
milliseconds.
The
expected
data
capacity
is
50
to
200,
Milli
Mbps
and
a
possible
implementation.
Examples
are
theme,
parks,
shopping
malls,
archaeological
sites
and
Museum
guidance
and
finally,
for
cloud-based
mobile
AR
applications.
A
A
So
one
thing
we
wanted
to
point
out
for
our
use
case
is
that
our
use
case
is
obviously
for
a
mobile
AR
scenario
and
that
it
specifically
deals
with
a
scenario
where
you
have.
Tourists
moving
in
an
outdoor
location
and
outdoor
locations
are
typically
very
challenging
for
most
of
the
techniques,
because
the
the
light
conditions
change
continuously.
The
angle
at
which
the
tourists
is
looking
at
the
scene
changes
continuously
and
there
might
be
people
moving.
A
Of
the
AR
Field
view,
so
so
our
particular
use
case
tries
to
showcase
the
problems
inherent
in
an
outdoor
mobile
AR
system.
So,
with
JS
permission
now,
I'd
like
to
invite
comments
and
discussion,
does
the
working
group
like
these
numbers?
Do
we
is
it
okay
to
for
us
to
write
up
these
numbers
in
the
actual
draft,
because
this
slide
in
the
previous
Slide
the
numbers
shown
there
have
not
yet
been
included
in
the
internet
draft,
because
we
wanted
to
have
a
discussion
at
this
ITF.
E
H
A
A
A
A
H
E
G
A
Yeah
absolutely
and
I
think
so
so
this
is,
this
is
from
someone
else's
world.
This
is
not
our
work,
and
what
we
really
want
to
do
is
to
capture
the
current
industry
practice
in
this
document,
and
the
goal
really
is
to
have
some
operator
going
out
and
deploying
in
the
field,
something
like
our
use
case
and
and
definitely
I'd
welcome
your
comments
on
the
draft
at
GitHub.
D
All
right
and
the
chair
recognizes
himself
it's.
It
seems
to
me
like,
if
you're
going,
to
put
numbers
in
at
all
they're
kind
of
a
a
moment
in
time,
and
they
need
to
be
from
the
same
moment
in
time.
Right
I
mean
uncompressed.
Video
right,
obviously
is
not
going
to
change
bitrate
ever
for
the
same
resolution,
but
compression
compressed
video
will
over
time.
So
are
these
numbers
all
from
kind
of
a
similar
generation
of
technology
for
video
compression?
A
E
C
C
Well,
if
it's
not
about
7.,
you
know
45
gigabits,
you
know
it
will
be.
You
know
it
will
be
something,
but
you
know
something
very
large,
so
taking
taking
what
Kyle
said
about
you
know
going
with
the
show,
you
know
one
generation
of
numbers
yeah,
you
know
and
then
thinking
in
terms
of
branches
I
think
that's
the
best
advice
I
could
give
to
the
working
group
about
about
this
draft.
Thank
you.
Thanks.
E
B
E
A
Just
want
to
leave
a
comment
on
so
so
the
other
issue
was
so
a
couple
of
ideas
ago.
Someone
mentioned
that
besides
Edge,
we
we
could
look
at
other
architectures,
but
we
we
have
argued
in
the
work
in
the
draft
that
edge
servers
are
necessary
for
latency
reasons.
You
need
to
place
the
computation
close
to
the
user,
so
one
question
I
had
was:
are
there
other
architectures
which
do
not
use
that
paradigm?.
E
A
A
E
Not
a
very
working
working
group
this
morning,
so
I
think
that
these
are
all
important
questions
and
sort
of
one
of
it.
Maybe
we
can
slide
into
the
where,
from
here
part
of
of
the
discussion
around
the
document,
I
think
that
the
there's
sort
of
three
things
on
my
mind,
one
I,
think
that
those
are
all
important
questions,
particularly
since
people
have
brought
them
up
in
previous
meetings.
It's
like.
Can
we
get
closure
on
whether
or
not
there
are
things
to
follow
up
here
and
if
not
drop
them?
E
If
yes
have
concrete
suggestions
and
then
there's
the
question
of
I
mean
it
seems
like
it's
worth,
it's
important
to
include
some
level
of
numbers,
because
it's
valuable
to
have
the
concreteness,
but
I
mean
following
on
Spencer's
suggestions
and
and
other
sort
of
follow-ups.
It's
probably
more
important
to
you
know,
have
a
sense
of
scale
of
where
this
fits
with
regards
to
current
technology.
So
keep
it
current,
as
Kyle
said
not
just
in
terms
of
all
of
these
numbers
from
the
scene
time
period,
but
also
compared
to
what
we
are.
E
You
know
what
is
realistic
to
deliver
or
what?
What
are?
Where
are
the
challenges
in
in
sort
of
contemporaneous
times,
and
then
the
final
question
is
well
and
what
else
you
know
is
it
is
it
just?
It
sounds
to
me
the
like.
The
the
current
action
items
on
this
document
are
the
numbers,
as
just
discussed
you
see,
do
a
last
a
last.
You
know
set
of
questions
to
the
working
group
to
see
if
there's
follow-up,
on
the
open
questions,
and
you
know,
if
not
what
else
are
we
done
question
mark?
A
E
F
You're
gonna
run
the
slides.
Yes,
yes,
hi
there,
I'm
glendine
from
Comcast,
NBC
Universal
and
today,
I'm,
going
to
give
an
update.
One
of
the
things
when
we
created
mops
a
couple
years
ago
was
to
try
to
connect.
You
know
the
professional
media
industry
streamers
with
work
on
the
ITF
and
vice
versa.
So
one
of
the
things
we've
been
doing
ongoing
is
at
svta
means
we
give
an
update
on
what's
going
on
with
the
ITF
and
at
mops
meetings.
