►
Description
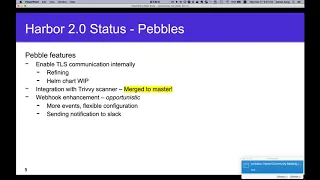
No description was provided for this meeting.
If this is YOUR meeting, an easy way to fix this is to add a description to your video, wherever mtngs.io found it (probably YouTube).
A
A
A
Hopefully
in
the
next
community
meeting
you
hear
the
news
about
the
fc
of
2.0
and
there
will
be
a
relatively
stable
build
for
you
to
try
and
play
around,
and
the
ga
and
rc
will
be
targeted
in
april.
Please
stay
tuned,
so
let's
see
drill
down
to
a
little
detailed
status
for
the
anchor
feature
of
2.0
making
hardware
cloud
native
registry
based
on
the
oci.
A
Currently
we
are
working
on
other,
enabling
other
features
to
cover
the
corner
cases
for
like
replication
quota,
and
we
are
doing
the
refine
refinement
on
ui
to
address
some
comments
and
we
also
fixed
a
field
box
to
on
the
osi
confirming
test.
So
we
can
make
harbor.
You
know
more
conformant
to
the
oci
standard,
but
given
that
the
oci
distribution
spec
is
not
g8
yet,
and
the
docker
distribution
which
we
leverage
to
provide
the
v2
api
also
has
some
legacy
issues
to
fully
comply
with
the
oci.
A
A
Finalizing
this
upgrade
and
migration
flow
to
make
sure
there
is
a
relatively
smooth
upgrade
migration
flow
from
the
previous
version
to
harbor,
because
considering
we
have
done
a
big
change
in
the
api
and
the
data
models.
So
this
is
pretty
complicated
and
challenging,
and
we
are
doing
some
clearing
house
work
like
adding
more
tasks
clean
up
some
unused
code
ether,
so
yeah
we
are
heading
toward
the
fc
beside
the
anchor
feeder.
A
A
B
B
B
B
B
B
B
B
B
B
B
The
children
nurture,
we
will
collect
the
children
artifacts
artifacts
of
the
imaging
bags
and
and
check
whether
the
artifact
is
supported
by
the
scanner,
for
example,
for
example
there
for
those
for
those
artifacts.
So
we
will
check
that
this
one
is
suppose
supported
by
the
scanner.
We
were
several
me
to
submit
the
children
artifacts
to
the
scanner,
to
scan
it
and
merge,
merge
the
scanner
a
lot
for
the
image.
C
D
B
B
A
A
G
Yes,
so
let
me
let
me
do
the
demos
I'm
just
trying
to
find
out
the
way
to
share
the
slides.
Okay,
maybe
I
will
use
my
local
copy,
because
I
will
just
give
you
a
quick
intro
to
the
architecture
of
3d
and
then
I
will
demonstrate
how
to
install
it
online
installer
and
then
just
a
sec,
I'm
trying
to
find
it,
and
then
I
will
show
you
application
library
scanning.
G
G
Okay,
yeah
so
the
quick
overview
as
daniel
mentioned,
so
it's
already
matched
to
master.
I
have
modified
the
install
scripts
and
all
the
build,
make
files
etc.
To
add
this
with
3v
sorry
with
3d
param
to
the
installation
script,
you
will
see
it
in
a
demo.
I
have
also
added
the
deployments
for
the
3v.
So
now
you
could
just
install
with
a
helm
command
and
by
default
the
3d
scanner
adapter
is
enabled
we
keep
clear
if
both
are
chosen,
the
3d
will
be
marked
as
as
default.
G
Just
very
very
simplified
architecture.
This
helps
in
troubleshooting
some
of
the
issues,
as
you
might
know,
number
one.
So
hardware,
scanner
3d.
This
is
the
adapter,
so
we
defined
the
plugable
scanners
api,
and
this
is
the
implementation
of
the
api
which
is
using
behind
the
scenes.
