►
From YouTube: OAUTH WG Interim Meeting, 2020-11-02
Description
OAUTH WG Interim Meeting, 2020-11-02
A
A
So
that's
that
no
well
so
we
have
today
we'll
be
talking
about,
is
logged
in
and
web
id,
but
we
have
still
one
more
meeting
and
that
will
be
talking
about
the
pop
and
that
would
be
in
november
30th
and
now
today's
meeting
will
be
talking
about
the
motivation
and
challenges
of
those
initiatives
and
we
will
spend
most
of
the
time
discussing
those.
The
goal
is
not
really
to
dig
deeper
into
the
details
of
those
initiatives.
A
I'm
not
expecting
this
meeting
to
be
with
the
conclusion
for
all
those
discussions,
probably
the
beginning
of
this
discussion.
So
I'm
expecting
that
we'll
have
a
follow-up
meetings
and
we
can
schedule
more
meetings
when
needed,
and
so
that's
that's
all.
I
have
on
my
side
so
I'll
I'll
hand
it
to
vittorio
and
george
to
take
us
through
their
slides
before
I
do
that
any
comments,
questions.
B
Can
you
see
my
enormous
desktop?
Yes,
we
can
all
right
perfect.
Thank
you.
Go
join
everyone
victoria,
from
zero,
presenting
with
george
from
verizon,
as
rifat
mentioned.
Our
goal
here
is
really
to
elicit
the
discussion
rather
than
educate.
However,
we
will
still
give
an
ultra
quick
glimpse
about
the
meat
all
the
things
that
we
are
discussing
in
terms
of
agenda.
B
We
are
going
to
spend
a
moment
taking
the
first
two
points,
as
in
like
some
distilled
down
details
about
what
is
logged
in
and
web
id
initiatives
are
about
and
some
idea
about
how
they
are
impacting
and
how
they
will
impact
their
work
and
the
applicability
of
the
guidance
that
we
generate
in
the
context
of
working
group.
And
then
we
have
a
couple
of
ideas
on
how
the
as
a
working
group,
we
can
influence
the
process
and
those
are
just
ideas
for
seeding.
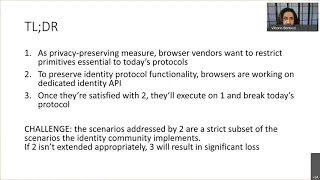
B
We
know
that
tracking
is
a
big
problem
today
and
the
browser
vendors
like
to
say
that
reality
is
a
classification
problem
which
is,
whenever
a
website
uses
low-level
primitives
like
radioactive
link,
decoration
third,
third-party
cookies
and
similar.
The
browser
doesn't
know
whether
those
primitives
are
used
for
tracking
the
user
or
if
they
are
used
for
doing
perfectly
legitimate
stuff,
such
as
singleton
singleton
across
multiple
applications.
B
C
Okay,
so
we'll
just
go
through
a
couple
of
these
th.
The
ones
on
this
page
here
are:
some
of
them
are
already
in
effect
right
same
site.
If,
if
you
haven't
been
affected
by
it
right,
you
have
probably
seen
effects
on
identity
flows
where
you
know
basically
same
site,
I
mean
prompt
equal,
none.
Requests
in
iframes
are
breaking
unless
you
explicitly
tag
your
identity
related
cookies
as
same
site,
equal
none,
which
of
course
doesn't
help
you
in
certain
browsers,
where
those
things
are
sort
of
ignored
or
when
third-party
cookies
are
disabled.
C
You
know
sort
of
across
the
board
right
because
effectively
a
same
site.
Equal
none
cookie
is
a
third-party
cookie.
So
so
we've
already
seen
this
we've
seen
other
cases
already
out
of
intelligent
tracking
protection
efforts
where
you,
the
user,
needs
to
be
engaged
with
the
idp
on
a
frequency
basis.
Otherwise
the
idp
cookies
go
away.
C
So
so,
basically
you'll
you'll
start
seeing
interstitials
in
the
single
sign-on.
So
single
sign-on
is
no
longer
silent
or
seamless
get
an
interstitial.
I
think
there's
been
a
number
of
places
in
australia
that
sort
of
had
to
do
this,
because
you
know
a
vast
array
of
domains
all
using
the
same
single
sign-on
provider
and
the
single
sign-on
provider
domain
was
separated
from
those
other
domains.
