►
Description
Все видео курса https://www.youtube.com/playlist?list=PL9tzQn_TEuFUakOn-IY9cDQL2ztNzZunh
Совместный курс NEAR & 4ire Labs
Подписывайтесь, чтобы получать обновления о новостях NEAR, акциях, запуске проектов, баунти, хакатонов
Русскоязычное сообщество NEAR https://t.me/near_protocol
Твиттер https://twitter.com/near_protocol
Общение с разработчиками https://t.me/openwebdev
Follow the latest from NEAR Protocol on:
Website: https://near.org/
Discord: https://near.chat/
Blog: https://near.org/blog/
Twitter: https://twitter.com/NEARProtocol
GitHub: https://github.com/near https://github.com/nearprotocol
#Blockchain #FutureIsNEAR #NEAR #nearprotocol #rust #wasm #assemblyscript #раст
A
A
It
is
to
read
the
details
if
you
have
a
special
desire
for
it,,
because
the
topics
of
reality
are
very
voluminous,,
especially
the
topic
that
concerns
the
collection,.
The
documentation
in
this
sense
is
very
good,.
It
is
in
English,
I
immediately
warn
you,,
but
if
you
have
a
desire
to
understand
this
in
more
detail,,
I
will
provide
links
the
same
lecture,
I.
Probably
look
at
the
handwriting
like
this.
In
this
topic,
if
you
have
questions
during
the
presentation,
do
not
be
shy,.
Let's
try
to
answer
them,.
A
B
A
How
where
memory
is
used,,
as
you
remember,
from
the
last
lecture,
Kirill,
spoke
in
detail
about
the
concept
of
storing
tanks,
and
in
this
case,
drop.
It
is
actively
used,,
and
so
we
have
it,
and
later
the
coup
corresponded,.
We
can
store
variables
variables,
given
data
can
be
stored
at
a
rack
or
in
a
heap,,
and
this
is
of
such
great
importance.
Because,
as
you
might
guess,.
A
The
data
storage
model
that
involves
storing
on
the
stack
allows
you
to
access
data,
naturally
faster,
due
to
the
fact
that
this
data
is,
as
you
remember,
as
Cyril,
gave
an
example
with
flights.
You
can
give
an
example,
you
know,
with
plates,
when
one
plate
lies
on
another
and,
accordingly,.
When
we
want
to
get
access
to
one
of
the
plates,,
we
gradually
remove
them.
A
A
Important
thing
is
just
to
remember
where
exactly
the
storage
takes
place,
and
this
is
an
important
nuance,
because
for
example,,
if
we
operate
with
arrays,,
then
this
will
impose
certain
obligations
to
the
developers,
and
so
the
arrays
and
layers
will
be
stored
on
the
stack
and
collection.
Of
course,
it
is
stored
in
a
bunch
and
here,,
as
you
can.
See,
I
gave
several
such
water
examples
and
how
the
description
of
the
array
happens.
Here
we
describe
the
director
here.
A
B
B
A
A
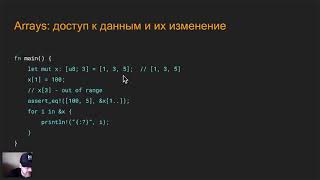
What,
in
this
case,
is
the
arrays
of
the
array
is
a
set
of
such
grouped
yes
and
they
are
stored
in
a
well-defined
sequence.
They
are
also
stored
in
lines
in
this.
You
need
to
remember,
and
this
sequence
is
it
not
natural
does
not
change
for
example,.
We
have
the
first
description,
and
here
an
important
nuance
is
that
the
array
is
described
through
underwater
brackets
and
its
size
must
be
known
at
compile
time.
A
B
A
A
Be
located,,
including
joints,,
very
efficiently,
and
quickly
to
operate
on
its
own,
in
principle,,
once
it
can
do
automatic
type
inference,,
but
still
for
an
explicit
understanding
of
what
type
of
array.
Sometimes
it
still
makes
sense
to
indicate
some
explicit
type
in
our
case,.
The
axis
about
this
is
the
remaining
four
more,,
including
and
so
on,
that
is,
the
most
different
and
2
2
caps
that
are
in
the
growth,.
