►
From YouTube: IDR WG Interim Meeting, 2020-03-20
Description
IDR WG Interim Meeting, 2020-03-20
A
A
B
A
B
A
A
B
A
B
A
B
B
A
A
B
B
B
A
A
A
A
D
B
A
Okay,
folks,
it's
about
four
minutes
after
please,
everyone
who's
online,
we're
recording
this,
but
it'd
be
really
handy.
If
you'd,
please
type
your
name
into
the
blue
sheets,
that's
part
of
the
request.
We
are
under
the
note.
Well,
we
did
project
that
earlier,
but
I
will
reshow.
It
is
proceeding
as
part
of
ITF
read
the
note.
Well,
we
suspect
you've
done
it.
If
you
have
any
questions,
read
the
note
well
on
the
firm
web
page,
so
our
20/20
idea
we're
going
to
have
two
threes
and
two
thoughts
pre-assigned
this
one,
an
April
8th.
A
A
Okay,
he
must
be
on
mute.
Ok,
let's
go
right
into
the
next
thing,
which
is
the
flow
spec
discussion,
our
first
two
presentations,
the
flow
spec
and
the
outer
configuration
or
more
discussion
discussion.
So
please
folks,
I'm
going
to
start
with
the
discussion,
but
we
need
your
feedback.
The
other
design
configuration
design,
team
G
will
give
a
summarization
and
the
rest
of
the
auditor
configuration
design.
Team
will
probably
add
comments.
It's
a
discussion
moment
on
where
they
are
then
we'll
go
into
60
minutes
of
draft
presentations.
B
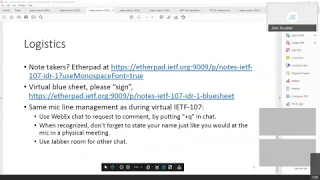
Before,
let's
just
talk
through
the
logistics
for
people
who
joined
later
didn't
view
those
yet
or
whatever,
so
if
I'm
not
sure,
if
anybody's
in
the
etherpad
yet
to
help
us
take
notes,
you
know
this
is
being
recorded,
of
course.
So
it's
and
and
there's
no
scope
for
side
chatter
that
can't
be
picked
up
on
the
recording,
so
that's
maybe
slightly
kinder
to
the
chairs,
but
even
kinder
to
the
chairs,
and
that
would
be
if
you
help
us
produce
the
notes
in
real
time.
That
would
be
great.
Thank
you.
B
If
you
haven't
signed
the
blue
sheets,
yet
please
do
I
will
repay
snows
URLs
into
the
WebEx
chat
in
just
a
second
we're
hoping
to
use
for
my
client
the
same
protocol
that
was
used
during
the
official
IETF
one
of
those
seven
sessions,
which
is
please
put
a
plus
Q
into
the
chat
and
wait
to
be
recognized,
and
you
know
just
like
you
would
at
the
regular
mic
line.
Please
state
your
name
and
yeah.
That's
about
it.
We
have
jabber.
If
you
need
to
do
other
side,
chat
and
I
had
one
other
slide
sue
with.
B
A
A
A
We
decided
to
do
a
quick,
5575
bits
that
didn't
turn
out
so
quick
and
we
have
a
good
there's,
a
kickoff
for
an
informed
call
for
presentations
on
April
8th
for
the
next
IDR
session,
I'm
gonna
sort
of
walk
through
what
we've
done
where
we're
going,
and
then
we
need
some
discussions,
so
we'd
set
requirement
last
question:
this
presentation
is:
do
we
need
other
discussions?
Do
we
need
to
have
before
we
get
there?
An
ID
are
a
large
community
discussion
case.
A
Review
you
should
remember
that
we
had
the
lri
we
had
v6
coming
in
no
user
base
filters
and
we
thought
about
security.
Okay,
and
could
it
be
lessened
within
this
single
draft
that
went
back
all
the
way
to
2016
here's
our
standard
flow
spec
policy?
It's
a
full
list,
followed
by
the
rule
followed
by
match
filters
followed
by
modifying
forward
that
should
have
been
mom
and
apple
pie.
A
The
RFC
5575
disposes
fix
the
lri,
replacing
the
encoding,
the
opaque
key
with
an
encoding
Devine
new
comparison,
bits
and
matches
had
traffic,
filtering
extensions
and
added
traffic
rate
security
section
was
updated,
but
that
didn't
change
anything
except
the
words
and
warnings.
You
have
a
draft
IDR
flowspec
v6,
which
we've
need
for
the
isg
to
consider
5575
bits,
or
they
strongly
recommended
they'd
like
to
see
it.
But
we've
had
no
working
group
last
call
comments
or.
A
A
A
Besides
begging
and
pleading
that
I
need
some
comments
on
the
v6
spec?
Here's
the
mature
specifications
and
here's
part
of
what
I
need
to
hear
from
the
operators
notice
back
in
2016,
the
draft
ID
our
BGP
flowspec,
oh
I,
D
was
there
because
it
allowed
a
a
SS
such
as
a
TPS
one
usage.
Do
you
centralize
flowspec
filtering
without
making
the
full
spec
filtering
go
through
a
sink
through
the
box.
A
Why
can't
I
have
this
pushed
onto
5575
this
and
the
list
seems
to
say
too
many
broken
things
so
I'd
like
to
dig
that
one
up
the
second
one
is:
there
are
several
additions
to
the
flow
spec,
either
adding
tunnel
filters
for
full,
spec
and
vo
through
adding
l2
VPN
filters
or
extending
the
RT
consideration
for
a
group
identifier
for
interfaces
or
having
the
path
redirect.
Most
of
these
have
either
gone
through
some
implementation
or
implementation
and
deployment.
So
we've
got
to
sort
of
say
what
are
we
gonna
do
with
this?
A
If
are
we
gonna
go
on
to
flowspec
ng
next
generation
was
the
next
lightest
thing
I
could
say:
are
we
going
to
pick
some
of
these
and
say?
Oh
no
to
our
ad?
These
must
go
in
unless
adopted,
but
less
mature
are
flowspec
match
for
MPLS
and
label
that
seemed
to
be
hot
and
then
maybe
with
us
MPLS
SR,
it
became
less
there's
an
adoption
request
for
draft
lis,
IDR
flows
back
and
a
couple
more
in
the
turning
situations.
A
A
That
was
what
I
had
originally
proposed
and
I'm
going
to
come
back
to
my
questions,
to
use
some
sort
of
sub
T
of
these
ordering,
because
that's
what's
really
there's
no
ordering
or
sequencing
of
the
filters
it's
all
of
them
were
turned
on,
and
that's
what
you
put
in.
If
you
wanted
to
have
some
ordering
to
say
this
is
the
priority.
First,
then
this
is
the
second
or
some
sort
of
waiting.
A
You
need
a
new
some
sort
of
TLV
with
some
sort
of
length
with
something
there
to
make
sure
we
know
what's
happening
and
one
way
to
put
it
was
to
put
a
new
action
atom
for
wide
communities
and
put
some
things
in
notice.
There
are
some
people
using
wide
communities.
Another
option
is
putting
the
atom
directly
in
white
communities
using
that
is
the
only
one
putting
a
source
number
a
s
and
a
list
of
atoms.