So
the
user
wouldn't
interact
with
the
single
sign-on
provider
domain
enough
right
and
the
cookies
would
go
away
and
then
the
user
would
have
to
re-log
in
right.
C
So
now
you
you
may
get
sent
over
there.
Hey
do
you
want
to
stay
logged
in
within
that
time
frame
to
keep
the
you
know
to
keep
the
cookies
fresh
bounce
tracking
protection
is
something
that's
in
safari,
it's
actually
coded
and
in
the
latest
versions
effectively.
What
it's
looking
at
is,
if
domain
one
redirects
the
user
to
domain
two
and
gets
a
redirect
back
right
and
that
same
domain
is
seen
to
do
that
redirect
to
more
than
10.
C
So
and
then,
obviously
it's
it's
not
just
third
party
cookies,
you
know,
domains
that
are
classified
as
tracking
domains
have
limits
put
on
their
first
party
cookies
firefox
uses
a
fixed
list
from
disconnect.me
safari
attempts
to
use
machine
learning
in
browser
to
determine
which
domains
are
tracking
and
which
ones
aren't.
So
these
are
sort
of
you
know
the
the
privacy
protections
that
the
browsers
have
put
in
place.
You
know
to
to
help
protect
us
online
from
what
the
ad
people
are
doing
and
building.
C
You
know
the
targeted
ad
targeting
profiles
about
us,
but
they
do
sort
of
bleed
into
already
the
identity
work
that
we
do,
or
authorization
oauth
or
openid
connect.
So
let's
go
to
the
next
slide,
so
web
id
is
intentionally
trying
to
preserve
identity,
federation
and
sam
who's
driving.
This
is
on
the
call,
so
he
can
correct
anything.
I
say
that's
wrong,
but
fundamentally
they're.
Looking
at
sort
of
solving
three
problems,
one
of
them
is
the
ad
targeted,
ad,
targeted
tracking
and
basically
the
way
that
happens
today.
C
In
many
cases
uses
the
exact
same
primitives
that
identity
federations
use
rp
collusion.
This
has
to
do
with
multiple
rps,
getting
a
globally
correlatable
identifier
and
talking
about
the
user
behind
the
user's
back
globally
correlatable
identifiers
from
an
identity
perspective
tend
to
be
things
like
phone
numbers
or
email
addresses
and
then
there's
the
classic
sort
of
idp
privacy
leakage.
C
Problem
of
you
know
the
idp,
knowing
where
the
users
you
know,
knowing
where
the
user
has
asked
to
be
logged
into
before
the
user
agrees
to
log
in
they're
not
trying
to
solve
the
problem
of
if
the
user
says.
Yes,
I
want
to
log
in
the
idp,
knowing
the
user
logged
in
there,
but
just
that
sort
of
leaking
that
at
the
beginning
of
the
authentication
request,
rather
than
at
the
end,
the
the
focus.
As
far
as
you
know,
the
primary
focus.
C
You
know
that
that
drove
the
initial
sort
of
imp
proposal
or
explainer
is
you,
know,
sort
of
a
normal
consumer
on
the
web,
navigating
the
web
accessing
content
and
services
that
they're
interested
in
there
have
been
a
number
of
issues
added
academic
issues.
What
I'm
calling
first
party
sso,
which
would
sort
of
be
that,
like
that
case
in
australia,
where
you've
got
multiple
domains,
but
you
know
all
using
a
single
identity
provider.
C
So
is
logged
in
is
basically
a
proposal
from
apple
and
and
again
link
there.
If
you
want
to
go,
read
the
explainer,
the
in
a
nutshell,
what
they're
looking
for
is
the
browser
to
have
a
state
of
user,
a
is
actively
logged
in
to
domain
b,
and
then
you
know
user,
a
logged
out
of
domain
b,
but
it's
really
trying
to
just
sort
of
maintain
this
state.
This
bit
of
is
the
user
logged
in
there
or
not.
C
C
One
of
them
is,
if
you're
just
you
know
if,
if
you're
an
identity
service
and
you
deploy
on
the
domains,
you
know
you
deploy
in
the
domain,
so
it's
login.you
know
mycoolsite.com
right,
then,
when
the
user,
logs
out
it's
likely,
mycoolsite.com
data
is
cleared,
which
probably
has
a
whole
bunch
of
other
stuff
in
it.
