►
From YouTube: Service APIs Meeting (EMEA Friendly Time) 20200312
Description
No description was provided for this meeting.
If this is YOUR meeting, an easy way to fix this is to add a description to your video, wherever mtngs.io found it (probably YouTube).
C
B
C
C
B
B
You
know
just
along
with
some
other
ideas
that
have
been
bubbling
around
in
my
head
over
the
last
several
weeks,
just
to
kind
of
make
sure
we
have
a
foundation
here.
I
wanted
to
call
out
the
definitions,
gateway
class,
doesn't
change
gateway,
doesn't
change
you'll,
see
now
virtual
host
instead
of
a
route,
although
the
definition
of
a
virtual
host
is
very
similar,
almost
identical
to
a
route
there's
also
something
called
a
TLS
config
request.
B
This
is
a
resource
that
defines
requesting
a
TLS
configuration
to
apply
to
a
virtual
host
and
then
one
other
definition
that
I
wanted
to
make
sure
that
I
call
out.
That's
been
introduced
as
a
concept
of
a
domain
similar
to
a
DNS
domain.
It
defines
a
realm
of
administrative
autonomy,
that's
serviced
by
a
gateway,
and
you
know
here
are
the
the
key
concepts
that
I'm
introducing
one
of
the
first
one
is
gateway,
no
longer
specifies
a
route
Association,
it's
now
reversed
and
we
no
longer
have
a
route.
B
So
it's
a
virtual
host
that
specifies
the
Gateway
that
it
wishes
to
be
hosted
by
a
gateway.
No
longer
specifies
a
listener.
Tls
configuration
so
upon
approval
by
cluster
ops,
a
TLS
configuration
is
bound
or
applied
to
a
virtual
host,
and
it's
reflected
in
status
of
that
virtual
host,
a
gateway
can
restrict
virtual
host
bindings
based
on
namespace.
C
C
This
is
interesting
because
I
think
we
have
use
cases
in
both
sides,
so
it
may
still
be
valuable
in
terms
of
reference
referencing
and
our
back
model
that
you
actually
have
to
have
a
way
to
specify
a
relationship
from
gateway
to
route
it.
Because,
though
we
meeting
with
folks,
we
wrote
down
a
couple
of
years
cases
where
so
I
see
that
this
one
you,
you
basically
pick
the
upwards
path.
Yes,.
C
B
C
So
number
three:
that's
because
we
had
a
meeting
with
Jordan
and
I.
Think
Nick
you
were
there
and
Rob.
You
were
there
and
basically,
in
kind
of
discussing
our
trying
to
make
wedge
everything
in
our
back
permission
model
versus
doing
it
things
on
the
main
stage.
It
was
actually
recommended
to
do
things
on
the
main
space,
so
it
sort
of
the
lines
just
generally
other
discussions
as
well.
Yeah.
B
And
what
I'll
do
what
I'm
gonna
get
to
is
is
kind
of
a
sample
workflow,
because
you
know
I
just
tried
to
put
myself
okay
day-to-day
operations.
What
is
this
like
right
and
one
of
the
things
I
thought
is
like?
Okay,
if
we've
got
you
know,
there's
in
my
mind,
there's
gonna
be
less
gateways
and
virtual
hosts
and
imagine
always
having
into
the
cluster
operator,
add
the
virtual
host
to
the
gateway.
Will
you
know
if
we
flip
it
around
and
say?
B
Well,
there's
gonna
be
less
association
of
a
virtual
host
to
a
gateway,
and
maybe
that
makes
sense
and
again
I
Illustrated,
in
kind
of
an
example,
detail
workflow
that
I
look
forward
to
good
number
and
feedback
on
okay.
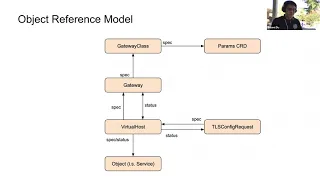
This.
This
is
just
kind
of
a
visual
representation
of
the
model.
Right
we
know,
gateways
reference,
you
know
are
part
of
a
gateway
class
right
and
here
I
represent
multiple
gateways
that
have
you
know
similar
responsibilities.
B
Similar
configurations
are
part
of
the
same
weight
class
and
and
then
there's
that
relationship
between
the
gateways
and
the
virtual
host,
and
you
see
here
Wow
well,
this
looks
a
little
different
right
virtual
host
right.
