►
From YouTube: Kubernetes SIG Security Tooling 20230301
Description
No description was provided for this meeting.
If this is YOUR meeting, an easy way to fix this is to add a description to your video, wherever mtngs.io found it (probably YouTube).
A
A
I
will
now
make
our
presenter
today
who
is
David
the
co-host
so
we'll
be
able
to
share
his
screen.
We
are
going
to
talk
about
the
project
dividend.
His
team
has
been
working
on
called
security
guard
and
the
intent
is
to
learn
a
bit
about
the
tool.
Give
some
feedback
ask
some
questions
that
you
might
have
for
him
and
also,
at
the
end
of
the
day,
end
of
the
session.
He
is
going
to
explain
if
you
are
interested,
how
you
might
be
able
to
contribute
to
it
so
I'm
excited
about
this.
A
A
If
anyone
has
joined
today
for
the
first
time,
I
would
love
to
do
a
quick
set
of
intros
before
we
start
so
I
go
first
and
then
anyone
who
wants
to
introduce
themselves
go
for
it:
hi
I'm,
pushkar,
I'm,
the
six
security,
two
links
a
Project
Lead
I.
We
have
these
sessions
every
couple
of
weeks
as
a
learning
session
or
as
a
working
session.
This
is
one
of
the
one
of
the
learning
sessions
and
in
working
sessions
we
discuss
our
day-to-day
activities,
what
things
we
are
working
on
and
what
things
are
coming
next.
B
Sure
I
can
go
next,
so
hi
I'm,
Liam
I'm
still
relatively
new
to
like
the
actual
kubernetes
open
source
Community,
but
I've
been
working
with
kubernetes
for
about
two
years
now,
I've
done
my
own
fair
share
of
like
writing,
controllers
and
basic
things
like
that.
But
I
haven't
done
a
whole
lot
of
like
work
on
the
product
itself,
so
I
just
want
to
sit
and
listen
and
learn.
More
again,
my
camera
will
be
off
because
I'm
messing
with
t
and
doing
other
things,
while
just
listening
right
now,.
D
I'm
Caitlin
I
am
a
infrastructure
security
engineer
at
Shopify.
I've
been
involved
with
six
security
and
open
source
kubernetes
for
about
a
year
now
and
I'm
working
currently
with
succeed
alive
working
on
some
Cube
CTL
commands,
hopefully
before
code
freeze
and
generally
trying
to
learn
and
help
other
people
learn.
A
E
It
is
a
research
project
that
I
developed
as
part
of
IBM
research,
and
we
decided
that
it's
a
good
way
to
promote
it
by
pushing
it
out
to
open
source
and
trying
to
get
other
people
involved
in
it.
It
is
fairly
intense
work
and
we
want.
We
want
it
to
be
a
contribution
that
would
last
because
the
community
would
actually
use
it
over
time
and
continue
to
evolve
it.
So
we
adopt
we,
we
asked
K
native
to
adopt
us
actually
and
we
integrated
into
k-native.
E
We
see
K
native
as
a
system
that
can
deploy
microservices
as
well
as
serverless,
by
the
way
in
kubecon
I'm
going
to
present
why
that
is
so.
We
have
a
session
cubicle
on
that
part.
I'll
briefly
also
talk
about
Garner.
That's
that's
a
session
that
we
have
there
and
today
I'm,
going
to
try
to
give
you
a
bit
of
a
better
understanding
of
of
what
is
this
tool
and
how
to
actually
use
it
and
what?
E
E
E
E
E
E
E
E
E
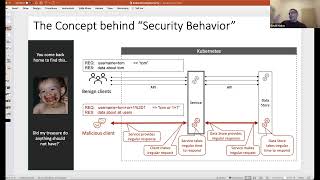
So,
a
little
bit
about
that
concept
of
security,
behavior
I
think
it's
easiest
to
to
take
an
example.