Those
are
all
things
that
we've
talked
about
in
the
past.
A
A
A
B
H
Yep
so,
unfortunately,
you're
barreling
through
a
whole
bunch
of
interrelated
topics,
so
that's
making
it
difficult
to
respond
to
them
individually,
you're
sort
of
hitting
at
the
beginning
of
your
slide.
Deck
really
is
where
we're
at
where
we
have
some
number
of
things
and
richer
so
like
5575.
This
is
about
the
pop.
That's
great
piece:
flowspec
v6,
basically
is
do
55,
75
and
v6,
so
that
should
be
easy.
Oh
ids
well
deployed
that
should
be
easy,
etc.
So
a
lot
of
these
things
are
just
simply
cleaning
up
stuff
that
has
some
level
of
implementation.
H
The
related
point,
unfortunately,
is
once
we
get
past
anything
that
involves
changing
the
NLRA.
The
actions
are
one
thing,
but
changing
the
NLRA.
One
of
the
things
that
is,
you
know,
became
very
apparent,
as
we
were
doing.
The
5575.
This
stuff
is
that
implementations
are
intolerant
of
no
the
original
specification
of
so
called
opaque
stuff,
mostly
because
the
TLV
format
not
actually
support
type
lengths
in
each
of
the
cases
which
made
it
impossible
for
us.
The
purse
things
that
we
didn't
understand.
H
If
you
would
move
to
your
slide
and
covering
the
flowspec
fees
to
stuff
or
gee,
it's
not
so
much
that
people
are
looking
for
the
sub
tlvs
to
actually
have
precedence,
order.
The
issue
that
people
have
since
closed.
It's
just
like
the
the
issue
is
that
since
flowspec
represents
firewall
rules
and
firewall
rules
are
groupings
of
no
apply
the
set
of
thing
in
this
order.
It's
less
that
an
individual
sub
TLV
which
matches
the
component
type
as
a
precedence.
H
H
C
H
Have
some
things
that
probably
can
be
done,
you
know
quite
easily
just
simply
by
doing
a
flowspec
v2
that
allows
for
strict,
no
TLV
definitions
of
the
N
or
I
know
that
that's
I
think
the
core
basis
that
we
need
to
proceed
through
these
I-55.
Something
like
this.
If
we
allow
for
rural
ordering
I
think
there's
going
to
be
interesting
debate
on
there
and
that's
gonna
be
a
tricky
thing
and
I
think.
H
The
final
item
that
will
be
somewhat
tricky
is
the
incremental
deployment
considerations,
one
of
the
things
that
sort
of
became
apparent
across
the
full
set
of
future
recommendations
that
we
have
is
once
we
start
getting
into
things
that
start
crossing
boundaries.
So,
for
example,
there
is
a
proposal
allowed
for
the
FIB
to
take
programming
from
flowspec.
H
At
the
same
time
as
the
firewall
rule
state
programming,
you
start
crossing
how
we're
ordering
can
actually
happen
and
in
some
of
those
cases
the
the
fix
for
it
may
be,
keep
the
same
encoding
but
potentially
different
a
fees
a
fee.
So
I
think
that's
the
three
broad
set
of
things.
The
rest
of
it
is
just
mostly
I
think
squishing
things
down
in
the
same
map
and
then
the
last
bits
of
fallout
as
you're
having
on
your
slides
is
for
our
various
actions.
A
A
H
H
The
motivation
I
believe
Christoph
cited
was
that
this
is
a
list
document
and
therefore
we're
cleaning
up
things
that
are
erroneous
out
of
it,
rather
than
trying
to
pull
in
different
proposals.
That
said,
every
flowspec
that
I'm
familiar
with
does
the
OID
things,
because
it's
the
necessary
work
to
originate
this
stuff
in
the
reflector.
H
A
H
B
B
Is
John,
with
my
co-chair,
had
on
just
just
to
remind
everybody
this
that
was
kind
of
the
plan
from
the
get-go
was.
You
know,
unfortunately,
sort
of
best
laid
plans
of
mice
and
men,
but
the
idea
was
to
get
the
the
best
out
quote
fast,
unquote,
so
that
we
could
then
turn
around
and
do
any
protocol
changes
in
v2,
which
was
itself
not
intended
to
be.
You
know
massive
new
protocol.
It
was
intended
to
be.
Let's
now
take
the
you
know,
any
non
backward
compatible
changes.
We
need
to
make
and
roll
them
in
okay,.
A
A
B
A
A
A
H
A
A
H
H
What
we
figured
out
over
the
course
of
the
development
work
is
that,
unlike
most
match
criteria
that
we
have
in
flowspec,
despite
the
fact
that
this
is
effectively
a
match
criteria,
this
is
a
match
criteria
that
may
actually
need
to
change
or
even
be
deleted
when
you
cross
various
boundaries.
So
as
an
example,
interface
scoping
means
something
at
a
given
domain.
This
is
one
of
the
usual
BGP
problems
of
you.
Don't
really
have
good
name
spacing
on
some
of
our
elements.
Oh,
if
you
know
s
who
you
know
it
has
your
face.
H
Id
scoped
is
100
mean
customers.
Once
you
leave
a
s
100,
it
stops
meaning
that
so
that's
a
case
where,
when
it
crosses
in
ASPR,
it
may
actually
make
sense
to
delete
that.
However,
if
it
was
encoded
and
all
right,
we
have
sort
of
long
standing
windows,
wisdom
that
changing
an
allure,
I
and
hot
by
hot
bases
can
be
dangerous,
because
you
could
end
up
with
sort
of
like
packet
copy
machines
where
things
are
just
sort
of
constantly
changing
back
and
forth
in
metastable
fashion.
H
H
Within
a
single
management
domain,
which
could
be
Confederations
a
single,
a
s
span
of
asses
under
a
single
entity,
it
should
be
fine.
This
operative,
word
being
should
be,
should
be,
and
it's
in
exactly
the
same.
Space
of
should
be
as
a
l3
VPN
operator
needing
be
careful
about
not
overloading
to
any
route
targets
into
a.
A
A
H
H
A
A
Okay,
we'll
take
private
comments.
That
would
be
fine.
The
chairs
are
really
trying
to
figure
out
where
we
draw
the
line.
What
I've
heard
right
now
is
flowspec
interface
and
flowspec.
Oh
I
D,
with
full
spec.
Oh
I,
D,
coming
as
fast
as
humanly
possible,
I
believe
the
OID
Jim
has
been
reviewed
by
Christoph.
It's
been
reviewed
by
me,
we'll
we'll
work
on
that.
A
A
A
H
You
Jeff
so
I
want
to
say
one
thing
general
about
large
communities,
and
this
applies
to
a
lot
of
things
they're
going
around
ietf
right
now
for
reasons
some
people
didn't
agree
with.
At
the
time
the
original
authors
for
large
communities
decided
to
not
to
leave
any
distinguished
number
space
for
them.
C
H
Matter
what
we're
going
to
use
it
for
we're
at
a
point
where
people
are
going
to
want
to
start
carving
out
sort
of
like
the
equivalent
of
1997,
well-known
communities?
You
just
see
the
picket
number
and
assign
it
and
live
with
the
fact
that
the
feature
is
young
enough
that
hopefully,
some
operators
somewhere
isn't
using
that
magic.
