►
From YouTube: Network Policy API Bi-Weekly Meeting for 20201221
Description
Network Policy API Bi-Weekly Meeting for 20201221
A
B
B
C
B
B
And,
and
so
what
happens
is
that
today
in
kubernetes
we
have
a
network
policy
resource
which
is
mainly
developer,
focused
apis.
So
generally,
what
we
have
been
seeing
is
that,
whenever
you
know
some
administrator
oriented
feature
ask
is
made,
we
kind
of
you
know,
push
back
saying
that
the
network
policy
is
meant
for
the
developers,
so
the
evolution
of
network
policy-
you
know
maybe-
and
it
takes
a
while-
and
perhaps
some
of
those
use
cases
are
not
addressed.
B
B
Some
of
the
use
cases
that
we
collected-
and
these
are
not
limited
to
these,
but
you
know
just
something
to
highlight
what
we've
collected
over
you
know
over
months
of
this
activity
that
this
group
has
done.
When
I
said
this
group,
I
mean
network
policy,
api
plus
plus
meetings
that
we've
been
doing
since
the
beginning
of
2020..
B
Let
me
back
up
administrators,
sometimes
or
communities
clusters
sometimes
are
multi-tenants,
so
you
you
want
to
allocate
certain
namespaces
to
you,
know,
tenant
a
and
certain
other
name,
spaces
to
10
and
b
and
so
on
and
so
forth.
Then,
in
that
case
you
know
having
a
a
security
guardrail-
or
you
know,
as
a
security
aspect,
that
these
name
spaces
should
not
overlap.
But
you
know
these
traffic
from
name
space
for
tenant
a
should
not
cross
into
traffic
or
distant
for
name,
space
or
tenant
b.
B
It
can
be
achieved
with
kubernetes
cluster
network,
sorry
with
kubernetes
network
policies,
it's
just
that
it
needs
to
be
repeated
in
every
name
space,
and
on
top
of
that
you
know
the
developers
or
the
tenants
have
the
ability
to
override
these
network
policies
by
adding
a
namespace
selector
in
there
to
from,
and
then
you
kind
of
do
not
guarantee
these
things
in
certain
cases
for
every
kubernetes
cluster,
an
administrator
may
want
to.
You
know,
allow
certain
traffic
by
default
or,
as
a
baseline.
B
You
know
most
pods
that
come
up
or
most
services
that
come
up.
They
would
want
to
talk
to
the
cube
dns
or
core
dns
pods
that
exist
in
your
kubernetes
cluster
and
they
probably
reside
in
one
name
space
and
not
probably
spread
across
every
name
spaces.
So
these
kind
of
baseline
rules
need
to
needs
to
be
enforced.
You
know
so
just
guarantee
that
certain
connectivity
is
available
in
certain
cases
you
want
to
restrict.
B
You
know
certain
ciders,
which
you
know.
Probably
the
workers
should
not
talk
to,
and
perhaps
in
certain
cases
they
want
certain
ciders
to
be
accessible.
So
again,
this
can
be
done
with
kubernetes
set
of
policies.
It's
just
that
with.
As
a
cluster
administrator,
you
can
give
that
guarantee
to
every
name
space
that
comes
up
dynamically
instead
of
you
know,
having
to
you
know,
do
some
sort
of
a
additional
tooling.
B
On
top
of
your
cluster,
we
have
also
seen
certain
use
cases
where
you
you
need
to
manipulate
the
traffic
in
your
kubernetes
cluster,
in
a
way
that
you
only
want
to
allow
traffic
ingressing
or
regressing
certain
name
spaces
through
some
firewall
gateways
or
security
gateways
that
exist
in
your
community
in
your
cluster.
Now.
The
intention
here
is
not
to
do
manipulation
of
that
traffic.
You
know,
because
that
is
kind
of
outside
the
scope
of
a
of
a
network
policy.
This
this.
B
So
temporarily,
you
may
want
to
enforce
a
a
a
rule
that
denies
this
particular
traffic,
so
so
that
you
can,
you
know,
reevaluate
your
cluster
and
and
take
necessary
precautions.
So
so
you
need
a
way
to
explicitly
deny
certain
traffic
either
egressing
or
ingressing
to
your
services
or
your
parts.
So
these
are
some
of
the
use
cases
that
that
we
collected
over
time-
and
you
know,
if
you
guys
have
any
question-
feel
free
to
unmute
yourself
and
ask.