Airport
security
is
one
example,
but
I
didn't
find
a
good
picture
that
would
not
irritate
anyone
when
it's
showing
someone
being
detained
or
something
so
I
found
a
different
example.
You
come
back
home.
You
come
back
over
every
time.
E
You
don't
have
a
signature
of
testing
for
chocolates.
None
of
this
is
true.
What
you
have
is
the
ability
to
identify
that
a
it
is
not
normal.
What
you
see,
which
is
something
we
do
as
humans
very
well
and
B.
This
not
not
normal,
is
not
only
not
normal,
but
it
is
suggestive
that
the
treasure
that
did
something
that
you
shouldn't
have
done.
E
So
that's
security
Behavior.
If
you
take
that
to
the
security
domain-
and
you
ask
yourself,
how
would
I
know
if
a
service
misbehaves,
but
not
just
do
something
out
of
the
normal,
but
how
would
I
know
misbehaving
a
security
affecting
way
so
I
need
to
be
able
to
capture
his
security
behavior
on
a
normal
day
and
then
capturing
security
behavior
on
a
normal
day
or
when
being
attacked
or
when
being
when
an
expert
being
sent
to
it
and
so
on
and
so
forth.
E
This
is
security.
Behavior,
it's
qtb,
monitoring
and
control
is
the
ability
to
monitor
security,
behavior
and
send
alerts
and
control,
says:
okay,
don't
only
send
alerts,
but
also
do
something
about
it
and
that's
what
security
guard
do
it?
It
can
work
in
different
modes
of
operation,
but
that's
essentially
what
it
does.
E
You
already
know
that
an
example
from
the
from
the
post,
so
I'm
not
going
to
repeat
that
I
would
just
say
emphasize
that
there
are
so
many
ways
in
which
you
can
determine
that
something
is
off
in
your
services
and
you
are
being
attacked
and
you're
something
you're
getting
wrong
if
you
were
spending
100
of
your
time.
Looking
at
the
logs
looking
at
the
behaviors
understanding.
E
E
C
E
Be
compromised,
it
may
be
vulnerable
or
it
may
get
a
request
and
block
it
or
it
may
get
a
request.
No
sorry,
regardless
of
the
request,
it
would
identify
that
the
Pod
or
or
the
service
for
that
matter
is
the
process
you
would
see
in
a
second
is
misbehaving
and
is
probably
compromised
and
you
need
to
restart
it,
so
you
would
delete
it
and
a
new
pod
will
come
up
now.
E
E
No,
the
the
two
think
of
it
as
two
different
security
Behavior
analytics
being
done,
one
of
the
requests
one
on
the
point.
Now
we
don't
do
a
lot.
We
don't
don't
do
everything
that
we
could
do
on
the
port
side
simply
because
there
are
already
tools
out
there
and
we
we
will
integrate
at
some
point
with
other
tools
such
as
we'll
get
a
better
view.
You
probably
wouldn't
need
to
write
everything
from
scratch.
E
A
E
So
both
of
them
need
to
be
continued
to
be
improved.
However,
it
is
already
you
will
see.
There
is
a
whole
ecosystem
around
it
that
will
help
you
cope
with
those
alerts
in
a
way
that
you
are
able
to
scale
the
amount
of
services
being
being
protected
with
God,
even
though
you
may
have
some
false
positive
and
true
negatives.
E
Oh
okay,
yeah,
two
negatives,
that
okay
I'll
talk
about
three
negatives
as
well,
so
that's
the
deployment
model.
Of
course
it
is
sitting
in
front
of
every
code,
so
in
in
in
kubernetes
environment.
It
is
a
cycle
in
a
k-native
environment.
There
is
already
a
sidecar,
the
kinetic
deploys
and
we
are
integrating
into
that
one.
E
Being
zero
day
solution,
if
you
are
working
in
a
block
mode,
it
doesn't
matter
where
the
exploit
comes
from,
or
the
attempt
to
attack
you
comes
from.