Number.
A
I
have
what
I
have
I'm
gonna,
soon
deprecated
a
assets
and
Confederates
as
I,
haven't
seen
anything
other
than
people
telling
the
steps
in
the
refinement.
Okay,
I've
gone
my
time
jet
on
this
may
be
a
little
long.
Jeff.
Thank
you
for
your
comments.
Anyone
else
so
I
will
be
contacting
all
the
authors
on
this.
A
The
OID
for
a
quick
status
update
the
OID
I
think
we're
pretty
good.
As
far
as
I
know,
it's
a
pretty
well
done
deal.
Do
you
want
to
you
in
any
of
the
co-authors
that
you
know
of
want
to
provide
any
feedback
on
deployment
at
the
next
night
at
the
next
IDR
meeting,
because
I
will
start
another
working
group
last
call.
I
A
B
I
would
like
to
relay
a
couple
of
comments
that
were
in
the
WebEx
chat,
just
to
make
them
part
of
the
main
conversation
here
so
Schneider
says
question:
what
does
flowspec
have
to
do
with
large
communities,
or
am
I
confused
about
the
topic
at
hand?
Jeff
Haas
replies.
Jo
people
want
to
encode
actions
in
them.
Job
ciders
very
cogently,
says.
A
J
K
G
A
A
D
D
It
so
basically,
this
is
quoted
from
trance
email
to
the
working
group.
The
purpose
of
the
design
team
is
to,
firstly,
to
identify
the
requirements
and
also
to
do
some
solution
space
review
and
which
can
be
used
to
guide
our
further
discussion
in
the
booking
group
to
produce
a
solution.
So
our
goal
is
not
to
give
a
specific
solution
from
the
design
team,
which
is
not
forbidden
from
the
chairs
nail
Mills.
D
D
Okay,
so
this
is
how
he
worked
in
the
last
two
months.
This
day
we
had
the
most
of
our
discussion
and
happened
on
the
mail
list,
and
the
people
can
check
the
mail
archives
for
the
designed
him
and
then.
In
addition,
we
also
had
one
conference
call
to
spin
up
the
discussion
and
the
meanings
can
be
found
on
the
iPad.
D
D
Okay,
the
first
same
way
speed
in
the
design
team,
mister
attending
for
the
scope,
and
we
have
agreed
to
work
on
the
data
center
case
first
and
designed
him
and
more
precessing
that
is
about
when
PGP
is
used
to
have
the
underlay,
not
in
protocol
in
the
data
center.
At
the
same
time,
we
will
also
consider
the
difference
difference
between
the
the
central
case
and
the
other
cases
like
the
web
or
XPS.
D
Okay,
so
the
most
important
thing
we
did
in
the
two
months
is
about
the
requirements.
We
want
to
identify
a
small
or
minimal
set
of
four
common
requirements
based
on
the
existing
proposals
and
case
on
the
design
team
discussion,
and
here
are
the
common
requirements
we
got.
We
can
check
really
first
days
that
we
need
a
support.
Different
address.
D
Families
like
I
can
follow
artistics
for
the
GP
session
a
second
and
we
need
to
support
those
using
the
direct
interface
address
or
the
loopback
address
for
the
recession
set
up
and
the
first
thing,
and
so
we
need
to
discover
some
necessary
information
for
the
Pearson
session
set
up
like
the
IP
address
of
the
peers.
Yes,
members,
then
we
want
to
have
some
authentication
in
their
order
for
the
recipe
or
call
a
city's
office.
D
D
This
way,
the
design
team
think
this
kind
of
capability
useful,
but
there
is
still
some
discussion
about
two
points
in
the
design
here.
The
first
is
whether
it
should
be
part
of
the
BGP
of
account
procedure,
or
it
should
be
done
in
BGP
self,
which
means
it
can
be
assist
kind
of
he
permission
may
be
exchanged
after
the
bit
of
assertion
is
established.
D
The
second
thing
is,
rather,
it
should
be
a
generic
ability
for
operators
customization
and
so
that
we
don't
need
to
if
an
army
encoding
or
anyone
IDs
right
here.
This
is
supposedly
thought
the
customer
for
poverty
or
to
customize
as
many
in
scientist
value.
Another
option
is
certainly
may
introduce
some
guidance
or
structures
to
this
kind
of
attribute.
D
D
Yeah,
so
the
in
this
page
at
the
next
one
we
released
some
pictures
suggested
in
some
existing
proposals,
but
they're
not
adopted
yet
in
from
the
design
team,
I
think
they
may
be
reviewed
later
or
some
update.
Some
of
them
can
be
considered
further.
Rather
they
will
be
added
into
the
minimal
common
set
of
requirements
or
someone
maybe
optional,
but
is
still
useful
requirements.
D
D
D
Another
thing
when
you
consider
is
about
the
message
side.
It
also
I
think
we
have
some
discussion
before
the
going
group
about
other.
If
we
have
a
some
particular
as
abuse
a
digital
message,
maybe
the
size
can
be
bigger
and
Osama
kind
of
protocols.
It
can
be
issue
whether
how
can
we
deal
with
that?
Some
extensions
also
require
some
coordination
with
other
steals.
D
A
B
D
Okay,
so
this
page,
where
he
lists
the
existing
proposals,
we
reviewed
and
discussed
in
the
design
team
and
the
four
drops
which
are
mainly
about
the
discovery
in
the
data
center.
Well,
the
last
one
is
merged
from
two
other
graphs
and
because
many
about
the
BGP
auto-discovery
in
the
one
or
XP
scenarios,
so
it
is
a
country-
is
not
listed
in
the
analysis,
income
analysis,
page
okay,
we
can
go
to
ms
one.
D
D
In
from
the
design
principle,
this
one
is
important:
we
can
see
different
drafts
of
those
different
mechanisms
either
based
on
existing
layer,
two
protocols
or
based
on
new
pursuit
and
two
protocols,
or
some
new
messages
for
PGP
or
reuse
and
US
team
digital
messages.
And
this
came
after
the
extensibility
of
this
mechanism
and
for
the
functional
functionalities.
D
D
Session
based
mechanism-
maybe
this
is
a
more
details:
I
need
to
discuss
further
in
the
group
and
photographed
issues.
There
are
some
concerns
about
its
change
to
the
BGP
mechanism
and
the
stainless
rings
introduced
the
last
one.
The
travel
graphic,
I
think
it's
English,
goddess
integrates
very
small
changes
to
the
BGP
and
the
content
in
a
distortion
is
not
quite
complete
and
the
scale
as
extensibility
is
until
they
mimic
it.
D
B
B
E
L
Ok,
so
I
want
to
know
that
the
the
second
or
the
third
way
I
mean
he
give
him
a
theory
based
on
you
deep
here
and
the
fossa.
Why
is
the
renewed
the
BGP
open
message
with
the
new
UDP
port
I
wanna
know:
what's
the
difference,
I
mean
so
that's
the
whatís.
Otherwise
do
you
the
some
of
the
existing
UDP
port?
Is
that
right.
D
D
L
D
D
Okay
for
the
next
steps
here,
so
things
we
want
to
do
in
the
for
the
next
steps.
