►
From YouTube: IETF-LPWAN-20220308-1500
Description
LPWAN meeting session at IETF
2022/03/08 1500
https://datatracker.ietf.org/meeting//proceedings/
A
A
A
A
A
And,
as
usual,
this
meeting
is
being
recorded.
It's
you
can
see
on
the
bottom
right.
There
is
a
recording
tag
which
is
actually
red,
so
we
are
recording,
minutes
are
being
taken
and
help
is
very,
very
welcome
for
capturing
the
minutes.
The
link
is
provided
in
the
agenda
on
the
data
tracker.
I
actually
sent
an
email
to
the
list
where
you
can
see
all
the
links
in
the
data
tracker
with
the
agenda.
A
A
So
the
agenda
for
today
we
have-
we
have
so
the
administrative
here.
I'm
missing
one
item,
I'm
sorry
for
this.
So
the
agenda
on
the
data
tracker
is
up
to
date
and
for
some
reason
it's
missing
here.
So
so
we
have
the
data
model,
worker
plus
core
five
minutes.
Then
we'll
be
discussing
continuing
the
discussion
that
carles
has
started
about
the
the
role
of
device
and
application
and
then
at
1645
we'll
be
talking
about
the
shepherd
review
on
compound
ack
and
I'm
sorry
that
they
failed
to
update
that
slide.
A
A
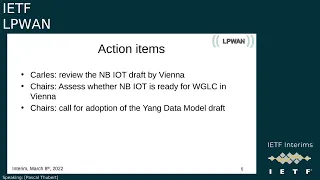
So
we
had
a
number
of
action
items.
The
first
two
action
items
are
not
targeted
for
this
meeting.
It's
just
a
gentle
reminder
that
carlos
said
he
would
review
the
npiot
draft
by
vienna
time
and
based
on
that
and
their
own
reading.
The
chairs
will
assess
whether
the
nba
ut
document
is
ready
for
workplace
calls.
So
we
will
have
an
nbiot
session
in
vienna
and
you
will
see
that
anna
has
asked
for
a
slot
anyway.
A
A
Less
than
a
week,
I
guess
now
around
a
week,
so
I've
not
seen
any
review
published
to
to
the
mailing
list.
So
please
be
be
very
aware
that
the
young
data
model
last
call
is
running
and
any
level
of
review
is
important.
So
if
you
can't
spend
time
looking
at
the
gory
details
of
the
model,
but
you
have
a
number
of
checks
that
you
would
like
to
do.
Please
do
this
check
and
post
something
on
the
mailing
list.
I
understand
the
data
model
is
not
easy
to
review
anyway.
A
A
We
are
a
little
bit
behind
for
nba
iot,
but
if
we
start
the
world
go
plus
core
in
vienna,
we
are
not
that
far
off
because
we're
supposed
to
to
be
shipped
to
the
asg
by
february.
So
we
are
just
two
months
off
basically
so
so,
what's
new,
we
have
a
three
new
publications
of
the
giraffes,
also
chic
over
and
the
iot
that
we
will
discuss
at
the
atf,
but
and
if
you
want
to
give
a
few
words
you're,
not
in
the
agenda
for
today.
C
A
A
A
A
A
B
It's
slightly
different
as
well
as
managing
the
queue,
and
I
would
suggest
that
lauren
also
look
at
this
training
simply
to
managing
the
queue
because
remotely
I'm
not
sure
that
you
will
see
what
the
people
are
standing
in
the
mic.
So
then
you
need
to
get
somebody
present
to
understand
what
to
do
it
anyway,
right
we
have
about
maximum
20
people
removed
and
in
in
the
room.
A
F
Yeah,
just
to
mention
that
I
attended
this
training
yesterday
as
part
of
the
working
group,
so
I
can
feed
you
in
if
you
want
either
an
hour
or
later,
and
there
are
test
sessions
that
you
can
program.
So
you
can
rehearse
ahead
of
time
that
do
not
generate
an
interim
meeting.
It's
just
a
training
session
purely
on
the
mythical
truth,
but
yeah!
That's
it.
If
you
have
questions.
A
It's
very
nice
dominic.
