►
Description
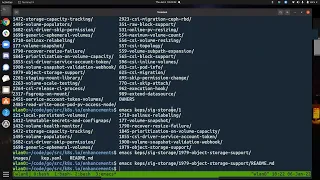
Kubernetes Storage Special-Interest-Group (SIG) Object Bucket API Design Meeting - 06 Jan 2022
Meeting Notes/Agenda: -
Find out more about the Storage SIG here: https://github.com/kubernetes/community/tree/master/sig-storage
Moderator: Sidhartha Mani (Minio)
A
Yep,
thank
you
shane,
so
jeff
had
a
question
about
the
cap.
I
wanted
to
also
provide
an
update
about
where
we
are.
I
I
pinged
michelle
yesterday
and
she
said:
she'll
take
a
look
at
the
cap
again,
but
but
jeff
has
been
reviewing
it
as
well,
and
one
of
the
questions
he
had
was
about
using
brownfield
buckets.
A
We
tried
to
open
the.
I
just
tried
to
open
the
github
page
for
it
it's
a
little
slow,
so
I
ended
up
just
opening
it
up
locally
and
we'll
just
quickly
go
over
how
we
do
brownfield
buckets
so
to
to
kind
of
bring
the
context
back.
So
we
we
decided,
we
will
call
the
resources
for
creating
a
bucket
as
bucket
claim
and
we
don't
have
any
bucket
access
requests
or
bucket
requests
anymore.
A
You
it's
just
like
pvcs,
persistent
volume
claims
and
pvs,
so
you
have
bucket
claims
and
buckets
and
then
to
get
access.
We
just
have
one
object,
called
bucket
access,
so
in
case
of
green
field
buckets
or
buckets
that
we
create
fresh
new,
we
create
a
bucket
claim,
and
that
ends
up
calling
the
appropriate
functions
in
cosy
to
create
the
bucket
itself
and
in
case
of
brownfield
buckets
or
existing
buckets.
B
A
B
Yeah,
what
I'm
gonna
I'll
make
some
wording
suggestion
changes
around
brownfield
now
that
I
have
heard
definitively
that
a
bucket
claim
is
not
needed
for
the
brownfield
use
case.
So
I
will
now
not
knowing
that
now
I
will
read
some
review
some
of
my
own
comments
and
some
of
those
paragraphs
and
said
I'll
just
make
some
suggestions
for
wording
that
will
make
it
clearer,
at
least
for
me.
It
would
make
it
clear.
A
B
A
Okay,
perfect
yeah.
We
appreciate
the
review
jeff
so
yeah.
Do
it?
Do
it
yourself?
Okay,
so
really
the
one
thing
that's
that's
really
left
to
address
is
reference
policy,
but
before
that,
before
we
jump
into
a
new
discussion,
I
wanted
to
ask
so
so
we
really
want
to
get
this
kept
through.
We
really
want
to
move
things
along.
A
I
know
michelle
is
going
to
take
a
look,
but
what
else
can
we
do
so?
Who
can
help
with?
So
I'm
just
looking
for
ideas
of
what
can
we
do
to
push
this
along
faster
like?
Should
we
just
keep
pinging
michelle,
or
is
there
someone
else
also
what
what
like
I
want
to
come
up
with
some
plan
of
of
how
we
address
this?
Let's
just
assume
that
you
know
the
cap
is
in
a
decent
state
like
ready
to
be
reviewed,
maybe
not
perfect
yet,
but
ready
to
be
reviewed.
C
C
C
A
A
D
E
C
C
D
C
A
A
A
A
G
A
G
To
not
do
this
in
the
alpha
version
and
we
had
convinced
ourselves
that
there
was
a
way
to
do
it
eventually.
I
I
don't
know
if
I
mean
I
remember
that
the
version
of
the
reference
policy
we
were
looking
at
a
couple
months
back
was
like
not
not
done
like
it
was
a
proposal
or
something
yeah.
Is
it
the
case
now
that,
like
reference
policies,
are
officially
supported
or
usable.
G
I
mean
I
don't
know
how
we
can
implement
anything
until
there's
something
to
implement
on
top
of,
and
I'd
be,
very
nervous
about,
delving
too
deep.
You
know,
while
they
might
still
change
something
on
us,
unless
we
want
to
like
go
get
involved
in
that
community
and
talk,
you
know,
make
suggestions
about
how
they
should
design
the
reference
policy
or
something
I
I.
G
G
So
so
my
concern
with
if
we're
gonna
go
off
and
develop
our
own
thing,
then
the
the
way
that
the
original
reference
policy
was
sketched
out
was
significantly
more
complicated
than
what
we
needed
right,
because
we
we
don't
need
any
type
information
or
any
of
that
kind
of
stuff.
