►
From YouTube: IETF-LPWAN-20221004-1400
Description
LPWAN meeting session at IETF
2022/10/04 1400
https://datatracker.ietf.org/meeting//proceedings/
B
B
B
B
A
A
A
A
A
B
A
B
A
A
A
Yes,
so,
first
of
all
I'd
like
to
thank
and
to
thank
everyone
that
is
here
and
our
ad,
it
is
always
a
pleasure
to
have
our
ad
very
helpful
and
very,
very
responsive
in
the
meetings.
So
thank
you
Eric
for
this,
so
this
is
an
official
IHF
meeting
and
as
such,
oietf
policies
apply.
So
this
is
now
the
note.
Well
that
outlines
all
of
them.
A
A
A
So
you
know
we
are
taking.
Everyone
is
taking
notes,
I
mean
I,
I'll,
be
taking
some
notes,
and
traditionally
we
have
Anna
Sergio
that
are
taking
notes,
Pascal
and,
of
course,
Dominique,
but
please,
you
know,
take
do
participate
into
the
minute
taking
so
this
meeting
might
be
recorded,
I'm,
not
sure
if
it
is
always
recorded
now
on
me,
Techo
I.
Think,
yes
of
course.
Yes,
it
is
so
it
is
recording
everything
is
recorded
and
your
presence
is
locked.
A
A
For
the
agenda,
so
this
is
an
agenda
bashing
for
today.
So
if
you
have
any
modifications,
please
say
now
so
we'll
start
with
the
administrative
and
review
of
the
data
model,
reviews
also
nbiot
feedback
and
presentation
from
Aloha
about
the
device
identifiers
and
then
a
discussion
on
the
lp1v
chartering.
A
A
A
None
so
we
consider
the
minutes
from
the
last
time
approved
so
for
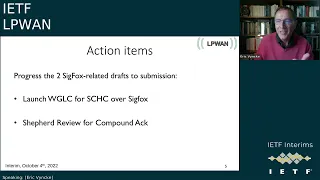
the.
Since
the
last
time
we
had
two
action
items
and
both
are
related
to
the
sick,
Focus
draft,
so
the
working
on
plus
code
for
Chicago
over
sick
Fox
and
Shepherd's
review
for
compound
ack,
so
the
working
group
last
call
was
started
so
Pascal.
A
B
B
A
No,
no,
but
that
that's
actually
an
excellent
point
and
thank
you,
Anna,
and
so
the
shepherd
review
the
shepherd
review
of
for
the
compound
deck.
So
I
did
a
review
that
good
news,
as
I
promised
so
I
have
a
couple
of
questions.
I
I
have
one
questions
which
I
asked
to
the
to
the
authors
on
which
I
so
I
I
have
not
received
all
the
answers
to
the
IPR
review.
A
A
So
this
is
this
is
one
point
and
the
other
point
is
about
Yang
doctor
review
so
because
the
she,
the
shepherd
review
for
the
compound
act,
I
mean
for
the
shepherd
review
it.
It
contains
a
Yang
document,
and
so
this
is
there
is
a
question
like
hasn't
been
reviewed
by
a
young
doctor,
and
the
answer
is
no.
A
Then
it's
not
like
a
big
change
to
the
to
the
it's,
a
quite
straightforward
young
model.
So
here
and
that's
probably
a
question
to
Eric
would
be
do
I,
publish
my
shepherd
preview,
Shepherd
preview
with
the
no
to
this
one
and
leave
it
like
this,
or
do
we
I
mean
I
my
so
my
initial
feeling
would
be
to
to
put
it
lock
it?
No,
it
was
not
performed,
but
it
is
a
very
straightforward.
Yang
document
so
and
I
have
compiled
it
with
piang,
so
I
mean
it
works
right.
A
D
D
Do
that
I
mean
everyone
is
a
small
group
right,
so
I
prefer
to
make
it
more
informal
and
more
efficient.
So
simply
you
you
put
the
list
in
CC
right
because
there's
a
working
group
document,
you
may
want
unicast
to
the
authors,
but
it
could
be
the
working
group
and
so
yeah.
You
need
to
do
this
this
and
this
and
this
and
they
should
do
it
right.
The
shepherd
is
really
like.