The
first
is,
as
I
mentioned,
a
way
to
confirm
the
minimal
set
of
common
requirements
based
on
the
list
of
the
common
requirements
will
show
in
the
slides
and
a
based
on
before
the
discussion
about
the
other
requirements.
D
And
the
second
thing
is:
we
won't
through
some
consensus
on
the
design
principles
and
then
based
on
the.
If
something's,
we
probably
could
approve
this
requirements,
and
it
is
on
principle
into
one
requirement
document,
then
I
think
the
job
of
the
design
team
will
be
done
and
we
can
canvas
the
next
half
solution.
Discussion
to
the
looking
groups.
We
can
work
more
people
to
join
this
discussion
here.
D
H
H
It's
Jeff,
so
I
think
one
other
thing
that
didn't
quite
make
it
out
of
our
discussion
in
the
design
team.
That's
somewhat
relevant
were
similarly
attributes
now,
for
these
protocols
come
from,
we
we
sort
of
left
it
as
a
it
has
to
be
figured
out
and
we
have
the
design,
if
that's
an
important
thing
as
part
of
the
auto-configuration
itself.
So
as
examples
interface,
headdress
configuration
some
of
the
proposals
that
use
things
like
ipv6
link
locals,
obviously
don't
require
coordination.
H
Things
that
happen
over
some
former
global
address
would
so
that
means
that
maybe
to
interact
with
things
like
DHCP,
the
same
thing
is
true:
for
like
a
s
number
discovery
is
that
something
that
is
provisioned
or
not
and
depending
on
exactly
which
solution
space
you're
targeting
for
things
like
data
center,
those
things
can
vary
eventually,
some
of
them
end
up
being
driven
strongly.
My
provisioning.
D
M
L
D
Okay,
okay
I
see
this
is
actually.
This
recovery
is
reflected
from
the
existing
draft
in
a
3d
L,
which
is
a
more
generic
and
miri
neighbor
discovery,
just
a
one
specific
feature
of
it.
So
this
is
a
more
generic
requirement
from
this
base.
Layer,
3d
aircraft,
which
is
a
truck
Tina
storm,
attracted
all
these
recovers
from
the
relevant
drafts,
and
this
one
has
not
been
fully
discussed
in
the
design
team.
So
I
just
put
it
here,
and
maybe
it's
not
directly
relevant
to
the
PGP
out
of
this
car
discovery
requirement.
B
G
N
Wow,
well
that
made
everybody
stop
talking
just
to
clarify
the
provide
layer
to
keep
live
messages
was
you
know,
should
this
also
be
used,
configure
something
like
BMP,
because
it's
a
standard
part
of
many
people's
configs
and
as
Randy
said,
these
are
not
adopted.
Just
things.
People
are
talking
about.
D
Suggestion
I
think
for
the
encoding,
maybe
I
can
consider
a
little
later
and
the
currently
I
think
the
most
most
important
thing
is
about
that.
These
are
in
principles
once
we
reach
certain
consensus
on
this
part,
the
encoding
can
be
something
we
discuss,
how
to
efficiently
call
and
message
and
make
it
more.
Generic
I
think
this
is
some
chance.
We
can
add
further
in
there
for
polling
discussions
when
to
go.
G
G
H
O
H
H
Different
examples
are
what
transports
things
go
over
so
the
feature
for
the
LD.
Anyone
was
mostly
just
leveraging
existing
stuff.
That
is
intended
for
a
switch
context,
but
that's
not
necessarily
useful
for
contexts
that
are
outside
of
fabric
positioning,
which
is
our
key
topic
right
now.
That
said,
mostly,
our
analysis
has
been
falling
into.
What
is
useful
for
just
getting
beaten
to
come
up.
Here
are
the
core
things
that
are
necessary
to
get
the
job
done.
H
H
Such
cases
help
in
the
auto
configuration
to
prevent
the
connectivity,
it's
potentially
hopeful,
but
it's
not
a
requirement
so
I
think
there's
some
interesting
questions
around
things
that
are
potentially
helpful
for
either
miss
connectivity
checks
or
because
that
are
outside
of
fabrics
being
able
to
say
things
like
a
vise
is
trying
to
discover.
Is
this
thing
about
reflector
or
not?
There's
a
different
piece
of
work
at
CNI,
Iran
or
the
NIV.
C
B
G
Just
to
contrast,
the
Jeff's
points
well-taken,
but
the
opposite
or
not
opposite.
The
complementary
view
is
that
but
types
of
roles
in
the
number
of
roles
are
not
innumerable
they're,
really
heavily
dependent
on
what
the
operator
is
doing
and
so
a
mechanism
which
allows
our
baterry
attributes
to
be
shared
before
BGP
stokin
can
cover
that
case.
I'm
a
spine,
I'm,
a
leaf,
I'm,
vanilla,
ice-cream
right,
it's
operator,
configured
I,
think
as
protocol
designers
were
it's
too
easy
to
fall
into
the
classic.
Fender
trap
is
I,
know
better
what
the
operator
should
be
doing.
H
P
P
P
David
coughs
key
hello:
does
that
I'm
a
bit
comma
Adam,
because
camera
I
was
just
thinking
and
I'm,
like
you
suggested
it
that
there
could
be
a
BGP
extension
in
form
of
UDP
and
all
that
stuff
up
from
operators.
Point
of
view
I
would
rather
go
with
the
sort
of
separate
protocol
that
were
where
I
could
serve
clearly
define
like
hey,
I'm,
not
running
this
protocol.
In
my
edge.
Therefore,
I
could
better
secure
my
edges
as
opposed
to
have
all
these
extra
features
or
protocol
interactions
within
the
protocol.
P
C
P
D
D
B
B
D
B
Know
then
it's
okay,
but
I.
Is
it
a
reasonable
goal
for
us
to
say
that
you
know
by
by
summertime
we're
we're
ready
to
open
this?
You
know
and
publish
publish
the
requirements
that
you're
gonna
produce
and/or
the
proposed
requirements.
I
really
should
say
and
should
be
careful
about
that
and
and
put
that
back
out
to
the
working
group.
D
B
Me
suggest
that
if
you're
soliciting
input
from
the
working
group,
I
mean
it's,
it's
great,
that
you've
made
this
presentation
and
publish
these
slides,
and
it's
probably
good
to
follow
up
with
a
email
to
the
working
group
with
a
pointer
to
the
slides
at
at
least
and
it.
It
would
be
fine
to
go
ahead
and
and
create
a
working
group
dry
or
create
a
draft.
Rather-
and
you
know,
put
this
information
into
the
draft
as
well
that
that
people
can
reference
that's
optional,
but
I.
A
A
Maybe
we
could
ask
for
another
one
and
just
focus
on
what
you
want
to
know
from
the
working
group
on
the
design
principles
and
have
a
very
short
rough
draft,
as
well
as
presentation
for
that
that
way,
we
can
push
this
along
so
that,
maybe
by
summer,
when
we
like
it
to
have
a
idea
face
to
face
meeting,
we
could
have
both
the
common
requirements
and
and
some
thoughts,
straw,
men
proposal
on
the
design
principles.
Just
just
a
thought
and
I'd
be
glad
to
talk
about
that
offline
as
well.
Tea.
