►
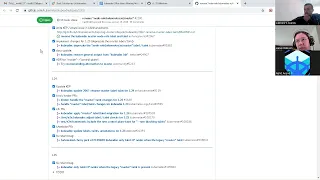
From YouTube: SIG Cluster Lifecycle - kubeadm office hours 2022-05-11
A
B
A
A
A
So,
let's
see
what
we
have
first
migrate
users
away
from
cri
socket
paths
that
don't
have
your
url
schema
now
a
scheme.
Now
this
is
the
problem
here
is
that
qbm
historically
didn't
add
the
unix
prefix
to
paths
and
it's
actually
deprecated
in
the
couplet
to
not
have
this
and
we
started
migrating
cubadm
to
do
this
properly
in
124
we
added
some
changes
in
125
is
the
next
one.
A
I
don't
expect
breaking
changes,
but
in
the
future,
which
may
be
like
126,
we
might
turn
our
warnings
for
the
lack
of
unix
urls
unix
prefix
url
schemes,
two
errors,
which
means
that
users
have
to
adapt,
and
that
would
be
a
like
an
actual
required
item
in
the
release
laws
for
sure
if
this
hasn't
been
decided.
I
ideally
we
collect
feedback
for
changes
like
that,
but
yeah.
This
is.
This
is
the
first
one.
A
A
A
Also
dogs
were
adopted,
but
basically,
who
wants
to
continue
using
docker
basically
has
to
now
use
the
cri
drd.
This
is
the
mirantis
owned
cri
shim
around
docker
docker
engine
to
be
more
precise,
and
basically
that's
yeah.
That's
what
we
have
to
do
with
125
for
some
cleanups.
Maybe
some
dog
update
box
updates
again,
but
probably
not
only
cleanups,.
A
B
A
You
know,
even
in
my
company
vmware,
I
saw
that
people
just
don't
see
the
notifications
that
we
send
so
it's
it's
very
difficult
to
sometimes
communicate
some
of
these
changes
again.
This
particular
change
was
driven
by
the
cncf,
remove
all
instances
of
the
master
word
inside
the
kubernetes
project.
A
A
A
A
C
A
A
We
are
renaming
the
complete
config
xy
version
config
map,
and
it's
currently
a
feature
gate
alpha
passed
beta
passed
in
124
and
now
we
are
125
ga
and
there
are
a
number
of
action
items
this
is
assigned
to
me
again.
I
will
probably
handle
this
as
early
as
possible
in
the
cycle
to
get
sufficient
entrance
signal
test
signal
to
modify
cube
spray
quest
api.
You
know
possible
consumers
that
might
be
affected
by
this
cost.
A
It
will
be
actually
in
124.
I
have
not
seen
any
reports
about
this
yet
so
this
means
that
we,
probably
our
action
item
in
the
release
notes,
is
has
seen
you
know
sufficient
visibility,
although,
like
I
said
earlier,
sometimes
users
just
don't
see
what
we
do
but
yeah.
Basically,
this
this
change
is
mostly
affecting
users
that
fiddle
with
the
cobra
config
map
users,
that
don't
care
will
not
be
affected
in
cubanium
upgrade
will
handle
it
transparently
for
them.
A
A
The
next
one
is
run
control
plane
as
long
some
history
in
122
we
added
a
feature
which
is
alpha
experimental
feature:
gate
to
support
manual
handling
of
linux
users
in
groups
on
a
linux
host
such
as
that
we
can
assign
users
in
groups
to
containers
that
cube,
adm,
deploys
and
static
ports,
and
the
thing
here
is
that
we
added
it
and
then
we
realized
hey.
But
there
is
this
new
feature
that
is
coming:
kubernetes
called
username
spaces.
A
So
we
had
some
discussion,
but
actually
I
would
argue
that
it's
insufficient
discussion,
whether
we
should
put
the
cubadiem
manual
handling
feature
or
hold
until
there
is
development
in
the
username
spaces
feature
that
is
coming
next.
So
potentially
we
can
stop
using
our
alpha
feature
and
start
using
the
username
spaces
feature
which
is
much
nicer.