You
are
shepherding
a
herd
of
of
lamps
right.
So
you
are
the
shepherd
right,
so
guidance.
A
Because
it's
I
mean
the
new
format.
I
followed,
the
the
the
description
in
one
of
the
links.
I
actually
had
a
little
bit
of
hard
time,
finding
that,
but
finally
I
found
that
the
the
like
the
new
template
and
because
there
is
no
abstract
like
in
the
Past
reviews,
you
needed
to
write
a
little
bit
of
an
abstract.
What
it's
all
about,
so
I
was
a
little
bit
afraid.
I
missed
something
but
I'm
going
to
publish
it.
A
And
then
maybe
you
know
you
can
you
can
say:
hey
Alex,
you,
you
missed
this
one,
but
I
mean
I.
There
are
no
problems
like
just
to
like
spoiler
alert
like
there
are
no
problems.
Everything
is
really
in
good
shape
and
the
authors
did
a
good
good
job.
So
the
only
really-
and
there
are
there-
are
also
implementations
out
there.
So
it
looks
really
good.
So
the
only
point
was
about
the
Yang
thing,
but
I'm
going
to
write
this.
A
So
that's
the
shepherd's
review
for
the
compound
Act
and
with
this,
so
we
have
of
course
like
the
the
traditional
Milestones
that
were
updated.
But,
like
it's
it's
all,
you
know
for
me,
it's
it's
course
of
action
and
then
on
the
document
advancement.
So
we
have
I
mean,
like
things
are
advancing
well
today,
we're
going
to
be
talking.
A
B
We
we
could
delay
it
to
the
end
of
the
call.
I
mean
the
the
story
has
not
changed
since
last
week
since
two
weeks
ago.
We
have
not
discussed
it
much,
but
so
I
just
pushed
you
know
the
item
in
the.
If
we
have
time
left,
if
somebody
wants
to
jump
in
to
to
ask
for
something
specific
soon
enough,
we
will
start
producing
some
text
so
I'd
like
to
have
the
main
items
in
mind.
So
yes,
let's
discuss
at
the
end.
If
we
have
time.
B
B
I
will
provide
you
with
you.
I'll
ask
Juan
Carlos.
As
you
know,
that's
the
next
six
facts
to
provide
this
review
as
well,
but
we'll
see
you,
but
please
jump
in
I
mean
it's
not
a
very
big
draft.
The
technical
complexity
has
moved
to
the
compound
act.
The
most
peace
and
the
compound
Act
is
already
reviewed,
as
I
said
in
my
mail,
since
we
did
last
call
of
confident
that
was
version.
One
component
is
now
version
six,
so
it
makes
a
lot
of
sense
to
do.
C
B
E
Yes,
I
can
give
news
so
I
answered
to
all
the
to
all
the
comments
that
we
we
have
and
for
the
document
from
vhg.
So
maybe
I
I
made
a
mistake
because
I
just
click
on
the
grid
and
I
answered
to
all
the
area
director,
but
I,
don't
I,
don't
understand
really
what
how
it
is
DPS
display,
because
sometimes
I
see
that
everything
is
blue
or
green
and
there
is
still
a
red,
a
red
path
by
the
young
doctor
and
I
think
I
I
answer
to
it.
E
D
You
are
correct
now
the
change
of
colors
is
not
automatic
right.
It
needs
basically
an
ad
needs
to
click
somewhere
and
change
its
position.
So
in
this
case
this
is
Rob
Wilton,
which
is
by
the
way
a
colleague
of
Pascal
and
mine
based
in
UK,
so
I
I
prove
him
this
morning.
Hey
look
your
discus
point,
the
blocking
point.
D
You
have
provided
an
XML
instantiation
example,
so
it
should
lift
his
discus
I
need
to
check
this
afternoon,
but
maybe
he
has
already
done
it,
but
I
haven't
not
seen
it
and
then
it
will
change
the
color
and
then
basically
the
next
step
for
the
small
details
about
the
process.
If
you
want
to
know
if
it
wants,
everything
is
green.
D
It's
up
to
me
basically
to
physically
change
the
state
and
say
approve,
but
typically
what
I'm
doing
there
I'm
checking
for
all
the
other
comments,
even
if
they're
not
blocking,
if
I
think
they
were
sensible,
I
check
whether
they've
been
applied
into
the
document
and
I've
already
done
it
partly
and
I've
seen
a
lot
of
change.
