►
From YouTube: IETF-LPWAN-20221018-1400
Description
LPWAN meeting session at IETF
2022/10/18 1400
https://datatracker.ietf.org/meeting//proceedings/
A
B
B
A
B
C
A
B
B
B
B
C
B
B
Yeah
there
are
a
lot
of
interesting
side
meetings
at
this
idea,
so
we'll
have
to
navigate
that's
my
unique,
also
I,
know
sustainability.
For
instance.
We
are
very
interesting
meetings
on
sustainability
that,
if
you
care
about
iot
you
care
about
energy.
If
you
care
about
energy,
you
care
about
sustainability,
so
I
guess
the
the
guys
at
ATF
who
worked
on
on
iot
could
help
a
lot.
Other
groups
thinking
low
energy,
because
many
Protocols
are
not
designed
follow
energy,
for
instance,
with
protocols
which
was
broadcast.
B
They
are
not
thought
to
follow
energy,
because
if
you
have
to
listen
to
broadcast
all
the
time,
you
cannot
see
yes
and
she
broadcast
your
consuming
a
lot
of
spectrum
and
a
lot
of
energy
and
Wi-Fi.
So
so
it's
sort
of
thing
that
the
iot
people
should,
you
know,
explain
to
the
rest
of
the
ATF,
maybe
how
to
design
the
product
low
energy
protocols
through
this.
That's
a
start.
A
A
So
this
is
an
an
official
IHF
meeting
and
as
such,
the
ITF
policies
apply
so
by
participating
the
ability
for
ITF
processes
and
policies
and
all
these
policies
apply
to
you.
So
this
is
just
the
the
summary
the
note
12,
but
you
should
go
and
read
all
the
BCPS
that
are
presented
here
and
typically
in
case
you
are
aware
of
any
IPR
that
is
that
is
mentioned
during
the
call.
A
A
So
with
this
being
said,
so
we're
taking
minutes.
So
thank
you
Ivan
for
for
leading
the
minute
taking
efforts,
but
of
course
we'll
all
be
contributing
to
to
that.
So
you
have
the
link
here,
I'm,
not
sure.
If
Pascal
did
you
fix
the
the
link
because
in
the
no
no
okay,
if
you
click
on
the
link,
it
takes
you
to
a
different
URL.
So
it
takes
you
to
a
past
I
mean
to
type.
A
B
Before
we,
we
took
a
little
bit
more
time
than
usual
for
the
administrative
here,
because
we'll
be
talking
a
little
bit
about
atf-15
and
then
we'll
move
on
with
the
discussion
that
we
started
last
time
and
I
guess
Laura
will
take
the
lead
of
the
discussion.
But
basically
we
have
isolated
the
number
of
different
issues.
B
Sometimes
we
need
to
isolate
which
device
we
are
talking
to.
So
we
can
apply
the
right
set
of
rules
now.
Usually
a
set
of
rules
is
command
to
a
good
number
of
devices,
which
means
we
need
a
rule
ID
and
then,
which
gives
us
a
rule
set
which
applies
to
a
group
of
devices.
But
then
at
some
point
there
are
some
values
inside
those
rules
which
need
to
be
instantiated
for
a
given
device.
B
Like
is
IP
address,
so
we
need
to
discuss
what
is
really
the
device
ID
for
what
is
the
rule
ID
for
indicates
which
set
of
rules
and
if
the
rules
evolve
to
begin
sequence
number
in
them
and
then
the
rule
instantiation
and
and
that's
the
thing
we
started
discussing
and
I
know
on
our
side
we
have
a
little
bit
of
IPR
on
that.
You
know
using
some
kind
of
dollar
sign
to
replace
stuff
like
the
idea
of
the
device.
So
if
you
have
the
device
ID,
you
have
this
IP.
B
B
A
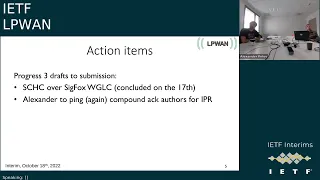
Yes,
so
that's
that's!
