►
From YouTube: IETF115-HOTRFC-20221106-1800
Description
HOTRFC meeting session at IETF115
2022/11/06 1800
https://datatracker.ietf.org/meeting/115/proceedings/
B
B
B
B
B
I
wasn't
sure
I
was
going
to
be
so
hi
everybody
we're
just
getting
ready
to
get
started
here
and
I
think
we're
ready
to
get
started
and
I
think
everybody
has
come
over
from
the
welcome
perception.
I
am
Spencer
Dawkins.
This
is
the
lovely
Alexa
Morris
and
we
are
joined
in
Spirit
by
Liz
Flynn,
also
of
the
Secretariat,
who
was
expecting
to
be
here
right
up
until
she
was
not
feeling
well
and
is
up
resting
in
her
room.
So
please
keep
our
thoughts
as
well.
B
Okay,
this
is
the
first
note.
This
is
the
first
session
of
this
ITF
meeting,
so
there
are
will
be
some
newcomers
who
have
not
seen
the
note
well
at
the
beginning
of
every
session,
and
there
will
be
some
who
haven't
seen
it
in
four
months
and
haven't
thought
about
it.
This
is
basically
covering
the
obligations
of
a
someone
who's
contributing
to
the
ietf,
which
is
what
100
RC
topics
are
doing.
B
So
in
person
participants
please
sign
in
using
the
meat
Echo,
probably
the
like
client.
This
does
the
blue
sheets
and
please
wear
masks
unless
you're
actively
speaking
at
the
microphone
and
if
you're,
using
the
full
thing.
Please
keep
your
audio
and
slides
off
if
you're,
not
using
the
on-site
version
and
use
masks,
as
we
say,
less
actively.
B
Speaking
at
the
microphone
note,
participants,
please
make
sure
your
audio
and
slides
are
off
unless
you
are
sharing
or
presenting
during
a
session
and
the
use
of
a
headset
is
strongly
recommended
and
that's
why
please
just
to
put
up
some
resources
for
ITF
115
in
London.
Welcome
back
to
London
and
please
especially,
keep
an
eye
on
the.
If
you
need
technical
assistance,
see
the
reporting
issues
page.
B
Yeah,
okay,
yeah
yeah
I
I
used
that
this
afternoon,
ground
rules
are
that
you
are,
we
are
doing
requests
for
conversation
here.
It's
a
good
way
to
find
people
at
the
ITF
to
talk
to
for
various
reasons,
and
we
don't
actually
gate
people.
What
those
reasons
are
presenters
will
tell
you
about
that.
Each
person
gets
four
minutes
from
go
to.
Please
applaud
at
four
minutes.
We
will
start
uploading,
we'll
practice
that
on
the
next
slide,
when
you
hear
Applause,
please
hand
the
microphone
over,
we
don't
do
questions
here.
B
B
B
B
C
D
You
timing,
I'll
start
now:
yeah
I'm,
Phil,
hi
Phil.
So
next
slide,
please.
So
you
might
have
seen
this
tweet
go
out
in
the
Tweeter
verse
that
Burning
Down
The
twitterverse
might
be
an
accelerant
to
creating
X
the
everything
app,
and
that
had
me
thinking,
because
in
the
comments
next
slide,
please
one
of
the
comments
was
well.
D
If
you
want
to
deliver
an
end-to-end
secure
everything
app
in
2023,
you
better
have
started
five
years
ago,
I
thought
yeah,
who
has
been
writing
and
everything
at
for
five
years
now
next
slide.
So
the
mesh
was
designed
I've
been
talking
about
this
here.
For
you
know,
we
had
that
buff
in
Singapore
I've
been
mentioning.
Yes,
it's
designed
to
do
end-to-end,
secure,
messaging,
key
management
and
so
on.
D
One
thing
that
I
never
mentioned
next
slide
is
that
the
original
use
case
that
motivated
all
of
this
was
end-to-end
Secure
social
media
I
wanted
to
have
something
like
Facebook
or
Twitter,
except
that
I
wanted
all
my
content
to
be
encrypted
so
that
whoever
was
hosting
that
Service
couldn't
read
it
by
end-to-end.
Secure
I
mean
the
the
administrator
of
the
website
cannot
read
the
content.
End
to
end,
in
my
view,
is
from
my
eyeballs
to
whoever
wrote
so
it
was
always
in
the
plan
and
so
I
pulled
out
that
next
slide.