So
you
mostly
follow
most
of
the
comments
as
well.
So
as
soon
as
Rob
is
acting,
and
it
should
be
very
easy
for
him
right,
okay
now
we
only
need
to
check
whether
the
XML
instantiation
is
correct.
D
D
So
if
you're,
confident
everything
is
fine
and
I'm,
confident
as
well,
it's
you
have
nothing
more
to
do
just
a
tip
for
other
times.
If
you
have
another
draft,
which
is
red,
glitter
square
right
for
the
ballot
ads
are
not
able
to
follow
all
the
draft
all
the
time
right.
So
you
come
after
one
day
or
two
day
you
contact
the
ad
by
email.
Saying:
hey
I
changed
my
draft.
D
E
C
B
C
C
B
Basically
triggered
me
to
write
okay,
a
letter
for
3gpp
to
let
them
know
that
we
have
this
draft
pending
review,
and
so
basically
the
document
has
the
notion
of
you
know
the
target
date
before
this
document
goes
to
the
ifg
as
increments
and
review,
and
let's
say
that
we
have
this
informational
pieces
in
the
document
and
and
started
start
to
track
the
piece
as
well.
So
the
normative
piece
as
well
I
did
not
see
any
answer
to
this
documentary.
D
Nothing
new,
so
honestly,
I
will
not
expect
three
gpp
to
give
a
reply
quickly.
Maybe
I'm
a
bad
face
right,
so
I
hope
that
I
can
send
correct
it
and
they
got
some.
Oh
that's
nice,
interesting
and
everything,
but
I'm
not
expecting
any
reaction,
but
at
least
we've
been
in
that
trip.
Then
we
have
food
really
is
also
we
cross
all
the
tea
and
we
put
a
dot
on
all
the
I.
Everything
is
fine.
D
C
D
Name
is
yeah.
If
you
know
him
personally,
you
can
do
it
now.
It's
not
Lionel
that
will
do
the
review.
Right
is
basically
the
liaison
so
outside
Gonzalo,
right,
Senator
liaison
statement
to
the
3gp
sketch
by
Lionel
and
then
Leona
in
dispatch
it,
and
we
are
no
more
in
CC,
I,
guess
internally
to
3gpp
and
then
the
the
reply,
if
any
will
go
the
same
way.
D
C
C
B
B
E
Should
know
okay,
so
this
will
be
not
so
new
because
it's
something
I
already
presented
during
the
last
ITF
meeting.
It's
to
discuss,
I.
Think
it's
something
very
important
now,
but
we
have
almost
a
young
data
model
is
to
work
on
a
device
identifiers
so
just
to
State
the
the
problem
right
now
in
yellow.
In
fact,
it's
what
we
have
developed
in
the
young
data
model.
It
means
that
we
are
covering
only
what
is
specified
in
RFC
87,
24
and
8824,
which
means
how
we
Define
the
rules.
E
E
So
one
thing
that
is
important
is
especially
right
now
in
the
core,
but
maybe
also
in
in
the
device,
is
that
we
have
to
identify
the
two
womb
belong,
this
set
of
rules,
so
we
have
to
to
find
a
way
to
to
do
it.
So
there
is
different
way
that
exists,
so
I
I
take
what
I
know,
for
example,
open
cheek
is
using.
You
have
two
two
communication,
two
possible
communication
right
now:
it's
either
to
use
a
UDP
tunnel
over
the
internet,
and
so
a
device
in
that
case
is
notified
by
the
keyword
UDP.
E
E
We
have
something
that
is
more
generic
that
has
been
defined
in
RFC
1939,
but
say
that
we
have
a
URL
that
is
defined
and
say
we
have
a
device,
and
this
is
a
MAC
address
and
then
we
can
put
the
dev
UI
at
the
end.
So
it's
what
I
know
now,
but
is
it
enough
for
what
we
expect
to
do
or
or
not?
For
example,
when
we
have
mac
address,
we
don't
say
which
technology
we
we
are
using,
which
means
that
normally
the
MAC
address
at
the
end
have
to
be
unique.
