►
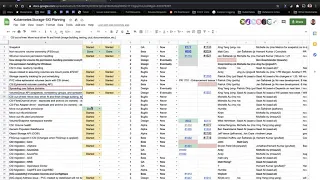
From YouTube: Kubernetes SIG Storage 20201203
Description
Kubernetes Storage Special-Interest-Group (SIG) Meeting - 03 December 2020
Meeting Notes/Agenda: https://docs.google.com/document/d/1-8KEG8AjAgKznS9NFm3qWqkGyCHmvU6HVl0sk5hwoAE/edit#heading=h.fry0hwxnun10
Find out more about the Storage SIG here: https://github.com/kubernetes/community/tree/master/sig-storage
Moderator: Saad Ali (Google)
A
A
A
A
B
We
don't
have
any
new
update.
The
last
update
still
holds
true
in
the
one.
The
next
release,
which
is,
I
think,
121,
will
work
on
two
items.
At
least
the
allow
volume
expansion
moving
to
pv
and
copying
it
to
pv,
and
then
the
node
secrets
that
still
has
to
be
reset
in
the
csi
community,
maybe
so
yeah
and
then
the
third
item
is
the
recovering
from
recess
very
well.
We
did
not.
B
A
C
C
Rotation
for
webhook
is
also
merged,
so
the
next
one
we're
trying
to
get
in
is
there
is
a
pr
update
controller
based
on
the
v1
snapshot
apis,
so
that's
been
reviewed,
just
need
to
get
that
one
merged,
and
then
we
also
need
to
update
the
the
client
go
module
to
v4.
I
think
yeah.
So
I
think,
after
that
we
are,
should
be
good
to
cut
the
release,
so
we're
getting
close.
C
A
A
E
A
F
Yeah,
no
no
changes
were
done
for
120.
In
this
release.
We
got
clarity
on
oh
well,
that's
the
other
line
item.
So
no
no
changes
there.
I
would
like
to
add
perhaps
that,
but
I,
but
I
started
working
a
little
bit
this
quarter
on
running
the
external
provisioner
alongside
each
node,
which
wasn't
originally
part
of
that
spreadsheet
here,
but
it
does
touch
on
this
capacity
tracking
a
little
bit
because
there
was
one
part
in
the
cap
about
that
particular
way
of
running
it
and
it
looks
like
we'll
we'll
have
it
implemented
for.
F
A
F
This
quarter,
we
basically
froze
or
they
didn't
didn't,
do
any
further
development.
But
we
had
one
important
meeting
on
the
api
questions
and
the
conclusion
was
that
for
the
generic
ephemeral
inline
volumes,
we
continue
as
planned
with
the
same
api,
so
that
that
will
is
something
that
I
I
intend
to
work
on
for
121.
Now
we
in
the
same
meeting
we
discussed
how
to
proceed
with
csi
ephemeral
in
nimoriums
and
agreed
that
the
epi
needs
to
be
revised.
F
Specifically,
we
want
to
move
the
top
level
entry
in
the
volume
source
structure
from
csi,
which
is
also
a
bad
name
for
it
into
something
that
is
a
bit
more
or
a
bit
more
more
obvious
about
what
it
is.
I
don't
remember
what
we
agreed
on,
but
it's
all
in
the
in
the
tracking
issue
in
enhance
kubernetes
enhancements,
there's
one
one
enhancement
issue
for
csi
efferent
volumes,
and
I
I
summarized
basically
the
next
step
in
that
issue.
F
A
C
C
A
A
A
A
G
So
I
got
some
help
from
michelle
on
how
to
proceed
with
the
image
building
on
this
one
planned
to
work
on
this
in
this
month.
At
the
same
time,
there's
actually
a
community
pr
that
came
in
for
the
nfl
subtitle
project
in
image,
building
via
github
actions
wanted
to
check
here.
If
that's
something
that
we
want
to
proceed
with,
or
should
we
go
with
the.
E
A
A
H
H
H
A
F
H
In
october,
I
had
a
we
started
up
the
meeting
the
series
of
meetings
to
to
design
this
and
those
have
been
going
well
and
and
this
week
I
have
been
making
a
lot
of
progress
on
this,
so
we're
aiming
at
1
21
for
this.