A
It's
like
a
field
in
the
pod
spec
and
you
just
just
magically
sandbox
the
containers
that
you
care
about
and
our
feature
is
kind
of
manual,
and
it
requires
some
boilerplate
manual,
parsing
of
user
and
group
files
on
linux,
which
works
as
long
as
your
linux.
Distribution
is
standardized,
but
there's
always
this
linux
distro.
That
is
rogue.
B
A
Decides
to
do
stuff
the
way
they
want
to,
but
yeah.
I
think
that,
and
I've
been
discussing
with
fabricio,
who
is
one
of
the
costa
rican
maintenance,
that
it
might
be
a
really
good
idea
to
wait
and
see
what
happens
with
user
namespace
support
and
then
decide
what
we're
going
to
do
with
our
alpha
feature.
Gate
maybe
move
more
to
beta
or
entirely
deprecated
in
favor
of
the
user.
Namespaces.
A
Switch
the
default
image
registered
to
register
case
dot
io,
so
the
story
here
is
that
there's
a
special
interest
group
in
kubernetes
that
is
migrating
all
of
the
google
owned
infrastructure
in
kubernetes
to
cncf,
something
that
is
more
community-owned,
and
one
of
these
changes
is
that
we
are
migrating.
The
dns
for
the
registry
of
container
images
used
by
cube
admin
a
lot
of
users
out
there
that,
basically,
you
know,
pull
something
that
is
from
kids
gcr.io.
A
The
new
target
is
going
to
be
registry,
dots
case
number
and
the
plan
is
pretty
nice
as
far
as
I
know,
because
we
are
basically
introducing
this
as
a
redirect
to
the
old
domain
and
at
some
point
we're
just
swapping
the
old
domain
to
be
a
redirect
to
the
new
one,
which
means
that
users
will
hopefully
never
see
any
blips
any
blockages
around
us.
It's
just
going
to
be
a
transparent
switch
for
cubic
m.
In
particular,
we
just
have
to
modify
all
the
cases
where
we
have.
A
A
A
Okay!
This
is
also
signed
to
me.
Yeah,
there's
a
there
was
an
announcement
that
hd
3.5
x,
which
is
basically
zero.
One
and
two
have
a
critical
bug
where
there's
potential
for
cross
member
data,
corruption
and
the
solution
for
that
was
to
the
best
solution,
for
that
was
just
to
release
a
new
patch
version
of
hcd,
and
this
patch
of
hcd
is
already
out
there.
A
But
cuba
gaming
in
the
meantime
added
this
flag,
which
is
to
prevent
block
hd
member
startup.
If
it
detects
data
detects
data
corruption,
but
in
125
what
we
want
to
do
is
we
have
to
upgrade
qbim
and
kubernetes
3.353
and
they
also
backboard
the
change
to
all
the
releases,
all
the
releases
that
have
three
point
x
as
the
version
that
they
use-
and
I
I
have
a
actually
I
think
I
have
cherry
picks
for
that,
but
it's
still
they
are
still
not
merged
yeah.
A
A
A
A
A
It's
it
has
been.
It
has
been
something
that
you
want
for
four
years,
pretty
much
it's
it's
difficult.
It
requires
a
lot
of
cleanup
and
basically
the
story
is
to
avoid
the
user
to
break
down
the
cubanium
upgrade
process
into
the
phases
that
it
has.
Currently
they
are
not
exposed,
mostly
because
it's
the
code
is
such
such
a
mess.
It's
complicated,
it
works,
but
it
needs
a
lot
of
cleanup
and
cleanup
is
pretty
much
the
prerequisite
here
to
be
able
to
expose
the
phases.
A
A
This
one
I'm
actually
willing
to
move
this
to
next.
It's
just
nice
to
have,
but
I
don't
think
is
you
know,
I
don't
think
we're
going
to
be
able
to
complete
this.
The
t
of
the
r
is
that
we
want
to
to
be
able
to
create
a
new
client
in
kubernetes.
There
is
a
wrapper
around
client
go
and
like
have
some
sort
of
consistent,
retry
and
logic
around
fetching
objects
and
fashion
objects
from
kubernetes,
and
also
maybe
posting
objects
to
communities.
A
A
This
one
I'm
not
sure
what
we're
going
to
do
with
it.