E
E
The
second
point
is
that,
if
we
do
it
do
we
do,
we
have
to
do
in
a
constraint
way.
So
for
for
me,
there
is
to
think
we
we
have
to
study
in
the
architecture.
The
first
one
is:
what
do
we
put
around
the
young
data
model,
so
we
have
to
include
IDs
so,
for
example,
on
here,
I
try
to
cover
all
the
case
we
we
saw
before.
So.
E
If
we
have
point-to-point
communication,
maybe
we
don't
need
identifiers,
because
it's
point
to
point
so
we
know
that
it
comes
from
Vivo
of
our
end
and
we
send
it
to
valorent.
So
here
we
don't
need
ideas.
What
we
are
working
right
now
is
the
start
apology
with
lp1s
network.
So
what
we
need
is
that
the
core
can
identify
to
which
device
the
rules
belongs
to.
B
Yes,
I,
don't
necessarily
agree
that
even
in
P2P
we
can
live
without
identifiers.
I
believe
that
we
do
need
your
players,
because
you,
for
instance,
say
you
have
this
IPv6
device
and
it
does
Auto
conference
address
and
the
tree
does
not
tell
you
what
device
that
is
and
so
that,
on
the
same
network,
another
device
which
is
kind
of
different
right
operates
at
very
different
rules
might
also
to
confident
rise.
They
will
be
on
the
same
64..
How
do
you
know
which
one
is
which
one.
E
For
me,
P2P
was
you
ever
there
already
established
link
and
you
work
on
that.
But,
of
course,
if
you
want
more
dynamicity,
then
we
we
have
to
to
cover
ever
the
start.
Apology
or
the
the
mesh
and
I
think
that
what
we
have
to
do
in
fact,
is
to
Target
the
mesh,
and
this
way
we
can
cover
the
other
cases.
Okay,.
B
B
E
It's
very
important
and
I
think
we.
We
had
also
to
add
this
in,
to
specify
it
in
the
architecture,
because
right
now,
I
don't
think
it's
specified
and
that's
very,
very
important
to
to
know.
So
what
are
the
capability
of
the
device
or
the
other
end
you
are
talking
to
and
right
now,
I,
don't
know
how
to
do
to
do
it.
So
even
the
young
model
will
not
the
curriculum
model
that
a
model
doesn't
cover
this.
It's
just
a
set
of
rules
that
we
have
represented.
B
Right
right,
basically,
the
PPP
draft
is
like
this
right.
When
you
basically
establish
your
PPP
connection,
you
have
to
negotiate
the
compression
technique,
so
we
have
defined
the
new
compression
technique
as
being
shake
and
and
when,
when
you
do
that
handshake,
there
is
some
room
for
data
and
in
the
data
it's
just
a
URL
of
the
the
the
the
the
model.
Basically,
the
the
rules
so
now
that's
to
go
and
fetch
that
rules
and
and
run
it.
E
B
Well,
it's
basically
like
I
try
to
open
the
P2P,
a
PPP
connection
with
you
and
they
say:
hey
I
want
the
compression
to
be
shake.
So
it's
step
two
and
the
URL
of
my
rules
is
this:
now
you
you
look
at
that
and
you
say:
do
I
support
check
if
I
don't
support
chick
type,
2
I
reject
if
I
support
I,
do
they
go
and
fetch
the
rail
can
I
run
with
these
rules.
It
might
be
that
you
can't
because
there
is
something
in
those
walls
that
you
just
don't
understand.
B
You
also
have
to
say
no
now,
if
you
can
run
run
with
those
rules,
then
you
will
say
yes,
it's
it's!
Okay,
when
you
can
go
and
fetch
rules,
I'm
wondering
that
cases
where
I
don't
know.
If
I
need
to
help
you
on
device,
I
guess
the
lp1
device
would
provide
the
URL
of
the
of
the
rules.
So
it's
yeah
from
the
internet.
B
E
B
E
B
So
that,
like
like,
we
said
there
are
two
things
we
need
to
identify
right
once
we
have
a
a
point
to
point
or
point
multipart
or
whatever
connection
with
somebody.
I
have
a
connection.
I
can
talk
to
you
right.