B
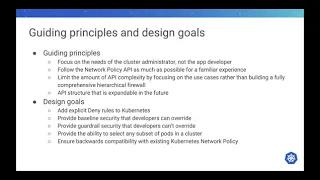
These
were
certain
guiding
principles
that
we
kind
of
tried
to
adhere
to
and
those
those
were
the
design
goals
that
we
wanted
to
achieve
at
the
end
of
this
proposal.
So
so
our
our
guiding
principle
was
that
we
need
to
focus
on
the
needs
of
a
cluster
administrator
and
not
the
app
developer.
That
doesn't
mean
that
the
app
developers
requests
are
features
that
that
are
necessary
for
a
developer
are
ignored.
We,
you
know
this.
B
This
particular
group,
the
network
policy
subgroup,
does
look
at
all
those
use
cases,
and
you
know
anything
that
is
developer
focused.
We
can
try
to
evolve
the
existing
kubernetes
network
policy
resource
for
for
those
use
cases,
but
for
for
the
cluster
scope
policies,
we
are
going
to
focus
on
the
needs
of
an
administrator.
B
We
also
want
to
ensure
that
we
follow
the
network
policy
api
as
much
as
possible
to
to
to
give
a
familiar
experience
to
users.
You
know
anyone,
who's
who's,
used,
network
policy,
apis
or
written
policies
should
not
have
a
tough
time.
Writing
cluster
scope
policies.
The
transitions
should
be
should
be
smooth,
and
you
know,
of
course
you
know
as
an
administrator
focus
policies.
The
cluster
scope
policy
is
going
to
be
slightly
more
complex
than
the
kubernetes
network
policy,
but
our
idea
was
to
keep
it.
B
B
That
is
that
the
api
can,
you
know,
because
you
know,
as
as
the
administrator
focused
use
cases,
can
get
complex
a
lot
more
requirements
can
come
through
for
for
this
particular
resource
it
is,
it
can
get
complex
quite
quite
early,
so
we
wanted
to
simplify
some
of
that.
So
you
know
there
were
multiple
proposals
that
we
could
have
gone
forward
with
and,
of
course,
this
they
also
remain
as
alternate
proposals,
because
you
know,
as
part
of
the
coming
up
with
a
proposal
for
cluster
scope
policy.
B
B
So
there
is
some
prior
art,
so
we
looked
at
all
the
three
specs
and
one
one
of
the
things
that
we
we
tried
to
avoid
was
the
the
ability
to
assign
priorities
to
policies,
because
it
may
make
make
writing
policies
a
little
bit
more
tedious.
You
know,
because
you
now
need
to
remember
or
rely
on
the
ordering
of
policies,
so
we
try
to
keep
it
a
little
simpler
and
you
know
not
make
that
complex.
B
But,
of
course,
if,
if
we
deem
that
now,
our
current
proposal
does
not
satisfy
all
the
use
cases
or
you
know
if,
if
if
we
think
that
the
ordering
base
or
priority
base
proposal,
makes
more
sense
and
is
more,
you
know
more
perfect
for
this
perfect
fit
for
this
particular
resource.
We
can
always
go
back
to
the
drawing
board
and
and
and
work
up
a
solution
based
on
that,
but
hopefully
we
can
find
that
this
proposal
solves
all
use
cases
and
we
can
move
forward
in
this
fashion.
B
We
also
wanted
to
ensure
that
the
the
apis
that
we
introduce
is
expandable
in
future.
We
want
to
make
sure
that
if
there
are
new
fields
to
be
added
to
a
clusterscope
policy,
it
should
not,
you
know,
be
difficult
or
it
should
not
really
warrant
a
v2
or
a
v3.
Perhaps
it
should
be
additive
to
the
existing
proposal,
so
so
so
those
are
some
of
the
principles
that
we
wanted
to
stick
to,
and
hopefully
we
can.
D
One
question
on
the
yeah
on
the
principles:
are
we
going
into
the
kind
of
like
designing
the
api?
Are
we
gonna
have
a
stance
on
how
lenient
or
how
aggressive
we're
gonna
be
around
compatibility?
So,
like
is
the
first
iteration
gonna
be
well.
I
I
guess
like
we
have
to
start
alpha,
but
like
are
we
gonna
go?
Are
we
gonna
create
the
apis
alpha,
knowing
that
we're
gonna
probably
break
something
or
are
we
gonna
be
alpha,
but
still
be
pretty
conservative
around
breaking
users
going
into
beta.