It's
just
it's
pending
discussion,
I'm
going
to
leave
it
in
the
milestone,
but
we
have
some
discussion
from
a
month
ago
where
we,
basically
we
are
really
realizing
that
we
kind
of
walked
on
it.
It's
we
want
to
move
the
correctly.
The
way
we
paint
control
brain
machines
with
whether
we're
going
to
do
it
with
a
couplet
config
or
a
mark
control,
plane
phase,
which
currently
uses
a
like
a
specialized
client
constructed
in
cuba.
A
A
I
think
I
actually
have
a
proposal
with
about
this,
but
I
have
to
discuss
with
fabrizio.
Basically
today,
cube
adm
allows
you
to
pass
a
single
complete
configuration
to
the
entire
cluster,
but
you,
if
you
have
different
machine
types,
the
only
way
to
override
configuration
on
a
specific
couplet
is
to
pass
corporate
flags,
and
most
of
these
kubernetes
flags
are
actually
deprecated
in
favor
of
the
favor
of
the
config
and
to
to
configure
a
specific
complex
on
a
specific
machine.
A
One
of
my
proposals
is
actually
to
use
patches,
which
means
basically
kubernetes
already
has
this
mechanism
for
patching
specific
types
such
as
you
know
the
lcd
static
port,
and
maybe
we
can
also
enable
this
for
the
couplet
configuration,
but
you
know
it
has.
It
requires
discussion
it.
It
requires
also
updates
to
the
kubernetes
patches
cap.
A
Kinder
base
image,
I
mean
I'm
going
to
move
this
to
next
as
well,
because
it's
just
I
don't
see
anyone
working
on
this
in
the
release
cycle,
but
it's
it's
really
nice
to
have
it.
Kinda
is
a
tool
we
we
use
for
android
testing
incubation.
We
need
a
a
better
way
to
create
our
base.
Images
for
testing
various
serps.
A
A
A
A
A
A
A
A
I
think
this
this
is
pretty
much
on
hold,
but
I
think
there
might
be
action
items
for
it
in
125,
so
I'm
going
to
leave
it
in
a
milestone.
Let
me
check
if
it's
frozen
yeah
it's
for
me.
I
don't
think.
Actually,
I'm
not
sure
whether
we
can
execute
any
action
items,
but
the
kubrick
at
least
recently
added
support
for
passing
the
cri
socket.
A
It
was
part
of
the
corporate
configuration
which
is
really
nice,
but
again
we
face
the
problem
that
I
discussed
earlier,
where
cuba
dm
can
only
configure
a
single
corporate
configuration
for
the
whole
cluster,
but
some
users
might
want
to
use.
You
know
cryo
on
one
of
the
machines
and
container
d
on
the
rest
of
the
machines
which
is
kind
of
difficult
for
us
to
handle.
If
you
only
have
a
single
corporate
config,
so
currently
kubernetes
annotates
the
cri
socket
inside
the
node
object.
A
This
effectively
allows
us
to
have
different
container
runtimes
of
different
nodes
and
we
have
to.
We
have
to
basically
design
it
properly
and
decide
how
we
can
use
it
by
basically
removing
the
nodes
here
right
socket
from
from
our
code
input.
Additionally,
using
the
complete
config,
it's
not
clear
to
me
yet
how
we're
going
to
do
it,
but
it's
still
an
option.
A
A
I
mean
I
don't
know
this:
is
it
really
it
it?
This
is
really
broken,
seek
release
because
they
currently
own
the
specifications
for
our
system,
this
specs
and
it's
not
clear
how
we
can
make
changes
to
those,
but
basically
we
have
to
change
the
specs
modify
cubaydm
and
consider
how
we
safely
propagate
these
changes
to
the
users
without
breaking
them,
but
it
has
been
already
in
the
pipeline
for
a
couple
of
years,
no
changes.
So
I'm
going
to
move
this
to
next.
A
A
A
We
relax
some
validation.
We
also
made
the
scheduler
and
kcm
point
to
the
local
api
server
instead
of
going
through
the
load
balancer
first
and
going
to
the
to
an
active
api
server,
but
we
found
another
thing
that
we
can
do.
Is
that
points
the
cubelet.com
file
as
well
to
the
api
server
that
that
doesn't
work
at
all?
