►
From YouTube: Bay Area Rust Meetup April 2016
Description
Rust meetup on the subject of operating systems.
Help us caption & translate this video!
http://amara.org/v/2Fhw/
A
Again,
thank
you
once
again,
Mozilla
for
feeding
us
and
giving
us
this
lovely
space
and
then
streaming
our
videos.
It's
wonderful!
Thank
you!
Okay,
so
we
have
Corey
from
all
the
way
from
Australia
who's.
Talking
about
like
using
rust
and
sell
for
in
order
to
have
like
ultra-secure
operating
systems
and
Jethro
is
talking
about
some
of
the
need
of
Intel's
security,
extensions
in
the
actual
CPU
that
can
do
all
sorts
of
things
that
he's
probably
going
to
tell
you
about
that.
I
don't
know,
but
then
the
other
thing
you
know
I
leave
the
community
team.
A
So
if
you
have
any
interest
in
doing
talks
or
like
helping
out
building
the
community,
you
should
follow
one
of
these
links,
it'd
be
lovely
and
also
coming
up.
We
actually
are
starting
to
get
into
a
full
schedule
where
I
actually
have
the
next
meetup
is
in
I.
Think
three
weeks,
two
and
a
half
weeks,
we
have
timely
data
flow,
Frank,
McSherry
who's
been
working
on
this
thing
for
about
a
year
to
is
actually
going
to
be
in
person,
and
then
we
might
have
something
on
early
june
ish
on
like
another
embedded
operating
system.
A
B
B
So
what
is
self
or
straight
from
the
cell
for
faq?
We
have
that
sell
for
is
the
most
advanced
member
of
the
l4
microkernel
family,
notable
for
its
comprehensive,
formal
verification
which
sets
it
apart
from
any
other
operating
system.
So
for
achieves
us
without
amaizing
performance
and
further
in
the
fact
we
have
some
core
concepts
from
what
a
microkernel
is
and
micro
kernel
is
the
minimal
core
of
an
operating
system.
B
This
quote
from
one
of
the
original
l4
papers.
A
concept
is
tolerated
inside
the
microkernel.
Only
if
moving
it
outside
the
colonel
that
is
permitting
competing
implementations
would
prevent
the
implementation
of
the
systems
required
functionality.
It
then
states
that
policy
freedom
is
an
important
characteristic
of
a
well-designed
microkernel
and
that
policy
freedom
is
going
to
pervade
all
the
discussions
about
the
cell
or
API
and
the
crates
built
around
it.
B
Some
of
these
services
are
thread:
control
blocks
for
thread
management,
address
spaces
for
managing
virtual
memory,
endpoints
for
communication
between
threads
by
a
IPC
or
inter
process.
Communication
notifications
for
non
blocking
signaling
between
threads
capability
spaces
for
managing
capabilities
themselves
and
a
sort
of
device
primitives
for
platform.
B
Now
it's
interesting
cell
phone
is
interesting
from
a
row
stations
perspective,
because
it's
a
kernel
that
can
be
trusted.
It's
rather
small
I
think
currently
less
than
twelve
thousand
lines
of
C
code,
and
they
have
they
have
formal
verification
of
what's
called
functional
correctness
and
a
few
security
properties.
B
Now
this
is
a
source
level,
proof
on
actual
C
code
and
not
a
handmade
abstraction
and
what
they're
proof
says
in
there
mechanized
theorem
provers
it's
a
bell.
They
have
a
specification
of
what
a
colonel,
so
foreign
does,
and
they
show
that,
according
to
their
interpretation
of
a
c
language,
that
the
kernel
as
written,
only
exhibits
behaviors
that
the
specification
explicitly
allows-
and
this
proof
extends
down
to
the
final
binary.
The
compiler
is
not
trusted
to
have
correct
output
that
is
checked
and
the
semantics
don't
need
to
agree
between
the
compiler
and
the
proof.
B
B
The
ultimate
goal
for
using
sell
foreign
rust
is
to
have
a
carbon
subcommand,
rbg
run
RBG
being
short
for
robo
gaya
the
whole
umbrella
project,
and
this
will
build
the
kernel
set
up
a
cross,
compiling
tool
train.
If
you
need
one
and
launch
the
app
in
a
virtual
machine,
now
we're
not
quite
there
yet
there's
a
lot
of
work
that
needs
to
be
done
along
the
way,
but
there's
a
really
good
chance
that
it
will
be
easier
to
build
and
run
rust
applications
and
so
forth
and
for
any
other
non-native
operating
system.
B
Now
the
current
story
is
using
the
raw
so
for
API,
with
no
stood
crates
and
there's
a
cell
for
crate,
which
abstracts
these
raw
system
calls
into
a
friendlier
API.
So
let's
take
a
look
at
some
desus.