B
So
I
think
the
idea
would
be
that
before
we
go
to
beta,
we
have
have
a
have
a
good
amount
of
use
cases
satisfied.
You
know
I'll
talk
about
some
goals
and
non-goals
and-
and
I
think
that
would
be
a
good
point
to
talk
about
like
how
the
versioning
might
be
able
to
be.
We
can
we
can
do
that,
but
but
the
idea
is
that
once
we
go
ga
it
might,
you
know
it
will
just
be
quite
similar
to
how
kubernetes
network
policies
are.
B
You
know
once
we
want
to
add,
let's
say
the
name
space
by
name.
We
had.
We
had
that
issue
over
here
that
you
know
we
are
introducing
a
new
field.
It
changes
the
semantics,
so
we
will
try
to
conserve
as
much
as
possible,
but
you
know
there
are
no
guarantees
that
you
know
future
use
cases
that
may
come
up.
We
might
be
able
to
solve
today
itself,
but
but
at
least
I
feel
that
you
know
we
should
have
like.
C
Right
abhishek,
this
is
when
I
just
to
at
your
point
right.
I
think
you
you
make
a
very
valid
part.
I
think
I
just
out
of
curiosity.
I
think
our
definition
of
a
alpha
api
means
we
I
mean
we
hopefully
try
not
to
break
it
too
much,
but
at
least
that
allows
us
to
break
right.
I
think
once
we
go
into
beta,
I
think,
is
when
we
want
to
keep
the
api
more
stable.
C
D
Yeah,
I
think
that's
the
general
understanding
and
or
at
least
it's
the
rule,
but,
like
you
know,
we
we
we
can
still.
We
can
still
make
statements
or
still
try
to
say,
like
people
have
built
alpha
apis,
but
they
treat
them
like
beta
apis
because
they
know
that
they
want
early
adopters
and
they
don't
want
to
break
those
adapters.
So
just
kind
of
staying
out
like
saying
from
the
start
like
this
is
an
alpha
api,
we're
going
to
break
it
versus
this
is
an
alpha
api.
D
C
And
I
think
I
agree
with
what
abhishek
was
saying.
I
think
we
should
use
actually
the
first
couple
iterations
of
v1
to
the
alpha
version.
To
see
I
mean
what
feedback
we're
getting
in
the
field
and
then
based
on
that,
if
we
decide
not
to
break
it
great,
if
we
decide
to
break
it,
you
know,
unfortunately
we
will
have
to
okay.
So
we
are
on
an
agreement.
E
B
E
B
Agree
with
what
young
said,
we,
I
think,
definitely
need
the
support
of
cni
providers,
because
you
know
at
the
end
of
the
day,
a
resource.
A
network
policy
related
resource
like
cluster
policy
without
any
implementation,
is
probably
not
going
to
be
used
at
all.
So
it
is
definitely
very
important
for
us
to
have
at
least
the
top
cni
providers
pack,
this
proposal,
so
hopefully,
once
we,
you
know,
move
this
proposal
to
the
sig
network,
and
you
know
once
we
are
ready
to
publish
the
alpha
apis.
B
Okay,
so
if
there
are
no
more
questions,
I'll
move
forward,
so
yeah
as
so
those
are
the
guiding
principles
we
also
so,
as
part
of
that,
you
know
we
kind
of
ended
up
with
certain
design
goals
for
this
particular
proposal,
which
is,
I
think,
we
need
a
explicit
deny
rules
which
is
unlikely
in
the
kubernetes
network
policy.
We
don't
have
a
have
such
action,
they're
all
whitelist
rules,
so
we
do.
We
do
need
a
new
action
for
dinner.
B
We
want
to
provide
baseline
security.
The
cluster
administrator
should
be
able
to
define
some
sort
of
a
defaulting
rules
or
baseline
rules
for
its
cluster.
You
know
at
least
some
guarantees
for
the
kubernetes
cluster,
but
they
can
be
overridden
by
the
developers,
so
we
should
leave
the
baseline
rules
can
be.
You
know,
overwritten
by
developers
using
kubernetes
network
policy.
