►
From YouTube: Harbor Community Meeting 20191218 - Americas Time zone
Description
No description was provided for this meeting.
If this is YOUR meeting, an easy way to fix this is to add a description to your video, wherever mtngs.io found it (probably YouTube).
A
All
right,
hello,
everybody
and
welcome
to
another
hardware
meetup.
This
is
the
united
states
version,
that's
friendly
to
the
u.s
time
zones,
it's
the
18th
of
december
and
that's
our
last
meeting
for
the
month
year
decade.
For
the.
However,
you
want
to
say
this
is
a
recorded
conversation,
so
make
sure
you
adhere
to
the
cmcf
code
of
contact.
A
So
hello,
everybody
again!
Thank
you
all
for
attending.
So
a
couple
of
big
news
from
since
the
last
time
we
we
we
talked
hardware
1.10
is
out.
So
it's
like
a
major
milestone
release.
Thank
you
to
all
that
that
worked
on
that,
especially
you
zack
you.
You
played
the
integral
role
at
the
one
of
the
biggest
capabilities
of
the
release,
which
is
a
flag
above
scanning
component
and
again,
like
I
mentioned
earlier,
congratulations
on
the
some
of
the
blog
posts
and
the
marketing
collateral
that
came
from
from
anchor
on
the
release.
A
So
we
will
continue
promoting
that
and
get
some
more
eyeballs
on
that
throughout
the
journey,
also,
so
the
the
webinar
that
we
did
last
week.
So
hopefully,
a
lot
of
folks
are
viewing
that
and
and
they're
seeing
the
better
together
story
between
encore
and
hardware
and
getting
to
light
that
up.
So
thank
you
again
for
all
your
work.
A
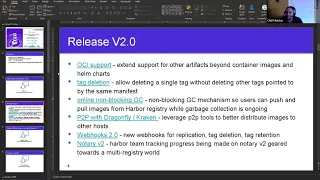
I
only
have
a
few
updates
here.
I
want
to
talk
a
little
bit
about
the
next
release
of
hardware
and
I
have
a
slide
here
that
that
alex
prepared-
and
he
also
presented
at
the
previous
community
meeting
for
harvard
that
happened
at
an
asian
time
zone
earlier
today.
So
you
guys
probably
can
see
my
screen
but
you're
not
seeing
the
presentation
screen
you're,
seeing
the
the
actual
powerpoint
I'll
leave
it
at
that,
so
the
two,
the
doe
release
of
hardware.
A
This
is
just
initially
we
started
calling
it
1.11,
but
since
it's
a
major
release
of
hardware,
we're
calling
it
to
the
dough
it
will
ship
at
or
near
cubic
on
europe,
which
is
end
of
march
beginning
of
april
of
2020.
So
that
gives
us
a
run
rate
of
about
three
and
a
half
months
and
it
will
be
anchored
by
one
of
the
biggest
changes
that's
happening
in
harbor,
which
is
the
oci
support.
This
can
enable
hardware
to
not
only
host
container
images
and
home
chairs,
but
other
artifacts
operators,
cena
bundles
scripts,
anything
that
organizations
need.
A
This
is
going
to
be
a
foundational
component
of
hardware
now,
and
it's
going
to
enable
us
to
to
to
attract
even
more
users
on
hardware
that
want
to
use
hardware
both
as
a
repository
but
as
well
as
a
policy
engine
that
does
the
plugable
scanning
that
we
talked
about
earlier.
That
uses,
anchor
and
aqua
will
be
able
to
do.
Codas
you'll
be
able
to
enforce
role-based
access
control,
you're
going
to
be
able
to
enforce
authentication
authorization.
A
So
all
of
the
cool
capabilities
of
harbor
now
will
be
applicable
to
a
wide
range
of
artifacts,
huge,
huge
release,
tag,
deletion,
we're
basically
fixing
a
situation,
that's
happening
in
harvard
today.
So
if
you
have
a
single
tag,
that's
basically
referenced
in
multiple
ways
and
you
delete
one
of
them.
They
all
get
deleted
today,
which
is
just
how
the
docker
distribution
and
harbor
have
implemented
that
work.
So
now
we'll
actually
be
able
to
properly
count
references
so
that
if
you
delete
a
single
tag,
we
won't
delete.
A
A
The
next
feature
is
something
that
has
been
asked
by
a
lot
of
customers,
especially
the
team
at
gitlab,
and
that's
don't
block
every
time.
Garbage
collection
happens
as
the
more
and
more
folks
are
using
hardware
at
a
large
large
scale,
you're,
seeing
a
huge
number
of
images
hosted
in
harbor.
So
when
garbage
collection
is
happening
either
weekly
nightly,
whatever
ends
up
being
configured,
your
users
cannot
push
or
pull
images
from
hardware,
and
this
is
becoming
a
problem
with
quality
of
service.
A
It's
becoming
a
problem
with
the
uptime
of
hardware,
so
now
we're
going
to
actually
enable
non-blocking
garbage
collection,
so
you'll
be
able
to
push
and
pull
images
while
gc
is
ongoing.
This
is
huge.
