►
From YouTube: JavaScript: The security concern answered - Adam Baldwin
Description
No description was provided for this meeting.
If this is YOUR meeting, an easy way to fix this is to add a description to your video, wherever mtngs.io found it (probably YouTube).
A
Hello,
everyone
and
welcome
to
today's
webinar
javascript.
The
security
concern
answered.
My
name
is
Danielle
Wambach
and
I'll,
be
your
moderator,
I
work
on
the
marketing
team
here
at
NPM
and
I'm
excited
to
be
hosting
today's
session.
I'm
pleased
to
introduce
today's
speaker,
Adam
Baldwin
Adam,
is
the
VP
of
security
here
at
NPM
and
Adam
was
also
the
founder
of
live
security
which
NPM
acquired
last
year
before
I
hand.
It
over
I
have
a
few
housekeeping
items
to
cover
about
the
presentation
and
the
bright
top
webinar
platform.
A
First,
today's
webinar
will
be
recorded
on
demand
after
the
live
session
and
is
successful
through
the
same
length
you're
using
now,
we've
also
added
some
attachments
which
are
available
through
the
attachments
tab
at
the
bottom
of
your
screen.
This
is
where
you
can
find
today's
deck,
a
link
to
the
full
survey
results
and
other
related
content,
including
MPs,
blog
and
upcoming
webinars.
Next,
we'll
love
to
hear
from
you
during
today's
presentation.
If
you
have
a
question
for
Adam,
please
feel
free
to
send
it
through
the
app
the
questions.
A
B
So,
let's
get
to
our
agenda
today
we're
going
to
talk
about
what
is
NPM,
hopefully
you're,
already
a
little
bit
familiar
with
this
talk
about
JavaScript
supply
chain
security.
Why
that
matters
to
all
of
us
and
incorporate
into
that
a
little
bit
of
our
insights
from
our
2019
developer
survey
and
also
talk
about
how
NPM
the
NPM
security
team
and
our
products
and
services
can
help
there
in
that
course,
at
the
end
of
Q&A
session,
as
we
have
time.
B
So,
what
is
n
p.m.
when
p.m.
first
and
foremost
is
a
company.
It's
NPM
Inc.
We
deliver
Enterprise
proximate
solutions
to
help
the
JavaScript
ecosystems
right.
It
takes
a
lot
of
effort
to
keep
this
ecosystem
going.
We
have
a
website
for
discovery
in
collaboration
on
packages
in
JavaScript,
and
most
developers
know
us
for
the
CLI
is
a
command-line
interface
that
that
they
use
and
love
every
day
to
rapidly
develop
applications
and
bring
dependencies
into
their
into.
B
Of
course,
it's
all
backed
by
the
public
registry.
This
amazing
corpus
of
reusable
JavaScript
that
lets
developers
build
fast.
In
fact,
it's
it's
roughly
nine
hundred
seventy
six
thousand
and
published
packages,
roughly
eight
point:
nine
million
packaged
versions,
individual
versions,
amazing
amount
of
reusable
code,
2.1
billion
downloads
per
day
of
this,
this
corpus
7700
package
publishes
per
day.
It's
an
ecosystem,
that's
moving
incredibly
fast,
and
this
is
an
important
thing
to
remember.
B
As
we
get
a
little
further
into
our
presentation,
it
really
signaled
everyone's
using
javascript
eleven
million
developers
of
NPM
registry
100
of
the
fortune
100,
which
we
actually
checked.
Fifty
large
tech
at
large
financial
companies,
tech
companies
and,
of
course,
five
hundred
the
fortune,
500
we're
pretty
sure,
as
well
as
governments,
foreign
and
domestic
financial
institutions.
You
know
you
name
it:
javascript
is
being
used
for
application
development.
I.
Think
you
get
the
point
here
that
that
everyone
is
using
javascript
and
then
it's
you
know
moving
up
at
a
high
velocity.
B
Why
are
those
numbers
so
big?
Let's
look
at
a
supply
chain
to
an
application
and
kind
of
just
go
into
that.
So
everything
starts
with
your
application.
Write
a
business
problem
to
be
solved
and
that's
the
starting
point
and
with
NPM
javascript
you
could
rapidly
brilliant
dependencies
to
bring
in
these
packages
from
the
Public
Registry
into
your
application
and
those
provide
a
way
to
rapidly
develop
and
prototype
and
Kalu
those
together
to
solve
your
business
problem.
Of
course,
dependencies
themselves
have
dependencies,
I
think
about
it.
B
Like
an
iceberg,
you
see
the
top,
which
is
your
application
and
your
top-level
dependencies
that
you
have
there
and
then
everything
else
is
kind
of
below
the
waterline
it
and
out
of
sight
out
of
mind.