B
A
very
good
example
of
this
is
the
namespace
isolation,
where
you
know,
as
as
as
a
baseline,
whenever
a
new
name
space
comes
in
the
intra
name,
space
traffic
is
allowed
and
the
inter
name
space
traffic
is
denied
and
that's
a
guarantee
that
we
give,
and
perhaps
there
is
a
tenant
who
owns
more
than
one
namespace
and
he
or
she
may
want
to
open
up
traffic
between
their
namespaces,
so
they
should
be
allowed
to
do
that.
So
that's
that's
one
of
the
goal.
B
The
other
goal
is
that
a
cluster
administrator
perhaps
does
not
want
their
developers
to
override
some
of
those
rules.
So
in
this
case
the
admin
wants
strict
enforcement
of
those
security
policies
and
kubernetes
network
policies
should
not
be
able
to
override
those
those
rules.
So
those
you
know
they
seem
very
conflicting
goals,
but
I
think
we
can
demonstrate
that
we
should
we
shall
be
able
to
overcome
or
we
should
be
able
to
address
both
of
these
use
cases.
B
B
And
finally,
we
also
want
to
ensure
that
there
is
compatibility
with
the
existing
capabilities
network
policy.
What
we
mean
by
this
statement
is
that
we
do
not
intend
to
change
any
any
inherent
qualities
of
kubernetes
network
policy.
We
don't
plan
to
override
its
behavior,
or
rather
we
don't
plan
to
change
its
behavior
or
the
expectation.
B
Of
course,
when
you
have
security
policies
defined
at
multiple
layers
like
at
a
cluster
policy
and
a
network
policy,
the
overall
effect
on
the
cluster
will
be
different,
but
that
doesn't
mean
that
we
are
changing
the
meaning
of
writing
certain
communities
network
policies.
So
so
the
idea
is
that
both
cluster
scope,
policy
and
community
centric
policy
coexist.
B
These
are
something
that
can
be
addressed
as
part
of
the
first
iteration
is
just
that:
it's
not
the
goal
of
today's
proposal,
because
in
our
initial
proposal,
what
we
wanted
to
tackle
was
the
we
wanted
to
tackle
the
precedence
and
the
complementary
behavior
between
network
policy
and
cluster
scope
policies.
We
wanted
to
tackle
the
goals
that
we
just
previously
mentioned,
but
there
are
other
use.
Cases
like
you
know,
for
example
the
node
policies.
B
You
know
that's
something
that
is
also
applicable
for
the
crystal
cluster
scope
policies,
but
it
can
be
debated
that
it
can
also
be
applicable
to
kubernetes
network
policy.
So
the
idea
is
that
we
can
have
separate
discussions
for
such
such
use
cases
and
see
whether
they
can
be
solved
for
both
the
resources
and
if,
yes,
then
we
inherit
it
from
that
proposal.
If
not,
then
we'll
certainly
try
to
tackle
it.
B
B
I
know
it
is
very
some
of
the
use
cases.
Some
of
the
requests
that
were
made
on
kubernetes
issues
were
around
audit
logging.
For
you
know,
traffic
that
occurs
in
a
cluster.
It's
an
it's
a
useful
feature.
Perhaps
we
can
follow
up
on
this
error.
Reporting
is
something
also
that
is,
you
know,
quite
arsenal,
because
you
know
sometimes
users
do
not
understand
whether
a
policy
was
realized
successfully
or
not,
and
I
think
the
same
this
this
this.
This
point
is
valid
for
both
the
kubernetes
network
policy
and
the
cluster
scope
policy.
B
B
So
maybe
we
can
keep
those
discussions
in
those
threads
so
and
then
we
can
again
inherit
them
and
again,
in
the
end,
we
don't
want
to
solve
a
placement
volume
policy
for
every
possible
permutation.
I
think
what
we
want
to
convey
here
is
that
there
are
multiple
ways
to
you
know:
do
cluster
scope,
policies,
for
example,
you
can
also
do
h
hierarchical
policies
like
tiered
way
of
policy
doing
policy
enforcement.
That's
not
the
goal
here
today.
B
It
is
certainly
something
that
might
be
useful
because
some
network
providers
already
do
implement
and
provide
that
solution.
But
if,
if
it
is
necessary,
then
maybe
we
can
take
a
look,
but
at
least
in
today's
proposal
it's
not
part
of
the
scope.
It's
not
in
the
scope
any
deal
breaker
here
or
this
sounds
good.