If
we
think
of
virtualizing
a
host
right,
a
host
can
deal
with
all
sorts
of
type
of
protocols
in
traffic,
and
then
we
want
that
virtual
host
to
to
act
upon
that
traffic
right.
If
it's
HTTP
traffic
all
right.
B
Well,
here's
some
rules
to
do
something
with
that
same
with
TLS
the
same
with
TCP,
and
we
all
you
know
in
this
example.
It's
those
rules
are
referencing
a
service,
but
this
could
be
really
any
in
cluster
object
and
again,
I
just
want
to
have
kind
of
a
visual
representation
of
them
out
of
the
model
and
here's
right.
How
did
these.
C
Different
one
question
is
that
when
you
do
it
this
way,
the
there's
an
advantage
in
that
you
just
have
one
there's
a
disadvantage
in
that
you
kind
of
have
to
is
basically
a
union
type.
It
also
is
a
given
the
way
gold
type
works.
It's
going
to
be
a
closed
type,
so
you
can't.
You
can't,
for
example,
support
something
easily
that
doesn't
exist
here
and
necessarily
we
would
need
to
be
all-encompassing
when
we
go
and
define
each
of
these,
what
I
guess
those
were
used
to
be
well,
it's
something
we
discuss
in.
B
C
B
There's
multiple
types
in
and
do
me
a
favor
and
just
kind
of
hold
on
to
that
a
few
slides
down
the
way.
You're
gonna,
see
detailed
examples
and
then
because
I
was
thinking
about
you
bringing
up
that
concern
in
the
past
when
we
touched
on
the
subject
and
I
think
I
worked
around
it,
but
if
I
didn't
then
I
would
definitely
like
to
be
aware
of
that.
B
So
again,
just
a
visual
representation
of
conceptually.
What
what
I'm
thinking
here-
and
this
is
how
these
different
objects
refer
to
one
another.
We
already
know
gateway
class
references
that
the
parameter
is
the
CRD
gateway
references
gateway
class.
You
know
difference
here
is
now
a
virtual
host
in
spec
is
referencing,
a
gateway
that
it
wants
to
attach
to,
and
then
you
see,
status
kind
of
has
arrows
in
both
directions
where
I
think
it
makes
sense
from
a
virtual
host
standpoint,
we
look
at
status.
We
want
to
see
what
gateway
you
know
is
it.
B
Is
it
attached
to
the
Gateway,
or
was
there
some
kind
of
problem
attaching
to
that
gateway?
Let's
reflect
that
in
status
same
with
vice-versa,
a
gateway.
We
would
want
to
see
all
the
virtual
hosts
that
are
attached
to
that
gateway.
You
know
and
then
the
other
new
part
this
TLS
config
request.
You
know
this
object,
we
create
and
we
specify
here's
a
TLS
config
that
I
want
here's,
the
virtual
that
I
want
to
associate
this
TLS
config
to,
and
you
see
that
it's
not
part
of
virtual
host.
B
C
B
B
A
B
B
Is
it
isn't?
It
is
a
string,
that's
meant
to
represent
domains
that
host
names.
Virtual
host
host
names
are
part
of
so
and
I'm
gonna
dive
into
it
again
here
in
a
little
more
detail
is
the
reason
that
I
introduced
it
and,
back
of
my
mind,
I,
was
thinking.
How
do
we
prevent
kind
of
don't
host
name
conflict
right
where
virtual
host
a
wants?
A
example.com
virtual
host
B
wants
a
dot
example.com.
B
How
do
we
make
sure
that
there's
not
that
conflict
there,
and
so
this
was
just
kind
of
an
idea
that
I
thought
okay,
whenever
a
virtual
host
attaches
to
the
gateway
and
the
Gateway
says:
okay,
my
domain
or
domains,
one
of
my
domains
is
example.com.
All
virtual
hosts
that
attach
to
it
have
to
be
of
example.com.
So.
C
B
D
B
Thinking
is
that
we
could
include
wild
cards
in
the
domain
so
that
virtual
host
could
be
right.
Food
sub
domain,
example.com
right
and
we
specified
the
domain
within
the
Gateway
as
star
example.com.
Whereas
if
we
say
we
know
women
want
host
names
of
example.com,
then
we
would
specify
example.com.