That's
so!
That's
for,
for
this
part,
I
think
that
so
I
did
not
look
it
up.
I
mean
I'm
not
going
to
speak
more
about
this
Anna
is
going
to
provide
the
the
full
overview
of
what's
happening
with
the
Looking
Glass
call,
but
it
seems
to
me
that
everything
works
fine
on
the
compound
act.
So
I
was
waiting
for
the
IPR
confirmations
from
the
authors,
so
I
have
everyone
except
Leon
that
have
answered.
B
A
A
So
yes,
Sergio,
can
you
hear
me?
Yes?
Yes,
just
one
note
in
the
compound
act
in
the
young
model,
there
is
some
sentences
that
doesn't
fit
the
the
page,
so
I
think
there
are
a
little
bit
of
the
need
that
says
that
but
I'm
not
exactly
sure
how
to
fix
it.
So
I
don't
know
if,
if
maybe
Laurent
can
help
us
check
that
out
to
see
if
we
can
compress
that
line
to
fit
or
or
do
something
similar
to
what
they
did
in
the
young
model.
A
C
A
A
B
Well,
yes,
and
yes,
we
have
to
fix
both
and
both
to
the
void,
commands.
I
mean
I.
Think
all
the
isg
members
give
you
the
same
command
is
a
waste
of
their
time.
So
please
don't
worry
about
you
know,
including
increasing
the
number
and
resubmitting
it
doesn't
you.
You
have
99
variations
versions.
If
you
like
to
fix
everything
and
republish
to
automobiles.
A
I
I
there's
just
one
question
that
I
asked
about
the
the
Sheikh
the
compound
deck
and
it
was
not
reviewed
but
by
a
young.
So
that
there's
a
specific
question
about
that,
and
it
seems
to
me
that
the
mod
is
not
big,
that
it's
quite
straightforward
and
I
compiled
it.
It
works
but
like
in
the
shepherd's
really
specific
question
like
was
it
reviewed
by
a
young
doctor
and
you
have
to
say
no
so
I
said
no,
but
blah
blah
blah
but
I
said
no.
But.
B
B
So
for
the
Chica
versus
it
was
concluded
yesterday
and
I
got
only
positive
note,
but
I
must
say
that
it
was
only
from
the
authors.
You
know,
my
impression
is
to
group
at
large.
Doesn't
care
too
much
about
sick
rocks.
We
never
got
many
reviews
on
the
sequence
document,
so
Eric,
it's
for
you
right
I
mean
the
it's
it's
kind
of
an
internal
effort
because
between
the
parties,
which
were
interested
in
sick
Fox,
which
is
like
a
group
within
the
group
and
they
they
seem
happy
with
the
work
they
produced.
B
I
guess
people
from
the
group
have
read
it.
They
are.
You
know
they
are
happy
with
it,
but
it's
just
a
subset
of
the
working
group.
Basically,
so
that
was
this
question
I
guess
in
the
shepherd
which
says.
Is
it
like
a
cork
team
interesting?
This
is
typically
a
golf
team
interested
so
I
mean
you
know.
When
you
promote
this
document
Eric,
you
have
to
know
that
it
was
really
the
work
of
a
specialized
core
team
inside
the
world
group.
A
B
A
A
B
A
B
B
So
this
is
this:
is
the
email
that
I
sent
so
usually
I,
don't
present
it,
but
this
time
I
will
that's
my
usual
email
I
just
charge
a
thing
here
and
there
as
it
was.
They
have
changed
the
agenda
link.
Now
it's
agenda
without
that
HTML.
If
you
try
that
HTML
it
doesn't
work
anymore.
So
it's
just
agenda,
and
so
we
have
a
November
11th
and
that's
the
very
last
meeting
so
from
noon
to
1,
30.,
so
I
hope
it's!
Okay.
