►
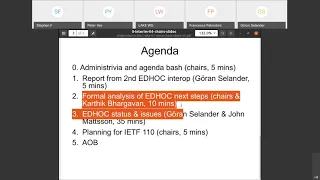
From YouTube: LAKE WG Interim Meeting, 2021-01-28
Description
LAKE WG Interim Meeting, 2021-01-28
A
A
A
Right
so
on
that
you
see
sure
names,
charter,
mailing
list,
jabber
room,
coordinates,
meeting
link
for
this
meeting
and
the
etherpad
we
have
notetakers,
garan
and
tim,
I
think,
have
agreed
to
take
notes
in
the
etherpad
thanks
for
that
we
can
keep
an
eye
on
the
jabber
room
or
ourselves
as
chairs.
I
guess-
and
we
have
the
no
well
so
this
is
the
pointers
to
various
bits
of
the
ietf
policy.
A
She
wasn't
expecting
to
be
here,
but
now
has
made
it
then
chairs,
but
ready
militia
and
karthik
will
talk
about
the
formal
analysis
and
uranus
john.
I
guess
will
run
us
through
our
open
issues
and
then
we'll
at
the
end,
just
kind
of
as
a
part
of
the
wrap-up
think
about
what
we
want
to
get
done
for
itf-110,
etc,
and
then
I
need
a
business.
A
A
Looks
fine,
okay,
good,
so
one
other
issue,
I
guess
we
should
have
put
in
the
slides.
We
didn't
if
you
in
the
webex
chat.
If
you
want
to
join
the
queue
to
grab
the
microphone,
we'll
use
the
usual
convention
or
what's
becoming
the
usual
convention.
Now
is,
if
you
type
plus
q,
if
you
want
to
join
the
mic
line
and
minuscu
to
leave,
if
whatever
you
wanted
to
ask,
has
actually
been
handled
already.
A
A
A
A
C
Thanks
this
is
the
report
from
the
second
interoperability
testing
of
edoc
next
slide.
Please.
So
we
had
our
second
session,
the
22nd
of
january
of
this
month.
This
time
we
had
three
implementations
that
were
tested
against
each
other.
Last
time
we
had
two
and
thirteen
attendees,
which
is
much
more
than
last
time,
and
I
also
collected
some
detailed
notes
and
detailed
reporting
in
at
this
at
this
link.
C
Next
slide,
please,
the
more
in
details.
We
started
by
testing
the
do
testing
based
on
the
test
vectors
on
appendix
b1,
which
is
the
one
with
signature,
authentication
x509
certificate,
so
the
method
is
zero
and
the
selected
cipher
suite
that
was
used
by
the
implementers
is
also
zero,
with
the
algorithm
mentioned
here
and
differently
from
last
time.
C
So
that
was
really
really
great
and
next
slide.
Please,
and
we
also
started
the
last
10
minutes
or
50
minutes
to
test
on
a
test
vector
for
appendix
b2,
which
is
the
one
based
on
error.
Code
indicated
with
static,
difficult
monkeys
and
the
method
is
method
number
three
and
the
same
selected,
cipher
suites.
C
C
Blight
so
yes,
I
also
wanted
to
mention.
We
had
some
implementers
that
had
implemented
older
cypher
suites,
so
michelle
veget
has
provided
additional
traces
for
method,
0
cypher
suite
5.
So
if
anybody
has
that
has
implemented
that
cypher
suite
and
that
method,
they
can
also
compare,
and
it
will
be
interesting
to
hear-
and
also
we
got
again
good
feedback
from
the
implementers
that
should
be
incorporated
into
draft,
and
we
have
also
had
more
communication
with
other
implementers
that
are
interested
in
participating.
C
D
A
That's
right,
actually
that
was
going
to
be.
My
question
was
the
discrepancy
between
3
and
13
was
a
was
a
puzzle.
So
it's
good
to
hear
and
thanks
everybody
for
doing
that.
I
I
do
have
francesca.
Can
you
talk
a
little
bit
about
just
the
the
setup
that,
where
people
in
different
time
zones,
how
did
you
get
it
to
work?
How
did
it
work
just
mostly
thinking
about
how
we,
you
know
how
we
can
improve
things
for
future
yeah.
C
C
D
All
right,
sorry,
so
yeah
I
mean
I
don't
know
if
that
was
what
you
were
asking
for,
but
basically
they
were.
