►
From YouTube: Kubernetes Cloud Native Online Meetup 20160906
Description
Learn about Kubernetes Identity Management from Mark @ Tremolo Security!
Join the meetup and keep learning about Kubernetes and Cloud Native applications. http://www.meetup.com/Kubernetes-Cloud-Native-Online-Meetup/
A
Let's
get
started
first
of
all,
going
to
double
check
here.
Can
everyone
hear
me?
Okay,
yep,
alright
sounds
good,
so
this
is
the
fourth
edition
of
our
kuba
netis
cloud
native
online
me
up
and
today
we
have
Marc
Marquez
from
tremolo
security,
who's.
Actually,
one
of
the
founders
of
the
company.
He
is
phased
in,
Washington
DC,
the
States.
We
have
people
from
I
think
all
over
world
here.
So
just
to
give
you
a
little
reference,
it's
about
moon
over
there
and
we
are
very
excited
to
have
him.
A
We're
gonna
have
a
hopefully
a
very
good
discussion.
Today,
I
we
was
going
to
be
running
a
bit
of
a
demo
right
mark
yeah
and
we
are
gonna.
Let
him
get
right
to
it,
but
before
we
do
just
a
little
bit
of
a
logistical
things,
this
meeting
is
recorded.
So
keep
that
in
mind
we
are
going
to
have
about
45,
50
minutes
of
presentation
give
or
take,
and
the
rest
of
the
time
will
be
allocated
to
question
and
answer
the
way
that
we
will
run.
A
That
is
that
you
can
send
me
a
message
privately
on
the
chat
with
your
question
and
I.
Will
read
your
question
out
loud
just
so
it
doesn't
get
too
messy
on
the
on
the
group.
Yet
after
that,
we'll
we'll
leave
a
will,
leave
the
group
chat
open
for
some
discussion
and
then
everyone
can
go
on
about
their
day
and
we
will
have
the
video
up
and
running
soon,
so
without
any
further
ado.
A
Yes,
so
Julian
just
mentioned
here
that
you
can
help
spread
the
word
about
this
talk.
That's
we're
still
expecting
some
people
to
show
up
like
like
Rob
just
did,
and
people
probably
still
be
popping
in
throughout
the
talk
up.
But
if
you
want
to
help
spread
the
word
you
can
share
the
link
to
the
video.
So
without
any
further
ado,
we'll
have
mark
talk,
you'll
introduce
himself
an
unhealed,
we'll
get
on
with
this
presentation.
You
can
take
it
over
mark
thanks.
B
A
B
It's
up,
okay,
cool,
so
I,
don't
want
I,
don't
need
to
see
me:
okay,
cool
there!
We
go
that's
good
enough,
so
we're
going
to
talk
about
any
management,
Cooper
Nettie's
we're
going
to
talk
about
both
SSO
and
Auerbach.
These
are
both
topics
that
have
been
coming
up
a
lot
lately,
especially
since
1.3
came
out,
and
so
there's
a
lot
of
interesting
things
about
it,
a
lot
of
very
powerful
things
that
you
can
do
with
it.
B
Of
course,
if
I
knew
how
to
use
my
Mac,
that
would
help
so
real
quick
introduction
to
Who
I
am
who's
tremolo
security.
We
were
found
in
2010,
based
on
10
plus
years
of
experience
in
my
daddy
management,
Microsoft,
open
source,
IBM,
Oracle's,
CEA,
ping,
sale
point.
You
know:
automotive
beverage,
financials,
federal,
US,
federal,
a
telco
cable.
B
So
a
lot
of
experience
deploying
all
these
different
types
of
identity
management,
software,
most
of
the
time
being
brought
in
after
a
project,
has
been
deemed
failed,
and
so,
with
a
lot
of
that
experience
and
turning
those
types
of
projects
around,
we
just
thought
there
was
a
better
way
to
go.
So
we
started
tremolo
security
and
not
to
get
too
deep
into
who
we
are
you'll,
see
kind
of
our
open
source
edition,
open
unison
here
as
part
of
showing
off
this
integration.
B
So
why
yss
on
yr
back
I
break
these
up
into
two
different
categories
because
they
serve
overlapping
but
very
important,
distinct
roles
with
sso
the
first
one
you're
going
to
run
into
is
compliance,
especially
if
you're
working
in
something
that
anybody
who's
dealt
with.
It
will
know
what
I
mean
by
covered
application,
at
least
in
the
US.