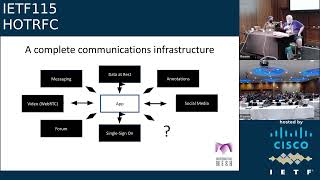
D
Please
and
so
yeah
I've
got
a
draft
out.
There
describes
how
to
use
the
mesh
to
build
a
complete
Communications
infrastructure,
and
actually
there
isn't
there
very
much
extra
work
to
do
social
media
on
top
of
synchronous
messaging
asynchronous.
Isn't
that
much
of
a
big
deal,
video
just
use
webrtc,
that's
already
done
all
the
heavy
lifting
to
do
that
part
of
the
communication
next
slide.
So
so
what
do
I
mean
by
an
open
social
media?
What
I
mean
is
I
own?
D
My
account
I
control
it
and
I
can
change,
take
it
from
one
service
provider
to
another
without
switching
costs,
without
losing
all
my
followers,
without
losing
all
that
context
that
I've
invested
that
belongs
to
me.
Not
my
publisher
and
I.
Want
you
to
be
able
to
choose
curators
who
are
choosing
content
for
them.
Not
have
somebody
with
an
algorithm
designed
to
make
me
engage
by
filling
my
feed
with
fascism.
D
I
want
a
Multiverse,
so
next
slide
so
I'm
building
this
stuff
and
of
course
what
people
will
be
saying
is
Well,
isn't
Mastodon
doing
something
like
that.
Well,
yes,
it
is
but
they're
not
using
cryptography,
not
yet
at
any
rate,
if
I
can
take
my
stuff
and
add
it
to
the
federal
verse,
so
it
becomes
the
encrypted
part
of
fediverse.
That's
great
to
me.
We've
got
all
that
encrypted
stuff
in
the
black
Network
and
there's
also
the
red
Network.
You
can
visit
for
the
things
that
don't
need
to
be
private
next
slide.
D
So
the
big
question
here
is:
what
do
we
call
it
and
I
think
I've
already
got
the
name.
You
know
everything,
and
you
know
it
might
be
the
co
Catalyst
to
building
the
everything.
So
if
you're
interested
in
building
a
social
media,
that
is
for
the
people
and
not
for
the
billionaires,
please
come
and
talk
to
me.
I've
got
a
draft
out
there,
everything
and
that
shows
how
you
don't
need
a
lot
of
mechanism
to
build
something
that
is
useful
and
matters.
E
Yeah
hi,
my
name
is
Roland
and
I'd
like
to
introduce
Kira,
which
is
a
scalable
ID
based
routing
architecture,
special
specially
designed
for
control
planes
and
for
control
planes.
Connectivity
is
really
important,
so
the
first
goal
is
to
uphold
the
connectivity,
while
the
second
goal
is
to
be
also
route
efficient
and
we
want
to
provide
a
highly
resilient
control.
Plane.
E
Scalability
was
one
objective,
and
here
we
targeted
at
hundred
thousands
of
nodes
which
could
be
present
at
a
single
domain.
We
route
on
node
IDs,
so
there's
no
natively
in
that
sense.
So
we
have
no
idea
to
locator
mapping,
for
example,
and
the
scalability
is
achieved
by
having
very
small
routing
tables
which
scale
algorithmically
with
a
number
of
nodes,
and
every
node
ID
has
an
Associated
path.
Vector,
which
stores
the
route.
The
routes
in
the
routing
table
actually
are
shortest
path.
E
It
also
works
well
on
various
topologies
out
of
the
box,
so
no
special
versions
for
data
center
topologies,
which
are
denser
than
other,
sparse
or
topologies,
and
so
on
required,
which
we
call
topological
versatility.
It
is
Loop
free,
even
during
convergence,
it
uses
path
IDs
as
labels,
and
it's
forwarding
tier
in
some
kind
of
label,
switching
and
so
out
of
the
box.
It
provides
zero
com.
Ipv6
connectivity
next
slide,
please.
E
E
It
also
supports
multi-path,
routing
and
forwarding
it
has
a
built-in
DHT,
which
is
a
key
value,
store
on
a
distributed
Manner
and
also
name
or
service.
Lookups
can
be
done
with
the
help
of
the
DHT
or
resource
Discovery,
and
recently
we
also
proposed
a
topology
very
efficient
and
scalable
topology
Discovery
scheme
based
on
that
key
resolution.
