►
From YouTube: Cloud Native Austin - Securing the Mesh
Description
No description was provided for this meeting.
If this is YOUR meeting, an easy way to fix this is to add a description to your video, wherever mtngs.io found it (probably YouTube).
A
A
A
His
talk
will
be
in
infused
devsecops
into
your
kubernetes
and
service
mesh
life
cycle.
Briefly.
Actually
I
don't
know
that
we
need
to
cover
this
because
I
think
I
see
all
friendly
faces
tonight.
All
folks
who've
been
here
before
so
this
is
the
cloud
native
austin
meetup.
It's
s,
sort
of
it's
well,
the
I
think
the
second
in
the
world.
If
I
get
it
right,
that's
been
sponsored
by
the
cncf
kind
of
the
first
one
of
the
first
to
go
into
the
fold.
A
A
Let's
take
a
moment
if
we
would
so
usually
we're
meeting
kind
of
physically
and
that's
typically
with
people
who
are
based
in
and
around
the
austin
texas
area,
but
we're
not
bound
to
those
physical.
You
know
walls
anymore,
rather
we're
bringing
together.
I
think
people
who
are
just
generally
interested
in
the
same
topic,
sort
of
irrespective
of
where
you're
coming
from
so
if
we
can
it'd
be
nice
to
exchange
a
little
bit
tonight
to.
A
B
C
B
D
I'll
get
I
mean
we
don't
we're,
not
hiring
we're
always
looking,
but
unfortunately
with
code,
we're
not
hiring
right
now,
but
our
company
is
moving
to
kind
of
kubernetes
environment
for
all
of
our
products.
So
that's
why
I
decided
to
come
here
tonight
kind
of
learn
a
little
bit
more
about
service
mesh
and
securing
service
mesh,
we're
using
istio
right
now
as
our
service
mesh.
So
I'm
still
new
to
that,
but
excited
for
the
content
later.
A
D
And
so
it's
a
big
journey.
Our
team,
my
team,
specifically,
is
involved
in
a
lot
of
the
analytics
like
analytics
products
around
that.
So
that's
kind
of
what
I'm
looking
to
to
learn
a
lot
more
about,
specifically,
is
how
this
kind
of
plays
into
I'm
not
going
to
say
big
data,
but
those
kinds
of
solutions
to
to
problems.
A
A
A
A
C
A
E
A
Sure
yeah
anybody
attended
some
virtual
events
here
recently
and
thought
that
they
were
pretty
well
done,
like
the
platform
that
was
being
used,
was
sort
of
facilitated
the
the
the
hallway
meet
and
greet
the
social
aspect
of
it.
I've
been
to
a
couple,
and
I
don't
know
that
you
know
they
were
you
know
it
was
still
like
half
the
experience
you
get
well
like
a
quarter
of
the
experience
that
you
actually
get
in
person.
That's
right.
E
A
Well,
yeah,
I've
done
a
couple
last
one
I
was
at
was.
I
was
speaking
at
all
things
open,
which
was
actually
supposed
to
be
here
in
austin
a
little
while
ago
and
they
didn't,
but
they
held
it
virtually,
and
I
forget
the
name
of
the
platform
they
had,
but
they
they
part
of
what
they'd
done
was
a
little
bit
of
speed
networking
which,
for
someone
as
long
winded
as
me,
is
quite
the
challenge,
but
people
are
generally
pretty
friendly,
it's
kind
of
a
nice
way
to
anyway.
A
For
me,
I'm
giving
two
talks
at
kubecon,
eu
and-
and
I
think
I'm
supposed
to
record
him
next
week-
maybe
I
should
actually
start
there's
too
much
going
on,
which
is
why
I'm
super
excited
that
I'm
not
speaking
tonight
rather,
this
fine
gentleman
here
is
heim
is
a
number
of
things,
someone
some
a
friend
actually
someone.
I
I've
really
enjoyed
over
the
last
few
years,
just
tickled
to
see
heim's
company
be
acquired.
A
C
C
So
we're
kind
of
the
where
those
two
lines
meet,
and
there
are
so
many
efforts
in
vmware
with
the
pivotal
and
heptio
acquisitions,
around
kubernetes
and
with
the
carbon
black
last
line
acquisition,
as
well
as
doctoring
around
security,
so
we're
trying
to
bring
it
all
together
to
kind
of
create
a
cohesive
story
around
intrinsic
security
for
cloud
native-
and
this
is
it's-
it's
a
very
large
organization,
but
it's
all
very
nascent.
