►
From YouTube: Kubernetes SIG Security Tooling 20220419
Description
No description was provided for this meeting.
If this is YOUR meeting, an easy way to fix this is to add a description to your video, wherever mtngs.io found it (probably YouTube).
B
B
Perfect,
so
thanks,
hello,
everyone,
I'm
christophe,
stephanie
dropper
and
the
slides
are
available
here
today
we're
going
to
talk
about
strategy.
It's
an
open
source
project
that
I've
been
working
on
in
the
past
few
months
that
we
released
in
late
january
and
yeah.
I
hope
to
give
a
bit
of
insights
beyond
the
projects
why
we
built
it
what
we
can
do
with
it
in
terms
of
community
security
and
also
a
small
call
to
action
for
the
for
the
community,
the
slides
you
can
find
them
here,
bid
dot,
ly
strategist
team
seek
security.
B
So
again,
I'm
christopher
stephanie
dropper.
I
work
at
datadog
in
the
cloud
security
research
team.
We
try
to
build
things
in
in
terms
of
like
how
to
help
cloud
security
practitioners
to
participate
to
operate
source
world,
and
things
like
that.
If
you
want
to
shoot
me
an
email
or
a
twitter,
dm
related
to
fragile
team
or
anything
else
feel
free
to
just
reach
out.
B
So
I
like
to
start
with
a
small
buzzword
that
is
purple
teaming
and
for
this
presentation
I
want
to
define
it
as
empowering
defenders
to
understand
or
produce
and
detect
common
attacker
tactics.
You
know
we
used
to
have
things
like
blue
team
and
red
team.
The
red
team
will
own
how
to
reproduce
their
attack
techniques
that
make
sense
for
the
organization
and
the
blue
team
would
need
to
know
how
to
detect
that
and
purple
teaming
is
more
about.
You
know
empowering
defenders
to
do
that.
Just
like
with
a
devops
mindset.
B
Your
developers
are
supposed
to
be
able
to
own
the
process
from
end
to
end
purple.
Teaming
is
kind
of
the
same,
and
I
also
wanted
to
highlight
the
teaming,
because
purple
teaming
is
not
supposed
to
be
a
team.
It's
a
mindset,
just
like
you
are
not
supposed
to
have
a
devops
team
public
teaming
is
more
a
mindset
and
a
way
of
working
than
a
team.
A
B
Yeah
sure,
and
typically
it's
a
it
can
be
challenging
to
reproduce
those
and
I'm
going
to
take
a
very
simple
example
of
the
kubernetes
world,
but
it's
even
more
applicable
to
the
cloud
world.
Let's
say
that
you
want
to
simulate
this
attack
technique.
I
want
to
reproduce
an
attack
where
someone
dumps
the
service
account
token
from
a
pod
that
is
currently
running.
So
how
do
you
do
that?
First
thing
you
have
to
create
a
service
account.
Then
you
have
to
create
a
role
or
a
cluster
role.
B
When
you
have
to
create
a
whole
binding
or
a
cluster
or
binding,
then
you
have
to
create
a
pod
with
right
definition
that
runs
out
of
the
right
service
account
in
the
right
name
space.
When
you
want
to
wait
for
the
pod
to
become
available,
you
exec
into
the
pod,
and
you
would
dump
the
service
account
token.
B
Now
that's
a
lot
of
manual
work
and
that's
a
lot
of
prerequisites
that
can
be
annoying
and
slow
to
recreate,
typically
you're
going
to
do
cube.
Ctl
create
service
account
test
and
someone
else
has
created
a
service
account
with
the
same
name,
etc,
and
when
you
are
finished
to
reproduce
it,
you
have
to
clean
it
up
one
by
one.
B
So
that's
a
bit
of
a
pain
point
that
we
try
to
solve
here,
because
in
the
end,
when
you
want
to
approach
an
attack
technique,
maybe
you
have
spent
like
a
lot
of
time
figuring
out
how
to
set
up
the
right.
