►
From YouTube: IETF-CBOR-20221005-1400
Description
CBOR meeting session at IETF
2022/10/05 1400
https://datatracker.ietf.org/meeting//proceedings/
A
A
A
Yeah,
hello,
everyone,
yeah,
yeah,
I,
it's
the
problem
with
can
I
just
see
Ira
that
I
didn't.
Oh
there's
her
card
yeah,
it's
the
problem
with
the
sort
that
I
did
and
not
noticing
the
ones
that
say
participant.
Okay.
Well,
then,
that's
a
that's
enough.
People
let's
get
started
so
welcome
to
the
the
seabor
interim
call
and
there's
one
item
on
the
agenda.
It's
Carstens
it's
to
talk
about
coordination
with
sedate
and
issues
with
the
time
tag
document
Carson
go
for
it.
B
B
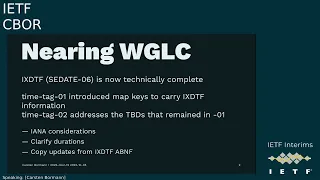
We
have
been
talking
about
the
Civil
term,
take
for
for
a
couple
of
years
already,
and
it
has
been
the
working
group
draft
and
for
a
while.
We
haven't
really
done
very
much
with
it,
because
we
were
waiting
for
the
seedage
working
group
to
define
the
internet
extended
date,
time
format,
which
is
essentially
RFC
c39,
with
the
addition
of
hints.
B
So
we
were
kind
of
prepared,
and
what
has
now
happened
is
that
the
city
bring
group
things
they
are
done,
and
so
now
we
we
suddenly
had
to
do
our
homework,
because
there
were
a
few
DVDs
in
the
documents
too
to
release
that
I
think
all
have
pretty
obvious
resolutions.
But
of
course
we
have
to
look
at
whether
I
think
and
I
did
this
in
the
right
way
by
the
way,
Hank
is
apologizes
again
because
he
has
this
standing
conflict
with
the
even
weak
meetings
at
this
time
slot.
B
So
we
had
to
fill
in
some
Ayana
considerations.
We
had
to
put
in
some
clarifications
about
durations
I,
didn't
prepare
slides
on
these,
but
I.
Think
if
you
care
about
durations,
you
may
want
to
to
read
the
the
additional
text
that
that
is
trying
to
clarify
them
and,
of
course
we
copied
update
over
from
the
sedate
changes
to
their
a
b
and
F,
because
the
ABN
F
essentially
governs
what
what
keys
10
and
11
can
can
point
to.
B
B
Of
course,
it
ripples
through
a
lot
of
documents
that
are
using
3339
but
I
think
the
the
actual
practice
should
be
closer
to
to
what
the
result
of
the
update
will
be
then
to
what
what
is
before
the
update,
so
I
I
see
see
the
the
message
that
went
out
to
art
at
edf.org
to
the
seaball
working
group.
So
you
so
you
know
this
is
going
on
and
so
far
we
we
just
had
one
request
for
for
information.
B
So
let's
see
how
how
that
is
going
so
just
cleaning
up
things
on
on
our
side.
Ariana
considerations,
time
scales,
are
an
obvious
extension
points.
We
currently
only
have
Tai
and
UDC
in
the
document,
which
are
the
obvious
ones
that
you
want
to
have
and
additional
time
scales
like
GPS
or
NGP
can
be
accommodated
by
by
just
converting
them
into
Tai
and
UDC.
So
time
scales
that
have
a
well-defined
conversion,
such
as
a
constant
offset
GPS,
is
just
19
seconds
different
from
from
Tai.
B
So
there's
really
no
point
in
supporting
that
for
interchange,
you
should
be
using
gai
then
so
these
should
not
be
registered,
and
the
policy
here
is
is
a
combination
of
expert
review
and
RFC
required.
So
Roc
required
is
probably
the
the
right
thing
for
for
something
that
is
as
Grave
as
adding
a
time
scale.
B
It's
not
iotf
review
it's
RFC
required,
so
people
can
actually
do
something
like
do
an
irtf
document
for
a
new
time
scale
or
even
an
independent
submission,
but
that's
the
reason
why
we
want
to
add
expert
review
to
that
as
well.
