►
From YouTube: Kubernetes SIG API Machinery 20190313
Description
No description was provided for this meeting.
If this is YOUR meeting, an easy way to fix this is to add a description to your video, wherever mtngs.io found it (probably YouTube).
A
A
Today
few
people
have
put
a
put
caps
on
the
agenda
and
so
I
went
through
and
just
grabbed
all
the
available
caps.
I
think
some
of
those
can
be
very
short
discussions,
but
I
think
it
would
be
nice
for
us
to.
You
know,
skim
the
ones
there
and
decide
if
we
need
to
take
some
action,
and/or
assign
somebody
to
review,
etc.
So
with
that
said,
let's
take
it
from
the
top
mic
and
men
have
you
know:
min
has
a
cap
out
and
I
just
realized
that
Mike's
design
is
actually
in
a
Google
document.
A
A
A
C
B
A
D
A
Still
feel
like
just
an
ordinary
guarantee
should
be
good
for
those
right
like
if
we
guarantee
a
certain
UPS
is
like,
like
skipping
the
and
you're
sending
more
than
that.
You
don't
want
some
of
your
requests
to
like
get
instant
service
and
some
of
your
request
to
be
arbitrarily
delayed
by
some
queue.
B
Well,
remember:
we
have
this
problem
that
some
requests
are
secondary,
they're
just
serving
primary
their
in
their.
You
know,
meta
requests
in
some
sense
that
happened
in
the
course
of
serving
primary
requests
and
if
the
primary
requests
are
top
priority.
Well,
the
meta
requests
had
better,
at
least
as
high
priority
as
the
primary
request.
And
if
the
primary
request
is
top
priority,
then
the
meta
request
has
to
be
top
priority
and
we
can
get
in
a
deadlock
unless
they're
admitted
unconditionally.
A
That
is
probably
true,
but
this,
but
it
doesn't
like
admitting
some
unconditional
okay,
so
so
I
guess
in
at
least
men's
thing.
It
wasn't
that
they
admitted
request
unconditionally.
Is
that
it
mitad
requests
unconditionally
but
admitted
could
requests
if
there
was
reserved
quota
remaining,
which
is
not
the
same
as
admitting
unconditionally
right.
B
A
Find
that
at
least
somewhat
compelling
I
need
to
spend
some
time
with
your
actual
document.
I
did
like
the
the
kept
here
are
the
like.
All
the
design
detail
section
like
I
think
at
least
like
95
percent
of
this
is
is
actually
like
background
reading
or
like
lit
review,
which
I
think
should
go
in
the
camp,
no
matter
what
design
end
up
with
yes,.
B
A
So
the
the
the
I
believe
one
of
the
like
the
kept
with
the
goals
in
the
unlikely
skeleton
I
believe
that's
merged.
At
this
point
at
least
I
guess
so
that's
good
min
suggested
on
chat.
I,
don't
know
if
he's
on
the
meeting.
He
suggested
on
chat
that
at
this
point
we
should
maybe
pick
an
overall
approach
before
like
optimizing,
individual
approaches,
work
and,
unfortunately
I
dispensable
time
reading
or
current
document.
B
Sure
yeah
I
think
he's
sleeping
right.
Now
he
and
I
have
been
discussing
I,
you
know
synchronously
and
asynchronously.
So
whenever
you're
ready,
let's
get
together,
perhaps
at
a
separate
meeting
or
in
the
next
iteration
of
this
meeting,
yeah
I
think
minute.
I
would
like
to
proceed
quickly.
So
you
know
whenever
you're
ready,
you
know,
email
or
a
separate
meeting
or
whatever
yeah.
A
B
A
E
A
E
A
Myself
a
note
next
on
the
list
is
Walters
and
I.
Don't
know
the
actual
name
of
the
other
include
young
is
I,
didn't
recognize
the
I
know
them.
I
didn't
recognize.
The
handle
is
the
network
proxy
captain,
and
this
is
maybe
not
a
perfectly
clear
name-
we're
talking
about
a
adding
a
layer
between
API
server
and
the
outside
world
in
terms
of
like
egress
from
API
server,
so
I
don't
know,
Walter
do.
F
F
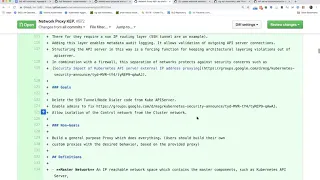
So
the
network
put
the
idea
for
the
network
proxy.
Is
we
have
a
few
things
that
we'd
like
to
solve?
One
is
DIMMs
has
been
asking
to
get
the
SSH
tunnel
code
removed
for
a
while
and
in
fact,
if
we're
gonna
make
progress
on
the
sig
cloud
provider
extraction
that
needs
to
happen.
In
addition,
there
are
a
couple
of
security
concerns
that
exists
today.
F
We'd
also
just
like
to
add
this
as
an
extension
mechanism
by
which
we
can
control
that
traffic,
whether
it's
for
auditing
or
other
reasons.
It
also
allows
us
to
take
care
of
issues
for
cloud
providers
where
the
I
pee
ciders,
for
the
control
plane
actually
overlap
with
the
IP
ciders
that
have
been
picked
by
the
customer
for
their
net
for
the
cluster
Network
and
regular
IP
routing
doesn't
fix
that.
But
this
network
proxy
system
does
so
that's
sort
of
an
overview
of
the
major
problems
that
we're
trying
to
solve.