This
is
what
you
can
do:
an
array
of
tasks
from
repeating
elements,,
that
is,
as
you
can
see,.
B
A
B
A
A
1
and
5
is
at
the
index
of
some
programming
languages,
Yandex
and
starts
with
one,
for
example,
for
july,,
but
here
it
is
important
to
remember
that
the
access
of
array
elements
in
Russia
starts
from
0
will
not
connect
from
zero
to
this,
therefore,.
We
indicate
that
x
with
index.
1
is
100,,
which
means
that
we
replace
the
number
3
with
a
table,
and
this
is
not
yet
what
it
will
happen
if
we
will
try
to
access
an
element
that
is
not
worn
in
our
case,.
A
This
is
naturally
a
rich
error
and,
let's
see
what
happens
if
we
check
which
elements
are
already
here,,
an
additional
gig
is
already
introduced
on
it.
A
little
later,
consider
this
slice
because
arrays
and
slice,
and
they
are
very
tightly
intertwined
and
here,
in
fact,.
We
are
the
element
in
question
from
the
first
to
the
last,
and,
as
you
can
see,
here,
we
have
the
numbers
of
the
rack..
It
is
also
very
easy
to
moderate.
The.
B
A
B
A
When
we
make
the
for
loop,,
we
use
the
method
and
peter
function,,
as
you
can
see,
the
literator
actually
and
this
iterator,
what
it
does
it
iterates
through
all
the
elements
that
are
in
this
array,
there
is
a
special
method
called
it
dies,
it
just
does
the
following:
it
returns
to
stupid,
as
you
can
see
here,
we
have
heat
contained
from
two
elements,
and
this
dome
itself
contains
elements
such
as
yandex.
We
here
we
put
a
variable
and
and.
B
A
A
Are
quite
a
lot
of
methods
in
the
documentation
of
methods
for
operating
smas
with
wearables,?
This
is
not
only
the
hydra
method,.
There
are
other
methods,
and
also
writers
provide
many
other
methods
that
allow
us
to
transform
this
array
that
we
receive,,
but
in
fact
even
create,,
including
collections,,
apply
anonymous
functions
to
it,
and
this
is
the
mechanics
we
will
consider
in
the
next
lectures,,
which
already
brings
us
closer
to
functional
programming,.
A
B
A
Element
is
not
included,
that
is,,
as
you
can
see,
here,
we
will
get
the
numbers
1
and
3,.
Since
we
have
four
elements,,
then,
as
you
can
see,,
we
have
thick
elements
that
refer
to
one
less,
so
that
you
don't
get
confused.
Just
remember
that
the
first
access
element
is
the
element
that
you
want
to
access
on
the
right
side
of
accessing
this
slice,.
It
will
actually
be
on
the
element
index
it
will
actually
have
when
included
from.
B
A
A
Further,
respectively,
we
get
access
when
we
specify
from
2
to
4.
This
means
that
the
specific
second
element,
in
our
case
it
will
be
5
and
before
the
final
element,
it
will
be
element,
t
0,
1,
2
3.
When
we
specify
4,.
This
means
that
we
actually
take
one
element
less,
that
is,.
If
we
consider
it
with
inclusion,,
it
will
be
the
second
and
third
element,
and
syntactic
sugar
also
applies
to
the
same
construction,.
That
is,.
We
know.
A
The
element
to
example
from
which
we
want
to
take
a
slice
is
2,
and
we
know
for
sure
that
we
want
to
take
the
end
of
our
array
and
it
contains
four
elements,.
Then
we
can
render
2
..
Why
is
it
convenient?
Sometimes
we
can
have
large
arrays,
for
example,
and
in
some
cases,
when
it
is
passed
there
by
references
and
so
on,,
we
will
need
to
get
its
length,
and
in
order
not
to
do
this,,
there
is
a
very
nice
simplification
where,
in
fact,.
A
The
compiler
does
all
the
work
for
us
and
there
is
one
more
beautiful
construction,.
It
solves
a
number
of
very
important
tasks:
when
we
specify
a
slice
:
that
is,
we
have
both
the
left
and
right
range
of
the
array,
fully
included,
why
this
is
done,.