Okay,
how.
B
We're
good
to
go
right,
there's
no!
There's
no
conflict,
the
new
virtual
host
comes
Ron,
says
well,
no
I
want
foo.example.com
gateway,
essentially
does
not
allow
that
virtual
host
to
bind
to
it
and
the
status
of
that
virtual
host
would
reflect.
You
know
non
unique.
You
know
the
status
would
be
unavailable.
Message
would
be
non
unique
host.
A
I
think
that
the
the
I
think
that
the
this
it
feels
to
me,
dannion,
like
you're,
designing
this
one
for
for
a
very
good
use
case,
which
is
the
the
the
cluster
admin
has
tight
control
over
it.
It
has
has
like
control
so
yeah
and
I'm
using
cluster
admin
to
mean
the
person
responsible
for
the
Gateway,
not
a
higher
up
on,
and
you
know
the
and
this
this
is
similar
to
what
we
did
with
HP
proxy.
We
had
a
similar
problem,
so
yeah
I
do
have
plenty
of
thoughts
about
this.
A
B
B
Let's
see
we
already
talked
about
you
know
using
namespaces
to
prevent
you
know
virtual
host
bindings
from
a
namespace
standpoint.
You
see
here.
Tcp
is
only
supported
listener
protocol.
What
I
was
thinking
here
with
protocol
TCP
or
UDP
if
we
want
to
in
the
future,
support
UDP
load
balancing
per
se
and
again
we're
not
associating
a
route
from
the
Gateway
but
based
on
feedback
that
we
could
change
that
as
well.
So
yeah.
C
B
Yeah,
what
we'll
talk
more
more
about
it
and
again
these
are
I.
Don't
maybe
I
missed
something
here,
so
so
yeah
we
need.
This
is
just
kind
of
de
foster
the
discussion
and
dive
down
into
some
of
these
areas
and
refine
them
remove
them.
What
have
you-
but
you
know
the
virtual
host
here-
you
see
kind
of
an
example.
Virtual
host
in
the
right
hand,
side
right,
so
it
binds
to
a
gateway.
B
B
B
If
the
sni
differs
from
the
actual
host
name,
whereas
HTTP
match
we're
gonna
be
able
to
match
on
headers
on
paths
on
all
sorts
of
stuff,
a
tcp
match
an
example
could
be
hey.
You
know
certain
source
IPS
I
want
to
just
you
know:
do
layer
for
load,
balancing
and
based
on
a
source.
Ip
range
I'm,
gonna
Ford,
that
TCP
traffic
to
a
specific
back-end
right.
C
I
have
to
I'm
curious,
though,
because
you
can
do
the
same
with
the
route,
but
for
a
per
protocol
now
you've
combined
it
into
one,
is
the
desire
to
basically
reject
that
whole
virtual
host.
Yes,
somehow
invalid
between
the
protocol
statements,
because
you
can
still
multiple
virtual
hosts
like
you-
can
basically
still
produce
the
same
kind
of
configuration
from
the
previous.
C
You
know
by
just
having
all
your
HTTP
thing
into
one
virtual
host
and
then
attaching
a
TLS
into
another
virtual
host
and
then
the
PCP
into
another
virtual
host
and
then
binding
all
three
to
the
same
gateway,
I.
Guess
what
I'm
trying
to
get
at
it's
like.
What
is
that
thing
that
you
got
out
of
doing
it?
This
way,
I
think.
B
It's
from
my
perspective,
it
was
kind
of
starting
with
the
idea
that
a
virtual
host
I
equate
that
to
like
a
normal
host
and
that
a
normal
host
can
deal
with
different
protocols.
So
it's
just
kind
of
a
mental
model
when
I
think
of
a
host
I,
don't
think
of
a
host
as
oh,
you
know
you
only
you
know,
you
only
know
one
type
of
protocol,
and
so
that
was
kind
of
my
thinking
for
organizing
or
structuring
the
data.
This
way
is
just
from
the
mental
model
of
a
host
to
a
virtual
host
yeah.
B
And
here's
here's
the
example
for
you
right.
So
you
know:
we've
got
the
gateway.
Foo,
alright,
are
to
all
our
different
listeners
and
and
the
domains
that
it's
you
know,
authoritative
for
right.
We've
got
the
virtual
host
foo
bar
right,
and
you
see
that
it's
referencing,
the
foo
gateway
and
it
has
a
host
name
of
foo.example.com.