3D
our
open
source,
vulnerability,
scanner,
static,
vulnerability
scanner,
since
the
api
assumes
that
the
scan
requests
are
asynchronous,
we
will
store
this
job
status,
scan
job
status
in
in
redis,
typically
you're,
using
the
redis
instance
or
radius
cluster,
which
is
you
know,
any
way
required
to
operate.
G
A
hardware
then
number
three.
This
is
a
3d
and
funnel
3g
and
funnel.
This
is
a
single
executable
that
we
run
as
a
as
a
child
process
of
the
hardware.
Standard
3d
panel
is
more
kind
of
a
library
which
is
used
to
recreate
the
file
system
of
a
given
image,
so
overlay
file
system.
We
are
trying
to
rebuild
the
file
system
and
then
detect
all
the
operating
system,
packages
and
application
dependencies,
and
then
actually
there
is
another
part
which
is
called
bot
db
or
3vdb.
G
This
is
a
index
which
is
built
on
a
daily
basis
by
a
crown
job.
We
don't
have
to
build
it
locally,
as,
for
example,
is
the
case
today
for
clerk
clarisse
is
using
those
updaters
which
are
pretty
much
killing,
probably
all
dev
environments
instead
of
3d
you
could.
You
could
download
pre-built
vulnerability
index
database,
so
both
this
data,
like
a
3d
cache
and
given
image
file
system,
is
cross-referenced
with
a
3vdb,
so
we
could
find
and
detect
vulnerabilities
and
report
them.
G
So
this
is,
as
I
said,
very
simplified
picture
and
I
will
show
you
the
directory
structure
in
a
second.
So
now,
let's
move
back.
Let's
move
to
the
to
demo
and
as
I
said,
I
will
install
3d,
hopefully
it
works,
then
I
will
show
the
main
configuration
parameters
like
environment
variables,
I'll
explain
the
directory
structure
where
to
find
logs,
which
directories
and
where
do
we
cache
data
and
then
the
demo
of
the
application
dependencies
scanning?
G
So
actually,
before
joining,
can
you
see
this
this
this
terminal?
Well,
just
for
the
sake
of
font
sizing
things.
I
have
just
built
all
the
images
of
of
hardware
before
the
demo.
As
you
can
see
now
we
have
an
image
which
is
called
3d,
adapter
photon
and
we
are
rendering
in
the
3v
scanner
adapter
version
023,
similarly
to
what
we
do
with
with
glare
right.
I
just
pre-built
it
because
it
takes
a
little
bit
of
time.
G
G
G
Just
double
check
the
cm
file
yeah.
So
now,
if
I
go
and
say
install
hardware
with
clear,
so
nothing
changes
here,
but
now
you
could
also
ask
to
install
3d
and
see
that
behind
the
scenes
we
create
a
look
and
compose
file
all
the
volumes
bindings
and
then,
if
everything
goes
well,
you
will
see
that
the
3d
adapter
is
up
and
running.
G
G
You
see
that
in
under
the
interrogation
services
we
have
both
3d
and
clear
and
3ds
markers
as
a
default
scanner.
Obviously,
if
you
want
you
can
change
it
and
make
clear
as
a
default
back,
but
that's
the
case
and
now,
let's
scan
something
just
to
quickly
demonstrate
and
see
that
it
works
and
also
at
the
same
time,
I
will
show
you
this
feature
of
scanning
photo
noise
images
I
will
have.
This
is
my
little
cheat
sheet
for
the
demo.
G
G
G
G
Yeah
so,
as
you
can
see
so
the
latest
stack,
luckily
for
all
the
people
who
use
the
photon
noise
version.
Three,
there
are
no
vulnerabilities,
but
here
there
is
a
little
older
version.
We
could
find
vulnerabilities
with
the
details
with
the
description
you
could
go
and
there
is
a
bunch
of
links
to
read
more
about
the
vulnerability,
and
so
that's
it
when
it
comes
to
operating.
