►
From YouTube: IETF-MLS-20230209-1500
Description
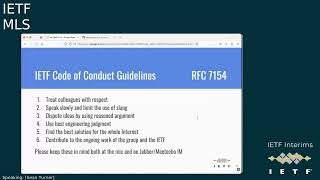
MLS meeting session at IETF
2023/02/09 1500
https://datatracker.ietf.org/meeting//proceedings/
A
A
Basically,
if
you
know
something
say
something:
if
you
have
any
questions
about
that,
I
can
fill
you
in
there's
a
place
to
do
third
party
IPR
disclosures,
Etc,
there's
also
an
Annie
harassment
procedures
and
code
of
conduct
and
all
that
stuff.
And
luckily
this
working
group
has
it
none
of
those
problems,
but
I
do
feel
compelled
to
talk
about
them
all.
A
C
C
C
A
A
C
So
this
came
up
in
well
in
the
process
of
interrupt
testing,
but
not
because
we
had
interop
bugs
just
because
we
were
looking
at
the
right
part
of
the
spec
looking
at
the.
If
you
could
flip
over
to
the
diff
view,
I
think
that's
probably
better.
So
the
the
Salient
part
here
is
is
the
top
part.
The
old
transcript
hash
description
didn't
actually
tell
you
how
to
initialize
things.
C
It
I
I'm
surprised
like
the
initialization
condition
there
at
the
top
says,
Epoch
and
not
zero,
so
it
didn't
actually
tell
you
how
to
initialize
things
in
particularly
didn't
tell
you
how
to
initialize
the
interim
transcript
hash.
So
this,
the
updated
version
says
that
you
initialize
both
the
trans
interim
and
confirmed
to
zero
length
strings,
and
then
you
you
roll
forward
in
the
in
the
way
discussed.
C
So
this
doesn't
change
the
behavior
I
think
it
just
describes
it
more
clearly.
I
think
there
was
no
disagreement
about
what
the
correct
Behavior
was.
It's
just
a
clarification
in
the
description.
It
also
adds
a
figure
that
tries
to
you
know,
show
a
timeline
view
of
what
goes
into
which
transcript
hashes.
That
this
kind
of
pointed
out
is
a
little
hard
to
capture
with
exactness,
but
you
know
may
be
helpful
in
helping
people
understand.
C
What's
going
on
here,
yeah
the
better
view
of
the
figures
on
the
on
the
overview
where
I
put
the
screenshot
in.
So.
If
you
have
any
comments
on
this,
this
is
mainly
a
clarification,
not
a
behavior
change.
So
it's
not
a
huge
deal,
but
the
folks
have
new
thoughts
or
comments
on
this.
Once
once
Conrad
and
I
get
happy
about
the
figure
we
can
I
think
we
can
probably
do
screw
and
immersions.
Unless
there's
any
comments
here.
D
E
C
B
C
I'm,
not
sure
I,
don't
think
it's
a
necessarily
a
deal
breaker
to
screw
up
the
texture
engine,
because
the
official,
the
official
thing
nowadays
is
XML
and
HTML.
So
I
don't
know
if
we'll
be
forbidden
from
publishing.
If
we
have
too,
why
not
too
wide
diet,
but
we
can
always
trim
it
back
to
one
or
two
epochs.
If
we
need
to
be
narrower.
A
F
C
F
F
G
C
A
A
Yeah,
so
I
was
just
clarifying
that
we
did
a.
We
talked
about
a55
and
it
looks
good
to
go
long
as
Richard
and
Raphael
agree
to
the
figure
at
8.
44.
Conrad
said
don't
forget
about
this.
One
and
Richard
said
he
just
forgot
to
hit
the
button,
so
the
rest
of
them
are
all
I.
Think
between
844
and
855
are
all
basically
just
dealing
with
various
things
from
the
isg
review.
G
G
So
this
was
basically,
there
was
one
comment
about
there,
not
being
enough
explanation
of
what
is
in
of
what
these
various
terms
are
that
are
used
in
architecture
that
are
defined
in
protocol.
So
if
you
go
to
files
changed,
you
can
see.
I
initially
did
this
as
a
glossary.
Ecker
said
he
didn't
like
that:
I
rewrote
it
in
a
narrative,
style
and
I
liked
it
better
as
well
and
I
think
there
was
one
comment
by
by
Brita
about
how
we
want
to
how
we
want
to
describe
a
leaf
package.
G
G
H
The
only
reason
for
this
suggestion
is
that
come
implying
some
sort
of
time
scale
to
this,
so
that's
not
just
a
static
I
could
see
where
someone
could
read
the
spec
and
see
including
its
Leaf,
known
as
if
it
was
ecstatic
across
multiple
initiations
or
the
various
ways.