So
Kira
provides
highly
scalable
resilient,
Euro
control,
plane
connectivity
and
we
think
that
is
important
for
future
networks
because
they
are
getting
more
complex.
E
So
if
you
want
to
know
more,
there's
no
draft
out
yet
we've
tried
or
we
want
to
get
feedback
on
whether
people
find
this
interesting
to
standardize.
We
think
yes,
but
we
want
to
hear
your
feedback
so
there's
a
link
to
the
paper
and
I
have
two
presentation
schedules
at
this
ITF
meeting,
one
in
the
routing
area
working
group
meeting
on
Thursday
and
also
in
the
anima
working
group,
which
is
related
to
the
autonomous
control
plates.
Thanks.
A
F
Animation
but
I
guess
it
okay
anyway,
so
you
have
those
ran
elements
r-u-d-u-c-u
and
then
you
have.
Those
are
the
for
the
Wireless
part,
and
then
you
have
the
UPF.
It's
like
a
router
or
a
broad
Broadband
can
Network
Gateway
and
the
UPF
is
connected
to
a
Data
Network
with
UPF
being
distributed
nowadays
for
Edge
Computing
purposes,
now
the
UPF,
and
then
it
also
means
that
data
networks
are
also
being
distributed,
and
that
means
they
are
implemented
as
a
VPN.
So
you
have
the
p.
F
Is
there
and
so
the
CEUs
are
the
genobi
centralized
units?
Now
the
CU
UPF
and
P
is
they
are
all
co-located
at
the
same
Edge
data
center?
Still
they
are
separate
entities,
so
the
between
the
CEO
and
UPF.
You
have
the
user
traffic
encapsulated
into
the
in
the
gtpu
tunnel,
even
if
the
UPF
and
CEO
are
running
on
the
same
server.
F
F
Now
the
wireless
Technologies
is
only
responsible
for
the
wireless
access
just
like
that
triple
E
technology
for
ethernet
connection,
for
a
router
and
after
that
everything
else
is
ietf
IEEE,
while
and
Technologies
with
the
routing
and
switching
and
all
the
features.
Vpn
EVP
and
whatever
they're
already
in
the
Wildland
world
can
be
applied
to
the
wireless
as
well
as
as
well.
No
changes
next
slide.
F
The
advantage
of
this
is
that
we
no
longer
required
as
a
tunnel,
so
it
can
simplified
signaling,
optimized
data
plane
and
because
we
now
have
a
unified
architecture.
Many
special
5G
features
procedures.
Dino
are
no
longer
needed.
You
basically
have
a
router
and
switch
with
wireless
and
wired
connections.
F
G
So
today,
when
you
want
to
assess
the
state
of
the
network
or
when
something
goes
wrong,
and
you
want
to
figure
out
what
is
going
wrong,
then
the
ITF
has
defined
quite
an
extensive
set
of
OEM
mechanisms
that
help
you
with
this.
So,
for
example,
we
have
young
netconf
and
rest
conf,
and
that
lets
you
well,
of
course,
configure
your
boxes,
but
it
also
lets
you
monitor
everything
related
to
your
boxes,
but
it's
boxes
that
are
under
your
control.
G
Obviously,
and
in
addition
and
more
recently,
we
have
things
like
in
c2oim
or
ioim,
and
there
you
add
data
or
information
to
your
data
packets
and
that
lets
you
measure
everything
that
is
related
to
your
segment
of
a
path
so
that
segment
of
a
path
that
is
under
your
control
and
with
a
bunch
of
other
things
like
ipfix
to
export
flow
level,
information
from
a
router.
We
have
a
bunch
of
mechanisms
that
have
been
defined
by
the
ietf,
but
they
all
have
in
common
that
you
have
to
be
on
in
control
of
those
boxes.
G
You
have
to
be
operating
those
boxes
and
the
question
is
what
about
the
public
internet,
so
the
places
on
the
internet
that
you
are
not
in
control
of
and
there
you
basically
have
two
tools
available.
One
is
Ping
and
ping
gives
you
very
little
information,
so
you
have
interface
reachability.
You
know
that
interface
is
reachable
and
it
gives
you
a
round
trip
time
estimation
with
it,
but
that's
all
the
information
ping
gives
you
and
then,
on
the
other
hand,
you
have
trace
route
and
trace
route
is
more
expressive.
