►
From YouTube: ROS 2 Security Working Group (13 Dec 2022)
Description
No description was provided for this meeting.
If this is YOUR meeting, an easy way to fix this is to add a description to your video, wherever mtngs.io found it (probably YouTube).
A
A
A
B
Okay,
I'll
I'll
introduce
myself
and
then
Benjamin
Ben
introduce
himself
and
then
I
can
start
the
presentation,
I
guess
so
has
so
we
have
a
bats
on
my
tech
lead
at
the
amrc
in
Sheffield.
That's
the
advanced
manufacturing,
Research
Center
and
last
year
we
joined
the
Ross
industrial,
Consortium
and
I'm
sort
of
the
representative,
the
one
that
sort
of
talks
with
the
rest
of
the
European
Consortium
so
I've.
B
B
But
the
reason
why
we're
here
is
that
one
of
the
approaches
that
we
started
this
year
is
involved
as
sort
of
the
transition
from
Ross
one
to
Ross
still
because
I've
got
quite
a
long
experience
on
lost
one
but
I
never
touched
roster,
and
it
was
about
time
for
for
us
to
start
so.
I
I
don't
have
much
if
any
experience
in
security,
while
Ben
I
think
comes
from
the
sort
of
opposite
and
the
perspectives
yeah.
It's
a
way
of
experience
in
Ross,
but
it's
more
of
an
excellent
security.
B
So
I
designed
one
work
package
on
that
project
that
we're
working
on
just
to
look
at
the
security
sort
of
side
of
Ross
and
how
that's
implemented
and
just
if
you
could
see
a
lot
almost
like
a
trade-sided
to
see
the
strengths,
the
and
the
weaknesses
and
and
that's
what
basically
Ben
has
done
as
part
of
this
project
and
I.
Think
I
can
leave
that
I'm
telling
you
a
bit.
So
you
can
introduce
yourself
and
let
me
start
with
that
presentation.
C
C
The
Ross
security
tool
when
it
sets
up
a
key
store,
obviously
because
you
thought
that
this
was
too
complicated
or
something
it
actually
unifies.
Those
two
certificates,
the
identity
and
the
permissions
certificate
authorities
into
a
single
certificate
that
lives
at
the
root
of
the
key
store,
and
it
creates
some
links
to
them
in
the
key
store
so
that
it
fulfills
both
functions.
C
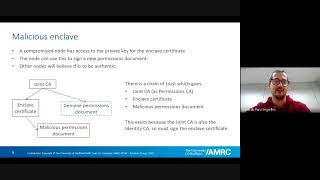
Normally,
this
isn't
a
problem.
The
nodes
publish
their
permissions
documents,
the
other
nodes
receive
them.
They
verify
the
signature
which
goes
against
the
against
the
authority
that
they
have
that
Authority
is
set
up
for
them,
as
the
permissions
Authority,
so
they're
quite
happy
to
accept
the
permissions
documents
and
everything
works
and
everybody's
happy.
C
However,
what
happens
if
you
have
an
enclave
that
decides
to
misbehave?
You
know
the
whole
point
of
having
security
is
so
that
you
can
start
to
separate
the
different
parts
of
a
robot
from
each
other.
So,
for
example,
if
a
user
has,
you
know
they're
running
RVs
on
their
laptop
and
you
maybe
don't
quite
trust
their
laptop,
it's
a
user's
machine,
but
you
want
to
give
them
read
access
to
the
robot,
so
you
start
setting
up
ACLS
so
that
they
only
have
read
access.
C
They
can't
move
the
robot
whatever
there
are
all
sorts
of
Access
Control
decisions.
You
know.
If
we
have
access
controls,
we
need
to
be
able
to
use
them
and
they
need
to
work
so
assuming
that
the
permissions
have
been
set
up
to
allow
different
parts
of
the
robot
different
amounts
of
access
to
each
other.
C
E
F
C
B
C
C
If
the
the
solution
I
mean,
the
straightforward
solution
is
to
have
two
certificate
authorities
as
DDS
had
in
the
beginning
and
then,
although
the
node
can
still
sign
a
document
with
its
Enclave
certificate,
that
document
is
no
longer
trusted,
because
the
Enclave
certificate
is
no
longer
signed
by
the
permissions
Authority.
It's
only
signed
by
the
identity.
C
Which
you
know
restores
the
security
you
know
restores
the
ability
to
set
proper
ACLS
on
the
nodes,
so
I
mean
I
was
I
I.