We're
not
gonna,
have
an
issue
with
that,
because
it
it
you
know
it's
referencing
gateway,
foo
and
it's
a
host
name
within
the
domain
of
gateway,
foo
and
then
for
TLS.
We
say
alright
for
any
type
of
TLS
traffic.
C
B
C
B
As
a
developer,
I
would
go
ahead
and,
depending
on
how
how
my
Enterprises
is
organized
right,
if,
if
TLS
management
is
a
responsibility
of
cluster
ops,
so
maybe
cluster
odds
is
responsible
for
creating
it
or
I
created
as
a
developer
right
and
I
reference
it.
But
what
I
would
see
am
I
in
my
virtual
host
is
I
would
see
that
the
virtual
host
44
TLS
is
is
basically
not
bound
or
whatever
kind
of
status
message.
C
B
Could
be
sec,
ops
could
be
cluster,
ops
could
be
a
developer
right
and
so
I
think.
The
key
with
this
request
is
that
when
we,
when
it's
not
directly
bound
to
a
gateway
or
directly
bound
to
a
router
or
virtual
host,
but
it's
it's
a
separate
object.
We
can
output
workflows
in
that
manner
that
support
these
different
use
cases
right,
because
if
we
say
TLS
is
part
of
the
Gateway,
then
we
know
that
the
developers
can't
configure
TLS
right
in
this
example.
If
we
say
okay,
you
know
developers
are
allowed
to
create
the
request.
B
They
go
ahead
and
say:
okay,
here's
the
certificate,
here's
all
the
configuration
and
then
I'm
gonna
reference
it,
but
until
it
gets
approved
by
cluster
ops,
you
know
the
TLS.
All
this
TLS
stuff
within
the
virtual
host
is
not
bound
right
and
I'm
gonna
walk
through
the
details
of
of
kind
of
an
example
workflow.
So
you
could
kind
of
see
what
I'm
talking
about
in
more
detail.
Yeah.
C
Would
there
be
a
situation
where
we
would
necessarily
want
to
separate
those
the
permissions
on
modifying
and
dealing
with
the
Gateway
versus
just
the
TLS
piece
of
it?
You
get
one
thing
like
the
reason
we
get
it
as
we
wanted
to
have
that
separation,
but
we
should
maybe
your
workflow
will
answer
this
question
but
like.
Why
would
why
not
just
give
on
that
that
the
v8
way.
B
All
right,
because
so
couple
thoughts
is
here
right.
This
model,
this
model
I'm
getting
I'm,
providing
flexibility
for
different
kinds
of
work-
clothes,
okay,
and
if,
if
my
enterprise
says
yep,
you
know
developers
are
allowed
to
create
requests,
then
you
know
my
are
back
rule
for
developers.
I'm
gonna,
allow
create
read,
update
blah
blah
blah
the
Telus
config
request
right
and.
D
B
B
Thought
about
I
thought
about
it,
and
it's
like
I
feel
like
the
only
way
that
we
can
make
TLS
configuration
management
flexible
enough
is
by
having
some
type
of
resource
and
there's
some
details.
I'd
like
to
kind
of
share
about
the
TLS
config
request
that
I
think
are
very
interesting
as
well.
Yeah
I'm,
curious.
C
B
Thinking
is
is
if
we,
if
we
do
that,
then
to
me
a
couple
things
as
we
might
as
well:
just
go
back
to
a
single
resource
model,
and
then,
secondly,
is
if
we,
if
we
do
that,
then
now
that
developer
has
full
control
over
a
gateway
and
what,
if
we
don't
want
a
developer
to
add
another
listener,
add
more
domains
along
with
any
other
kind
of
properties
that
we
that
we
add
to
a
gateway
in
the
future.
So
it
is
kind
of
limits
that
scope
to
just
the
TLS
configuration
yeah.
It
might
be.
B
Yeah
yeah
and
again
I
mean
this
is
just
you
know.
I
I
feel
like
I've,
gotten
to
the
point
where
I'm,
like
okay
I've,
really
thought
through
these
different
ideas.
I
formulated
them
gone
through
different
use
cases
and
organize
the
information
and
share
it
with
everyone
and
lets.
You
know
is
this
something
that
we
can
say
wow.
You
know
this
makes
sense.
