►
From YouTube: Security Policy Working Group Meeting 11.1.17
Description
No description was provided for this meeting.
If this is YOUR meeting, an easy way to fix this is to add a description to your video, wherever mtngs.io found it (probably YouTube).
C
A
See
the
security
policy
notes
and
notes.
So
what
we
have
on
the
agenda
is
basically
kind
of
running
down
a
couple
of
updates
on
the
p,
0
and
P
ones
that
we
discussed
at
last
meeting
and
then
there
is
a
kind
of
more
general
kind
of
forward-looking
policy
proposal
that,
when
Jiang
put
together,
which
we
will
discuss
so
do
burn,
are
you
on
the
call?
Do
you
want
to
give
us
an
update
on
incremental
mts
adoption?
Okay.
D
I
think
just
all
the
discussion
happen
in
the
last
two
weeks
so
for
the
plans
that
for
the
incremental
plan
that
we
base
our
multiplex,
it
could
be.
We
still
need
to
work
on
that,
but
it
could
be
p1
because
of
the
multiplex
may
involve
some
dependencies
that
we
not
aware
of
two
weeks
ago
as
well
as
sounds
so
no.
A
We
talked
about
multiplexing
with
with
this
group,
so
just
to
kind
of
clarify
for
people
on
the
call.
The
the
idea
was
that
we
could
built
supporting
an
envoy
to
have
a
single
listener,
be
able
to
accept
both
M
TLS
or
plain
text
actions,
and
that
would
allow
us
to
incremental
e
roll
it
out
without
introducing
new
ports
or
service
interruption.
D
D
So
that's
the
good
in
progress
and
buddy,
put
it
to
p1
or
maybe
even
further.
At
the
same
time,
we
my
we
want
to
use
annotation
for
now
to
provide
service
in
a
moment
and
provides
the
traffic
shifting,
not
free
shipping
but
traffic.
My
presence
by
adding
annotation
to
create
a
new
part
for
the
chair
for
the
migrations
I
will
put
yeah.
We
put
the
link
up
to
this
item.
Any
disease
is.
B
D
D
D
D
D
D
E
So
before
we
get
into
the
detail,
let
me
just
ask
on
the
big
picture
saying
so
today,
with
co2
user
have
sto
us
and
it's
Jmol,
are
we
thinking
with
this
proposed?
It's
going
to
be
consolidated
with
one
llamo
file
and
by
default
the
mutual
tears
would
be
disabled
for
every
single
service,
and
that's
the
user
actually
turned
on
this
annotation
in
their
service
and
they
can
enable
by
a
particular
port.
Is
that
the
idea
for
this?
Yes.
D
D
D
So
if
you
don't
have
to
do
this
on
the
surface,
it
sees
the
mess
policy,
so
the
mess
could
be
mutual
TLS
at
that
time.
So
everything
you
need
mutual
TOS.
So
there
are
two
mo5
far
as
I
remember
when
we
all
turned
out
with
the
other
words
Austin
with
Austin,
no
I
think
it's
a
national
one
is
assuming
music
has
turned
on,
and
if
you
apply
this
for
policy,
you
can
turn
it
off.
So.
D
That
is
migration
strategy,
so,
yes,
I
can
just
only
turn
mutual
TOS
on
on
the
mess
level
and
disable
that
on
the
service
that
not
work
that
not
fit
with
them
mutual
TOS
in
the
beginning,
when
they
start
to
use,
they
can
start
with
the
mess
with
the
initial
TOS
and
tell
the
service
by
service.
You
know
just
to
be
sure,
for
the
slow
vibrations
right
also
on
a
design
like
Easter
configurations,
know
not
about
a
single
Yamaha
I
understand
Rana
sir
presented
in
franciotti
files.
E
F
Yeah
so
currently
we're
used
to
the
yama
and
the
Easter
siamo
and
eventually
we'll
definitely
get
rid
of
I
mean
we
only
keep
one,
but
either
we
go
from
default
turn
on
East
eel
cluster,
wise,
enable
ask
or
disables
that's
a
productive
decision,
but
eventually
we'll
have
one
and
the
user
can
gradually.
If
you,
if
is
disabled
by
default
user,
can
graduate
the
enable
service
by
service
the
other
way.
It's
also,
they
can
disable
one
by
one.
F
E
D
So
we
have
strategy
good
life.
