►
From YouTube: IETF-LPWAN-20220920-1400
Description
LPWAN meeting session at IETF
2022/09/20 1400
https://datatracker.ietf.org/meeting//proceedings/
A
A
A
Please
join
and
help
the
Keynotes
and
The
Usual
Suspects,
usually
Anna
and
Dominic
help,
but
Dominique
won't
be
with
us
today
or
it
will
be
partially
with
us
because
he's
attending
to
meetings
at
the
same
time,
so
I'll
be
taking
notes,
and
if
someone
can
help,
please
be
my
guest
and
help
us
and
then,
as
usual.
You
know,
you're
always
welcome
to
to
help
as
well.
C
A
B
B
A
A
So
this
is
Knight
Jeff
meeting,
so
as
you,
the
not
well
visual
apply.
So
if
you're
aware
of
any
IPR
that
was
not
disclosed
in
in
what
we'll
be
discussing
today,
please
let
us
know
our
refrain
from
mentioning
that
IPR
and
the
anti-arrassment
and
code
of
conduct
best
practices
also
apply
as
all
of
the
BCPS
listed
here.
A
A
So
agenda
for
today
so
we'll
go
through
tell
this
trivia
as
usual,
and
we
will
have
a
little
bit
on
the
Reach
Out
train
so
asking
mostly
people
to
think
about
what
the
rich
offering
items
are
or
could
be
and
and
start
discussing
on
the
mailing
list.
Then
lahron
will
tell
us
about
the
the
data
model
reviews.
So
there
are
a
good
number
of
ASG
reviews
already
on
the
data.
A
Bundle
and
Laura
has
questions
to
answer
so
so
we
will
explain
that
then
we'll
talk
about
the
NBA
iot
draft
and
I
just
submitted
a
new
version,
and
there
are
comments
from
Eric
and
also
discussion
about
the
relationship
with
5gl
on
this
well
with
3gbp
on
this
draft.
So
whether
it's
a
normative
draft
or
if
it's
just
informational,
depending
on
how
we
deal
with
3gbp,
then
we
love
the
LT1
convergence.
Research
work
by
Sergio
Sergio
would
like
to
share
with
us
some
of
his
work
and
and
results
about
converging
using
Shake.
A
A
A
At
the
line,
but
the
the
the
well
a
number
of
recent
changes
on
the
architecture
where
we
we
hinted
how
we
deal
with
the
the
device
versus
application
side,
depending
on
how
you
you,
you
start
the
shake
of
our
food
so
and
and
I
think
that
was
that's
pretty
recent
I
mean
was
is
was
that
already
six
months?
Okay,
but
what
else
would
you
like
to
discuss
about
the
architecture?
Do
we
have
more
topics
that
you
want
to
fit
in.
A
D
A
A
A
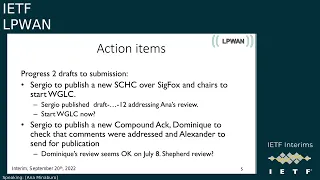
So
Sergio
has
to
publish
a
new
Shakira
seek
Fox
and
that
was
done
actually
three
of
them.
Since
we
took
the
action
item,
10,
11
and
12.,
and
so
12
addresses
the
ship
out
review
by
Anna
to
the
top.
So
it's,
why
do
I
have
start
working
quickly,
so
the
what
group,
let's
go
was
done
already
right
or
not
unconscious.
Now,
no,
it
was
not
that
and
now
please
go
ahead.
F
A
F
A
So
we
will
discuss
more
at
the
end,
but
at
least
we
have
your
point
that
when
the
draft
is
ready
for
work,
okay
and
then
there
was
the
compound
act,
that
was
to
be
a
round
trip
between
Dominic
and
Sergio,
and
that
number
of
front
trip
I've
effectively
happened.
Last
I
saw
was
Dominic,
saying
if
I
read
you
well,
we
are
in
agreement
and
I
didn't
see.
B
A
Okay,
so
we
we
know
where
the
ball
is,
and
so
we're
cool.