That's
useful
for
first
party
tracking
that
isn't
related
to
authentication.
So
it's
unclear.
C
You
know
if
they're
going
to
just
clear
the
one
cookie
that
was
the
authentication
cookie,
but
the
explainer
basically
says
they
want
to
wipe
all
the
data.
So
I
think
that's
one
problem.
The
second
problem
is
we
today
right,
we
leverage
the
mechanisms,
we
have
to
establish
trust
for
a
given
user
using
a
given
browser
against
a
given.
You
know
relying
party
for
to
log
in
tends
to
be
cookies.
C
The
browser
can
validate
so
right
now,
what's
proposed
is
web
authen,
something
related
to
the
credential
api
and
password
managers,
which
takes
out
a
boatload
of
authentication
mechanisms
that
are
very
convenient
for
users
that
are
very
strong,
like
a
push
notification
to
an
authentication
app
on
their
phone
right.
The
browser
won't
see
any
of
that,
but
it's
a
very
strong
authentication
and-
and
so
I
think,
that's
another
area
where
you
know
we
have
to
under.
We
have
to
sort
of
figure
out.
B
All
right,
great
thanks,
george.
Now
what
like
first
thing
like?
We
know
that
these
things
affect
more
stuff
that
is
upstream
to
us
so
identity
like
as
a
working
group.
We
normally
operate
under
the
assumption
that
a
session
is
in
place
and
a
lot
of
the
mechanisms
described
here
pertain
the
session
rather
than,
but
so
it's
just
like.
If
we
are
downstream
river
and
someone
is
polluting
it
closer
to
the
source
we
still
suffer.
So
I
think
that
it's
useful
for
us
to
consider
whether
we
want
to
do
something
about
it.
B
Wherever
we
want
like
try
to
influence
the
course
of
bits-
and
there
are
a
couple
of
macro
areas
that
we
identified,
one
is
just
use
our
classic
playbook,
which
is
there
are
working
groups
that
describe
this
like,
for
example,
is
login
in
the
privacy
working
group
in
w3c,
and
so
we
can,
as
individuals
or
a
nominating
representative
participate
in
this
discussion.
And
if
you
go
through
the
minutes
of
meetings
in
the
past,
you'll
see
that
brian
participated
george
participated,
so
we
can
be
there
and
we
can
supply
our
perspective
as
things
develop.
B
This
might
work,
but
it's
gonna
be
a
bit
of
a
trench
bottle
a
trench
war
as
in
everyone
will
like
it.
It's
it's
gonna
be
hard,
like
I've,
seen
also
the
way
in
which
some
of
these
are
going
interactions
go,
and
it's
interesting
that
we
come
from
very
different.
Cultures
like
it
seems
that
the
browser
vendors
have
very
strong
assumptions
that
there
are
dramatically
different
from
the
one
we
have,
so
it's
not
always
easy
to
find
common
ground.
B
This
becomes
an
explicit
act
rather
than
in
the
result
of
the
browser
vendor
not
being
aware
of
those
scenarios,
so
somehow
it
might
make
it
easier
to
communicate
and
also
once
something
breaks
and
customers
come
after
us.
We
can
have
a
discussion
about
why
why
the
breakage
happened,
which
I
don't
know
if
you
had
experience
with
itp
and
same
side,
but
it
wasn't
fun
for
me
to
deal
with
that
with
customers.
B
A
Okay,
before
before
we
jump
into
the
discussion,
so
I'm
gonna
post
that
link
again
and
if
you
haven't
added
your
name
to
the
list,
please
go
and
do
that
because
I
see
different
numbers
here
like
I
see
about
36
people
on
this
conference,
but
I
don't
see
that
many
attendees.
So
please,
if
you
haven't
added
your
name,
go
and
add
your
name
and
now
to
the
discussion.
A
D
Not
very
profound,
but
I
did
want
to
correct
one
thing:
victoria
said
that
these
are
working
groups
within
the
w3c
they're,
actually
community
groups,
which
I
don't
fully
understand
the
difference
thereof.