F
We
give
an
update
on
what's
going
on
to
svta
as
a
wave
connect
industry
with
the
media,
Ops
working
group.
So
here's
the
update
for
iitf115
next
slide,
please.
So
the
first
thing
I'd
like
to
announce
is
that
SVA
has
changed.
Its
name
to
the
svta
has
a
t
now,
because
T's
are
cooler
than
not
having
a
t
in
your
name
but
new
name
same
Mission.
We
have
a
t
and
we
got
a
new
logo.
That
also
has
a
t
in
it.
F
So
it's
even
cooler
than
the
old
logo
and
we
have
a
new
domain
name,
which
is
actually
much
easier
to
hike
the
old
one
with
streaming,
video
technology,
Alliance
or
Siri
Siri
anyways
that
one
has
just
svta
much
shorter,
easier
to
type
and
life
is
better
next
slide.
Please,
and
for
those
who
haven't
heard,
these
updates
in
the
past,
svta
is
a
Industry
Group.
F
And
so
that's
why
we
have
this
connection
point,
because
this
is
what's
using
output
for
us
here
at
the
ITF
and
then
feeding
back
insights
next
slide,
please
and
as
an
example
of
the
stuff
that
is
actively
being
used.
Within
These
groups,
one
of
the
things
we're
doing
over
the
svta-
is
we're
cataloging,
going
through
and
identifying
key
Technologies
from
groups
like
The
ITF,
and
we
plan
on
submitting
a
draft
into
mops
cataloging.
What
professional
groups
are
using
in
terms
of
ITF
Technologies?
F
F
In
fact
the
cdni
caching
being
done
here
at
the
ITF
is
built
upon
it,
like
I,
have
a
few
slides
about
that,
but
it's
built
upon
over
at
the
svta
into
a
thing
called
open
caching,
which
is
then
being
used
in
production
in
environments
for
in
the
real
world.
So
it's
a
great
connection
point
next
slide.
Please!
Oh,
but
I,
see
I
had
a
typo
there.
I
should
have
RC
9000
for
quick,
not
900.
I
will
fix
that.
F
This
this
horrible
picture
and
but
it's
a
great
picture
at
the
same
time,
and
if
you
go
to
that
link,
you
can
actually
see
the
the
full
picture
in
all
its
Glory.
What
this
does
is.
This
is
a
mapping
of
where
open
caching
from
svta
makes
interconnections
with
cdni
from
the
ITF
and
builds
it
actually
into
a
production
environment.
F
So
you
can
sort
of
see
where
the
two
pieces
All
Connect
together,
and
it
makes
it
all
very
relevant
for
for
us
here
at
the
ITF
and
what
we're
working
on
and
that
is
a
horrible
picture.
I
admitted
I'm
gonna
try
to
get
them
to
make
a
better
picture
for
the
next
time.
We
do
this,
so
we
can
sort
of
illustrate
it
and
you
can
actually
read
it.
So
my
apologies
next
slide.
Please
we
have
updated
the
open,
cache
configuration
interface
specification
again.
F
This
builds
upon
cdni,
there's
version
1.1
just
got
released
over
at
the
SBA
svta.
Sorry,
I'm
still
stuck
without
that
T
I
need
to
learn
to
stick
that
t
in
always,
but
this
covers
you
know
the
interfaces
for
controlling
these
environments
that
are
deploying
cdni
built
upon
the
open
cache
framework
from
the
svta
next
slide.
Please.
F
Rfc
9000.,
so
there's
a
PLC
going
on
over
at
the
svta,
which
is
attempting
to
take
quick
because
for
a
lot
of
streamers,
quick
everybody
knows
next
new
thing:
really
cool
technology
production
environments
very
hesitant
at
times
to
pick
up
brand
new
technology
and
deploy
it
at
scale.
This
is
scary
and
when
we
talk
to
the
people
who
are
doing
these
things,
we
said
well,
what's
your
key
problem
when
they
identified
well
I
know
I
want
to
play
with
it.
I
know,
I
want
to
test
it,
but
I.
F
Don't
necessarily
know
how
to
do
that.
There's
too
many
options
when
I
say
give
me
a
you
know:
a
quick
server,
there's
a
lot
of
quick
server
implementations
out
there.
How
do
I
test
that
I,
don't
know.
I've
got
a
lot
of
guys
that
are
experts.
You
have
expertise
in
TCP
delivery,
a
quick
delivery,
not
so
much.
What
do
we?
What
do
I
even
have
to
ask
the
questions
of
so
what
we've
taken
on
is
doing
a
PLC,
but
it's
sort
of
a
meta
PLC.
F
In
addition
to
ultimately
measuring
you
know,
quick
delivery
versus
HTTP,
2
delivery,
we're
also
documenting
how
do
you
build
that
test
environment
so
that
people
who
want
to
play
with
a
quick
technology
for
streaming
delivery
have
a
framework
that
they
can
take
and
then
they
in
their
own
environments,
can
build
it
test
it
and
run
it,
and
this
involves
things
like
metrics.
You
know
how
do
you
hook
into
players
on
on
this
on
the
player
side
and
collect
data
for
them?
How
do
you
monitor
on
the
network?
F
And
how
do
you
ask
the
questions
and
what
questions
should
you
even
be
asking
when
you
want
to
evaluate
and
understand
quick,
better
next
slide,
please,
and
in
fact,
one
of
the
exercises
we're
doing
isn't
at
the
very
end
of
that
PLC
to
produce
a
final
report
with
a
lot
of
glossy
slides.
What
we're
doing
is
along
the
way
we
are
documenting
the
thought
process,
that's
going
into
the
quick
PLC,
so
one
of
these
we've
already
produced
we've
produced
a
tech
brief
that
talks
about
quick
overall
to
the
streaming
environment.