In
fact,
97%
of
the
code
in
a
modern
web
application
comes
from
NPM.
That
means
that
small
piece
that
you're
writing
your
developers
writing
as
glue
code.
It's
it's
stitching
all
those
modules
together,
but
it
makes
up
a
very
small
portion
of
the
actual
deployed
codebase
and
to
relate
that
to
you
or
to
to
an
enterprise.
B
You
know
we're
looking
at
20,000
dependencies
used
by
typical
enterprise
right,
a
large
corpus
of
software
that
you
have
to
inventory
and
think
about,
and
the
thing
beyond
those
dependencies.
That
I
think
is
extremely
interesting.
Is
that
in
the
foundation
of
that
entire
supply
chain
is
that
is
maintainer
x'
people,
humans,
maintain
these
modules
and
you
have
thousands
of
developers
that
don't
work
for
you
that
are
shipping
code
to
production.
B
So
that's
that's
a
supply
chain.
So
let's
take
a
look
at
what
some
of
these
packages
are
bringing
in
with
themselves
as
they
cross
from
the
public
into
your
private
space.
First
thing:
your
vulnerabilities
known
vulnerabilities
security
flaws
that
are
found
in
the
packages
right
and
we
surveyed
these
33,000
participants
in
our
inner
developer,
serve
areas
here
and
83%
of
them
were
concerned
about
the
open
source
software
that
they
use
not
sure
about
the
other
17
percent.
But
83%
were
concerned
about
that,
and
we
also
did
a
survey
of
8
large
banks
and
we.
A
B
At
23
million
downloads
and
22,000
packages
that
were
being
consumed
by
these
financial
institutions-
and
we
came
up
with
any
824
of
them-
had
vulnerabilities
3%
of
that
those
packages
and
55
of
those
were
critical
vulnerabilities,
something
that
could
be
exploitable
and
something
you
need
to
know
about
just
coming
into
your
environment.
This
is
a
really
interesting
perspective
on
we've
got
this
large
purpose
of
a
software
course.
The
more
software
we
have
will
bring
in
the
more
potential
there
are
for
bugs
and
vulnerability
and
security
vulnerabilities.
B
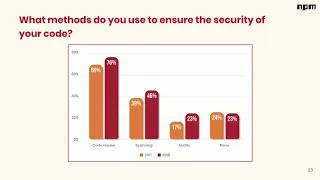
We
looked
at
what
methods
do
organizations
use
or
developers
use
to
ensure
the
security
of
their
code,
and,
what's
interesting
to
me,
is
across
the
board.
Everything
is
up,
that's
great,
because
more
attention
is
being
paid
to
security,
which
is
good,
but
you
see
we're
still
heavily
relying
on
code
review,
this
sort
of
necessary,
but
very
difficult
and
expensive
process.
B
That's
shipping
versus
being
able
to
keep
up
with
all
those
dependencies
sort
of
moving
underneath
to
your
application.
So
to
address
it's
a
bit,
you
know
we
we
incorporated
NPM.
We
built
NPM
audit,
finding
fix
vulnerabilities
and
JavaScript
dependencies
for
users
of
NPM
and
NPM
Enterprise
right.
It
allows
you
to
go
down
that
entire
dependency
tree
right
to
analyze
for
advisories
that
are
in
our
database.
B
These
no
boner
abilities
and
packages,
and
this
champion
audit
tooling,
is
backed
by
the
NPM
security
team
as
well
as
that
that
corpus
of
11
million
users
of
our
registry
right,
we
have
a.
We
have
bridge
the
communities
between
security
and
our
developer
ecosystem
to
bring
information
to
you
into
the
enterprise
faster
right.
We
have
a
reporter
vulnerability
button
on
every
page
in
the
in
the
NPM
website.
That
goes
to
our
security
team
for
triage,
which
means
that
maintainer
z'
get
a
very
high.
B
High
accurate
signal,
we
don't
send
them
just
garbage
right,
so
the
garbage
is
batted
down
and
that
way
when
we
get
it
out
to
our
tooling.
Hopefully
it's
going
to
make
positive
impact
on
allow
you
to
find
in
fix
things
with
your
within
your
project.
So
that's
security,
vulnerabilities
lookout.
Let's
go
on
to
another
risk
that
getting
brought
in
from
the
public
registry
into
your
own
private
space
and
that's
malware,
and
when
I
talk
to
developers
and-
and
you
know,
GTO
and
Cisco's
and
I
asked
what
they're
most
afraid
of
it.
B
It
small
word
always
comes
up
that
they're
scared
about
that
malicious
package
designed
to
you,
know:
disrupter
damage
our
business
and
mom
or
gets
brought
into
the
registry,
and
you
know
anybody
can
publish
to
the
registry
there's
no
barrier
to
entry.
There's!
No!