Some
of
these
ap
is
the
first
and
arguably
one
of
the
most
important
objects
is
the
endpoint
object
and
an
endpoint
is
one
half
of
a
IPC
channel.
B
B
You
can
also
send
a
single
capability
across
an
endpoint
transferring
your
authority
to
service
to
another
threat,
and
you
can
also
receive
a
message
from
an
endpoint
now
sending
and
receiving
our
blocking
operations,
and,
in
particular
the
primitive
they
implement
is
called
a
rendezvous.
What
this
means
is
that
no
data
will
be
transferred
or
queued
until
both
a
sender
and
a
receiver
are
waiting
on
the
same
end
point
at
which
point
data
is
exchanged.
B
Now
this
received
token
that
received
returns
keeps
track
of
some
metadata
about
the
message
that
was
received,
as
well
as
a
handle
to
the
data
that
was
actually
transferred
if
data
was
transferred
and
not
just
a
capability.
This
data,
this
message
is
temporarily
stored
in
a
threadlocal
IPC
buffer
that
the
colonel
knows
about,
and
the
receive
token
does
not
have
a
copy
of
that
data,
because
that
data
it
can
in
general,
be
quite
large
and
copying
it
on
every
message
when
most
messages
are
generally
short,
would
not
be
efficient.
B
Additionally,
we
have
try
receive
which
will
not
block.
However,
there's
little
indication
if
a
message
was
actually
received
and
in
particular,
as
we'll
see
later,
capabilities
have
what's
called
a
badge
and
the
only
indication
that
a
message
was
not
actually
received
is
that
the
badge
will
be
zero,
which
can
happen
in
normal
operation
as
well.
If
your
system
is
poorly
designed.
B
These
final
two
methods
are
the
meat
underlying
the
send
methods
in
full
generality,
sending
a
message
on
South
or
transfers,
both
data
and
capabilities
at
the
same
time,
and
it
can
technically
transfer
multiple
capabilities
now.
I
say
technically,
because
only
one
unique
new
capability
can
be
transferred.
However,
you
can
transfer
multiple
capabilities
if
the
set
the
thread
you
are
sending
the
capability
to
already
has
a
copy
of
that
capability.
B
B
The
next
object
will
examine.
Is
the
notification
object
and
a
notification
is
an
array
of
one
bit
semaphores
packed
into
a
single
word,
and
there
are
two
basic
operations
signal
and
weight
and
the
bits
in
the
array
that
will
be
notified.
When
you
call
signal
are
indicated
by
the
badge
on
the
underlying
capability.
B
There's
no
indication
of
whether
a
signal
was
received
were
acknowledged
in
any
way.
It's
completely
asynchronous.
On
the
other
side
of
the
notification,
we
can
wait
for
a
signal
to
be
signaled,
and
this
will
block
until
some
other
thread.
Notifies
notification
object
and
it
will
return
the
notification
word.
B
B
You
can
buy
nor
unbind
a
notification
and
binding
a
notification
is
sort
of
like
a
UNIX
signal
in
that
it
is
an
asynchronous
mechanism
for
interrupting
a
thread
regardless
of
what
it
was
doing.
For
example,
if
a
thread
is
currently
blocked
receiving
on
an
endpoint
and
another
thread
signals
the
notification
that
it
bound.
B
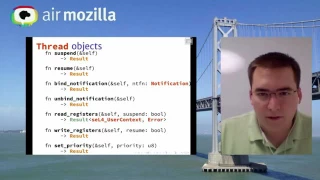
The
next
two
methods
are
read:
registers
and
write
registers
made
registers
is
largely
useful
for
debugging
and
bright
registers
is
missing.
An
argument
should
have
a
user
context
as
an
argument,
but
right
registers
is
vital,
because
when
you
create
a
new
thread,
it
has
no
initial
register
state.
So
you
need
to
set
its
stack
pointer
to
a
stack
you
allocate
for
it,
as
well
as
the
instruction
pointer
to
an
executable
that
you
load
for
it.
Threads
also
have
a
priority
and
so
forth.
B
Scheduler
right
now
is
a
brown
brow
round
robin
in
each
priority
level
and
there's
255
priority
loads,
where
255
is
the
highest
priority
and
0
is
the
lowest
now.
Capabilities
are
references
to
Colonel
objects
with
a
badge
and
specific
rights
and
depending
on
the
object
type,
this
badge
and
rights
could
be
interpreted
in
different
ways.
B
Capability
spaces
are
somewhat
analogous
to
traditional
Hardware
page
tables
used
for
virtual
memory.
If
you're
not
familiar
with
how
virtual
memory
look
up
works,
a
pointer
interpret
as
a
virtual
address
is
broken
into
a
number
of
chunks
and
each
of
these
chunks
is
interpreted
as
an
index
into
a
table.