This
is
typically
financials
health-based
things
like
that,
where
you
have
to
comply
with
certain
regulations,
sarbanes-oxley,
HIPAA,
etc,
and
a
lot
of
that
when
it
comes
to
security
side
of
things,
is
centralized.
B
Managing
individual
credentials
is
hard,
it's
difficult
and
so
having
that
centralized
system
makes
a
better
security
experience
and
I,
always
personally
and
maybe
I'm
biased,
because
I've
been
doing
this
so
long
but
I
think
it's
easier.
One
less
thing
to
remember
is
always
a
good
thing
leads
to
less
things
being
written
down
on
stickies.
On
my
desk,
so
you
know
there's
that
aspect
as
well
and
then
one
that
I
don't
really
mention
here,
but
you
know,
would
be
important
for
anybody
trying
to
sell
the
idea
of
using
Cooper
Nettie's
in
a
corporate
environment.
B
It
just
makes
it
easier
to
deploy
you're
focusing
more
on
your
coo
benetti's
deployment
rather
than
managing
users.
Our
back
a
lot
of
the
same
ideas.
Compliance
still
comes
up.
Multi
tendency
is
one
that
gets
talked
about
a
lot,
but
I
would
argue
that
even
in
a
non
multi-tenant
environment,
if
you're
deploying,
if
you're
deploying
Cooper
Nettie's
just
for
a
single
application
or
set
of
common
applications,
that
even
a
simple
are
back
mount
can
give
you
a
lot
of
power.
B
For
instance
you're
using
external
monitoring
solutions,
you
might
want
to
be
able
to
provide
a
simple
set
of
URLs
that
they
can
access,
rather
than
giving
them
just
a
certificate
laying
them
half
of
at
it.
And
then,
finally,
you
might
have
some
different
roles
inside
of
your
team
and
moderating
one
of
them
that
you
might
want
to
think
about.
B
B
Are
none
except
for
service
accounts,
in
fact,
if
it
had
not
been
already
said
on
the
OpenStack
side
because
of
the
you
build
system,
this
title
actually
would
have
been.
There
are
no
identities,
there
is
only
zuul.
Everything
has
to
be
asserted
to
cooper
neighs.
There
is
no
internal
user
store
right
now.
Cooper
Nettie's
doesn't
know
how
to
talk
to
an
LDAP
directory,
but
that's
been
discussed,
and
this
is
very
different
from
open
shift.
B
If
so,
I
started
off
in
the
open
chimpo
before
I
start
with
stock
cooper,
Nettie's
and
in
open
shift,
you
do
have
a
centralized
identity
management
store,
it's
very
simple,
but
there
is
something
that
you
can
interact
with.
To
say:
who
is
this
user?
And
what
groups
do
they
have?
You
can't
do
that
with
Q&A,
so
that
that
offers
some
very
powerful
decisions,
but
also
some
interesting
choices
that
you
need
to
make
and
when
it
comes
to
SSO
it's
just
open,
ID
connect.
B
There
is
no
sample
to
I'd,
be
really
surprised
if
Samuel
too
has
ever
supported,
I'm
sure
somebody's
asked
for
it,
but
just
given
the
fact
that
most
interaction
with
Cooper
Nettie's
happens
using
web
services
and
open
ID
connect
is
really
a
lot.
I
want
to
say
better
for
web
services,
because
I
could
really
Sparkle
religious
war,
but
it's
been
adopted
much
more
for
web
services
and
given
how
powerful
the
existing
implementation
is.
I,
just
don't
see
sample
to
really
being
something
that
becomes
super
white
boy,
at
least
in
the
near
term
I.
B
Now
one
thing
to
remember
is
again:
this
is
api's
and
there's
no
system
for
redirects.
So
when
you
talk
about
an
sso
solution,
you're,
usually
talking
about
okay
I,
go
to
my
web
app
like
Google
Apps
for
enterprise
or
whatnot
I,
go
to
my
app
it
redirects
me
to
an
identity
provider.
I
put
my
information
and
bounces
me
back
but
being,
but
it
won't
might
have
a
session
that
that
redirect
system
doesn't
exist
in
Coober
Nettie's.
So
if
you're
going
to
add
and
SSO
solution,
you
have
to
figure
out
a
couple
of
things.
B
One
is
how
do
you
trigger
the
authentication
and
then
to
how
do
you
get
your
token
and
start
using
it
inside
of
cupones
use?