Actually,
you
know
worked
this
out
when
I
was
thinking
about
rollover
of
certificates
and
and
signing
certificates
with
other
certificates,
so
that
you
can
roll
over
the
route
and
so
on
and
I
was
thinking
backwards
through
the
problem,
I
said
actually
I.
Think
I
can
do
this
here.
I
think
I
can
cheat
I.
C
D
C
The
Listener
is
correctly
failing
to
be
able
to
subscribe.
The
publisher
of
the
talker
is
publishing
and
The
Listener
is
not
allowed
to
subscribe,
then
acting
as
a
malicious
listener
load
I
take
the
permissions.
Xml
and
I
just
change
the
topic,
so
the
listener
was
allowed
to
subscribe
to
something
else,
and
it
just
changes
the
topic
to
the
to
the
topic.
C
G
F
F
You
want
to
be
cautious
that
you're
that
that
CA
isn't
signing
authenticating.
Another
CA
to
like
you
know,
extend
the
chain
of
trust
further
to
truncate
that
the
ca
can
deliberately
choose
to
only
sign
certificates
that
do
not
have
the
certificate
Authority
flag
set.
So
then
the
chain
of
trust
truncates
there
from
what
I
remember
I
thought
we
were
using
the
x5x9
python
library
to
deliberately
disable
that
flag
for
certificates
for
Toc
for
the
enclaves.
But
maybe
did
you
find
that
that
was
that
wasn't
the
case.
No.
C
The
when
you
sign
the
permissions
documents
you're
using
S
mime,
the
permissions
document
is
not
a
certificate.
It's
just
an
XML
certificate
signed
with
s
mime,
which
means
that
it
is
not
supposed
to
be
signed
by
a
certificate
Authority
at
all.
It's
supposed
to
be
signed
by
a
plain
endpoint
certificate,
so
the
the
signature.
C
Not
it's
it's!
It's
a
it's
a
possibly
a
misunderstanding
of
the
function
of
the
of
the
function
of
the
different
certificates
involved,
I'm,
not
sure
so
as
the
as
the
ross2
security
tool
creates
the
key
stores
and
so
on.
This
certificate,
Authority
certificate
has
has
capath
zero.
It's
it's
not
allowed
to
sign
any
sub-authorities
when
the
permissions
document
is
signed
directly
by
the
certificate
Authority,
that's
not
actually
how
it's
supposed
to
work.
You're
supposed
to
always
have
an
intermediate
certificate
by
x509
Design.
C
So
the
idea!
Well,
if
you
go
back
to
the
original,
the
idea
here
is
that
normally
you
would
have
the
permission,
certificate
Authority
and
then
you
would
have
sub
certificates
issued
perhaps
to
individual
administrators
who
had
authority
to
sign
permissions
documents,
a
personal
certificate
for
a
you
know,
for
a
systems
administrator,
and
then
they
would
sign
the
permissions
document
with
their
personal
certificate.
C
C
F
C
I
think
I
think
you
still
need
well,
certainly
as
ros2
security
creates,
the
certificates
that's
not
implemented,
maybe
maybe
it
could
be
fixed
just
by
changing
the
flag.
I
didn't
I
didn't
think
that
you
could
I
thought
that
you
actually
needed
the
sign
data
flag
in
order
to
do
the
certificate
exchange,
because
you
have
to
sign
diffie-hellman
stuff
as
part
of
the
exchange.
Don't
you
even.
G
F
F
C
F
F
C
D
G
C
F
F
C
I
mean
looking
at
the
looking
at
the
flags
the
this
this
this
this
flag
is
the
one
you're
talking
about.
Isn't
it
this
digital
signature,
flag,
you're
saying:
if
can
you
turn
that
flag
off
on
The,
Enclave
certificate
and
I?
Think
the
answer?
Is
you
can't?
Because
you
can't
do
anything
without
it?
You
can't
do
you
can't
prove
your
identity
without
it,
because
the
way
you
prove
your
identity
is
by
signing
stuff.
C
F
C
C
D
C
I
mean
it
would
be
nice
to
be
able
to
have
a
single
authority
to
that.
You
could
change
from,
but
it's
it's
difficult
to
see
how
it
works,
because
the
the
simple
Act
of
signing
a
certificate
with
the
permissions
Authority
gives
that
certificate
permission
to
set
any
permissions
on
the
whole
robot.
It's
actually
quite
a
serious
act,
signing
something
with
the
permissions
Authority.