I
have
your
IP,
you
have
my
AP
or
something
do
I,
need
your
device
ID
or
do
I
just
need
your
rules,
at
which
point
do
we.
E
Need
an
ID
so
that
that's
a
good
question
and
I
I
am
not
so
sure
right
now
and
maybe
that's
the
difference
in
My
View
From.
What
I
presented
that
during
like
ATF
so
I
think
that
maybe
we
don't
really
need
to
identify
the
device
when
we
are
exchange
the
rule
between
two
Sheek
instance,
because
we
can
maybe
rely
on
Layer
Two
to
do
that
and
but
on
the
other
end,
when
we
go
to
a
database
and
get
the
information
here,
we
have
to
identify
the
which
information
we
we
need.
C
E
So
that's,
but
this
one,
let's
say:
okay,
we
we
do.
We
need
identify
identifier
between
the
device
and
the
two
Chic
instant,
so
not
so
I'm,
not
totally
convinced
that
we
need
one
and
I
think
that
if
we
don't
use
it
and
we
rely
on
layer
2,
then
maybe
we
will
have
a
stronger
security
because
we
cannot
cheat
and
you
cannot
access
to
something
else
and
from
the
other
side
do
we
need
to
I
think
we
need
something
to
identify
the
rule
on.
Could
it
be
your
RN?
B
And
this
is
very
much
the
way
the
PPP
draft
presents
It
Tattoo
as
well.
I
forgot
what
I
wrote
in
the
architecture,
nothing
much,
because
we
never
got
an
agreement.
But
yes,
we
if
we
agree
that
basically
the
model
that
you
have
in
front
of
you
is
is
the
reference
model.
Then
we
can.
We
can
document
it
on
the
architecture,
but
we
need
to
express
what
goes
in
the
urad,
because
at
some
point
you
need
a
urine
which
tells
you
this
unique
piece
of
information
that
you.
B
If
you
have
a
point
that
sorry
on
your
previous
point,
I
mean,
as
you
said,
if
you
don't
provide
something
for
which
protocol
that
is,
you
don't
even
know,
if
you
expect
six
bytes
or
right
bytes
and
and
if
you
have
none
of
the
IEEE
Max
but
something
different,
how
do
you
know
what
kind
of
Mac
address
what
kind
of
format
you're
going
to
get
so
it
looks.
It
looks
weird
that
that
we
have
something
without
you
know,
expressing
the
protocol.
B
And
even
careless
is
with
us,
so
you
have
longer
to
try
and
bite
and
short
addresses
which
are
by
the
ID
device
ID.
Basically,
two
bytes,
two
bytes,
and
if
you,
if
you
do
that,
then
you
know
it's
set
to
the
format.
It's
just
four
bytes,
and
how
do
you
know
which
one?
It
is
well,
it's
very
weird
and.
E
C
B
B
There
is
no
way
if
you
don't
know
that
it's
a
sick,
Fox
Global
I
mean
basically
it
cannot.
It
can
only
be
a
name
if
it's
a
global,
unique
address,
and
so,
if
you
rotate
max,
if
you
use
short
Mac
I
mean
there
are
tons
of
cases
where
the
the
Mac
can
rotate
and
and
they
won't
indicate
which
device
that
is.
E
So
I
think
we
we
have
also
to
to
cover
the
this
point,
and
there
is
a
subjection
in
section
in
the
review,
was
to
use
something
that
I
am
absolutely
not
familiar
with.
But
it's
a
network
configuration
as
X
control
model.
We
seems
to
give
access
to
leads
and
say
how
to
who
can
modify
it.
So
I
have
to
look
to
that
in
in
more
details,
but
maybe
some
interesting
approach-
I,
don't
know
if
it
works
well
in
constraint,
environment
if
I
call
my
representation
of
that
will
be
good
or
not.
E
E
It's
something
very,
very
important,
because
we
we
are
targeting
devices
that
can
be
very
intrusive,
so
we
have
to
to
take
care
about
privacy,
I
would
say
for
me,
it's
more
it's
orthogonal
to
what
we
are
doing
right
now,
because
it's
more
in
the
rule
by
itself
that
we
manage
the
address
that
will
be
sender
to
network.