We
will
be
managing
the
documents
etc,
all
right.
So
all
the
piece
of
the
training,
which
is
how
do
you
upload
the
documents
from
data
tracker?
How
do
you
make
them
available
or
to
to
the
people,
etc,
etc?
All
this
we
can
take
care
of,
and
if
there
are
people
in
the
room
who
present-
and
they
do
next
lightning
slide,
we
can.
We
can
do
that
as
well
from
from
here
so
yeah,
I
would
say.
F
The
one
who
sits
in
the
room
is
to
remind
people
who
enter
the
room
physically
to
turn
their
mythical
light
client
on
the
phone
or
computer,
so
that
they
are
registered
in
the
blue
sheet.
Otherwise,
if
somebody
comes
in
and
does
not
start
the
mythical
session,
then
they're
not
registered,
that's
the
only
real
thing
to
do
if
they.
F
A
A
I
don't
know
if
the
meeting
will
take
place-
okay,
so
anyway
blah
blah.
So
we
we
have
a
call
for
presentation
ongoing
and
I
have
to
publish
the
early
agenda
by
tomorrow
and
basically,
the
meeting
the
agenda
is
final,
so
we'll
be
missing
a
meeting
virtually
or
physically
for
those
meeting
physically
it's
going
to
be
on
tuesday
at
2,
00
pm
final
time,
which
is
also
your
cut
time
at
this
time.
A
So
it's
the
first
afternoon
session
it's
going
to
be
in
room
grant
park,
hall,
2.
and
and
basically
the
request
I've
received
so
far.
I've
I've
received
a
request
for
honor
for
mbiot,
and
I
you
did
not
specify
time
but,
like
I
said,
I
expect
20
minutes,
because
we
want
to
to
discuss
the
the
capability
to
for
adoption
and
and
maybe
carless
will
present
his
review
comments.
A
G
A
A
A
A
C
A
A
A
A
A
A
So
so
I
will
be
your
your
shepherd
lauren.
So
you
better.
It's
a
pleasure,
be
a
good,
a
good
good
guy.
Okay,
so
that's
that's
it
for
the
one
good!
Let's
go!
So
what
about
this
dave
and
aft
discussion?
That
was
very
heated
last
week
and
I'd
like
to
to
continue
so
everybody
remembers
the
context
or
do
we
want
to
to
real
just
remain
the
context.
Can
I
say
you
want
to
remind
the
context
just
a
little
bit
just
to
make
sure
that
people
have
the
private
mind.
D
D
D
D
Okay,
because
in
fact
the
the
rules
for
compression
and
decompression
are
expressed
in
terms
of
dev
and
up
so
here
we
have
a
sort
of
mismatch
and
well
based
on
the
feedback
that
has
been
received.
So
far.
It
seems
like
there
is
a
preference
for
trying
to
keep
the
app
and
dev
roles
as
they
have
been
defined,
trying
to
reuse
to
the
extent
possible
the
existing
chic
functionality
and
that
there
could
be
like
alternatives
like
defining
new
roles
or
something
like
that.
D
But
perhaps
that
deviates
from
chic
as
it
is
too
much
and
well,
then
I
didn't
receive
more
feedback.
One
point
is
that
perhaps
the
the
notes
that
would
communicate
in
this
sort
of
peer-to-peer
mesh
network
might
need
to
know
which
is
their
role,
whether
they
are
developer
app,
perhaps
for
each
possible
endpoint.
D
Several
hops,
apart
in
in
route
over,
I
understand
that
intermediate
nodes
would
need
also
to
be
able
to
decompress
packet
headers,
and
then
there
could
be
a
problem
because
yeah,
maybe
these
intermediate
nodes,
might
need
to
know
as
well,
which
are
the
the
rules
that
are
being
used
by
say
any
pair
of
endpoints
and
even
the
the
roles
as
well
within
those
rules
so
yeah.
This
is
like
some
additional
topic
that
wasn't
brought
up
before,
but
yeah.
F
F
D
Yeah,
so
actually
that
was
like
our
initial
idea
and
in
in
the
draft,
which
is
a
sixth
low.