G
It
gives
you
router
level
information,
so
it
basically
lists
or
enumerates
all
the
routers
from
you
towards
the
destination
on
the
public
internet,
and
it
gives
you
round
trip
time
estimations
for
every
hop
and
the
final
destination,
and
what
we
would
like
to
do
is
we
would
like
to
make
trace
route
better
in
the
sense
that
we
also
want
to
estimate
the
reverse
path,
because
today's
internet
is
highly
asymmetric.
That
means
the
forward
path
and
the
the
return
path
are
typically
not
the
same,
and
we
would
like
to
basically
illuminate
this.
G
This
reverse
path
using
a
better
trace
route.
Next
right,
so
we
have
published
an
internet
draft
in
area
and
in
The,
Orange
Box.
You
see
the
link
towards
that
draft
and
we
would
like
you
to
to
actually
read
the
document
and
then
join
the
discussion
in
in
the
area.
We
also
have
implemented
we
like
running
code.
Obviously
so
we
have
implemented
reverse
trace
route,
and
we
would
like
you
if
you
could
host
a
reverse
trace
route
endpoint.
G
It's
a
ebpf,
a
small
ebpf
program
that
you
can
run
on
any
Linux
box
and
it
would
offer
reverse
trace
route
to
clients.
So
if
you
don't
want
to
do
that,
you
could
also
help
by
running
the
client
and
send
us
the
output,
because
we
would
like
to
assess
how
good
this
implementation
is.
What
the
properties
of
the
implementation
are,
what
we
see
on
the
public
internet
so
running
the
tool
would
be
very
helpful
to
us
and
remember:
the
internet
is
for
the
end
user.
That's
at
least
what
RFC
8890
says
and
shows
this
works.
G
So
this
is
for
people
and
organizations
that
don't
necessarily
run
the
infrastructure,
but
they
have
something
that
is
running
in
the
cloud
and
they
would
like
to
measure
path
quality
from
their
point
of
the
network
to
another
Point
over
the
public
internet
or
for
organizations
that
consume
Services
of
the
public
internet.
So
for
everybody
that
is
not
running
the
internet
or
running
parts
of
the
internet,
so
there's
a
website.
You
can
look
at
there's.
Clearly
the
draft.
G
H
H
Arno
tadai
from
broadcom
should
be
around
later
on
this
evening.
His
flight
hasn't
landed
yet
so
anyone's
interested
either
speak
to
me
or
speak
to
her,
though,
through
this
week
slide,
please
a
very
brief
bit
of
context.
Ech
is
a
mechanism
in
the
TLs
protocol.
That's
been
added
to
encrypt
the
client
Hello
message,
which
has
previously
been
in
plain
text.
H
It
builds
on
the
previous
encrypted
Sni
proposal.
It
is
like
a
superset
of
that
within
the
TLs
working
group
and,
if
you're
interested,
to
see
more
detail
about
ech
I've,
put
a
link
to
the
the
relevant
draft
which,
when
I
last
checked,
was
at
draft
15,
it
is
being
continuously
updated
next
libraries.
H
Rfc
8404
looks
at
security
network
operations
and
their
practices
that
could
be
impacted
by
the
move
to
end-to-end
encryption,
and
it's
I
think
perhaps
not
widely
understood
that
the
Sni
data
is
widely
used
by
on
path
security
actors.
So
it
does
have
quite
significant
implications
for
a
number
of
different
sort
of
groups
of
users,
particularly
so
Enterprise
and
consumer
next
slide.
H
Please
rc8744,
which
looks
at
the
need
for
encrypting
Sni
and
now,
if
you
didn't
really
consider
insufficient
depth
of
the
implications,
I
won't
go
through
the
detail
on
the
slide
in
the
interest
of
time.
What
we're
aiming
to
do
as
a
group
is
to
fix
that
and
actually
write
a
draft
which
covers
insufficient
detail,
what
the
implications
are
for
end
users
and
what
actions
they
may
need
to
take
next
slide.
Please.
H
So
with
that
in
mind,
if
that's
of
interest
to
you
for
in
any
reason,
we'll
be
uploading
a
draft,
hopefully
as
soon
as
tomorrow,
when
data
tracker
reopens,
which
will
have
the
latest
sort
of
thinking
it's
by
no
means
complete,
yet
we're
certainly
looking
for
people
to
add
to
the
text.
