►
From YouTube: IETF-CBOR-20211006-1400
Description
CBOR meeting session at IETF
2021/10/06 1400
https://datatracker.ietf.org/meeting//proceedings/
A
A
A
A
C
C
C
So
I
think
I
just
put
them
in
the
order
of
lowest
of
low
hanging
fruit
first,
so
you
can
see
in
this
example,
we
have
upper
and
lower
case.
We
have,
you
know,
attempts
to
spell
cute
things
in
the
words
in
the
hex
content
and
I
think
the
workings
needs
to
say
whether
we
think
we
should
put
them
in
upper
or
lower
case
and
whether
or
not
we
should
avoid
any
of
these
kind
of
wordy
things
there.
I
think
we
should.
We
should
have
a
consistent.
A
C
Okay,
so
I'm
going
to
do
that,
I
will
make
it
all
lowercase,
and
that
was
the
easiest
one.
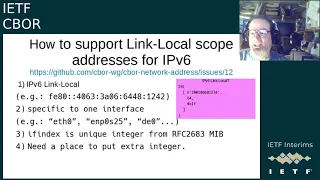
How
are
we
gonna?
Do
ipv6
link
local
addresses,
so
we
had
so
what
are
they?
I
guess
probably
most
people
here
know
this,
but
I'll
say
this
anyway.
They
typically
start
with
fe
80,
a
bunch
of
zeros
and
then
a
64-bit
iid,
which
is
sometimes
derived
from
a
layer
two
address
and
they're
specific
to
one
interface.
C
If
we
could
find
a
place
to
put
one
extra
integer
so
a
way
that
I
can
think
is,
we
could
recognize
that
this
is
most
cases
is
probably
relating
to
a
bit
to
an
interface
address,
even
if
it
we're
just
specifying
something,
and
so
the
idea
was
that
we
would
add
an
additional
integer
to
the
end
of
an
interface
address
and,
if
necessary,
you.
You
know
not
really
talking
about
an
interface
address,
we
could
talk,
we
would
set
the
64
to
128.
C
C
A
D
Okay,
having
a
three
entry
array
where
the
the
first
entry
is,
is
the
the
actual
byte
string.
The
second
entry
is
either
the
net
mask
or
it's
null
or
false
or
whatever.
If
no
net
mask
is,
is
intended
and
the
third
one
would
be
the
the
zone
identifier.
That
would
be
the
most
general
thing
to
do
where
zone
identifier
can
be
an
integer
or
a
text
string.
D
So
there
is
already
a
way
to
to
send
all
this
information
in
yang,
obviously,
so
this
is
a
different
way
to
to
send
the
same
information
which
is
fine
and
yes,
I've,
seen
systems
where
I
needed
to
use
the
zone
id.
It's
still
kind
of
a
special
case,
but
I
think
using
this
this
triple
with
with
nulls
or
false,
we
can
avoid
really
becoming
a
ton
of
different
cases.
C
I
like
false,
if
there's
no
net
mask
and
and
do
we
just
we're
just
extending
that
array
by
one
item,
it's
either
there
or
it's
not.
What
does
it
mean
if
it's
not
a
link
local
address
and
there's
a
scope
id?
I
think
the
answer
is,
I
don't
know
it.
You
know
it's
actually
valid
to
do
that
in
a
socket
bind
call,
but
sometimes
it's
meaningless.
C
C
C
D
C
D
C
Okay,
so
we
need
to
specify
more
clearly
what
is
invalid.
Then
it's
invalid,
if
the,
if
the
in,
for
instance,
on
a
for
instance
in
an
in
a
an
ip
addresses,
always
has
to
be
128
or
32,
and
we've
said
that
trailing
zeros
are
okay
for
the
subnet,
so
those
va
lengths
could
be
different
but
and
we've
said,
the
interface
definition
is
always
128.,
so
the
only
cases
are
what,
if
it's,
not
what
not
128
bits,
then
it's
invalid
or
if
it's
not
0
to.
E
D
C
D
There
is
this
document,
if
you
haven't
seen
it,
which
contains
all
kinds
of
ancient
and
and
arcane
knowledge
about
ieee
defined
identifiers
used
in
the
idf
context,
it's
a
little
bit
like
like
a
book.
You
would
check
out
from
the
hogwarts
library
I
mean
it's
really
all
very
ancient
and
and
stuff
you,
you
don't
normally
come
into
contact
with.
So
I
think
defining
a
sibo
tag
for
for
mac
addresses
in
in
that
document
would
be
the
right
way
because
we
have
all
the
context.
D
So
we
we
know
what
what
kinds
of
mac
addresses
we
talked
about
and
so
on.