Kubernetes
configuration
the
right
cloud
infrastructure
and
in
in
the
end,
the
time
that
you
actually
spend
testing
your
thread.
Detection
is
very
low,
and
especially
with
cloud
so
with
aws,
azure
or
gcp.
B
When
you
have
to
test
things
that
have
an
ec2
instance
of
vpc
subnets,
it
takes
a
lot
of
time
and
basically
you
are
doing
anything
else,
but
actually
testing
a
threat,
detection,
so
long
story
short,
two
challenges
that
we
saw.
First,
one
is
the
complex
testing
prerequisites,
as
I
just
showed,
and
second
one
is
also
the
fact
that
humanities
and
cloud
security
is
still
pretty
young.
B
Second
thing
I
like
to
pitch
it
as
atomic
team
for
the
cloud
so
atomic
has
team
is
a
project
by
red
canary
which
is
focused
on
endpoints,
so
windows
and
linux,
and
the
ide
is
really
to
have
a
simple
way
to
reproduce
some
common
attack
techniques-
and
here
it's
for
the
cloud,
so
it's
written
in,
go
it's
a
single
binary
and
it
comes
packaged
with
a
bunch
of
cloud
native
attack
techniques.
Currently
it
supports
aws
humanities
and,
in
the
future,
we'd
like
to
add
support
for
azure
and
maybe
gcp.
B
So
there
are
some
other
tools
in
this
space.
There
is
a
page
on
the
website
that
compares
it,
but
basically
some
other
tools,
like
paku,
are
more
focused
to
offensive
paint
russian
testers.
Some
of
them
are
product
specific,
like
amazon
gathered,
tester,
and
some
of
them
are
more,
are
more
complete.
They
have
more
features
and
also
more
complex
to
set
up
like
leonidas
and
atomic
team
is
more
focused
on
endpoint.
That's
for
the
short
for
the
short
version
now.
B
The
first
thing
that
we
wanted
to
have
is
a
philosophy
for
the
attack
techniques
that
we
have
in
stratosphere
team,
and
it
comes
down
to
two
things.
First
thing
is
that
we
want
to
have
attacks
as
code,
so
we
want
it
to
be
version
to
be
testable,
etc.
So,
currently
it's
written
in
go
and
entire
form
and
we'll
see
that
in
in
a
few
slides.
The
second
question
we
ask
is:
what
attack
techniques
do
we
want
to
package
and
it's
not
a
simple
question
in
vienna.
B
We
decided
to
have
only
things
that
are
actionable
for
defenders,
and
that
are
what
I
call
threats
informed.
So,
basically
we
don't
want
to
have
attack
techniques
that
are,
you
know,
bleezing
edge,
but
that
no
one
is
using.
We
don't
want,
like
fancy
privilege
escalations
in
aws,
that
not
a
single
penetration,
tester
or
offensive
actor
has
used,
and
that's
kind
of
the
tradeoff
that
we
want
to
find
here.
B
So
the
value
proposition
that
the
project
hopefully
brings
is
a
catalogue
of
real-world
cloud
attack
techniques
and
an
easy
way
to
reproduce
them
against
a
live
environment.
So
typically
you're
going
to
point
stratosphere
team
at
an
existing
kubernetes
cluster
at
an
existing
aws
account
and
be
able
to
work
with
it.
And
the
question
that
comes
here
pretty
often
is:
isn't
this
the
same
as
mitral
attack
for
cloud?
B
And
the
answer
is
it's
a
bit
similar,
except
that
nitro
attack
for
cloud
is
a
bit
higher
level
and
it
doesn't
try
to
go
into
the
specifics
of
a
cloud
provider
or
of
communities,
and
so
I
I
would
say
that
mitral
attack
helps
a
lot
to
classify
the
attack
techniques
here.
But
it's
not
at
the
same
level
of
detail.