You
know
with
cube
control
command,
very
easy,
but
it's
just
things
you
have
to
think
about
and
then
finally,
the
dashboard
dashboards,
not
our
back
away
I,
mean
the
dashboard
just
integrate
or
interacts
with
the
various
web
services,
but
it
has
no
idea
of
who
you
are
it's
just
this
tool
that
runs-
and
you
know,
security
is
just
something
that
you
guys
think
about.
B
There
is
an
open
issue
that
has
been
actively
discussed
on
how
to
make
dashboard
more
I
dandy
aware,
but
as
of
right
now
that
doesn't
so,
if
you're
going
to
use
the
dashboard
you
getting
some
very
specific
precautions
around
that
time
check
here.
Ok,
so
I've
been
told
that
every
presentation
needs
at
least
one
meme,
here's
my
first
one
remember
all
these
features
in
Cuba
natives
13
around
SSO
and
our
back
our
alpha.
They
are
subject
to
change
and
there's
an
active
discussion
about
changing
them
up.
B
You
know
because
and
general
tell
you
the
first
time
you
build
something.
A
lot
of
things
will
go
into.
These
seems
like
a
good
idea
at
the
time
bucket
and
that's
probably
going
to
be
true
of
the
trooper
naas
identity
management
implementation
as
well,
but
there
are
certainly
things
that
you
can
do
that
if
you
really
need
these
features
now,
and
you
want
to
start
to
use
them
that
can
help
insulate
some
best
practices
that
I'm
going
to
recommend
here.
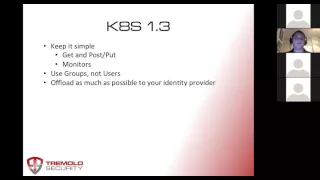
B
So
first
often-
and
this
is
really
true
of
any
I
daddy
management
implementation
yeah
at
the
beginning,
I
mentioned
that
most
implementations,
I
was
a
part
of
I
was
brought
on
because
the
implementation
was
considered.
A
failure
very
few
times
have
I
been
able
to
start
from
scratch
and
build
things.
B
The
way
I'd
really
like
to
do
it
and
most
of
the
time
the
failure
resides
in
a
couple
places,
sometimes
its
technology,
sometimes
the
implementers,
but
most
of
the
time
it
has
to
do
with
overcomplicating
things
and
the
underestimation
of
the
implications
inside
of
your
organization.
So
and
I'll
show
you
this
in
of
us.
You
know
I
only
have
about
700
sites
left,
so
we're
doing
good.
B
Well,
the
folks
who
own
active
directory
probably
are
going
to
be
in
the
same
line
of
command
that
that
the
folks
that
are
paying
for
your
Cooper
name
is
implementation
are
in,
and
so,
if
those
goals
don't
align,
trying
to
get
resources
out
of
the
Active
Directory
team,
that's
really
focused
on
managing
a
windows
network,
not
managing
your
kubernetes
deployment
to
be
really
difficult.
So
the
simpler
you
can
keep
things
the
less
those
types
of
organizational
impacts
will
happen,
and
then
you
know
don't
reference
users
directly
in
your
robot.
B
B
Well,
you
can
name
you
can
a
bruise.
You
can
also
name
service
accounts,
a
really
bad
idea
to
name
users,
and
the
reason
is
that
users
can
be
very
ephemeral.
They
can
move
around
it's
very
hard
to
track,
and
it's
one
of
those
things
that
okay,
if
you're,
if
something
changes
underneath,
if
you're
using
groups,
then
you're
changing,
maybe
one
or
two
points.
If
you're
changing
users,
then
you
have
to
change
it
for
every
single
user
in
the
system.
B
It
will
be
tempting
to
try
and
do
as
much
inside
a
cooper
night
as
possible
for
no
other
reason
than
you,
as
the
implementer
might
have
the
most
control
that
you
do
over
Cooper
net.
However,
the
more
that
your
identity
provider
does,
the
less
likely
changes
in
the
1.3
API
design
will
affect
your
current
deployment.
B
So
if
you're
using
your
identity
provider
I'm
going
to
list
a
couple
of
here
in
a
future
slide,
you
know
do
as
much
as
you
can
there,
because
there's
going
to
probably
be
less
change
on
that
side
than
inside
of
Cooper
Nettie's,
so
hows
it
all
work,
let's
get
into
the
meat
of
it.
So
this
is
what
I
think
of
as
a
reference
architecture
for
a
identity,
managed
SSO
where
Cooper
neighs
deployment.