So
I
will
just
take
the
example
of
Laura,
one
that
says
that
you
do
Ash
with
the
application
session
key,
and
so
it's
each
time
you
renew
your
join.
E
B
It's
something
I
studied
and
I
have
to
I
have
to
look
at
my
notes
and
what
I
did
with
that,
but
I
remember
when
I
was
trying
to
look
at
Chic
over
hamesh
at
some
point.
I
figured
that,
for
instance,
in
the
what
we
deploy
in
our
own
mesh
is,
you
know
for
smart
grid.
The
devices
are
mostly
the
same,
very
few
sorts
of
devices,
so
the
the
rules
are
the
same
for
hundreds
of
devices
in
one
mesh
and
you
don't
want
to
to
go
and
give
a
different
set
of
rules
to
each
individual
device.
B
You
want
to
distribute
the
same
rules
and
then
just
say
you
replace
dollar
IP
by
uip
or
something
so
so
having
you
know
some
pre-processing
of
the
rules
which
will
change
some
dollar
or
something
into
the
real
value,
some
of
those
values,
depending
on
the
network,
some
of
the
values
depending
on
the
device.
So
if
the
device
knows
is
on
dollar
Network
and
is
on
dollar
IP,
then
you
will
instantiate
these
rules
based
on
the
generic
rules,
implementing
the
dollar,
IP,
dollar,
Network
and
changing
everywhere
or
something
you
see.
E
B
Yeah
I
mean
the
resulting
model
of
the
instantiated
set
of
rules,
for
that
device
will
be
effectively.
What
you
have
described.
I
was
just
wondering
if
it's
purely
an
implementation
thing,
in
which
case
it
doesn't
go
in
into
any
standard
or
if
it's
something
that
we
need
to
write
somewhere,
in
which
case
we
need
to
standardize
something.
B
You
know
how
to
to
go
from
a
generic
set
of
rules
which
works,
Library
IP,
and
then
you
have
to
put
your
own
IP
everywhere.
There
is
the
rip
you
know.
Is
there
anything
that
we
should
standardize?
Or
is
it
Preparatory?
If
you
really
want
to
find
the
generic
rule
at
some
your
hand
and
the
IP
cannot
be
in
there,
it
has
to
be
dollar
IP.
E
B
Yeah
first,
you
need
to
find
the
rules,
but
then
you
need
to
instantiate
them
the
next
step.
Basically,
that
comes
after
that
and
if
the
rule
is
at
the
urine,
if,
unless
you
have
for
each
device
which
rotates
its
IP,
you
have
a
new
set
of
rules
that
that
URL,
which
is
or
basically
it
has
the
right
candidate
or
maybe
the
Uranus
question
mark.
You
know
IP
question
mark
whatever.
Then
you
have
to
pass
them
as
parameter
to
http
or
something,
but
but
we
have
to
design
all
the
way
we
can't.
E
E
B
So
everything
which
is
a
parameter
should
be
kind
of
isolated
and
I.
Guess
we
need
so
that's
my
question
to
the
group.
Do
we
need
to
standardize
that,
as
part
of
this
process
of
wrapping
basically
you're
wrapping
the
data
model
with
information
and
they
believe
that
we
we
know,
we
also
need
to
notify
the
the
parameters
in
the
rules
that
need
to
be
instantiated
for
each
device
and
into
to
basically
the
relocation.
If
I
can
talk
this
way
of
the
rule
to
that
device.
B
E
A
I
think
so,
I
think
that
it's
really
so.
These
are
really
super,
interesting
questions
and,
and
so
I
love
all
this
and
probably
the
so
that
that
comes
in
the
what
goes
into
the
architectural
draft.
And
what
do
we
do
in
the
chartering
but
I
think
maybe
in
the
architecture,
draft
and
Lawrence.
Thank
you
for
actually
putting
up
all
these
different
points
and
what
also
what
Pascal
said.
So
probably
we
can
do
a
short
write-up
in
the
like
yeah.
B
What
I've
seen
is
you
need
a
rule
ID,
and
so
so,
at
least
on
both
ends
know
which
role
to
apply,
but
do
they
need
to
know
an
identifier
for
the
other
hand,
I've
not
seen
that
yet.
