►
From YouTube: ROS 2 Security Working Group (09 Nov 2021)
Description
No description was provided for this meeting.
If this is YOUR meeting, an easy way to fix this is to add a description to your video, wherever mtngs.io found it (probably YouTube).
A
B
A
D
A
A
E
E
E
Basically,
what
I've
been
working
on
is
I've
been
porting
a
been
part
of
a
team.
That's
supporting
a
large
ros
one
code
based
ii.
It's
targeting
multiple
ground
platforms.
It
is
an
enormous
legacy.
Application
that's
been
developed
for
a
long
time
and
it's
still
under
active
development
and
experimentation.
So
it's
not
really
a
you
know
like
product,
yet
it's
it's
still
very
much
in
flux,
with
new
capabilities
getting
added
to
it
for
the
us
government.
E
So
we're
still,
you
know
trying
to
figure
out
how
everything's
going
to
work
with
it
and
so
kind
of
in
parallel
with
that,
we've
also
been
looking
at
how
we
can
turn
on
security
for
the
system.
We
largely
didn't
do
anything
with
it
with
ross
one
security.
Just
because
I
mean
I
you're
all
familiar
with
ross
one
security.
E
We
didn't
see
a
big
advantage
at
that
point,
but
now
we're
very
much
interested
in
using
dds
security
and
secure
roster
to
really
lock
this
thing
down,
and
you
know,
and
not
only
secure
the
application,
but
also
try
and
kind
of
get
the
security
processes
integrated
into
our
workflow,
because,
unfortunately,
up
until
now,
we've
just
been
focused
on
development
and
testing
and
haven't
really
the
security
aspect.
Just
haven't
been
a
part
of
our
part
of
our
workflow.
E
E
Importantly,
we're
probably
going
to
use
multiple
dds
domains
to
kind
of
manage
the
traffic
and
make
everything
manageable
from
a
map
from
a
dds
standpoint,
and
we
really
need
to
restrict
access
between
the
different
systems
and
network
interfaces
on
this
vehicle.
So
we
really
want
to
make
sure
that
everything's
kind
of
isolated.
So
if
one
system
gets
compromised,
you
know
doesn't
take
down
the
entire
vehicle
kind
of
the
other
use
cases
in
the
back
of
our
mind.
Are
things
like
uav
swarms
where
you've
got
dozens
of
uavs,
maybe
with
multiple
computers?
E
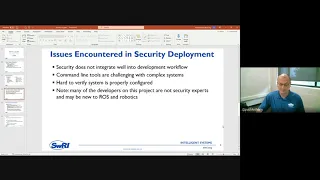
What
we
have
found
from
our
kind
of
developers
that
are
working
with
it
is
they're
really
having
a
hard
time.
Integrating
the
sros
to
into
their
development
workflow
particular
things
we've
we've
encountered.
Are
you
know
when
the
command
line
tools?
When
we
start
talking
about
you
know,
half
those
you
know
trying
to
have
a
half
dozen
computers
that
are
all
you
know,
maybe
configured
differently
or
have
different
policy
configuration.
You
know,
different
computers
are
supposed
to
have
different
levels
of
communication
with
other
computers
you
know
like.
E
Maybe
we
want
a
computer
vision
system
to
talk
with
one
computer.
That
then
sends
you
know
some
kind
of
processed
version
of
the
computer
vision
imagery.
You
know
like
object,
detect
you
know
doing
whatever
we're
doing
like
pedestrian
detection,
object,
detection,
semantic
segmentation
and
then
sending
that
on
to
you
know
more
of
the
like
path
planning
computer.
E
You
know
we
want
to
kind
of
restrict
the
communication
between
all
those
computers
to
just
the
topics
that
they're
that
are
actually
relevant
to
each
other.
So
we
don't
just
have
a
free-for-all
talking
between
the
systems
and
and
so
kind
of
the
first
feedback
we
got
from
the
developers
are.
The
command
line.