For
example,
in
this
case
we
have
three
chunks.
B
The
first
two
are
10
bits
and
the
last
is
12
bits
and
a
two-level
paging
structure,
so
the
first
level
page
table
all
the
way
on
the
Left
takes
the
first
10
bits
of
the
pointer
and
looks
up
into
this
table
to
see
if
there
is
another
level
of
page
paging
structure
or
if
there's
no
address
mapped
there
at
all.
If
there's
no
address
mapped
our
no
page
table
mapped,
then
the
hardware
will
signal
a
fault
and
that
will
bubble
up
in
an
a
unix
system
as
a
segmentation
fault
signal.
B
If
there
is
a
page
table
map
there,
the
next
10
bits
will
be
examined
and
used
as
an
index
into
that
further
table
and
then
that
table
entry
can
either
point
with
a
physical
address
to
physical
memory,
or
it
could
be
on
mapped
segmentation
fault
again,
and
the
last
12
bits
of
the
pointer
pointer
here
being
32
bits
is
used
as
a
bite
index
into
that
final
4
kilobyte
page
capability
lookup
is
a
generalized
software.
Implementation
of
the
same
basic
concept
and
capability
spaces,
and
so
for
are
what's
called
guarded.
B
Page
tables
so
takes
the
basic
idea
of
these
painting
tables
and
add:
what's
called
a
guard.
So
in
this
example,
the
address
is
still
broken
up
into
three
portions.
The
first
portion
is
14
bits
with
an
8-bit
guard
value
and
the
remainder
6
bits
are
called
the
racks.
Now
each
thread
has
associated
with
it.
A
single
see
note
or
capability
node
capability
nodes
are
the
tables
in
a
capability
space
that
correspond
to
a
page
table
they're
an
array
of
capabilities,
and
that
capability
could
either
be
a
concrete
kernel.
B
So
when
looking
up
a
capability
pointer
for
a
friend,
the
first
Chomp
notes,
the
rootsy
node
is
looked
at
to
determine
how
many
guard
bits
and
how
many
radix
bits
of
pads
the
first
g
guard
bits
are
stripped
from
the
address
and
compared
against
the
guard
value
stored
Massino.
If
it
does
not
match
a
capability,
fault
is
signaled.
If
it
does
match,
the
radix
is
used
as
the
index
into
the
sea
node,
which
is
then
used
to
recursively,
continue,
lookup
or
as
the
final
capability.
B
If
it's
the
last
level
of
the
address
or
there's
already
a
concrete
capability
on
the
table
now
this
is
a
rather
simple
see
space
depicted
here.
They
can
actually
be
recursive
and
have
point-like
capabilities
into
themselves.
All
sorts
of
crazy
nonsense
that
typically
isn't
too
useful
and
is
mind-bending
to
try
and
understand.
B
Now,
to
create
a
capability,
you
must
have
an
object
in
the
kernel
that
your
that
the
capability
refers
to.
However,
self
for
itself
does
no
dynamic
allocation
for
this.
Inside
of
the
kernel
user,
space
is
responsible
for
providing
memory
for
new
objects
via
untyped
memory
objects
and
untyped
memory.
B
Objects
are
like
a
kernel,
managed
arena
and,
in
the
sense
that
a
memory
allocator
is
an
arena
in
that
you
can
allocate
objects
sequentially,
and
then
you
can
flush
the
entire
thing
and
reuse
the
memory
the
operation
on
these
is
called
retype
and
retype
takes
a
capability
to
an
untagged
memory,
object,
an
object,
type
that
it
will
create
and
a
window
into
a
C
note
that
it
will
store
the
new
capabilities.
In
now.
B
It's
important
to
note
that
this
untyped
memory
isn't
something
that
user
space
can
actually
look
at
the
contents
of
the
only
way
that
user
space
can
refer
to
this
memory
is
via
a
capability,
and
this
is
important
for
isolating
the
colonel
from
user
space.
In
order
to
actually
inspect
memory
derived
from
a
nun
type
memory
object,
you
need
to
create
a
page
object
and
map
it
into
a
virtual
address
space
and
in
a
sit
in
the
same
way.
C.
Nodes
cannot
be
inspected
by
user
space.
B
Now,
the
so
far
out
crate
handles
all
of
the
details
of
virtual
address
spaces
and
capability
spaces,
for
it's
not
quite
fully
baked,
and
it
can
be
used
stand
alone
in
a
raw,
what's
called
a
root
server,
which
is
the
initial
thread
that
the
cell
for
Colonel
spawns
and
gives
all
resources
to,
but
it
really
wants
integration
with
process
management
in
particular.
Creating
a
new
stack
of
allocators
from
very
little
resources
is
very
finicky
now.