We
we
don't
care
any
microservice,
even
the
one
that
is
not
exposed
to
the
internet
is
being
protected,
so
you
may
have
a
compromised
redis
the
tries
to
attack
one
of
your
services
or
compromise
whatever
or
just
a
Insider.
E
So
if
he's
sending
a
request
that
he
shouldn't
be
sending,
it
will
be
blocked,
and
if
he's
able
to
somehow
compromise
your
pod,
your
pod
will
be
deleted
so
soon
after
he
is
able
to
compromise
it.
A
new
pod
would
come
on
instead
of
it,
and
what
he
has
done
is
is
was
useful
for
a
very
short
time
now.
That
also
means
that
if
we
have
a
microservice
a
and
we
have
a
force.
E
E
So
if,
for
example,
if
you
have
an
SQL
injection
and
for
some
reason
you
can't
detect
that
in
in
the
front
end,
you
might
be
able
to
detect
that
in
the
back
end-
and
we
are,
we
are
monitoring
both
the
requests
and
the
responses.
So
if,
if
you
didn't
identify
that
in
the
request,
you're
still
going
to
block
the
response,
if
it
is
completely
out
of
line
compared
to
the
other
responses
we
have
seen
and.
E
Now,
each
set
of
guards
protecting
a
microservice
share,
a
guardian,
a
guardian
in
the
crd
or
it
can
be
deployed
as
a
config.
If,
for
some
reason
you
can't
have
crds
in
your
system,
so
it
is
a
crd
which
includes
all
the
specs
of
what
was
learned
and
so
on
and
the
controls.
It
says,
for
example,
there,
whether
to
block
or
not
and
because
every
microservice
has
one
it
means
that
we
have
the
ability
to
capture
the
behavior
of
each
microservice
individually.
E
So
that's
bring
me
back
to
that
picture
that
we,
we
also
had
it
in
in
the
in
the
post,
which
says
okay,
now,
I
only
see
these
requests
coming
into
that
service
and
these
requests
coming
into
that
service
and
I
can
monitor
both
the
behavior
of
the
requests
and
the
behavior
of
the
service
in
view
of
what
I
see.
So,
if
you
have
a
pretty
strong,
easy
way
to
learn
an
easy
way
to
detect
misbehavior,
which
is
security,
oriented
assuming
again
assuming
my
learning
is
of
features
which
are
security,
oriented.
E
So
and-
and
that's
that
works
very
well
with
microservices,
because
a
typical
micro
Services,
if
it
would
follow
at
12
Factor
up,
it
would
already
be
divided
into
functions
to
a
specific
function
that
this
microservice
does
and
it
answers
specific
requests.
Maybe
tools,
kind
of
requests,
maybe
three,
but
it's
not
a
monolith.
E
E
That's
a
front-end
service
which
is
serving
iot
or
Event
Source,
or
some
service
deployers,
where
I
have
a
back-end
service
and
I
have
a
third
service,
which
is
a
front-end
service
which
goes
and
and
all
kind
of
browsers,
try
and
reach.
It
I
think
it's
very
clear
that
the
protection
of
this
front-end
service
and
the
back-end
service
would
experience
even
greater
uniformity
of
what
they're
being
sent.
E
For
example,
the
user
agent
will
always
look
the
same
because
it
is
the
same
same
service
that
is
using
it
and
the
headers
will
always
look
the
same,
and
the
body
will
always
look
the
same
and
the
responses
with
those
who
could
say
because
it's
the
machine
to
machine
here
the
system
needs
to
generalize,
it
will
generalize,
but
it
will
generalize
across
all
user
agents
and
all
headers
being
sent
and
so
on
so
forth.
So
it
will
have
a
much
bigger
Guardian
that
defines
what
that
that
microservice
is
supposed
to
accept.