It
means
that
we
have
converted
our
array
of
four
elements
into.
B
A
B
B
A
A
B
A
A
B
A
Do
not
need
to
be
explicitly
specified
and
the
collection,
as
it
is
important
to
understand
they
do
not
belong
to
the
standard
library
by
the
standard.
Library
is
meant
true,
and
you
just
need
to
remember
this,
because
if
suddenly
in
the
future,
you
will
to
develop
a
news
program
that
does
not
contain
itself
standard
binding
and
sometimes
such
needs
are
especially
when
you
are
developing
for
any
devices
or
smart
contracts
that
have
special
requirements.
A
It
is
possible,
but
someday
you
are
faced
with
the
fact
that
you
need
to
use
the
news,
and
in
this
case
you
need
to
remember
that
the
collections
are
not
included
there
and
you
will
need
to
use
special
auxiliary
libraries,.
They
just
have
everything
and
just
broadcast
a
separate,
skating
rink.
This
is
such
an
important
nuance
that
I
feel
I
will
remember
and
we
will
start
with
the
simplest
type,.
This
is
a
vector,.
A
Which
means
that
their
size
is
limited
only
by
the
size
of
the
RAM
that
the
operating
system
provides
you
with,.
There
is
an
example.
The
operating
system
provides
you
with
the
volume,
for
example,
the
island.
You
have
there,
laptops
8,
provides
sex,
half
a
gigabyte,,
then
in
fact
you
have
access
to
all
this
memory.
Through
the
collections,
in
this
case,
a
person,,
then
we
all
the
rest,,
including
an.
A
B
A
Thing
that
it
is
better
not
to
touch
it,
because
you
must
understand
very
clearly
what
you
are
doing,.
So
if
you
have
a
need
for
intensive
and
large
use,,
you
will
come
in
handy
of
course,
collections
and
the
first
helper,,
as
I
said
for
you,,
will
be
a
vector
vector,
is
a
set
of
ordered
data
that
is
stored.
A
Which
is
of
one
type,
in
fact,,
it
is
the
same
wear,,
it
is
simply
organized
and
different
and
it
is
not
stored
in
heaps,.
One
of
the
nuances
is
that
the
type
is
vector,
including
the
string
string,
since
it
is
an
embodiment
of
the
branch
type
8,
the
vector
to
lead
eight
elements,
and,
accordingly,.
Through
this,
it
is
possible
to
represent
any
Judith
and
youtube
element
8,
since
we
operate
by
studying
8
to
the
lines
and
how
the
vector
is
declared,.
This
is
quite
simply
done,,
but
there
are
some
nuances.
As
you
see,.
B
A
We
we
describe
vectors
here.
We
have
how
to
say
this
is
a
symbol,
more
less
I
will
say
so,
and
in
this
case
it
allows
us
to
specify
what
type
the
elements
of
the
vector
are.
In
this
case,
there
are
several
ways
to
describe
a
vector,.
We
describe
it
with
such
a
classic
vector
as
vectors
of
it,
that
is,
we
initialize
axis,
respectively,
in
order
to
work
with
it,.
A
This
variable
must
be
mutable
and
the
vector
has
a
lot
of
methods
and
I
intentionally
did
not
list
them
here,
because
they
are
all
described
in
the
documentation
in
the
general
case,.
One
of
the
most
useful
methods
is
this
method,,
which
means
that
you
can
add
secretly.
It
is
sequentially
scanned
from
this.
It
follows
that
the
volume
of
the
array
stink
is
limited,
that
is,.
A
A
B
A
B
A
Trade
of
topic,,
since
for
different
elements,
we
can
independently
implement
how
it
will
happen
and
tagging,
sorry,.
This
has
already
been
done
for
you
in
the
standard
library
of
the
vector,
collection
and
I,
recommend
that
you
take
your
free
time
to
look
at
this
library.
A
little
function,
and
one
of
aspects
is
that
it
is
quite
well
sanely
described
most
often
with
examples
and
how
to
win
and
integration
occurs
through
the
for
loop,
in
fact,.