So
what
group
status
nothing
much
so
we
yes,
we
are
I
would
say
we
are
a
bit
late
versus
the
the
Chicago
Fox.
But
then
again
we
know
where
we
are
so
we'll
have
one
year
off
basically
and
the
Milestone
about
the
ping
and
the
way
up
that
one
we
have
not
started
work
so
we'll
have
to
Def
to
decide
probably
by
next
iitf
or
so.
If
we
keep
this
Milestone
or
if
we
drop
it.
A
And
then
the
current
work,
there
is
only
one
draft
which
is
pending
one
personal
submission.
That's
the
mesh
thing
the
whole
that
you,
you
discussed
last
time.
The
documents
that
we
have
are
well
Advanced,
so
the
architecture
is,
is
not
obsolete,
but
I
mean
I'm
cool
to
to
update
it.
So
I
was
kind
of
surprised
that
you
said
it
was,
but
no
because
we
have
a
dated
it
on
in
June
end
of
June
and
that's
that's.
When
fetv
we
discussed
this,
this
Prime
of
with
the
device
side
and
OSD
application
side.
A
For
instance,
when
you
start
a
connection
like
a
PPP
connection,
the
starter
would
be
the
device
by
definition,
something
like
that.
When
you
have
a
happens
box
situation
like
a
Bluetooth,
then
the
Hub
would
be
the
application
side.
We
kind
of
derive
it
from
from
the
environment.
Unless
there
is
some
external
signaling
compound
act
which
has
disgusted.
A
Will
present
to
us,
but
basically
we
we
have
a
review
by
Eric.
That's
we
are
in
the
ad
evaluation
right
now,
young
data
model.
We
are
going
through
the
ASG
and,
as
you
can
see,
there
are
a
number
of
of
reviews,
and
there
are,
there
is
already
one
green,
which
is
which
is
good,
and
now
we
have
to
to
write,
including
young
vectors
I.
A
Don't
know
why
it's
not
clear,
but
the
law
will
explain
and
then,
as
I
said,
we
I
would
like
to
discuss
with
chartering
so
basically
just
to
to
give
a
hint
of
where
we
are.
We
discussed
two
main
subjects.
One
of
them
is
she
cover
full
here
and
the
other
one
is
protocol
extension
and
the
one
that
stands
out
is
SEC.
So
initially
it
was
the
next
half
or
next
letter,
and
then
we
realized
that
this
doesn't
fit
in
in
here,
but
Robert
has
spotted
it
and
the
document
is
being
adopted
right
now.
A
So
so
the
next
set
of
value
is,
is
not
our
business,
but
the
fact
technique,
as
another
fragmentation
or
reliability
method
would
be
very
interesting
for
us
and
probably
that
one
is
Within
chapter
by
the
way
and
that's
it
for
this.
And
how
do
you
want
to
to
get
the
ball
and
and
share
your
slides?
Let.
A
D
So
it
are
almost
all
the
comment
has
been
done
and
you
have
a
file
now
in
repository
that
tells
you
the
status
of
all
the
commands.
So
there
is
some
that
are
not
close,
but
most
of
them
are
are
closed.
So
I
send
two
weeks
ago
a
message
on
the
walking
and
we're
working
again
and
the
mailing
list
to
get
comments
and
I
don't
get
any
answer.
So
I
will
want
to
take
the
opportunity
of
this
presentation
to
start
discussion
on
some
points
that
are
not
for
me
very
easy
to
solve.
D
So
just
to
give
you
an
update.
So
now
we
have
a
draft
17
and
a
new
Young
data
model
with
the
date
that
is
shown
on
the
on
the
slide.
So,
as
you
say,
it's
not
catastrophic.
We
we
have
a
lot
of
green
or
almost
green,
and
we
have
only
two
two
red
and
to
discuss
so
that's
what
I
would
like
to
to
do
now
is
to
discuss
what
cannot
be
solved
easily,
at
least
for
me.
So
the
first
comment
was
about
giving
some
example
at
the
end
of
the
document
in
NX.