B
G
The
pressure
point
where
we
have
to
make
some
crux
decisions
on
what
D
and
the
information
is
now
sort
of
roughly
agreed,
but
the
transport
and
the
encoding
are
the
key
points
and
like
investigating
whether
lldp
really
will
do
whether
we
have
to
invent
something,
wonderful
and
new,
so
on
and
so
forth
and
I.
Don't
think
I
think
that's
why
you
made
a
design
team
and
having
that
for
the
whole
working
group
is
probably
not
going
to
focus
the
discussion.
B
I
do
see,
saying
in
the
chat:
I
agree
with
Randy
and
Warren,
saying
yup,
which
I
was
confused
enough
by
what
randy
said
to
not
be
exactly
sure
of
what
they're
agreeing
with
other
than
I
think
what
randy
said
is
we're
not
done
yet
and
please
don't
jiggle
our
elbows
too
much
until
we've
completed
the
task
you
set
to
set
us,
which
makes
sense
to
me.
I
do
not
want
to
jiggle
your
elbow.
We
will
schedule.
P
G
H
C
H
B
Is
exactly
what
we
hope
to
avoid
by
charter
and
the
design
team,
so
yeah
I
agree?
That's
that's!
Not
what
I
hoped
to
get
out
of
the
design
team
is
a
giant
laundry
list.
So
just
to
be
clear,
my
comments
about
you
know:
if
you
want
input
from
the
working
group,
please
focus
it
by
sending
you
know
a
list
of
questions,
sending
your
slides
and
or
sending
a
draft
to
the
mailing
list.
That's
if
you
want
input
from
the
working
group
I'm
not
saying
you
must
do
this,
make
sense.
B
B
Q
Will
now
hand
end
of
as
a
policy
a
note
will
receive
connected
as
4s
our
policy
two
different
ways,
for
example
super
configuration
through
PGP
our
policy,
so
she's,
yes,
our
policy.
So
what
is
we
can
summarize?
This
has
come,
initiate
or
refer.
Sometimes
we
may
attempt
to
initiate
or
some
kind
of
a
supportive,
some
some
even
happens
and
would
like
to
come.
Topper
or
some
senior
point.
She
will
generate
a
sauna
policy
and
policy
satisfies
some
requirement
with
the
head
end.
Q
Q
Q
Q
So
this
is
a
new
some
TV
record
requests
the
parameter
a
supporter
of
e,
so
these
are
somewhat
lve
were
campaign
requests
night,
but
for
you
to
request,
we
would
like
to
have
a
ID
to
identify
this
request.
In
addition
to
this
request,
IDs,
we
also
have
some
kind
of
parameters
indicator
the
request.
For
example,
we
may
have
a
flag
to
indicate
that
this
request
is
for
real
optimization
of
the
existing
pass.
Q
Q
Q
We
also
any
the
details
about
synchronized
socket
LV.
In
fact,
this
is
a
written
anyway.
I
have
a
spec
synchronization
actor,
so
we
just
essential
aim
to
civilization
in
Subterra
V.
So
in
this
is
synchronization.
Software
would
be,
we
add
more
informations,
because
we
want
to
synchronize
multiple
requests,
so
we
needed
to
have
those
request
IDs
for
those
multiple
requests.
As
always
wave
half
of
multiple
requests
at
ease,
then
Sergio
comforter
can
compute
a
pass
to
consider
these
requests
at
the
same
time.
So
these
are
updates
or
the
string
imagination
sake
of
peace.
Q
D
B
I
said
long
comment
in
the
chat
from
Keita
and
he's
I:
don't
need
to
get
to
a
mic.
Okay,
I
will
read
your
comment
then,
because
I
think
that
we
should
try
to
keep
it
in
one
conversation
says:
this
draft
proposes
an
extension
for
PGP
to
support
a
request
response
mechanism
for
s
our
policy.
We
know
that
BGP
does
not
natively
support
such
transaction
mechanism.
Unlike
peace
app.
Can
the
author's
please
describe
how
this
mechanism
is
supposed
to
work
and
how
such
s,
our
policies
are
going
to
be
maintained.
B
Q
For
example,
we
propose
to
use
the
distinguisher
user
FFF
and
then,
when
we
said
that
whenever
you
send
from
heaven
to
the
controller
to
make
the
request
and
that
after
a
controller
request,
you
Steve
this
request
and
then
controller
may
some
special
processing-
or
this
is
a
request.
Something
I
can
report
it
to
the
head
end.
So
this
is
one
proposal
or
what
Vicky
I
think.
Maybe
the
other
person
in
suggestions.
B
So
I'm
putting
myself
in
the
mic
lon
speaking
as
a
working
group,
member
I
just
have
sort
of
a
fundamental
question
or
concern,
which
is
I
mean.
Let
me
say
in
both
ways
the
question
is,
as
you
pointed
out,
piece
F
has
this:
why
do
we
need
to
reinvent
piece
F
and
the
concern
is
that
as
you've
just
sort
of
talked
through,
it's
not
really
a
natural
fit
for
bgp
PGP.
Has
things
like
state
compression
that
really
mess
with
the
whole
idea
of
request
protocols?
B
Q
That's
good
question,
so
a
big
piece
I
have
this
request
and
reply
protocol
stare.
So
why
do
we
need
to
do
the
same
thing
in
the
BGP?
So
this
is
that,
right
now,
if
you
see
working
as
a
controller,
so
there
can
be
that
kind
of
person
requests
on
the
replying
protocol,
so
VP,
it's
also
a
user
as
a
controller,
so
looks
like
we've
some
kind
of
requirement
to
have
this
kind
of
a
request
and
a
reply.
Q
So
that's
a
mess
of
photos.
Our
first
question
for
second
person
is
that
note:
yeah
you're
right,
the
BPA's
already
have
some
kind
of
since
there
and
we
should
endure
broken
the
PPE
award
misbehavior
too
much.
So
that's
a
four
second
person
so
much
opinions
that
sees.
We
have
four
people
since
we
have
P
key
as
a
controller
and
then
we
have
this
kind
of
requirement.
So
this
should
we
have
who
just
find
in
some
way
that's
it
to
PGP,
then
that
might
be
GPE
to
have
the
same
or
similar
functions.
Q
B
Thank
you
and
sort
of
putting
back
on
my
meeting
moderator,
hat
I'm.
Just
gonna
read
the
comments
that
were
put
into
the
chat,
so
Jeff
tensor,
says
+1
I
think
to
mine
might
comment.
Jacob
Hyde
says
I.
Also
think
PGP
is
not
a
request
response
protocol.
Why
not
use
peace,
app
Haas,
says
Morse.
More
importantly,
BGP
regularly
fails
to
be
request
response,
and
then
he
makes
an
editorial
comment
about
best
which
I
won't
repeat
kitten
says
it
is
not
just
request
reply,
but
also
need
to
maintain
the
SR
policy
through
its
entire
lifetime.
B
Ok,
right
now,
with
you
know,
sort
of
working
group,
chair
hat
on
I,
think
you
you
have
some
skepticism
to
overcome,
so
I
think
creating
that.
If,
if
you,
if
you
choose
to
proceed
forward,
I
would
I
would
encourage
you
to
fill
in
that
detail.
Thank
you
any
other
comments
for
the
mic.
Otherwise,
I
think
we
can
probably
move
on.