It's
all
young
and
fresh,
and
it's
exciting
yeah.
A
Wow,
okay,
yeah.
That
is
exciting,
because
it
would
be
some
opposite
words
that
I
would
use
to
describe
large
corporate
technology
organization
and-
and
I
totally
believe
you
that
it's
not
particularly
for
for
any
number
of
reasons
and
and
that
the
way
that
you've
described
it
yeah,
you
guys,
you
know
formally
octorine
like
right,
bridging
the
divide
between
those
those
two
exact
things.
So
that's
a
perfect
lead-in
into
into
hearing
more
from
you
just
kind
of
about
this.
This
subject
I'll
give
you
a
moment
to
share
so.
A
A
D
It's
definitely
an
area
I
need
to
educate
myself
in
more.
I
feel
like
it's
one
of
those
things
that
you
kind
of
use
some
of
the
generally
more
popular
features,
but
then
there's
a
whole
layer
of
really
really
clean
architecture.
You
can
pull
off
if
you
use
the
service
mesh
in
the
right
way,
which
is
kind
of
an
area
I'm
not
totally
comfortable
in
but
hoping
to
learn
more
about
it.
Yeah.
A
C
B
A
B
B
A
A
E
A
Yeah,
it
was
I'll
put
it
this
way,
and
this
is
the
way
that
one
of
my
friend
nick
jackson
had
put
it
to
me.
So
I
can't
claim
the
credit,
but
the
morning
that
it
happened.
I
was
on
a
call
with
him
and,
and
he
had
articulated
it
like
well,
actually
this
isn't
quite
how
he
said
it,
but
it
was
a
little
bit
like
what
core
os
was
to
red
hat
or
core
os
was
to
open
shift.
A
Maybe
rancher
is
a
bit
of
that
to
susie,
as
a
matter
of
fact,
like,
I
think,
there's,
there's
tons
of
examples
where
older
well,
where
organizations
that
have
got
older
offerings,
but
maybe
deeper
pockets,
need
to
can
reach
out
and
pull
themselves
forward
with
with
an
acquisition.
I
think
that
I
guess
I
believe
they're
found
the
rancher
founders
when
they
say:
hey,
they're,
they're,
pretty
excited
about
it
and
they're.
Probably
gonna,
stick
around
and
and
try
to
do
some
good
things.
E
C
D
A
B
C
That's
that's
lee's,
presenting
all
right
so
nice
to
meet
you
all.
As
lee
mentioned
him
hellman.
Until
recently,
I
used
to
be
the
cto
and
co-founder
of
octorin.
Without
in
octorine
we
were
developing
a
security
solution
for
kubernetes.
We
started
focusing
on
network
security,
but
we
expanded
to
look
at
other
things,
like
configuration
of
kubernetes
workloads
and
kind
of
securing
the
whole
pipeline
of
helping
and
deploying
workloads
into
kubernetes,
as
well
as
monitoring
them
and
runtime
to
look
for
threats.
C
So
today,
I'm
going
to
cover
several
topics
around
security
for
kubernetes
in
general
and
then
in
the
end,
I'll
specifically
talk
about
service
mesh
and
how
it
can
help
you,
and
what
do
you
need
to
do
for
it
to
help
you
actually
secure
your
workloads
again,
we
are
the
goal.
Here
is
not
really
to
secure
this
service
mesh
or
to
secure
kubernetes.
It
is
to
secure
our
applications.
C
C
All
right
so
kubernetes
is
a
game
changer
not
just
as
a
platform
and
and
how
it
affects
the
architecture
of
software,
but
really
it
has
very
deep
implications
on
on
the
organization
as
well
and
both
those
changes.
The
change
in
the
stack
and
the
change
in
the
organization
have
a
very
profound
security
implications.
C
C
There
is
no
affinity
anymore
between
the
network,
identity
of
a
workload
and
what
it
actually
does.
The
the
second
aspect.
The
organizational
aspect
means
we're
now
moving
from
a
very
predictable
deployment
model
to
a
distributed
and
continuous
deployment
model,
which
means
a
developer
pushes
code
and
at
some
point,
that
code
is
actually
being
deployed
into
production,
and
there
is
no
time-
and
there
is
no
way
to
have
a
very
organized
process
of
validating
security
policy
on
on
workloads
as
they
are
being
continuously
developed
and
deployed.