F
And
why-
and
why
would
you
even
do
that
particular
test
and
ask
the
question:
are
there
tests
that
we're
missing
that
are
relevant
to
the
professional
media
environment
and
that's
available
at
the
link
down
below
next
slide?
Please
so
there's
a
few
of
us.
Actually,
the
participants
here
in
the
svta,
but
so
Sanji
over
here
is
one
of
the
chairs
over
there
and
there's
the
email
address.
F
If
you
want
to
find
out
more
information,
I'll
point
out
Ali
as
well
a
chair
over
at
a
working
group
on
players
and
I
chair
that
we
can
Transport
Group.
So
if
you're
interested
in
any
of
the
work
we're
doing
if
you've
got
comments
again,
we
release
it
publicly.
So
you
can
go.
Take
a
look!
You
don't
have
to
be
a
member
to
read.
E
And
again,
I'll
encourage
people
to
use
the
media
Co
Mike
line.
One
thing
that
I'd
like
to
sort
of
reiterate,
while
waiting
to
see
if
there
are
questions
or
thoughts,
is
one
of
the
reasons
why
we're
particularly
Keen
to
have
these
ongoing
updates
from
the
svta
is
the
fact
that
that's
the
the
alliance
of
Industry
players
who
are
deploying
this
stuff
and
using
it
at
scale
so
I
mean
I.
E
F
And
we've
also,
you
know,
the
Outreach
between
the
two
groups
has
resulted
in
a
whole
pile
of
people
that
are
svta
people
who
didn't
previously
come
to
ITF
meetings,
they're
now
coming
to
ITF
meetings
and
engaged
in
the
working
groups
here,
which
is
really
awesome.
That's
something
I've
championed
for
a
long
time
to
get
more
media
people
into
the
room
here
and
we're
getting
them
and
I'm
really
happy.
Success
is
always
good.
F
It's
already
gdp3
the
framework
yeah.
It's
it's
we're
not
trying
to
get
into
the
weeds,
yet
whether
it's
really
just
using
it
as
a
as
a
as
a
transport
pipe.
Okay
right,
thanks
very
much
but
maybe
down
the
road
we'll
play
with
you,
know
we'll
get
in
and
play
with
some
really
cool
stuff,
but
baby
steps.
Yeah.
G
J
Hello,
everybody
so
I
I
will
present
now
follow-up
of
the
one
project
that
we
have
in
in
telefonica.
The
idea
is
to
deploy
Alto
for
integrating
for
exposing
the
network
topology
that
could
be
consumed
by
the
telephonica
CDN.
So
this
is
an
update
from
last
IDF.
So
next,
please
so
the
the
rationale
for
the
work
as
a
reminder.
Well,
the
idea
is
to
optimize
the
delivery
of
the
traffic
right.
So
nowadays
the
the
CDN
in
telefonica
is
consuming
the
topology,
but
is
a
loaded
uploaded
manually.
J
J
Let's
say
we
of
this
uploaded
upload
and
there
are
changes
in
the
topology
and
these
changes
are
missed
as
are
lost,
so
the
idea
is
to
have
an
automated
way
of
populating
the
topology
in
such
a
way
that
telephotical
CDN
could
have
a
timely
view
of
the
topology
in
in
every
moment,
right
so
taking
the
best
decisions,
not
only
thinking
on
on
the
capabilities
of
the
cache
node,
but
also
on
the
transport
circumstances,
transport
situation.
So
this
project
was
presented
in
in
last
idea,
so
I
recommend
the
the
progress
on
that.
J
So
next,
please
yeah
also
as
a
reminder.
We
are
playing
essentially
with
two
concepts:
the
network
map
and
the
cost
map
and
the
network
map.
Essentially,
we
identify
we
associate
in
different
pids,
the
prefixes
or
of
the
let's
say
the
endpoints
of
of
of
the
map.
In
this
case
the
endpoints
will
be
the
prefixes
for
the
end
users
on
one
side,
so
the
ones
that
are
requesting
the
content
and
another
side,
the
the
endpoints
will
be
the
cdns,
the
caches
itself.
J
So
we
will
have
the
ideas
to
have
a
number
of
pids,
considering
all
this
kind
of
endpoints
right
and
then
we
will
have
the
the
cost
map.
The
cosmap
essentially
shows
the
relationship
in
terms
of
some
metrics
between
those
pids.
In
this
case,
the
method
that
we
are
using
by
now
is
the
number
of
hops
the
ideas
to
improve
and
to
enrich
all
this
metric
in
the
future.
Adding
performance
capabilities
like
latency
and
and
so
so
important
to
say,
the
the
network
map
is
essentially
retrieved
through
bgp.
J
So
the
idea
is
that
the
alto
contains
a
bgp
speaker.
The
bgp
speaker
is
connected
to
Raw
reflectors
in
the
network
for
collecting
this
information
from
the
user
so
dep
session
in
the
in
that.
In
that
point,
and
the
cost
map
is
retrieved
by
leveraging
on
bgpls,
so
bdpls
provide
us.
They
build
the
topology
how
the
different
nodes
are
interconnected
in
the
network,
so
having
a
view
of
the
number
of
hops
or
some
other
capabilities
that
could
be
exposed
by
vdpls
next,
please
so
the
process
follows
so
far.
J
J
So
next,
please,
there
was
at
the
time
of
running
in
the
parade.
There
was
an
initial
constraint,
an
initial
restriction.
So
this
is
a
kind
of
of
level
shows.
You
are
a
basic
topology
basic
hierarchy
that
we
have
in
telephonical
network,
so
we
have
more
or
less
one
to
five
levels.