They
were
pinging
between
pinging
and
then
running
co-op.
So
that
was
basically
how
the
and
that
advocate
on
top.
That
was
basically
how
it
was
set
up
and
and
and
poor
michelle.
He
was
in
canada
and
he
actually
didn't
go
got
the
round
to
test,
because
no
one
had
implemented
cypher
suite
five,
but
all
the
others
were
in
europe.
So
it
was
germany,
belgium
and
sweden.
I
think
was
testing.
A
C
A
E
So
this
is
something
that
kartik
and
his
team
plan
on
working
on
kartik.
Please
fill
me
in
if
I'm
taking
something
or
if
I
haven't
been
complete,
but
then
also
apart
from
the
protocol
itself,
we
do
want
to
ensure
that
the
implementation
that
we
produce
and
that
we
test
as
part
of
or
as
part
of
the
interrupt
testing
event
are
also
secure
and
what
that
means
is
in
to
this
end.
E
F
A
A
Open
wsn
project,
and
just
from
my
understanding,
is
that
that's
not
that's
nothing
to
do
with
india
as
an
implementer
you're,
only
being
a
tester
in
that
role.
So
this
is
indriya's
implementation
that
timothy
is
leading
okay.
So
it's
a
it's
an
in-house
implementation
and
test
great
okay,
thanks
yeah.
Somebody
else
wanted
to
talk
again.
If
you
want
to
use
the
mic
line
to
feel
free,
if
we
don't
need
it,
if
there's
only
one
or
two
people.
G
I'll
just
do
a
small
clarification
on
on
the
goals
of
this
point,
two
here
at
least
from
my
viewpoints,
and
maybe
people
can
respond
to
that
as
well.
I
think
what
would
be
nice-
and
I
think
that
we
all
agree
in
the
working
group
more
or
less,
but
it's
worth
stating
this
out
clearly
is
at
the
end
of
the
process.
G
G
G
So
that's
the
basic
idea
between
these
two
different
projects
that
malisha
just
described
and
I'm
sure
there
are
if
we
could
get
interest
from
other
groups,
there
would
be
more
things
to
do
as
well.
But
these
are,
I
think,
within
these
three,
you
would
have
a
pretty
nice
coverage
of
all
the
specs.
Anyway,
that's
my
two
cents
and
please
ask
questions
and
comments.
F
F
D
Tamarind
modeling
was
done
by
a
team
from
university
of
copenhagen,
kth
and
ericsson,
and
that
that
there
was
there
is
a
pre-print
available,
an
archive
and
they
have
I
talked
to
the
author
and
they
have
essentially
rewritten
the
paper
with
an
extended
analysis
and
that's
been
sent
to
a
conference.
It's
been
submitted
and
they
wait
for
a
response
for
that,
probably
in
march
sometime,
so
that's
the
status
of
and
that
they
actually
managed
to
cover
some
of
the
cases
which
they
didn't
cover
in
the
pre-print.
So
it's
it's
fairly
comprehensible.
D
G
No
that
I
didn't
have
much
else
to
add
to
that
the
so
the
tamarind
analysis.
Yes,
as
one
says,
it
has
already
been
done
or
is
in
the
process
of
publication,
but
it's
done
by
a
different
group.
We
are
proposing
to
do
a
computational
cryptographic
proof
using
crypto
verif,
which
is
a
tool
which
I
can
send
a
link
around
to
later.
Fdp
on
ether
pad
and
the
verified
implementation
will
be
done
using
f
star,
which
is
a
third
tool
which
focuses
on
verifying
code
or
interoperable
reference
code
in
c.
G
H
G
That's
great
so
there's
one
question
that
still
comes
up
when
we
are
doing
this
kind
of
analysis,
which
is
in
terms
of
what
is
I
mean?
Is
there
a
documented
target
security
level
for
ad
hoc?
Like
I
mean
if,
for
example,
we
if
you
wanted
to
say
that
okay
cipher
suit
0
should
provide
128
bit,
security
2
should
provide
80
bit
security
and
so
on.
G
Then
there
is
something
to
also
check
during
a
computational
analysis,
which
is
because
that
you
can
actually
check
the
concrete
security
bonds
and
make
sure
that
each
of
these
cypher
suits
meets
its
desired
security
level
and
currently
looks
like
I
don't
know
what
exactly
the
current
understanding
for.