C
So
probably
most
of
you
are
seeing
something
like
this
diagram.
It's
the
traditional
kind
of
cncf
diagram
of
the
text,
the
cloud
native
text
stack,
which
means
we
have
our
cloud.
We
have
kubernetes
and
the
service
mesh
as
the
new
infrastructure
layer
and
then
on
top
of
it
we
run
our
applications
using
containers
and
the
way
we
kind
of
learn
to
look
at
kubernetes
is
is
a
little
bit.
C
C
We
see
it
as
a
the
new
api
for
infrastructure
is
code,
so,
as
organizations
want
to
create
a
more
cloud
agnostic,
more
uniform
way
to
provision
workloads
both
in
on-prem
in
hybrid
cloud
scenarios
in
multi-cloud
scenarios.
Kubernetes
is
really
that
unified
api
that
allows
you
to
provision
your
storage,
your
network,
your
compute,
to
manage
your
our
back
to
your
secrets,
the
privileges
of
each
workload.
C
C
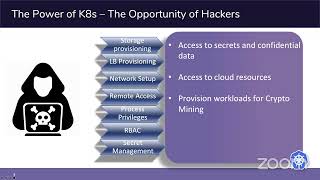
So
so,
let's
talk
about
a
little
bit
the
the
risk
of
having
such
a
powerful
api
at
hand.
So
when,
when
hackers
see
that
that
that
api
and
they
can
quickly
realize
how
they
can
exploit
it
for
their
own
benefit,
the
first
one,
obviously
the
main
goal
of
hackers
is
to
access
secrets
and
confidential
data
that
can
be
that
can
be
achieved
again
by
taking
advantage
of
this
api.
C
C
C
C
C
C
C
C
C
C
C
Or
there
is
no
real
way
to
track
which
users
have
access
to
your
cluster,
because
in
kubernetes
there
is
no
such
thing
as
user
object,
so
objects
and
groups
are
all
entities
that
live
in
the
client
certificates
they
do
not,
and-
and
so,
if
we
have
a
user
that
belongs
to
a
group,
that
group
has
a
certain
capabilities
in
our
cluster.
We
will
not
know
that
this
user
still
has
that
access
and
and
once
those
credentials
are
compromised,
they
can
be
used
for
many,
many
things
that
we
mentioned.
This
is
a
very
powerful
api.
A
C
C
C
But
not
no
great
tools
exist
that
obviously
the
main
best
way
to
avoid
that
is
not
to
use
client
certificates,
but
really
to
use
a
more
manageable
authentication
method
like
tokens.
So
if
we're
running
in
in
public
clouds,
usually
we
would
connect
our
authentication
mechanism
to
the
clouds
public
cloud
authentication
mechanism,
so
that
will
be
our
cube,
iam
authenticator
in
aws
or
connected
to
gcloud
in
gke
or
to
your
active
directory
in
azure.
C
A
C
All
right,
so
what
what
would
our
attacker
want
to
do
once
they
got
a
foothold
in
our
cluster?
So
the
first
thing
that
we
would
expect
the
attacker
to
do
is
is
privileged
escalation.
So
you
are,
let's
say
you
have
a
shell
running
now
inside
a
container
that
container
has
a
certain
service
account
in
kubernetes,
which
defines
what
the
container
can
do
against
the
api
server.
C
So
a
tiller
is
part
of
the
helm
package
manager
and
at
least
the
helm
version.
Two
and
one
of
the
nice
things
about
taylor
for
attackers
is
that
it
had
cluster
admin
privileges
as
well
as
no
authentication,
so
it
was
running
in
your
cluster
and
as
long
as
you
had,
you
were
in
any
pod
in
your
cluster,
and
you
didn't
have
a
network
policy
that
limited
you
from
accessing
tiller.
C
C
The
second
path
to
to
an
attack
is
the
container
escape.
So,
as
we
know,
containers
provide
some
level
of
isolation,
but
not
it's
not
a
virtual
machine.
We're
still
sharing
the
kernel
with
all
the
other
pods
in
on
the
node,
so
if
we
can
take
advantage
either
of
the
privilege
of
the
container
itself.
C
The
the
third
thing
an
attacker
would
look
like
would
look
for
is
secrets.