You
know
special
test
that
you
have
to
take
to
publish,
so
anybody
can
do
that.
B
The
next
one
is
account
compromised,
actually
modified
met,
getting
getting
malware
into
a
popular
package.
Because
of
that
nested
dependency
tree,
you
could
compromise
one
of
those
human
maintained
errs
that
has
a
bad
security
hygiene,
bad
password,
something
like
that
and
get
access.
You
publish
malware
in
the
registry.
That
way.
Let's
look
at
you
know
this
mall
we're
sort
of
like
trend
over
time
in
the
registry
and
we're
looking
at
we're
2017.
B
Forty
six,
you
know
instances
a
mall
where
we
have
published
in
our
advisor
database
sixty-eight
for
2018
and
will
be
partway
through
2019,
we're
already
up
to
2017
numbers,
I.
Think,
as
you
can
see,
this
is
probably
going
to
continue
to
trend
up
as
it
becomes
a
useful
target,
because
the
supply
chain
is
a
useful
target
to
your
enterprise.
B
You
may
be
doing
everything
right,
but
maybe
one
of
those
maintained
errs
of
the
thousands
of
packages
in
use
has
bad
security
hygiene
and
it
allows
for
a
targeted
attack
against
an
organization,
but
also
when
you
look
at
the
comparison
of
numbers
and
the
number
amount
of
packages
you
can
publish
versus
the
number
of
packages
in
the
registry
versus
the
malware
numbers,
we're
looking
at
still
pretty
low,
pretty
low
numbers.
Although
do
expect
to
see
that
trending
up
take
care
of
some
is
more,
where
we're
investing
heavily
in
sort
of
automated
threat.
B
If
your
maintainer
of
a
popular
package,
but
you
want
to
collaborate
with
others,
you
can
require
that
your
other
maintainer
have
this
enable.
Of
course,
we
have
sensitive
data
protection
to
revoke
tokens
that
may
be
published
in
NPM
packages
and
we're
going
to
be
expanding.
This
effort
very
soon
so
be
watching
the
blog
for
an
announcement
on
some
other
things.
We're
going
to
be
doing
here
around
sensitive
data
protection,
protecting
those
those
valuable
tokens
to
the
NPM
registry.
So
first
we
Pentium
Enterprise.
You
can
take
more
account
control
with
SSO.
B
We
know
with
different
vendors,
any
popular
sort
of
Lloyd's
DC
provider
there,
so
lots
of
control
and
that
you're
getting
from
NPM
Enterprise.
Finally,
let's
talk
about
a
risk
that
I
think
doesn't
get
talked
about
enough.
We
talked
about
vulnerabilities,
we
talked
about
malware,
but
this
is
also
one
of
those
risks
that
creeps
into
an
organization.
That's
of
interest
right,
licensing
compliance
issues.
It
often
gets
forgotten
about.
So
in
our
survey.
Let's
just
look
at
what
our
users
thought
about
this.
B
In
their
perspective,
you
know
what
does
an
NPM
package
license
impact
or
doesn't
impact
each
license
impact
your
decision
to
use
it?
Yes,
yes,
58%
of
respondents
say
yes,
it
actually
impacts
the
decision
to
use
it.
Does
your
company
prevent
or
prohibit
use
for
using
certain
licenses
again
a
high
degree
of
yes?
You
know
over
the
majority,
fifty
five
percent
yes
and
then,
which
licenses
do
get
prevented.
You
know,
we've
got
unrecognized
licenses,
we've
got
code
without
a
license.
Gpl
a
GPL.
B
Some
of
these
restrictive
licenses
that
you
know
brought
into
a
project
may
require
you
to
contribute
changes
back
may
require
you
open
source,
the
application
that
it
was
brought
into
potentially
risks
if
it's
a
commercial
venture
right.
So
that's
a
definitely
license.
Risk
is
an
important
one
to
get
a
handle
on
it's
all
about
knowing.
What's
there,
we
did
an
analysis
of
sort
of
that
same
corpus
of
data
in
a
big
banks,
and
there
was
a
lot
of
different
licenses
in
there
out
of
those
packages.
We
support
15
different
licenses.
That
would
have
to
be.
B
You
know,
legally
reviewed
and
understood
about
where
they're
being
used.
Mit,
of
course,
was
the
most
popular
license,
but
just
like
a
vulnerability,
there
was
at
least
one
there's
just
about
a
percentage
of
unlicensed
and
GPL
licenses
present.
That
may
be
restrictive
or
cause
issues
for
an
organization
depending
on
how
that's
being
used
the
risk
tolerance
of
the
organization.