C
D
E
E
E
I,
don't
know
if
you
have
seen
this
before
or
not,
but
the
thing
is
that
you
store
the
private
key
on
a
hardware,
secure
module
that
then
the
rmw
can
retrieve
when
neat
or
fast
EDS,
rather
can
retrieve
when,
when
needed,
using
a
film
or
or
kind
of
a
password
right.
So
it
makes
the
it
makes
systems
more
secure.
E
C
C
C
C
D
C
E
E
C
C
C
This
one,
so
normally
when
you,
when
you
generate
a
x509
certificate
for
a
web
server
or
whatever
you
start
by
generating
your
private
key
locally,
you
generate
a
public
key
from
the
private
key.
You
generate
a
certificate
signing
request
from
your
public
key.
You
send
that
off
to
the
certificate
Authority,
they
sign
it
and
it
comes
back
as
a
certificate
that
you
use
and
your
key
always
stays
in
your
possession
and
their
key
always
stays
in
their
position,
and
you
never
have
to
switch.
C
E
C
No
I
think
this
is
I
think
this
is
quite
a
I
mean
it's
I
think
it's
maybe
a
little
bit
of
a
an
approach
change.
You
know
that
that
you
need
a
Security,
Management
setup
that
is
isolated
from
the
robot
and
has
private
keys
for
the
certificate
authorities
and
everything
else
so
yeah
anyway.
This
is
this
is
where
I
this
is
where
I
came
to.
You
know:
where
do
I
run
this
command?
C
If
I
run
it
on
in
My
Signing
system,
then
I
have
to
transport
the
private
key
back
to
the
robot,
which
is
bad
security
practice.
If
I
run
it
on
the
robot,
then
I've
got
to
put
my
certificate
Authority
Key
on
the
robot,
which
is
even
worse
so
I
mean
you
know.
It
just
needs
options
to
generate
the
request
and
do
the
whole
dance
in
the
right
order.
With
everything
you
know.
F
Yeah,
the
the
processor
of
this
tooling
that
I
wrote
with
keyment
and
calm
armor
I
I.
That
was
my
initial
approach,
where
I
sort
of
have
a
workspace
and
everything
was
sort
of
staged
in
the
file
system,
and
so
you
could.
You
could
have
an
intermittent
stage
with
the
certificate
requests,
signing
requests
and
then
so
so
then
you
could
like
kind
of
manage
that
out
of
bands
from
the
the
CLI
based
on
how
you
were
exchanging
these
files.
G
C
Yeah
I
mean
presumably,
if
you're
talking
about
these
Hardware
security
modules,
I
think
I
mean
I,
don't
really
know
how
they
work,
but
I
think
quite
often
they
insist
on
generating
their
own
key.
Don't
they
and
they
don't
ever
give
it
to
you
so
it
you
know,
you'd
have
to
take
you'd
have
to
use
the
one
that
it
you
know
that
it
made
for
you.
C
C
C
You
know,
and
and
and
just
the
idea
of
having
a
separate
signing
key
store
from
your
running
key
store
and
and
tooling
that
can
pull
out
the
right
files.
If
you,
if
you
just
run
through
the
tutorial
for
the
for
the
setting
up
the
security,
you
end
up
copying
your
certificate,
Authority
private
key
onto
the
robot,
and
that's
not
really
something.
We
want
to
encourage.
G
C
D
G
C
Yeah
I
I
just
think
it's
not
it's
not
it.
You
know
it
wasn't
entirely
clear.
If
you
just
follow
the
you
know,
if
you
just
follow
it,
it
just
says:
skip
the
whole
directory
which
works,
but
it's
not
yeah
anyway,
that
that
was
all
really
just
you
know,
I
mean
even
I
mean
the
conclusion.
I
came
to
really.
C
Is
that
if
you
take
it
as
it
stands
right
now,
You
can
generate
a
key
store
with
a
single
Enclave
which
has
full
robot
permission
and
that
and
then
you
treat
that
whole
key
store
as
a
shared
secret
and
just
copy
it
to
all
your
robot
nodes.
Even
that
gives
you
a
significant
security
increase
over
Ross
one
or
unsecured
Ross
2..
You
know,
you've
got
pre-shared
secret
level.
Security.
F
For
me
from
your
experience,
I
I
met,
but
this
is.
This
is
probably
not
a
pre-existing
problem
that
many
other,
like
iot,
vendors
or
even
web-based
ecosystem
is
has
probably
tackled,
like
I.