D
C
C
So
if
you
use
the
same
language
or
the
grammar,
I
think
it
will
be
a
lot
easier
for
people
to
comprehend,
because
with
now
with
the
cluster
network
policy,
for
for
better
or
worse,
it
has
gotten
a
little
bit
more
complex
with
in
terms
of
like
you
know,
with
the
the
prioritization
of
the
cluster
network
policy
or
network
policy
and
default
allow
or
the
baseline
allow.
So
all
these
things
get
so
this
this
would
be
useful.
So
now
what
you're
suggesting,
if
I'm?
C
D
I
I'm
just
saying
like
like
I,
I
think
we
should
always
start
with
what's
familiar
like.
I
think
that
makes
sense
yeah.
I
guess
all
I'm
saying
is
like
we
shouldn't
put
something
off
the
table
because
it's
too
different
from
existing
apis.
Like
all
I'm
saying
is,
like
you
know,
we
should.
We
should
consider
different
ways
of
expressing
things,
even
if
they
seem
different
at
first
yeah,
but
I
definitely
agree
with
starting
and
meaning
towards
apis.
That
are,
you
know,
familiar
with
to
users
and
already
existing
for
sure
yeah.
I
think.
A
Probably
the
point
here
is
also
that
we
we
have
like
here
the
opportunity
to
change
what
we
think
that's
bad
into
the
old
api
right.
So
we
can.
We
can
use
this
moment
to
like
implementing
the
clusterscopic
network
policy
that
oh,
we
are
not
going
to
deal
with
with
priorities,
because
we
don't
have
them
in
kubernetes
network
policy
and
nice.
I
also
think
that
we
shouldn't
like
remove
this
from
from
the
table,
just
because
that's
not
compliant
with
the
kubernetes
network
policy.
D
Yeah,
I
agree,
I
think
it's
a
good
time,
there's
a
lot
of
confusing
parts
like
for
people
just
hopping
into
network
policy.
I
think
there's
ways
we
can
improve
it
and
this
could
kind
of
be
a
road
map
to
do
that.
So
we
definitely
shouldn't
restrict
ourselves
just
because
it's
already
defined
one
way.
C
So
hey
abhishek,
I
had
like
one
more
point
I
wanted
to
make.
So
if
I
heard
what
ricardo
said
and
what
I
understood
so
he's,
I
just
want
to
get
a
clarification.
Are
we
saying
that,
coming
up
with
the
breaking
change
for
a
network
policy,
a
new
version
of
the
network
policy
which
takes
into
account
the
prioritization
deny
allow
the
cluster
level
at
the
network
level?
A
Table,
I
don't
think
we
should
break
how
how
the
network
policy
works,
but
I
think
that
we
we
don't
need
to
stick
with
the
like,
follow
the
network
policy
api
as
much
as
possible
for
a
farm
for
a
familiar
experience.
I
don't
think
we
should
remove
anything
from
the
table
because
that's
not
like
the
experience
from
the
network
policy
api.
A
A
A
So
I
think
that
what
what
andre
was
saying
here
and
what
what
what
what
I
agree
with
that,
it's
that
we
we
don't
need
to
stick
with
the
follow
the
network
policy
as
much
as
possible,
because
we
have
like
here
the
opportunity
to
change
how
it
works
and
and
and
figure
out
what
what
the
cluster
I
mean.
They
expect
from
the
network
policy
and
add
as
much
as
feature
as
possible
without
sticking
with
the
old
network
policy,
and
maybe
later
we
can
like
discuss
if
network
policy.
Api
also
needs
some
sort
of
syntax
evolution.
D
But
but
I
do
think
that,
like
what's
already
what
abhishek
already
mentioned
is
like
a
good
starting
point,
so
I
don't
think
we
need
to
change
anything
right
now.
I'm
just
saying
you
know
like
before
we
go
to
beta
if
we
find
that
there's
a
way
to
collapse
like
10
fields
into
one
field
and
like
we
want
to
do
that,
like
we
shouldn't
not
do
that,
because
only
if
the
only
reason
is
like
this
is
too
different
from
network
policy.
We're
not
going
to
do
it.
B
Oh,
no,
I
think
it's
pretty.
I
think
we
should
probably
word
it
differently
in
the
sense
that
it's
nice
to
have
this
design
goal.
But,
of
course,
if,
like
I
think
in
previously,
when
I
mentioned
that
when
we
looked
at
prior
art
like
calico,
andrea
and
psyllium
for
their
policies,
they
are
slightly
different
than
the
kubernetes.
That.