B
So
currently
we
have
23
aws
attack
techniques
and
six
for
kubernetes
with
police.
You
can
see
that
the
stratosphere
team,
dot
cloud
attack
techniques
and
so
it's
map
to
mature
attack
tactics,
so
persistent
privilege,
escalation,
exfiltration,
but
not
to
the
techniques,
and
the
reason
is
that
sometimes
it's
hard
to
map
things
to
the
very
specific
techniques
and
at
first
we
didn't
want
to
be
blocked
and
to
not
release
an
attack
technique
just
because
we
could
not
map
it
correctly.
A
B
So
the
attack
tactics
are
the
same
for
containers
and
for
cloud
because
it's
the
big
domains.
You
know
it's
like
a
initial
access
privilege
escalation
persistence.
So
it's
mapped
to
that
and
currently
it's
not
mapped
to
the
microsoft
threat
matrix
for
kubernetes.
It
might
make
sense
to
add
this
mapping.
B
B
No
thank
you
for
the
question.
So
the
website
looks
like
this
currently
status.
Strategy.Cloud.
There
is
a
list
that
is
automatically
generated
from
all
the
attack
techniques.
There
is
the
mapping
to
my
attack
here
on
the
left.
You
can
see
the
kubernetes
attack
techniques.
There
are
more
for
aws,
there
is
a
user
guide
and
you
can
also
search
in
the
site.
So
if
we
have
a
quick
look
at
a
specific
attack
technique,
we're
going
to
keep
the
same.
B
So
stealing
a
running
pod
service
account
token
first
thing
you'll
see
is
so
there
is
the
title.
The
platform
for
which
the
attack
technique
works,
the
mapping
to
my
true
attack,
and
then
you
have
also
a
description
which
basically
tells
you
what
the
attack
technique
is
doing,
and
you
will
see
and
we'll
get
back
to
that-
that
there
are
two
phases:
the
warm-up
phase
that
is
going
to
create
the
prerequisite
to
be
able
to
detonate
to
test
the
attack
technique
and
the
detonation,
which
is
basically
reproducing
the
attack.
B
So
we
try
to
show
like
some
leads
on
how
you
could
detect
that
so
here,
for
instance,
for
this
technique,
we
have
something
around
well,
when
you
do
a
quick
ctl
exec.
Here
is
what
the
api
server
logs
look
like.
So
you
could
go
ahead.
Look
at
that
and
try
to
see
if
someone
tries
to
dumb
the
service
account
token
using
a
coop,
ctl,
exec
or
similar
under
the
hood.
There
are
two
things:
there
is
some
telephone
code
that
is
handling
the
prerequisite.
B
B
So
in
this
case
you
know
we're
just
going
to
say:
I
want
to
run
this
command
in
the
pod
that
we
have
created
during
the
warm-up
page
and
then
just
print
it
to
standard
out
and
in
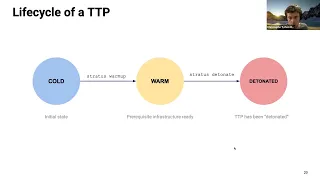
terms
of
lifecycle.
It
goes
like
that.
So
initially,
when
you
have
an
attack
technique,
it's
called
so
it's
not
ready
to
be
detonated.
You
don't
have
the
like
requisite
infrastructure.
Yet
brain
is
going
to
be
warm.
B
So
when
you're
going
to
run
a
stratus
warm-up,
my
attack
technique
is
going
to
do
a
terraform
apply
under
the
hood.
Again,
you
don't
see
it,
but
it's
going
to
create
the
infrastructure
that
you
need
and
when
you
do
strategies
detonate.
It's
going
to
detonate
the
technique
to
be
like
it's
basically
to
reproduce
it
to
test
it
to
to
trigger
it.
B
B
Okay,
so
you
can
see
my
terminal.
I
hope
first
thing
you
can
do
is
to
list
the
attack
techniques.