This
could
be
misinterpreted,
so
I
just
propose
that
we
have
some
sort
of
initiation
there.
Other
start
point.
G
A
G
B
G
A
The
the
background
here
is
they
were,
we
were
getting
a
lot
of
bounces
and
I
always
get
a
lot
of
hate
mail
from
the
isg,
so
I,
basically
just
rummaged
through
my
emails
to
find
ones
that
were
were
fixable
and
fix
them.
That's
probably
past
the
point
of
pain,
but
I
think
we
should
go
ahead
and
fix
them
where
we
can.
G
G
E
A
G
G
D
A
A
D
Okay,
that's
a
good
point:
I'm
gonna
check
on
that
and
then
I
can
comment
on
the
pr
and
to
your
point,
Ron
the
we
have
this
number
of
50k
so
far,
I
think
it's
even
in
the
charter,
if
I
remember
correctly
and
it's
completely
arbitrary
I
think
John
Millican
made
it
up
at
the
time.
So
in
that
sense
there
is
no
no
good
reason
to
stick
to
that
particular
number.
D
G
G
You
know
it,
everybody
I
think
everybody
is
comfortable
with
saying
that
we
want
to
do
at
least
that,
and
if
people
want
to
say
you
know,
this
is
what
we.
This
is
what
we
envision.
This
is
what
we
thought
of,
but
if
we're
going
to
go
bigger
than
that,
there's
probably
additional
they're,
almost
certainly
additional
things
that
we
would
need
to
do
that
are
not
in
the
protocol
yet,
but
we
could
add
them
yeah.
So
I
think
this
is
a
safe.
This
is
a
safe
place.
G
G
G
G
F
B
G
Think
you're
reading
more
into
it.
It
was
that
people
who
said
that
they
wanted
to
have
you
know
that
they
were
trying
to
understand.
Are
you
sending
the
message
to
a
group?
Are
you
sending
users?
You
are
sending
it
to
you
to
individual
members,
they
didn't
really
understand
and
it's
as
like.
The
purpose
of
the
DS
is
to
deliver
messages
which
are
addressed
for
a
specific
group
and
send
them
to
the
individual
members.
That's
the
function
that
DDS
is
offering
and
that's
why
I
changed
the
article
because
they
were
confused.
G
All
right,
there's
another
little
minor
privacy
wording
change
in
1056
here,
MLS
is
designed
under
the
assumption.
The
transport
layer
is
present
to
keep
metadata
private
from
Network
Observers,
while
the
MLS
protocol
provides
confidentiality,
integrity
and
authentication
guarantees
for
the
application
data
which
could
pass
through
multiple
systems.
G
G
This
is
where
we're
talking
about
using
Anonymous
credentials
and
Roman
had
an
allergic
reaction
to
Anonymous
credentials,
because
it's
it's
not
defined,
except
in
a
U.S
government
document.
According
to
him,
so
I
put
use
credentials
uncorrelated
with
specific
users
to
help
prevent
dos
attacks
in
a
privacy,
preserving
manner.
Actually
I
think
somebody
asked
to
change
this
to
you
just
to
prevent
us
yeah
to
prevent
dust
attacks
in
a
privacy
preserving
manner.
I
G
So
if
you
use
anonymous
credentials,
then
you
get
the
property
that
it's
you
have
to
have
an
authentication
credential,
but
you
are
still
remaining
Anonymous.
So
in
this
case
this
is
credentials
which
are
uncorrelated
with
specific
users.
Is
the
property
that,
in
the
context
of
this,
the
section
that
comes
slightly
before
this.
G
G
It's
a
little
weird
like
this
is
one
of
the
places
where
the
document
is
a
little
bit
weird,
because
we
have
where
you
know,
we
sort
of
talk
about
things
that
a
lot
of
folks
do
and
and
then
we
we
talk
about
about
adding
a
bunch
of
extra
privacy
protections
that
many
systems
do
not,
and
here
we're
talking
about.
You
know,
sort
of
trying
to
merge
those
two.
Those
two
needs
together
in
a
single
recommendation.
G
I
H
B
G
B
G
So
we
have
we're
basically
saying
two
contradictory
things
in
the
same
paragraph.
So
roughly
speaking,
deniability
is
the
opposite
of
non-repeviation,
that
a
property
that
isn't
possible
approved
to
a
third
party,
then
Master
goes
set
by
a
given
sender,
so
I
reworded.