G
G
G
Yeah,
you
can
see
that
we
also
detect
vulnerabilities
in
in
industrialized
images
and
then,
since
we
scanned
a
few
things,
let
me
show
you
quickly
the
important
parts
of
the
installation
it's
like
so
the
3d
adapter
has
this
reports
directory.
So,
as
I
explain
in
the
architecture
review,
we
need
some
file
system
space.
One
is
for
a
temporary
reports
where
we
store
scan
results
and
then
we
move
them
to
redis,
which
eventually
is
copied
to
hardware
database.
G
But
this
is
the
more
interesting
part.
This
is
where
we
download
the
pre-built
vulnerability
index
from
github
releases
page,
and
then
there
is
a
cache.
Actually,
this
is
a
pretty
sensitive
and
it's
currently
changing.
We
do
cache
all
the
layers
of
the
scanner
image
and
actually
it
might
grow
quite
fast,
and
this
data
is
redundant
and
actually
scanner
doesn't
need
it.
G
G
G
G
G
G
G
I
don't
know
if
you
realize,
but
it's
based
on
photo
noise.
My
intention
was
to
use
photon
3.0
to
only
show
you
the
application,
the
dependencies
like
in
npm
packages
dependencies,
but
anyway,
you
will
see
that
we
can
show
both
like
we
detect.
Basically,
what
is
in
the
package
log
json
file,
and
then
we
display
it
in
the
ui
right.
So
you
see
that
we
have
15
dependencies.
G
F
Hey
daniel
this,
this
is
amazing.
First
of
all,
thank
you
and
your
team
for
all
the
great
work
that
you
all
did
in
basically
making
3v
the
built-in
included
scanner
in
harbor
and,
most
importantly,
working
in
updating
home
charts,
docker
compose
and
everything
else
that
was
necessary.
We're
like
from
the
community
standpoint
we're
super
excited
to
have
3v
to
be
part
of
harbor.
It
offers
us
a
better
experience,
better
scanning,
more
updates.
So
this
is
awesome.
Thank
you.
G
Yeah
thanks,
that's
pleasure
and
yes,
as
you
said,
this
is
like
the.
We
would
like
to
contribute
even
more.
The
ongoing
changes
3d
has
its
root
in
the
cicd
environment,
so
it
started
as
a
you
know,
single
executable,
but
its
architecture
is
flexible
enough,
so
we
can
make
it
more.
You
know
suitable
for
such
integration
as
with
with
hardware
and
also
currently,
we
use
3d
adapter
when
you
deploy
it
in
kubernetes,
it's
deployed
as
a
stateful
set
because
of
the
file
system
structure.
G
I
was
showing
you
and
this
layered
cache
it's
a
file
system.
We
don't
have
any
locking
mechanism,
so
I
was
afraid
of
concurrent
access
to
this
directory
structure,
but
we
are
changing
it
and
it
will
very
soon
refactor
it
to
make
the
3d
adapter
a
more
scalable
deployment.
So
this
is
like
the
outline
of
the
future.
F
G
A
D
G
A
G
Exactly
so
and
exactly
db,
you
downloaded
from
the
aqua
security
3vdb.
Actually
I
think
we
were
in
the
morning
reported
an
interesting
fact
that
if
you
download
this
database
very
often
you
might
reach
the
rate
limit
of
github,
but
you
could
provide
a
github
token
to
increase
the
limit
from
60
to
5000.
I
don't
remember,
I
have
actually
opened
the
pr
to
fix
it
right
now,
and
this
is
a
crown
job.
G
G
A
A
A
G
G
G
A
G
So
what
normally
you
know,
this
default
60
request
per
hour
limit
for
us.
We
thought
that
it's
the
reasonable
benefit,
because
you
know
the
database,
you
just
download
it
in
the
beginning
and
then
detect
all
right.
There
is
no
need
to
download
it,
so
we
do
update
it
on
a
daily
basis.
Right
so
let's
say
I
scan
it
today,
so
I
downloaded
it
once
so.
There's
no
chance!