That
makes
sense,
or
let's
pick
it
apart-
whatever
it
might
be,
but
that's
kind
of
what
the
purpose
of
this
presentations
were
so
virtual
host.
Now
we
virtual
host
supports
HTTP
rules.
B
You
know
here's
kind
of
the
the
details
or
an
example
right
where
we
got
the
Gateway
on
one
hand
on
the
right
side,
the
virtual
host
and
a
lot
very
simple
example.
Right
where
we're
saying
hey
you
know,
I
want
to
take
any
traffic
for
food
example:
comm
go
through
the
food
gateway
and
if
that
traffic
comes
in
via
the
insecure
listener,
so
ie
port,
80
right
I'm
gonna
match
my
path.
If
it's
the
my
path
path
forward
it
over
to
my
in
cluster
service,
my
HTTP
service,
oh.
C
B
I
think
it's
because
I
use
this
kind
of
same
example
for
a
few
different
use
cases.
So
for
this
particular
slide
you
could
I
mean
nothing's
using
the
secure
right,
those
virtual
hoses
and
using
the
secure
right.
If,
for
example,
if
if
a
request
comes
in
for
food
at
example.com
and
it's
over
TLS
well,
foo.example.com
has
has
doesn't
know
what
to
do
at
illa.
B
So
if
that
handshakes,
never
going
to
be
established
right
so
really
in
reality
like
if
anything
comes
in
via
just
plain
TCP
on
this
port
I
have
no
TCP
rule
here,
so
it's
gonna
be
dropped,
so
in
reality
this
is
the
only
listener
that's
being
used
by
this
virtual
host,
but
I
think
to
your
question.
I
use
this
the
same
listeners
for
other
examples,
presentation.
B
C
It
does
illustrate
a
good
thing,
though,
that
in
in
sort
of
you
know,
are
actually
a
little
bit
of
flexibility
when
people
go
to
implement
this,
how
to
model
it,
and
if
we
we
figure
out
like
hey,
it's
recommended
that
P
typical
many
people
are
gonna.
Do
it
one
way
or
the
other?
We
should
figure
out.
C
B
C
Tpp,
what
that
hostname
means?
Is
it
just
like
a
token
like
what?
Why
would
why
is
that
DCP
foo.example.com,
because
tcp
doesn't
have
such
a
thing?
I
guess
yeah.
So
the
other.
You
worry
a
bit
curious.
What
what
we
would
kind
of
like
what
they?
What
would
be
the
comments
during
for
hostname
with
respect
to
TCP?
Is
it
simply
that,
oh,
it
must
match
one
of
the
domain
in
gateway.
B
C
Is
a
CCDA
frame?
Yeah!
That's
that's
where
I
would
see
it
is
that
it
is
for
external
integration
as
sort
of
a
token
that
could
be
consumed.
We
should,
for
example,
external
DNS,
but
we
just
have
to
make
sure
that
it
doesn't.
It
is
still
sensible,
I
guess,
but
it's
I
I
can
see
uses
for
it.
I'm
just
curious.
What
you
were
thinking
would
so.
B
That
was
kind
of
my
thinking
is
like
okay.
Either
we
use
it
to
make
sure
that
there's
a
virtual
host
you
know,
is
from
this
domain.
The
other
thing
I
was
thinking
as
you
mentioned,
was
well
what
if
we
can
actually
resolve
right
and
when
we
say
okay
this,
although
we
can't
see
an
HTTP
header
or
don't
have
you
know
an
sni
server
name
to
match
on
you
know,
can
we
there's
still
going
to
be
a
destination,
IP
right
and
can?
And
if
that
doesn't
resolve
to
foo.example.com,
do
we
consider
that
invalid
right?
So
right.
C
That
the
one
inconsistency
is
that
for
HTTP,
you
can
check
that
the
match
rules
actually
match
that
hostname,
but
for
TCP
you
have
no
guarantee
and
then,
if
you're,
going
to
use
the
domain
part
of
the
Gateway
as
a
way
to
basically
say
hey,
this
gateway
can
only
serve
this
set
of
stuff.
That
is
less
like
there's
no
connection
there
with
the
TCP
we'd
have
to
think
about
how
that
fits
in
with
how
like
external
DNS
would
need
it,
and
maybe
we
can
make
some
guarantee
there.