This
too
deniability
is
not
currently
provided
by
the
mrf
protocol,
but
the
protocol
avoids
constraints
that
would
make
it
impossible
to
add
deniability
properties
for
the
extensions
defining
the
specific
requirements
and
resulting
Notions
of
deniability
requires
further
analysis.
D
I
think,
plus
the
first
sentence
is
a
little
bit
problematic,
simply
because
I've
been
going
through
a
world
of
pain
regarding
the
ability.
So
it's
not
it's
not
clearly
defined.
What
deniability
actually
is,
and
so,
if
we
start
with
saying
deniability
is
not
currently
provided.
It
implies
that
there
is
a
crisp
definition
of
what
it
is,
whereas
before
it
was
a
lot
more
vague
and
that
worked
better.
C
C
D
G
C
D
I
assume
that
some
thought
has
gone
into
this
and
the
decision
was
made
not
to
provide
this
as
a
core
feature
actually
due
to
the
latest
usefulness
and
example:
even
the
court
system
or
log
messages,
deniable
or
not
are
recovered.
I
assume
it
was
not
easy
to
add
this
property
and
it
was
there
for
mostly
left
out
because,
of
course,
it
would
be
nicer
to
have
it
done
to
have
it,
but
I
also
vaguely
remember
Richard
replying
to
that
on
list.
D
A
G
G
Recommendation
if
the
threat
model
of
the
system
is
against
an
adversary
that
can
access
the
messages
on
the
device
without
even
needing
to
attack
MLS,
the
application
should
delete
plain
text
messages
and
ciphertexts
immediately
after
encryption
or
decryption.
I
changed
this
to
as
soon
as
practical
after
encryption
or
decryption.
The
comment
was
they
basically
that
this
is
like?
You
know
you
decrypted
the
message
and
deleted
before
we
display
it
to
the
user.
You
know.
G
So
I
changed
this
to
not
note
that,
with
a
legal
request
to
ask
the
service
provider
for
the
push
token
associated
with
an
identifier,
it
is
easy
to
correlate
the
token,
with
a
second
request,
to
the
company
operating
the
push
notification
system
to
get
information
about
the
device
which
is
often
linked
with
the
real
identity.
Etc.
G
All
right,
moving
down
to
1619
Brendan,
suggested
changing,
centralized
server
to
Central
server
I
accepted
most
of
his
comments,
but
this
one
I
left,
as
is
because
there
are,
there,
were
at
least
half
a
dozen
or
more
references
uses
of
centralized
and
I
didn't
want
to
have
to
unnecessarily
go
back
and
change
all
of
them
and
make
sure
they
still
made
sense
any
any
heartbreak.
If
I
leave
it
as
centralized
Brendan.
E
G
G
G
D
C
E
And
also
like
to
comment
about
why
this
was
changed.
I
saw
it
earlier.
It
was
on
the
screen
from
Nat.
Was
it
says
that
this
can
be
performed
autonomously
in
the
ad
was
confused
about
the
meaning
of
autonomous
and
I?
Think
in
the
context
of
the
document,
autonomous
was
meant
to
mean
requiring
no
interaction
from
the
user,
because
the
sense
afterwards
is,
in
contrast,
you
can
require
the
user
to
have
to
do
something
to
verify
the
credential
or
you
can
use
like
x19,
which
doesn't
require
the
user,
interaction
and
I.
G
G
G
B
G
Okay
line
1700
key
transparency
was
mentioned
twice
in
two
different
recommendations
and
in
this
one
I
just
changed
it
to
provide
one
or
more
out
of
band
authentication
mechanisms
to
limit
the
impact
of
an
authentication,
Service
compromise
and
I
didn't
specify
key
transparency.
Are
you?
Okay,
with
that
Brendan.
G
All
right
and
then
last
one
1736
recommendation.
Instead
of
always
using
Cryptid
group
operation,
messages
to
limit
privacy,
risks,
I
said
use
encrypted
group
operation,
messages
to
limit
privacy
risks
whenever
possible,
and
that's
specifically
because
we
have
a
lot
of
people
who
are
who
are
using
encrypted.
You
know
unencrypted
group
operation
messages
for
for
legitimate
purposes
and
we
have
a
different
recommendation
that
says,
if
you
do,
that,
do
it
inside
of
an
encrypted
transport.
B
I
G
G
So
I
particularly
was
thinking
of
brita's
application.
Here
you
know
if
there's
I
don't
know,
if
anybody
has
any
heartburn
with
saying
you
know,
I
thought
that
just
saying
just
just
stick:
MLS
inside
of
TLS
or
or
quick
is
pretty
non-controversial
in
this
group,
but
I
didn't
know.