It
doesn’t
really
differ
much,,
as
you
can
see,.
A
B
A
We
will
do
the
following,
first
it
to
explain
as
simply
as
possible.
Further
you
can
consider
this
description,
which
I
am
cool
here.
It
is
also
late
and
the
documentation,
and
if
you
have
more
wishes,
the
path
is
built
because
it
is
a
nightmare,
it
is
actually
in
other
languages.
of
the
example
imagine
this
is
some
key-value,
some
structure
that
contains
when
retrieving.
When
we
store
the
chest
value,
there
is
one
of
the
fundamental
problems,.
A
It
lies
in
the
fact
that
access
by
key
can
be
compromised
and
fishman
is
used
for
this,,
which
means
why
exactly
does
this
mean
that
it
uses
a
certain
hashing
algorithm
for
the
shoulder
and,
as
you
can
see,
by
default
in
grow,,
algorithm
13
is
used.
If
y
in
you
have
a
desire,
again,,
you
can
see
in
more
detail
what
it
is,.
A
That
it
has
a
certain
guarantee
of
the
uniqueness
of
this
key
and
there
are
various
kinds
of
attacks
on
the
map
and
why
this
is
important,.
This
means
that
you
can
access
data
that
should
not
be
accessed
and
grow
up
with
this.
Everything
is
fine,
because,
since
this
is
system
programming,
it
is
positioned
as
safe
and
I
want
to
be
afraid
of
the
task
completely
copes
if
on
the
fingers.,
this
is
just
a
key-value,
that
is,
you
have
a
certain
key
to
which
you
can
get
a
value.
B
A
A
B
A
B
B
A
A
A
Is
that
for
the
type
that
is
used
for
the
key,,
the
hashing
function
must
be
implemented,.
It
is
a
standard
type,.
It
is
simply
implemented
by
default.
If
it's
your
constant
type,
then
you
have
to
figure
out
how
to
implement
it.
Somehow
it's
not
really
it’s
difficult,.
We
won’t
consider
it
because
it’s
a
principle,
most
often
it’s
a
critical
case
when
we
use
a
custom
type
for
the
shoulder,,
sometimes
it’s
necessary
enough,.
A
B
B
A
There
are
a
lot
of
functions
built-in
for
cashback
and
in
order
to
find
out
what
they
are,
and
I
highly
recommend
that
you
go
to
the
documentation
for
this
library,,
which
will
be
located
on
such
a
dress,
and
there
will
be
a
lot
functions,
described
I,
reasonable
to
duplicate,
because
in
the
documentation
and
very
well
written
off
measures,
and
so
you
can
find
a
lot
of
auxiliary
functions.
We
just
for
starters,
it
is
to
remember
it
is
inserted.
A
B
A
Simply
has
nothing
to
do
with
it,,
but
in
this
form
it
is
displayed
very
similarly
agree
in
this
case.
If
you
just
visually,
remember
how
it
looks
like
on
the
left
side,
we
have
the
key
on
the
right
side.
Is
epic
key-value
values,,
as
you
remember,,
when
we
printed
the
vector,,
we
displayed
the
data
through
square
brackets
and
through
a
sequence
of
elements
of
the
same
key-value,
type,.
B
A
Is
in
all
collection
types
that
exist
in
grow
standard
library,
I.e.
as
you
see
this
standard
library
there
they
are
collections
and
it
contains
a
whole
set
of
nightmare.
Sorry,
collection,
type,
including
vector
you
want
this
petimat
and
there
are
actually
others,
but
they
are
rarely
used.
If
you
want
to
need
to
use
them,
you.
B
B
B
B
B
B
A
A
A
A
Look
at
it,
I
consider
myself
a
hashtag,.
This
is
one
of
the
abstractions
that
allows
you
to
operate
with
keys,
that
is,
the
hash
set
is
under
the
shmap
type
and
again
the
tendrils
it
itself
contains
the
same
elements
and
attributes
means
that
it
is
stored,
a
bunch
of
some
kind
of
shmar,
because
it
is
actually
rejected
by
Hoffman.
A
B
A
Inherently
a
set
of
keys,
that
is,,
if
hashmi,
is
a
key-value
set,
the
headset
is
a
set
of
keys.