B
Servers
and
components
written
in
rust
in
the
first
few
iterations
actual
operating
system
interaction
will
be
very
limited,
but
it
should
be
functional
in
particular
file
systems
and
networking.
Well,
it
might
only
be
back
I,
say
a
read-only
tar
archive
and
there
might
not
actually
be
any
Nick's
connected.
The
api's
should
work.
B
Our
current
status
is
that
we're
working
on
building
a
foundation
for
future
applications
and
rust
applications
using
the
standard
library
is
only
the
start
of
it.
There's
lots
of
low-level
fiddling
at
the
moment
and
to
get
any
useful
devices.
We
need
a
driver
framework
in
place,
so
the
whole
thing
didn't
evolve
to
spaghetti
immediately.
Our
long-term
goal
is
to
create
a
POSIX
compatible
application
server
that
uses
system
call
translation
to
host
unmodified
Linux
binaries
inside
the
cell
phone
colonel,
in
the
same
sense
that
you
can
run
unmodified
linux,
binaries
in
freebsd
and
now
in
windows.
B
It's
all
pretty
well
specified
these
days
and
NFS.
Before
has
few
of
pitfalls
than
older
versions,
and
it
would
be
very
interesting
to
see
a
purist
implementation
of
that
another
thing
would
be
crypto
protocols
and,
for
example,
TLS
or
SSH.
It
doesn't
have
to
be
pure
rust,
NEC
code,
as
long
as
it
can
be
compiled
free-standing
or
with
a
very
minimal
lipsy
in
place,
is
fine
to
use.
B
This
would
include
certain
configurations
of
openssl,
but
not
all
another
project
that
would
be
interesting
not
only
to
us
but
to
any
application
running
will
be
a
hard
of
mount
with
sort
of
mitigating
heat
exploitation,
and
we
have
an
issue
open
for
this
in
our
meta
repository
issue,
number
11
and
the
current
idea
is
to
build
on
the
die
harder
design.
Emery
Berger
has
the
core
of
that
allocator.
B
The
ideas
has
have
my
understandings
that
it
was
either
stolen
from
opus,
openbsd
or
openbsd
stole
from
them,
and
it
also
made
its
way
into
windows.
7,
somehow
I
don't
really
understand
the
whole
family
tree
there,
and
ideally
that
Malik
would
be
useful
for
other
purist
applications
where
wouldn't
necessarily
be
as
fast
as
Gmail.
So
it
would
be
more
robust
to
certain
kinds
of
errors
in
untrusted
C
code
that
the
rust
is
calling
into.
B
Of
course,
device
drivers
need
to
be
written
if
you're
interested
in
device
drivers
I'm
sorry
they
can
be
fun.
You
should
talk
to
me
first,
so
we
can
coordinate
a
little
bit
on
what
the
interface
it
needs
from
the
rest
of
rebellion
and
what
it
will
expose
a
device
tree
parson
would
be
interesting
and
device.
Trees
are
the
structures
that
these
days
largely
arm
platforms
exposed
from
firmware,
so
the
operating
system
can
understand
what
hardware
it's
running
on,
but
it's
also
used
in
ibm's,
Power,
Architecture
and
maybe
some
other
stuff
and
of
course
anything
else.
B
That's
cool
and
and
rust
is
really
really
awesome,
with
the
goal
being
that
the
more
things
are
written
in
rust,
the
ideally
the
safe
for
the
world
would
be
if
we
actually
use
that
software.
If
you
want
to
keep
in
touch,
we
have
a
website
or
Bengali.
Org
is
a
mailing
list.
It's
vaguely
active
with
occasional
updates
from
me
and
sporadic
discussion.
There's
a
IRC
channel,
pound,
robogoalie
and
free
know.
That
is
much
more
active
and
before
I
ask
four
questions.
B
I
would
like
to
mention
that
running
rust
and
sell
for
is
not
just
a
pure
rust
affair.
There
is
currently
work
on
going
inside
of
data
61
to
get
rust
interoperating
with
the
already
existing,
see,
libraries,
and
this
actually
is
pretty
far
gone
and
that
it
works
pretty
well
using
a
fine
gin
cheddar,
which
is
a
sea
header
generator
for
lust
declarations,
but
for
some
reason
or
another
the
repository
hasn't
pushed
out
yet
also
in
an
email
list.
When
that
eventually
does
happen,
and
with
that
any
questions
from
the
audience.
A
C
B
Phd
and
the
way
this
works
is
that
it
d
compiles
the
binary
and
extracts
the
behavior
of
the
instructions
using
a
project
out
of
I,
believe
Cambridge,
and
it
feeds
descriptions
of
what
those
instructions
do
into
an
smt
solver
and
there's
some
quite
complicated
infrastructure
to
show
correspondence
between
statements
in
the
C
code
and
actual
behavior
of
the
assembly,
as
well
as
a
mapping
between
their
control
flow
graphs
and
I.