E
Now,
if
we
have
a
guardian
that
protects
both
this
one
that
one
and
that
one
then
sure
you
you
understand
that
these
two
services
will
be
less
protected
when
compared
to
having
one
for
each
one,
because
this
Guardian
is
pretty
fine
grained.
All
of
them
are
fine
grained,
but
this
one
is
says:
okay,
I
only
see
requests
of
that
kind.
E
It's
exactly
looking
like
that,
and
it
takes
very
little
time
and
I
have
no
more
alerts
and
everything
is
very
stable
and
let's
go
and
this
one
would
say:
Okay
there
are
some
new
kind
of
users
coming
in
for
a
while.
I
will
have
for
some
alerts.
As
a
result,
I
will
need
to
review
them
and
see
that
he's
fine
and
at
some
point
I
would
say:
okay,
I'm,
I'm
done
I
see
no
more
alerts
system
is
stable.
If
I
see
now
an
alert
I
can
block
it.
E
I
can
I
can
really
treat
it
as
something
which
is
wrong
and
I
need
to
do
something
about
it
and
and
the
further
away
you
are
from
a
unified
micro
service.
That
does
only
one
thing:
the
Lesser,
your
your
profit
from
security
Behavior.
It
doesn't
mean
that
it
doesn't
profit,
it
can
still
profit
you,
but
it
is
a
lesser
profit
compared
to
a
situation
when
you
are
actually
working
against
a
monolith.
E
So
yeah,
so
that
that's
that's
this
picture
here,
it
does
again
it.
It
doesn't
say
that
we
cannot
extend
the
security
of
it,
the
the
tour
over
time
to
improve
the
way
it
works
against
monolith
and
so
on.
But
this
is
like
our
first
Target
and
a
very
important
Target,
because
microservices
are
everywhere.
E
E
E
E
E
And
then
we
saw
that
and
then
we
have
those
four
use
cases
and
what
I'm
trying
to
do
right
now
is
to
explain
how
it's
being
used
to
address
those
four
use
cases.
So
I'll,
try
I'll
start
with
the
normal
and
I,
have
three
sides
to
three
options:
to
treat
the
normal
and
then
I'll
talk
about
the
vulnerable
exploitable.
E
The
misuse
is
always
always
the
same.
It's
it's,
it
could
be
said
all
three
of
them
on
particular,
so
I'm,
taking
three
approaches
by
different
organizations
for
securing
their
microservices.
The
first
approach
is
I.
Don't
want
to
do
anything
I,
don't
want
to
care
about
that
until
someone
really
really
really
really
really
forced
me
to
do
that
so
I'm
in
a
normal
day,
I
currently
I
have
no
no
such
protection
I'm.
Adding
that
that
protection
I
don't
want
to
add
more
work
for
me.
E
E
B
C
E
E
E
If
we
see
now
an
alert
based
on
our
configured
bucket,
which
we
better
need
to
worry
about
that.
So
that
is
a
second
mode
of
abrasion.
The
third
one
is
security,
where
a
company
which
says
Okay
I
I
want
to
block
whatever
is,
is
not
not
in
line
with
what
I've
learned
so
I
start
the
same,
but
the
minute
I
go
to
after
the
initial
deployment.
I
would
say:
okay
now,
I
trust,
my
learned
configuration
I
would
move
to
block
and
don't
learn
and
use
a
configured
in
this
mode
already.
E
E
E
B
E
E
E
B
E
C
While
you're
bringing
that
up
quick
question,
how
do
these
sidecar
the
sidecar
implementation?
How
would
it
be
or
would
it
be
compatible
with
something
like
a
istio
or
something
that
has
its
own
sidecar
injection
going
on
and
specifically,
if
you've
got
something
coming
in
and
doing
Mutual
TLS
for
you?
How
can
you
make
sure
that
your
sidecar
is
not
in
front
of
that,
so
that
it
can't
see
the
encrypted
headers
and
whatnot.