B
C
You
get
that
because,
if
you're
using
on
the
Gateway
you're
using
the
list
of
domains,
that's
like
hey
I'm,
going
to
restrict
this
gateway
to
this
set
of
domain.
When
you
attach
a
virtual
host
in
that
virtual
host
is
HTTP
virtual
host.
That
host
name
actually
has
a
meaning,
because
you
can,
for
example,
enforce
that
that
given
virtual
host
is
self
consistent
with
its
host
name
right.
C
Someone
could
just
write
two
example
comm
just
to
make
it
line
up
and
then
attach
themselves
that
gateway,
so
in
some
sense
that
that
domains
on
that
gateway
is
not,
for
some
protocols
might
not
be
enforcing
anything.
It's
just
a
way
to
kind
of
match
in
dumping,
which
is
from
a
semantics
standpoint,
a
little
bit.
C
B
C
C
People
have
been
asking
about
external
domain
and
how
that
would
work.
We'd
have
to
work
through
the
details
to
see
if
this
is
something
that
makes
sense
for
workloads,
but
they
would
also
motivate
putting
hostname
for
something
like
TCP,
because
ordinarily
hostname
and
TCP
it's
like
kind
of
meaningless
great.
B
B
B
Okay,
we're
not
talking
about
two
different
people
like
a
developer
or
an
operator,
but
we're
talking
two
different
components
of
the
system:
right
is:
how
do
we
create
a
cluster
and
make
sure
that
couplets
can
trust
the
API
server
vice
versa
and
they
could
communicate,
and
so
I
I
looked
at
that
and
and
said
wow.
You
know
I
feel
like
this
could
almost
apply
to
what
we
would.
You
know
the
problem
that
we're
having
as
well.
C
B
High
level
work
flow
right,
hey
I'm
in
props
and
nothing
changes
here,
I
create
my
gateway
class
I
create
my
my
CRD
for
the
parameters
of
the
gateway
class
cluster,
ops,
right
I'm,
creating
a
gateway
here
in
this
example,
I
create
multiple
gateways,
and
you
know
before
I
create
those
I'd.
You
know,
I'm
doing
a
read
on
gateway
class
and
see
gateway.
Class
foo
bars
exist.
B
B
B
But
you
know
there
could
be
other
tooling.
That
may
be
implementers
also
provide
a
controller
that
maybe
will
automatically
approve
time
and
so
on
and
so
forth
and
again
status
is
you
know
whether
it's
been
approved,
denied
or
what-have-you
is
surfaced
and
status?
So,
let's
go
through
a
more
detailed
example
right,
so
I'm,
infra,
ops,
I
create
my
gateway
class,
along
with
the
CR
d4
or
the
custom
resource
for
what
I'm
referencing
them
with
him.
My
gateway
class
for
the
parameters
gateway.
D
B
Yep
yep
yeah
cluster
office,
now
I'm
cluster
ops,
right
I
go
ahead
and
I
did
a
you
know:
did
a
coup,
cuddle,
get
gateway,
classes,
I,
see
ones
out
there.
Okay,
great
it.
You
know,
I'm
gonna
go
ahead
now
create
my
gateway
and
I
accidentally
forgot
to
put
class
and
reference
to
gateway
class.
So
I'll
update
this
slide
with
that
and
now
I'm
didn't
alter
right.
B
Right
so
we're
referencing
it
in
spec
right
and
until
the
TLS
configure
presses
approved
in
status.
We
would
see
that
hey
some
type
of
status
message
that
gets
surfaced
at
saying,
hey,
TLS
is
inoperable
because
my
TLS
config
has
yet
to
be
approved.
Alright,
the
other
key
point
of
this
is
take
a
look
at
the
TLS
config,
the
termination
policies
edge
right
and
so
because
it's
edge,
this
block
basically
says
okay,
I'm
ETA,
LS
connection
that
comes
through
I'm,
going
to
process
it.
B
It
has
termination
edge,
and
so
now
I
can
deal
with
that
connection
as
HTTP,
because
I
completed
my
handshake,
based
on
the
certificate
that
was
associated
to
this
TLS
config
and
now
I'm
going
to
be
dealing
since
its
termination
edge
I
can
deal
with
it
as
HTTP
traffic,
I'm
gonna
match
a
particular
path
and
then
forward
it
onto
a
service
within
my
cluster.