How
is
the
internal
structure
of
the
muscle?
It
is
actually
Hoffman
whose
all
values
are
the
same.
This
type
you
see,
just
two
parentheses
fell,
as
you
remember,.
There
is
no
type
in
growth,,
well,
or.
B
A
A
Here
such
a
construction
with
two
curly
braces,,
and
as
you
remember,,
if
I
told
you
at
one
of
the
last
lectures,,
if
you
see
a
function,
that
does
not
return
anything,.
This
is
actually
simplification
of
the
compiler,,
which
means
it
does
not
require
the
program
mmist
explicitly
indicate
mounted,
and
if,
for
example,
we
have
a
main
function,
I
don’t
return,
a
type,.
This
means
that
by
default
it
returns
such
a
type.
B
B
A
A
You
need
to
remember
that
this
is
a
key
store.
Which,
on
the
one
hand,
is
unique,
that
is,
they
cannot
be
repeated
from
one
of
the
requirements;.
The
second
is
that
we
use
cashmere,,
which
means
that
under
the
hood,
they
have
a
hashing
algorithm,
and,
accordingly,,
a
lot
of
protection
that
the
programming
language
itself
guarantees
compiler.
Neither
m
is
located
in
order
to
avoid
hacking
for
a
long
time.
I
will
speak
very
primitively,
and
this
is
one
of.
A
B
A
Links
at
the
end
of
this
slide
will
be
that
it
will
not
be
difficult
to
find
everything
and
the
declaration
of
a
variable
for
you
want
it
happens
in
this
way.
As
you
see,
we
describe,
the
variable
I
want
this,
which
we
have
only
one
type,
is
the
key
type.
In
our
case
with
to
string
and
again,
this
is
our
pride,
any
type
that
actually
implements
all
standard
like
to
grow,
they
implement
this,
again,
initialization
occurs
the
same
way
as
you
remember,,
our
lecturer,
so
initialized
also
initialized
cached,
that
is,.
A
B
A
B
B
A
This
is
apparently
by
because
the
reason
and
the
tree-
and
it
automatically
thought
that
it
would
be
nice
to
put
it
this
way,,
and
this
is
an
even
more
complicated
concept
again.
However,
I
will
try
to
simplify
it
for
you
to
make
such
a
small
short
excerpt
from
the
documentation,,
but
in
fact
this
is
working
with
binary
as
you
know,.
There
are
effective
search,
algorithms
for
a
binary
tree,
and
this
type
implements
these
algorithms,
as
you
remember,.
A
B
A
A
A
A
Through
the
hashing
function,,
this
is
already
happening
in
a
different
way,
and
here,,
as
you
can
see
in
the
mapi
children,
consumables,
in
other
words,
access
to
elements
to
rent
due
to
the
fact
that
it
provides
various
kinds
of
internal
elements
for
and
things
on,
all
for
data
access
and
search,.
Since
it
that
is
effective.
You.
A
A
B
A
It
happens
a
little
differently
for
this.
We
calculate
and
again,,
as
in
the
have
my
baby
fresh
network,,
all
the
same
standard
insert
functions
are
an
iterator
and
here
all
the
same
standard
creation
functions
without
repair
and
I
have
brought
here.
For
you,
one
of
the
interesting
elements
specially
saved
money
at
the
end,
when
you
want
to
make
sure,
for
example,
insert
the
key
and.
B
A
You
have
such
a
task.
There
are
keys,
there
is
nothing
do
and
if
there
is
no
key
make
a
bet
in
this
case,
the
function
or
method
are
in
soft.
It
does
it
mean,
and
if
it
exists,
it
will
not
do
anything
if
it
does
not
exist,
it
sets
the
value
to
100
and
how
to
increase
it
using
an
iterator,
then
in
exactly
this
way.
A
Access
to
the
elements
is
what
flash
mob,
that
is,
when
we
operate,
we
get
such
a
dome
that
contains
Kiev
itself
and
again,
we
are
through
the
emperor,
may
not
actually
get
access.
There
are
quite
a
lot
of
ways
to
get
access.