You
want
to
turn
on
TOS
for
the
globally
for
the
whole
mess
and
then
turn
off
one
by
one
on
the
service
that
not
work
with
us,
or
you
can
also
start
with
the
mess
that
musical
tiaras
globally
and
then
turn
on
the
service
one
by
one.
So
is
this
our
operations
decision
to
choose
either
way
the
annotation
basically
provides
a
way
to
override
the
mask
policy.
E
E
D
D
C
E
E
E
Essentially
it's
going
to
overwrite,
what's
being
conferred,
what's
been
conflicted
at
the
mesh
global
level,
which
is
always
enable
me
to
TRS
for
every
single
port,
but
then,
if
I
want
to
open
up
mutual
TRS
only
for
specific
ports,
that's
one
of
the
reason
I
will
use
this
annotation,
even
when
neutral
GRS
is
enable
globally
for
a
mesh.
Is
that
yes
I
get
it
right?
Okay,
thank
you.
Yeah.
D
I'm
sorry
I'm
kind
of
problem
statement
on
when
I
say
this,
because
I
assume
the
different
set
of
audience
but
yeah
as
I
said,
there's
a
link
for
the
deciders.
Let
it
be
any
clearer.
So
this
one
which
is
Larry
presenter,
the
season
we
want
to
do
for
0.3,
right,
I,
think
I
definitely
reminds
confusion.
I
wish
you
miss
your
chances
right
now.
A
D
Okay,
but
in
future
we
can
change
or
if
how
about
new
events
happy
now,
because
this
is
mostly
controlling
the
suicide.
Was
it
this
polisher
to
host
the
key
export
of
plant
export
in
the
future?
Will
support
like
Monica
likes
post,
cares
and
plane
tax
we
may
see
a
little
comedy
is
that
true,
I
think
the
authentication
policy,
enum
or
API
will
change
in
the
future.
We
may
have
a
different
line:
server
only
client
only
as
well,
but
that's
TBD.
D
D
Not
only
you
can
put
a
notice
and
early
on
the
ease
of
service
that
when
you
have
a
service
lamp
I
write
for
API
server,
for
example,
you
cannot
understand
on
you
know
on
that.
There
is
no
such
a
thing
so
to
identify.
Let's
say
this
is
a
guy
silver,
so
do
not
use
TLS.
You
have
to
specify
the
service
name
or
main
space.
That
is
easy.
Does
it
in
oh,
this.
E
D
D
D
D
So
we
we
also
wanted
to
see
what
a
better
way
to
do
this
for
for-4
kind
of
service
management
request.
So
one
of
them
is
we
do
nothing
and
wait
for
the
environment
a
place
that
can
support
both
us
and
90s
or
the
state.
Also,
we
can
configure
filter
of
mixer
to
allow
only
he'll
check
on
that
pop
now
I
mean
plain
text
I'll
check
on
that
pot,
and-
and
that
is
the
ideal
solution,
I
think,
but
the
other
approach
is
also
change.
D
The
humor
in
check
to
kill
help
pot
to
some
dedicated
pot
and
configure
armies
pilot
to
browse
that
part
to
the
regular
object
format
and
of
the
app
oh
she's
on
the
combine.
You
see
the
current
work
around
that
require
operator
to
do
that
manually.
So
it
is
Lisa's
option
here
just
for
discussion,
I.
Think
right
now
we
my
using
often
one.
E
D
D
Instead
of
specifies
the
easy
to
be
get,
they
change
that
into
comment.
You
know
was
kind
of
a
comment
that
is
incurred
to
query.
The
local,
for
example,
on
the
local
host
checking
can
run
any
comment
on
the
this
retires
to
do
health
check,
what's
wrong
command
generation
again
and
the
otherwise
not
to
kiss
me
check
and
I
think
the
recommended
solution
is
actually
to
curb
this
amount
as
Danny,
and
we
are
documenting
how
to
do
that.
D
D
D
The
second
objective
is:
we
want
to
extend
a
notation
for
traffic
migration
as
well.
So
just
we
cut
the
problem
for
traffic
migration.
You
want
all
by
the
mechanism
for
customers
to
switch
form,
no,
not
to
us
without
doubt,
without
any
doubt.
So,
in
this
plan
we
want
to
provide
a
way
for
customers
to
specify
a
extra
pot
that
they
can
rather
jump
into
that
pot
using
TLS
and
then.