So
if
this
subjects
of
interest
to
you,
please
look
at
the
draft
and,
more
importantly,
we
have
a
side
meeting
tomorrow
evening
at
7
P.M
local
time
in
Richmond
six.
H
C
Abcon
is
a
construction
that
allows
me
to
understand.
What's
exactly
inside
a
conversation,
so
I
can
use
it
appropriately.
I
can
share
it
appropriately.
I
know
what
I
shared
and
when
a
customer
asks
me.
Could
you
please
delete
my
data?
I
can
because
I
know
what
data
I
have
next,
please
so
the
vcon
has
four
parts
to
it.
The
first
part
is
obvious:
it's
the
conversation,
it's
the
video,
it's
the
audio,
it's
the
chat
transcript.
Maybe
it's
a
lot
of
those
as
a
person
has
gone
through
a
channel.
That's
the
obvious
part.
C
C
C
C
So
this
really
solves
a
lot
of
practical
problems,
but
the
most,
but
the
most
important
one
is
the
responsibility
problem
that
I'm
being
asked
to
have
responsibility
for
data
and
I.
Don't
know
what
it
is
and
more
than
that,
if
we
standardize
the
format
of
what
a
conversation
looks
like,
then
we
can
ask
questions
like
why?
Didn't
you
authenticate
that
you
can
ask
questions?
We
can
interrogate
it
because
there's
facts
to
be
interrogated
and
then
I
think
this
is
the
iitf's
job
this
act,
this
vcon
idea
came
out
of
a
different
group.
C
C
We
just
put
in
the
draft,
but
maybe
a
great
place
to
start
is
the
white
paper
that
was
written
by
a
half
a
dozen
people
from
the
communications
industry.
To
tell
you
how
important
this
problem
is
to
solve.
This
is
an
open
source
project.
This
is
an
open
source
idea.
We
are
not
looking
to
we're
looking
to
solve
this
for
every
person
and
I
think
you
as
people
should
be
interested
in
this,
and
so
we
we're
here
right
now.
C
We
have
a
dispatch
meeting
tomorrow
at
9
30.,
if
you're
interested
in
in
privacy,
if
you're
interested
in
machine
learning,
please
be
there
and
please
support
us
and
then
listen
if,
if
you're
on
a
Thursday
night,
I'm
gonna
need
a
drink,
another
need
someone
to
have
a
drink
with
me
and
we're
having
a
birds
of
a
feather
session
at
the
very
same
time.
So
if
I,
were
you
I'd
come
board?
Thank
you
very
much.
I
I
I
I
Then
we
have
a
quick
nfpc
presentation,
then
they're
reducing
acknowledgments
in
iitf,
quick
presentation,
and
then
we
just
added
a
bbr
for
quick
over
Geo
presentations.
So
the
focus
as
you
can
see
on
this
particular
intercept,
meaning
is
Geo,
so
the
meetings
Wednesday
at
11
45
in
Richmond
six
we'd
like
to
see
you
there,
but
we
also
have
remote
participation
set
up
and
again.
If
you
need
more
information,
you
can
email
me
or
email
the
other
set
list.
That's
it.
J
Okay,
thank
you
and
I'm
going
to
be
talking
about
some
some
stuff.
That's
giant
work
with
Leno
artzook.
So
what
I
like
to
do
in
this
short
talk
is
make
a
case
that
formal
specifications
can
be
can
provide
benefits
in
the
ietf
process.
Next
slide,
please
so
bioformal
specification.
What
I
mean
is
just
some
unambiguous
mathematical
description
of
a
system
usually
described
at
some
interface
and
that
can
be
either
represented
in
logic
or
it
might
be
represented
in
some
more
familiar
form
like
an
abstract
programming
language.
J
So
there's
an
obvious
benefit
to
writing
specifications
in
that
way,
which
is
we
have
then
unambiguous
documentation
that
can
be
used
by
both
implementers.
You
know
and
users
who
are
building
on
top
of
a
given
interface,
so
that
specification
acts
as
an
interface
contract,
but
a
less
obvious
benefit
is
that
we
can
do
much
more
rigorous
testing
when
we
have
formal
specifications.
J
You
know
or
the
implementer
did,
or
there
was
an
ambiguity
in
the
spec
and
a
lot
where
even
low-level
code
crashes
that
just
weren't
exposed
by
by
testing.