In
some
cases,
six
depends
on
the
size
of
the
country,
the
being
the
level
one
interconnection
within
the
the
lower
part,
the
SLC
router.
J
So,
between
the
backbone
level,
I
mean
the
the
mesh
of
the
routers
and
connecting
or
moving
the
traffic
in
a
national
in
the
National
footprint
and
connected
with
the
different
regions.
We
have
some
issue
with
one
of
the
vendors
one
of
the
rotor
vendors,
the
ability
system
that
we
have
the
dealing
support
or
had
promised
for
supporting
bgpls
for
ospf.
J
So
we
are
trying
to
fix
that
this
was
an
initial
constraint,
so
we
know
in
advance
that
we
will
not
collect,
or
we
will
not
be
able
to
collect
in
this
point
or
to
retrieve
in
this
point
the
complete
topology,
but
at
least
we
have
a
region
that
is
completely.
We
have
all
this
over
there,
so
at
least
this
would
be,
let's
say,
the
the
the
the
POC
we
will
be
focused
on
this
region
by
now.
Next,
please
so,
after
realizing
the
book
The
Pilot.
J
So
in
a
preliminary
analysis
that
we
are
running,
we
have
some
good
news
and
not
so
good
news,
so
we
present
first
the
good
news,
so
we
are
retrieving
a
good
amount
of
summarize
summarize.
Ip
address
ranges,
so
these
are
ranges
that
are
used
for
fixed
mobile
and
Enterprise.
This
is
more
or
less
as
expected.
J
Also
as
one
of
the
IP
ranges
are
external.
This
is
understandable
ones
that
we
are
collecting
and
are
those
for
the
in
the
for
the
national
interconnection.
The
point
is
in
the
telephonic
and
international
interconnection
is,
is
run
by
a
career,
a
tier
one
career
also
from
the
telephonical
group.
So
what
we
are
collecting
here
is
only
the
national
interconnections
that
are
being
run
by
this
operation
in
telefonica.
J
This
is
good
because
in
the
telephonica
CDN
is
serving
also
traffic
to
external
customers.
So
it's
good
to
have
a
a
view
of
those
that
are
not
from
telephonica
side.
If
we
have
in
the
National
interconnection
or
in
international
interconnection
is
certainly
true
that
this
could
be
obtained
by
other
means,
but
here
we
could
have
an
automatic
automatized
way
of
of
collecting
and
and
aggressive
retrieving
information
that
those
customers
are
rich
by
certain
nodes
that
are
serving
the
national
interconnection.
J
So
we
could
optimize
the
traffic
also
for
those
external
customers
that
are
not
part
of
telefonica.
The
available
information
in
the
course
map
is
currently
retrieved
as
well
and
reflects
the
defined
IEP
metrics.
So
that
is
working
fine.
So
we
are
not
taking
only
the
number
of
hops,
but
also
we
are
taking
the
the
proper
geometric
defined
on
those
links
between
the
nodes
and
from
the
perspective
of
the
alto
server
itself.
J
The
the
load
of
the
service
is
not
significant,
so
we
are
retrieving
all
the
topology,
even
though
we
cannot
relate
because
we
have
that
gap
for
the
VIP
less
the
ospf
that
I
mentioned
before.
We
cannot
Stitch,
let's
say
all
the
nodes,
but
we
are
retrieving
the
information
from
all
the
nodes
and
the
load
of
the
server
is
not
not
high,
so
it
seems
to
be
sufficiently
I
mean
scalable.
J
So
next,
please,
in
this
slide,
I
show
you
just
an
example
of
the
network
map
retrieve
the
real
level
map
and
the
real
cost
map.
I
put
some
asterisk
on
the
pids
just
to
let's
say:
don't
disclose,
let's
say
the
the
real
information
of
the
network,
but
you
can
see
the
IP
addresses
from
the
phonica
site
and
also
you
can
see
the
in
the
cost
map
the
actual
igp
metrics
between
different
mpids.
J
So
this
is
being
collected
properly
at
this
point
in
time.
So
next,
please
they're,
not
so
good
news
or
the
the
news
that
well.
The
points
that
we
need
to
to
keep
working
on
is
that
we
don't
have
information
for
some
pops,
the
four
percent
of
the
pops.
We
are
not
receiving
information,
so
we
need
to
analyze
what
what
are
the
particularities
of
these
pops?
Why
these
pops
are
not
populating
the
information.
J
Also,
some
of
the
IP
ranges
seems
not
to
be
retrieved,
so
we
need
to
check.
We
have
the
proper
bgp
sessions
established.
So
probably
we
could
be
the
case
that
we
need
to
connect
to
some
other
some
additional
root
reflector.
So
this
is
also
understudy
and
probably
a
more
complex
problem.
Is
this
the
third
one
that
we
only
have
27
pids
both
in
the
network
map
and
the
cost
map?
J
This
could
be
the
case
of
the
ospf
issue
for
the
bgplse
information
that
I
mentioned
before,
but
we
need
to
further
Analyze
This
to
to
verify
that
this
is
the
point
and
also
the
the
latest
one,
the
pids
for
the
CD
CDN
nodes,
the
caches
are
not
yet
captured,
so
probably
probably
is
also
a
matter
of
connecting
to
a
new
reflector.
So
this
is
as
well
under
study.
J
So
as
next
steps
for
the
pilot
itself
to
understand.
The
first
point
will
be
how
to
understand:
I
mean
understand
how
to
consume
the
other
information.
So
how
often
so
we
need
now
to
enter
into
their
operability
of
the
health
information
so
yeah
to
define
the
frequency
of
Retribution
topology
analyzing,
the
topology
and
uploading
the
topology
automatically.