Obviously
there
are
some
secrets
that
have
to
do
with
the
application
itself
database
passwords
aws
over
any
cloud
api
tokens
as
well
as
kubernetes
related
secrets.
So
again,
once
you
are
able
to
reach
secrets,
you
have
all
the
service
account
tokens
so
that
pretty
much
means
you're
a
cluster
admin
again,
because
you
can
authenticate
yourself
as
any
service
account
in
the
classroom
and
the
fourth
one
is
the
more
conventional
attack
pattern
of
lateral
movement.
So
we
start
exploring.
C
A
I
I
have
a
couple
and
one
is
that
with
the
container
escape
or
no
yeah
the
container
escape,
maybe
it's
with
the
privilege
escalation
as
well.
But
I
guess
it's
been
a
while,
since
I
looked,
you
know
what
what's
the
current
state
of
a
given
a
sort
of
a
vanilla,
kubernetes
deployment
with
its
container
run
time
requiring
that
container
runtime
to
run
as
root.
C
So
so
containers
are
now
are
not
run
as
root
by
by
default
anymore
and
docker
agent
does
not
run
as
root
as
well,
as
runs
as
the
docker
in
the
docker
group,
with
the
docker
user,
so
that
has
been
resolved
a
while
ago.
Still
there
were
incidents
where
run
c
was
vulnerable
to
a
privilege,
escalation
attack
that
allowed
you
to
become
root
on
the
host
itself,
that
that
was
fixed.
A
C
Or
yes,
so
that
that
is
really
bad
practice.
If
you're
putting
your
secrets
in
environment
variables,
it's
probably
there
are
two
ways
to
do
it.
One
is
by
importing
the
the
value
of
the
environment
variable
from
a
secret
from
a
kubernetes
secret,
which
is
not
the
preferred
way
to
do
it,
because
you
can
still
look
at
the
environment
variable
of
each
process.
So,
if
you're
in
a,
if
you
have
some
access
to
different
processes
on
the
host,
you
can
read
all
their
environment
variables.
C
People
mistakenly
think
that
read
only
permissions
in
kubernetes
are
not
that
bad,
but
really
a
read.
Only
permission
in
kubernetes
is
exactly
the
same
as
cluster
admin,
because
the
first
thing
you'll
do
is
you'll
read
the
what's
the
service
token
access
the
services,
the
service
accounts,
token
for
a
cluster
admin
and
go
from
there.
A
Last
question:
for
me:
the
lateral
movement
in
the
network,
just
as
it
pertains
to
service
meshes,
is
you
know
that
some
of
these
meshes
will
you
will
require
the
net
admin
capability
in
order
to
you
know,
do
some
traffic
redirection
between
the
application
containers
and
the
side
card
proxies
and
some
of
the
service
meshes
will?
Will
leverage,
maybe
cni
to
remove
the
need?
C
B
C
Well,
maybe
the
most
important
one,
but
a
lot
of
the
attack,
vectors
and
attack
patterns
that
we
talked
about
can
be
avoided
by
having
some
sort
of
admission
control.
So
admission,
control
in
kubernetes
means
we're
looking
at
the
spec
of
each
workload
that
is
being
deployed
and
we
applying
some
kind
of
some
set
of
rules
to
decide
whether
this
is
acceptable
for
us.
C
So
one
of
the
cases
that
that
lee
mentioned
is
the
net
admin
capability,
so
it's
very
natural
that
we
would
want
to
have
a
way
to
prevent
containers
with
net
admin
capability
from
being
deployed
in
our
cluster.
That
can
be
achieved
with
what
we
call
a
validating,
webhook,
so
validating
webhook
means
any
api
call
can
be
routed
to
that
validating
service
via
webhook,
and
that
service
will
apply
some
policy
and
will
decide
whether
to
admit
the
word
the
resource
or
to
reject
it.
C
Very
common
admission
controllers
are
the
image
policy
webhook,
which
looks
at
the
image
of
the
containers
that
we
want
to
deploy
and
checks,
whether
it
comes
from
a
registry
that
we
trust,
whether
it's
a
repository,
that
we
trust
whether
it
has
been
scanned.
If
we
have
some
scanning
solution,
so
probably
most
of
the
container
scanning
solutions
today
offer
some
kind
of
an
image
policy
web
hook.