Believe
the
most
recent
status
is
that
it
works
at
GCC
01
and
is
almost
working
at
GCC
02.
B
B
Rebuilding
that
even
just
mostly
informally
on
any
rust
system
would
take
decades
of
effort
and
millions
of
dollars
just
because
she
has
a
long-running
and
fairly
robust.
These
days.
Verification
verification
infrastructure,
whereas
rust
right
now,
has
none
and
it's
also
a
much
more
complicated
language.
E
F
E
B
G
B
So
that
is
an
option
and
early
on.
I
considered
it
to
me
it's
not
as
interesting,
because
it's
not
all
that
much
effort
once
the
basic
infrastructure
is
in
place
to
slowly
piece
in
everything
that
the
standard
library
needs
and
the
reach
of
the
software
that
will
be
able
to
benefit
from
that
is
far
greater
than
if
it
were
just
targeting
LRS
or
a
minimal
standard
library.
G
A
counterpoint
for
why
you
might
want
that
so
I
think,
like
the
typical
use
cases
of
sulphur
or,
like
you're,
running
it
co-tenant
with
another
operating
system,
right
you're,
trying
to
implement
like
a
secure
Enclave.
So
where
you
have
something
like
a
Linux
ring,
Android,
potentially
on
one
side
right
and
then
you
want
to
you
solve
for,
for,
like
crypto
secure
operations
and
your
kind
of
raised
on
Diaw
tray.
There
is
like
minimizing
code
surface
there
you're
going
to
attack
service
rate
right.
B
So
this
two
different
there's
two
different
use
cases
in
mind.
There's
that
and
the
most
sane
architecture
in
that
case
would
have
cell
for
being
the
separation
kernel
or
running
in
the
secure
world
of
a
trust
own
platform,
for
example,
and
it
would
be
the
VMM
running
the
Linux
machine
like
there
smacking
program,
which
is
a
DARPA
funded,
secure.
Mathematically
assured
cyber
control
systems
is.
F
B
B
So
you
can
show
that
you're
whole
system
as
a
whole
has
certain
information
flow
and
security
properties.
Given
a
cam
keys,
description
and
I
network
is
not
fully
complete
yet,
but
portions
of
it
have
been
published
a
thing
to
look
forward.
Big
cap.
Do
the
capability
description
language,
so
there
could
be
an
argument
for
building
that
sort
of
software
and
rust.
But
to
me,
I
think
that
the
immediate,
immediate
use
cases
are
not
quite
as
favorable
for
rust
compared
to
see.
H
Worried
too
hello,
so
I
just
heard
the
word
microkernel
for
the
first
time
this
evening
and
I'm
wondering
what
this
is.
If
you
could
explain
it
to
me
in
a
way,
that's
familiar
so
I
know
what
up
I
know
what
my
my
operating
system
is
on.
My
computer
or
I've
used
a
bun
bun
two
before
what
is
what
is
a
microkernel
in
relationship
to
that
sure.
B
So
a
microkernel
takes
the
very
essence
of.
What's
inside
Linux
has
a
scheduler,
it
can
schedule
kernel
threads
as
well
as
user
threads.
It
has
an
abstraction
for
managing
memory,
so
in
the
kernel
you
can
allocate
memory
and
do
page
table
management.
You
can
also
do
it
from
users
face
with
the
M
babb
system
call
which
Malik
eventually
boils
down
to
and
inside
of
the
Linux
kernel.
Also
there's
abstractions
for
dealing
with
devices
and
device
drivers.
B
Now
the
microkernel
approach
takes
out
the
very
core
essence
of
what
is
needed
to
make
a
whole
operating
system
work
and
extracts
it
into
an
individual
small
component
and
the
benefit
for
sell
for
and
the
sort
of
systems.
It's
designed
for
originally
it's
that
it's
much
more
small
and
formally
analyzing
it
and
doing
proofs
about
it
becomes
feasible
when
it
it
becomes
that
small,
alright
I'll
forward,
even
just
two
or
three
times
bigger
its
formal
analysis,
would
be
almost
infeasible.
H
B
The
kernel
itself
doesn't
provide
a
file
system,
but
if
you're
going
to
build
an
operating
system
on
top
of
it-
and
you
want
a
file
system
you're
going
to
have
to
provide
one-
it's
oh
icic,
okay,
right
so
it'd,
be
a
user
space
process
running
somehow
and
you
communicate
it
over
to
it
using
either
end
points
or
shared
memory
of
some
kind,
and
you
communicate
that
way.
So,
instead
of
talking
directly
to
the
colonel,
like
you
would
in
Linux,
for
example,
with
the
open
syscall,
you
would
use
the
colonel
to
communicate
to
another
component.