Also,
we
need
to
continue
analyzing
the
information
received
to
understand
the
Dynamics
in
a
production
Network,
so
how
the
changes
have
reflected
how
how
we
can
be
sure
that
we
don't
lose.
J
Let's
say
any
any
kind
of
change
in
the
network.
Also,
we
need
to
debug
the
issues
that
could
be
funded
in
the
process.
So
this
is
a
new
process
and
we
don't
have
an
operational
experience
on
that
and
then
we
need
to
wait
for
sure
until
the
resolution
of
the
operating
system
of
this
router
vendor
to
be
ready
for
having
the
possibility
of
a
stitch
in
all
the
areas.
All
the
pids
and
completely
see
the
map
of
all
the
network.
J
So
all
the
security
concerns
the
logins
all
the
kind
of
this
kind
of
stuff,
the
logs
and
so
and
and
then
also
to
work
on
the
loading
automatically
the
topology
into
the
logic
of
the
telephonica
CDN.
So
by
now
we
can
retrieve
the
the
topology,
but
there
is
just
tending
to
to
interest
me
to
work.
Let's
say
to
integrate
that
with
the
logic
of
the
telefonica
CDN
in
such
a
way
that
could
be
essentially
automatically
done
working
group.
J
J
For
instance,
we
are
now
seeing
that
probably
we
need
to
lose
something
into
the
security
part,
so
so
how
obfuscate
the
the
pids,
and
so,
if
we
are
exposing
this
to
third
parties,
so
that
would
be
a
matter
to
let's
say
no,
not
reveal
a
sensible
information
and
then
well,
and
the
next
step
finally,
step
for
sure
is
to
provide
another
update,
if
possible,
in
the
next
ITF
and
hopefully
with
all
the
solves
the
issue.
Let's
see
if
we
are
able
to
do
to
do
that
and
I
think
that
that
was
the
biggest
one.
E
E
D
I
L
L
One
recent
kind
of
a
perfect
example
is
for
those
not
familiar
Thursday
night
NFL
Thursday
night
football,
which
is
American.
Football
is
in
the
last
two
months
for
the
first
time
ever
is
being
streamed
exclusively
over.
The
Internet
Amazon
Prime
announced
that
the
first
game,
which
was
in
mid-september
had
I
believe
over
11
million
stream
streams.
L
L
One
thing
to
keep
in
mind
is
live
streaming
is,
is
has
a
unique
set
of
requirement,
characteristics
that
are
different
from
say,
on-demand
streaming,
you
know,
they're
some
folks
have
said
hey.
What's
the
difference
between
live
streaming
versus,
you
know
people
just
watching
on-demand
movies.
You
know
on
Netflix,
you
know
if
if
people
are
going
to
be
watching,
you
know,
there's
a
fair
amount
of
saturation
and
people
are
on
a
given
evening,
they're
probably
going
to
be
watching
something.
L
L
So,
for
example,
if
you
have
you
know,
if
you're
watching
a
movie,
you
can
live
with
a
minute
or
two
play
out
buffer.
You
know
the
movie
was
made
perhaps
years
ago.
So,
on
the
other
hand,
if
it's
a
if
it's
a
sporting
event,
you
know
much
longer
than
say
you
know.
10
seconds
the
traditional
broadcast
television
has
had,
you
run
the
risk
that
you
can
get
a
text
message
from
your
friend
saying
man,
what
an
incredible
you
know,
game-winning
score.
L
You
know
a
minute
or
so
before
it
actually
happens,
or
you
hear
people
cheering
next
door
or
at
a
bar
before
you
know
a
minute
before
you
see
what
happens,
and
then
you
know
that
for
for
use
cases
on
things
like
in-game
micro,
betting,
the
the
latency
requirements
are
even
tighter.
The
other
thing
is
join
rates
and
traffic
rates
are
vastly
different
depending
on
demand
and
live
streaming.
L
If
you
look
at
the
typical
traffic
streams
on
a
service
provider,
what
you'll
see
is
kind
of
a
very
smooth,
predictable
growth
rate.
There's,
you
know
we've
all
seen
kind
of
those
diurnal
patterns
of
you
know.
It
starts
out
at
about
9,
00
a.m
and
Rises
till
about
five
and
then
drops
and
then
about
8
P.M
up
till
about
midnight.
L
L
L
You
know
this
is
a
much
more
efficient
way
of
of
delivering
this
content
and,
and
specifically
multicast
has
been.
You
know.
This
is
what
multicast
is
out
there
for,
and
it
has
been
fairly
successful
in
some
use
cases,
it's
absolutely
vital
in
financial
networks
for
video
distribution
networks,
it's
commonly
used
as
well,
as
you
know,
VPN
service
providers
and
some
Enterprises.
L
There
have
been
over
the
years.
You
know
the
best
best
way
to
describe
the
issues
with
with
internet
multicast
has
been
it's
been
kind
of
like
three
main
problems
with
Internet
multicast
one
is
the
All
or
Nothing
problem,
and
that
is
for
for
multicast
the
work
you
need.
Every
single
layer,
three
hop
between
the
source
and
destination
to
be
multicast
enabled
needs
to
be
running
some
type
of
multicast
routing
protocol,
and
it
turns
out
having
every
single
interface
on
every
single,
router
and
firewall
on
the
internet.
L
Running
a
complex
set
of
protocols
is
a
pretty
high
bar
and
it's
it's.
It's
proven
to
be
really
really
difficult
to
get
everyone
to
do
something
like
I
said,
I
think
V6
has
has
a
similar
problem,
anything
that
requires.
You
know
that
kind
of
level
of
change
on
the
Internet
ubiquitously
is
going
to
struggle
for
traction
and
deployment.
L
The
second
problem
has
been
you
know.