D
Basically,
you
want
to
go,
buy
a
richer
information.
For
example,
we
want
to
specify
what
part
is
equivalent
to
the
original
one.
What
is
a
authentication
policy
you
want
to
use
on
this
part
and
the
state
which
means
rise?
It's
the
traffic
should
be
use
this
one
all
the
server
you
just
quit.
The
the
new
part
of
the
server
was
not
accepting
any
traffic
yet
the
profile.
D
D
So
now
the
server
already
have
a
pot
and
when
they
change
the
district,
if
the
pilot
start
routing
the
traffic
goes
through
the
you
know
the
pot
it
yet
it
can
take.
You
know
few
second
minute
it
doesn't
matter,
but
because,
like
the
origin,
traffic
goes
through
empty
still
available,
so
there's
no
downtime
when
they
switch
over
once
it's
done.
All
the
traffic
goes
through
88.
D
They
can
upgrade
the
original
pot
to
music
device.
Now
again,
this
no
are
because
there's
no
traffic
laws
rules.
This
original
pot,
the
first
time
which
is
do
the
opposite.
We
switch
from
88
back
to
NT
by
undertake
the
hot
80s
now
became
idle,
so
the
chopping
switch
back
to
port
80,
which
is
now
easing
POS
and
the
final
step,
which
is
removes
the
old
size.
The
new
transition
odd.
E
E
E
E
D
E
D
E
D
Do
have
a
rough
idea
if,
for
users
they
don't
care
about
it,
so
a
short
window
downtown
like
water
will
be
the
shoulder
window
downtown
if
they
just
switched
a
bid,
animation,
speed,
I,
think
it's
depend
on
how
big
is
a
service
right
if
they
have
like
hundred
of
thousand
of
micro
surveys
that
cross
the
globe,
all
I
don't
know
10
feet
minute.
Boulevard
is
only
the
short
scale.
Small-Scale
health
services
I
mean.
A
I
think
that,
like
anybody,
who's
like
running
in
production
like
downtimes,
not
not
acceptable.
So
if
we
don't
provide
a
way
to
do
this
with
no
downtime,
then
they
have
to
consider
some
other
higher
layer
as
a
way
to
prevent
downtime
like
they
have
to
go
up
to
their
load.
Whatever
they're,
you
know,
a
cloud
load
balancer
is
and
then
switch
from
one
you
steel
cluster
to
another.
Basically
like
anybody,
who's
in
production,
like
you
just
can't,
have
have
downtime,
that's
like
almost
not
like.
No,
no
one
does
that
right.
Satellite.
D
E
I
think
time
to
demo
this
too,
and
for
production
I
agree,
that's
what
we
are
trying
to
achieve.
No
downtime
but
I
wonder
if
there
is
a
way
we
can
roll
out
the
configuration
to
you
one
instance
to
say
at
a
time.
So
maybe
let's
say:
if
I
have
three
instances,
maybe
I
take
one
down
instead
of
all
three
down
together,
then
that
type
of
downtime
could
be
acceptable
right.
If
I'm
only
take
30%
of
my
traffic
down.
A
A
Once
we
have
multiplex,
then
we
want
to
futz
around
with
all
these,
like
these
extra
listeners
and
things
like
that,
you'll
be
able
to
open
up
a
single
listener
that
that
could
accept
either
plain
text
or
TLS
connections.
And
then
you
can.
You
can
sort
of
roll
clients
over
from
from
the
old
port
to
the
new
port,
basically
just
as
as
fast
as
you
as
you
want,
as
the
operator.
D
D
Very
paranoid
user
that,
like
you
know,
don't
want
to
multiplex
because
we
are
sleeping
the
package,
so
you
have
some
firewalls
are
preventing
that
all
they
want
to.
You
know,
know
exactly
what
happened
so
I
mean
for
some,
because
this
may
be
a
good
approach,
good
enough
for
people
who
don't
care
about
downtime
that
can
fit
a
bit
and
for
the
middle.
We
won't
because
a
still
yeah
it.
D
D
E
A
I
mean
I
think
that,
like
if
you
go
down
this
this
path
of
like
trying
to
automatically
pick
a
port,
then
the
edge
cases
are
gonna
just
drive
you
up
the
wall.