The
gitlab
folks
are
going
to
help
us
on
the
stress
and
stale
and
scale
testing
of
this
capability,
but
encourage
anybody
else.
That's
interested
to
come
in
and
help
us
here.
A
The
the
next
of
the
features
are
not
necessarily
required
for
the
to
the
door
release,
but
if
the
finishing
time
will
very
well
include
them
for
sure
and
that's
advancing
the
peer-to-peer
capabilities
with
dragonfly
and
kraken
to
enable
better
distribution
of
images
to
other
hosts,
there's
a
lot
of
lot
of
good
things.
That
can
happen
by
being
able
to
distribute
your
images
across
the
board,
but
there's
also
problems
as
well.
A
Okay,
me
and
alex-
and
a
couple
of
others
were
talking
about
that-
I
believe
it
was
two
weeks
ago
and
I
called
out
two
of
those
issues-
I'll
call
them
out
here
in
the
public,
so
you
guys
can
hear
them
as
well.
So
one
way
that
we
can
enable
the
p2p
distribution
is,
we
can
actually
add
one
more
replication
target
to
harbor
that
could
be
dragonfly
or
kraken.
So
essentially,
today
you
can
say
hey.
A
I
want
to
replicate
this
repository
or
sorry
this
project
into
docker
hub
or
I'm
going
to
replicate
that
to
azure
azure
registry.
Now
you
can
say
I
want
to
replicate
it
to
dragonfly,
and
then
you
can
use
dragonfly's
peer-to-peer
distribution
mechanism
to
properly
land
that
image
every
word
that
you
want
to
put
it
where
that's
on
the
edge
or
distributed,
and
that's
great.
However,
if
your
end
users
are
pulling
the
image
from
dragonfly.
A
Essentially
that
becomes
a
problem
for
hardware,
because
the
hardware
policy
is
no
longer
applied,
so
it
can't
just
only
distribute
the
images
because
you
lose
out
on
the
policy.
So
that's
my
biggest
concern
with
this
capability.
I
want
to
make
sure
that
when
we
design
it
to
design
it
right,
the
dragonfly
and
kraken
community
are
going
to
help
us
implement
the
distribution.
A
B
A
A
D
How
does
it
work
with
the
current
replication
and
pardon
my
ignorance
on
that
feature
when
you
replicate
to
docker
hub
or
ecr
and
the
other
registries
does?
Are
you
expected,
then,
to
also
be
running
harbor
somewhere
else,
and
it
will
pull
it
down
into
another?
Harbor
installation
and
users
interact
there
or
you
have
the
same
problem.
We
have
that
we.
A
A
That
that's
correct.
You
know
we
depend
like,
for
example,
if
we
just
distribute
to
docker
hub.
For
example,
we
depend
on
docker
hub's
ability
to
enforce
some
form
of
policy
like
authentication
authorization,
but
there's
definitely
no
scanning
and
here's
actually
the
kicker.
Let's
say
your
version,
one
of
your
docker
image,
and
you
replicate
that
because
it
was
clean,
there's
no
cvs
right,
then
the
then
the
image
the
cv
is
found.
A
Then
hardboard
itself
will
not
allow
you
to
download
that
because
you're
still
on
v1
and
it
has-
and
it
has
a
problem-
and
it
will
also
not
distribute
it
again
to
any
of
the
replication
targets.
But
if
it
has
already
been
distributed,
there's
nothing
we
can
do
like.
We
won't
allow
you
to
push
it
out
to
another
application,
because
we've
already
blocked
it,
but
the
guys
that
have
already
gotten
it
because
it
was
attributed
yesterday
or
the
day
before
the
cv
was
happening.
Those
guys
are
going
to
ship
it
out.
A
D
A
Yeah
many
many
months
ago,
we
talked
about
being
able
to
proxy
proxy
connections.
That
might
be
what
we
might
have
to
go
through.
So
basically,
the
docker
client
still
interacts
with
hardware
to
do
the
authentication
authorization
and
determine
if
the
image
can
be
pulled,
but
the
actual
image
pool
happens
from
somewhere
else.
A
We
can
proxy
that
we
talked
about
that
in
the
past.
Maybe
that's
something
that
that
that
will
do.
I
don't
know.
I
just
wanted
to
throw
it
out
there,
so
you
guys
are
engaged
on
that.
The
next
one
is
webcourse
2.0,
so
we're
adding
a
new
web
host
for
application
tag,
deletion,
attack
retention
and
as
new
capabilities
are
coming
into
hardware
or
continuously
adding
more
web
hooks
as
well.
Some
of
them
come
along
the
same
time
as
the
release
of
a
new
feature.
A
Some
of
them
come
later
on,
and
the
last
feature
is
something
that's
been
asked
by
quite
a
few
customers
today.
If
you
send
an
image
and
that
image
is
replicated
to
another
location,
the
signing
is
lost
because
the
signature
on
image
using
notary
depends
on
both
the
uri
of
the
image,
as
well
as
the
image
itself.
A
So
we're
trying
to
hop
or
push
the
notary
community
on
their
version,
two,
which
will
enable
you
to
do
signing
of
an
image
that
can
persist
across
a
replication
or
of
the
image
where
it
changes
the
download
location
and
you
don't
lose
the
signature.