If
there
was
anybody
who
and
and
I
wasn't
also
really
sure
exactly
where
to
where
to
put
this.
H
Speaking,
we
have
some
applications
where
it
would
be
very
problematic
to
put
inside
of
TLS
or
quick
and
there's
various
other
solutions
for
trying
to
ensure
that
transport
I
think
part
of
this
issue.
Here,
we've
just
we've
described
what
we
mean
by
secure
transport.
I
went
back
to
other
doc
to
ensure
meaning
there,
because
we're
not
really
saying
it
providing
a
lot
of
security.
G
Yeah
so
I
guess
the
first
question
is:
do
you
care
if
the
architecture
document
says
you
know
in
general,
you
should
go
and
do
this
thing
you
don't
do
it
and
if
you
write
an
ITF
document
doing
something
different.
You
have
an
extra
paragraph
in
your
document
explaining
why
it's
safe
that
you
do
the
thing
differently
than
the
recommendation
and
architecture.
C
H
C
H
Yeah
I
think
if
we
were
saying
and
make
it
explicit
that
is
said
as
an
advisory
Note
versus
a
should
and
I
know
those
two
things
very
similar,
but
kids
are
actually
interpreted
more
broadly
as
a
this
is
fundamental
to
the
security
of
MLS,
and
that's
not
what
we're
really
saying
we're
saying
that
it's.
It
helps
improve
the
overall
security
and
it
also
gives
this
reliability
of
the
transport.
There's
two
different
properties
there
that
we're
getting
from
containing
it
inside
of
TLS
or
quick
or
something
one
is
the
meditating.
H
The
other
is
reliability,
and
if
we're
explicit
about
those
goals
and
say,
if
you
do
this
inside
of
TLS-
and
do
this
in
kind
of
quick,
then
you
get
the
properties
you're.
Looking
for
and
just
advise
that
that's
a
easy
solution,
then
I
think
it's
that's
probably
the
best
way
forward.
If
the
wording
sounds
like
this
should
be
done,
and
it's
recommended
as
the
main
way
forward,
then
I
think
we're
going
to
run
into
issues
because
then
it
kind
of
does
sound,
like
it's
locked
in
the
design
to
that
place.
G
A
A
I
D
C
H
Would
suggest
a
slightly
rewarding
here,
maybe
that
we
should
use
for
one
clarification?
Maybe
you
secure
transports
that
provide
reliable
delivery
and
protect
metadata
whenever
possible,
such
as
input
the
TLs
or
quick
at
the
end
you're,
using
the
Ed
option
like
that,
before
I'm,
putting
it
less
front
and
center
as
those
are
the
distance
and
more
as
a
the
solution
needs
to
provide
these
things.
G
B
C
G
G
B
B
G
G
B
A
Yeah
I
mean
like
at
the
end
of
the
day.
What's
gonna
happen,
is
we're
going
to
publish
and
they're
gonna
tell
us
whether
they
think
that
we've
done
it
or
not
right?
So
it's
it's.
If,
if
you,
you
know
if
this
was
your
first
rodeo
Rowan
I
might
be
a
little
worried,
but
it's
not
so
if
you
think
you're
you
think
we
addressed
them,
then
I'm
gonna
go
with
that
and
then
we'll
just
have
to
see
that
we've
addressed
them
to
the
satisfaction
of
the
people
that
all
the
discusses.
A
G
B
A
A
A
C
A
Yeah
so
I
guess
that
brings
this
to
a
close-up.
We
will
be
done
with
this.
If
not,
we
can
always
set
up
another
meeting
to
go
over
whatever's
left
if
something
comes
back
up,
I'm
hoping
I'm,
hoping
not,
but
apparently
these
apparently
these
two
drafts
brought
a
lot
of
interest,
so
I
think
that's
good,
actually
any
event.
D
A
Yeah
so
basically,
after
these
documents
get,
you
know
formally
approved
by
the
isg
they're
essentially
put
in
the
RFC
What's
called
the
RC
editor's
queue,
and
then
what
happens
is
mostly
just
copy,
editing,
they're,
going
to
make
sure
that
we
did
our
references
right.
You
know
that
the
commas
are
in
the
right
place
like
they're,
going
to
do
a
lot
of
copy
editing
and
then
the
kind
of
document
goes
through
if
any
other
large
changes
get
proposed.
A
That
comes
back
to
the
working
group
and
we
can
make
those
changes
we'll
have
to
discuss
those
changes
before
we
put
them
in
the
document,
and
if
there
are
any
big
enough
changes,
we
have
to
start
this
whole
process
over
I.