As
you
can
see
here
we
have
a
center.
There
are
other
methods,
that's
all
you
can
see
in
the
documentation
describe
what
methods
are
for
the
guitar.
We
again
repeat,
I
think
it's
pointless
just
in
case
I
another
useful
method
here
decided
to
show
this
is
Kudrinsky.
A
As
you
understand
this
world,
there
is
a
type
for
the
hash
we
by
and
for
the
set,
because,
accordingly,
you
have
such
a
task
to
check
whether
the
data
set
contains
a
certain
key,.
Then
the
debt
of
such
frequent
tasks-
you
can
use
this
and
in
the
end
we
see
that
when
we
are
given
53
pampas,
they
look
very
similar
and
I.
B
A
Me
remind
you
that
we
have
considered
three
basic
types.
collection
is
a
vector
that
itself
contains
a
sequence
of
elements
of
the
1st
type.
Hash
map
is
a
key-value
where
all
keys
must
be
of
the
same
type
and
implement
a
hash
function,
and
value
value
must
also
be
all
of
the
same
type
programming
language.
A
All
keys
must
be
of
the
1st
type
as
well
as
the
value
each
of
them
is
calculated
from
a
certain
you.
Space
I
would
highly
recommend
when
production
does
not
have
tasks
that
will
require
you
to
understand
which
of
these
types
to
use
refer
to
these
links,
a
special
one
picked
them
up
somewhere
to
save
them
and
slice
with
on
the
pole,
as
you
can
see,
just
beeches
chapter
4.
A
Library,,
the
collection
is
located
along
this
path,
too,,
as
you
can
see,.
These
are
the
standard,
libraries
and
the
collection,
as
well
as
do
not
forget
that
we
have
the
samples
run
which
shows
in
such
an
expanded
form.
So
he
said
how
to
work
with
this,,
since
we
have
an
example
to
dilute
a
little
zapals
examples
a
lot
and
they
are
different,
sometimes
exotic
languages.
are
useful.
I
highly
recommend
you
to
climb,
and
one
of
the
specifics
is
that
you
can
execute
them
directly
on
this
site.
There
is
such
a
button
to
start.
B
A
And
you
forget:
something,
contact
them
with
this
juice,.
They
will
help
you
figure
out
what
functions
are
there,,
how
to
work
with
it,.
Since
today
we
have
considered
only
some
such
tip
of
the
iceberg,,
because
the
topic
itself
is
enough.
Complex
voluminous
and
there
are
many
underwater
amney,
and
this
documentation
will
obviously
help
you
I
highly
recommend
on
this
I
think
that
we
will
all
move
on
important
issues.
A
A
A
B
A
A
A
A
A
Look,,
you
need
to
understand
that
memory
management
occurs
in
the
operating
system
and,
as
Cyril
correctly
said,.
This
is
not
a
question
of
paint
about
the
operating
system,,
the
usual
one
will
use
of
memory,,
but
again,.
It
all
depends
solely
on
the
operating
system,
and
the
settings
on
priority
from
on
raincoats,
for
example,.
A
A
So
it
all
depends
on
very
specific
cases,
and
if
memory
overflow
occurs,
it
won’t
end
up
with
anything
good,
they
mentioned
that
randomness
does
not
have
cashback
hashing
and
it
protects
against
getting
an
element
of
another
on
one
shoulder,,
including
yes,
I,
understood
correctly,
can
I
tell
you
in
more
detail,.
So
let
me
try
to
understand
that
you
asked,
randomness,
protects
against
getting
an
element
of
another
key
using
one
key
using
one
key
received
Eat
an
element
to
a
friend
of
a
key.
A
What
does
it
mean
to
get
an
element
of
another
key
from
one
key?
Above
you
get
see,
you
need
to
understand
what
you
have
as
an
end
user
as
a
programmer.
There
is
only
one
key,
then
there
are
algorithms
that
allow
you
to
secure
access
to
elements
that
would
allow
you
to
access
to
data
that
can
be
compromised.
And,
accordingly,,
some
hashing
algorithms
are
used
for
this,
no,.