So
we
cannot
just
have
a
random
independent
submission
defining
time
skates.
That
then
turn
out
not
to
be
interoperated,
so
I
think
commented
that
maybe
we
should
add
ut1
as
well,
so
ut1
is
essentially
the
smooth
version
of
UTC
or
the
the
target
to
which
UTC
adjusts
itself
using
leap
seconds.
B
B
So
that's
the
time
scale.
Registry.
The
map
key
registry,
is
pretty
obvious.
It's
pre-filled
with
the
map
keys
that
are
defined
in
in
the
spec
in
in
the
time
tag
draft
and
the
policy
for
additional
registrations
will
be
specification
required,
which
also
includes
expert
review,
but
does
this
by
definition
of
the
term
and
there's
also
an
request
to
the
expert
reviewers
to
curate?
B
B
Bound
to
something
like
a
time
zone
or
a
time
offset
from
the
time
scale
only
by
local
context.
So
if
I
tell
somebody
we,
we
will
meet
tomorrow
morning
at
8..
That
is
a
floating
time,
because
this
communication
only
makes
sense
if
we
have
common
contexts
that
identifies
which
time
zone
I
I
mean
by
eight.
B
So
these
are
often
useful
and
we
actually
have
tag
100,
which
is
based
on
floating
times,
but
it
when
discussing
this.
We
notice
that
that
the
MTP
working
group
is
also
looking
at
floating
times,
and
the
assumption
is
that
we
want
to
do
this
in
a
way
that
is
compatible
with
what
ntp
will
come
up
with,
but
it
will
take
another
year
so
a
year
and
a
half
for
that
to
converge,
so
this
probably
should
be
added
later.
B
B
The
document
has
negative
map
Keys,
which
are
ignorable
information
items,
and
it
has
unsigned
ones,
non-negative
ones
that
are
critical
and
the
the
status
so
far
was
that
the
only
critical,
critical
piece
of
information
was
the
base
time.
So
only
one
key
could
ever
be
unsigned
the
base
time
key,
which
could
be
a
different
one
for
five,
depending
on
the
representation
of
the
base
time,
but
there
could
only
be
one
of
them
and
now
it
turns
out.
B
We
have
critical
informations
or
information
that
must
be
understood
by
the
consumer
of
the
tag,
and
it
makes
sense
to
use
enzymed
non-negative
keys
for
those.
So
essentially
the
the
obvious
or
straightforward
fix
for
this
is
to
limit
this.
Only
one
key
restriction
to
the
base,
time
keys
and
then,
of
course,
we
need
to
know
whether
he
is
the
best
time
key
or
not.
But
since
all
the
critical
keys
are
the
ones
that
that
their
consumer
is
supposed
to
know
to
process
the
document.
B
B
And
finally
one
thing
that
came
up.
We
have
a
pretty
good
set
of
of
map
keys
that
describe
time
in
more
detail
which
are
essentially
stolen
from
PDP
from
IEEE
1588,
not
directly,
but
through
their
Zhang
model
of
through
the
email
that
the
IDF
has
created
for
1588.,
and
that
is
pretty
pretty
useful
because
we
can
replace
some
some
ad
hoc
stuff
with
that.
B
However,
there
is
one
piece
of
information
that
currently
cannot
be
expressed,
and
that
is
whether
the
timestamp
is
is
a
planned
or
computed
timestamp
or
an
actual
time,
and
that
may
be
important
because
time
scales
are
not
entirely
predictable
if
they
were
entirely
predicted
or
we
wouldn't
need,
several
of
them
would
just
use
one.
So
we
we
know
how
Tai
and
UTC
relate
to
each
other
for
the
past,
but
we
don't
know
it
for
the
future,
at
least
the
future
more
than
a
few
months
ahead
because
of
leap
seconds.
B
So
all
this
stuff
is
is
really
only
of
interest
to
people
who
care
of
accuracy
down
to
a
second
or
less
so
for
most
applications.
You
can
completely
ignore
this,
but
for
for
applications
that
need
this
and
Yes.
Actually,
even
some
security
applications
want
to
know
when
something
happened
very
precisely.