Don't
think
there
will
be,
but
once
it's
in
the
RFC
editor's
queue
it'll
probably
take
two
to
three
months
before
it
pops
out
with
an
actual
RFC
number
and
at
the
end
is
the
editors.
All
you
really
need
to
do
is
like
start
reading
your
email.
A
G
G
So
I
think
that
if
for
no
other
reason
than
to
demonstrate
that
we
are
still
that
we
are
not
a
moribund
group,
if
everybody
for
transparency
that
we
should
request
a
meeting
and
talk
about
MLS
extensions
just
so
that
we
have
the
you
know
the
minimal
process,
you
know
place
where
somebody
can
come
and
ask
questions
they
can
find
out.
Who
you
know
there
will
be
people
there,
there
will
be
Outsiders.
This
is.
G
This
is
a
useful
thing
for
Outsiders
to
be
able
to
come
and
find
out
about
MLS
and
at
the
end
of
this
month,
there's
going
to
be
a
workshop
on
the
digital
Market
markets,
Act,
where
people
are
going
to
be
talking
about
interoperability
in
MLS,
and
things
like
that
and
they're
going
to
be
a
lot.
There's
going
to
be
a
lot
of
sort
of
Outsider
interest,
we
need
a
place
where
people
can
find
us
in
that
way.
Who
are
not
the
people
that
normally
attend?
These
calls.
G
D
A
D
A
D
C
C
D
So
yeah,
maybe
to
give
some
perspective
on
that.
There's
been
some
low-key
I've
heard,
with
royal
and
Marta
regarding
Conrad
and
I
regarding
the
extensions
document
to
come
up
with
yeah,
some
at
very
some
guidelines
on
how
to
develop
new
extensions
so
that
they're
safe
and
then
they
don't
jeopardize
the
core
protocol
Etc.
So
that's
still
ongoing
and
it's
obviously
going
to
be
a
while
and
the
document
is,
is
going
to
be
open
for
a
while.
D
G
A
A
Oh
I
can
definitely
do
that.
I
can
swing.
They'll
they'll,
probably
love
that
actually,
so
all
right
so
I
mean
unless
I'm
hearing
any
violent
objections.
I
don't
really
have
a
problem
putting
in
in
our
request
and
they'll
Friday,
and
it
will
be
probably
Friday
afternoon,
but
it
it'll
it'll
work.
Yeah.
A
Okay,
I'll
go
in
I'll,
go
ahead
and
do
that
then-
and
you
know
just
be
I-
guess
Raphael.
The
thing
is
that
we
just
have
to
make.
We
have
some
presentations
or
Rowan
you're
gonna
have
to
do
it
yourself
to
carry
the
weight.
So
that's
fine,
that's
fine!
That's
what
I
figured
all
right!
All
right,
cool
I
will
go
ahead
and
put
that
in
and
I
think
that
might
be
it
for
today.
Unless
anybody
has
anything
else.
G
G
Finally,
the
the
inability
of
a
client
to
remove
itself
I
was
waiting
for
basically
us
to
get
isg
approval,
but
I
talked
with
Richard
about
some
ideas
of
how
to
improve
client
removal,
because
it's
it
really
is
a
pain
in
the
butt
it's.
It
is
like
not
it's
not
a
great
thing
that
the
protocol
is
it's
so
hard
to
remove
yourself.
B
C
G
If
somebody
disagrees
and
thinks
that
we
should
stick
this
in
the
architecture
that
we
should
talk
about
these
in
the
architecture,
document
I
could
go
and
do
three
separate
PRS
on
these
or
two.
You
know
if
you
have
specific
one
or
two
of
these
that
you
think
are
important.
I
could
do
a
PR
for
them.
G
A
A
She's,
not
she's,
not
new,
all
right
cool,
so
I
think
what
we're
gonna
do
is
we're
gonna.
The
way
I
would
probably
try
to
address
is
that
we,
you
know
collectively,
don't
think
they
need
to
be
specifically
addressed
here
in
the
architecture
document,
but
they're
that
it's
given
us
food
for
thought
for
other
documents.
A
Okay,
that
brings
us
to
a
close
thank
you
Richard
for
taking
notes.
Thank
you
for
authors
and
everyone
who
showed
up
at
early
and
late
times
to
get
this
done
again.
Thanks
for
your
continued
efforts,
and
hopefully
we'll
get
this
all
knocked
out
and
get
this
approved
announcement
sent
as
soon
as
possible.
Awesome
all.