Think,
there's
Key,
Management,
Frameworks
I
think
trying
to
remember
these
the
most
popular
one,
that's
like
from
key,
I
o
or
whatnot,
but
in
terms
of
doing
all
the
logistics
and
and
transporting
and
managing
certificate
signing
requests
and
having
us
having
a
Consolidated
API
to
do
that
kind
of
middleware
Exchange.
F
C
C
A
F
E
E
Improving
a
bit
on
the
raw
2
documentation,
even
taking
a
look
at
the
tutorial.
Maybe
if
we
can,
you
know,
split
the
the
enclave
and
and
the
key
store
you
know
having
one
for
signing
and
one
for
running,
and
then
you
know
saying
that
you
should
deploy
the
one
from
running.
This
is
still
not
perfect
because
of
what
you
described
right,
that
you
can
still
sign
things
with
a
malicious
note,
but
it's
definitely
better
than
what
we
have
now
so.
E
Not
really
think
any
further
than
that
yeah
exactly
so,
and
that
that's
kind
of
the
point
right
that
we
need
to
encourage
the
use
of
security
because
from
our
experience-
and
we
do
some
consultancy
on
projects
using
those
two
actually.
No.
But
everyone
says
that
they're
very
concerned
with
security
and
nobody
ever
uses
it
so
kind
of
need
to
make
it
very
easy
for
them.
No
way.
E
And
regarding
this
Hardware
secure
module,
feature
proposal,
I
I,
don't
know
how
to
be
honest,
but
the
person
that
opened
the
pull
request
used
to
work
here
and
he
was
the
one
attending
the
security
working
group
meetings.
And
then
we
have
a
had
a
period
where
we
are
not
attending
so
I
actually
don't
know.
F
Today,
sorry,
the
design
docs,
the
last
two
design
docs,
that's
currently
houses
the
equivalent
of
what
would
have
been
the
Reps.
The
Ross
enhancement
was
also
bar
on
the
security
front.
So
there's
the
three
design
docs
on
on
Rusty
design
that
you
can
take
a
look
at
and
then
I
would
propose
Maybe
modifying
that
opening
up
the
pr
and
then
that
way
we
have
like
a
more
concrete
high
level
overview
of
How
It's
expected
to
integrate
with
the
rest
of
the
user
experience
like
are
they?
F
Are
they
controlling
where
the
keys
are
located
the
environment
variables?
Or
is
this
some
extra
command
large?
How
is
this
expected
to
be
found
in
the
rmw
layer
to
like
notify
the
DDS
layer
where,
where
the
keys
are
is
it
is
it?
Is
it
a
file
path
or
to
the
unique
Linux
resource,
or
is
it
like
in
specific
you
ID
I'm,
not
sure
how
this
is.
E
F
G
F
G
G
G
E
A
G
E
F
B
Better
so
yeah
we
sort
of
my
role
is
the
one
I've
mentioned
at
the
beginning,
but
I
just
said
he
probably
missed
it.
We
so
my
role
is
to
sort
of
look
at
the
what
we
call
novel,
robotic
side
of
Robotics,
which
is
anything
to
do
with
robots.
That's
not
traditional
industrial
robots,
so
you
know,
like
a
tradition
like
cooker
robots
that
just
do
like
KRL
or
like
ABB
robots
are
only
used
proprietary
languages.
B
B
So
predominantly
we
are
a
research
center
and
we
are
one
of
our
goals
at
the
moment
is
to
push
Rose
more
towards
industry,
because
you
guys
probably
know
better
than
me
is
used.
A
law
in
Academia
Industries
are
quite
reluctant
and
I
guess
that's
the
reason
why
Boss
2
was
born
to
answer
all
there's
the
issues
of
all
the
problems
the
industry
is
hard
with.
B
B
Link
to
the
website,
we've
got
different
centers
across
the
UK,
we're
both
in
Sheffield,
but
we've
got
a
lot
of
different
subjects
or
we
looked
at
what
we
call
Integrated
manufacturer,
which
is
basically
integration,
control
system,
robotics
security,
IO,
iot
and
factor
of
the
future
sort
of
things.
And
then
we've
got
the
centers.
F
A
Yeah
and
for
the
action
point
so
feel
free
to
add
anything
else
that
we
don't
on
the
agenda
I,
usually
to
prepare
the
meetings,
the
minutes
I
go
by
the
recording
later
on,
but
just
so
to
work
here
together.
If
there's
anything
else,
you
decided
to
take
upon
yourself,
like
I,
saw
Eduardo
added,
improving,
secure
examples,
almost
two
dogs
so.