C
B
B
You
know
if,
if
that's
a
broad
agreement
in
the
community
for
that,
but
but
I
think
to
as
a
starting
point,
I
think
it
makes
more
sense
to
start
something
simple
and
which
is
more
familiar,
and
but
I
think
one
thing
that
we
should
definitely
not
try
to
do
is
that
we
should
not
break
the
kubernetes
network
policies,
meaning
today,
for
example,
you
know
the
cluster
native
policy
is
not
not
being
written
to
replace
the
community
network
policy.
It's
it's
meant
to
be
a
complimentary
to
it.
B
C
No,
I
think,
you're
right.
I
think,
but
this
is
what
we
discussed
here
right,
like
I
think,
for
the
cluster
network
policy,
we'll
keep
it
as
a
separate
resource,
because
I
think
sufficiently
it's
the
the
the
elements
of
the
cluster
network
policy
are
sufficiently
different,
that
it
begs
its
own
crd
compared
to
like
you,
know,
merging
it
with
the
network
policy
without,
like
you
know,
creating
an
entirely
new.
B
We
are
not
going
to
do
that
because
we
we
can
derive
the
same
thing
using
the
ingress
rules
or
egress
rules
that
are
being
defined
so
so
we
are
trying
to
in
our
proposal.
You
will
see
that
shortly
that
you
know
we
have
tried
to
not
use
some
of
those
confusing
factors,
but
but
also
try
to
have
a
similar
experience.
So
so
it's
not
like
we
are
adding.
You
know
new
selectors
or
anything
they're
still
working
with
the
pod
selector
or
namespace
selector,
which
are
label
selectors.
B
All
right,
okay,
so
I
think
we
went
over
this
and
then
some
of
the
non-goals
so
yeah
so
before
without
further
I
mean
you
know
we
can
move
into
the
proposal
aspect.
So
first,
I
wanted
to
talk
about.
You
know
more
on
the
technical
side,
like
you
know
how
the
api
types
looks
like.
I
think.
Probably
this
is
a
good
way
to
understand
the
some
of
the
fields,
and
then
we
will
look
at
the
like
a
sample
yaml
resource
for
cluster
network
policy
with
all
the
fields
that
we
can.
B
B
B
B
B
Now,
if
we
look
at
the
ingress
rule
or
an
egress
rule
structure
there
again,
you
will
see
a
little
bit
of
similarity
that
you
have
a
ports
field
where
you
you
we
talk
about
that
this
particular
rule
is,
should
be
matched
against
the
sports
and
protocol,
and
you
know
we
also,
you
know,
get
the
port
range
for
free,
because
it
will
be
by
then
implemented
in
the
network
policy
port.
So
so
we
should
be
able
to
specify
a
port
or
portrait
and
then
similar
to
the
kubernetes
network
policy.
B
It
also
has
a
from
section
and
a
two
section
from
for
the
ingress
rules
and
two
for
the
egress
rules.
This
essentially
tells
you
that
these
per
set
of
applied
two
parts
can
either
talk
to
these
set
of
pods
or
can
accept
traffic
from
these.
So
the
semantics
is
very
similar
to
the
kubernetes
network
policy.
So
no
change
so
far.
B
The
new
field
that
you
see
here
is
an
action
you
know,
which
is
of
type
something
called
rule
action.
The
action
field
is
is
pretty
important,
is
one
for
you
know
for
one
that
it
is
not
available
in
the
kubernetes
network
policy,
because
you
know
all
kubernetes
network
policy
rules
are
whitelist
tools
only,
but
we
do
want
to
have
the
ability
to
deny
a
certain
traffic.
So
that's
why
we
introduced
this
new
field
action,
not
only
that
the
action
also
determines
the
precedence
of
the
rule
as
compared
to
a
kubernetes
network
policies.
B
B
For
example,
let's
revisit
what
a
kubernetes
network
policy
does
when
a
kubernetes
network
policy
selects
certain
pause
in
part
selector
and
has
certain
whitelist
rules.
If
the
pod
is
selected
by
that
part
selector,
then
the
traffic
is
allowed
only
by
those
whitelist
rules
that
are
available
to
ingress
and
egress.
B
B
The
other
thing
that
then,
is
also
worth
to
note
is
that
an
allow
action
will
always
precede
any
kubernetes
network
policy
rules.