Tools
are
really
hard
to
work
with,
in
this
case,
like
I'll
talk
about
that
a
little
bit
on
our
next
slide,
it's
hard
to
verify
that
the
system
is
properly
configured.
E
You
know,
add
the
code
they
develop
to
a
secure
system
and
so
kind
of
existing
command
line
tools,
as
I'm
kind
of
paraphrasing
some
of
the
direct
feedback
I
got
one
was
the
cat
felt
like
an
all
or
nothing
thing
like
you
know
they
they
followed
the
roster
tutorial.
They,
you
know,
created
an
enclave.
E
You
know
added
it
to
their
command
line,
launch
arguments
and
then
they
said
well
everything's
encrypted,
but
trying
to
do
more
granular
levels
of
control
felt
like
a
lot
of
effort.
You
know
we're
going
in
and
hand
editing
policies
like
the
governance
and
permissions.xml
files
to
especially
to
work
with
multiple
ros
domains
or
dds
domains.
E
E
It
was
really
tough
to
get
everybody's
security
environment
set
up
the
same
way
and
then
reproduce
changes
like
when
somebody
made
a
change.
It
was
hard
to
do
it
because
you
know
we,
you
know,
even
if
we
version
control
like
the
xml
files,
that
control
the
policies
and
the
governance
like
you'd
end
up
having
to
regenerate
the
assigned
versions
of
those,
and
it
was
hard
to
verify
the
system
was
configured
as
expected.
Like
you
know,
right
now,
you
know
to
make
sure
that
we
really
had
secured
a
topic.
E
We
would
end
up
looking
at
in
wireshark
to
see
if
it
was
encrypted
or
using
some
of
the
other
linux
system
tools
to
see
you
know
things
were
actually
as
we
thought
they
were
and
so
kind
of
the
overall
consensus
is
yeah.
We
can
do
it,
but
it's
going
to
be
really
tough
to
make
this
part
of
our
normal
workflow
and-
and
I
think,
that's
unfortunate,
you
know
we-
we
really
do
want
secure
systems,
and
you
know
I
think
about
what
happens.
E
If
I
unleash
this
on
a
distributed
team
with,
you
know
dozens
of
developers
and
how
do
we
and
they're
all
you
know
like
when
they
write
a
new
node
that
publishes
new
topics?
How
do
they
get
that
properly
configured
and
then
distribute
those
changes
to
the
other
team
members
and
so
kind
of
the
wish
list
we
kind
of
internally
thought
about
is
one.
It
would
be
really
nice
if
we
had
a
graphical
tool.
E
So,
like
I'm
thinking
like
rqt
graph,
could
I
actually
look
at
the
topics
in
an
rqt
graph
and
see
how
they
are
encrypted
or
make
sure
that
they
are
in
fact
encrypted?
You
know
which
keys
or
enclaves
are
they
using
for
encryption
and,
and
that
fits
into
the
view
of
like
when
we
have
a
developer
that
adds
new
code.
We
want
to
make
sure
that
they
can
easily
double
check
that
their.
What
they
did
is
right
and
also
we
want
to.
E
Frankly,
we
want
to
look
at
our
existing
system
and,
as
we
slowly
enable
security
options
for
everything
we
want
to
make
sure
that
we're
we're
getting
everything
locked
down
as
we
expect
we'd.
Also,
you
know
one
of
the
other
things
that
came
up
is
you
know
we
have
continuous
integration
tests
and
deployment.
You
know
through
things
like
docker
containers,.
E
You
know
setting
up
environment
variables,
you
can
figure,
the
security
is
something
we
can
do,
but
we've
already
ran
into
issues
where
somebody
has
a
bug
and
it
turns
into
oh.
Did
you
set
this
environment
variable
properly
in
the
terminal
and
we'd
really
like
to
get
it
more
of
a
programmatic
like
everything
gets
set
through
a
command
line,
or
some
sort
of
you
know
configuration
file
to,
and
you
know
to
make
sure
that
we
can
really
reproduce
our
environments
and
change
them
effectively.
