►
Description
Kubernetes Storage Special-Interest-Group (SIG) Object Bucket API Design Meeting - 02 December 2021
Meeting Notes/Agenda: -
Find out more about the Storage SIG here: https://github.com/kubernetes/community/tree/master/sig-storage
Moderator: Sidhartha Mani (Minio)
A
A
B
A
A
Can
you
can
you
still
hear
me
yep,
okay,
perfect,
all
right,
so,
let's
continue
where
we
left
off.
Actually
so
as
of
last
week.
Well
that
week
before
that
last
we
talked
about
was
our
final
design
and
jeff,
and
I
talked
after
that
and
we
went
over
our
authentication
method.
The
one
issue
was,
as
I
started,
flushing
it
out
more.
While
writing
a
lot
of
the
conversation
we'd
had
before.
A
C
A
Yeah
yeah
exactly
so
so
the
thing
is
during
our
discussions.
We
discussed
a
lot.
I
I
believe,
ben
you
brought
up
some
concerns
that
I'm
just
worried.
We
might
be
ignoring
concerns,
that's
the
one
thing,
and-
and
what
I
want
to
do
today
is
make
sure
that
we're
not
and-
and
let
me
start
by-
sharing
and
showing
you
what
I
mean
so
this
is
this
is
where
we
left
off
two
weeks
ago.
So
just
to
give
a
quick
recap,
I
mean
these
things
remain
the
same
bucket
bucket
class
and
bucket
request.
A
These
are
the
permissions
that
you
request
and
the
driver
is
supposed
to
provision
iam
credentials
and
a
provision
service
account
that
gets
tied
to
a
workload
identity
now
tying
it
to
workload.
Identity
is
the
part
that
I
have
some
questions
about.
So
take.
Take
google,
for
example,
and
let's
say
you
are
creating
a.
Let
me
just
pull
up
the
google
vcloud.
E
A
So
there
is
a
there
is
a
step
where
we
need
to
so
there
is
a
step
where
there's
like
a
weird
dependency
issue,
so
we
have
to
yeah.
I
think
I
think
the
issue
is
with
the
service
account.
So
say
you
have
a
service
account
and
you
have
to
provide
that
service
account
name
while
requesting
the
im
style
authentication.
A
D
A
D
A
D
A
Yeah
we
could
yeah
exactly,
it
has
to
exist
up
front,
and
the
other
issue
is
if
I,
if
I
have,
if
I
have
a
namespace,
where
I
want
the
service
account,
I
don't
want
the
default
service
account
to
get
certain
credentials
see
the
thing
is,
it
might
not
be
for
security
reasons
as
much
as
you
don't
want.
One
service
account
to
have
all
of
the
credentials
like
let's
say
I
have
three
different
buckets.
D
B
A
Right
right,
yeah,
yeah
authorization,
so
so
if
it
has
access
or
if
it
provides
access
to
more
than
one
bucket
and
and
from
a
manageability
perspective,
I
let's
say
I
don't
want
it
to
have.
You
know,
provide
access
for
more
than
one
bucket
now,
I'm
forced
to
create
multiple
service
accounts
which
is
okay,
but
but
if
there
are,
if
the
workload
already
depends
on
the
default
service
account
for
for
a
bunch
of
other
privileges.
Now
we
are
asking
for
for
anything
but
cozy.
A
D
I
think
I
see
where
you're
going,
but
like
this,
this
feels
like
in
just
an
inherent
disadvantage
of
using
I
am
style
authentication
is
that
you
know
you're
using
one
credential
for
multiple
purposes.
Of
course,
you're
going
to
have
situations
where
you
can't
do
exactly
what
you
want,
but,
like
that's.
A
D
E
D
It's
a
disadvantage
of
im
style,
authentication
that
your
identity
determines
what
you
can
do
and
you
can't
have
multiple
identities
so,
but
I
I
I
remember
when
sod
and
andrew
were
here
way
back
at
the
beginning
and
they
were
pushing
for
im
style
authentication
and
my
interpretation
of
the
request
was
like
it's
just
so
convenient.
Surely
we
should
just
let
people
do
it
like
not
like?
It
enables
some
amazing
use
case
that
you
couldn't
otherwise
achieve
it's.