D
D
D
C
C
D
D
Okay,
so
V
over
point,
though,
is
about
sensitive
and
sensible,
and
so
it
cost
me
already
a
bottle
of
Susan
about
about
that
and
it
it
was
not
correct
in
the
document,
but
I
I
did
it
and
now,
and
so
we
have
the
for
the
2015.
We
have
some
comment
and
now
for
draft
17.
So
there
is
a
question:
what
be
the
impact
of
attacker
reading
the
module?
D
So
that's
something
that
I
think
we
we
don't
have
to
wait
for
the
arcade
to
architecture
drive
to
to
publish
the
this
young
data
model.
Otherwise
we
will
delay
a
lot
of
things,
so
we
have
to
find
a
nuclear
Brahma
on
that
and
for
me
it's
not
very
easy
to
to
do
that.
So
if
you
have
some
idea
to
to
help
me
to
write
some
good
thing
on
the
security
point,
it
would
be
very
useful.
C
C
So,
okay-
and
there
is
nothing
wrong
to
write.
Yes,
if
you
have
read
access
to
the
rules
and
the
configuration,
then
you
can
decode
the
traffic
for
instance,
and
so
on.
Basically,
okay,
the
secretary
consideration
can
say:
if
you
have
access
to
the
channel,
everything
is
broken.
I
mean
that's,
not
nice,
but
it's
good
enough
to
approve
the
RSC
right.
What
Raman
wants
to
say
is
not
a
bulletproof
claiming
yeah.
We
fix
all
the
problem.
No,
you
need
to
provide
Roman
and
The
Others
a
list
of
depending
issue,
and
there
could
be
a
long
list.
D
D
D
C
D
So
for
me,
I
I,
don't
think
it's
really
an
implementation
issue,
because
what
we
will
have
is
just
numbers
are
identifier,
and
if
the
young,
mother
or
the
implementation
using
this
young
model
doesn't
recognize
any
Notifier,
it
will
generate
an
error.
So
it's
not
because
you
have
things
in
the
young
data
model
that
it
leads
to
to
have
an
implementation
with
with
it.
So
that's
something
or
so
we
we
have
to
to
discuss
so
originally
we
had
two
files.
D
One
was
with
the
identifier
and
the
other
was
with
the
containers
and
we
we
merge
them
and
it's
difficult,
then
to
say
which
filter
will
be
useful
or
not,
because
our
goal
also
is
to.
If
we
use
all
this,
identifier
is
2x
augment
the
the
young
data
model
and
for
example,
if
someone
wants
to
do
mqtt
compression,
then
you
will
write
his
own
things
and
this
is
out
of
horoscope.
So
for
me,
I
I
would
say
that
we
keep
it
like
this.
B
D
But
I
think
it's.
It
becomes
very
heavy
to
to
have
this.
We
have
already
two
feature:
one
is
compression
and
fragmentation
and
it
has
a
sense
because
we,
if
you
do
seek
at
the
application
layer,
you
will
not
have
fragmentation
and
if
we
look
at
the
Ericsson
document
about
how
to
send
a
long
document
in
using
fragmentation,
we
don't
have
compression.
D
B
So
I
I
understand
your
point
and
and
I
mean
this
is
the
first
time
I
see
this
type
of
reasoning
and
actually
for
me
it
makes
some
sense
to
say
well,
you
know,
I
have
a
device
and
it
supports
compression
and
it
only
supports
IPv6.
So
I
have
the
feature
compression
and
the
feature.
Ipv6
I
think
that
in
Practical
terms
it
doesn't
change
anything
because,
but
from
for
from
a
young
perspective,
maybe
it
changes
like
because
if
the
then
the
Yang
some
Yang
engine
can
automatically
determine
that
hey.
B
D
B
B
Well,
do
you
feel
strongly
about
this
features
thing,
and
if
the
reviewer
comes
back
with
yes,
I
mean
that
that
some
that's
something
that
would
really
make
it
more
clear
from
Young
perspective
than
I
mean
I
I,
I,
I
I,
see
from
a
personal
point
of
view,
there
will
be
almost
no
difference
right
and
yeah
I
I
like
it
in
some
way
like
I
like
it.