E
One
of
the
other
things
the
developer
brought
up
was,
could
you
know,
could
something
like
rostitude,
node,
info
or
rost2
topic
info?
Show
you
information
about
the
enclaves
that
the
node
is
using,
or
you
know
how
the
or
how
a
publisher
and
subscriber
is
configured
for
encryption
and
down
the
line.
We're
also
thinking
about
things
like
key
management.
You
know:
how
do
we
in
that
uav
swarm
case?
How
do
we
deploy
keys?
You.
E
Keys
to
this
entire
swarm,
that's
you
know
not
involving
a
lot
of
bash
scripts,
and
you
know
copying
over
encryption
keys
one
by
one
or
you
know
very
ad
hoc,
so
yeah,
that's
kind
of
my
sorry
and
that's
kind
of
my.
I
guess
it's
kind
of
my
presentation,
that's
kind
of
what
we
ran
into
and
that's
kind
of
what
we're
thinking
about,
and
I
just
didn't
know
if
the
overall
security
working
group
commit
community
is
is
also
kind
of
thinking
about
these
issues.
E
A
There
thank
you
very
much
for
the
interesting
presentation,
with
the
an
actual,
very
real
use
case.
You're
also
touching
quite
a
few
points
that
we
have
already
discussed
and
some
of
which
are
more
or
less
already
ongoing.
So
before
I
I
leave
the
floor
so
that
others
can
can
react
and
I'm
sure
some
of
them
have
quite
a
few
things
to
say.
E
Yeah,
so
we're
we're
not
directly
related.
I
talked
with
ross,
I
quite
a
bit
since
you
know:
we've
got
quite
a
few
other
people
here
at
sweary
yeah.
I
talked
with
matt
robinson,
quite
a
bit
yeah
and
they're.
I
should
have
mentioned
that
too
yeah
they're,
definitely
thinking
about
a
lot
of
the
same
things
too.
A
B
A
Think
and
then
seeing
that
four
of
us,
I
think
it
would
be
interesting
to
to
get
our
two
communities
in
touch
on
those
particular
topics
right.
My
second
question
was
simply
if
you,
if
you
or
your
team,
had
a
look
at
the
links
I
provided
on
the
metrics
room
and
the
work
we
are
doing
on
the
launch,
launch
files
side
of
things.
E
A
F
So
I
I
think
what
you've,
which
you
brought
up
is
is
is
quite
relevant
and
pretty
accurate
in
a
sense,
a
lot.
A
lot
of
what
the
working
group
has
sort
of
been
focusing
on
is
the
capability
and
just
like
in
a
lot
of
the
sense
that
security
is
now
possible,
but
it's
not
necessarily
usable
so
that
a
lot
of
the
a
lot
of
the
pieces
and
components
are
there.
F
But
the
usability
of
these
tools
is
is
still
lacking
and
I'm
I'm
a
bit
I'm
pretty
interested
in
what
you
kind
of
envision
and
maybe
particular
about
the
the
use
case.
So
so
you're
talking
about
we're
dealing
with
another
ross
community
members
that
are
in
other
domains
such
as
planning
and
perception,
and
so
it's
it's
security
is
somewhat
outside
of
their
their
scope,
but
the
ways
they
they
intend
to
enable
security
features.
B
F
F
The
no
no
dl
to
kind
of
co-locate
the
the
information
to
generate
the
policy
as
close
as
possible
to
the
code
base
that
uses
it
so
that
code
location,
would
would
make
it
fairly
easy
to
track
modified
policy
modifications
or,
and
that
would
that
would
be
generated
downstream.
You
know
either
by
your
contingent,
continuous
integration
pipeline
or
your
deployment
pipeline
services.
F
E
Yeah,
I
I
don't
know
that
we
haven't
have
quite
an
ideal
in
mind
and
and
that's
why
I
was
a
little
I
didn't
want
to
come
in
here
and
just
be
like
complaining
to
be
honest,
because
I
really
do
appreciate
what
the
community
has
done.
I
think
it's
fantastic.
You
know,
I
I
think.