B
B
B
So
the
dates
are
there,
the
the
engine
that
cutoff
is
on
the
26th,
so
it
would
be
nice
of
this
month.
So
it
would
be
nice
that
you
respond
by
the
25,
so
we
have
one
day
to
organize
the
agenda.
We
have
one
hour
and
a
half
considering
the
work
that
we
have.
It
should
be
enough,
but
please
tell
us
about
the
work
of
the
discussions
you
want
to
go
after
in
this
video
and
as
usual,
we
have
the
questions.
Rough
name
present
per
Etc.
B
B
A
B
B
Now,
if
we
look
at
Chicago
India
UT,
it's
a
lot
of
green
I
mean
I've.
Rarely
seen
documents
passing
so
well,
and
so
is
this
through
the
ASG.
Okay,
so
I'm
impressed
and
congratulations
to
the
authors
as
well
congrats,
except
that
the
ASU
recognizes
it's
a
very
good
document
and
I
expect
that
it
will
pass
quite
quickly
considering
the
all
the
green
darkness
in
here.
A
A
B
B
So
the
the
PCS
which
quote-unquote
should
be
standardized
by
three
gpp
are
just
informational
when
the
end
to
end
is
normative,
so
only
the
end-to-end
pieces
is
presented
as
normative
in
this
errors
to
come
so
with
this
leaves,
you
leaves
us
with
the
two
Sig
Fox
draft
to
promote,
and
if
you
look
at
it
after
that,
it's
just
the
architecture
and
actually
all
the
drugs
that
we
have
OEM
Etc.
They
they
are
all
like
expired.
B
B
B
C
B
C
C
C
C
C
B
Well,
that's
okay,
because
we
didn't
want
to
interrupt,
but
so
basically
what
what
you
said
on
the
previous
slide
was
like.
You
identify
the
rule
get
off
because
of
this
nation
IP.
So
basically
you
have
a
business
IP,
yes,
and-
and
you
said
basically,
what
you
needed
to
find
now
is
how
to
talk
to
device
or
something
like
it's
Market
drives,
and
you
have
a
table
somewhere
which
resolves
IP
into
Mac
like
take
advantage
of
an
ND
cash
right,
even
if
it's
not
used
by
ND
but
I'm.
B
Looking
at
the
architecture,
so
I'm
trying
to
figure
out
what
else
are
they
figure
that
there
is
one
component
which
matches
an
ID
in
the
IP
packet
like
this
National
IP
into
an
ID
in
the
lower
or
lp1
network
like
a
MAC
address
and
and
that
table
is
not
part
of
the
rules?
It's
it's
a
social
machine.
C
C
A
B
B
B
You
must
also
have
another
table
which
says
for
this
device
ID,
it's
this
rule
set
and
it's
a
third
table
which,
because
initially
you
said
I
need
to
find
to
have
a
device
ID,
because
for
this
device,
I
will
have
a
rule
set
set
of
rules
yeah,
so
that
you
also
have
another
table
I'm
trying
to
look
at
the
architecture
again
right
when
I
do
the
drawing
I
need
to
show
which
abstract
databases
you
have
one
of
what
is
the
rule
itself?
You
have
a
number
of
rules
in
the
table
of
rules.
B
Then
you
can
validate
when
you
get
a
packet
coming
in
and
you
match
a
rule
you
can
validate
and
and
so
so.
Basically
that
gives
you
the
rule.
You
you
look
at
the
IP,
you
get
the
device
ID,
you
look
from
the
device.
Id
you've
got
the
whole
set
and
you're
very
validate
that
it's
the
same.
So
it's
okay,
you're
good.
C
D
C
B
B
Yeah
yeah,
we
can
check
it,
but
if
we
have
the
three
tables
we
have
the
rules,
we've
got
VIP
to
Mark
and
we've
got
the
Mac
to
rule
set.
We
can
effectively
check
find
validate
that
the
rule
that
we
apply
on
the
incoming
packet
is
actually
in
the
rules
set
that
matches
the
magnet
class
we
can
validate.