The
only
little
problem
might
be
that
this
document
is
informational,
and
so
the
tech
definition
would
be
informational
and
any
standards
document
that
that
does
a
normative
reference
to
that
tag
would
need
a
downright,
but
I
think
that
that's
a
manageable.
C
C
B
C
C
B
C
A
F
I
wanted
to
point
out
that
in
the
email,
if
you
haven't
seen
it
today,
is
a
comment
last
night
from
brian
carpenter
in
the
thread
about
link
local
and
scope
with
eric
and
others
that
says
about
the
interface
index
that
unfortunately,
it's
actually
possible
to
change
the
interface
id
in
linux
and
it's
actually
true
in
other
unix-like
systems,
so
mac,
os
and
elsewhere,
which
breaks
the
mapping
between
if
index
and,
if
name-
and
I
don't
know
if
that
matters.
But
I
suggest
you
may
want
to
look
at
that.
Come
and
respond.
C
C
D
D
Okay,
so
this
this
is
essentially
the
content
that
we
should
be
discussing.
We
just
don't
know
where
that
content
will
go.
I
just
wrote
a
single
draft
so
for
for
a
while,
we
can
can
discuss
it
in
one
piece,
but
of
course
this.
This
has
dependencies
on
on
things.
That
really
would
probably
suggest
moving
some
of
this
to
the
place
where
the
dependency
is.
D
So
the
the
four
names
that
are
that
are
taken
are
described
as
reserved
here,
because
they
are
really
just
by
strings
and
the
the
other
two
are
the
ones
that
this
document
defines
mostly
to
have
an
example
and
yeah.
That
would
be
an
iana
registry.
I
seem
to
remember.
Informational
documents
can
have
inner
registries,
but
I
I
never
remember
the
details
of
that
and
it's
not
written
up
in
a
place
where
I
would
find
it.
D
So
81
26
is
mute
about
that
which
kind
of
sounds
like
if
it's
not
forbidden,
it
should
be
allowed,
but
it's
nicer
if
you
actually
know
it's
allowed,
so
we
need
to
define
the
policy,
which
is
probably
some
specification
required
thing,
or
maybe
not,
let's
discuss
this
later
and
the
the
actual
detail
template.
But
I
think
this
is
pretty
straightforward.
D
D
There
is
one
ugly
thing
here
or
maybe
interesting
thing
depending
on
what
your
perspective
is.
The
the
href
document
defines
a
conversion
from
cri
to
ui,
but
not
from
uri
to
ci.
So
theoretically
that
is
ambiguous.
There
might
be
more
than
one
ci
that
can
be
converted
to
the
same
ui
yeah.
I
don't
have
an
example
for
that,
but
there
are
so.
There
is
some
cautionary
text
here.
That
implementations
should
favor
the
simplest
variant
available.
I
mean
you
could
you
could
instead
of
-4,
you
could
write
a
string
containing
https
here.
D
So
this
is
trivially
true,
but
it's
also
trivial.
What
the
right
answer
is,
but
there
may
be
more
complicated
cases
where
we
don't
have
a
100
percent,
unique
mapping
and
that's
new
because
so
far
diagnostic
notation
always
gave
you
exactly
not
at
the
encoding
level,
but
at
the
data
model
it
will
give
you
exactly
what
you
wrote.
D
So
that's
the
cra
case
and
just
to
have
an
another
case
here.
I
took
the
dt
syntax
from
the
coral
document
and
converted
this
into
an
application
extension
identifier,
and
so
you
can
now
write
something
like
gtd,
1969
or
721
and
get
an
epoch
based
time
which,
in
this
particular
example,
is
a
negative.
D
You
will
also
note
the
absence
of
a
b
and
f,
which
is
very
unusual
for
me.
If,
if
I
have
any
text-based
information
I
usually
have
abnf,
but
in
8949
we
took
the
position
that
this
is
not
an
interchange
format,
so
we
shouldn't
try
to
define
it
using
the
same
mechanisms
we
use
for
interchange
forms
yeah.
So
if
this
is
your
comment,
where's
the
abn
f,
here's
your
answer.
That
doesn't
mean
that
you
need
to
agree
with
that.
Of
course
we
can
provide
abn
for
this.
A
F
A
B
A
A
And
that
is
the
last
one
that's
scheduled,
because
then
we
are
the
wednesday
before
ietf,
so
yeah.
I
think
we're
good
on
that.
We
can
always
schedule
one
for
for
november
3rd.
If
we
need
the
extra
time
I'm
guessing
we
don't,
we
will
have
a
meeting
during
ietf
112,
so
we
should
be
good
and
then
at
that
point
we'll
schedule
them
for
post
112..