If
there
are
existing
tools,
I
could
use
as
a
basis
we'd
be
really
excited
for
that.
You
know
any
as
standard
as
we
could
get.
E
D
D
C
Thank
you
for
for
sharing
with
what
you
you
share
by
the
way
super
cool
to
have,
like
other
members
of
the
community,
also
sharing
their
views,
and
I
think
what
the
security
working
group
definitely
at
least
historically,
I
I
felt
it
needed
was
external
input
from
users
from
power
users
like
liqueri,
so
it
would
be
awesome
to
get
more
and
more
of
your
input
in
the
line
that
roughing
was
suggesting
actually
in
terms
of
usability
and
criticism.
So
so
please
don't
don't
be
shy.
C
D
C
Right
now,
and
as
far
as
I
know,
though,
jeremy
correct
me,
if
I'm
wrong,
we
don't
really
have
this.
As
far
as
as
I
believe
I
know,
some
other
working
groups
are
working
on
on
this
direction.
Specifically,
I
can
give
you
a
pointer
to
the
one.
That's
currently
being
used
in
the
real
time
working
group,
which
is
also
being
considered
in
a
hardware
acceleration
working
group,
so
I'll
I'll,
just
fetch
it.
A
C
Terrible
turtlebot
is
great
to
to
be
honest
and,
and
I've
got
a
few
of
those
here
with
me
also
turtlebot
is
great.
I
think
what
what
somehow
we
need
in
here
is,
and
probably
that's
that's
your
call,
jeremy.
We
need
somehow
a
bit
of
leadership
in
here
and
define
you
know.
We're
gonna
grab
like
this
subset
of
the
computational
graph
of
the
turtlebot.
C
Both
all
of
us,
I
think
it's
what's
probably
gonna,
take
off
down
the
road,
so
turtle
boat
is
awesome.
I
I
love
the
turtle,
but
actually
we
did
community-wise
some
work
in
the
past
around
the
turtle
boat,
aws
and
and
myself
as
part
of
bds
robotics.
We
cooperated
on
on
essentially
doing
threat
modeling.
C
F
F
D
F
All
using
containers-
you
just
you,
know,
pull
it
and
spin
it
up
and
it
starts
a
vibe
session.
It
drops
you
in
with
the
turtlebot
demo.
You
can
flip
whether
you
want
to
use
everything,
security
or
not
or
use
your
custom
profile,
and
what
that's
sort
of
an
insight
is
to
really
the
scale
that
even
modest
ground-based
service
robots
are
kind
of
facilitating
in
terms
of
number
of
topics
and
number
of
nodes
and
and
how
these
raw
graphs
are
composed
with
nodelets
or
compose
nodes,
and
that's
what
that's
been
really
used.
F
Yeah
like,
like
you
know,
victor
said,
these
are
really
useful
for
teasing
out
the
the
use
case
or
the
the
friction
points
and
using
the
esros
tool
so
like
in
particular,
nav2
rolling
is
sort
of
a
moving
target.
You
know
every
time
you
know
pr's
get
merged,
there's
certain
parameters,
get
that
get
renamed
or
nodes
that
get
renamed
or
whatnot.
F
F
E
E
E
Well,
in
particular,
things
like
you
know
the
node
discovery
and
things
like
that,
if
you
can
restrict
it
to
a
single
domain,
it's
going
to
be
a
lot
more
efficient
and
you
know:
we've
we've
had
some
conversations
with
like
rti
and
when
we
talked
about
our
our
system,
architecture
they're,
like
yeah,
you're,
probably
going
to
need
to
use
the
dds.
You
know
multiple
dds
domains
just
to
keep
traffic
manageable
and
your
system
performing
like
you
want
it
to
so.
F
This
this
is
a
small
side
that
I've
I've
been
meaning
to
bring
up
with.
The
middleware
group
is
the
the
use
case
of
sworn
robots
with
rost2
and
the
scalability
issues
and
using
domains
like
domains
are
really
nice
and
like
it's
a
hard
cutoff
that
limits
the
discovery
overflow
of,
like
you
know,
and
avoiding
crosstalk,
but
at
least
from
the
specs
perspective,
there's
a
finite
number
of
domains.