C
A
B
You
can
validate
it,
so
we
can.
We
can
show
this
flow
that
the
logo
has
been
talking
about
that
this
moment
of
times.
We
we
so
the
rules
we
understand,
then
we
have
the
young
model
the
mapping
table
between
if
the
device
ID
is
the
Mac.
If
an
8K
Mac
it's
a
generalization
of
the
ND
cache,
so
we
understand
it,
and
so
the
the
real
question
we
are
discussing
is:
do
we
need
a
device
ID
to
index
the
table
to
know
which
rules
apply
to
this
device?
C
A
B
Say:
okay,
that's
that's
what
open
G
does,
but
it's
my
my
way
of
looking
at
it
would
be
I'm
getting
a
packet
before
I
match
any
rule.
I
go
to
my
ND
cash
I
find
the
device
ID.
If
I
don't
have
a
device.
Id
I
you're
lost
finished.
Yes,
if
I
have
a
device,
ID
I
know
this
device.
I
should
have
rules
for
him.
So
I
take
this
table
device
ID
to
rules,
I
have
a
set
of
rules
and
I
only
try
to
match
those
rules.
B
They
match
a
little,
but
I
would
I
would
not
match.
First
I
would
match
after
I've
found
from
IP
to
device
device
to
all
set
and
look
at
those
rules.
That's
why
I
would
look
at
it.
So
you
can.
You
can
never
have
a
rule
which
matches
for
the
wrong
device,
because
you
will
only
look
at
the
rules
which
fit
the
device.
That's.
A
B
B
We
were
talking,
for
instance,
on
the
rebuild
case
with
careless
and
with
ripple
you
always
have
a
tunnel
to
the
root.
So
say
you
have.
You
have
the
lower
device.
You
have
the
first
XLR
which
is
attached
to
the
Roja
device,
and
so
the
raw
device
itself
is
not
triple
aware.
It's
a
ripple
and
aware
leaf.
It
can
talk
to
the
first
XLR.
B
The
XLR
will
take
everything
he
gets
turn
on
to
the
root,
so
the
route
will
terminate
Sheikh
if
first
it
decapsulates
the
APD
IP
inside
it's
a
Chic
packet
so
from
the
tunnel
it
close
to
6lr
but
not
the
device.
So
that's
when
we
did
the
device
ID,
so
the
root
can
effectively
find
which
device
you
know
is
on
the
other
side
of
that
tunnel,
because
it
knows
the
6lr,
but
not
one
of
the
many
devices.
B
So
the
repo
the
repo
domain
would
be
exactly
like
you
haven't
spoke,
you
get
the
root
and
through
the
tunnels
every
lp1
device
appears,
like
you
know,
one
half
away
because
the
tunnel
was
just
Ripple
itself
is
not
visible.
So
we
we
need
a
device
ID.
So
we
know
which
rules
are
used
to
compress
the
root
will
select.
A
A
Sorry
I
know
you
want
to
move
further,
but
so
here
you
put
that
the
IP
address
is
the
identifier,
but
is
there
a
possibility
that
no,
but
then
it
becomes
like
a
nut,
I
mean
if
you
look
at
purely
from
Chic
perspective,
you
can
have
the
if
you
apply
shift
rules,
I
mean
the
way
opencheck
works
today.
Theoretically,
I
think
that
you
can
have
two
devices
that
have
the
same
IP
address
and
that
they
only
differ
in
the
UDP
port.
A
B
B
C
B
B
A
Let's
switch
it
to
us
now,
but
then
it
can
be
that
the
table
has
duplicate
entries
with
the
same
IP
address
and
the
same
and
different
devices,
and-
and
basically
that
says
well,
hey
can
match
to
any
of
these.
So
you
need
to
apply
ship
later
to
discover
which
one
you
actually
are
going
to
go
later
on.
B
Okay,
I:
don't
like
the
idea
to
use
the
rules
as
the
way
to
go.