Well,
it's
intended
for
civil
law,
which
aims
to
use
chic
for
15.4
for
heavy
compression.
That
was
sort
of
like
the
the
initial
attempt
that
we
had
in
zero
one.
However,
then,
the
feedback
that
was
received
from
the
lp1
working
group
in
this
interim
also
on
the
list
seemed
like
to
to
prefer
sticking
to
to
dev
and
up
and
not
defining
source
and
destination
so
yeah.
D
I
I
also
was
like
initially
as
the
first
attempt,
perhaps
the
the
straightforward
solution
to
to
define
something
like
source
and
destination.
Then
it's
true
also
that
using
devon
up
in
principle,
at
least
in
the
lp1
scenario,
has
the
advantage
of
allowing
a
rule
to
be
used
in
both
directions,
whereas
with
source
and
destination,
we
might
need
to
duplicate
the
rules.
However
yeah
I
don't
know,
if
maybe
there
are
like
other
effects
to
be
considered
if
we
still
try
to
stick
to
devon
up
in
the
mesh
peer-to-peer
scenario.
A
A
A
A
A
E
E
So
here
we
break
the
the
symmetry
by
by
this
information
and
to
get
the
device
id
something
very
important,
because
there
is
a
core
part
of
chic.
This
way
knows
where
to
send
the
information,
so
it
can
be
wi
or
it
can
be
in.
What
we
are
doing
right
now
in
in
open
cheek
with
ivan,
is
that
we
use
a
udp
tunnel
and
udp
tunnel
is
something
that
could
be
quite
close
to
something
that
is
mesh.
H
Then
there
is,
there
is
another
question
I
mean
when
we
talk
about
mesh
networks,
so
on
the
first
hub,
of
course
the
sender
is
so.
If
we,
if
we
have
route
over,
then
the
second
hub
doesn't
have
any
more
the
the
mac,
the
death
ui
information
from
the
sender
from
the
initial
sender
right,
so
basically,
either
we
have
shape.
That
is
on
the
link
and
directly
on
the
link,
in
which
case
the
death.
You
are
like
death
and
up
makes
sense,
but
if
we're
somewhere
in
the
middle,
then
you
know
it's
it's.
A
Two
ways
of
looking
at
this:
the
first
one
look
at
it
from
the
perspective
of
each
hub
and
say
that
if
you
compress
the
ipad
on
my
heart
and
decompress
it
but
keep
the
amplitude
per
layer
compressed,
then
you
can
forward
the
packet,
the
multiplayer
up
and
just
decompress
the
ip.
That's
one
way
of
saying
it.
You
don't
compress
the
ap
or
you
just
compress
and
decompress
the
lp,
but
you
leave
the
rest
compressed.
A
So
so
same
thing
you
can
say:
if
you're
doing
in
round
over
you
can
say
either
I
don't
compress
ip
or
I
compress
ip
but
separately
from
from
the
upper
layer.
So
the
operator
packet
can
can
stay
compressed
without
the
compression
at
the
rear.
If,
if
you
do
it
on
buyer
based
on
ip,
then
this
prime
goes
away,
because
each
time
the
sender
becomes
it's
not
really
true.
A
A
H
Is
this
still
a
question
about
like
if
we're
on
one
link
on
one
hub,
we
can
pretty
clearly
say
well,
the
dev
is
the
sender
and
app.
Is
the
receiver
they're
on
one
hop
right
and
we
can
use
both
like
we
can
use
the
mac
layer
to
to
to
actually
do
the
you
know,
do
the
calculation
and
with
the
computation,
but
if
they're
not
on
hop,
then
you
cannot
use
that
notion
right.
E
H
H
H
H
H
D
Yeah
yeah,
I
agree
because
to
some
extent
an
intermediate
note
in
in
row
october,
if,
if
we
assume
we
compress
also
ip,
the
ip
addresses
then
would
need
maybe
to
know
say
all
the
rules
in
use
all
the
roles
in
use.
Who
is
that
an
app
for
each
pair
of
endpoints
so
yeah?
That
was
like
increasing
complexity.