And
I
my
speculations
in
the
thread
here
is
that
this
is
due
to
leader
election
and
I
don't
know
how
to
solve
it.
A
A
We
had
a
long
discussion
in
zoom
meetings
about
it,
like
basically,
whenever
cuba
dm
downloads,
the
cluster
configuration
from
the
coaster
and
applies
some
dynamic
defaults,
some
very
interesting
things
happen
and
we
don't
have
consistent
logic
around
our
commands
that
download
the
config.
So
basically
we
wanted
to
do
some
cleanup.
I
love
the
issue,
but
I
also
did
a
lot
of
testing,
but,
as
you
can
see,
we
have
been.
A
Mutable
upgrades
upgrade
the
cube
proxy
ds,
so
at
some
point
we
realized
that
in
our
kubernetes
upgrade
apply.
We
don't
follow
some
of
the
kubernetes
versus
key
policy
around
qproxy,
which
is
not
fatal,
and
actually
I
think
that
the
current
policy
is
a
bit
debatable
because
it's
so
strict
that
the
it
requires
from
the
operator
to
be
very,
I
don't
know
how
not
not
realistic,
you
know
to
execute
on
the
right
upgrade
steps,
but
basically
we
were
discussing
some
solutions
like
hey.
How
do
we
comply
with
this
policy?
A
A
This
is
something
that
you
can
actually
start
executing
on.
Basically
currently
cubadian
science,
super
administrator,
admin.com
file,
it
uses
the
system,
masters
group
and
that's
a
super
user
group
that
allows
you
to
bypass
rbac,
which
can
be
problematic
if
this
particular
admin.conf
leaks
to
someone
that
you
don't
want
to
link
it
to,
and
we
had
discussions
with
the
basically
the
contributor.
We
also
had
discussions
with
sigoff
and
the
story
is
that
cuba,
dm,
should
probably
sign
a
separate
admin.com
file
like
one
is
the
that
mean.cuff
that
is,
can
be
used
in
the
cluster.
A
A
This
the
story
around
this
is
basically
holly
contributed.
This
extension
to
kubernetes
join
to
support
dry
run,
and
but
we
found
some
problems
around
how
we
handle
configuration
directories
such
as
you
know,
the
customer
configuration
certificates
directories
not
handled
very
well
in
our
dry
run
logic,
so
she
locked
this
issue
to
potentially
try
to
solve
the
problem,
and
it's
documented
in
these
comments.
A
A
This
is
the
liveness
probe
yeah.
This
is
actually
related
to
one
of
the
first
tickets
I
discussed
at
the
beginning.
Basically,
it's
let's
check
which
one
is
it
yeah?
This
was
around
the
data
consistency
flag.
Basically,
it's
it's
related
because
in
both
these
tickets
we
want
to
upgrade
hcd.
If
you
upgrade
hcd
to
trip
five
three,
we
gain
a
very
nice
feature
in
cuba,
dm
where
we
can
actually
check
member
health
on
a
single
member.
Currently,
actually
has
this
sorry
in
previous
versions.
A
He
had
this
weird
behavior,
where,
if
one
member
is
failing,
the
whole
question
is
reported
as
failing
on
health
checks,
which
is
not
ideal,
because
you
might
have
like
five
members.
You
know
you
have
a
majority.
Maybe
three
members
are
voting
properly.
One
of
the
members
is
failing,
and
but
because
of
this
failing
member,
the
whole
quester
is
reported
as
failing
and
users
cuba
dm
users
are
trying
to
go
around
it
by
using
etsy
cuddle
immediately,
but
just
that's
just
not
ideal.
A
He
contributed
the
change
and
we
just
have
to
enable
ncd
353
in
all
the
supported
versions,
and
we
have
to
backboard
the
proper
health
check
inside
the
icd
starting
pot
manifests
that
kubernetes
deploys
and
yes,
this
is
track
for
125.,
I'm
not
assigning
myself,
but
I'm
going
to
pink
people
on
this
ticket.
Let
me
see.
A
A
A
Something
we
want
to
do
in
125.,
just
upgrade
hcd
solve
these
two
problems
around
the
data,
consistency
problem
and
the
health
check
problem,
and
these
are
going
to
be
some
really
nice
fixes
hd
driver,
okay,
so
enter
the
tests
for
dry
run.