I
I
I
I'm,
a
PhD
candidate
at
UC,
Berkeley
I
studied
computer
security,
mostly
in
a
past
year
or
two
have
been
focusing
on
trustworthy
cloud
computing
talk
to
you
about
what
that
means
that
in
the
next
slide,
I've
also
done
research
on
network
security,
mobile
phone
security
and
large-scale
internet
measurement
I'll
be
graduating
in
a
couple
months
and
it
will
not
be
staying
in
academia,
so
I'm
looking
for
some
new
opportunities.
After
that,
all
right,
so
trustworthy
cloud
computing
is
being
able
to
outsource.
I
Your
computational
needs
to
the
cloud
while
maintaining
the
privacy
and
integrity
of
both
the
computation
and
the
data.
So
you
know
when
you
currently
set
up
some
storage
on
s3
or
run
some
vm
on
ec2.
There
are
someone
at
amazon
who
is
able
to
like
break
into
your
system
and
modify
it.
Of
course,
they
have
a
strong
economic
incentive
not
to
do
that,
but
there's
nothing
that
prevents
like
a
rogue
employee
or
someone
who's
being
pressured
to
like
do
those
kinds
of
things.
I
So
the
goal
of
the
trustworthy
cloud
computing
research
is
to
prevent
that
kind
of
access
all
right,
so
one
of
the
key
component
is,
I
think,
is
very
useful
in
providing
this
is
a
secure,
Enclave
and
I
know
a
lot
of
people
use
different
definitions
for
what
a
secure
Enclave
is
so
I'll
tell
you
exactly
what
I
mean
by
secure
Enclave
so
that
we're
all
on
the
same
page,
secure
Enclave,
and
it
provides
three
very
important
security
properties.
The
first
is
fully
isolated
execution.
I
The
second
is
remote
at
the
station
and
the
third
is
sealing
and
I
will
go
over
each
of
these
three
to
explain
in
detail
what
they
mean.
So
if
you
look
at
the
traditional
you
know
operating
system,
privilege
separation,
you
might
have
like
a
vm
hypervisor,
which
is
like
all
powerful
in
the
whole
system.
It
will
might
be
able
to
run
multiple
operating
systems
concurrently
and
it
was
operating.
System
are
isolated
from
the
shutter,
but
the
vm
I
improvise
are
still
maintains
control
over
the
whole
system.
I
All
devices
all
memory,
similarly
for
operating
system
kernel,
might
in
a
similar
way
run
multiple
user
processes.
The
user
processes
are
isolated,
but
the
colonel
still
has
full
control
over
all
the
individual
processes.
So
really
the
normal
privilege
model
that
you
know
you
think
about.
Is
this
hierarchy,
but
with
secure
on
clays
it's
no
longer
a
hierarchy.
You
actually
have
like
distinct
sets
of
privileges,
so
one
way
you
could
implement
is
is
by
having
like
a
separate
enclave
mode
that
is
kind
of
like
similar
to
user
mode,
except
that
it
yeah.
I
Alright,
the
second
thing
is
remote
at
the
station
and
which
is
being
able
to
prove
to
other
people
what
programs
you're
running.
You
know
in
a
current
setting
your
type,
some
command
in
your
command
line,
to
run
it
on
your
server,
and
you
know,
hopefully
it's
running
the
way
it's
supposed
to
be.
You
had
stole
that
binary.
We
are
there
before.
I
So
it's
probably
ok,
but
you
know
really,
there's
there's
no
guarantee
here,
you
know
about
binary
could
have
been
modified
on
disk
or
you
know
it
could
have
been
modified
by
the
vm
hypervisor
as
it
has
been
loaded
into
memory.
So
with
remote
at
the
station,
you
give
some
kind
of
proof
that
you
are
in
fact
running
the
same
program
that
you
know
you
meant
to
run
generally.
I
This
is
done
using
cryptography,
for
example,
by
taking
a
hash
of
the
program
binary
as
it
is
being
loaded
into
memory
and
at
hashes
then
signed
by
some
hardware.
Specific
key-
and
you
know
the
proof
or
the
guarantee
here-
is
that
you
know
the
hardware
that
you
have
to
trust
a
hardware
vendor
to
you
know,
implement
this
correctly
and
so
a
little
trusted
computing
jargon
this.
This
hash
of
the
program
is
generally
called
the
identity
or
the
measurement
of
the
program.
I
I
Alright
cool,
then
no
questions
and
we'll
move
on
to
the
next
part.
Intel
SGX
is
a
recent
instruction
set
extension
that
Intel
implemented
in
its
skylake
processors
released
last
September
that,
basically,
you
know,
implements
a
secure
Enclave.