Because
it's
all
inferred
right.
We
know
what
the
what
the
referent
type
is
and
what
the
referee
type
is,
and
it's
just
a
matter
of
putting
some
names
in
an
object.
And
then
it's
a
name
space
right.
That
says
this.
A
G
A
D
A
G
G
A
G
G
D
G
B
G
A
G
I
mean
it
would
be
nice
to
say,
like
this.
Guy
has
read
only
access,
but
the
problem
is,
is
that
you
have
to
put
the
bucket
access
class
name
in
the
reference
policy
and
the
meaning
of
the
bucket
access
class
can
change
over
time
right
if
someone
changes
the
bucket
accident,
and
so
it's
like
from
a
security
perspective,
it's
it's
kind
of
like
standing
on
sand.
A
A
A
A
G
F
D
C
C
G
A
Yeah
so
they
have
yeah.
This
is
kind
of
what
we
talked
about
and
we
thought
was
not
a
good
idea,
so
they
have
this
option
of
sharing
is,
is
defined
up
front
same
name.
Space
is
the
default
option
only
routes
in
the
same
namespace
as
this
gateway
may
be
attached,
all
is
all
name
spaces
and
selector
is
based
on
names.
We
selectors.
G
G
Yeah
yeah,
I
mean
normal
people
can't
edit
namespaces
so
yeah
I
mean
you
could
imagine
a
scheme
like
that
right.
So
so
then,
at
that
point
for
the
buckets
whole
lifetime,
the
question
of
whether
a
given
bucket
access
can
bind
to
it
or
not.
Can't
change
right.
It's
a
well!
I
guess
in
a
selector
someone
could
modify
the
names,
but
I
don't
know.
A
G
G
Is
there
a
better
way
because,
because
the
reference
policies
had
some
advantages,
but
it's
also
feels
extra
complicated
to
have
another
object
for
this
strange
use
case,
not
a
strange
use
case.
I
mean
like
it's
a
use
case
that
we
expect
to
be
reasonably
common
and
and
to
like,
introduce
a
whole
new
object
just
to
address
it.
A
G
Although
the
problem
was
was
that
it
could
only
be
modified
by
the
administrator,
we
we
never
created
a
scheme
to
upfront
at
bucket
creation.
Time
say
I
want
to
share
my
bucket
with
alice,
find
bob,
or
vice
versa,
whereas
they
seem
to
have
done
that
we
were
always
assuming
that
this
was
something
you
would
do
after
the
fact.
G
A
So
the
difference
between
them
and
us
is
gateways
are
admin
controlled
entirely
from
what
I'm
reading,
I
don't
think
a
gateway
can
be
defined
by
a
user,
so
the
admin
gets
to
create
the
gateway
with
these
parameters
up
front,
so
the
admin
would
know
what
are
the
other
name
spaces.
The
admin
would
know
just
they'll
have
full
view
into
the
cluster,
whereas.
G
So
so
so
you
could
take
the
view
that
you
know
four
buckets
that
are
meant
to
be
shared
across
multiple
namespaces,
like
those
are
going
to
be
the
responsibility
of
the
administrator.
The
administrator
should
create
a
special
shared
bucket
name
space,
put
all
the
shared
buckets
there
and
set
up
whatever
needs
to
be
set
up
to
give
everyone
access
to
those
shared
buckets
and
then
for
people
who
create
their
own
buckets
in
their
own
name
spaces
like
those
ones
can't
be
shared
like
you
could
look
at
it.
G
That
way,
and
just
say
this
is
an
admin
problem
and
ordinary
users
can
do
self-service,
but
they
can't
do
self-service
sharing.
I
think
we
had
been.
We
had
been
presume.
You
know
we
had
been
going
along
the
lines
of.
We
want
two
individual
users
to
just
be
able
to
collaborate
by
creating
a
bucket
and
then
sharing
it.
But
I
don't
know
if
that
really
exists
in
the
kubernetes
world.
Like
I
don't.
A
G
You
know
namespace
transfers
for
things
like
pvcs
and
snapshots
that
are
that
don't
require
an
administrator,
because
we
we
somehow
thought
that
was
an
important
thing
to
do
and
what
I,
what
I
don't
know
is:
are
there
people
out
there
who
are
like
sharing
a
kubernetes
cluster
but
not
sharing,
namespaces
and
talking
to
each
other
and
wanting
to
collaborate
like?
Is
that
a
thing
that
happens
or
is
it
just
the
case
that
people
who
work
together
are
in
the
same
name,
space.