Anybody
who's
familiar
with
multicast
is,
is
probably
aware
of
the
the
challenges
and
the
complexities
of
of
of
deploying
and
operating
a
multicast
network
operators
have
long
complained
that
you
know
the
the
protocols
are
really
complex
and
it's
too
difficult
and
too
difficult
to
deploy,
operate.
L
Troubleshoot
and
you
know
they've
they've
complained
for
for
years
that
just
multicast
is
just
too
complex
and
then,
of
course,
there's
the
chicken
and
egg
problem,
which
is
you
know,
there's
no
multicast
audience,
because
there's
no
multicast
content
and
there's
no
multicast
content,
because
there's
no
multicast
audience
so.
The
good
news
is
there
have
been
recent
developments
in
network
replication,
Technologies
that
are
available
today
to
address
these
problems.
So
you
know
these.
You
know
the
the
it's
not
your
your
grandfather's
internet,
multicast
Solutions.
Today.
L
We
now
have
solutions
that
address
these
problems
and
I'll
kind
of
go
through
those.
So
what
is
tree
treaty
end
tree-based
cdns?
It
leverages
advances
in,
and
developments
in,
Native
Technologies,
as
well
as
overlay
Concepts,
to
deliver
a
service
to
end
users,
even
where
parts
of
the
network
don't
support
multicast.
L
L
L
Ssm
is
source-specific
multicast
and
it
vastly
simplifies
the
the
deployment
of
multicast
and
with
with
SSM,
you
eliminate
a
lot
of
the
complexities
and
headaches
of
multicast
things
like
Rendezvous
points
and
msdp
and
shared
trees.
Pim
register
messages
register
end
cap,
dcap
tree
switch
over
data-driven
State
events.
L
The
point
is,
if
you
just
use
SSM,
you
can
address
the
most
common
use
cases
and
eliminate
a
lot
of
the
complexity
of
multicast
deployment.
The
second
key
component
of
treaty
n
is
overlays
and
automatic.
Multicast
tunneling
AMT,
which
is
described
in
RFC
7450,
is
a
technology
that
dynamically
builds
tunnels
from
end
hosts.
L
So
it
allows
users
on
unicast,
only
networks,
unicast
only
parts
of
the
network
to
Tunnel
dynamically
to
the
the
edge
of
the
multicast
network
and
receive
content.
So
this
enables
any-
and
everyone
who
is
on
the
internet
with
AMT
is
able
to
receive
multicast
content,
even
if
they
are
not
on
a
multicast
enabled
Network.
G
L
This
solves
the
All
or
Nothing
problem
that
fundamental,
you
know,
probably
the
biggest
of
the
three
Pro
by
far
problem
of
All
or
Nothing
also
solves
the
chicken
and
egg
problem,
because
with
AMT
potentially
any
every
single
post
on
the
Internet
is
a
potential
audience.
Member
am
AMT
is
the
most
common.
Has
some
really
nice
benefits,
because
it's
a
dynamically
built
tunnel,
it
can
be
integrated
into
the
application
or
in
the
host
stack,
but
any
other
overlay.
L
L
The
key
thing
is
treaty
n
provides,
you
know
a
significant
benefit
that
previously
was
not
available
with
multicast,
which
is
incremental
deployment
for
those
parts
of
the
network
that
are
multicast,
enabled
they
enjoy
the
benefits
of
multicast
and
for
the
rest
of
the
network.
That
is
unicast
only
we
simply
we
simply
tunnel
over
those
parts
of
the
network,
so
end
users
receive
the
service,
regardless
of
what
the
what
the
topology
looks
like
and
you
know
significantly
end.
L
So
here's
kind
of
a
a
30,
000
foot
view
of
what
treaty
end
looks
like
and
they
they
those
familiar
with
IP
multicast
technologies
will
notice
that
there's
there's
no
there's
nothing
groundbreaking
or
really
new.
From
a
protocol
standpoint,
it's
really
the
synthesis
of
existing
tools
and
existing
protocols
to
Define
an
architecture
and
describe
an
architecture
that
operators
can
leverage
and
service
providers
can
use
to
deliver
new
Services
for
customers
and
end
users.
L
That's
kind
of
the
high
level
view
of
the
whole
internet
and
where
treaty
n
fits
within
that
ecosystem
kind
of
drilling
down
into
you
know.
What
does
you
know?
What
would
the
treaty
end
part?
Look
like.
Let's
compare
it.
A
treaty
end
to
a
CDN
without
multicast
there's
different
models
for
cdns,
but
a
common
one.
Is
you?
L
Have
a
An
Origin
a
source
with
content
that
kind
of
pushes
it
out
to
CDN
boxes,
pushes
it
to
one
and
they
kind
of
distribute
it
and
those
CDN
boxes
that
are
deployed
throughout
the
network,
handle
local
receivers
much
more
scalable
than
unicast.
Obviously,
and
has
the
nice
benefit
of
not
requiring
you
know,
just
works
over
the
Internet
doesn't
require
you
know
a
set
of.
It
doesn't
require
multicast
protocols
to
make
it
work.
So
that's
why
it's
been
popular.
L
That
said,
you
know,
with
treaty
end
to
compare
with
cdns
without
multicast.
We
can
rename
these
those
CDN
boxes,
we'll
call
them
AMT
relays
push
them
out
to
the
Border
of
the
network
and
they
deliver
traffic
notice
that
the
the
the
the
multicast
tree
gets
delivered,
natively
from
The
Source
to
those
AMT
receivers;
I'm.
L
L
If,
if
there
are
no
interested
receivers
in
an
area,
those
relays
will
not
participate
in
the
tree
and
the
key
difference.