But
you
know
one
important
thing
is
that
they
are
not
encumbered
by
the
same
kind
of
membership
qualifications
that
full-blown
working
groups
are
so
like,
because
they're
community
groups,
anyone
can
join.
I
think.
E
G
A
G
C
Yeah,
so
I
mean,
I
think
you
know-
maybe
something
as
it
relates
to
identity
will
get
big
enough
to
be.
You
know,
standards
track,
but
so
far
pretty
much
everything
that's
been
discussed
like
in
the
privacy
community
group,
around
privacy
features
from
browsers
has
been
implemented
and
deployed
by
the
browsers,
without
necessarily
becoming
an
official
standard.
C
A
F
F
You
know
an
issue
that
we
often
have
is
the
identity
of
the
client
and
the
browser
knows
the
site
that
is
asking
to
be
logged
in
or
asking
for
authorization,
and
so,
if
the
brow,
if
the
client
side
is
calling
an
api
to
the
browser,
and
then
that
comes
over
into
the
identity
provider,
the
browser
could
tell
the
identity
provider
identity.
Information
such
as
url
from
the.
A
E
So
while
I
like
the
idea
of
a
document,
let
me
also
just
encourage
dialogue.
The
people
that
I
see
involved
here
mostly
come
with
an
engineering
background,
and
you
know
I'm
used
to
having
these
hallway
conversations
at
the
ietf.
If
someone
doesn't
understand
it
and
you
go
spend
a
half
hour
with
them
and
they
understand
it
better
and
you
have
to
spend
another
hour
with
them
and
they
understand
it
even
better,
but
there
are
sincere
folks
here
and
they
want
to
understand
and
they
want
to
do
things
right.
So
you
know,
documenting
is
great.
A
Oh
and
obviously
that's
the
reason
we
are
having
this
discussion
here,
but
I
think
a
document
will
make
sure
that
everyone
is
on
the
same
page
and
what
and
we
are
not
talking
past
each
other
right,
so
it's
very
useful
so
but
but
yeah
we'll
take
in
a
sam
jeff.
You
had
some
comment
on
in
in
the
chat
there.
Do
you
want
to
talk
to
that,
or
is
that?
Are
you
satisfied
with
that?
B
B
Sometimes
I
I
believe
that
during
our
discussions
we
land
on
places
where
we
seem
to
have
really
fundamentally
different
assumptions,
which
is
why
I
believe
that
having
a
document
of
an
artifact
of
some
kind
might
make
some
of
those
things
more
solid,
more
evident
otherwise,
like
some
of
these
things,
just
get
lost,
but
definitely
most
definitely
the
dialogue
and
the
mutual
understanding
is
what
we've
been
trying
to
achieve.
This
is
just
like
moving
things
up
to
the
next
level.
F
Yeah
just
on
the
document,
obviously
I
think
we're
all
in
favor
of
it,
but
it
also
enables
us,
as
a
community,
to
get
rough
consensus
on
what
features
we
want,
as
opposed
to
you
know
a
bunch
of
one-on-one
point
opinions
and
there
isn't
really
consensus
on
we
want.
So
if
we
have
a
document,
we've
got
clear
consensus
on
the
features
that
work,
what
we
need,
etc,
and
then
we
can
have
be
much
more
organized
as
we
chat
to
other
people.
H
Jeff
yeah.
I
just
wanted
to
comment
that
I
do
think
it's
really
important
that
even
in
the
places
where
we
identify
that
we
need
to,
we
do
need
to
make
changes
and
we
do
need
to
accept
some
of
these
new
restrictions
and
everything
for
user
privacy.
We
also
need
to
be
really
sure
that
there's
going
to
be
a
clear
migration
path,
particularly
for
any
long
tail
rp's
that
are
out
there.
B
So
if
we
actually
wanted
to
go
ahead
with
a
document,
then
I
think
that
the
same
problems
will
be
voiced
by
other
communities
in
the
identity.
Space,
like
I'd
argue
that
the
open
idea
is
even
more
impacted
than
us.
In
fact,
if
you
look
at
all
the
all
those
proposals,
they
all
talk
about
establishing
the
session,
which
again,
as
I
mentioned
earlier,
we
had
a
bit
downstream
and
I
don't
think
it's
very
efficient
for
every
group
to
come
up
with
their
own
system.