Just
we
have
this
thing.
It
already
works
like
it's.
D
So
it's
it's
simple
and
it's
arguably
more
secure
than
access
key
secret
key,
at
least
for
a
single
pod
in
a
single
bucket.
So
let's
just
enable
it
but
yeah
when
you
have
multiple
pods
and
multiple
buckets
and
multiple
service
accounts,
and
you
start
to
worry
about
which
ones
can
access
which
buckets?
Of
course
it's
going
to
get
ugly
and
that's
nothing.
You
can
do
about
that
other
than
switch
to
access
key
secret
key
where
you
get
fine
grain
control
again,.
A
Make
sense
so
so
yeah
so
and
and
also
the
other
thing
is
our
responsibility
with
im
doesn't
end
here.
We
need
to
work
with
cloud
sdks
to
mine
workload,
identity,
credentials
from
cosy,
really
or
kubernetes,
so
current
sdks.
They
know
they
know
how
to
get
say.
Current
object,
storage
sdks
know
how
to
get
credentials
from
instance
merit
later
so
they
know
how
to
talk
to
the
instant
instance,
metadata
service
and
and
get
credentials
cosy
would
have
to
either.
A
D
D
There
is
a
I
don't
know
top
of
my
head,
but
there's
a
standard
place
that
you
can
go
into
any
and
it
can
be
disabled.
You
can
have
a
pod
that
has
no
service
account
token
in
it,
which
slightly
speeds
up.
You
know
how
fast
your
pod
comes
up,
because
cubel
has
less
work
to
do,
but,
but
if
you
don't
disable
it,
cuba
always
puts
it
in
a
standard
place
and
again,
we'd
have
to
look
up
what
that
is,
but.
A
A
Okay,
so
so
take
this,
take
this
example.
So
how
would
this
work?
I
just
want
to
go
through
the
example
to
make
sure
you
know
we
cover
all
bases,
I'm
coming
back
to
the
original
issue
I
raised,
because
I
I
saw
this
example
and
I
figured
this
is
a
good
example
to
work
off.
Of
so
add
image.
Full
secret
service
account,
so
you
patch
a
service
account
to
add
image,
full
secrets.
D
The
the
actual
service
account
token
does
get
plumbed
in
so
that,
if
you,
if
you
try
to
create
a
kubernetes
client
inside
your
pod,
it
will
have
all
of
the
appropriate
information
to
go,
find
the
kubernetes
api
endpoint
for
the
cluster
that
it's
running
in
and
have,
and
the
identity
of
the
service
account
and
any
all
the
standard.
Kubernetes
sdks
know
how
to
go.
Find
that
token,
as
one
of
their
many,
you
know,
bootstrapping
methods
for
getting
credentials
and,
of
course
they
have
fallbacks
and
optional
ways
of
doing
other
things,
but
they
just
know.
A
D
If,
if
your
bucket.json
says
service
account
authentication,
then
the
credentials
are
in
this
file
and
we
spell
it
out
and
and
then
how
you
get
from
that
to
like
an
sdk
reading
that
file
and
doing
the
rest
of
the
work
is
somebody
else's
problem
now
we're
interested
in
that
solution,
but,
like
we
don't
have
to
solve
it
right,
we
can
punt
on
that
as
long
as
we're.
As
long
as
we're
clear
about
like
the
service,
you
know
when
you
see
service
account
in
your
bucket.json.
A
D
And
we
would
want
a
proof
of
concept
that
there
is
at
least
a
way
to
then
take
that
surface
account
and
go.
Do
all
the
things
you
need
to
do
to
go
after
and
and
I'm
not
enough
of
an
expert
to
know
how
you
would
do
that.
But
I
I
do
worry
that,
like
service
accounts,
might
look
different,
whether
you're
running
in
like
an
on-prem
cloud
versus
like
a
google
cloud
versus
like
an
amazon
cloud.
A
Yeah
and
one
more
thing
is
so
you
know
the
driver
would
have
to
set
the
service
count
to
point
to
or
to
assume
the
role
of
a
cloud
service
account
and
when
it
does
that
there
are
like
see
roles
that
I
am
workload:
identity,
user.