It
is
a
secure
of
life,
implementation
for
the
x86
instruction
set,
and
they
do
this
by
providing
some
separate
piece
of
encrypted
memory
that
you
can
run
your
uncle
is
in,
and
this
will
be
isolated
from
the
operating
system
using
cpu
Harper
mechanisms
all
right
so
far
so
good.
I
I
The
second
thing
is
that
the
remote
attestation
capability
in
sgx
requires
you
to
talk
to
Intel,
directly
or
a
proxy
for
Intel
to
verify
an
attestation.
So
every
time
you
want
to
do
this
remote
Association
protocol,
you
need
to
talk
to
Intel,
which
has
both
privacy
and
availability
concerns
all
right.
The
third
problem
with
SJ
x
is
that
the
official
SDK
is
only
available
for
c
and
c++,
and
I
think
this
is
really
a
missed.
I
Opportu
d
for
Intel
I
feel
like
I'm
preaching
is
required
here
when
I
have
to
say
when
I
say
you
know,
this
is
a
great
would
be
a
great
opportunity
to
use
rust,
and
this
is
because
there
is
no
lipsy
in
sgx
right.
So
none
of
your
legacy
code
is
going
to
work
anyway.
So
really
in
my
like
in
my
mind,
there's
no
reason
to
you
see
it
all
here,
because
you'll
have
to
write
everything
from
scratch
to
begin
with
all
right
now
there
are
several
enclaves
that
Intel
provides
that
are
required
to.
I
You
know,
run
any
anything
in
sgx.
It
has
to
do
with
the
drm.
This
has
to
do
with
the
attestation
and
these
two
enclaves.
We,
of
course
don't
know
what
your
written
in,
but
it
seems
very
plausible
to
me
that
they
are
written
using
the
same
SDK
daddy,
make
available
to
everyone
else,
so
they're,
probably
written
in
C
or
C++.
These
two
binaries
together
are
about
one
megabyte,
big
and
the
whole
security
of
this
age.
I
J
I
Right
then,
the
last
problem
is
that
into
SJ
x,
don't
actually
provide
any
protection
against
side-channel
attacks,
and
you
know
you
just
have
to
keep
this
in
mind
when
writing
sgx
software,
and
I
hope
they
had
it
in
mind
when
writing
there
at
the
station,
like
I'm,
clays
and
everything,
because
there's
a
lot
of
crypto
involved
in
there
and
we,
you
know
if
the
private
key
used
for
the
attestation
leaks
out,
then
again,
the
whole
security
of
sgx
falls
apart.
Okay,
so
well
after.
I
First
of
tools.
I
roads
are
to
work
with
the
xjx
stream
format,
which
is
the
lowest
level,
which
is
a
low
level
format
very
similar
to
which
represents
enclaves
in
a
way,
that's
very
similar
to
the
way
they
are
actually
loaded
into
memory
using
the
sgx
instruction
set.
So
the
tools
here
you
can
kind
of
compare
them
to
object
and
read
health.
Just
for
inspecting.
You
know.
Unclip
wineries
and
the
other
thing
I've
been.
I
The
only
software
for
sjax
is
kind
of
like
building
your
own
operating
system
kernel.
Many
things
that
you've
come
to
expect
from
like
a
regular
up
user
binary
environment,
don't
really
exist
in
SG
x,
there's
no
dynamic
linking
there
are
no
system,
calls,
there's
no
and
no
kind
of
input
output.
The
only
thing
you
can
do
is
a
share
memory
with
user
space.
I
So,
let's
take
a
look
at
how
switching
from
user
mode
to
arclight
mode
actually
works
in
lib
enclave.
So
you
have
some
some
program
it's
running
and
you
call
this
entry
function,
which
then
will
call
the
e
enter
instruction,
which
is
a
special
sgx
instruction,
will
go
into
Enclave
mode
and
besides
go
into
on
cliff
mode.
It
will
also
reset
the
instruction
pointer
to
a
previously
defined
point
within
a
previously
loaded
Enclave.
I
So
this
is
designed
to
not
let
user
mode
jump
into
like
some
arbitrary
code
somewhere
in
the
middle
of
an
enclave
but
other
than
that.
Nothing
has
really
changed
about
the
processor.
So
you
have
to
manually
save
all
the
registers.
You
have
to
switch
the
stack
because,
of
course
you
don't
want
to
put
your
sensitive
function,
arguments
on
the
user
stack
and
then
once
the
stack
is
switched.
I
So,
but
basically
everything
between
here
this
call
here-
and
this
call
here-
that's
all
written
in
assembly,
unfortunately,
but
there's
not
really
another
way
to
do
it.
Alright,
once
that
returns,
you
know
the
user
state
and
stack
is
restored.
You
call
the
e
exit
instruction,
which
activates
Enclave
modes,
the
enter
instruction
returns
and
a
user
program
can
continue
with
whatever
it
was
doing
before.