B
So
I
don't
know
if
there
is
a
precedent,
but
like
I'm
wondering
whether
it
would
make
sense
to
make
a
pan
group
effort
in
which
open
id
cantara
and
these
other
people
that
are
as
affected
as
we
are
or
more,
we
can
actually
band
together
with
them.
Like
I
don't
know
what
are
the
bureaucratic
administrative
implications,
but
I
just
wanted
to
bring
this
up.
A
So
I
I
want
to
a
little
bit
understand
this.
What
do
you
mean
by
bond
together
like
there
is
nothing
that
will
prevent
anybody
from
joining
those
calls
and
and
contributing
to
any
document
on
on
a
work
group
document
here
like
what
did
you
see
more
than
that
like
what?
What
is
it
that
you
meant
or
have
in
mind
here.
B
So
what
I
mean
is
and
again
sorry,
if
I'm
not
yet
very
clear
on
how
the
mechanics
of
a
working
group
works.
But
what
I
mean
is
the
same
call
that
we
are
having
now.
I
think
we
are
likely
to
have
a
similar
call
with
the
open
and
you
connect
people.
So
if
this
document
needs
to
live
under
some
umbrella
like
so
first,
are
we
fine
with
collaborating
with
others?
B
Or
are
you
saying
that
we
should
tell
kantara
and
open
id
if
you
want
to
participate,
join
the
way
of
to
working
group,
like
I'm
thinking
more
in
terms
of
the
mechanics
of
how
to
put
this
document
together,
making
sure
that
the
identity
community
has
a
voice?
We
are
a
part
of
the
identity
community,
but
we
are
not
the
entire
thing.
A
Yeah
absolutely
the
goal
is
not
like
we,
we
are
we're
happy
to
communicate
or
or
collaborate
with
any
anyone
any
other
community
or
groups.
We
will
probably
have
to
discuss
those
like
that.
The
ways
to
do
that
later
on,
but
but
yeah.
Absolutely
it's
not
we're
not
excluding
we're
trying
not
to
trying
to
exclude
anybody
here
right,
so
the
more
the
the
better
right
for
sure,
okay,
anything
else
say
vittorio.
A
That's
it.
Okay,
george
said
academic
research
communities
as
well:
yeah,
okay,
yeah,
okay,
vladimir
david,
okay,
okay,
any
anybody
has
any
comments,
thoughts
beyond
what
we've
discussed
so
far.
I
see
a
strong
support
for
a
document.
So
let's
maybe
start
with
the
document,
and
then
maybe
we
can
discuss
how
to
bring
together,
oidc
and
cantara
and
others
to
collaborate
together
on
this.
One
right,
sam
go
ahead.
I
Well,
I
just
wanted
to
reinforce
support
here
for
any
form
of
feedback
that
you
can
provide.
You
know
there.
There
are
a
few
of
us.
We
were
getting
feedback
from
a
lot
of
people.
We
struggle
to
respond
to
all
or
to
digest
all.
We
know
that
identity
is
a
large
world
and
it's
not
our
intent
to
ignore
feedback,
so
we'll
take
that
as
a
gift.
I
So,
if
you
prepare
a
doc
to
us,
we
will
take
that
as
a
gift,
we'll
take
feedback
as
as
something
that
we'll
we'll
we'll
digest
meaningfully
as
far
as
format
or
how
that
gets
done
from
process
perspective
up
to
you
to
decide
whatever
works
best
for
you
all.
If
you
invite
me
to
some
of
these,
I
would
love
to
comment
and
and
have
some
shared
ownership
of
this,
so
that
maybe
increases
the
chances
that
we'll
we'll
have
will
have
a
you
know
higher
chance
of
converging.
I
So
I
I
also
wanted
to
just
kind
of
give
you
the
sense
of
just
my.
My
only
ask
is
that
you
remain
open,
open,
open-minded
and
that
you
understand
what
the
privacy
atmosphere
is
today
and
the
context
in
which
bronzers
are
coming
from.
So
you
know
as
much
as
we
you
know,
you're
also
digesting
the
other
side
of
the
equation
here
from
a
privacy
perspective
and
you're
and
you're
internalizing.
That
and
and
our
goal
is
to
preserve
federation,
but
the
parts
the
federation
that
you
know
are
within.
I
I
A
Yeah
and
just
to
make
clear
the
idf
process
is
open
to
anyone.