E
C
E
It
does
this
for
you
in
in
the
microservice.
You
need
to
set
it
up
correctly.
We
need
to
set
it
up
to
terminate
the
TLs
that
side.
That
guard
is
in
a
reverse
proxy
that
can
terminate
your
TLS
okay
in
K
native.
That's
a
natural
thing
to
do,
because
you
don't
want
the
the
user
containers
to
deal
with
the
TLs
certificates
and
so
on.
A
E
So
we
have
a
bunch
of
documentation
here
a
little
bit
about
why
it
is
needed,
how
it
helps
secure
that
diagram
that
you
saw
with
an
extra
part
which
we
are
we
don't
have
yet
in
open
source,
which
is
a
UI.
We
had
a
POC
on
that
and
it
hasn't
made
it
into
the
open
source
yet
because
it
requires
some
changes
and
more
work.
E
There
is
here
instructions.
Instructions
on
4K
native
are
in
the
K
native
docs
instructions,
so
it
sends
you
to
the
clinic
docs
inside
instructions
for
kubernetes
are
here
in
a
in
a
readme
file,
so
it
has
an
explanation
of
how
to
deploy
it
in
in
a
micro
service.
There
are
two
modes
to
deploy
it.
One
is
that
you,
you
have
a
container
in
front
of
your
user
container,
but
also
you
can,
if
you
really
want
to
not
an
advised
one,
to
have
your
own
card
in
front
of
your
service
board.
C
A
E
You
can
open
an
issue.
Can
you
open
an
issue
to
ask
question?
You
can
open
an
issue
to
to
contribute
whatever
ideas.
You
have
open
an
issue
for
anything
I'm
I'm.
As
you
know,
I'm
I'm,
available
in
security
and
six
security,
tooling
I'm
also
available
on
the
cncf
K
native
cff
slack
on
the
K
native
security
channel.
So
you
can
go
there.
There
is
more
exposure
there
for
people
in
in
the
K
native
area,
yeah.
E
Just
to
show
you
how
an
alert
look
like
80,
it
could
be
more
descriptive,
maybe
one
day
it
will.
It
says
that
your
HTTP
request
on
that
session,
your
HTTP
request,
add
a
query
string
with
a
key
a
that
was
never
appeared
before
you
can
get
an
alert
for
having
all
kind
of
special
characters
that
you
don't
expect
to
see
in
the
value
or
in
the
key
you.
E
You
can
have
alerts
about
too
long
values
which
may
suggest
that
someone
is
trying
to
exploit
some
field
that
you
have
everything
that
we
did.
We
are,
we
were
able
to
identify,
identify
as
something
we
need
to
monitor,
have
been
monitored,
and
that
means
that
anyone
new
coming
into
this
to
to
this
open
source
is
most
welcome
to
identify
new
kind
of
microbes.
E
E
There
will
be
more
scripts
as
we
move
forward,
because
the
scripts
right
now
are
based
on
latest
and
all
this
documentation
is
fairly
new
for
kubernetes,
so
it
has
been
less
detailed
before
so.
We're
gonna
have
now
that
we
have
that
we're
going
to
have
a
bunch
of
scripts
going
to
be
come
up
with
the
next
version,
probably
in
a
few
weeks,
so
we're
gonna
have
easier
even
easier
time
to
deploy
it.
Okay,.
A
That
sounds
that
sounds
great.
We
have
about
less
than
a
minute
remaining,
so
unfortunately
we
have
to
stop,
but
thanks
a
lot
private
for
sharing
your
knowledge
and
a
little
bit
about
the
project
as
well.
I
learned
a
lot
as
well.
I
tried
my
best
to
capture
some
notes,
I'll
listening
in
parallel.
If
anyone
wants
to
add
to
that,
please
do
it.
We
will
meet
again
a
couple
of
weeks
from
now
on,
March
15,
so
that
will
be
just
after
code
phase,
if
I'm
not
wrong.