The
key
value
is:
if
those
AMT
relays
are
deployed
on
existing
Network
infrastructure,
it's
essentially
a
CDN
on
a
chip.
This
there
are
routing
router
platforms
out
there
that
support
AMT
tunneling
natively,
and
what
that
means
is
you?
If
you
have
these
devices
in
your
network,
at
the
borders
of
your
network,
say
it
period
points
or
Edge
routers?
L
You
can
offer
this
service
at
essentially
zero
cost
at
only
the
cost
of
configuring,
a
few
lines
of
config
on
your
on
your
routers.
So
it's
essentially
zero
capex
and
you
can
argue,
you
know
zero
Opex,
because
you're,
not
you
know
typically
CDN
boxes
in
these.
You
know
a
stack
of
x86
boxes
that
are
sitting
in
a
network
that
need
to
be
racked
and
powered
and
plugged
into
Revenue
generating
ports
on
on
routers
and
the
network
infrastructure.
We.
L
L
L
You
know
the
experience
of
sitting
Courtside
at
a
you
know,
front
front
row,
Center,
Court
at
a
basketball
game
or
a
you
know,
a
soccer
football
game.
What
it's
like
to
to
sit
in
the
stadium
and-
and
you
look
left
and
right-
we
see
the
crowd
and
you
see
the
game
as
if
you're
there,
and
what,
if
you
wanted
to
to
deliver
those
those
streams,
live
to
mass
audiences
of
thousands,
tens
of
thousands,
perhaps
Millions.
L
L
It
enables
service
providers
and
operators
to
offer
new
Services
replication
as
a
service.
Send
us
your
content,
we'll
replicate
it
and
we'll
deliver
that
to
to
end
users,
I
mean.
Essentially,
this
is
what
cdns
have
always
been,
but
what's
what's
key
here
it
is.
It
allows
operators
to
offer
this
service
at
potentially
zero
cost
to
deliver
the
service.
If
existing
infrastructure
already
supports
AMT,
it's
also
an
open,
open,
standards-based
architecture.
That's
used
using
that's
leveraging
widely
available
protocols,
as
opposed
to
some.
L
Essentially,
you
know
with
treaty
end,
the
CDN
is
just
forwarding
packets,
there's
no
need
for
storage
or
data
protection
or
key
management.
Things
like
that,
just
just
pushing
out
packets,
the
other
nice
part
of
this
technology
is.
It
is
a
democratizing
and
decentral.
It's
it's
a
decentralized
architecture
which
essentially
makes
it
exceedingly
inexpensive
for
sources
to
send
High
data
rate
streams
to
met
to
an
arbitrarily
large
audience.
L
So
live
streaming,
isn't
the
obvious,
and
you
know
sexiest
use
cases
you
know
typically
Multimedia
Audio
Video,
specifically
AR
could
also
be
Telemetry
data
from
things
like
you
know,
imagine,
weather
satellites
that
need
to
push
out
real-time
Telemetry
data
to
research
institutions.
That's
one
use
case,
but
there's
also
a
large
file.
Software
updates
things
like
OS
upgrades.
Those
are
you
know
things
that
can
really
crush
a
network.
L
L
It's
really
about
kind
of
the
the
there's
there's
these
Crossing
of
supply
and
demand
curves
when
it
comes
to
live
streaming
on
the
internet.
On
the
demand
side,
it's
really
that
combination
of
exploding
audience
sizes
combined
with
increasing
bit
rates
to
to
generate
you,
know
large
amounts
of
Demand
on
the
internet
for
live
streaming
and
the
potential
resource
consumption
implications
on
the
network
and
on
the
supply
side.
L
You
know
for
for
those
who
kind
of
tuned
out
and
said
you
know
15
years
ago
and
said
you
know:
multicast
isn't
viable.
Let's,
let's
not
waste
our
time
on
this.
You
know
there
have
been
developments
in
evolution
in
in
how
multicast
can
can
replicate
across
the
Trap
across
the
internet
and
address
the
issues
that
you
know
plagued
internet
multicast.
L
You
know
in
in
previous
decades,
so
it
is
now
easier
to
deploy
and
more
available
and
useful
than
ever.
So
it's
really
kind
of
the
the
synthesis
of
existing
tools
to
address
you
know.
A
very
recent
phenomena
where
you
know
live
streaming
is
consuming
significant
amounts
of
resources
in
the
networks
and
that's
what
that's
what
treaty
end
is?
D
Thank
you
Leslie,
so
I'm
speaking
as
you
know,
with
Hats
Off,
not
as
chair
here,
I
have
a
a
couple
of
points.
So
I
read
the
I
read
the
draft.
When
you
initially
made
the
request
to
to
presented
mops
and
I
thought
it
was
really
interesting.
The
presentation
here
has
has
answered
a
bunch
of
the
questions
that
I
had
after
reading.
D
The
draft,
but
I
still
have
some
I
still
have
some
issues
and
I
don't
know
if
we
want
to
go
into
all
of
these
at
the
moment,
but
I
can
maybe
outline
what
I
was
thinking.
So
the
the
issue
of
or
the
the
benefit
that
you
say
about
a
democratizing
Content
distribution
is,
you
know,
I,
take
that,
as
as,
like
that's
a
good
point,
I'm
not
sure
like
that.
It
that
addresses
democratization,
of
availability
of
the
of
the
the
the
sort
of
replication
function,
the
fan
out
function.
D
It
doesn't
address
the
democratization
of
content.
Right
I
mean
there
are
rights
holders
that
have
you
know
that
have
access
to
that
have
exclusive.
You
know,
access
to
say,
sporting
events
and
that's
not
gonna.
That's
not
gonna
go
away,
you're
not
going
to
be
able
to.