So
if
you
do
just
stratus
list,
you
have
a
bunch
of
attack
techniques
with
the
name
and
the
platform,
you
can
be
a
bit
more
granular,
so
you
can
say
I
want
to
see
it
only
for
kubernetes
and
maybe
only
for
persistence.
B
B
A
B
C
B
Yeah,
mostly
for
simplicity
or
otherwise,
you
know
it's
slow
to
do,
and
let's
say
that
you
have
some
security
monitoring
things
in
your
cluster.
It
means
that
you
have
to
mimic
that
as
well,
so
it
becomes
too
too
too
specific
so
for
iws
and
for
communities
we
chose
to
say
you
point
that
at
an
existing
cluster
at
an
existing
account,
oh
okay,
that
makes.
B
B
So
here
I
just
want
to
show
the
fact
that
you
can
warm
up
the
attack
technique
and
it's
just
going
to
spin
up
the
prerequisite
so
incubate
it.
It
might
be
a
bit
less
valuable,
but
in
some
other
environments
like
in
aws,
it's
going
to
create
a
lot
of
infrastructure
for
you.
So
here,
if
I
warm
up
this
attack
technique,
it's
telling
me
it
has
created
a
pod
in
this
namespace.
So
I
can
just.
B
A
B
Cool
and
yeah
just
a
quick
comment,
so
I
said
that
it
was
this
terraform
under
hood
generally.
It
would
make
me
scared,
but
it
doesn't
have
any
prerequisites.
So
actually,
if
you
look
at
in
your
strategic
folder
in
your
home
directory,
you
will
see
that
it
creates
a
directory
and
it
basically
downloads
its
own
terraform
binary
and
its
own
terraform
version,
so
that
even
if
you
have
a
locally
installed
terraform,
it
won't
clash
with
it
or
it
won't
ask
you
to
install
the
writer
from
the
version
extra
just
for
the
context.
D
B
Cool,
so
now
we
have
a
demo.
I
just
want
to
touch
in
a
bit
of,
like
other
use,
cases
that
I
think
are
interesting
to
tackle
with
satisfaction
and
that
hopefully
I'll
be
able
to
release
some
things
on
all
that
soon.
So
one
is
what
I
like
to
call
continuous
detection
testing
or
also
non-regression
testing
for
detections,
but
it
starts
to
be
a
bit
complicated
and
basically
the
idea
is
that
detection
that's
code
is
becoming
pretty
popular
and
more
and
more
people
are
writing
their
detection
rules
as
code.
B
So
maybe
it's
yaml,
maybe
it's
terraform
ansible
or
anything
like
that,
and
we
tend
to
forget
that
when
we
have
code
generally,
the
good
practice
is
to
test
it
right,
because
if
we
look
at
a
pipeline
like
that,
typically,
let's
say
that
you
are
using
any
kind
of
cm
or
loss
management
solution
and
you
are
sending
all
your
aws
kubernetes
logs
to
that
you're
going
to
have
something
like
this.
You
have
your
manage
control
plane.
It's
going
to
send
the
logs
to
a
service
specific
service,
so
here
is
going
to
be
cloudwatch
for
aws.
B
B
Maybe
you
don't
have
the
right
setup
to
send
your
logs
to
your
sim?
Maybe
the
passing
is
messed
up.
Maybe
someone
disables
an
alert
rule.
Maybe
your
layers
are
just
not
created,
as
you
expect
them
to
be,
etc,
etc.
So
the
idea
is
that
you
can
consider
that
as
a
black
box,
you
don't
look.
What's
inside,
you
trigger
some
attack
techniques
using
stratosphere
team
and
you
look
at
what
goes
out
and
it's
something
that
is
made
possible
in
part,
because
we
tried
to
design
stratified
team
as
a
library
as
well.
B
B
B
Then
you
are
going
to
use
the
api
of
your
cm
of
your
log
management
solution
to
look
at
the
security
layers
that
it
has
generated
and
once
you
have
the
alert
you
can
say.