There
I
mean
because
this
this
solution,
where
you've
got
multiple
ports,
already
needs
to
be
coordinated
with
any
network
policy
in
kubernetes
or
any
firewalls
that
you
might
have
so
like
having
it
pick.
This
stuff
automatically
is
I,
think
gonna
be
a
nightmare
and
I'm
kind
of
not
worth
the
effort.
Yeah.
E
A
C
E
A
E
E
A
I
mean
the
product
page
like
service,
is
entirely
in
the
mesh
and
gets
a
connection
from
the
from
the
ingress
proxy,
and
so
that
would
be
protected
with
mutual
TLS.
The
connection
from
from
the
ingress
proxy
to
the
product
page
service,
but
the
connections
coming
to
the
ingress
proxy
will
typically
not
be
each
or
we
don't
have
a
solution
for
the
ingress
proxy
to
have
mutually
authenticated.
Tls
listeners.
D
B
D
A
I
mean
I
think
that
they,
like
you,
are
gonna,
have
people
that
are
migrating
some
services
to
sto,
but
there
will
still
exist
clients,
maybe
inside
their
cluster,
that
are
making
calls
to
that
service
that
are
not
integrated.
With
this
do,
and
so
this
dual
port
solution
sort
of
gives
you
that
ability.
A
B
B
Yes,
so
for
each
unit
of
attack,
so
for
the
four
last
weekend,
I
was
trying
to
focusing
on
how.
How
is
the
attacker
can
converge
to
kubernetes
our
back
and
I
had
a
discussion
with
spike
and
we
we
had
a
rough
proposal
and
we
talked
for
kubernetes
folks
about
the
convergence
plan
and
so
early
cooper,
extreme
yeah,
gugak,
honest
yeah,
so
so
the
current
from
from
the
feedback
we
have
got
I
think
the
current
plan
is.
We
will
mostly
keep
the
current
proposal.
B
Basically,
we
will
make
small
changes
like
the
name
changes,
property
from
Eastern
Road,
who
service
row
or
some
kind,
the
name,
but
mostly
it
will
be
the
same
proposal
and
the
the
plan
is
we
will
implement.
This
is
the
upper
guess
as
ceoddi
custom
resource
initially
for
kubernetes
and
later
kubernetes
community
making
site
who
incurred
in
steal
a
pack
as
part
of
the
last
internal
resource,
but
the
front
play
is
not
finalized,
I'm,
just
giving
an
update
here,
we
will
still
continue
with
discussion
with
other
folks
and
the
broader
community,
including
the
communities
community.
G
That's
inside
the
right
approach
to
me,
you
were
like,
even
if
the
kubernetes
community
was
bowled
over
with
the
proposal
and
really
liked
it
that
almost
certainly
want
to
start
with
prototyping
it
with
C
IDs
anyway,
and
so
I
think
decoupling
ourselves
from
that
process
will
allow
us
to
keep
moving
forward
quickly.
Yeah.
G
B
H
B
D
D
We
has
method
how
that
Japanese
ambassador
magma
to
actually
method
and
how
that
is
I
mean
relate
to
each
other,
so
such
that
we
can,
if
I,
consistent,
ACO
policy
and
the
other
thing
I
notice
later,
is
it's
possible
for
us
for
pretty
fun
so
before
the
role
like
editor
law
at
the
middle
and
that
could
be
reused
on
monkey
for
services
just
like
water,
we
can
see
from
cloud
I
am
and
that
will
correct
coming
great
listening
by
using
experience.
I,
don't
think
we
have
explored
too
much
on
that
direction.
C
D
A
D
H
H
B
H
D
D
D
Okay,
can
everyone
see
my
presentation,
my
slide?
Sorry,
my
dog?
Okay,
so
these
are
mostly
forwarded,
leukemia
proposals,
so
this
could
you
can
imagine
this
at
the
follow-up
work
as
from
horse
p.m.
and
swag
is
doing
so
currently
we're
mostly
talking
about
how
to
enable
authentication
for
music
ars-art
beyond
that.
We
also
wanna
cover
other
authentication
type
as
at
least
in
here,
as
well
as
how
does
legacy
application
that
doesn't
use
my
talk
to
service
using
my
beyond
that.
D
Now,
Jessica
quickly
cool
or
walk
through
the
channel
proposal,
and
this
talk
is
still
walking
progress,
I'm,
not
sure
visitor.