We
have
a
few
different
pieces
here,
so
obviously
urban
ace
right
and
then
over
here,
I'm
using
key
cook.
B
As
my
daddy
provider
I'll
listed
a
few
others,
and
then
we
have
a
data
store
here
now,
I
I
went
with
a
virtual
store.
What
I
wanted
to
be
able
to
do
is
say:
okay,
I'm,
going
to
assume
I,
don't
own.
My
active
directory,
so
I
need
to
store
roles.
Someplace
I
need
to
store
groups
some
place,
so
I
wanted
to
experiment
with
the
idea
of
using
a
virtual
directory
to
manage
your
groups
in
one
data
source,
but
your
users
in
another
data
source
and
then
bringing
them
together
virtually
using
a
virtual
directory.
B
So
that's
what
our
demo
is
actually
set
up
to
do
so
I've
got
a
virtual
directory,
my
virtual
directory,
our
open
source
virtual
directory
active
directory,
where
my
users
are
and
then
I'm
keeping
my
roles
as
attributes
inside
in
this
instance,
free
IPA
server.
Only
reason
why
I
want
with
this
particular
configuration
was
actually
had
already
set
up
for
a
different
demo,
so
I
figured
less
work.
I
need
to
do
to
get
things
working,
the
better
and
then.
Finally,
up
here
we
have
open
unison,
open
unison
is
our
flagship.
B
Open
source
project
is
the
basis
for
a
commercial
product
and
it's
got
several
different
functions
which
you'll
see.
One
is
a
reverse
proxy,
so
that's
how
we're
actually
going
to
handle
security
for
the
curb
Renee's
dashboard
will
show
you
how
we
do
SSO
with
that.
It
also
has
a
workflow
engine
for
user
provisioning.
B
So
once
you
have
access,
you
know,
how
do
you
determine
who
should
have
access
to
different
roles
without
users
having
to
manually,
add
users
to
groups
and
then,
finally,
that
that
redirect
system
that
Cooper
neighs
doesn't
have
open
unison
will
give
you,
so
we
will
manage
the
redirects,
and
then
we
have
an
app
that
we
call
token
that
will
actually
let
you
display
a
token.
So
in
this
instance,
it'll
be
your
access
token
for
Cooper
Nettie's,
so
this
all
happens
really
fast.
That's
why
I
like
to
go
to
the
screen.
B
First,
it's
sometimes
hard
to
appreciate
how
much
is
going
on
in
the
background.
So
first
I'm
going
to
do
is
I'm
going
to
access
open,
unison,
open,
Unison's,
going
to
say,
don't
know
who
you
are
I'm
going
to
redirect
you
over
to
key
cloak
key
cloak.
Is
going
to
say,
I
still,
don't
know
who
you
are:
let's
go
and
collect
your
credentials,
click
the
credentials,
redirect
you
back
to
open
unison,
and
then
we
do
a
back
channel
called
key
code
to
get
your
access
to
its
open.
Id
connects
your
access.
B
Token
is
a
JWT,
a
JSON
web
token.
This
is
a
bit
of
JSON
that
has
who
you
are
some
date
and
time.
Information
is
also
digitally
signed,
so
Cooper
neighs
can
check
this
and
not
have
to
phone
home
to
validate
it,
which
is
really
great
at
which
point
opening
some
presents
you
a
portal
and
you
can
click
on
some
links.
One
is
going
to
be
for
the
dashboard
assuming
you're
authorized.
The
other
is
going
to
be.
To
get
your
token,
so
we're
going
to
click
on
the
dashboard.
We
click
on
the
dashboard.
B
Every
request
that
runs
through
open
unison,
tsukuba,
Nettie's,
api
server
will
actually
have
your
aw,
your
JWT
token
embedded
in
the
request.
It
will
be
injected
so
you're
authenticated
with
open,
unison
and
then
open
unison
tells
Cooper
Nettie's,
who
you
are
by
injecting
that
bearer
token
for
you.
So
that's
how
you
get
SSO
into
the
Cooper
Nettie's
dashboard.
B
What's
the
benefits
of
this
approach,
couple
of
one
you've
got
with
the
browser
based
approach
when
it
comes
to
authentication
a
lot
more
options.
You
know
if
you're
just
doing
username
a
password,
okay
I
can
see
why
the
browser
page
might
be
overkill,
but
in
all
the
different
multi-factor
capabilities
out
there
most
of
them
are
designed
around
a
browser.