Anyone
can
join.
Anyone
can
look
at
the
discussion
recording
whatever
meetings
document.
There
is
nothing
that
prevents
anybody
from
joining
those
those
calls
right
so
just
to
be
clear,
like
I'm
not
familiar
with
with
other
organizations,
I
I
think
there
is
more
restrictions
there.
Itf
is
wide
open,
so
you're
welcome
to
join
anytime
yeah.
So
we're
not
trying
to
hide
anything
here
right
so
just
to
be
clear.
Okay,
anybody
else
has
any
comments.
Questions
I
think
clear
support
for
a
document.
A
A
A
B
Personally,
I
don't
think
I
can
lead
it
because
I
don't
know
how
much
time
I
have
I
I
need
to
go
back
to
my
bosses
and
see
if
they
are
okay,
we've
been
spending
a
lot
of
time
but
like
even
if
they
tell
me
yes,
you
can
spend
time.
I
cannot
be
the
only
offer
of
this,
so
I
hope
that
george
will
have
time.
C
I
don't
know
that
I'll
have
a
ton
of
time
either,
but
yes,
I
I
can
definitely
help
you
know
with
the
framing.
I
would
I
would
want
a
community
to
you
know.
I
think,
if
we
can
put
together
the
way
we
want
to
document
use
cases
right,
then
it
should
be
open
for
many
people
to
contribute,
because
for
sure,
the
use
cases
that
I'm
going
to
be
familiar
with
are
not
the
use
cases
that
you
know.
I'm
not
going
to
know
what
brian's
use
cases
are
what
aaron's
octa
use
cases
are.
C
So
I
think
we
have
to
use
the
entire
community
to
submit
those
things,
and
then
you
know
we
can
put
it
in
some
sort
of
structure
that
you
know
is
is
easy
for
people
to
follow.
So
I'm
happy
to
work
with
victoria
on
the
framing.
You
know
and
sort
of
structure
the
document,
and
we
can
put
some
examples
in
there,
but
we're
going
to
need
the
entire
community
because
I
for
sure,
do
not
have
the
the
global
scope
of
all
the
ways
we
use
identity
across
the
web.
B
The
other
thing
that
I
would
add
is
I'm
a
bit
burned
from
what
happened
with
the
idp.
If
some
of
you
guys
might
remember
that,
a
couple
of
years
ago
I
tried
to
put
together
a
document
in
which
we
went
back
to
apple,
saying,
hey
itp
is
breaking
this
number
of
scenarios.
I
tried
to
get
there
or
to
sign
that
document
so
that
companies
that
were
affected
by
that
could
signal
that,
yes,
they
were
caring
about
these
and
for
this
document
it
would
be
great.
A
Just
to
make
sure
so
so
vittorio
and
george,
you
will
start
at
least
that
document
is,
is
that
and
and
then,
if
we
need
to
add
more
people
to
to
that,
we
can.
We
can
add
more
volunteers
that
that
might
be
interested
in
helping
with
that
is
that
is
that
a
fair
kind
of
summary
here:
victoria
and
george
yeah
yep,
okay,
okay,
okay,
suggesting
to
use
github,
okay,
yeah,
okay,
any
go
ahead!
Sam.
E
A
B
B
If
you
can
see
some
of
the
things
that
occurred
recently
with
like
delaying
the
rollout
of
same
site,
delaying
on
ios
14
extra
checks
for
privacy
and
similar,
I
think
it
will
be
naive
to
assume
that
the
business
does
not
keep
the
scale.
So,
of
course,
the
goal
of
a
document
I
agree
completely
should
be
clarifying
the
use
cases.
However,
giving
a
sense
of
how
prevalent
that
use
case
is
versus
an
education
that
interests
the
subset
of
the
community.
I
think
it
can
really
drive
home
how
much
damage
this
thing
is
gonna
make.
J
A
Okay,
well,
that
was
a
great
discussion
guys
and
I
think
we
have
a
way
forward,
at
least
for
now.
Vittorio
and
george
will
start
working
on
a
document,
and
if
we
need
a
follow-up
meeting
after
that,
we
will
be
happy
to
schedule
more
meetings
to
continue
this
discussion.
And
thank
you
all.
I
appreciate
your
time
and
see
you.