A
Yes,
I
don't
I
I
I've
been
thinking
about
it,
since
you
mentioned
it
guys,
but
I
really
don't
like
the
idea
of
trying
to
do.
Multi-Hop
and
sheik
has
always
been
defined
for
a
direct
connectivity
between
two
devices
and
you
compress
between
those
two
and
and
relaying
that
I
guess
you
know
the
might
be
thinking
it
doesn't
make
much
sense.
So
if
you
really
want
to
do
a
multi-year
network,
then
stick
to
six
lapa
4
for
ip
as
lauren
said
and
don't
try.
I
mean
that
is
just
taking
us
too
far.
A
E
D
Well,
in
that
case
I
wasn't
so
it
could
be
any.
I
was
thinking
about
the
problem
of
intermediate
nodes,
but
actually
there
was
a
hidden
problem
which
is
yeah.
Maybe
there
was
like
just
one
hop
or
maybe
there
could
be
nodes
in
between
so
this
could
be
like
an
end-to-end
multi-hop
communication,
so
yeah,
if
it's
just
one
hop
between,
say
neighboring
devices,
then
it's
easier.
D
Well,
not
necessarily
so
first,
the
idea
would
be
to
to
understand
whether
it
it's
actually
useful,
or
it
has
advantages
to
use
chic,
also,
instead
of
six
low,
six
open
header
compression
for
say
the
ipv6
addresses
and
well.
If,
if
the
conclusion
is
that
it's
better
not
to
do
it
like
it
has
more
disadvantages,
then
maybe
that's
fine
and
and
then
well.
We
can
see
whether
there's
still
value
in
maybe
using
chic
for
upper
layer
compression
on
top.
H
A
A
A
Basically,
as
long
as
you
keep
it
mesh
under
or
one
hub,
then
it
makes
sense
to
chic
compress
ip.
But
if
you
are
multi-hop,
then
my
recommendation
would
be
don't
don't
compress
ip
or
do
a
tunnel
and
to
compress
ip
inside
that
tunnel
or
labor
or
anything.
But
basically
don't
try
to
to
do
something
like
that,
because
that
there's
a
hell
of
a
list
of
complications
which
we
have
solved
in
six
slope
and
after
how
many
rfcs,
including
and
90,
it's
9
30
31
for
the
front
ones.
A
I
mean
don't
take
that
path,
because
in
sixth
open
you
can
also
always
say,
hey
you,
you
can
put
it
in
the
clear
the
ip
address.
And
here,
if
you
start
saying,
I
want
to
have
all
the
ip
addresses
in
all
the
rules
and
each
time
you
have
a
new
iep,
you
have
to
establish
your
rules
and
distribute
them
and
that
doesn't
fly.
A
So
I
don't
think
we
should
spend
too
much
time
on
multi-hop
for
now,
at
least
for
now
say
for
now
we
can
say
for
multi-up,
you
don't
compress
ip,
you
compress
the
elps,
but
and
then
later
people
can
do
more
if
they
like,
but
for
now
that
the
the
prime
is
really
the
original
problem.
They've
been
up
and
do
how
do
we
know
who
is
deaf
with
app
and
what
is
the
difference
between
the
roles
I
mean
can?
Could
we
could
we
have
dev
to
dev
communication
with
sheik
today?
A
A
A
A
A
A
F
A
A
We
are
adding
a
new
method
for
you
know
acknowledging.
So
this
is
extending
blah
blah
blah
and
if
you
want
offline,
I
can
show
you
the
the
the
myriads
document
eric
is.
Is
it
any
official
this
this
because
it's
still
a
draft
could
leave
it
currently
I
can
pronounce,
but
it's
still
a
draft
miriam.
Basically.
B
A
Because
michael
and
roll
insisted
to
do
a
challenge
which
he
did
because
I
did
not
want
to
do
it
for
me,
but
changing
every
time
we
say
we
extend
or
something
it
was
more
specific,
using
effectively
reference
to
myania's
document
to
to
explain
the
meaning
of
the
words.
So
he
says
it's
important,
maybe
for
the
he.
He
was
taking
this
implementer
position
where
he
wants
to
know
if
he
needs
to
change
his
code
or
write
new
code.