So
a
lot
of
those
errors
in
turn
were
potentially
exploitable.
For
example,
we
found
a
case
where
you
could
exploit
the
flow
control
mechanism
in
quick
in
order
to
read
arbitrary
memory
out
of
the
server
or
a
case
where
you
could
have
a
denial
of
service
that
exploited
the
client
migration
feature
of
quick
next
slide.
J
Please
so
one
of
the
takeaways
from
this,
then,
is
that
interoperability
testing
isn't
really
enough
because
it
doesn't
tell
us
whether
the
implementations
are
really
compliant
to
the
RFC,
and
that
can
give
us
a
lot
of
issues,
especially
security
issues
when
we
get
non-compliant
implementations
out
in
the
wild.
This
happened,
for
example,
with
downgrade
attacks
in
SSO.
Formal
specification
could
be
part
of
that
solution
because
it
allows
us
to
find
out
before
things
get
in
the
wild,
whether
they're
really
compliant.
So
there's
a
lot
of
research
left
to
do
here.
J
There
are
hard
trade-offs
between
readability
of
the
specs
testing
issues,
formal
proof
and
so
on.
But
what
we're
mainly
interested
here
is
try
to
understand
how
formal
specifications
can
be
usefully
and
practically
integrated
into
the
ietf
process,
and
if
you're
interested
in
this
topic,
there's
a
meeting
coming
on
up
on
Thursday
of
the
usable,
formal
methods,
research
group
or
please
contact
us
directly,
and
we
love
to
to
hear
from
you.
Thank
you.
B
So
the
next
person
that's
on
our
list
is,
is
Rich.
Kulowak
and
I
am
not
seeing
him
in
Meet
Echo.
He
was
expected
to
be
remote.
He's
lost
power
at
his
house
twice
in
two
days.
He
let
us
know
that
he
was
trying
to
join
using
the
neighbors
bandwidth,
but
he
said
web
pages
were
painful,
so
he
didn't
think
he
could
get
in
on
on
meat
Echo
and,
if
he's
not,
if
he's
not
here,
it's
not
for
lack
of
trying.
B
K
K
So
it
is
just
a
mapping
of
session
initialization
Pro
sorry
session
initiation
protocol
over
quick
transport
very
much
inspired
by
HTTP
3's
mapping,
given
that
sip
is
quite
close
to
http
1.1,
the
original
idea
came
from
some
work.
I
did
on
trying
to
run
RTP
over
quick,
but
one
of
the
problems
I
was
having
was
okay.
Well,
I
can
send
media,
but
how
do
I
negotiate
that
in
a
nice
way?
K
K
The
idea
of
sending
live
media
over
quick
is
a
very
active
topic.
So
there's
obviously
the
New
Media
of
a
quick
working
group.
There's
stuff
in
avt
core
as
well
talking
about
this.
So
yes,
we've
been
looking
at
the
possibility
of
reusing
system
magnetics
to
do
control
metadata
for
that
next
slide.
Please
so,
like
I
say
it's
inspired
by
HTTP
3,
so
I've
got
data
frames
in
there
for
carrying
the
Sip
requests.
K
So
the
internet
is
now
actually
up
on
data
tracker
I
managed
to
do
that
on
Avanti,
train
Wi-Fi,
amazingly
on
the
way
down
this
morning.
So
please
do
go
and
have
a
look
at
that.
If
you're
interested
happy
accept
any
and
all
feedback,
but
I'm,
also
specifically
looking
for
what
Avenue
is
the
best
place
to
continue
this
work?
Is
this
something
for
sip
core?
Is
there
something
for
avt
core,
or
is
this
something
that
should
be
living
in
mock?
L
From
the
University
Queen
Mary
of
London
and
I
have
a
question
for
you,
which
is:
how
is
the
idea
of
doing
and
that's
what
I've
been
trying
to
analyze
with
some
colleagues
slide?
Please,
and
we
have
been
crunching
and
looking
into
the
emails,
the
drafts,
the
rfcs,
how
long
it
takes
and
many
other
details,
and
what
we
find
is
that
the
conversation
seems
to
be
increasingly
complex.
It
seems
to
be
increasingly
harder
to
publish,
and
it
seems
like
there
is
an
influential
minority
that
is
growing
increasingly
relevant
inside
of
the
ITF
next
slide.