You
know
legally
broadcast
some
some
soccer
game
right
that
you
don't
have
rights
to
broadcast
I
mean
you
might
be
able
to
do
it
technically,
but
somebody
will
shut
it
down.
D
So
there's
that
issue,
but
you
also
I
mean
there's
a
you're,
essentially
you're,
introducing
a
novel
attack
surface
when
you
have
replication
as
a
service
and
so
not
having
any
controls
over
that
seems
like
it.
It
at
least
requires
a
significant
amount
of
thought
to
figure
out
how
to
avoid
problems
with
that
right.
D
The
other,
the
only
other
thing
that
that
I,
that
I
was
thinking
of
as
a
I
mean
I'm
not
trying
to
I'm
not
trying
to
throw
cold
water
on
this
I'm,
just
trying
to
bring
up
a
bunch
of
a
bunch
of
things
that
I
thought
of
when
I
was
when
I
was
reading.
The
the
draft
and
listening
to
your
presentation
is
the
you
know
related
to
the
the
content
rights
issue.
Is
you
say?
Well,
you
know
there's
no
key
management.
D
You
know
what
are
what
are
the
the
consequences
of
outside
observers
being
able
to
know
what
content
you're
consuming
and
how
do
you?
You
know?
How
do
you
kind
of
fit
that
into
the
web
security
model?
And
it's
not?
There
are
a
lot
of
subtleties
there
and
I,
don't
think
we've
even
kind
of
teased
them
all
out
yet,
but
I'm.
It's
something
that
I'm
happy
to
to
help
to
help
work
on
to
to
push
this
work
forward.
D
L
L
L
C
L
Surface
multicast
has
a
different
attack
surface
than
unicast
I,
wouldn't
say
that
it's
more
risky
or
less
risky
I
think
it's
in
some
cases
it
is
more
it.
It
just
has
different
risks.
So
so,
for
example,
things
like
spoofing,
you
know
because
multicast
has
RPF
built
into
it.
Naturally,
you
can,
you
know,
eliminate
lots
of
spoofing
attacks.
You
know
on
the
data
plane,
so
it's
you
know
in
some
ways
more
resistant
to
certain
data
plane
attacks.
L
However,
it
is
more
vulnerable
to
say,
control,
plane
attacks,
because
you
have
users
generating
control
traffic
on
the
network
in
ways
that
you
don't
necessarily
have
with
unicast,
so
I,
don't
know
that
it's
more
insecure
or
less
insecure.
It's
just
it
has
a
different
attack
surface
and
there's
lots
and
lots
of
work
over
the
years
that
kind
of
describes.
L
You
know
how
to
harden
a
a
deployment
to
address
some
of
those
security
issues
and
the
last
thing
about
the
key
management
stuff
that
you
mentioned:
I,
guess
what
what
I
meant?
You
know
what
is
meant
there
is
that
there's
you
still
have
key
management
issues,
but
it's
it
goes
on
between
the
the
content
provider
and
the
end
user.
So
you
can
do
things
like
encryption
and
you
don't
necessarily
have
to
the
the
the
intervening
players
between
say
the
CDN
provider.
L
D
I
So
everything
the
responsibility
for
mobs.
So,
regarding
your
last
line
on
these
slides,
it
looks
for
me
that
document
I
still
have
to
read
it.
To
be
honest,
it
looks
more
like
best
human
practice
or
informational
about.
Oh,
you
can
stitch
existing
Technologies
together.
So
mobs
would
be
the
perfect
working
group
for
this
right.
I
We
are
not
allowed
to
do
any
kind
of
protocol
work
so
if
you
need
to
do
extension
to
AMT
or
whatever
and
Bone
right,
but
you're
more
than
welcome
here
and
I
hope
that
Cal
will
write
his
questions
on
the
mailing
list
and
we
got
a
review
at
this
one
now
as
an
individual
contributor,
I,
just
wonder
and
I
see
your
co-authors
from
Verizon.
So
do
you
intend
to
run
some
proof
of
concept
to
get
the
scalability
issue
fixed,
for
instance,
or
identified.
L
So
the
the
there
are,
this
is
actually
being
you
know
in
use
and
deployed
today
across
the
internet.
There
there
are
providers
that
and
and
I
welcome
you
to
join
us
in
mbon
d
and
there's
going
to
be
an
operator
who
will
talk
about
how
they're
essentially
doing
this
in
their
Network
on
Wednesday
morning.
So
yes,
this
is,
and
there
has
been
a
a
a
treaty
and
network.
L
That's
been
up
and
running
for
the
last
few
years,
it's
connected
to
Internet
two
and
giant
nodes
and
has
been
delivering
content
using
this
architecture
for
the
last
few
years.
So
yeah
we'd,
it's
it's
not
just
Verizon,
but
it's
it's.
It's
been.
It's
been
deployed
by
a
number
of
operators
on
the
internet
and
and
that's
not
to
say
by
the
way,
I
I'm,
not
don't.
L
I
can't
speak
for
my
co-author
in
terms
of
what
his
company
is
doing
in
terms
of
whether
they
are
aren't
delivering
this
service,
but
it
is
being
used
on
the
internet
today.
So
this
is
really,
as
you
said,
Eric
there
are
new,
no
new
protocols
here
if
it
was
actually
that
would
probably
belong
in
Pim
and
Bundy.
E
L
It
definitely
does
not
use
TCP
because
it's
multicast
doesn't
support
TCP,
so
it's
typically
UDP
were
kind
of
agnostic
to
the
transport
as
long
as
it's
on
IP
multicast
packet.
So
any
any.
Let
me
put
another
way
any
non-tcp
traffic
that
is
multicastable
Can
can
utilize
this
technology,
it's
kind
of
agnostic
to
the
to
what
transport
Protocols
are
used.