F
Maybe
another
approach
of
partitioning
the
dds
domains
for
large
scale
swarms
I
felt
like
dds
perpetitions
were
a
fairly
good
fit,
particularly
because
they
can
be
cons
and
they
can
be
considered
directly
in
the
access
control
so
from
a
dds
security
perspective,
they're
fairly
transparent
with
dds
bridging.
I
think
it
adds
a
whole
new
like
layer
of
complexity.
In
terms
of
suddenly
your
configuration
files,
the
access
policy
and
permissions
you
set
are
a
lot
more
flexible
than
maybe
you
anticipate.
So
if
you,
if
you're
like
from,
if.
D
A
F
D
A
A
B
For
those
I
don't
know,
if
you
remember,
but
just
a
quick
recap:
kalian
and
his
group
unique,
were
asking
for
support
for
pikachu
11
urls
on
the
security
properties
which
currently
nor
frost
soon
or
the
the
middlewares,
the
middle
implementations
to
support.
So
we
stepped
up,
and
they
said
that
we
could
add
that
support
for
fast,
fast
dds.
B
B
The
test
is,
they
are
already
already
done,
but
this
integration
in
the
in
the
environment
and
in
the
is
missing,
and
we
don't
want
to
make
the
merge
until
that's
that's
in
place,
so
I'm
guessing
that
it
will
be
delivered
officially
on
our
next
mine
or
released
at
the
end
of
december.
I
think
that
will
be
version
2.5
and
on
the
other
hand,
we
have
this.
B
B
Some
design
in
order
to
how
we
can
integrate
all
this
support
into
the
current
enclave
architecture
of
of
securos
that
was
proposed
to
the
india
rust
to
design
a
repository,
which
was,
I
think
it
was
already
approved,
and
there
is
also
a
pull
request
for
the
fast
rtgs
rmw
implementation.
In
order
to
support
this,
which
integrates
nicely
with
the
implementation
that
we
did
in
in
fast
ets.
B
D
B
Particular
side
and
also
the
pull
request
that
we
made
to
the
rmw
implementation
to
be
merged
and
just
as
a
side
note,
we
are
also
preparing
for
ford
niger
for
kalyan
and
his
team
demo,
so
that
they
can
showcase
all
these
new
features
to
their
clients,
and
I
think
that
maybe
it
would
be
also
good
if,
when
this
team
was
prepared,
we
can
showcase
it
here
in
the
in
the
working
group.
This
is
planned,
I
think,
for
the
end
of
december.
B
D
A
C
A
few
of
those
will
be
given
in
the
ros
industrial
conference
flavor
in
europe,
which
will
happen
in
december
early
december
and
then
there's
just
ongoing
conferences,
as
in
any
other
field
in
security
all
the
way
or
all
through
the
year,
we're
giving
a
number
of
them
in
upcoming
venues.
The
next
one
is
in
black
hat,
and
I'm
sharing
it
link
here
in
the
chat
for
those
of
you
that
are
not
familiar
with
black
hat.
C
On
top
of
the
dds
security
plugins,
you
just
right
away
gain
security,
however,
as
probably
most
of
you
are
aware,
as
of
now,
security
is
not
a
product
that
you
just
patch
or
apply
once
and
that's
it
you
you
get
secure,
it's
actually
a
process
and
you
need
to
care
about
it
over
and
over
and
over,
and
there
are
methods
to
do
so,
both
defensively
and
offensively.
In
this
case,
we
are
tackling
the
problem
from
an
offensive
perspective
with
a
group.
This
group
is
represented
by
essentially
dds
vendors.
C
We
had
80
link
in
the
group
researching
with
us.
We
have
also
tx1,
which
is
a
big
cyber
security,
firm
trend
micro,
which
is
another
huge
cyber
security,
firm
ads
robotics,
which
is
the
site
that
I
I
participated
in
at
the
time,
and
this
has
gone
for
quite
a
few
months.