So
the
roles
are,
I
think,
the
user
id
or
the
service
account
id
the
cloud
service
account
id
is
added
as
an
annotation
into
into
the
into
the
service
account
itself.
A
So,
in
order
to
revoke
you
need
to
remove,
remove
the
annotation
from
the
community
service
account.
So
so
it
looks
like
you
know.
The
kubernetes
service
account
gets
an
annotation
from
you
know
from
tying
this
service
account
to
the
cloud-based
service
account,
and
that
needs
to
be
taken
on
that
that
that
should
be
a
part
of
the
part
of
the
orchestration.
A
D
D
Like
a
gke,
I
I
don't
know
the
answer
to
that,
but
I'm
saying
you
could
go
determine
that
empirically,
okay,
without
too
much
trouble,
but
you're
right
that,
then
we
have
the
responsibility
as
the
cozy
side
car
to
when
we're
minting
a
credential
or
when
we're
granting
access
to
a
bucket,
and
it
is
a
service
account
style
access.
Yeah.
We
got
to
go,
pull
the
information
and
shove
it
down
into
the
driver
and
say
give
access
to
this
thing
and
and
what
that
is,
could
vary
from
implementation
implementation.
A
D
But
that's
not
that's,
not
us
we're
just
interested
in
what
the
gke
account
is
that
is
associated
with
the
surface
account
right,
we're
not
going
to
be
attaching
or
detaching
these
things.
Someone
else
does
that
and
then
we
just
go
see
what
it
is
and
pull
it,
pull
it
and
then
push
it
down
into
the
driver,
and
then
the
driver
goes
and
talks
to
the
gke
you're,
the
the
google
control,
assuming
this
is
like
a
google.
It
goes
and
talks
to
that
control,
plane
and
says.
D
I
mean
it
would
matter
like
if,
if
you're
going
to
like
create
a
pvc,
for
example,
you'd
want
to
you,
want
the
the
g
there,
the
I
forget
what
a
gc
epd
that
gets
created
to
be
owned
by
the
person
who
created
that
pvc,
so
like
the
the
gcepd
driver,
has
an
interest
in
knowing
what
your
google
service
account
is.
When
you
do
something
so
that
it
when
it
goes
and
talks
to
the
google
control
plane
it
can
it
can,
it
can
act
as
you.
A
A
A
A
C
D
A
B
A
D
A
Was
our
original
stance?
I
agree
that
was
our
original
stance,
but
but
but
tim
hawking
said
it
clearly
that
unless
we
have
a
complete
story
around,
maybe
not
complete
a
clear
story
around
about
your
identity.
You
know
he
he
is
still
like
holding
it
back
and
it's
fair.
It's
it's!
Okay!
It's
it's
a
feature
request.
It's
has
to
be
done
at
some
point
I
mean
it
comes
at
the
cost
of
not
pushing
it
right
away,
but
it's
okay.
A
We
are
kind
of
gated
on
on
tem
approving
so
we'll
work
with
it,
but
but
just
to
be
clear,
me
included
all
of
us
who
are
attending
the
meetings
regularly,
we're
all
thinking
that
we
should
move
forward
with
what
we
have
today.
We
we
should
get
to
alpha
state
already
and-
and
we
kind
of
disconnected
from
from
the
api
reviews,
I'm
you
know.
I
see
that
as
one
of
the
issues
we're
facing
and
thinking
about
doing
something
about
it.
Well,
I'm
not
thinking
I'm
doing
something
about
it.
A
Basically,
I
want
to
involve
sad
or
timid
the
process
a
little
bit
more,
because
they're
really
hard
to
reach
and
the
worst
part
is
they
have
no
clue
what's
going
on
here
right
now,
so
so
at
least
I
plan
to
just
think
them
about
the
details
of
where
we're
at
just
every
week
that
way,
they're
not
completely
lost,
maybe
they
just
they
just
they
don't
even
have
to
respond.
They
just
have
to
look
at
it.
D
Because
because
I
don't
know-
and
you
don't
know-
I
don't
know
if
anyone
else
here
has
enough
familiarity
with
like
exactly
how
gcs
works
in
a
gke
context,
can
you
just
take
your
kubernetes
service
account
and
go
and
access
a
gcs
bucket
with
that?