L
Please,
and
if
this
sounds
interesting,
we
have
been
working
together
with
colleagues
from
the
University
of
Glasgow
and
we
have
already
published
some
papers
which
have
much
more
details,
and
this
is
part
of
a
broader
project
called
so
the
stream
next
slide.
Please,
and
as
a
part
of
this,
we're
also
trying
to
create
tools
that
might
help
the
community
in
particular.
Right
now,
we
are
developing
a
tool
for
a
supporting
crossover
review.
L
If
you
scan
that
QR
code,
that
will
bring
you
to
the
website
and
the
tool
is
there
and
we
are
trying
to
find
good
matches
between
drops
and
reviewers,
and
we
do
this
by
using
a
combination
of
our
NLP
tools
and
social
network
analysis.
If
this
sounds
interesting,
please
help
us.
We
need
a
little
bit
of
information
to
Chrome
truth.
The
findings
that
we
have.
L
We
are
also
preparing
a
few
other
things,
to
gather
more
information
like
a
survey
on
like
the
survey
that
I'm
saying,
and
if
this
in
general
sounds
interesting
and
sounds
like
something
that
you
think
that
more
people
should
be
doing.
We
have
a
side
meeting
with
the
idea
of
preparing
a
research
group
called
rasp
research
on
internet
standards,
processes,
and
that
will
happen
on
Thursday
and
everybody
is
welcome
to
join.
Thank
you
very
much.
B
B
M
M
Next
slide,
please,
and
during
this
research
project
we
were
basically
studying
synchronization
over
over
the
Internet,
how
you
can
synchronize
components
and
we
made
a
kind
of
a
discovery,
or
at
least
we
founded.
We
found
an
ID
that
we
we
thought
was
very
interesting
to
to
share.
So
that's
what
I
want
to
do
right
here.
You
know
probably
Shannon's
information,
Theory
right.
This
basic
idea
of
what
information
theory
is
you
could
code
and
decode
and
then
you
can
use
basically
bits
to
encode
any
kind
of
message
that
you
want.
M
But
the
problem
with
this
notion
is
that
this
is
a
Time,
insensitive
notion.
Whenever
you
encode
it,
this
is
done
statically.
You
don't
regard
the
moment
when
you
encode
it
or
the
moment
that
you
decoded,
and
so
it
seems
that
this
capacity
of
a
channel
measured
in
bits
per
second
is
sufficient.
Next
slide,
please,
but
it
turns
out
that
you
can
introduce
a
so-called
site,
Channel
and
also
Shannon
was
aware
of
this
ID,
but
this
is
less
wide
widely
known.
M
What
the
idea
of
a
side
channel
in
in
this
case
time
is,
is
that
if
you
have
two
processes
that
are
synchronized
in
time,
so
that
they
have
a
clock
running
at
the
same
speed,
then
you
can
send
a
signal.
Just
a
single
signal
and
the
moment
of
reception
is
then
significant
and
whenever
you
synchronize
these
machines
that
you
can
send
just
with
a
single
signal,
more
information
than
is
present
within
the
signal.
M
And
so
then
we
have
basically
ethereum,
which
is
that
the
effective
capacity
is
higher
than
the
capacity
and
now,
an
important
new
measure
that
you
have
to
also
consider
is
that
of
Jitter,
which
is
unpredictable
variation
in
the
delay.
Whenever
you
communicate
next
slide,
please
so
for
based
on
this
Insight,
we
basically
want
to
develop
a
new
Internet
Protocol
called
TMP
standing
for
time
modulation
protocol.
M
We
are
really
in
the
research
stage
right
now,
and
it
would
be
really
nice
to
get
into
contact
with
more
people
Hazard,
for
instance,
to
collaborate
on
prototypes,
but
also
for
working
on
better
models
for
predicting
delays.
Let
me
end
with
what
are
the
potential
benefits
of
using
this
protocol.
There
is
a
potential
increase
of
effective
capacity,
which
might
be
interesting
whenever
you
want
to
send
more
data
than
whatever
is
metered
on
links
and
very
important
for
end
users.
Application
is
that
you
could
increase
confidentiality
by
hiding
data
in
time.
Thank
you
very
much.
B
N
Thank
you
so
hello,
everyone.
This
is
my
first
time
attending
I,
ietf
and
I
come
with
a
question,
a
a
challenge,
which
is,
is
privacy
preserving
web
filtering
possible?