It's
been
going
on
for
for
quite
a
while.
C
But
we
also
find
a
few
above
eight
if
you're
familiar
with
cvss,
they
affect
all
of
the
dds
implementations
we
analyzed,
which
are
essentially
the
three
open
source
ones
and
the
three
most
popular
proprietary
ones,
including
rti's,
core
dx
and
a
few
others.
Of
course.
That
also
applies
to
approximates
80
links
and
a
few
others,
and
it
shows
really
nicely
and
really
directly
how
security
needs
to
be
considered
end
to
end
and
way
way
beyond.
Essentially,
some
of
the
aspects
we're
typically
discussing
here.
C
So
my
proposal
to
the
group
was
if
such
topics
are
interesting.
I
can
possibly,
of
course
bring
myself
and
also
maybe
bring
a
few
other
of
the
authors
who
participate
in
this
research
and
try
to
give
a
20
minute
session
in
here
and
give
you
kind
of
like
a
heads
up
about
it
again.
This
is
happening
in
two
days
and
I'm
not
really
sure.
When
is
the
next
security
working
group
meeting
that
we
could
schedule
it
in
the
future?
I
just
wanted
to
at
least
bring
the
opportunity
in
here.
D
A
C
Month
sounds
good
yeah,
so
if
we
can
book-
and
you
tell
me
jeremiah
how
much
time
we
have
and
I'll
schedule
things
I'll
accommodate
whatever
time
you
give
me
like,
if
it's
10,
we
will
do
it
in
10.
If
we
have
15,
we
will
do
it
in
15..
Whatever
and
again
we
we
will
try
to
keep
it
high
level,
but
also
the
plan
is
to
release
details
about
disclosures
and
how
you
can
actually
trigger
each
one
of
these
flows.
C
In
a
nutshell,
what
that
means
is
that
you
can
really
easily
dissect
whatever
network
packages
from
rtps,
which
means
any
rush
to
interaction
right
now.
Our
current
implementation
of
the
dissector
does
not
include
dds
security.
I
have
one
in
my
local
development
station
that
does
include
some
aspects
of
the
dds
security,
plugging
and
specification
and
spec
overall,
but
it's
not
it's
not
pushed
publicly
yet.
C
There
we
go
yeah,
so
that's
that's
it
and
that's
a
great
starting
point
for
anyone.
That's
caring
about!
Also
this
topic
you
can
play
around.
You
can
do
quick,
sniffers
of
traffic.
You
can
enable
encryption
and
you
can
see
how
still
you
get
some
information
out
of
it.
You
can
try
to
break
some
of
the
fields
so
both
for
dds
vendors,
security,
researchers
and
defenders.
This
is
typically
the
way
things
work
from
a
dissection
and
research
perspective.
So
encouraging
you
to
take
a
look
at
there
and
I'll
try.
C
You'll
enjoy
you,
you
won't
be
disappointed,
so
we
can.
I
mean
there
are
things
we
still
can't
disclose,
but
I
can
give
you
I
can
give
you
something
interesting,
which
is
that
we
are
being
blocked
by
governmental
organizations
not
to
do
full
disclosure,
because
apparently
we
hit
flaws
that
are
being
used
by
military
contractors
and
that's
raise
things
like
heavily
so
so
it's
been
a
fun
story
from
a
research
perspective,
but
I
think
from
from
so
from
a
user
perspective.
A
A
All
right
folks,
we
are
just
on
time,
so
I
propose
we
stop
here
for
for
today,
as
I
told
you
earlier,
I
will
be
setting
up
a
shared
document
to
pour
ideas
on
on
the
reference
device
and
see
if
we
can.
If
we
can
actually
agree
on
something
and
as
usual,
I
will
be
cleaning
up
the
agenda.
It's
always
the
same
link
and
if
you
have
any
anything
that
you
want
to
to
discuss
or
anything
that
you
want
to
to
present
just
feel
free
to
to
add
it
to
the
agenda.