G
Yeah,
but
I
mean
I
I'm
trying
to
think
of
a
real
world
situation
where
you
have
a
kubernetes
cluster
and
a
bunch
of
users,
that
kind
of
don't
trust
each
other,
but
still
need
to
interact
a
little
bit,
and
so
they
have
their
own
name
spaces
and
then
they're
yeah.
You
can
share
services
across
name
spaces
and
presumably
there's
some
out-of-band
communication
where
you
become
aware
of
them,
but
like
for
data
storage,
is
it
the
same?
G
I'm
nervous
about
spending
a
bunch
of
our
time.
You
know
trying
to
design
that
when
it
might
not
be
something
anyone
cares
about.
You
know.
The
more
important
thing
is
the
self-service
use
case
and
the
the
admin
creating
a
shared
one
use
case
and
then
maybe
a
distant
third
is
two
two
ordinary
users
collaborating
with
each
other.
A
G
A
So,
generally
this
you
know
in
any
big
data
workload
that
kind
of
sends
data
to
object,
storage,
there's
a
there's,
a
separate
set
of
services
that
that
push
data
in
and
there's
a
separate
set
that
actually
process
it.
I'm
I'm
looking
at
like
one
one
one
common
use
case
that
we
see
with
many
other
deployments.
A
A
Who
does
this?
I
mean
there's
another
question
that
kind
of
comes
along
the
way
when
you
ask
that
question,
which
is,
which
is
how
many
buckets
are
going
to
be
there?
If
there's
going
to
be
lots,
something
that
that
that's
going
to
tax
the
admin
a
lot,
then
then
it's
reasonable
to
say
the
user
should
be
able
to
do
it,
but
I
don't
think.
That's
generally
the
case.
E
The
way
they're
doing
it
here
seems
to
make
sense
for
that
a
user
would
choose
whether
they
don't
want
it
to
be
shared.
They
want
to
be
shared
with
all
or
they
want
to
be
shared
with
the
select
group
that
is
known
and
then,
if
there's
a
new
group
that
comes
along
or
a
new
namespace
that
comes
along,
then
the
admin
would
have
to
get
involved.
To
add
that
namespace
as
an
option
right.
E
E
Or
all
right
or
the
selection
that
they
know
of
at
that
time
at
the
time
of
creating
the
bucket
yeah.
And
if,
if
you,
in
that
one-off
use
case
or
whatever,
that
a
new
namespace
comes
along,
that
you
want
to
share
a
bucket
with
an
admin,
would
have
to
get
involved
to
modify
the
namespace
either
modify
the
namespace
or
modify
the
the
selector
list
so
that
that
new
name
space
could
be
added.
But.
G
A
A
Yeah,
but
I
like
what
we're
talking
about
what
you're
saying
is
we're
not
aiming
for
a
100
self-service
it
is.
It
is
self
service.
As
long
as
you're
you
define
upfront
who
all
gets
access
to
your
bucket,
but
if
you
need
changes
beyond
that,
you
get
an
admin
involved
and
okay,
so
then
then
comes
the
question
of
who
all
can
you
allow
to
access
this
bucket?
So
let's
say
I'm
user
foo
and
I'm
working
in
namespace
foo.
A
E
A
E
E
A
E
A
A
A
A
G
Well,
if
you
wanted
flexibility,
you
would
use
the
selector
scheme
and
then
put
like
labels
on
namespaces
and
do
it
that
way
and
you
get
your
flexibility.
But
if
you
did
pick
static
listed
namespaces,
it's
not
clear
that
an
admin
could
modify
that
list.
Maybe
he
can.
Maybe
he
can't
depends
on
admission.
A
That's
all
I
have
for
today.
I
want
to
start
implementing
this.
I
want
to
start
writing
code.
I
think,
since
we've
been
kind
of
going
back
and
forth,
we've
kind
of
just
fallen
back
on
just
having
something
to
show,
so
I'm
just
going
to
start
start
writing
some
code
and
and
having
something
that
that's
demo-able
well.
Well,
it
might
not
be
fully
flushed
out
or
production
quality.
A
It
should
be
demo
already
at
least.
I
think
the
way
the
way
we
can
start
showing
it
to
people
and
even
proving
that
some
of
our
designs
work
and
while
implementing
we
might
even
run
into
some
issues
that
that
we
didn't
foresee
so
so
I
so
I'm
just
gonna,
I'm
announcing
it
here,
because
if
there's
anyone
here
who
who
wants
to
contribute
or
anyone
here
who
knows
someone
who
can
contribute,
please
please
put
them
in
touch
with
me.