B
B
As
we
talked
about
sort
of
the
tooling,
the
NPM
audit,
tooling,
that
helps
you
find
a
fix
vulnerabilities
within
your
within
your
projects,
and
then
we
we
talked
about
some
of
the
efforts
that
Dan
cave
security,
team
and
APM
has
in
place
to
you,
know
protect
accounts
and
identify
malware,
and
things
like
that
and
as
it
turns
out,
businesses
have
compliant
security
and
oversight
means
it
must
be
met
when
using
open
source.
You
know
ends.
Our
product
philosophy
is
simple:
that
we
offer
on
top
of
NPM
workflow
that
the
developers
already
love.
B
You
know
with
that
in
mind
we
created
in
came
Enterprise.
It's
it's
a
way
for
you
to
gain
control
over
your
open
source
usage
to
reuse
code
within
your
your
enterprise.
To
have
you
know
your
dedicated,
you
know,
search
and
discovery
for
collaboration
internally,
of
course,
account
control
with
single
sign-on
and
premium
support,
and
it's
all
wrapped
up
in
it
like
a
single
tenancy,
dedicated
deployment
as
well
as
all
of
the
really
amazing
security
compliance
features
that
I
just
can't
quite
tell
you
about,
but
are
going
to
be
coming
very
soon.
B
To
recap:
there
you're,
using
a
lot
of
JavaScript
that
JavaScript,
creates
security
and
appliance
risk
for
your
organization
for
your
users
and
they
became
an
Enterprise
NPM
Enterprise
can
help
by
giving
you
your
own
private
space
just
or
control
over
your
open
source
consumption.
That's
all
I
have
for
you
today.
I
hope
got
some
questions
and
thank
you.
A
B
So
we
have
something:
that's
amazing
and
I
hinted
at
it.
That's
our
that's
our
team
security
team
and
our
11
million
users.
So
that's
a
lot
of
eyeballs
in
source
code,
so
we
we
have
pushed
to
be
able
to
have
those
vulnerability
reports
and
triage
them
as
fast
as
possible
to
get
them
into
our
tooling.
So
from
that
perspective
we
try
to
be
fast
and
we
try
to
be
thorough,
but
we
don't
want
to
be
so
fast
and
we're
providing
you
a
very,
very
poor
signal.
B
Is
that
we
we
built
our
tooling
to
push
as
far
left
as
we
possibly
can
to
the
developers
so
that
they're,
seeing
hey
I,
need
to
update
this
to
this
this
particular
package,
oh
I,
can
run
NPM
on
it
fix
and
just
automatically
bumped
my
dependency
to
a
fixed
version
that
allows
developers
to
have
a
friction
for
experience
and
move
fast.
So
I
think
that
that
helps
cover
that.
B
So
I
think
that
you
know
it's
all
about
incremental.
So
here
it's
all
about
incremental
progress.
I
security
is
not
a
destination.
It's
a
journey!
It's
a
process!
It's
a
it's
a
way
of
looking
at
things.
You
guys
are
continuously
I.
Think
about
like
this,
like
you're,
going
up
an
escalator
backwards.
If
you
have
to
keep
moving
or
you
end
up
back
at
the
bottom,
you
have
to
and
you'll
never
reach
the
top.
It's
a
very
tiresome
journey,
and
so
you
need
to
keep
applying
in
proving
security
right.
B
So
we're
going
to
listen
to
our
users
and
we're
gonna
apply
that,
but
we're
not
going
to
forget
about
you,
know
the
developers
as
well
and
the
need
for
what
made
NPM
and
the
jobs
the
JavaScript,
because
it's
been
great
in
the
first
place,
which
was
that
frictionless
experience
to
be
able
to
install
packages
and
use
them
and
rapidly
develop.
So
we
want
you
to
be
able
to
build
amazing
things,
but
build
amazing
things
safely.
B
So
we,
you
know,
we
have
the
attention
like
I
said
attention
of
11
million
developers
and
in
them
I
mean
we
hear
about
things
before
anybody
else
does
I
think
you
know
nobody's
finding.
You
know
a
piece
of
malware
doing
research
on
data
stored
in
those
registries,
they're
looking
at
our
registration,
they're
they're
communicating
to
us
about
things
that
they
find
so
we're
able
to
get
that
signal.
Our
tooling
is
able
to
see
those
packages
on
publish.
A
A
Well,
thank
you
so
much
Adam.
As
mentioned
earlier,
today's
webinar
will
be
available
on
demand
after
the
live
session.
It
is
accessible
through
the
same
link
that
you're
using
now
we've
also
added
some
related
material
material,
including
today's
slides,
which
are
available
through
the
attachments
tab
at
the
bottom
of
your
screen.
Our
next
webinar
will
be
on
Tuesday
May
14th
at
10
a.m.
Pacific
time
12:00
p.m.
Central
Time.
It
wants
two
p.m.
Eastern
Time
and
you
can
register
right
through
the
attachment
link.