On
the
other
hand,
the
rules
will
need
to
be
instantiated,
so
we
have
to
discuss
all
those
steps,
but
the
the
need
for
an
ID
has
two
primes
right.
First,
it's
not
problem,
we
need
one
and
second,
we
don't
know
how
to
build
it,
and
apparently
from
what
law
has
searched.
B
B
A
Yes,
yes,
that
sounds
like
a
good,
actually
an
excellent
point.
Pascal
when
we
ask
the
the
question
is
to
to
further
justify
like
to
determine
what
is
the
problem
we
are
trying
to
solve
because,
as
you
said,
the
home
is
starting
with
device
ID,
but
maybe
it's
a
different
thing.
So
what
are
the
properties
of
that
different
thing?
And
once
we
once
we
describe
that?
Well,
then
I
think
that
the
answer
is
going
to
be
very
straightforward.
Like
it's
going,
okay.
Well,
we
described
it.
B
We
probably
need
to
look
at
the
floor
right,
which
is
what
I
did
for
PPP.
I
looked
at
the
flow
I
said
hey,
we
need
to
establish
a
shake,
so
they
need
to
agree
to
understand
Shake.
Then
they
need
to
agree
on
which
set
of
walls
they
have
and
then
they
need
to
instantiate
the
rules
because
they
have
new
IPS
each
type
and
and
so
that
that
that's,
why
I
have
this
this
model
in
mind
now
the
and
that
doesn't
require
any
idea
for
at
least
for
the
flow
I
understand.
B
So
certainly
there
is
it's
not
just
the
URL
of
where
those
rules
are,
but
maybe
some
assurance
that
they
are
original,
that
they
are
not
and
they
have
not
been
touched
basically
and
corrupted.
So
it's
probably
it's
it's
a
signed
thing.
That
needs
to
be
some
agreement
on
how
you
go
and
fetch
them
and
ensure
that
they
are
correct.
So
it's
not
a
simple
thing,
but
it
does
not
require
me.
E
Sorry
I,
maybe
I,
should
have
asked
the
right
to
talk,
but
just
to
on
this
point,
since
it's
very
difficult
to
to
have
a
signature,
an
authentication
if
we
don't
have
a
canonical
format
for
rules
and
thanks
to
Kamai
akokov,
we
have
something
that
is
very,
very
strict
and
cannot
change
easily
so
to
have
a
signature
on
it.
It's
quite
easy.
E
A
The
difference
is
the
different
thing:
coreconf
is
the
protocol,
so
the
way
to
represent
is
either
in
Json,
let's
say
on
c
bar
or
XML.
Once
you,
you
write
down
the
the
Yang
data
model,
like
the
the
expression
of
the
young
data
model
and
that
expression
is
going
to
be,
let's
say
in
sibo,
so
you
have
the
Yang
to
seaboar
RFC,
which
is
now
an
RFC,
so
you
can
actually
serialize
your
yang
data
model
in
a
cboard
representation,
and
this
this
gives
you
a
canonical
representation.
E
And
I
think
this
nickel
representation
is
more
stable
than
the
Json
or
XML,
because
if
you
add
a
space
in
a
Json
or
XML,
it
will
not
change
the
representation,
but
it
will
change
a
hash
which
is
not
the
case
with
coconut.
Because
cyborg
is
you
don't
have
space?
You
have
a
very
strict
format
to
represent
the
information.
B
Okay,
which
is
back
to
the
question
he
said,
is
there
a
prime
to
say:
oh,
let's,
let's
use
conf
to
go
and
fetch
it
or
do.
Can
we
make
it
the
default
and
then,
if
in
the
future,
somebody
defines
something
else,
because,
basically,
when
you
have
this
picture,
whether
the
app
goes
to
fetch
the
rules
from
from
you
know,
the
server
on
the
top
right
I
mean
if
if
the
server
can
be
trusted,
doesn't
prove
that
the
server
has
the
right
information,
it
could
have
corrupted
information.
B
So
it's
much
better
to
be
able
to
check
that
the
data
itself
that
you're
fetching
from
the
server
is
correct.
So,
for
instance,
if
if
the
device
on
the
left
can
produce
the
key,
the
hash.
Basically
you
know
after
the
the
rules
to
be
downloaded
and
it's
it's
it's
obtained
as
sibo,
then
effectively.