Resolution
I
think
you
should
resolve
which
set
of
rules
work
for
this
guy
and
then
find
one
rule
in
that
set.
So
with
the
indications
take
this
initial
IPS,
this
is
one
device
for
IP.
You
know
business
type,
key
best,
ID
device,
ID,
Pro,
Set,
now
I,
but
choosing
the
rule
set
as
the
discovery
mechanism.
B
A
B
C
C
We
have
no
more
up
and
down
ascale's
States
so,
but
we
can
continue
new
to
have
this
notion
of
up
and
down,
but
it
will
be
very
limited
in
to
some
to
some
traffic,
and
so
that's
why
I
try
to
represent
here
is
that
we
need
in
to
identify
the
rule
by
an
element
that
will
be,
let's
say,
the
core
and
another
element
that
will
be
the
device
and
if
we
have
communication
that
has
symmetric.
So
here
we
need
to
to
have
to
identifier.
C
B
B
C
B
C
B
Matter,
it's
it's
you
all
of
this
point-to-point
connections.
They
live
their
life,
so
so
you
it
doesn't
matter.
If
you're
the
core
of
X
and
Y
is
Yoko,
doesn't
matter,
there's
no
chord.
There
is
an
application
inside
and
and
the
device
side
and
for
each
point-to-point
connection
the
device
will
be
the
one
that
starts
the
connectivity
that
stops.
C
D
The
the
way
to
address
all
of
these
is
that
the
the
end
points
that
will
communicate
need
to
know
in
advance
whether
they
will
be
acting
as
Dev
or
up
in
some
cases.
Perhaps
there
are
like
different
it
relationships
here
like
different
interactions
like
node
B,
maybe
using
one
role
when
talking
to
a
but
on
a
different
row
when
talking
to
Y.
D
So
perhaps
one
option
is
that
the
nodes
need
to
know
in
advance
somehow,
which
will
be
their
role
on
talking
to
each
one
of
the
other
potential
endpoints
and
also
perhaps
consistently
with
this.
The
the
rules
should
be
written
accordingly,
so
that
the
notes
should
know
in
advance,
which
are
the
rows
when
talking
to
each
specific
endpoint.
B
Yeah,
that's
if
you'd
want
to
do
Chic
flak
flat
over
the
mesh,
but
if
you,
if
you
establish
a
transport
layer
like
a
I,
don't
know
UDP
between
a
and
Y.
If,
if,
for
instance,
the
overall
I
have
a
demon
waiting
for
some
connection
like
this
or
it
could
be
PPP,
it
could
be
anything
as
soon
as
you
wrap
into
something,
and
somebody
has
to
start
with
something.
Then
then
you
know
who
started
it
and
it's
the
application.
It's
the
device.
B
B
B
If
you,
if
so
two
cases
first,
if
your
network
has
one,
then
you
don't
have
a
problem
right
repo.
There
is
a
root,
so
you
always
know
which
one
is.
When
you
have
a
real
mesh,
basically,
two
devices
you
talk,
they
need
to
know
they
have
to
talk,
and
basically
it's
not
just
a
random
X
talking
to
random
y.
B
That
needs
to
be
a
reason
why
X
and
Y
took,
and
they
need
to
kind
of
know
that
they
will
do
together
of
some
form,
and
so
my
suggestion
for
the
case,
where
you
don't
effectively
have
something
like
repo
to
say
who's.
The
root
is
that
you
expect
that
there
is
a
session
when
you
you're
saying
you
don't
have
a
session,
they
say
if
you
don't
have
a
scheduled,
that's
why
we
need
to
have
a
session.
B
C
D
B
Sorry
but
yes,
the
rule
needs
to
be
written
in
advance,
but
maybe
the
IP
address
of
a
and
the
IP
address
of
Y
should
not
be
written
at
the
time.