Q
Q
So
since
controller
is
just
a
single
point
of
failure
for
the
light
walk
we
be
bilateral
is
controlled
by
its
annual
controller.
So
in
order
to
provide
a
reliability
or
FLP
via
the
LAN
look
so
people
proposal
using
control
cluster
which
contain
our
two
controllers
and
then
an
above-normal
controllers
as
one
option
or
you
we
enhanced
in
Fenster,
reliable
controller.
So
another
is
that
we,
you
can
use
a
multiple
controllers
work
at
same
time,
so
what
options
for
controller
reliabilities?
Q
First,
we
focus
on
our
network
controller
clusters
for
this
kind
of
architectures
reliably
so
for
controller
cluster.
So
when
the
failure
happens
in
the
cluster,
they
may
split
into
different,
separate
classic
groups
complete.
So
each
each
group
will
yell
acted
themselves
as
a
primer
controller
group
and
then
control
the
network.
Q
Q
Q
Only
each
group
were
selected
to
the
selections
I
mean
they
were
selected
primary
secondary
and
adds
unnecessary,
he's
go
back
to
the
selection
and
then
me
the
intended
primarily
in
that
group
soon.
The
information
about
who
that
the
same
element
then
better
and
Edmund.
Well,
trust
me
that
those
information
to
the
other
controllers.
So
in
this
way,
even
though
we
have
multi
failures
in
the
cluster
and
the
cluster,
it's
literally
multiple
separate
group,
because
we
have
this
information
channel.
Q
Q
So
here
we
talk
about
a
cynic
information,
primary
intended
primary,
the
author
controllers
and
Mike
Redmond.
So
here
in
the
bomber
situation,
only
primary
controller,
similar
information.
The
information
will
include
the
private
controllers,
counter
position,
so
we
have
one
two,
three
four
one
means
primarily
to
means
secondary
three
minutes.
Every
episo--
on
the
card
in
the
position
of
this
is
a
controller
among
the
older
partition
with
his
controller
and
then
this
control
as
a
priority,
to
become
primary
controller.
Q
Q
So
after
failing
the
clusters,
so
we
may
have
worst
separate
control
groups.
So
each
group,
we
also
select
its
intended
control
protocol
in
22
second
controller.
So
so
only
the
intern
intended
primer
controller
in
each
group
well
Cinda
the
informations
to
the
other
controllers
through
a
battle
Egmond
and
then
after
every
controller
have
those
information.
Q
They
will
determine
correct
primary
group
so
after
the
controller
determined
that
the
primary
primary
controller
group
and
then
that
primary
controller
group
well
control
the
network,
that's
the
rough
idea,
so
even
the
case,
because
in
the
case
that
to
group
a
time
or
piece
the
primary
group,
so
we
have
also
proposed
some
kind
of
operating
rules.
For
example,
we
have
time
so
the
rule,
for
example,
let's
have
a
rule
that
the
maximum
number
of
controllers-
the
group
has
a
maximum
number
of
controllers.
Q
We
win
the
election
in
the
case
that
if
the
two
groups
have
same
number
controllers
hi
in
this
case
we
may
use
a,
we
may
use
it.
The
parameter
and
the
older
producer
number
so
evil
group
as
older
as
a
bigger
or
higher
or
a
producer
number,
and
then
they
win
that
will
prepare
to
the
the
times.
So
he
so
unique.
In
any
case,
one
only
one
primary
group
will
be
elected.
Q
Q
Q
These
are
talking
about
recovering
procedures,
so
when
a
cluster
of
failures
and
classes
ability
to
multiple
groups,
each
group
will
select,
is
a
10
in
10,
the
primary
intent
the
secondary
and
then
only
the
intend
primary
voter
submit
information,
a
lack
of
element
so
in
the
normal
case,
because
we
care
for
a
cluster
only
the
primary
controller
in
that
cluster,
we
have
seen
the
opposing
information.
So
after
failure-
and
then
you
see
me
in
10,
the
primary
controller
in
that
group
were
submitting
information
about.
Q
O
This
is
Linda.
Thank
you
very
much
for
presentation,
so
I'm
just
curious,
like
today's
many
applications
used,
they
have
many
many
instances
and
to
the
client
are
to
the
repeal
the
the
peer
they
appear
as
one.
So,
if
you
use
a
virtual
IP
address
to
represent
the
cluster
of
HP
controllers,
then
they
can
decide
among
themselves
who
will
be
in
main
control
of
synchronizing
all
the
information
but
to
the
PE,
the
BGP.
They
would
be
the
same.
There's
no
difference
from
PE
perspective
and
guess
what
here's?
Why
don't
you
use
that
way.
O
Right,
so
so
that
just
just
detach
it
from
bgp
per
se,
you
have
a
class
of
controllers.
You
may
have
synchronization
among
each
other,
but
to
the
PE
perspective
when
they
propagate
their
routes
when
they
receive
the
rounds.
It's
all
the
same
incoming
from
what
an
entity
may
be
it's
a
virtual
entity.
They
don't
really
care
which
one
send
it
to
them.
Yes,.
Q
Yes,
you're
right
is
one
entity
from
the
incident
from
you.
There
are
multiple
entities.
Yeah
we
see
the
inside.
We
may
have
macro
failures
and
then,
because
always
elevated
those
into
the
inside,
they
were
synchronized
give
where
her
failure,
the
splitter,
those
in
the
mud
when
it
is
out
of
sync
and
then
because
after
sub
elite
and
people
to
out
of
things,
they
don't
know
each
other,
then
they
will
well
you
like
themself
as
a
private
controller
and
the
Marco
entity.
Well,
you
like
themselves
controllers
I,
mean
those
private
Marco,
private
controller.
Q
O
Yes,
you
can
do
the
same
way
with
virtual
IP
to
represent
the
cluster
of
them,
say
basically
from
PE
s
perspective.
They
they
just
receive
from
this
work,
one
virtual
IP
address
to
to
the
controller,
and
if
the
cluster
fair
one
cluster
fell
or
the
other
cluster
fail,
you
can
have
a
load
balance
to
to
to
select
elect
one.
So
my
point
is
you
have
many
more
PE
s
than
the
controllers,
so
just
keep
the
PE
behavior
the
same
and
then
have
the
controllers
decide
among
themselves
to
choose
one.
Q
O
Q
R
J
I
mean
I
noticed,
you
know
we
have
some
yeah
well,
it
makes.
The
big
question
is
these:
these
clusters
are
they're,
gonna
have
to
be
talking
to
them
each
other
anyway.
Why
would
you
move?
What
would
you
just
do
this
this
high
availability
election
outside
of
it
and
put
in
BGP,
make
any
sense
to
me.
It
makes
even
less
than
it
makes
even
less
sense.
To
put
it
in
on
I
know:
I
know
you
I
know
you
get
us
all
of
them,
because
then
it
goes
to
the
whole
routing
domain.
J
It
should
go
in
in
this,
whatever
you're
doing
between
those
controllers.
You
know
we're
not
to
the
point
we're
not
to
the
point
where
you
can
just
take
controller
a
off
the
shelf
and
controller,
be
off
the
shelf
and
run
them
and
having
this
little
piece
standardized,
isn't
you
know
the
synchronization
itself
between
the
control
clusters
doesn't
make,
doesn't
make
any
sense
at
all,
from
a
requirement
standpoint
to
me.