I'm
going
to
keep
this
in
the
milestone,
paco,
no,
no
pacquiao
sarakiri
is
working
on
that.
A
I'm
not
going
to
assign
him
because
he
actually
submitted
already
some
of
the
pr's
the
remaining
action
items
here.
Let
me
check
what
we
have
yeah.
So
basically,
cuba
dm
join
currently
doesn't
even
have
a
dryer
in
climate
clan.
So
when
you
run
kubernetes
joint
qb
is
not
really
dry
running
fully
it
just.
A
It
still
tries
to
fetch
some
some
stuff
from
the
cluster,
and
what
we
want
to
do
is
add
a
dryer
and
client
fetch
it
like
a
fake
config
map
and
then
work
with
it
and
you
know,
could
create
a
proper
dry
run
for
join,
but
we
realized
that
we
need
some
changes
and
solid
queries
already
submitted
some
pr's,
but
I'm
going
to
keep
this
in
the
milestone.
Maybe
he
can
come
back
to
it.
What
not
something
nice
that
we
did
is
that
we
already
had
it
entered
this
for
dry
run.
A
A
We
just
have
to
fix
attack
for
you,
so
we
had
some
ideas
like
how
do
we
support
this
event?
But
basically
the
story
is
that
I
think
we're
currently
blocked
and
it
requires
pretty
much
requires
a
new
api
type,
which
is
maybe
v1
beta
4,
I'm
not
sure.
If
we
can,
we
are
able
to
execute
on
it,
but
if
I'm
going
to
leave
it
in
a
milestone
for
now,
because
it's
really
a
fresh
discussion
and
maybe
some
of
the
participants
can
get
back
to
it
and
we
can
add
more
comments.
A
A
What
is
next,
this
is
something
that
we
can
actually
do.
It's
really
nice.
When
you
do
cubadium
in
its
skip
phases,
we
skip
skip
phases
out,
so
we
can
actually
skip
another
one,
but
we
can
actually
do
this
kubernetes
phase
add-on
with
a
cube
proxy
and
add
the
flag,
which
is
you
know,
maybe
print
manifest,
and
you
can
actually
skip
the
phase
skip
the
other
completely,
but
still
obtain
what
manifest
would
have
been
applied
for
the
saddle.
So
maybe
you
can
deploy
your
custom
item
using
some
sort
of
a.
A
I
don't
know,
helm
wrapping
or
something
like
that-
that
that's
a
really
nice
feature,
and
I
think
we
we
can
add
it
in
this
release.
It's
backlogged
because
I
have
not
seen
any
requests
from
users.
I
see
that
waxy
assigned
himself.
Maybe
he
can
set
a
piano
for
that
and
that's
pretty
much
it
that's
the
housekeeping
tasks
last
one.
We
do
this
every
release.
C
A
C
C
C
Like
after
reaching
to
the
85
percent,
like
kubernetes,
garbage
collector
will
start
and
when
15
percent
of
the
space
is
available,
the
pod
of
the
eviction
will
start
here.
So
in
both
the
cases
85
of
the
disk
space
is
consumed,
so
wondering
why
these
two
values
are
defaults
are
same
like
is
there
any
specific
reason
behind
aligning
those
two
values.
A
If
you're,
if
you're
seeing
problems
with
this,
you
can
pass
a
custom
corporate
configuration
in
kubernetes,
but
I
really
don't
know
why
why
the
values
are
the
same.
You
can
join.
You
can
ask
on
signal
slack
channel
right,
but
I
think
the
better
option
is
to
just
join
the
signal
meeting
and
ask
like
maybe
the
maintainers
know
about
this,
or
maybe
they
have
forgotten.
I
see
a
comment
about
docker
here.
Actually,
which
is
I
don't
even
know
if
this
is
this
value
still
matters.
A
A
Yeah
yeah,
it
seems
like
a
good
plan
I'm
going
to
because
I
couldn't
type
and
speak
at
the
same
time.
I'm
going
to
add
some
highlights
here.
Maybe
you
know
some
of
the
the
more
important
stuff
like
docker
shin
stuff,
rename
master,
I'm
going
to
add
them
here,
but
that's
pretty
much
it.
I
think,
for
this
call.