You
write
those
rules,
it
should
be
saying
dollar
device
and
Dollar
application,
and
once
you
decide
to
play
those
rules
between
a
and
Y,
then
you
would
reply
and,
and
the
session
is
starting
by
a
meaning-
is
the
device.
B
Then
in
every
rule
you
should
replace
dollar
device
by
a
and
dollar
up
by
y,
but
it
can
only
be
done
once
you
have
decided
who
plays
the
role
of
device
and
who
plays
the
role
of
the
application
because
effectively
otherwise
we're
in
the
loop
I
agree
with
you.
If,
if
you
write
the
rules
such
that
a
is
the
device,
then
a
has
to
be
the
device
you
should
know
in
advance
and
you
force
a
to
start
the
session.
Well,
all
good.
B
But
if
you
don't
know
we'll
start
the
session,
then
you
can
only
instantiate
the
rules
once
you
have
started
the
session.
So
that's
that's
why
we
add
in
the
title
we
have
this
concept
of
instantiation.
So
basically
the
rule
set
should
be
the
exact
same.
All
those
devices
are
equivalent
right,
they're,
all
the
same
same,
so
the
rules
for
a
to
talk
to
Y
or
a
to
talk
to
X
all
right
to
talk
to
W
should
be
the
same.
B
But
for
one
thing,
the
the
the
the
name
of
a
and
the
name
of
w
inside,
like
the
IP
address
inside
those
rules,
but
otherwise
the
rules
should
be
the
same.
So
we
should
not
have
1000
set
of
rules
flying
in
the
network.
We
should
have
a
single
set
of
rules
where
a
and
Y
and
W
Etc,
also
application
and
device,
are.
C
B
A
A
Different
problems
that
come
from
this
mapping
of
like
a
plane
up
and
down
to
open,
Dev
I,
don't
seem
to
recall
what
are
what
were
all
the
issues
with
because
they
were
like.
There
were
issues.
If
you
do
that
in
a
in
a
very
naive
way,
let's
say
and
but
I
think
that
it's
not
an
unsurmountable
problem
right,
so
I
think
that
we
need
to
have
a
session
specifically
on
that
have
like
a
small
I
mean
here.
A
A
C
So
we
have
a
topic
was
to
then,
if
you
want
to
provision
a
car
with
rules,
so
it's
to
find
a
way
to
identify
it
and
I.
Think
Pascal
made
a
very
nice
comment
last
time,
because
here
we
don't
have
to
identify
the
device,
but
we
have
to
identify
the
rule
and
we
have
to
take
care
of
sort
of
privacy
in
in
that
part,
and
the
last
point
is
about
security
and
I.
C
Think
it's
a
funny
thing,
because
if
you
look
at
the
Young
data
model,
in
fact,
you
can
give
a
readily
or
writerly
to
some
leaves
in
in
a
model.
So,
for
example,
here
I
say
that
all
the
leaves
concerning
the
field.
Id
are
writable
and
we
over
I
don't
know.
We
can
specify
your
sofa
then,
but
in
fact,
when
we
will
have
a
a
Chic
rule,
it's
not
what
we
want.
C
B
C
A
That's
actually
that's
I
would
I
mean
that's
actually
an
excellent
point.
I'd
say
that
maybe
we
need
to
ask
to
the
young
guys
to
the
young
guys
to
because
I
would
be
very
surprised
that
we
were
the
first
ones
having
this
kind
of
of
problematic
and
to
ask
them
hey.
Have
you
seen
that?
So
if
they
have
seen
it,
you
know,
how
did
you
solve
it.
B
Yeah
and
it's
not
only
to
say
I
mean
avocado,
which
say
if
it's
really
or
not
I
mean
you
should
have
a
way
to
enforce
it.
For
instance,
say
we
distribute
those
rules,
so
some
fields
are
rewrite
some
Fields,
so
they
are
mutable.
Basically,
and
some
things
are
not
mutable
and
the
rule
set
should
be
signed
so
that
the
non-miccable
fields
can
be
validated
because
you
will
distribute
the
rule
right.