We're
not
doing
the
work.
We're
merely
observers
here,
but
we're
trying
to
track
that
closely.
A
Given
the
recent
reorganization
changes
between
mirantis
and
docker
that
even
significantly
deflate
some
of
the
resources
that
docker
has
we've
been
in
some
discussions
with
another
big
harbor
customer,
that's
using
their
own
forked
docker
distribution
to
maintaining
a
combined
docker
distribution
between
the
two
of
us
that
that
will
have
updates,
we'll
maintain
it
and
you
know,
push
it
upstream
as
well
as
needed,
but
we
won't
depend
only
on
docker
for
fixing
things.
That's
ongoing
and
I
believe
that's
gonna
be
a
big
thing
for
us
as
well.
A
C
I
just
wanted
to
say
a
good
job
on
the
10
release.
I
just
upgraded
working
pretty
good.
I
haven't
played
with
all
the
advanced
features,
especially
the
scanning
yet,
but
we
hope
to
integrate
it
with.
I'm
not
sure
if
twist
lock
is
on
the
list
but
or
whatever
twist
lock
is
going
to
get
renamed
to
not
how
I'll
bought
them,
but
I
hope
to
eventually
get
that
integrated
into
harbor.
One
comment
is
as
we're
trying
to
set
up
our
our
clusters
for,
for
users
is
enabling
ldap
authentication.
C
It
seems
that
you
have
to
like
delete
all
your
existing
users
before
you
can
enable
ldap.
I
could
be
wrong
about
that,
but
that
seems
like
sort
of
a
like
user
management
being
able
to
like
get
that
going,
because
that
may
not
be
a
day
one
operation,
but
you
might
already
have
things
in
there
that
you
don't
want
to
delete
that
people
are
using.
That
would
be
maybe
an
area
that
could
be
improved
upon
for
for
being
able
to
have
both
local
users
and
ldap.
At
the
same
time,.
A
Unfortunately,
that
that
was
a
principle
that
harvard
made
at
the
beginning,
where
you
could
either
do
ldap
or
basically
use
hardware
as
your
user
store
in
a
database.
So
once
you
actually
make
one
of
the
choices
you
cannot
go
back.
That's
that's
basically
what
you
guys
were
encountering,
so
you
can
either
choose
ldap
or
the
other,
but
not
both
if
there's
a
key
user.
A
A
A
D
Nothing
nothing
major
I
mean
we
have.
We
have
some
some
new
features
we'll
be
adding
into
the
anchor
adapter
stuff
for
harbor,
some
a
little
better
like
granularity
support
for
for
the
vulnerabilities
and
leveraging
some
of
angkor's
white
list
and
policy
capabilities
so
that
you
can
kind
of
filter
what
gets
shown
in
harbor.
So
it
would
more
match
what
your
policy
enforcement
is
getting
done
on
the
other
side
of
encore,
with
like
the
kubernetes
controllers
and
such
and
we're
working
with
some
some
mutual
customers
on
that
stuff.
D
So
there
will
be
updates
coming
on
that
adapter
container,
the
actual
adapter
service
itself.
So,
if
anybody's
watching
that,
let
me
know
if
there's
any
any
additional
issues
on
that
specific
adapter
implementation
or
feature
set.
I'm
happy
to
have
those
discussions
and
github
is
the
best
spot
to
have
those
conversations.
A
Okay,
cool
by
the
way,
I
know
you
were
looking
into
windows
containers
has
that
progressed,
because
I
think,
as
windows
containers
have
become
more
and
more
prevalent
in
this
ecosystem.
Hardboard
is
probably
one
of
the
few
registers
that
can
host
them
and
apply
all
this
different
fanfare
that
harbor
does
being
able
to
scan.
Those
windows
continues,
is
going
to
be
big
and
since
encore
enterprise
is
the
only
paid
solution
that
works
with
hardware
today,
that
might
be
a
good
scenario
for
you
guys
to
light
up.
D
Yeah
yeah
we're
active,
we're
actually
that's
actively
in
development
right
now
and
we'll
be
it's
planned
for
our
next
enterprise
release
sometime
in
queue,
late,
q1,
early
q2
expected
again
no
guarantees
there,
yeah
and
so
yeah
when
we're
working
with
some
folks
from
microsoft
on
making
sure
that
that's
that's
kind
of
short
up
and
and
the
best
that
it
can
be.
And
then
the
adapter
will
just
kind
of
seamlessly
support
that
so
yeah
major
changes
necessary
for
hardware
users
that
would
just
start
being
able
to
scan
them.
A
Absolutely
if
you
guys
need
any
help
on
the
microsoft
front,
just
let
me
know,
and
then
once
you
guys
do
it
seek
windows
from
from
kubernetes
community
will
definitely
amplify
that
as
well,
because
that's
important
to
us,
like
all
our
kubernetes
customers
using
windows,
we
want
that
plus
all
our
hardware
customers.
So
you
you
got
you
guys,
will
get
multiple,
facetime
and
and
promotions
from
from
two
different
areas.