You
know-
and
so
that's
that's
where
it
becomes
useful.
B
G
A
G
A
And
if
you
can
have
a
very
small
section
which
says
we
are
extending,
so
basically
this
section
would
be
updating
rfc8724
and
just
one
sentence
which
says
we
are
extending
the
rfc
for
adding
to
add
this
new
feature,
because
when
you,
you
have
to
say
how
you
you
update
somewhere
so
switch.
It
really.
E
A
I
Yeah
regarding
that
sentence,
we
will
be
changing
it
and
saying
that
if,
if
window
number
zero
is
present,
it
should
be
in
the
she
compound
header.
In
that
case,
I
think
it's
it's
clearer
than
that
that
what
we
meant
is
that
it
should
be
on
the
header
by
saying
that
it
should
be
between
the
rule
id
and
the
save
it
so
yeah.
We
will
change
that
sentence
in
that
sense.
G
Pascal
that
the
rule
or
the
way
it
should
work,
is
that
the
lowest
number
window
should
be
in
the
header
and
then
further
windows
are
on
the
payload.
So
by
definition,
if
window
number
zero
is
present,
it
should
be
in
the
in
the
in
the
header.
So
so
I
guess
it's
kind
of
redundant
to
the
to
the
requirement
of
the
of
this
order
of
the
windows.
But
we
understand
that
that
it
was
a
little
confusing.
So
we
will
clear
the
text
so
that
it's
better
explained.
A
And
then,
when
you
did
the
diff,
you
had
this
this
sentence
here
and
you
copied
it.
It
was
on
the
original
and
it
wasn't.
It
wasn't
old
and
it
was
a
new
and
I
missed
if
there
is
one
bit,
because
it's
like
six
lines
and
they
tried
to
compare
weight
by
word
to
see
which
word
you
compa,
you
changed,
but
they
could
not
find
any.
It
was
like.
Is
there
any
change
in
that
sentence?
A
F
A
G
A
It
makes
sense,
but,
procedurally
speaking,
there
is
a
difference
between
do
that
and
and
have
it
force
it
force
a
retrofit
on
the
old
implementations
or
just
say
it's.
It
applies
to
people
implementing
this
new
rfc
right
in.
If
it's
just
something
new
which
comes
with
this,
but
you
don't
expect
it
in
all
implementations,
then
it's
it's
really
extends.
A
A
So
maybe
it's
a
bug
right.
Maybe
we
should
have
made
it
in
the
original
spec
and
that's
exactly
why
I'm
saying
if,
if
you
want
it
retrofitted,
even
if
you
want
this
made
to
apply
to
8724
without
compound,
so
it
may
return
a
knack
for
the
missing
fragment
without
compound
right.
If
you
expect
that,
then
you
need
to
specify
it
to
have
some
words
on
on
the
updates
section
that
I
discussed
and
then
basically
you
also
allow
an
old
implementation
to
send
a
knack.
A
A
F
F
A
A
So
please
write
it
in
in
this
new
section
which
says
what
you
update.
You
say
we
are
clarifying
that
there
could
be
a
a
knack
for
the
missing
fragment.
Even
if
it's
not
compiled
okay,
you
see
what
I
mean.
We
are
clarifying
that
it
can
be
done,
which
was
missing
in
the
original
text,
but
that's
the
problem.
A
A
Okay,
okay,
so
alex.
I
guess
you
you
can
go
ahead
with
your
shepherding
and
basically
we'll
we'll
push
the
button
at
the
atf,
because
we
on
monday
the
the
window
will
reopen.
So
what
colors?
If
you
can
publish
on
monday
and
then
we'll
push
the
button,
and
we
will
announce
that
we
push
the
button
at
the
meeting.
A
A
A
Okay
and
now
with
this,
we
have
to
adjourn
so
not
much
time
for
ub,
but
thank
you
very
much
all
for
for
attending
and
for
this
discussion
so
laura.
If
you
don't
mind
post
something
to
the
list
about
how
different
the
role
of
app
and
dev
are.
Yes,
you
could
have
dave
to
death.
What
that
would
mean,
or
up
to
up.
I
don't
mind.