In
some
way,
you
can
say
that.
E
B
D
So
I
go
quickly,
so
here
we
have
this
something
that
is
quite
linked.
It's
that
we
don't
in
the
young
data
model.
We
don't
make
a
test
on
the
field
ID
and
say,
for
example,
if
you
have
a
feeder
field,
ID
IPv6
version
and
we
don't
allow,
for
example,
the
the
length
to
be
token
length.
So
for
me
it's
become
very
heavy
to
to
do
that
and
I'm
not
sure
what
we
when
we
augment
the
model-
and
we
say
for
example,
token
length
is
just
use
for
this
kind
of
things.
D
D
So
maybe
we
can
discuss
that
on
on
the
list,
so
we
have
a
point.
Is
yes,
we
we
talk
about
negotiation
of
the
compression
mechanism,
but
the
fragmentation
mechanism,
but
in
fact
we
we
don't
need
it,
because
we
will
not
say
our
rule
will
be
first
fragmentation
and
then
we'll
be
will
be,
will
be
equal
ways
and
then
we'll
be
at
an
error.
We
don't
do
that.
We
can
change
parameter
inside
the
rule
to
send
out
all
your
tidelines
with
that,
but
we
don't
change
the
behavior
of
the
rules.
D
D
C
Okay,
we
cannot
select
whether
it's
informative
or
normative,
whether
we
want
delay
or
not,
delay
I
think
an
architecture
is,
is
informational
right,
so
it's
very
difficult
to
put
a
normative
reference
into
the
data
model
to
something
which
is
informative
or,
like
an
architecture,
is
typically
informative,
reference,
an
architecture
document,
it's
something
that's
useful
to
read,
and
that's
it
and
I
guess
at
that
point
of
time.
That's
maybe
because
it
was
expired
right.
D
D
Koreana
I,
it's
white,
okay,
it
was
a
an
area,
is
just
the
details
that
we
have
two
choice
that
downloads
use,
but
for
me
they
are
important
just
because
if
someone
want
to
augment
noack
or
Uncle
Waze,
he
has
an
anchor
to
do
it
and
will
not
invent
his
own
representation.
So
that's
why
I
think
it's
it's
better
to
to
keep
it
in
the
model,
even
if
it's
empty
and
it
costs
nothing
in
in
term
of
representation.
A
A
F
C
A
little
more,
there
are
three
years
right,
so
two
are
basically
for
the
infrastructure
of
three
gpp,
so
we
can
be
information
not
only
there,
because
we
cannot
dictate
all
the
around
the
network,
but
on
the
application
layer.
What
you
call
end
to
end
yeah,
we
can
be
standards
there
because
3gpp
issues
as
a
transport
right.
So
we
don't
hear
what
we
are
doing
below
my
understanding
at
least
so
we
may
want
to
do.
C
Go
for
strand,
abstract
or
post
standards
and
be
very
clear
in
the
the
sections
annoying
by
five
one
and
five,
two
I
think
that
you
talk
about
using
Chic
inside
the
3gpp
network.
You
say
for
informational,
only
right
and
then,
when
you
go
to
five
four,
if
not
mistaken,
when
you
took
the
end
to
end
or
the
application
stuff,
you
say
normative
between
after
the
title
and
you
are
very
clear
there
and
you
may
want
to
play
in
a
few
things
where
you
describe
the
three
use
case.
C
C
F
F
Yeah
sorry
I
make
a
mistake.
Then:
okay,
yes,
okay,
I,
will
look.
I
will
change
the
abstract
too,
and
then
here
is
the
what
you
are
telling
and
we
have
three
uses
cases.
The
first
two
use
case
are
using
really
Chic
in
the
3gpp
architecture,
so
in
the
radio
link
and
in
the
north
success
stratum,
so
they
are
more
informative
and
then
here
the
question
is
about
the
name
or
the
title
of
the
third
user's
case
where
we
are
for
the
3gpp
network
is
transparent
and
we
are
using
cheek
over
there.