If
the
appropriate
operations
have
been
done
outside
of
kubernetes
like
I
I
I
imagine
you
can,
but
I
don't
know.
A
It's
not
going
to
be
the
same
as
someone
who
architected
it
see.
The
thing
is
I
can,
I
can
find
out
from
a
user
perspective,
but
when
designing
an
api
around
it,
I'd
want
to
know
what
the
reasoning
behind
some
of
these
style
of
authentication
was.
I
have
a
fair
bit
of
idea
because
you
know
minio
client
is
used
in
aws
simply
because
it
has
a
very
focused
footprint
and-
and
you
know
we
we
support.
You
know
in
our
client
we're
fully
aw
aws
compatible.
What
that
means
is
we.
D
So
also
so
hold
on
to
be
clear.
I
think
we
have
to
not
necessarily
prototype,
but
like
proof
of
concept,
this
each
scheme
working
before
we
put
it
in
the
spec
and
like
have
someone
walk
through
the
steps
manually
and
do
all
the
things
to
convince
ourselves
that
it
could
work
that
that
seems
like
a
prerequisite
for
putting
it
in
the
spec
is
at
least
we've
done
it
one
time
manually
and
seen
that
it
gave
us
the
result
that
we
expected.
A
A
It's
just
we're
going
down
a
path
when
I
get
into
identity,
there's
there's
a
whole
bunch
of
possible
ways
to
implement
authentication
authorization
for
object,
storage.
Another
one
is
ldap,
another
one
is
active
directory.
Another
one
is
open.
Idc
open,
open
id
connect,
open,
int
connect,
so
it's
just
it's
it's
a
rabbit,
hole
and
yeah.
A
A
A
They
were
moving
away
from
from
s3
to
mineo,
and
you
know
they
were
in
china
and
they
were
having
issues
with
the
accessibility
and,
and
the
thing
was
our
sdk
supports.
Our
client
sdk
supported
min
io.
Is
not
workload
and
cli
based
servers
are
not,
and
there
was
such
a
strict
requirement
for
them
now
we're
looking
at
what
we
can
do,
but
I
presume
that
anyone
who's
going
to
use
object,
storage
using
koji
will
have
strict
requirements
like
that
too.
A
A
No,
my
wife,
I
just
went
out
for
a
second
that's
what
I
was
asking
anyway,
so
so
yeah,
so
so
all
right.
So
another
thing
to
add
to
the
list
is
just
just
orchestrating
this
annotation.
So
I'll,
we'll
manually
go
over
the
steps
we
we
can
do
it.
Maybe
even
here
I
don't
know
how
long
it
will
take
to
set
up
a
set
up
a
google
cloud,
gke
cluster.
But
let's
say
it's
quick.
A
A
A
A
A
A
A
E
A
E
A
So
yeah,
let
me
go
through
the
steps,
maybe
I'll
even
do
a
recording
of
it
if
needed,
screen
recording.
Actually
it
might
be
easier
to
just
do
it
from
the
command
line
like
you
mentioned,
but
but
let
me
go
through
the
steps
and
and
I'll
see
what's
needed,
but
it
looks
like
extra
orchestration
steps
are
needed.
I
mean
we'll
just
have
to
let
the
driver
mention
this
part,
but
this
annotation
setting
and
removal
cozy
has
to
orchestrate-
and
I
don't
you
know
so
far.
A
D
Okay,
so
my
intuition
is
that
the
work
that
we're
going
to
have
to
do
is
to
extract
the
information
from
the
service
account
in
the
access
granting
sidecar
when
we
see
a
bucket
access-
and
it
has
a
service
account
name
in
it.
We're
going
to
have
to
go
crack
open
the
service
account
and
pull
out
the
relevant
details
so
that
we
can
shove
them
down
to
the
driver
through
the
grpc
that
says,
grant
access
to
bucket
or
whatever.
I
forget
what
it's
called
the
grpc.
A
B
B
B
A
C
D
Is
that,
oh
no,
I
thought
you
were
talking
to
jeff,
I'm
just
saying
like
we
have
to
go
through
this
process
and
and
and
see
what
it
looks
like
you
know.