B
So
this
makes
that
a
lot
easier
and
unless
you're
physically
sitting
at
a
terminal
which
I
suppose
as
possible
for
the
most
part,
you're,
probably
going
to
be
accessing
or
remotely
anyway
on
a
windowed
system,
whether
it's
Windows
Mac,
Linux
whatever.
So
this
model
provides
a
lot
of
flexibility
and
then
use
them
all
for
provisioning.
I
want
is
separated
out,
so
you
can
get
an
idea.
What's
going
on,
the
authentication
process
is
the
same,
so
the
user
access
is
open.
Then
I.
Thank
gave
me
a
key
club
now
if
I
request
access
for
an
application.
B
B
That
says
what
this
group
does,
what
you
know
what
information
needs
to
go
into
the
the
dynamic
workflow
things
like
who
the
approver
would
be
or
pervers
description,
information
things
like
that,
and
so
you
log
in
I'll
show
you
this
as
part
of
the
demo
and
you
request
access
that
goes
to
an
approver.
The
approver
says:
okay,
and
it
gets
provisioned
into
this
data
source
here,
we're
using
red
hats,
free,
API,
free,
free
IPA.
B
B
So
have
you
set
all
this
up?
It's
actually
really
easy.
Once
you
get
through
a
few
things,
so,
first
you
need
an
identity
provider,
Key
Club
Dex's
from
core
OS.
You
can
use
google
I've
heard
of
folks
using
Azure
ad
I'm,
actually
going
to
give
you
guys
a
link
I'm
going
to
post
a
bunch
of
links
to
the
meetup
board
after
after
we're
done
with
the
presentation,
one
of
which
will
be
a
nifty
little
utility,
if
using
google,
to
be
able
authenticate
without
a
browser.
B
If
that's
somebody
find
a
port,
but
you
got
pic
an
open,
ID
connect,
identity
provider
make
sure
to
avoid
anybody
who
says
open,
ID
to
or
open
ID
one.
They
have
nothing
to
do
with
open,
ID,
connector
they're,
just
they
share
similar
names
and
branding,
but
they're
completely
different
incompatible
systems.
B
If
you're
going
to
go
with
a
local
identity
provider
like
a
cloak
or
decks
or
one
of
the
others
that
are
out
there,
make
sure
that
your
certificate
is
signed
by
a
CA,
it
doesn't
have
to
be
signed
by
a
commercial
CA
like
thought
or
GoDaddy
or
whatnot,
but
you
cannot
use
a
standalone
self-signed
certificate.
The
way
that
go
laying
is
that
we
actually
narrowed
this
down
to
the
goal.
Lang
issue:
it's
not
a
coup,
bernetta
cific
issue,
where
it
can't
verify
a
self-signed,
sir.
B
B
Up
doing
to
get
my
key
code
server
up,
everything
is
two
additional
API
server
parameters,
and
mostly
quick
starts,
will
not
work.
I
think
I
feel
did
two
questions
alone
in
the
last
48
hours,
asking
about
mini
coop
being
able
to
to
do
SSO
and
are
can't
do
it
right
now,
I
know.
Mini
coop
has
an
open
issue
to
be
able
to
pass
in
server
flags
right
now,
unless
you
compile
it
won't
work
same
is
true
of
like
the
generic
vagrant
image.
I
wasn't
able
to
get
working
with
Google
either.
B
B
To
just
dabble
play
around,
but
you
don't
have
an
existing
lap
to
work
in
I
would
definitely
recommend
that
again
another
link,
I
will
make
sure
to
post.
So
you
have
a
bunch
of
parameters
you
got
to
put
in
here.
These
are
all
pretty
straightforward.
Your
issuer
URL.
This
is
a
URL
to
whoops.
This
is
a
URL
to
your
open,
ID
connect
server
that
will
load
up
all
the
metadata
about
the
server
certificates,
different
URLs
for
token
management
parameters,
stuff
like
that
client
ID.
B
This
is
how
your
client
identifies
itself
to
your
open
ID
connect
identity
provider,
the
username
claim
AKA
attribute.
This
is
the
name
of
the
attribute
ur
claim
inside
of
your
JWT,
that
identifies
you
as
a
person
or
as
a
user
group
claimed
same
idea,
except
what
are
the
lists
groups
that
you
have
and
then
finally,
your
certificate
authority
file
our
backs
similar
setup,
all
the
same,
all
the
same
disclaimers
as
SSO
when
it
comes
to
set
up
here,
but
a
couple
additional
things
that
you
gotta
keep
in
mind.