F
C
F
C
That's
my
issue
with
the
intern.
You
can
leave
it
like
this,
but
this
is
kind
of
confusing
and
it's
it's
not
really
clear.
I
mean
the
two
first
one
I
know
very
clear:
they
are
normative
right.
They
are
for
3gpp.
This
one
is
normative
for
use
by
application
or
whatever
I
think
this
will
open
to
the
working
group
to
decide
on
this
one.
Okay,.
F
F
A
F
C
C
I
was
about
to
ask:
if
there
is
anybody
working
for
Ericsson,
you
can
contact
Gonzalo
Maybe
by
some
chat
or
Internet
chat
to
see
whether
he's
ready
to
go
because
normally
we
should
go
through
him
now
if
he
does
not
reply
or
whatever.
Then
it's
up
to
the
chair
so
Pascal
and
Alexander
to
send
an
email,
putting
a
Gonzalo
in
in
CC
putting
a
statement
at
iitf.org
in
CC,
and
now
we
need
to
find
a
destination
person
in
3gpp
to
send
it.
C
F
A
A
E
A
E
In
this
case,
well,
the
problem
is
that
you
don't
have
one
iot
technology
that
fills
all
the
the
use
cases.
I
will
go
really
fast
that
that's
a
problem
mostly
for
iot
applications
and
developers
that
they
are
really
tied
up
to
L2
specifications,
mostly
because
energy
optimization,
because
of
that
we
have
also
Chic
and
IP
version
6
to
do
all
these
convergence
at
the
application
Level,
and
you
have
actually
two
options
on
how
to
to
do
these
convergence
I
mean
convergence
using
the
same
application
on
several
Networks.
E
One
option
is
to
use
cheat
cover
a
specific
lp1
as
Sig
folks,
Laura,
one
or
narrowbande
iot
in
this
case
is
depending
on
the
layer
two
or
we
can
use
a
tick
overall.
That
is
actually
independently
of
the
layer
2..
We
have
in
these
two
sides.
If
the
packets,
if
I
check
packet,
for
example,
is
sent
over
a
specific
lp1,
you
must
begin
and
end
sending
this
packet
in
that
specific
lp1.
E
In
that
sense,
as
more
technologies
have
been
implemented,
adopted
or
implemented,
they
want
to
use
cheek.
So
we
will
be
having
more
and
more
documents
of
cheek
over
specific
Technologies
and
we
will
probably
have
a
compatible
standard
that
is
incompatible
at
the
fragment
layer.
You
cannot
resemble
a
packet
if
it
comes
from
different,
lp1
Technologies,
so
with
some
applications
we
can
actually
Orient
this
to
have
the
same
header.
E
This
is
I
will
go
really
fast
in
two
minutes.
This
is
the
actual.
What
we
have
right
now
that
we
have
several
implementations
in
different
places.
The
idea
is
to
have
the
same
implementation,
so
you
can
have
the
same
to
your
assembly
fermentation
reassembly.
As
you
have
the
same
compression
decompression,
you
will
need
some
logic
to
select,
which
is
the
network
and
the
number
of
tiles
that
you
will
need,
and
you
will
probably
we
need
some
logic
to
to
obtain
the
Json
file
from
the
cheek
fragment
I.
E
Actually
compared
this
this
fermentation
modes,
the
act,
the
opling
I-
could
never
to
see
what
they
have
in
common
and
what
are
the
differences
between
the
three
of
them,
because,
obviously
we
can
use
what
we
already
have
going
going
into
these
two.
Actually,
we
see
that
they
have
a
lot
in
common
I.
I
will
move
really
fast.
You
can
see
there
that
we
have
actually
the
same
tile
size
that
there
is
a
huge
advantage
and
the
same
sides
of
the
headers,
so
we
can
actually
Define
and
check
over
Alexander.
E
D
E
Want
to
send
the
fragments
in
different
Technologies.