In
the
course
of
working
on
this,
I
managed
to
find
a
bug
in
the
prisoner
side
car
and
I
have
a
new
pr
that
is
already
up
for
the
controller
and
that
will
handle
populator
crds,
I'm
working
on
the
new
sort
of
sample,
populator
implementation
and
so
yeah.
A
A
H
H
A
A
A
E
A
A
A
A
A
Okay,
next
item
is
the
next
set
of
items
are
co-owned
between
sig
storage
and
other
cigs.
The
first
few
are
coned
with
sig
apps,
the
first
of
which
is
an
issue
with
pvcs
where
stateful
sets
create
pvcs.
But
when
you
delete
the
stateful
set,
the
pvcs
are
not
deleted.
It
would
be
nice
if
they
were
auto
removed.
A
A
A
A
A
Sounds
good
so
we'll
go
ahead
and
get
this
moved
to
the
121
release.
Thank
you.
Shane,
for
the
update.
Next
item
is
size
memory
backed
sizing
and
empty
der
memory,
backed
volume
as
minimum
of
pod
allocatable
memory
on
host.
I
don't
recall
seeing
this
one
before
looks
like
derek
is
working
on
it
and
vermont's
helping.
A
Cool
next
item
is
a
ask
from
sig
architecture
to
move
our
mount
library
out
from
kubernetes
utils
into
a
standalone
repo
and
have
that
repo
be
replicated
in
the
staging
directory.
Sereni
was
helping.
With
this
last
status.
Update
was
ran
into
some
problems
and
needed
to
revert
the
c
advisor
change
will
continue
after
120,
so
we'll
go
ahead
and
move
this
to
121.
A
Perfect
so
I'll
go
ahead
and
mark
that
as
started
as
well
and
we'll
go
ahead
and
get
that
moved
over
to
the
121
spreadsheet
looks
like
shane
has
already
created
a
new
tab
here,
so
we
can
go
ahead
and
get
started
on
on
populating
that
moving
back
to
the
agenda
before
we
continue.
I
had
a
question
for
everyone
in
the
next
meeting
is
in
two
weeks,
which
is
december.
17Th.
A
H
A
Yeah,
so
if
we
skip
the
31st,
the
next
available
opportunity
would
be
the
14th
which
would
land
us
into
kind
of
the
beginning
or
like
almost
halfway
into
the
first
month
of
the
next
cycle.
So
I
was
thinking
if
we,
if
we
do
our
planning
session
on
the
17th
it'll
set
us
up
well
for
q1
and
then
and
then
we
can
on
the
7th.
When
we
reconvene
we
can
come
back
and
and
reassess
and
re-add
items
as
needed.
A
A
A
A
E
H
Read
the
pvc
annotations
and
you
know
to
to
sort
of
prototype
some
new
feature,
and
we
had
talked
about
the
potential
of
just
like
taking
the
pvc
annotations
and
merging
them
with
the
storage
class
parameters
and
passing
them
all
down.
Every
time
you
do
a
crate
volume
but
like
that,
creates
real
problems.
In
terms
of
you
know
the
possibility
for
conflicts,
the
possibility
of
user
overriding,
the
administrator's
intent,
the
the
the
fact
that
administrators
may
not
like
that
idea
entirely
and-
and
so
I've
been.
So.
H
I
basically
kind
of
gave
up
on
this
a
while
ago,
but
I
had
a
new
idea
a
couple
months
back
when
I
was
looking
at
a
the
extra
metadata
option
on
the
external
provisioner.
The
idea
is
this.
I
would
like
to
add
a
a
new
command
line
parameter
to
the
external
provisioner
sidecar,
which
lets
you
specify
a
prefix,
and
then
only
pvc
annotations
that
are
that
are
have
that.
H
H
H
H
Other
prefixes,
where
you
have
some
sort
of
a
you
know:
name,
dot,
name,
dot,
name,
slash,
annotation
name
and
then
a
value
where
that
name
would
be
some
sort
of
vendor
domain
name,
presumably,
and-
and
it
also
addresses
the
issue
of
you-
know
administrators
wanting
to
disable
this,
because
the
administrator
can
just
modify
the
sidecar
container
definition
to
not
specify
this
prefix
and
then
the
sidecar
won't
pass
anything
down.