With
this
yeah.
F
A
given
proxy
and
then
that
proxy
is
responsible
for
knowing
how
to
get
the
traffic
where
it
needs
to
go.
So,
for
instance,
if
you
are,
you
know
a
cloud
provider
and
you
need
to
deal
with
IP
Sider
conflicts,
or
you
just
want
to
tunnel
the
traffic
in
a
secure
manner
between
the
networks.
Then,
all
of
the
logic
that
used
to
be
the
SSH
tunnel
code
is
pulled
out
of
the
QB
API
server
and
exists
in
a
separate
process,
which
is
the
proxy
that
you
know
can
be
left
as
an
exercise
to
the
cloud
provider.
A
F
F
A
Cool
so
I
think
well,
I,
don't
I,
don't
know
that
we
want
to
go
in
depth
design
here.
I
think
what
we
can
use
usefully
do
in
this
meeting
is
make
sure
that
the
right
side
of
approvers
is
on
this
document
or
on
this
cap,
so
that
we
can
basically
know
what
we
have
to
do
to
get
it
approved
I've
made
at
least
one
pass.
A
H
F
F
On
this
and
I,
don't
think
I've
actually
addressed
all
those
concerns.
Yet
so
I
need
to
spend
a
bit
more
time
with
Mike
what
about
sig
cloud
provider
so
I'm,
actually
III
I'm
one
of
the
leads
on
sig
cloud
provider
and
in
addition,
at
Andrews
psyche
him
who
is
the
chair?
First,
a
cloud
provider
has
reviewed
it,
so
I
I
will
probably
bring
it
up
in
the
next,
not
so
much
as
a
approver,
but
we're
definitely
going
to
get
reviews
from
six
provider.
F
B
A
A
Maybe
Walter
can
take
that
as
an
action
item,
so
actually
a
and
the
viewers
from
off
and
it
kind
of
compromise,
I
guess
yeah.
It
sounds
like
you're
covered
from
clapping
like
a
bit
it'd
be
good
to
officially
have
someone
from
off:
okay,
okay
cool!
So,
like
I,
said,
I
scanned
the
open
caps
with
API
machinery,
actually
I
punted
one
out
because
it
wasn't
actually
relevant,
and
so
we've
got
three
laughs
that
I
think
it
would
be
good
to
look
at
so
let's
see,
first
is
the
convert
weapons.
This
is
actually
Jordan.
H
Yeah,
so
this
is
a
follow-up
to
some
of
the
design
work
we
did
for
1:14.
There
were
two
issues
that
were
in
the
list
of
GA
requirements
for
web
book
admission,
and
one
was
automatically
converting
incoming
requests,
wait
back
up
what
books
registered
for
resources
that
they
want
to
intercept
and
they
register
particular
versions.
Particular
API
groups
that
they
understand
and
want
to
intercept
as
new
versions
of
those
resources
are
added.
H
It
is
possible
that
a
web
hook
that
registered
for
one
version
is
now
no
longer
intercepting
all
of
the
available
versions,
and
that
may
be
what
they
want,
but
likely
is
not,
and
so
having
a
way
for
a
web
looks
you
register
for
a
set
of
versions
that
they
understand
and
if
other
versions
of
those
resources
come
into
existence
in
the
future,
allow
the
API
server
to
convert
those
requests
to
versions
the
web
book
understands
and
still
route
them
through
the
web
block.
It
would
be.
H
The
web
look
understands
correct,
and
so
this
expands
the
admission
review
object
that
is
sent
to
the
web
hook
to
provide
additional
information,
so
the
web
hook
can
see
that
that
occurred
if
it
did
and
a
wave
or
the
webhook
to
opt
out
of
that
behavior.
If,
for
some
reason
they
don't
want
to
intercept
all
versions,
so
this
is
one
of
the
two
outstanding
GA
requirements
for
web
books.
This
updates
the
existing
kept
to
add
a
detailed
design
around
around
that.
H
A
Like
clearly,
this
is
much
more
user
friendly
to
the
webhook
author,
my
the
the
thing
that
I
am
somewhat
concerned
about
is
it.
It
implies
that
in
principle,
it's
impossible
for
the
aggregator
to
hook
the
web
hooks
like
every
backing.
Api
server
has
to
implement
the
web
book,
which
is
that
is
already
the
case
yeah.
It's
already
the
case,
but
I
think
it's
kind
of
a
problem
given.
H
A
A
H
F
H
A
F
Can
register
for
multiple
versions,
so
yeah
yeah?
No!
No,
that
makes
sense
I
just
wanted
to
make
sure
that
we
had.
You
know
very
clear
mechanism
for
upgrading
h.
A
web
looks
yeah
roll
out
the
new
code,
then
roll
out
the
config
that
sends
me
over
and
you
and
I
think
to
Daniel's
point.
Is
it's
as
hard
requirement
that
you
have
to
be
able
to
tolerate
two
versions?
Yes,
because
otherwise
you
can't.
E
H
G
G
A
H
I'm,
given
that
it
needs
to
be
able
to
do
the
conversion,
I
think
polling,
building
the
map,
of
which
resource
versions
are
identical,
based
just
on
discovery
like
there
has
to
be
a
corresponding
conversion
code
that
it
has
to
handle
too,
and
so
it
seems
like
the
the
code
that
knows
how
to
convert
between
things
is
much
more
prescriptive
than
hey.
I.