B
So
one
you
have
to
go
ahead
and
add.
This
are
back
authorization,
Kate,
iov,
1,
alpha
1
to
your
runtime
can
fix
that
turns
it
on
and
you
get
a
turn
on
the
authorization
mode.
You
can
have
multiple
authorizations
I'd
be
very,
very
careful
with
that
design,
more
complicated.
Your
security
is
more
likely,
it
is
to
fall
apart
and
then,
finally,
you
need
a
super
user,
chicken
and
egg
problem.
Coop
first
starts
up:
it
has
no
policy.
B
So
how
do
you,
but
also
our
back-
will
not
allow
you
to
give
policies
that
you
don't
yet
have.
So,
how
does
somebody
who
has
no
policies,
give
policies
that
they
aren't
authorized
to?
Do
you
have
a
stupid
user
and
the
superuser?
This
is
a
user
where
no
policies
apply.
You
can
do
anything.
You
can
use
SSO
for
this.
There
is
a
trick,
though,
where,
if
you
are
using
SSO
and
open
ID
connect,
your
issue
or
URL
needs
to
be
prevented
to
prepend
it
to
the
name
of
your
user.
B
Unless
it's
an
email
address
and
there's
some
discussion
as
to
whether
or
not
that's
an
appropriate
way
to
do
this.
If
you
have
a
certificate
that
you're
using
pre
SSO
setup,
that
is
often
the
easiest
way
to
go,
your
user
would
be
the
common
name,
a
the
common
name,
part
of
the
subject
of
your
certificate.
So,
for
instance,
the
single
instance
vm
that
I
or
vagrant
that
I
use
create
something
see
n
equals
two
bad
men,
not
a
data.
That's
what
the
too
bad
it
comes
from.
A
B
Logging
in
so
I'm
gonna
start
logging
in
with
a
power
user.
Here
just
give
you
an
idea,
and
you
know
everything
just
happened
right.
You
didn't
see
the
fact
that
I
first
went
to
scale
jas
got
bounced
over.
You
obviously
saw
me
putting
my
credentials
and
then
all
the
stuff
behind
the
scenes
that
all
happens
very
very
quickly,
and
so
first
thing
I'm
going
to
show
off
as
I
am
authorized
to,
and
we
look
at
my
user.
B
This
admin
role
is
my
trip,
road,
Eddie's
Admiral
and
that's
what's
giving
me
access
to
the
true
bearnaise
dashboard.
So
if
I
click
on
the
dashboard
and
by
bing
botta
boom
I
am
signed
in
you
know
again.
This
is
all
happening
very
quickly
behind
the
scenes,
you're
not
really
seeing
a
lot
of
the
orchestration
that
has
to
go
into
this
working.
But
now
everything
works
great
and
then
I'm
going
to
go
ahead
and
close.
That
and
I
am
going
to
load
up
my
access
I.
B
Don't
do
it
this
way,
but
you
actually
can
just
drop
this
token
right
into
your
coop.
Config
and
coop
control
will
know
how
to
use
to
it.
Cooper
neighs
will
also
know
to
reload
it
because
these
these
tokens
are
actually
very
short-lived
and
to
give
you
an
idea
as
to
what
that
would
look
like
I'm
just
going
to
go
ahead
and
copy
that
clear,
but
might
help
if
I
knew
how
to
type
so
I'm
just
going
to
go
ahead
and
paste.
B
My
token,
this
is
from
key
cloak
and
you
know
cluster
itself,
so
you
can
see
that
I've
got
everything
up
and
running
and
I'm
going
to
go
directly
to
hear.
So
this
is
my
Cooper
naas
API
server.
Now,
if
I,
try
and
bypass
the
open,
unison
reverse
proxy
and
go
to
the
UI
or
sconce
a
certificates,
don't
work,
obviously,
but
unauthorized.
So
I
can't
bypass
that
proxy,
which
is
really
important.
B
So
if
they're
a
star
wars,
fans,
Star,
Wars
fans
out
there
bonus
points,
if
you
know
who
Jacen
Solo
is
so
you
can
see,
I've
got
a
token
I,
don't
have
my
micronase
dashboard,
that's
because
I
don't
have
access.