We
we
it's
like
when
you
download
open
source
code
right,
you
download
a
new
image
of
your
favorite
distribution.
B
You
basically
have
the
whatever
hash
of
the
the
image
that
you're
going
to
download
and
now,
when
you
once
you've
done
load,
you
can
validate
that
the
ash
is
correct.
Same
thing
here,
the
the
device
on
the
left
when
he
says
go
and
fetch
is
your
end.
It
could
also
say
here
is
the
hash
of
what
you
expect
and
then
the
device
on
the
right
could
get
it
from
anywhere.
As
long
as
the
Azure
40
gets
fits
he's
kind
of
happy
that
the
the
the
the
the
rules
that
they
obtained
are
correct.
Right.
D
B
Yeah,
which
is
the
device
effective
the
design
effectively,
because
if
you
have
a
factory,
for
instance
and
and
you
have
tons
of
devices
sensors
in
the
factory,
you
want
a
local
server
to
own
to
to
locally
copy
all
the
rules
right
that
are
implemented
by
all
the
devices
and
then
your
switches,
your
Cisco
switches,
which
talk
to
those
devices,
will
go
and
fetch
the
rules
on
that
look
or
repo.
They
don't
want
to
go
to
the
manufacturer
or
HTTP
site
or
something
inside
the
factory.
Usually
you're
cut
off,
showing
the
control
Network.
B
You
will
not
have
access
to
the
internet,
so
it's
very
important
to
have
this
capability
to
to
go
and
fetch
the
rules
law
calling.
So
it
has
to
be
local
urines
that
you
can
fetch,
but
I
think
the
switch
capable
to
to
download
from
the
right
and
and
check.
You
know
that
it
matches
the
ash.
That's
the
plane
from
the
device
on
the
left,
then
we're
sure
we
can
start
working,
because
if
we
don't
have
the
right
rules,
I
mean
anything
can
happen.
It's
really.
We
really
need
to
have
the
right
tools.
B
A
E
B
B
A
B
I
I
I'm,
not
at
all
the
ex-conf
guy
or
even
the
sibo
expert
or
anything.
So
what
I
can
write
is
the
global
view
of
this
and
then
Alexander.
She
can
please
go
down
to
okay,
there
is
what
you
get
with
the
URL
and
it's
this
format
and
whatever
said
about,
you
know
the
for
the
fact
that
it's
canonical
blah
blah
blah
I
mean
I.
I
will
need
you
to
add
some
text
here
and
there
to
make
it
to
make
the
picture
correct.
B
A
D
A
B
From
there
there
are
two
things
which
can
happen:
I
mean,
as
we
know,
we
need
to
I,
don't
have
to
to
update
the
rules
for
each
device
to
put
the
IP
of
the
device,
for
instance,
if
it's
being
compressed,
and
so
it
can
happen
on
the
top
right,
in
which
case
you
need
to
run
code
on
on
the
server
which
understands
how
to
change
IP
with
the
real
IP.
So
you
need
to
go
to
provide
question
mark
IP
to
the
right.
B
Thank
you,
big
big
thanks
for
you
know,
starting
all
those
discussions,
and
so
let's
continue
on
why,
if,
if
effectively,
we
need
a
real
ID
somewhere
and
I'll
start
documenting,
at
least
this
slide
in
the
architecture
and
then
work
with
Alexander
about
the
exact
wording
of
stuff
and
then
we'll
publish
a
new
version
of
the
architecture,
but
for
now
I
don't
feel
at
ease
to
talk
about
device.
Id
I,
don't
see
the
need
and
I
don't
see
so
I
can't
write
it.
We
need
to
to
talk
more
okay.
B
Okay,
so
thank
you
all
for
for
this
great
meeting
and
well.
We
meet
again
for
the
last
time
in
two
weeks
and
after
that,
I
guess
we'll
be
getting
ready
for
the
ATF
in
London.
So
again,
thank
you
all!
Please.
You
please,
in
the
next
hour
to
go
to
the
minutes
and
check
that
what
you
said
is
correctly
captured
and
at
the
end
of
the
day
today,
I
will
basically
take
the
whatever
is
in
the
code
EMD
and
push
it
as
the
minutes
of
the
meeting.