It's
not
like
entirely
ready
for
review,
but
only
feedback
is
welcome,
so
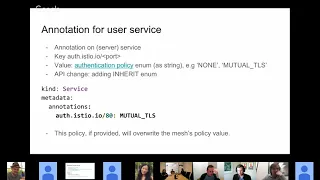
instead
we'll
have
using
annotation
to
define
music
errors
or
not
new
to
tears.
Here
we
are
proposing
to
use
a
CR
be
just
like
how
do
we
define
authorization
policy?
So
we
have
consistent
story,
so
add
a
new
character,
authentication
policy
and
also
a
so.
D
The
metadata
is
the
same
in
the
stack
we
added
a
I
am
we're
proposing
security
level,
so
security
level.
You
can
specify
many
more
security
level
that
could
be
plain
tags
and
in
the
future
we
could
add
a
lot
kill
us
without
encryption.
What
he
has
written
encryption,
Maxim,
secure
level
is
just
adding
here
for
completeness.
If
you
want
code,
Q,
plaintext
or
then
you
can
specify
both
min
and
Max
to
a
plaintext
and
security
level
could
be
applied
at
a
namespace
level
at
a
service
level
and
at
a
core
level
and
even
master
level.
D
If,
if
you
have
use
case
for
that,
other
than
security
policies
are
two
more
section
wines
credential
policy.
Basically,
we
want
to
describe
what
kind
of
credentials
create
client
new
to
prison
either
certificate
we
can
set
our
music
errors
or
chronic,
and
just
pro
presents
your
token
or
other
authentication
token.
C
B
D
D
Are
sure
about
this
part,
so
I
think
that
that
was
something
we
needed
more
discussion.
But
again,
this
is
just
pre
most
presenting
the
use
cases
here.
I
think
we
need
a
way
to
describe
the
case
like
if
client
doesn't
have
any
credential.
Do
we
accept
them
or
not
or
know
if
they
belong
to?
If
whether
this
blunt
was
an
occasional
authorization,
I
think
that's
debatable.
D
H
D
Yeah
we
have
more
discussions,
but
let
me
just
quickly
run
through
the
use
cases.
I
think
that
I,
like
the
first
step,
is
assuming
we
have
multiplex
supported,
ready
and
we
could
have
said
many
more
secure
level
to
claim
tax
setting
means
each
service
can
accept
both
tos
and
plaintext
traffic,
and
we
allow
clients
without
any
credential
and
cloud
could
be
come
from
either.
D
Is
your
client
that
has
my
brownie
or
lexicon?
Doesn't
have
my
that's
where
we
start,
but
we
do
encrypt,
so
we
don't
have
inclusion
at
this
at
this
moment,
I'm
moving
forward.
The
second
step
we
could
enable
you
to
tears
between
my
clients
between
is
the
clan
and
the
ether
service,
and
what
we
need
to
do
is
to
change
the
permissions
from
no
current,
no
crust
to
use
use
certificate.
For
my
clients
are
for
lack
of
the
clients,
they
can
still
talk
to
Easter
service
without
presenting
certificate.
D
D
E
E
D
E
D
A
good
question
I
think
you
really
need
to
figure
this
out,
not
just
for
sanitation
policy
for
any
policy,
including
authorization
policy
who
has
access
to
air
the
deciduous
and
we
commonly
defined
different
levels
of
operators
like
a
stop.
Radio
national
operator
such
as
lab
operator,
are
definitely
not
users,
I
think.
D
Right
now
we
are
the
white
door,
which
is
a
mean
superpower
or
the
mean
and
I
think
that
might
be
a
sufficient
enforce
more
customers
for
big
customers
like
based
on
experience
from
Google.
We
typically
have
given
the
roads
by
we
even
have
service
operator.
They
can
only
operate
the
service
belonging
to
that
king
and
they
cannot
modify
service
that
doesn't
belong
to
them
same
thing
for
ACL
yeah,.
B
E
D
B
Permission
itself
can
be
a
commission,
so
like
income
net
is
it
has
defined
the
work
verbal
which
can
be
used
at
all
to
say,
I
you
can.
You
can
use
this
point.
Work
for
cluster
rows
are
crafted
row
bindings,
so
that's
basically
assign
you
the
Commission
to
to
define
the
artwork
to
so
define
your
access
control
policy.
Okay,.