I
guess
this
also
is
inherited
a
bit
from
oscore
because
we
use
short
tags
and
so
on.
So
there
must
be
some
target
security
level
that
we
are
aiming
for.
H
A
So
on
that
karthik,
I
I
think
it's
a
good
idea
to
create
a
thread
on
the
list.
With
that
discussion,
it
would
seem
to
me
that
there's
nothing
special,
particularly
about
lake.
In
that
that's,
you
know
if
we
do
reach
consensus
in
the
working
group
on
let's
say
128
for
confidentiality
and
64
for
integrity,
it's
probably
worthwhile
bringing
that
up
on
the
security
area
list
in
the
itf,
because
presumably
the
same
thing
will
apply
in
other
working
groups
that
are
concerned
about
constrained
devices.
G
A
A
H
H
H
So
main
changes
is
that
we
are
based
on
developer
feedback.
We
are
more
or
less
going
back
to
the
solution
in
zero
two,
but
completely
changing
this.
The
description
of
it.
We
it
raised
concerns
that
we
were
associated
with
the
source
cipher.
Now
we
described
it
it
as
we
using
hkdf
expand
as
an
ad
binary
additive
stream
cipher.
H
According
to
our
understanding,
this
provides
better
confidentiality
than
asctr,
which
actually
is,
is
a
permutation
that
don't
really
do
well,
but
I
have
more
details
slide
on
this
later,
so
we
have
specified
message
four
as
option
to
support
as
discussed
so
far.
We
have
not
specified
any
signaling
instead
making
key
confirmation
mandatory,
then
the
cypher
suitable
has
been
discussed
for
long
term.
Now
we
have
implemented
the
suggestion
from
stephen
from
last
meeting
that
one
and
two
should
be
implemented
by
more
non-constrained
and
more
constrained
devices
should
implement
one
of
them.
H
H
H
Then
we
have
sold.
Hopefully
the
services
issues
psk
this
the
name
is
psk
each,
but
the
issue
is
really
lightweight
forward
secrecy
that
has
now
been
implemented
in
the
ad
hoc
re-key
fs
function.
I
think
this
will
need
more
work
later
and
interaction
with
core
no
resumption
shaken
kmac
is
done.
Cyphysis
with
high
security
is
done
and
we
have
added
a
reference
to
the
co-cc
board
certificate
work.
We
have
got
done
several
requests
to
provide
test
vectors
for
seaboard
certificates
and
also
for
their
encoded
certificates,
which
will
come
later.
D
D
H
The
new
normative
it's
in
zero.
Four,
I
don't
know
it
says
that
you
should
once
episode
is
as
before,
eddisa
it's
it's
basically.
Half
of
the
comments
were
gotten
is
that
ed
dsa
is
the
way
to
go
people
like
that
they
can
use
threshold
and
they
have
no
problem
implementing
it.
The
other
half
is
saying
we
can
only
support
chart
256
with
ecdsa,
so
there
is
no
changes
to
the
cypher
suits.
The
normative
text
is
that
you
should
support
both,
but
if
you
cannot,
you
can
choose
one.
D
Yeah
rene,
please
please,
okay,
so
that
too
or
stephen,
if
you
could
flip
back
two
slides
or
three
there.
Thank
you
so
bullet
three,
that's
the
normative
text
and
the
reason
for
should,
instead
of
shall
was
that
there
was
an
input
from
michael
richardson
last
meeting
that
if
we
really
want
to
nail
down
all
the
the
mandatory
to
implement
not
only
related
to
cipher,
suites
and
and
then
we
should
make
it
in
a
separate
draft,
and
this
draft
should
only
contain
the
recommendation
yeah.
D
So
I
said
list
I,
as
you
probably
recall,
I
had
a
presentation
at
the
december
18
interim
right
and
at
the
time
and
as
I
looked
up
in
the
minutes,
it
was
also
suggested
to
to
support
that
which
I
have
not
seen
before
before
the
raffle
yet.
But
I
sent
an
email
to
the
list
about
the
best
current
practice
about
mandatory
to
implement
algorithms,
and
I
think
that
would
be
good
guidance
for
getting
to
conclusion
on
that
right.
E
D
So
what
is
your
proposal?