If
we
look
at
my
roles
that
admin
roles
not
there,
so
I'm
just
going
to
go
ahead
and
show
you
there's
nothing
up
my
sleeve
I'm
going
to
pull
up
sorry.
B
B
A
B
Don't
have
access
so
even
though
I'm
authenticating
I'm
not
authorized.
So
this
is
going
to
give
me
an
error.
You
can
see
no
idea
what's
going
on,
because
the
are
back
system
stopping.
So
this
is
where
the
management
part
of
identity
management
really
comes
in,
so
I'm
going
to
go
ahead
and
request
access.
Now.
This
is
listing
by
namespace.
I
took
this
from
that
idea,
from
the
way
that
we
did
our
original
integration
with
open
shift,
which
basically
maps
a
namespace
to
a
project,
and
so
I've
actually
got
annotations
in
each
individual
namespace.
B
B
Don't
know
if
you
just
heard
that
being,
but
that
was
actually
me
finding
out.
I
haven't
opened
approval,
so
I'm
going
to
log
in
and
see
I've
got
this
open
approval.
Now
this
is
all
open
source.
So
you
can
download
this
and
start
playing
around
with
this
today,
I'm
going
to
review
the
request,
here's
information
about
me
for
demo
I'm,
going
to
prove,
and
so.
B
What's
going
to
happen
is
open,
unison
is
going
to
say
alright,
I'm
going
to
add
the
admin
attribute
into
the
data
source.
That's
used
to
identify
what
groups
you
remember
of
so
that's
been
done.
Just
to
show
you
I
can
go,
see,
completed
approvals,
workflow
name,
it
was
label,
here's
person
and
it
was
approved
so
I'm
going
to
go
ahead
and
log
out
walk
back
in.
As
my.
B
So
you
can
see
I've
got
access
here,
and
this
is
the
attribute
that's
going
to
get
sent.
This
is
the
attribute
value
that's
going
to
get
set
to
Cooper
Nettie's
so
that
when
I
go
ahead
and
log
in
and
I
try
to
do
something,
it
knows
that
I
am
in
fact
able
to
do
these
things
and
in
fact
I
click
on
now
the
dashboard
here
I
am,
I
am
in
the
dashboard
now
the
dashboard
doesn't
actually
know
who
I
am
curr
benetti's
knows,
but
the
dashboard
itself
doesn't,
and
so
that's
why
there
is
nothing.
B
B
B
B
Cluster
and
so
and
now
you
can
see
I'm
actually
able
to
use
the
Cooper
Nettie's
API.
Now,
access
requests
are
important,
but
the
other
part
of
management
is
turning
off
access,
so
here
I'm
actually
going
to
use
a
very
simple
example
where
I'm
going
to
request
be
removed
in
actuality.
This
would
be
some
kind
of
automated
process
because
my
role
has
changed.
I,
don't
work
here
anymore.
Any
number
of
reasons
why
so
I'm
going
to
log
back
in.
B
And
we
will
see
that
this
again
I've
got
this
open
approval,
so
you
can
see
I've
got
this
request
to
please
remove
or
request
I'm
actually
going
to
deny
the
request
so
this
time,
instead
of
making
sure
that
the
user
has
the
attribute
value
of
admin
I'm
going
to
remove,
and
if
I
come
to
reports
and
I
see
all
provable
is
completed
by
me.
You'll
see
I
actually
rejected
the
user,
and
what
I
can
actually
do
here
is
show
another
report
which
they
are
singly
changelog
and
no
com.
Okay,
now.
B
B
B
And
help
if
I
knew
how
to
type
bring
the
copy
and
paste
and
you'll
see
then
work
I
couldn't
even
get
the
API
version,
because
our
back
was
stopping
me.
So
that
kind
of
shows
you
the
entire
life
cycle.
It
also
shows
you
too,
you
know
I.
I
have
this
ideas,
reference
architecture.
You
know
this
is
all
really
new.
The
trip
Renee's
world.
So
there's
a
lot
of
things
still
to
shake
out
things
like
baseline
roles.
You
know:
where
do
you
start?
That's
usually
the
first
question.
B
Okay,
I
will
start
now
what
here
I
used
a
really
simple
you're:
either
an
admin
or
you're,
not
as
kind
of
people
start
using
this,
I'm
sure
more
is
going
to
shake
out
around
the
types
of
roles
that
that
people
are
going
to
use
and
then
from
project
level.