That's
an
HTTP
service,
Oh.
C
B
C
B
That's
going
to
depend
on:
are
we
terminating
it
at
the
edge
or
is
it
it
passed
through
right?
So
let's
say
this
was
passed
through
and
I
have
some
example.
Some
examples
here
that
may
be
so.
If,
if
this
was
passed
through,
then
we're
basically
saying
okay,
there
is
no
HTTP
blocked
for
this
traffic
because
it's
gonna
be
passed
through
a
steel
us
all
the
way
to
the
back
end,
so
there's
very
limited
things:
I
can
do
with
it.
So,
within
this
TLS
block,
the
matches
that
I
can
do
are
very
minimal
right.
B
Maybe
we
expose
a
match
s
and
I
if
we
want
to
go
ahead
and
specify
which
of
you
know
which
s
ni
server,
name
that
we're
gonna
match
on
this
is
when
this
example
is
pretty
easy,
because
we
only
have
a
single
host
name.
So
by
default,
we're
saying:
hey
the
s
ni
that
we're
looking
for
the
server
name
is
this
hosting,
but
we
can
match
on
to
that.
We,
you
know,
there's
very
few
things
and
again.
B
Some
of
the
examples
I
provide
to
help
illustrate
the
idea,
but
in
this
example,
I'm
saying
terminated
at
the
edge
right
do
the
TLS
handshake
based
on
this
configuration,
and
now
that
that's
done,
what
do
we
want
to
do
from
HTTP
standpoint?
We
want
to
go
ahead
and
say
ole
based
on
my
path
forward
it
to
this
service.
All
right.
We
could
have
other
HTTP
matches
and
do
all
the
standard
HD
meant
match,
filter
action
stuff.
But
let's.
C
B
So
the
dead
persona
right
we
create
this
virtual
host
and
now
the
devs
like
okay,
goes
on
lunch,
break
and
says
all
right.
You
know
waiting
for
a
cluster
ops
to
do
their
thing
right.
Well,
waz,
on
lunch,
break
cluster
ops
went
ahead
and
said
you
know,
could
cuddle
Telus?
Can
you
know
crew
cuddle
get
you
know,
TLS
configs,
all
namespaces,
oh
I,
see
that
there's
one
that
exists.
Let
me
look
at
it.
Oh,
it
doesn't
have
a
self-signed
certificate
check,
so
it
matches
our
security
policy
from
a
corporate
standpoint.
B
C
I
see
interesting,
okay,
yeah,
I'm
curious.
This
is
an
interesting
way
to
approach.
It
is
to
kind
of
have
the
layers
of
protocols
in
your
setup.
Let's
say
you
were
doing
TLS
termination
but
PCP
on
the
back
end.
Would
that
come
out
as
pls
:
match
config
and
then
forward
to
or
would
it
be,
TLS
match
config
and
then
TTP
:
for
do
well.
B
Here's
two
examples
for
you:
Bowie
all
right,
so
here's
our
gateway
with
a
bunch
of
listeners,
different
ports,
all
TCP
we've
got
our
TLS
config
request.
Okay,
let's
say
it's
already
been
approved
right
and
you
see
that
we've
got
a
single
virtual
host
tie
that's
attached
to
this
gateway
over
here
and
it's
it's
the
virtual
host
as
a
single
host
name
right
and
we're
saying:
okay,
when
TLS
comes
through
we're
gonna
match
this,
my
TLS
config
right,
so
the
certificates,
that's
we're.
B
Gonna
use
a
certificate,
we're
gonna
use
all
these
TLS
settings
here,
we're
gonna,
say:
hey
match
listener:
foo,
that's
gonna,
be
another
match
that
we're
gonna
do
right
and
the
reason
being
is
because
you
know
I'm
exposing
foo.example.com
on
different
ports.
So
I
want
to
make
sure
that
this
block
here
you
know,
is
for
food
example.com
coming
in
office
foo
listener,
which
is
for
three
and
now
that
I
go
ahead
and
take
that
traffic.
All
right
tell
us
is
good
to
go
now:
let's
go
ahead
and
match
the
HTTP
path.
B
Alright
now
we
got
another
host
though,
and
bar
got
example.com
alright
and
again
it's
TLS,
but
it's
TCP
within
TLS
right,
so
we're
using
the
same
TLS
config.
Why?