Rene
proposal
is
to
support
sha
256,
which
is
supported
by
most
hardware,
as
at
least
as
I
know,
as
far
as
I
know,
and
not
go
for
a
scythe
suit,
zero
and
two,
because
there's
essentially
a
zero
and
four
f,
five
twelve,
which
is
not
supported
by
lots
of
devices.
I
just
checked
it
on
a
new
github
web
page
as
well
right
so
but
john
mentioned
that
we
have
a
problem
with
the
the
community.
D
Some
of
split
time
in
two
parts
where
one
part
is,
is
targeting
eddsa
only
and
the
other
part
is
targeting
ecdsa
only,
and
how
do
we
solve
that
yeah?
So
I
I
might
have
is
that
I
have
not
seen
any
discussion
since
december
18
on
this
particular
topic
and
now
suddenly
it's
it's
marked
as
closed
where
it
bears.
D
A
E
E
H
So
here
is
encryption
of
message:
two
based
on
developer
feedback.
So
basically
we
have
the
current
zero
four
is
more
or
less
reverting
back
to
zero.
Two
technically
it's
the
same
solution,
but
the
label
is
different.
It's
key
stream
instead
of
k
and
the
description
of
how
it
works
is
quite
different,
but
technically
it's
the
same
same
the
candidate.
H
The
other
two
solution
has
been
not
been
favored
by
implementations.
It's
they
see
it
as
complicated,
so
and
01
was
not
dropped
because
it's
insecure
it
was
dropped
because
at
least
the
description
of
it
raised
comments.
I
think
the
developers
are
happy
with
this
current
solution.
As
far
as
we
have
seen,
and
that
is
to
use
hkdf
expand
as
a
binary
address
stream
cipher
that
fulfills
all
the
requirements
that
I
can
see.
H
H
It
was
pointed
out
that
carl,
that
not
all
all
app
users
might
use
an
application
protocol
at
all,
and
now
we
have
added
a
error
message
for
that
basically
replaces
sending
an
application
that
your
protocol
like
or
score,
and
you
can
use
that
if
you
use
authentication
only
or
maybe
if
you
use
only
one-way
application
protocol,
it
was
discussed
earlier
that
this
should
be
some
signaling.
That
could
then
be
in
message
one
or
message
three.
H
H
Just
a
comment:
yeah
next
slide,
then
issue
is
sure
there.
All
the
other
messages
have
accelerated.
Data
should
be
accelerated.
Data
in
message.
Four
and
yeah
open
question
adds
complexity,
but
only
for
message.
Four,
which
is
optional,
makes
it
look
like
the
other
messages,
but
so
far
nobody
has
expressed
that
they
need
this
either.
H
B
H
H
H
Then
we
have
clarified
that
the
intention
that
all
error
messages
are
fatal.
They
close
down
the
the
the
protocol,
but
also
that
they
are
not
authenticated.
So
if
you
send
them,
you
know
this
is
fatal.
If
you
receive
them,
you
you,
it
might
be
an
attacker
something.
You
should
consider
that
then.
The
other
thing
is
that
the
basically
there,
when
suit
r
suits,
are
included.
It's
meant
for
the
ad
hoc
application.
H
H
I
think
this
this
fulfills
all
the
requirements
that
the
developer
opening
this
issue
had
also
been
further
discussion,
whether
the
diagnosis
messages
would
need
to
be
standardized,
could
have
standardized
text
strings
or
you
could
have
standardized
codes,
but
there
has
not
been
a
clear
requirement
on
that.
Yet
that's
still
up
for
discussion.
I
think
the
the
text
would
still
need
some
more
guidance
on
when
to
send
the
error
message,
but
basically
the
idea
is
if
anything
goes
wrong.
It's
fatal
and
you
send
an
error
message.
I
I
I
H
D
H
H
I
think
this
needs
some
more
consideration.
I
think
the
initial
idea
of
ad
hoc
was
that
you
would
not
use
that
that
this
would
be
sold
by
the
lower
layers,
but
and
I'm
not
sure
if
there's
something
missing
or
if
the
implementation
thoughts
in
addock
is
not
aligning
with
how
people
would
like
to
implement
this.
I
think
this
needs
to
be
analyzed
and
considered
further,
and
maybe
there
will
need
some
addition
to
the
messages
or
guidance
how
to
distinguish
them.
A
H
Next
so
length
values
when
using
an
exporter.
This
was
open
one
two
weeks
ago
by
marco.