Okay,
basically,
I
triggered
the
layout
from
one
side
and
I
confirmed
that
on
the
other
side,
I
have
the
alert
coming
in.
So
for
me,
it
means
that
my
detection
is
working.
End-To-End-
and
I
know
that
nothing
is
broken
in
the
middle.
B
So
it's
basically
going
to
be
a
piece
of
goku.
I'm
not
going
to
go
too
much
into
detail,
but
basically
this
is
saying,
or
this
strategy
attack
technique,
so
kws
persistence
create
admin
cluster
role.
I
expect
to
have
an
alert
that
is
called
this
way
for
this
one.
I
expect
to
have
an
alert
that
has
visitor
and
basically
so
here,
I'm
using
the
the
data
api,
but
it
could
work
for
anything
like
a
splunk
or
anything
else.
B
B
And
then,
after
a
few
seconds,
it
means
that
my
logs
have
been
sent
to
my
lux
management
solution.
The
alias
should
have
run
against
it
and
I
should
be
able
to
see
basically
that
the
alert
has
been
found
and
that
the
end-to-end
test
was
done.
So
you
know
here
it
says.
Okay,
I
saw
that
the
expected
alert
was
created
in
15
seconds.
I
can
just
close
it
and
confirm
that
it
has
worked
and
that's
a
bit
of
a
goal.
B
B
So
I
know
of
a
startup,
I
don't
remember
the
name
who
was
integrated
in
their
attack
simulation
library.
I
don't
remember
the
name,
but
I
know
that
they
are
doing
it.
And
hopefully
you
know,
as
time
goes
by,
we
see
a
few
more
people
that
use
it
yeah.
So,
let's
let's
see,
but
for
now
I
know
of
one
company
and
we
also
do
it
internally
at
datalog.
B
Right
so
now,
just
a
few
few
things
on
what's
next,
so
first
thing
is
that
we
want
to
add
eventually
support
for
azure
id
for
azure
and
maybe
for
gcp,
but
at
least
for
azure.
Second
thing
is
that
the
community
is
welcome
to
participate
to
attack,
technique,
ids
and
specifically
for
humanities.
We
are
super
interesting
to
hear
about
things
that
you
have
seen
in
the
wild.
B
So
if
you
have
something
some
insights
around
that,
the
first
step
is
to
open
an
issue
on
the
status
threat
in
repo
and
basically
when
there
is
an
agreement
that
it
makes
sense
to
implement,
will
help
to
make
it
happen
either
through
contribution
or
we.
We
also
have
some
some
bandwidth
to
do
it
ourselves.
So
that's
the
idea
and
yeah.
If
you
feel
free
to
have
a
look
at
the
at
the
website
how
to
set
team
cloud,
you
will
see
the
attack
techniques
that
I
discussed
here.
B
The
repo
is,
there
shoot
me
a
dm,
an
email
for
anything.
This
is
the
introduction
blog
post,
so
it
shows
a
bit
also
in
terms
of
design
choices
that
we
tried
to
to
to
decide
and
why
we
made
them
and
the
alternatives
and
yep.
Let
me
as
a
queen,
yes,
and
besides,
are
there
and
that's
basically,
it
so
quick.
A
B
B
One
of
the
design
choices
that
we
made
is
to
use
go,
which
means
that
it's
harder
for
people
to
like
write
their
own
attack
tactics
without
contributing
back
to
the
core
of
such
a
serious
team,
because
you
know
if
it
was
in
python,
it's
very
easy
to
load
some
code
dynamically
in
go
it's
not
the
case.
At
least
it's
not
straightforward.
B
B
B
Sure
sure
so,
yeah
so
first
thing
that
you'll
see
is
some
frequently
asked
questions
typically
around
the
permissions
that
you
need,
how
it
keeps
the
state
how
you
can
add
your
attack
techniques,
some
design
choices
and
things
like
that
so
feel
free
to
have
a
look.