B
Q
B
So
this
is
John
Scudder
I'm,
adding
myself
to
the
queue
as
a
meeting
participant
so
well.
Actually,
first,
as
moderator
I
will
pass
on
Tony
agenda,
saying
in
fact,
inventing
paxos
/
BGP
is
a
curious
idea
idea,
so
I
agree
with
AC
and
then
for
myself.
I
will
add
yeah.
This
is
basically
a
group
consensus
protocol
that
you're
trying
to
invent,
and
there
are
various
places
where
you
can
get
it
off
the
shelf.
You
might
want
to
take
a
look
at
zookeeper.
I
also
really
see
a
need
to
stick
it
into
BGP
and
if
comment.
P
K
About,
if
he
didn't
say
it
on
the
actual
mic,
but
I
agree
with
him,
and
that
if
there
is
any
connectivity,
if
any
PE
or
any,
can
speak
to
more
than
one
control
within,
then
those
two
controllers
can
browse
to
each
other
and
therefore
you
do
not
have
a
partition.
So
the
only
way
you
can
have
a
partition
is
all
of
the
payees
or
also.
B
B
Q
I
mentioned
that,
because
we
may
have
some
customization
make
this
more
retail
I
think
maybe
this
one
I
think
maybe
the
most
similar
example
so
for
those
kind
of
a
single
addresses
inside
and
then
some
closing
similarities
and
past.
Maybe
okay,
as
I
mentioned,
because
the
microvilli
inside
the
controller,
so
cover
for
controller,
always
have
connections
to
the
metal
element.
Q
So
DC
is
a
convention
is
the
more
persistent,
so
the
other
can
commence
in
someone
control
is
broken,
but
we
still
have
a
convention
Suleiman
and
then
we
can
use
this
passed
to
a
single
Edition
among
those
separated
controllers
right.
So
this
is
as
a
master
option
there,
and
then
this
is
the
preferred
extruder
fallibilities
to
there,
and
then
we
may
use
it.
So
this
was
the
first
single
gesture
only
that
in
tender,
my
controllers,
sender,
the
information.
So
that's
what
element
that
then
food,
the
other
controllers,
so
also
the
the
information
is
a
minimum.
A
A
S
S
Knew
vocally
define
how
the
on
path,
telemetry
techniques
can
be
applied
in
several
situation
in
particular,
we
can
mention
in
bando,
I'm
ultimate
multilateral,
also,
others
like
I
bring
to
step
so
other
techniques
that
are
investigated
in
I,
see
I'm
working
group,
for
example,
and
graph.
It
frameworks
also
allowed
the
so
called
reflection
application.
This
means
that
the
controller
on
the
controller
side,
we
can
get
telemetry
information
from
the
network
based
on
this
telemetry
information
that
we
can
get.
S
So
as
I'm
as
I
said
before,
the
idea
is
to
enable
the
on
path,
data
playing
calamity
for
our
policies,
and
this
framework
allows
the
flexibility
and,
in
particular,
address
the
deployment
challenges
for
most
its
data
play
meter.
So,
in
particular,
all
these
methods
to
be
applied
of
different
challenge
regarding
the
performance,
the
deployability,
the
flexibility.
So
this
framework
aims
to
facilitate
the
deployment
of
these
methods
in
order
to
allow
the
flow
selection,
the
dynamic
network,
probing
the
on-demand
technique,
integration
and
so
on.
S
S
Coming
back
to
the
real
scope
of
our
draft
after
this
introduction
of
in
situ
flow
information
telemetry,
the
idea
is
very
straightforward,
very
simple.
So
considering
the
SR
policy
and
cutting
structure,
we
are
going
to
define
new
sub
judice,
that
we
can
say
we
can
call
them
iFit
attributes
in
order
to
install
and
apply
to
the
candidate
our
eye
feet,
performance
measurement
technique.
For
example,
if
we
go
to
the
next
slides,
we
can
see
some
details
about
that,
for
example.
S
S
B
F
T
S
Not
all
the
types
of
not,
for
example,
alternate
marking
is
one
of
the
methodology,
that
is
by
definition,
is
about
loud
or
by
op
measurement,
and
the
same
also
for
in
man
who
I
am
for
resorption
is
also
Oh.
Bobby
depends
by
the
which
kind
of
on
pad
telemetry
we
are
going
to
activate,
and
it's
also
managed
by
the
controller
side.
So
it
is
up
to
the
controller
based
on
which
kind
of
service
and
which
kind
of
traffic
we
are
going
in.
We
would
like
to
monitor.
C
S
S
Or
by
up
measurement,
but
for
example,
if
in
case
you
don't
need
so
detailed
information,
because
the
SLA
are
not
so
important
for
that
kind
of
traffic,
you
can
just
configure
an
ant
well.
So
this
is
the
kind
of
flexibility
that
I
mean.
So
you
can
start
monitor
your
network
without
going
in
your
details
and
then,
if
a
problem
comes,
you
can
specify
better
the
flow
selection
criteria,
the
flow
selection,
the
the
most
suitable
performance
measurement
method
that
allow
you
to
get
the
important
information.
For
example,
you
can
prefer.
S
S
H
S
Why
we,
we
are
investigating
both
BGP
and
EC,
because
maybe
there
are
several
scenarios
where
we
can
use
with
whether
to
use
BGP
and
other
scenarios
where
it's
better
to
use
PC.
Yes,
so
it
is.
It
depends
well
time,
but
also
we
can
say
near
real-time,
but
also
we
can
say
flexibility
that
can
be
for
a
period
of
weeks
or
month.
It.
It
depends
by
which
scenarios
we
are
investigating,
but
I
agree
with
you.
I
P
A
O
B
B
O
Do
it
nothing,
that's
a
great
way
to
do
use
the
extended
poverty
raw
target,
but
we
would
like
to
use
a
different
name
instead
of
calling
raw
target,
which
is
same
as
VPN
just
use,
so
that
for
the
CPE,
who
only
support
the
VPN
to
have
a
different
name,
would
that
be
a
problem?
We'd
call
a
different
name,
same
purpose
as
a
broad
target.
We
call
it
s
t1
target
but
that'd
be
a
problem.
O
Thank
you,
and
also
our
second
question,
is
VP
I
write
in
a
VPN
different
instances.
Different
VPN
can
have
their
own
private
addresses
and
they
can
use
the
route
distinguisher
to
distinguish
different.
The
brows
belong
to
different
instance,
so
we
want
to
use
similar
approach
as
well,
but
I'm
just
concerned
of
using
the
Satya
128,
because
128
it
has
specific
semantics
associated
with
it.
B
O
O
O
The
thing
is
for
the
propagation
of
the
sqm
property
is
really
between
the
edge
node
to
its
controller,
and
then
controller
can
use
this
constraint
right,
argot
to
distribute
to
the
relevant
peers
right.
So
we'll
now
go
through
other
routers,
so
we
don't
have
the
issues
of
backward
compatibility
like
some
vowels
in
the
middle
doesn't
recognize
that
and
drop
it.
We
don't
have
that
issue.
U
So
Linda
so
I
don't
think
there
is
some
really
a
problem
with
different
sake.