Because
all
these
other
settings
are
the
same,
and
let's
say
this
certificate
is
a
wild-card
search
to
get
for
both
bar.
You
know
for
a
start
at
example.com
right,
but
I'm
saying
match
listener
bar
right,
so
TCP
for
4,
3,
4
3
s
coming
in
it's
gonna
match.
You
know
here
and
then
I'm
gonna
say
hey.
C
B
And
if
this
was
straight
TCP
that
I'm
expecting
to
come
in
I'm
this
bar
listener
right,
then
I
could
just
get
rid
of
all
this
TLS
here
and
just
say:
hey
TCP,
you
know
do
whatever
match.
Filter
afford
that
I
want
to
do
right
and
obviously
the
TCP
match,
fill
filter
for
Zoar,
know
much
lesser
verbose
and
what
we
can
do
with
HTTP.
C
B
Ok
and
I
just
kind
of
jumped
into
slide
here,
because
because
your
question
silly
right
so
just
to
kind
of
step
back
again
right,
I
came
back
from
lunch.
Cluster
ops
approved
me
instead
of
denying
me
since
I
didn't
use
a
self-signed,
cert
right
and
now
I
say:
okay
did
Roger
over
in
cluster
Rob's.
Do
what
he
said
he
was
gonna.
Do
I
knew
that
I
didn't
use
a
self-signed
certificate.
B
D
D
B
D
B
C
C
Yeah,
like
the
question
in
my
mind,
is:
would
we
want
to
oh
the
other
thing
that
this
does
is
lets?
You
have
create
something
that
you
can
reference
so
it'd
be
the
higher
permission.
Person
can
create
something
that
can
be
referenced,
but
you
may
not
have
permission
to
create
it,
the
normal
reference,
or
course
that
new,
yes,.
B
B
I
mean
we've
got,
we've
got
different.
We've
got
different
workflows
that
we
need
to
support
right.
We
need
to
support
the
simple
mom-and-pop
cluster.
Where
someone
does
it
all,
we
need
to
support
kind
of
a
mid-level
where
hey
we
got
cluster
ops,
dealing
with
gateway,
devs
dealing
with
you
know,
with
virtual
hosts
and
depending
on
their
policy.
They
say
you
know,
developers
you
manage
to
tell
us.
Well,
we
can
do
that
right,
Oh
nope!
B
B
You
know
maybe
I
stopped
here
and
for
those
that
are
interested
like
there's
different
kind
of
implement
a
to
different
implementation
options,
and
if
we,
let
me
just
kind
of
get
out
of
here,
yeah
so
I've
got
a
handful
of
slides
on
each
implementation
option
and
then,
if
we
jump
over
to
kind
of
epic
use,
these
are
just
for
kind
of
questions.
That
I
was
asking
myself,
you
know
and
then
just
like
some
ideas
for
next
steps.
Right,
let's,
let's
digest
review
comment,
everyone
should
be
able
to
comment
on
the
slides
resolve
questions.
B
There
are
some
questions
that
you
know
that
I
have
that
are
in
the
back
of
my
mind,
as
I
put,
you
know,
put
this
together
and
then
bowi
as
I
mentioned.
You
know
at
the
beginning
of
the
presentation.
Is
you
know?
We
then
get
this
to
a
point
where
we
say
wow.
This
is
this.
Is
we
want
to
carry
this
forward?
D
C
C
It's
for
like
governing
references,
but
like
I
can
reference
to
you.
You
can
reference
it
and
then
our
back
obviously
is
the
mechanism
for
like
who
can
create
something.
So
those
are
actually
two
different
permission
models
that
it
looks
like
you're
already
using
it
we'll
just
we
just
got
more
clarity
that
those
were
like
the
recommended
path
and
a
lot
of
the.
If
you
had
them,
you
think.
B
C
B
It
just
kept
going
and
going
and
going
so
I
appreciate
everyone's
time.
I,
don't
didn't
mean
to
monopolize
the
whole
meeting
and
I
will
actually
be
out
tomorrow
and
Friday,
so
that
should
give
everyone
time
to
digest
and
I'm
gonna
try
to
to
join
the
call
tomorrow.
In
case
we
do
come
back
to
this
with
any
more
discussion,
but
if
not
I'll
make
sure
that
circle
back
with
anyone
that
wants
to
talk
more.