B
There
may
be
maybe
useful
to
add
a
flag
for
this
distinction,
so
my
current
view
of
this
feature
is
we.
We
definitely
want
to
have
that,
but
we
may
want
to
wait
until
we
have
talked
to
enough
time
not
to
understand
whether
we
actually
want
to
add
more
information
to
this
than
just
the
flag
between
planned
and
actual
times.
So
since
these
keys
can
be
registered
by
by
anyone.
It's
it's
not
hard
to
end
that
so
here
again
my
a
recommendation
would
be
one
fix.
B
So
with
that
said,
we
are
now
entering
this
discussion,
which
happens
on
several
mailing
lists.
The
art
mailing
is
the
C
date,
mailing
list,
ntp
and
Tick
Tock
have
been
addressed
and,
of
course,
the
the
sibo
mailing
list.
So
within
the
next
two
weeks
we
might
get
some
some
additional
issues,
some
additional
information,
some
additional
editorial
corrections
as
well,
so
my
assumption
would
be.
We
should
be
able
to
have
a
digital
three
ready
for
working
class
call
before
ietf
115
at
rb4
October
24th.
C
A
question
about
the
flag
for
Planned
time
versus
actual
time
functionally.
It
makes
good
sense
to
me,
but
how
do
we
know
that
the
originator
sets
the
flag
correctly
and
doesn't
it
have
really
bad
side
effects
if
they
set
it
to
plan,
but
it
is
actual
because
we
can't
translate
well.
This
would
raise
this
flag
is
more
dangerous
than
not
than
not
addressing
the
issue.
B
C
C
B
C
A
C
B
A
B
So
it's
really
a
complicated
area
and
I
I
was
very
surprised
to
read
message
on
the
course
and
mailing
list
that
apparently
the
the
result
of
the
discussion
was
not
to
use
the
the
Cozy
way
of
representing
cheese
but
use
the
hpke
way
which,
as
I
said,
is,
is
not
really
fully
defined.
At
this
point,
one
of
the
things
that
that
we
did
when
we
defined
cozy
was
trying
to
get
rid
of
of
20
30
years
old
baggage
and
weird
key
representations
and
come
up
with
key
representations.
B
D
B
B
So
I'm
I'm
not
entirely
sure
that
that
the
fact
that
the
discussion
is
over
means
that
we
cannot
have
this
discussion
now
so
that
that's
why
I'm,
bringing
this
up
I
really
don't
understand
what
it
means
to
use
an
hpk
Library
representation
Because.
Unless
that
is
standardized,
that
doesn't
mean
anything.
D
Well,
in
the
the
E
spec
the
place
where
that
appears
is
opaque,
and
so
that
that's
really
the
thrust
of
the
argument
is:
do
you
have
to
convert
the
opaque
thing
into
a
cozy
key
or
not,
and
because
the
the
hpke
interface
basically
treats
that
as
a
internal
thing?
That
is
not
need
to
be
standardized,
and
anyway,
I
I
think
that
that's
going
in
the
wrong
direction,
as
I
already
said,
is
that's
the
reason
for
my
stepping
away
from
that
document.
B
Okay,
so
so
raising
attention
here
to
this
item
is
about
all
we
can
do
here,
but
I
think
that
this
is
a
major
change
in
the
the
underlying
principles
of
how
cozy
operates.
What
should
be
worked
on
by
the
Cozy
people,
of
course,
but
I'm
not
sure
that
this
is
being
curated
in
in
the
right
way.
Right
now,
anyway,
we
will
need
to
discuss
this
in
in
the
Cozy
environment.
B
C
Okay,
cddl2,
of
course,
has
much
interest
far
beyond
the
ITF
ly,
and
my
two
cents
on
the
Cozy
and
hybrid
public
key
is
merely
to
observe
that
the
NSA
has
come
down
strongly
against
hybrid
public
key
inside
NSA
2.0,
and
this
doesn't
be
supporting
it
as
much.
So.
I
also
really
dislike
the
idea
that
doesn't
matter
that
it's
opaque
in
some
hybrid
Public,
Library,
neurode
Posey
and
for
things
derived
from
closing
of
which
are
far
more
than.