So
basically
the
allow
action
will
be
evaluated
first
and
it
is
basically
think
of
it
like
if
you
have
multiple
cluster
network
policies,
you
you
know,
each
of
those
cluster
policies
may
have
one
or
more
allow
actions.
B
Isolation
or
you
know
the
opposite
of
isolation
that
occurs
for
a
deny
rule,
so
the
rule
will
be
evaluated
as
is
again
similar
to
allow
you
know
all
deny
rules.
Multiple
deny
rules
cannot
conflict
with
each
other,
so
so
they
are
also
additive
and,
and
they
similar
to
the
allowed
rules,
will
also
precede
the
cluster,
the
kubernetes
network
policies,
so
the
deny
rules
will
be
evaluated
first
and
then
all
the
capabilities
network
policy
rules
if
the
traffic
did
not
match
any
of
the
deny
rules.
B
Now
you
may
say
that
you
know
there
can
be
a
conflict
between
an
allow
rule
and
a
denial
and
that
that
is
certainly
possible.
You
may
have
the
same
selector,
you
may
have
the
same
port
and
you
may
have
the
same
to
and
from
for
for
multiple
rules,
and
one
of
the
action
is
says,
allow
the
other
says
tonight.
Now
that's
a
conflicting.
B
Those
are
conflicting
rules.
In
that
case
we
say
that
deny
always
deny
always
wins
so
now,
if
we
think
about
the
priority
the
precedence
we
have,
the
deny
the
aggregated
deny
rules
at
the
top.
The
aggregated
allow
rules
after
that
and
then
once
all
of
that
is
evaluated
and
no
traffic
is
matching,
then
we
go
to
the
kubernetes
network
policies
and
then
we
see
how
the
kubernetes
network
policies.
You
know
the
semantics
remains
the
same.
B
So
essentially,
this
lies
at
the
bottom
of
the
of
the
precedence
priority
so
and
the
other
difference
is,
or
rather
other
similarity
with
the
kubernetes
network
policy
or
for
a
baseline,
allow
rule
is
that
it
is
similar
to
a
kubernetes
network
policy.
Allow
rule
in
that
that
any
applied
to
is
selected
and
has
a
baseline
allow
in
its
rule
it
it
it
will
be
only
allowed
if
there
exists
a
baseline,
allow
rule.
If
not,
then
those
workloads
get
isolated.
B
C
D
B
Yeah,
just
just
a
quick
response
to
that
is
that
we
started
off
with
the
default
allow
and
I
think,
just
last
week
we
changed
it
to
baseline,
but
we
can.
We
can
talk
about
it
in
follow-ups,
okay,
yeah
yeah,
and
so
this
is
how
the
the
rules
are
or
the
api
types
for
the
scope
resource
cluster
for
resource.
But
this
is
how
a
sample
cluster
network
policy
resource
may
look
like
any
yaml
form.
B
You
know.
Essentially,
you
know
this.
You
will
see
that
there
is
no
name
space
here,
so
the
name
is
a
sample
clustering
policy
and
it
applies
to
a
namespace
selector,
which
is
empty,
which
essentially
is
similar
to
how
kubernetes
semantics
is
for
the
namespace
selector.
An
empty
name.
Selector
selects
everything.
So
here
this
will
be
applied
to
all
the
namespaces
that
come
up
in
the
cluster.
So
as
a
sample
here
you
will
see
we
have
dmz
cube
system,
these
few
name
spaces
that
exist.
The
policy
applies
to
all
of
them.
B
B
It
is
also
allowed
to
talk
to
this
particular
site,
so
maybe
there's
an
internal
sider
that
cluster
he
needs
to
be
able
to
talk
to.
So
it
explicitly
allows
traffic
to
this
cycle
for
all
the
namespaces
and
it
it
is
allowing
as
a
baseline
rule.
That
is,
you
know
if
there
is
no
network
policy
overriding
this,
it
is
allowing
these
name
spaces
to
talk
to
the
the
core
dns
pods
or
the
coding
spot
that
exists
in
the
cube
system
namespace.
B
B
So
this
is
the
sample
cluster
network
policy
resource
and
I
think,
like
I
mentioned,
I
think
this
is
going
to
span
multiple
sessions.
Probably
this
is
a
good
stopping
point.
I
know
you
know.
I
know
I'm
sure
that
there
are
a
lot
of
questions
that
may
come
up
and
you
know
as
you
as
we
go
move
forward.
You
will
see
a
lot
of
examples
that
we
have
here
for
every.