So
yes,
right
now,
when
using
ad
hoc,
the
lengths
of
the
key
and
the
salt
you
export
are
fixed.
The
length
of
the
key
is
the
key
length
of
the
aad
used,
but
all
score
is
deriving
keys
from
this
master
key,
so
this
could
potentially
be
longer
and
then
the
master
salt
is
set
to
eight
bytes.
This
could
potentially
be
shorter
if
you
have
a
longer
key
or
longer.
H
If
you
more
want
more
randomness,
it
was
compromising
a
trade-off
and
marquis
is
suggesting
that
these
number
are
made
defaults
instead
of
being
required
and
that
an
application
two
parties
can
agree
on
other
things,
and
this
would
this
would
this
would
definitely
work
would
maybe
somewhat
lower.
Interoperability
would
add
flexibility.
J
Yeah
just
to
clarify,
I
think
they
are
good
default
values
by
the
way,
but
there
are
chances
they
can
get
them
through
other
protocols,
for
instance,
a
possible
edo
oriented
profile
base
with
an
authorization
server
mediating
and
knowing
the
preferred
values
for
the
for
the
responder,
essentially
at
its
registration
time
and
then
synchronizing
the
initiator
later
on
during
the
ace
workflow
as
an
example.
But
there
can
be
many.
J
H
Okay
next
slide,
please
please
discuss
all
these
things
on
on
the
list
or
on
github.
There
are
issues
for
everything
there,
then
passing
information
to
application
is
an
issues.
The
the
current
document
says
that
if
there
is
error,
you
should
not
pass
everything
to
the
application,
but,
of
course,
in
the
case
of
an.
H
H
H
H
C
But
yeah
these
were
the
additions
that
were
done
to,
or
that
came
from
feedbacks
from
the
interrupt,
both
the
first
and
the
second
one,
and
we
have
started
doing
some
of
this.
For
example,
we
obsoleted
the
test
vectors
and
we
started
the
adding
the
th4
output
and
export
and
export
exporter
outputs
to
the
test
vectors.
But
to
to
do
the
rest
of
this,
we
we
have
to
like
regenerate
new
test
vectors
and
change
the
values.
H
H
H
D
Okay,
so
summary,
just
adding
one
word
here
is
that
the
I
mean
we
are
going
back
now
somehow
to
to
things
that
are
looks
very
much
like
version
zero,
two
of
the
draft,
so
it
should
be,
and
the
changes
we
make
are
only
changes
that
will
will
impact
test
vectors.
But
it's
so
we
haven't
really
changed
the
the
actual
protocol
in
the
in
the
large
in
the
long
time
now,
which
I
think
is
good
but
yeah
more
more
issues
pop
up
and
we
try
to
try
to
resolve
them.
D
A
A
Great
thanks
and
yes,
I
mean,
I
think
you
know
I've
encouraged
people
to
discuss
things
on
github.
I
mean
obviously
clearly
think
that
you
know
finally
evaluating
working
with
consensus
is
something
that
will
happen
based
on
drafts
on
the
list,
but
and
for
example,
with
the
cypher
suite
shoulds
and
muslims
are
we
we
might
wanna
we'll
try
and
get
that
pinned
down
on
the
list
soon.
Okay,
any
other
issues
on
these
ad
hoc
status
and
issues
are
with
fat.
Four.
A
K
A
E
D
A
A
A
A
Yep
great
okay
and
we're
trying
to
finish
in
a
couple
of
minutes.
The
other
thing
we
had
on
the
agenda
was
itf-110
again.
I
think
this
might
be
almost
a
no-up.
I
had
two
questions.
One
is
whether
the
people
implementing
are
okay
to
kind
of
coordinate
with
these
all
the
changes
that
they
expect
between
now
and
the
next
time
they
do
it
a
hackathon
event
or
something
around
itf-110
or
if
they
need
the
working
group
to
have
kind
of
a
draft
five
produced
that
they'll
implement
too.
A
A
D
A
Great,
that's!
Okay!
If
the
implementers
are
all
fine
with
that,
that's
great
just
wanted
to
check,
and
then
second
thing
I
had
for
icf110
is:
have
we
got
any
specific
goals
or
issues
that
we'd
like
to
try
and
close
off?
We
don't
need
the
answer
right
now.
We
can
do
that
on
the
mailing
list,
but
just
yeah.