If
I
can
have
the
next
slide,
please
foreign
work
at
the
iwf,
we're
a
charity
in
the
UK
and
we
work
to
find
a
remove
child
sexual
abuse
material
from
the
internet.
N
A
really
crucial
part
of
that
work
has
been
providing
data
to
Industry,
to
enable
detection
blocking
filtering
of
known
content
by
platforms,
isps
and
filters
as
Internet
standards
have
developed
and
encryption
has
become
more
commonplace.
Those
methods
have
become
less
effective.
It's
been
harder
to
detect,
it's
been
hard
to
to
block,
so
the
challenge
really
is
it
can
legitimate
legal
web
filtering
coexist
with
secure
and
private
internet
can
advance
as
an
encryption
and
privacy
enhancing
Technologies
be
used
to
filter,
harmful
web
content
without
compromising
user
privacy
for
the
next
slide,
please.
O
All
right,
I'm,
Travis
I'm
here
on
behalf
of
the
spec
core
team
for
Matrix,
not
a
lot
of
time,
but
a
lot
of
information,
so
I
am
going
to
speedrun
this.
Please
try
and
find
me
afterwards
or
just
message
us
on
the
Mimi
mailing
list.
If
I
can
get
the
next
slide
please,
so
there
are
three
major
questions
that
I
would
like
to
sort
of
cover.
First,
what
is
Mimi?
Why
are
we
doing
this?
O
O
They
are
being
or
they're
having
a
buff
on
Wednesday
to
actually
form
themselves
into
a
proper
working
group,
and
it's
created
a
lot
of
an
interest
for
the
eu's
digital
markets,
act
or
dma,
so
in
that
dma,
Gatekeepers
or
large
Messengers
are
required
to
interop
with
each
other,
as
well
as
other
sort
of
Messengers
in
the
space
as
Matrix.
We
think
this
is
a
good
thing,
because
Matrix
is
an
interoperable
open
standard
for
security,
centralized
communication
and
you
might
see
where
this
is
going
if
I
can
get
the
next
slide.
O
Please
So,
currently
Gatekeepers
kind
of
look
like
this
today,
where
you
have,
you
know,
say:
WhatsApp
and
Instagram
they're
able
to
communicate
with
each
other
and
then
Twitter's
kind
of
off
to
its
side,
and
there
are
others,
of
course,
so
with
the
next
slide,
the
dma
kind
of
wants
something
like
this,
where
you
just
apply
magic
in
the
middle
and
then
they're
able
to
talk
to
each
other
next
slide.
Please.
O
The
trick,
though,
is
that
with
encryption
maintained
the
entire
way
through
so
because
WhatsApp
supports
encryption,
all
three
would
need
to
support
encryption
and
anybody
else
sort
of
in
that
conversation.
So
next
slide
please.
So
how
would
we
do
that
next
slide
with
Matrix
next
slide,
so
with
Matrix
use
for
interoperability?
You
convert
everything
to
a
home
server,
at
least
on
this
sort
of
public
internet
front,
so
they're
able
to
communicate
with
each
other
and
briefly
next
slide.
O
O
O
This
is
the
rough
timeline,
so
Matrix
was
created
back
in
2014.,
we're
currently
November
22,
where
maybe
becomes
a
working
group,
and
we
have
a
lot
of
conversations
ahead
of
us
and
we're
hoping
that
you
know
Matrix
will
be
sort
of
adopted
eventually
and
that's
kind
of
our
goal
here.
Next
slide,
please!
O
So
how
can
you
help
next
slide?
Just
let
us
know
what
do
you
think?
How
can
we
actually
make
this
kind
of
work
in
a
governance
process
that
sort
of
stuff
if
you're
on
Matrix?
That's
the
room
to
sort
of
talk
to,
if
not
otherwise,
just
come
talk
to
me
after
or
yeah
on
the
mailing
list,
but
that's
all
just
next
slide.
Please.
B
B
First,
let
people
know
what
you've
thought
about
this
format
and
whether
whether
it
seemed
helpful
to
you
or
not,
we
got
one
request
to
present
about
40
minutes
before
the
social
started
and
we
were
able
to.
We
were
able
to
do
that
thanks
to
a
lot
of
assistance
from
the
Secretariat.
So
please
I
tell
people
what
you
appreciate
about
them.