D
So
one
quick
clarifying
question
on
on
the
last
slide
there,
so
there's
a
deny
rule
for
all
namespaces,
except
for
istio,
egress
and
food
system.
So
if
a
pot
did
want
to
egress
out
to
those
name
spaces,
is
it
implied
that
there's
an
allow
rule
in
the
namespace
network
policy
in
that
namespace
or
it
doesn't.
B
B
D
Ask
that
question
again:
yeah!
So
there's
a
there's,
the
there's
a
deny
rule.
The
first
egress
two
is
a
deny
for
all
namespaces,
except
for
sdo
egress
and
cube
system
right
so
yeah.
So
if
I,
if
a
pod
didn't
want
to,
if
I
wanted
to
allow
a
pod
to
egress
traffic
to
those
namespaces,
is
it
assumed
that
I
have
a
namespace
network
policy
that
allows
it.
B
No,
no,
that's
not
necessary,
because
you
know-
and
here
what
it
says
like
I
said,
the
deny
and
the
allowables
are,
as
is
so.
It's
just
saying
that
we
do
not
have
a
deny
rule
for
is
to
egress
or
acute
system.
Now,
if
you
want
to
deny
that,
then
maybe
you
need
to
write
a
new
policy
or
something
or
a
kubernetes
network
policy
to
deny
that
explicitly.
B
If
not,
then
it
just
water
falls
through
and
it
will
see
whether
any
kubernetes
network
policy
denies
or
disallows
this
kind
of
a
traffic.
If
not,
then
it
kind
of
flows
through
the
baseline
allow
rules.
If
not,
then
eventually
it
allows
the
traffic.
So
so
you
don't
need
to
create
a
kubernetes
network
policy
to
allow
that
is
this.
This
cluster
network
policy
does
not
explicitly
deny
that.
A
B
Then
you
would
change
this
to
deny
and
you
know
all
deny
rules
are
additive,
because
you
know
you
won't
have
those
conflicts
and
you
always
have
the
denials
too
without
so
you
could
do
that
and
you
could
also
do
a
deny
for
an
ip
block
cider
with
an
accept
which
essentially
would
mean
that
you
don't
have
a
deny
rule
for
that.
Accept
block
it's
just
that
this
policy
does
not
create
any
rules,
special
rules
for
that
except
law,
so
similar
semantics
as
what
we
have
for
kubernetes.
C
C
I
think
abhishek,
I
think
you
may
want
to
point
out
that
it
was
never
the
intention
that
it
was
you're
going
to
conclude
this
proposal
in
like
one
session.
This
is
going
to
be
like
a
and
a
lot
of
people
are
out
this
week
like
at
least
from
folks
that
I
know
so.
Maybe
I
think
what
we
should
do
is
like
slide
that
shake
and
yang
put
together.
I
think
it's
we
get
an
opportunity
to
go
through
that
and
then
in
the
next
meeting,
whenever
we
have
a
start,
we
go
through.
A
C
B
I
think
we
have
good
content
to
cover
those
aspects,
so
I
don't
know
when
we
will
meet
next,
but
perhaps
it's
some.
I
expect
that
it'll
be
sometime
in
jan,
so
maybe
maybe
for
the
next
meeting.
We
go
back
through
this
recording
and
and
come
back
with.
You
know
questions
because
I'm
sure
there's
going
to
be
a
lot
of
digesting
to
be.
A
C
I
don't
mind
attending
ricardo,
because
this
is
pandemic.
We
have
pretty
strict
lockdown,
so
I
don't
haven't,
got
any
plans
so
we're
all
gonna
be
stuck
at
home,
so
I
might
as
well
join
in.
But
having
said
that,
it
doesn't
mean
others
don't
have
plans.
So
if
you're
going
to
have
it-
and
you
can
count
me-
we
can,
we
can.
A
We
can
we
can
start
discussing.
I
saw
your
proposal
about
this
service
selector,
so
we
can
use
the
next
meeting
to
just
discuss
yeah.
We
can
maybe
like
okay,
that's
a
good
point,
because
I
don't
think
we
are
going
to
have
like
enough
people
to
discuss
about
the
cluster
scope
network
policy.
So
we
can.
We
can
leave
those
two
or
three
weeks
for
people
to
take
a
look
into
the
video
recordings
also
and
this
live
deck
and
so
on.
So
we
can
start
discussing
about
about
that
services.
Selector
sounds
good.