There
is
the
comparison
with
other
tools
that
I
that
I
discussed
as
well,
so
with
atomic
team,
leonidas,
paku,
amazon,
guardity,
tester
and
cloud
goat.
B
B
You
have
a
reference
per
command
as
well.
Some
troubleshooting
dock,
the
the
programming
usage
that
I
mentioned
before
so
there
is
some
auto
automatically
generated,
go
go
code
that
works
by
version
as
well,
so
you
can
go
back
in
time.
So,
typically,
you
can
see.
The
api
here
is
pretty
simple:
you
can
get
the
attack
techniques
list
them
register
a
new
attack
technique
as
well,
and
there
are
a
few
examples
around
that
in
the
main
repository.
B
B
It's
a
bit
more
involved
personally,
I'm
not
sold
on
the
use
case
because
I
feel,
like
the
main
value
of
stratified
team,
is
the
attack
things
that
come
packaged
with
it.
I
don't
think
there
is
a
huge
value
in
writing
your
own
and
registering
them
inside
your
thread
team
when
using
it
as
a
library,
but
maybe
we'll
see
some
use
cases
around
that
and
then
there
is
the
most
interesting
part.
B
The
attack
techniques
reference,
so
this
is
automatically
generated,
so
each
attack
technique
has
some
metadata
and
these
docs
are
automatically
generated
from
that
and,
as
I
showed
before,
maybe
we
can
see
another
one,
but
for
the
page
you
have
the
description,
the
instructions,
how
you
can
detect
it
and
yeah
it's
pretty
simple
to
get
started.
You
know
you
go
there,
click
on
the
copy
copy,
the
command,
you
just
run
it
in
your
terminal
and
it
should
work
out
of
the
box.
B
B
B
I
think
it's
a
name
that
people
have
heard
a
lot
and
I
like
the
fact
that
if
you
hear
something
red
team,
you
kind
of
know
what
it's
about
and
stratus
is
just
because
it's
a
cloud,
it's
a
kind
of
cloud
and
well
stratus
is
mostly
for
cloud
environments.
Initially
it
was
only
for
aws,
then
we
did
support
for
humanities.
So
that's
where
the
name
is
is
coming
from.
There
was
some
hesitation
around.
B
D
B
Yes,
so
that's
a
great
question
thanks
for
asking-
and
I
should
maybe
have
had
more
context
but
yeah.
The
motivation
is
mostly.
I
want
to
detect
some
specific
attack
techniques.
How
can
I
easily
reproduce
them
to
make
sure
that
you
know
that
my
detections
are
working
and
when
you
do
it
once
it's
easy,
it's
very
simple
to
do.
B
It's
mostly
for
like
someone
who
is,
writing
detections
or
is
expecting
some
kind
of
threat,
detection
and
wants
to
be
able
to
have
a
simple,
or
at
least
an
encapsulated
way
to
to
to
trigger
them?
If
that
makes
sense
and
like
you
know,
for
communities,
I
think
for
quite
a
lot
of
scenarios,
it
could
have
been
just
by
scripts,
even
if
this
process
makes
it
easier.
I
think
when
you
have
some
some
prerequisites
for
aws,
there
are
some
cases
where
it's
very
hard
to
produce
it.
Typically,
we
have
an
attack
technique
around.
B
B
B
A
Yeah,
it
seemed
like
you
want
to
do
like
it's
almost
like
making
a
meal
for
yourself
where
you
just
want
to
eat,
but
all
the
prerequisites
take
so
much
time
to
get
done
and
then
you're
almost
feeling
like.
Oh
it's,
too
late.
Now
I
almost
feel
like
I
spend
so
much
time.
I
don't
know
if
the
meal
is
going
to
be
good,
so
this
kind
of
just
automates
all
the
beginning,
part,
and
then
you
can
almost
home,
deliver
your
meal.