From
the
draft
perspective
of
RFC
perspective,
the
issue
is
with
leveraging
the
implementation
right
because
using
different
Safi
now
you
either
have
single
implementation
to
handle
VPN
routes,
or
now
you
diverge
the
code
to
do
different
code
bases,
which
is
very
difficult
to
maintain.
So
that's
really
a
difficult
question
to
really
answer
in
idea:
it's
a
vendors
who
will
suffer
if
you
just
make
a
difference
a
fee
just
for
the
heck
of
it
right.
O
O
You
have
different
egress
port
on
the
router
and
depending
on
different
egress
port.
You
may
have
different
properties,
sunny
transport.
You
need
encryption,
some
egress
court,
you
don't
need
encryption,
so
that
has
to
be
added
so
from
implementation.
Point
perspective
is
actually
much
simpler.
You
use
sd-1
Safiye.
U
Pointers
and
also
to
actually
play
from
the
perspective
of
isolation.
Maybe
it's
a
feature
to
isolate
layer,
2
VPN
from
sd1
VPN,
even
if
you're
using
the
same
PE,
so
they
may
be
pros
and
cons
I'm,
just
saying:
let's,
let's
make
them
discuss
on
the
list
pros
and
cons
and
reach
some
consensus
right.
Thank
you.
B
O
B
Yeah
I
mean
the
as
jeff
says
in
the
chat.
Effie
is
the
is
the
address
type?
It's
you
know
it's
it's.
It's
called
an
address
family,
so
I
think
people
have
instinctively
been
like
well.
This
is
only
to
be
used
for
address
families
and
then
Saffy
has
been
used
for
you
know
subtypes,
underneath
those
things
I.
In
my
personal
opinion,
it's
it's
sort
of
it's
kind
of
unfortunate
that
we
even
split
it
up
into
two
different
spaces,
because
really
it
ends
up
being
like
there's
just
a
three
byte
number.
That
means
here's
a
particular
behavior.
G
O
B
B
B
B
I,
don't
know
about
anybody
else's
expectations,
but
exceeded
my
expectations
in
terms
of
seeing
if
we
can
use
a
virtual
meeting
as
a
substitute
for
the
for
an
in-person
meeting
and
if
you've
got
if
you've
got
any
feedback
for
for
what
went
well,
what
went
poorly,
how
we
can
use
these
kinds
of
sessions
in
the
future
or
anything
else,
please
send
them.
You
know
either
to
the
list.
If
you
want
or
to
you
know,
either
or
both
of
the
chairs
yeah
thanks
a
ton.
Oh
hey
Holly
seems
like
you
have
audio.
K
B
B
C
V
Protect
me
so
at
present-
and
we
all
know
there
are
family
of
emerging
from
past
and
I.
Think
women,
including
IOM
phones,
are
best
me3
I
am
exposed
and
they
have
magic
mark.
You
know
so
so
that
and
all
the
definition
of
I
bet
on
ending
I
face
were
more
abstract,
I
think
oh
man,
the
part
of
network
which
may
cross
multiple
network
demands
so
within
and
I
think
so
many
are
parametric.
V
V
V
V
V
Before
we
extend,
I
did
Union
digit,
we
first
defined
as
a
stability
information
here,
because
we
considering
five
categorize
I
fail.
It's
option
types,
the
English
word
paragraph
and
still,
and
the
we
also
considering
some
subset
overall,
the
I
speak,
often
tights
and
and
their
own
correspond.
Corresponding
active
field
can
be
associated
I
faded
map
space.
So
here
we
defined
I
think
the
building
information
processor
of
one
of
most
pairs
of
them
state
IDs
and
option
types
labels
at
you,
English
speaker.
F
Yeah,
so
this
is
a
case
one
question
I
have:
is
that
I
understand
the
requirement
for
the
endcap
and
d-cap
note
to
know
the
capability,
because
encap
can
add
and
be
kept,
doesn't
understand
and
we
have
a
problem.
But
it's
not
clear
to
me
at
the
intermediate
notes,
because
the
way
I
understand
IOM
data
feels
are,
if
intermediate
nodes
do
not
support
or
understand
they
can
just
ignore
and
they
don't
need
to
process
it.
So
what
is
the
use
case
for
all
the
intermediate
nodes.
E
L
L
L
L
I
mean
so
that's
the
capability
is
exported
by
the
nose
by
the
ingress
in
the
intermedia
nose
by
the
way
or
when
you
enable
this
neighborhood
is
I,
think
it
detention,
the
user
will
be
for
us,
perceive
it
as
our
past.
The
host
perceive
it
for
specific
route,
this
being
done
by
the
PDP
philosophy
or
the
BGP,
as
our
policy
that
has
been
explained
by
receive.
V
V
V
C
V
V
V
V
B
J
D
H
Might
be
addressing
a
C's
comment,
I
think
there
are
two
use
cases
here.
The
first
use
case
is
that
a
flowspec
injected
route,
which
you
may
want
to
get
the
Institute
a.m.
information,
think
about
it,
sort
of
like
triggered
NetFlow
or
IP
fix
as
an
example.
So
this
is
a
way
to
potentially
allow
for,
like
a
flowspec
das
mitigation,
to
provide
telemetry
that
can
be
used
to
help
with
the
DDoS
itself.
So
that's
that's
one
use
case.
The
second
uses.
H
But
I
was
going
into
the
second
use
case,
which
I
have
not
read
the
draft,
so
I
don't
know
if
this
is
covered
or
as
well,
but
if
you're
looking
strictly
to
get
this
type
of
OM
information
for
specific
flows,
we
basically
have
at
least
as
far
as
I'm
familiar
with
two
technologies,
Knight
EF,
that
are
sort
of
flows
back
related.
You
know
one
being
flow,
spec
itself,
the
other.
What
is
the
piece
of
extensions
that
they
put
in
that?
H
Allow
things
to
be
closed
to
be
interested
in
piece
up
as
well,
in
those
cases
being
able
to
inject
state
into
a
router
that
says
for
flow
that
matches
these
properties?
I
would
like
to
be
able
to
get
om
information.
That's
a
potentially
useful
property
as
well.
I
think
it
may
have
interesting
scaling
problems
and
somewhat
like
what
I
addressed
to
the
people
working
on
the
piece
of
clothes
Beck
feature.
H
If
there
are
situations
were
rather
going
for
a
fully
general
piece
up
extension
where
you
can
address
everything
and
you're
just
looking
to
address
certain
types
of
no
flow
tuples
that
are
common
for
a
forwarding
hardware
he's
the
example
being
like
I
want
to
match
a
TCP
flow
that
happens
to
be
using
this
source
port
desperate
to
this
sources
best
address.
These
are
things
that
flow
caches
on
14
chips
already
do
for
things
like
net
flow.
This
means
that
you
could
also
trigger
the
same
thing.
L
B
E
B
You
anybody
else
once
going
twice.
We
have
reached
the
end
of
our
scheduled
time
and
I'll
remind
everybody
that
we
have
a
second
session
scheduled
next
week.
Wednesday,
that's
April,
8th,
hope
to
see
you
all
there,
virtually
speaking
and
thanks
so
much
everybody
for
hanging
in
there
and
making
it
a
productive
meeting.