Actually
the
example
that
I
have
I
will
go
through.
Is
this
one
where
you
actually
fragment
the
the
packet?
Sorry
and
then
you
are
actually
able
to
to
send
it
one
fragment
in
in
each
of
the
different
Technologies
and
you
are
able
to
reassemble
the
packet
and
actually
send
an
act
in
any
network,
and
you
are
actually
sending
the
the
the
data
to
the
to
the
application.
E
Well,
this
is
good
for
multi-radio
devices,
as
you
can
have
a
single
code
base,
and
actually
you
make
a
bit
more
transparent.
What
is
the
L2
layer
and
actually
yeah?
You
can
have
some
cheek
fragmentation,
reassembly
modes
out
of
the
box,
that
you
can
use
in
other
Technologies
if
you
need
them
and
you
can
converge
a
fragmentation,
reassembly
layer
and
well.
I
also
think
this
is
possible
thanks
to
the
compound
act
that
actually
helped
control
the
the
excise
I'm.
Sorry
I
went
so
fast,
but
I
really
wanted
to
share
this
with
you
all
so.
A
E
But
now,
with
all
the
work
that
we've
been
done,
we
can
see
that
actually,
these
profiles
are
not
a
difference
in
the
fragmentation
level
in
the
fragment
header
level
and
that
we
can
actually
do
something
to
converge
them
and
actually
reduce
the
amount
of
code
in
the
device
and
actually
allow
to
transmit
you
that
you
can
transmit
in
different
networks
the
tiles
and
actually
converge
in
the
application
server
in
the
Chic
Network
server
and
reassembly.
All
the
packets.
A
A
So
you
should
just
look
at
two:
it's
a
nice
exercise,
but
us
as
we
we
reach
out
to
do
Shake
of
a
real
food
and
the
foods
will
probably
have
very
different
matte
layers
and
and
the
adaptation
of
shapes
of
sheet
are
really
to
adapt
to
the
material
constraints.
So
so
that
will
be
much
wider
than
it
is
today.
E
B
That's
actually
just
just
one
one
point
here
and
then
I
I
feel
so
long.
Coming
at
some
point
early
on
in
the
working
group
we
were
discussing
about
the
idea
of
having
a
default
rule,
it's
giving
some
kind
of
a
default
Focus
that
would
be
able
I
bet
we
can
use
for
bootstrap,
maybe
and
then
extend
with
additional
rules
eventually.
B
E
D
C
A
So,
thank
you
as
well
Sergio.
It's
really
neat
that
you,
you
started
this
DC
Fort
and
she
wanted
to
publish
it
as
a
personal
submission.
You
know
what,
where
you
are
I
mean
it's
always
interesting
and
that
that
remains
as
a
paper
that
we
can
access
so
that
that
would
be
very
interesting
with
this.
We
are
pretty.
We
are
close
to
to
the
end
of
the
hour,
so
we
were
supposed
to
discuss
a
little
bit
about
recharing.
A
F
A
Good
to
see
you
you
can,
you
can
always
I
mean.
The
point
is:
if
you
have
a
normative
reference,
then
your
document
will
go
through
review,
but
it
will
be
stuck
at
the
RFC
editor
in
the
state
where
it
is
waiting
for
the
other
document
to
be
RFC
as
well.
But
it's
only
when
you
have
a
normative
reference.
So,
for
instance,
it's
not
impacting
LOL
who
wants
to
reference
informatively
the
architecture,
but
in
this
case
it
would
be
normative
reference
to
campanak.
A
A
B
A
I'm
hearing
none
so
I.
Thank
you
all
for
your
participation
and
that
was
effectively
a
great
meeting.
I
will
all
the
little
bits
on
the
minutes
before
I
publish
them.
So
if
you
want
to
look
at
them
and
do
a
quick
edit
on
something
that
was
said,
I
will
pick
the
the
Kodi
MD
file
in
in
an
hour
or
so.
So,
please,
please,
look
at
the
the
notes
that
we
took
and
and
fix
them
if
we
did
Rock.