Have
a
kubernetes
cluster
have
a
service
account
have
a
bucket
that
was
created
outside
of
kubernetes,
see
if
we
can
take
a
kubernetes
service
account
and
find
the
thing
that
we
need
to
grant
access
to
the
bucket
and
then
see
if
a
pod
running
with
that
service
account
has
a
credential
that
can
be
used
to
access
the
bucket.
D
D
A
E
A
A
A
D
A
A
A
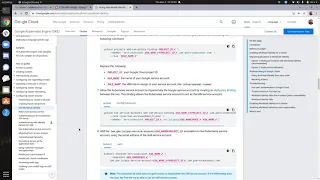
I
mean
you:
we've
all
used
command
line
interfaces.
This
is
pretty
straightforward,
it
seems
like,
but
I
don't
know
what
the
issue
here
is
I'm
exactly
following
the
same
format
like
you
can't
tell
me
this
doesn't
match
this
format.
Maybe
it's
a
project
name.
I
think
it's
project,
name
which
they're
not
looking
for
a
numerical
value.
So
let
me
do
menu
there.
You
go.
A
C
A
Yeah
so
I'll
I'll
get
permissions
to
do
this
I'll
set
up
a
cluster,
and
I
will
try
this
out,
but
but
the
resolution
we
got
today
was
one.
We
need
to
do
extra
orchestration,
that
that
is
something
new
and
two
is
yeah.
We
should
just
go
through
the
steps
once
before.
We
confirm
and
put
it
in
the
spec
yeah
I'll
I'll
bring
you
up.
A
A
D
D
A
Fair
enough,
okay,
so
so
yeah.
So
so,
basically,
what
we
learned
was
just
try
it
out
see
if
it
works.
Do
that
extra
orchestration
and-
and
the
response
to,
I
think
we're
putting
users
in
this
weird
situation
where,
if
they
want
one
service
account
for
a
particular
part
to
have
multiple
privileges,
they
need
to
orchestrate
that
somehow.
A
Then
they'd
have
to
do
that
along
with
this
and
anything
else
that
gets
along
the
way.
So
so,
let's
say
they
use
service
account
for
some
other
service,
maybe
not
for
gk,
maybe
not
for
talking
to
the
cloud
or
the
infrastructure,
but
let's
say
they
use
it
for
provisioning
access
or
authorizing
the
part
to
some
other
service
running
in
the
same
cluster.
A
A
A
A
A
D
I
I
thought
we
had
said:
if
it
was
service
account,
we
would
just
have
a
just,
have
a
a
sentinel
that
says
service
account
and
then
you
would
go
to
the
normal
place
to
get
your
service
account.
I
thought
that's.
That
was
the
plan,
because,
because
there
is
only
one
when
once
you're
inside
the
pod
it
all
you
have
is
what
cubelet
has
plumbed
down
to
you
and
I
don't
think,
there's
a
circumstance
where
cubelet
gives
you
more
than
one.
So
the
name
would
be
superfluous.
A
D
A
D
Right,
we
just
say
we
just
say
service
account
and
then
with
no
value,
and
then
we
document
that
when
you
see
that
you
go
look
in
that
file
path,
where
the
service
account
is
and
figure
it
out
and
and
that's
the
recovery,
that's
where
cozy's
responsibility
ends
is
to
point
you
towards
the
service.
Account
token
so
like
that.
F
And
type
no,
no
like
I
have,
like
so,
let's
say
the
port
in
the
door
json
like
if
you
specify
the
service
account
name.
At
least
the
user
can
know
that,
like
his
sport
service,
account
is
different
from
what
we
expect
right.
Otherwise,
the
user
will
get
the
dna
dollar.
He
doesn't
know
what
matter
is
done.
D
D
A
A
A
D
A
Oh,
it's
two
o'clock
where
you
are:
okay,
all
right
have
a
have
a
good
rest
of
your
afternoon.
Ben,
have
a
good
rest
of
your
day,
see
you
and
different
good
night,
but
but
yeah
I'll
update
the
spec.
Once
I
try
this
out
and
quick
quick
summary,
I'm
gonna
use
type
here
and
authentication
again
like
this
authentication
type
here
and
then
there's
authentication
type
here.
If
it's
iam,
then
access
key
secret
key
would
be
empty.