So
so
it
puts
control
in
the
hands
of
both
vendors
and
controllers.
H
To
turn
this
feature
on
sorry,
vendors
and
administrators
to
turn
this
feature
on
if
they
want
it
and
it
addresses
it,
addresses
this
need
for
people
to
sort
of
prototype
things
in
pvc
annotations
without
many
of
the
problems
we've
had
in
the
past.
So
I
just
wanted
to
sort
of
throw
this
out
there
to
the
whole
group
and
see
if
people
hate
it
or
if
people
think
this
has
any
promise
at
all
as
being
a
way
to
sort
of.
Let
you
optionally
pass
down
some
pvc.
H
H
Specifically
worried
about
because
they
they're
both
the
administrator
and
the
the
user
of
their
particular
kubernetes
cluster.
They
know
which
csi
plug-in
they
have
and
they
want
to
enable
some
sort
of
functionality,
and
we
know
I'll
tell
you
our
csi
plugin
already
does
the
thing
I
mentioned
earlier
today,
where
we
we
just
go:
read
the
pvc
annotations
ourselves
and
it's
it's
just
kind
of
gross.
So
it's
not
that
people
can't
do
this
today
and
it's
not
that
it's
a
good
thing
to
do
because,
as
sod
mentioned
like
this
is
an
ansi
pattern.
A
You
know
it
might
sound
evil,
but
I
I
feel,
like
the
kind
of
icky
things
that
you
have
to
do
to
make.
This
work
are
a
good
thing
because
it
forces
the
driver
vendor
to
realize.
Should
I
be
doing
this
because
it's
not
a
standard
supported
thing,
but
I
worry
that
if
we
do
provide
a
standard
way
of
doing
this
like
a
flag,
then
it
becomes
a
oh
well,
it's
a
supported
feature.
A
Of
course,
I'm
going
to
start
using
it,
and
I
I
like
the
way
that
you
put
it,
which
was
you
know
this
should
be
used
for
prototyping
and
you
know
trying
new
things,
but
I
worry
what
it's
going
to
end
up
being
is
we'll
end
up
with
a
set
of
csi
drivers
that
require
the
use
of
this
flag.
They
won't
work
without
it
and
and
we
will
end
up
with
a
generation
of
csi
drivers
that
are
effectively
not.
A
H
A
Agree,
I
think
the
the
difference
is
kind
of
it's.
It's
a
psychological
one
right,
it's
a
hey,
I'm
doing
something
that
I
probably
shouldn't
be
because
I
have
to
do
all
this
icky
weird
custom
stuff
to
make
this
happen
versus.
Oh,
this
thing
is
supported
out
of
the
box
so
like
it
must
obviously
be
okay.
A
H
Yeah
yeah,
I
mean
that's,
that's
the
portability
guarantee
which
is
is
really
valuable.
It's
just
that
there
are
some
users
that
don't
care
and
they
they
want
to.
You
know,
get
at
vendor
goodies
and
you
know
the
pressure
to
provide
those
goodies
is,
is
immense
and
so
yeah
we
we
do
the
the
gross
thing
and
read
the
read:
the
pc
annotations.
A
H
A
F
H
H
A
I
H
No,
I
mean
when
you're
down
in
the
trenches
you
frequently
end
up
with
these
weird
sticky
problems
where
it's
like.
Oh,
if
only
I
just
had
you
know
some
extra
information,
I
could
solve
this
better
right
so
yeah
I
come
across
those
not
that
specific
problem,
but
you
know
that
kind
of
stuff
right,
so
so
so
what
I'm
hearing
side
is.
That
is
that
you
would
prefer
to
just
make
this
hard
simply
to
discourage
it.
A
C
That
is
why
I'm
kind
of
concerned,
when
I
see
that
pr
to
add
this
extra
metadata
in
external
snapshot
so
just
to
follow
what
is
there,
for
example,
provisioner,
because
we
do
see
a
lot
of
requests
right
for
adding
this
type
of
metadata
per
person
snapshot
or
per
pvc.
But
what
do
we
want
to
accept?
What
do
we
want
to
say?
No,
I
don't
know
what
is
the
criteria
yeah.