C
C
C
So
a
little
bit
about
what
how
admission
controllers
operate
and
again
there
are
two
kinds:
the
first
one
is
the
mutating
admission
control,
that's
the
one
that
takes
a
yamo
or
a
resource
definition
at
that
point,
it's
in
json
format
and
actually
modifies
it
based
on
some
kind
of
rule
set
of
rules.
Istio
sidecar
injector
is
probably
the
most
famous
mutating
admission
controller.
C
C
Go
to
the
next
slide,
we'll
see
how
our
back
looks
like.
So
again
we
have
our
roles
or
if
it's
across
the
entire
cluster,
then
it's
called
the
cluster
role,
which
says
which
operations
we
can
do
on
which
resource
and
then
we
bind
it
either
to
a
service
account
that
can
be
used
by
one
or
more
workload
or
to
a
user
or
a
group
of
users,
and
our
back
is
is
hard
to
to
manage
again.
C
So
we
mentioned
the
read-only
access
which
seems
harmless,
so
we
just
allow
the
get
operation
on
all
resources
that
is
actually
equivalent
to
a
cluster
admin
privilege
in
kubernetes.
So
it
is
very,
it
is
recommended
that
any
role
would
actually
enumerate
all
the
resources
that
you
want
to
access
in
all
the
operations
that
you
would
like
the
subject
to
have.
C
It
is
very
recommended
to
use
an
external
tool
to
kind
of
audit
your
rbac
recommendations
or
even
automatically
manage
them.
There
are
some
scripts
that
analyze
your
auditor
and
can
tell
you
how
does
that
compare
to
your
rbac
policy?
So
if
you
have
permissions
that
you're
not
using
it
will
tell
you.
C
B
C
C
B
C
And
yes,
there
are
many
tools
out
there
that
can
help
you
we're
for
admission
control.
We
talked
about
opa
and
and
gatekeeper,
which
uses
opa.
Our
backmanager
is
a
nice
tool
to
visualize
your
our
bag
and
control
it
in
a
more
atomic
way.
There
are
certain
changes
that,
when
you're
doing
rbad,
you
have
to
do
it
together,
our
back
manager
does
it
for
you.
There
are
many
other
tools
for
visualizing
your
outback
policy.
C
C
C
C
A
C
C
It
has,
as
william
morgan
would
like
to
remind
everyone
and
hashicorp
has
their
console
connect
service
mesh,
so
in
octarine
has
we
have
our
own
service
mesh
as
well,
and
and
to
those
of
you
now
still
don't
know
what
service
mesh
is
a
service
mesh
is
a
proxy
and
a
control
plane.
It
means
we
have
a
proxy
running
as
a
sidecar
running
alongside
each
workload
handling
network
functions,
and
then
we
have
some
control
plane
that
configures
all
those
on
those
proxies
the
most
common
proxy
out.
C
There
is
envoy
that
was
developed
by
lyft
used
in
istio
and
console
connect
and
octarine
and
others.
Linker
d
has
their
own
proxy
and
there
are
a
few
other
proxies
out
there
moving
on
so
the
nice
thing
that
service
mesh
gives
you
when
it
comes
to
security,
is
that
concept
of
zero
trust?
Zero
trust
means
that
all
the
communication
in
your
cluster,
so
not
just
coming
from
the
internet,
should
be
treated
as
untrusted,
which
means
everything
needs
to
be
encrypted.
C
Obviously,
another
way
to
limit
the
blastery
use
of
an
attacker
is
by
using
an
authorization
policy.
This
is
another
thing:
that's
supported
by
most
service
meshes
today,
so
you
can
define
layer,
7,
very
granular,
access
control
policy
for
your
cluster
again
to
do
it
well
is
is
challenging,
but
if
you
do,
then
you
get
you
really
minimize
your
risk
of
exposure
in
terms
of
lateral
movement
and
extraction
of
sensitive
data.
C
Specifically,
eco
provides
the
egress
gateway
component
that
you
can
route
all
your
traffic
through
and
then
you
can
use
firewall
rules
to
make
sure
that
no
other
service
will
actually
be
allowed
to
talk
to
the
internet
to
to
go
outside
of
your
cluster.
And
then
you,
you
get
a
pretty
good
control
over
what
kind
of
communication
leaves
your
question.