You
know
some
of
the
stuff
we're
thinking
about
doing
is
making
this
aspect
a
little
bit
easier
to
deploy,
we're
actually
in
the
process
of
building
out
a
MongoDB
virtual
directory,
connector
and
provisioning
connector.
B
If
you're
here
in
the
Washington
DC
area
I'll
be
giving
a
very
similar
talk
at
Google,
Google
def
SDC
here
in
Northern
Virginia
on
the
twenty-fourth
and
25th
tremolo
security
is
going
to
have
a
table
at
coop
con
and
with
a
little
bit
of
luck,
will
also
be
presenting.
So
please
swing
by
on
the
web.
You
can
find
us
at
remote
security
com
or
tremolo
dot,
IO
and
our
open
source
project
on
github,
and
you
know
thank
you
very
much
for
spending
some
time.
I
look
forward
to
your
questions.
A
Alright,
thank
you,
Mark,
ok,
so
and
now
we
are
going
to
get
started
with
the
question
and
answer
part
of
the
presentation.
So
if
you
have
a
question,
please
click
on
chat
and
then
next
to
to
you
should
see
my
name
Johan.
So
just
send
me
a
private
message
with
the
question
and
I
will
read
it
out
loud,
so
go
ahead
and
do
that
now.
A
B
A
B
The
the
ability
to
assert
your
groups
is
great
for
open
ID
connect,
but
if
you're
using
certificate
authentication
not
so
much
because
if
you
think
about
it,
there's
no
way
to
really
do
that
with
the
certificate
and
there
are
but
I'm
painful,
and
so
they
want
there's
a
desire
to
have
an
ability
to
say:
okay.
Well,
if
you
can
assert
what
your
groups
are
great,
but
if
you
can't,
you
know,
have
some
kind
of
way
that
you
could
go
hook
that
up.
B
B
However,
there
is
a
PR
in
place
to
be
able
to
have
a
web
service
for
doing
that.
So
more
verbs
around
here
are
back
policies.
So,
instead
of
saying,
okay,
here's
my
role
binding-
you
can
say-
add
mark
to
this
role
rather
than
you
know,
change
the
role
binding
and
redeploy
very
similar
to
the
way
open
shift.
Does
it
folks
that
are
doing
the
work
in
Cooper
Nettie's,
a
large
side
of
the
percentage
of
them
have
also
done
this
on
openshift.
So
a
lot
of
the
lessons
learned
from
openshift
are
coming
back
into
Cooper
Nettie's.
B
A
B
B
Just
to
make
sure
that
the
folks
who
analyzes
policies
don't
have
a
stroke
looking
at
that,
sometimes
perception
beats
reality,
but
yeah
just
the
API
servers,
basically
just
a
web
server.
So
all
whatever
the
principles
that
you
would
have
when
you're
dealing
with
the
web
server
I
would
apply
to
an
API
server.
So
you
know:
reverse
proxies
are
always
a
good
thing,
adding
more
security
and
authentication
understanding
what
your
threat
environment
is
things
like
that.
B
So
if
I'm
interpreting
that
question
correctly
you're
asking,
not
only
can
you
do
sm
so
into
the
coop
API
server,
but
also
for
apps
running
inside
of
Coober
nettings
yeah,
I
mean
it.
That's
more
apt,
dependent
than
cupones
dependent,
really
open.
Id
connect
is
a
very
well
established
and
it's
been
around
for
a
few
years
now
and
most
open
ID
connect.
B
Identity
providers
are
generic
ID,
daddy
providers,
I'll
support,
open,
ID,
connect
or
sam'l
to,
or
you
know,
pick
your
favorite
new
protocol
that
screw
gets
created
every
few
years,
and
so
that
would
really
be
more
about
your
application.
We
did
a
folks
who
are
well-versed
in
the
open
shift
world.
We
didn't
open
shift
Commons
briefing
about
four
months
ago,
where
we
did
actually
estação
into
WordPress
running,
on
open
shifts
to
the
exact
same
principles
will
exist.
A
A
If
you
like
the
to
talk
and
you
felt
inspired-
and
you
want
to
give
your
own
talk-
it's
very
easy
to
apply
to
do
so.
You
can
just
click
on
that
link
there.
We
might
be
changing
the
method
of
application
soon,
but
for
now,
as
that
will
work
and
your
application
will
be,
will
get
through
mark.
Thank
you
so
much
for
coming.
It
was
a
pleasure
to
have
you
and
I'm
sure
the
folks
enjoy
it
as
well.