A
He
said,
therefore,
self-assertion
in
one
key
to
receive
an
element
of
another
doctor
is
not
very
true,
that
is,
you
get
some
value
on
the
shoulder,
in
fact,.
You
don’t
even
really
need
to
think
about
how
exactly
it
works
for
you,.
The
most
important
thing
is
to
understand
that
it
has
the
properties
of
reliability
and,,
most
importantly,.
It
works
on
the
key-value
principle,.
A
Yes,
absolutely
right,.
It
is
protection,,
including
this,,
because,
for
example,
you
have
sensitive
sensitive
data,.
There
is
an
application,
but
suppose
m.
You
have
an
application
that
works
in
the
financial
sector,
and,
accordingly,.
In
order
to
protect
the
gate
elements,,
since
in
Kashmir
you
can
implement
various
kinds
of
attacks,.
You
already
know
such
a
dense
topic,,
but
it
is
important
to
understand
that
this
allows
you
to
secure.
B
A
A
B
A
A
A
Natural
that
you
do
not
need
to
return
an
empty
value,
but
see
in
some
cases,
this
empty
value
can
be
written
differently,.
We
will
have
the
results
and
errors
of
times
in
the
next
topic
type
rs.
There
is
such
a
special
wrapper,
in
which
an
example:
u
can
also
use
this
empty
type
dream,
that
is,.
This
is
what
allows
us
to
explicitly
describe
what
we
don’t
return
anything
to
them,.
A
So
the
next
question
is
whether
there
is
any
a
way
to
programmatically
avoid
memory
overflow
when
using
a
vector,
that
is,
to
prevent
the
situation
of
adding
an
element
that
will
lead
to
such
an
overflow,.
I
would
say
something
to
the
holy
mink,.
You
will
agree
with
me,
that
is,
you
need
to
try
hard
to
overflow,
the
memory,,
but
naturally
in
Russia.
A
B
A
On
performance,
because
for
example,,
if
you
have
a
task
when
in
a
loop
you
add
elements
and
Algorithmic
calculations
are
taking
place
at
the
same
time,
and
you
are
constantly
doing
this
kind
of
check
there,,
this
can
greatly
affect
the
operation
of
the
Volgar,.
Therefore,
it
is
very
clear
to
understand
in
what
cases
it
needs
to
be
done
in
such
cases.
It
does
not
need
to
be
done
in.
A
A
It
is
just
very
related
to
the
topic
of
memory
and
how
overflow
occurs,,
because
the
factorial,,
as
you
can
easily
guess,,
can
be
obtained
instantly,.
So
if
you
want,
try,
it
will
be
such
an
interesting
experiment.
Fact
by
example,
if
you
do
through
tk.
there,
it
will
be
remembered,
very
quickly,,
and
if
you
do
it
through
a
bunch,,
it
will
naturally
take
longer,
while
what
types
of
data
can
be
used,
because
four
will
end
very
quickly,
and
so
on,.
B
A
A
Process,
whether
like
errors
from
incorrect
input,,
most
likely
you
mean,
when
you
move
arguments
by
force,
I,
would
recommend
processing
the
only
specifics
that
I
cut
the
topic
and
errors,.
We
will
go
through
if
I’m
not
mistaken,
next
time,,
but
if
you
can
figure
out
for
yourself
what
you
are
watching,
homework,
it’s
actually
for
you,
she
computer
guess
me
I
need,
and
it
was
made
for
you.
We
tried
our
hand
at
a
fairly
simple
task.
It
is
simple,
but
at
the
same
time
fascinating
it
cannot
be
accepted.
To
bring
some
variety
life
is
endless.
A
A
A
Somehow
set
aside
time
to
do
homework
during
this
time
because
which
one
is
quite
practical
and
difficult
if
it’s
not
difficult
for
you
try
to
unite
in
such
group
menus.
Why
in
general,,
so
that
the
first
thing
you
can
help
each
other
is
very
important
to
know
how
any
help
team
is
sometimes
very
necessary,,
especially
some
are
more
experienced
than
others,
and
the
shoulder
of
a
faithful
comrade
in
this
sense
can
be
very
useful
because
you
can
learn
from
each
other
and
the
second.