C
Many
in
many
cases
we
see
deployments
that
are
partial,
so
we
we
only
instrument
some
of
our
workloads,
but
not
all
of
them,
because
there
is
some
overhead
in
latency
and
cpu
for
the
service
mesh.
So
some
of
our
services
are,
they
can't
be
instrumented,
and
then
we
need
to
create
exceptions
in
the
authentication
and
encryption
policy
for
accessing
those
services.
C
C
Egress
control
is
not
trivial
to
implement,
so
an
egress
gateway
is,
is
an
optional
feature
in
many
cases,
not
deployed
authorization
policy
again
very
useful,
but
does
not
exist
by
default.
So
if
you
just
deployed
the
service
mesh,
you
don't
have
any
authorization
in
place.
Everything
is
allowed
that
which
might
be
strange
for
people
who
are
familiar
with
older
platform
as
a
service
solutions
like
cloud
foundry,
for
example,
where,
if
you
didn't
whitelist
something
if
you
didn't
allow
it
specifically,
it
wasn't
allowed
in
kubernetes
and
initial.
C
So
what
can
you
do
to
avoid
all
those
pitfalls
again?
The
first
one
is
avoid
partial
deployments
as
much
as
possible.
It's
not
always
possible,
but
instrumenting
as
many
services
as
possible
means
you
get
the
best
visibility
means
you
get
the
most
encryption
authentication
and
the
most
ability
to
create
access,
control
and
egress
management.
C
C
Implement
an
egress
gateway,
even
though
it's
hard
it's
again,
there
are
no
successful
attacks
without
egress
traffic.
If
you
can't
connect
to
the
internet
there
is
it
doesn't
work,
it's
so
controlling
your
eagers
traffic
is
extremely
important
it.
It
has
to
also
be
accompanied
with
network
with
some
sort
of
firewall
rules
or
a
security
group
that
prevents
outbound
access
from
the
cluster.
By
anything.
That's
not
your.
Your
eager
escape.
C
Use
some
tool
that
will
allow
you
to
create
and
maintain
at
least
privilege
of
the
authorization
policy.
So
in
octarine
we
built
such
a
tool,
but
it's
really
not
that
hard.
Once
you
have
visibility
once
you
know
which
traffic
you
have.
You
just
take
that
information
and
you
can
very
or
somewhat
easily
convert
it
to
an
authentication
policy
in
your
in
your
service
mesh,
so
that
visibility
that
service
mesh
provides
and
the
ease
of
creating
an
authorization
policy
is
something
to
take
advantage
of.
C
C
C
D
A
A
D
C
Right,
so
that's
where
a
good
policy
engine
has
to
come
into
place
because
you
can
define
shadow
policy,
so
you
you
can
define
policies
that
are
going
to
create
a
a
log
but
are
not
going
to
actually
block
traffic.
So
there
is,
there
are
ways
to
you
know,
put
a
policy
in
place,
but
not
actually
suffer
the
consequences
of
that
policy
right
away.
C
You
create
a
permissive
authorization
policy.
You
still
need
a
tool
to
actually
look
at
those
logs
and
see
where,
if
you
are
having
any
sorts
of
violations
and
and
yes,
it
was
a
challenge
and
that's
one
of
the
solutions
that
we
actually
provided
in
octo,
which
was
that
visibility
and
alert
mode.
So
you
can
create
a
policy
but
not
block.
C
C
A
A
I
wish,
as
a
matter
of
fact,
we
should
stop
the
recording
before
I
swear
too
much
more
I'd
said
that
I'd
give
a
link.
I
don't
know
how
interesting
it
is
or
not,
but
we
were
sort
of
talking
about
acquisitions.
There's
a
just,
I
think,
just
as
a
point
of
interest
to
the
cncf
and
to
some
of
its
member
companies.
It
keeps
track
of
just.
B
A
A
E
A
E
A
A
Yeah
yeah
they've
been
released.
They
skunks
are
amazingly
like
some
of
the
softest
sweetest
of
the
animals
that
we
get,
but
we've
got
a
ton
of
raccoons
that
have
been
released
on
our
property.
So
speaking
about
the
the
this
rooster,
he
nests
just
on
the
back
porch
and
we
have
raccoons
that
come
back
nightly.
They've
been
released,
they're
out
doing
their
thing,
but
they
come
back
and
funny
enough.
They
also
go
for
the
dog
food
and
turns
out
hey.