If
you
have
this
big
mess
so.
B
D
B
C
B
C
Alex
approach,
because
when
you
write
a
young
data
model,
you
say
this
leave
is
readable
and
readable
or
writable.
You
have
a
model
that
can
allow
you
to
control
that,
but
maybe
there
is
a
way
to
say
when
we
can
allow
real
writing
only
if
the
value
of
this
Leaf
is
this
this
and
this,
but
I
am
not
so.
A
They're,
just
one,
there
is
one
more
point
also
here:
it's
identity,
so
authentication
who
has
the
right
because
I
mean
you
can
say
that
yeah
this
is
writable,
but
maybe
then
you
need
to
say
who
has
the
right
to
write?
It
I
mean
we
can
say
well,
it's
everyone
and
know
like
it's
either
it's
a
constant
or
everyone
can
can
write
it.
So,
like
that's
a
simplification,
yeah,
so.
B
So
when
you
don't
know
the
rule,
my
question
remains
right:
when
you
don't
know
the
rule,
there
are
material
fields
and
non-metal
Fields
now
I
will
say
which
one
I
mean
about
which
one
I'm
not,
but
it
will
not
prove
that
it
was
not
hacked.
So
if
everybody
obeys
the
rules,
yes,
you
will
only
mutate
the
mutatable
fields,
but
my
question
from
the
beginning
is:
how
do
I
know
that
nobody
has
done?
Got
it,
because
it's
not
because
it's
written
with
right
that
it
is
retry
I
mean
somebody
sends
the
bits
you
want
right.
So.
A
Yes,
actually
you
have
two
things.
One
is
the
values
that
are
there
and
this
is
like
you
get
from
somewhere.
Oh,
are
you
sure
that
that's
really
the
thing?
So
that's
the
first
thing
and
then
once
you
have
it
installed,
then
becomes
alive.
Let's
say
the
the
open
Chic
someone
sends
a
message:
hey.
Well
change
that
you
have
the.
Then
you
have
the
access
control.
Then
you
have
that
you
know
well
hey,
but
who
are
you
you
need
to
do
the
authentication
part
and
okay?
A
A
C
But
that
the
beauty
of
seabor
and
is
that
when
you
do
Ash
I,
think
it's
it's
similar,
you
don't
have
a
white
space
or
a
notification
that
makes
that
if
you
do
a
lash,
you
have
the
same
reason
form,
but
it
repeats
your
present
in
different
ways.
Here
we
have
something
that
is
easy
to
sign.
After
so
if
we
have
a
way
to
define
how
we
we
say
what
is
writable
and
what
is
readable,
and
we
trust
the
guy
that
sign
I,
think
we
we
solve
the
problem.
B
B
B
C
A
C
A
B
That's
that's
what
IP
does
I
mean?
Yes,
for
instance,
when
you
do
IP
site,
you
know,
and
we
have
a
rig
with
us,
but
basically
the
Elijah
is
you,
you
zero
out
the
mutable
fields
and
that's
that's
what
you
compute.
For
instance,
the
flow
label
is
mutable,
and
even
if
the
IP
standard
size
or
those
drugs,
they
say
you
write
this
or
write
that
or
don't
touch
it.
There
is
no
way
to
delete
it
if
it
was
not
touched
off
at
all,
because
it's
never
signed
right,
so
they
just
we're.
B
So
we
will,
we
need
to
look
at
which
rooms
and
I
don't
know
when
when
they
are
made
available,
you
know
to
book
basically
to
side
rule
these
side
roads,
but
we
need
to
book
one
and
it
depends
on
everybody's
travels.
So
all
the
guys
who
are
interested
in
that
discussion,
please
let
us
know
about
your
travel
environments,
because
we
we
have
this
constraint
to
book
that
room
pretty
much
near
the
meeting,
because
we
still
won't
be
there
for
the
whole
week.
Yes,
so
we
need
to
look
at
Thursday
or
Friday
I.