I
So
this
basically
shows
you
how
the
switch
from
user
mode
to
unclick
mode
works,
but
you
might
also
want
to
call
the
other
way
from
Enclave
mode
to
user
mode.
So
that's
also
supported
through
what
I
call
user
call.
When
you
do
a
user
call,
you
must
save
the
Enclave
state
so
that
nothing
leaks
into
the
user
space,
no
sensitive
information.
You
restore
the
user
state.
That
was
as
the
way
it
was
when
the
Enclave
originally
got
called
as
well
as
stack,
and
then
you
call
the
exit
instruction.
I
So
at
this
point
the
users
stack
and
state
just
look
looks
just
like
before
the
ENT
instruction
was
executed,
so
yeah
there's
nothing
weird
with
the
stacking
you
can
just
do
like
regular
program.
Calls
at
this
point
and
the
regular
program
called
we're
doing
is
calling
the
user
call
handler,
which
was
passed
in
as
a
closure
to
the
enter
instruction
earlier.
I
I
So
when
writing
a
secure
line
class
is
very
important
that
you
not
leak
any
like
secret
information
to
user
mode,
and
you
know
when
using
safe
rust
is
actually
very
easy,
because
any
memory
allocated
using
safe
for
us
will
either
be
on
the
stack
or
it
will
be
on
separate
enclave
heap,
which
is
in
protected
memory.
So
nothing
can
really
go
wrong
there
and
then
implemented
a
special
user
heap
abstraction
that
you
can
use
to
communicate
information
across
during
a
user
call.
I
So
there's
this
user
box
typing
user
slice
type,
which
will
be
able
to
read
and
write
from
user
memory,
and
but
you
cannot
directly
access
the
data
inside
these
types.
Everything
has
to
go
through
unsafe,
abstractions
using
pointer,
resour
unsafe,
sell
because
of
course,
this
memory
is
existing
user
space.
You
could
easily
be
modified
by
someone
outside
our
trust
zone
so,
and
you
cannot
consider
it
being
like
having
no
alias
or
anything
like
that.
I
Alright,
so
that's
it
for
the
implementation
of
the
lip
Enclave.
Next
we're
going
to
look
at
how
you
build
an
enclave
and
actually
get
to
run
so,
let's
slow
complicate
it.
So
you
take
the
place
or
which
is
written
in
rust
as
well
as
live
Enclave,
which
is
also
written
reversed.
You
send
it
to
the
rust
compiler
and
then
you
get
the
static
library
out
so
the
static
libraries
not
yet
linked.
I
Then
you
have
to
compile
the
entry
functions
which
are
written
in
assembly
and
link
those
together.
At
that
point,
you
will
get
a
dynamic
library,
so
at
this
point
it's
very
important
to
check
whether
your
dynamic
library-
actually
you
can
doesn't
contain
any
code.
It's
not
going
to
work
in
rust,
and
this
is
what
the
oh
sorry,
no
I
meant
sgx
nut
thrusts.
So
it's
important
that
you
check
that
the
dynamic
library
does
not
contain
any
code.
That's
not
going
to
run
in
SG
x,
so
the
helps
to
sgx
comfort,
sgx
s.
I
Converter
will
check
that.
Then
you
get
this
SGS
X
file,
you
can
sign
it
and
then
you
use
the
signature
and
the
gsx
in
the
two
loader
and
run
alright,
so
the
elf
to
SGS,
X
converter,
you
know,
checks
with
a
bunch
of
things.
I
also
put
the
linker
options
here.
Anyone
is
interested
in
if
you
leave
any
of
these
out,
it's
probably
not
going
to
run
in
sgx,
but
so
you
have
to
use
the
gold
linker,
not
standard,
LD
linker,
because
that
won't
work.
I
I
The
reason
is
that
relocation
represents
a
change
in
memory
from
what
is
like
the
binary
on
disk
and
what
is
the
program
that's
going
to
be
executed,
but
this
change
kind
of
happens
before
the
program
starts.
So
if
you
would
change
your
binary
this
way,
the
measurement
of
the
binary
changes
and
now
all
your
ceiling
or
your
your
remote
as
a
station,
doesn't
work
anymore,
because
the
hash
should
actually
changed
so
most
relocations,
don't
work
and
the
relocations
that
do
work
need
to
be
done.
The
first
time
the
user
mode
calls
into
the
outlet
mode.
I
Also,
you
know
many,
you
know
standard
features,
you
would
think
of
don't
work
in
sgx
such
as
initialization
functions,
finalization
functions,
global,
also
table
procedural
linkage
table
those
kind
of
things,
and
also
some
memory
atlases
need
to
be
replaced
in
the
conversion
from
health
to
SJ
excess.
So
there
you
know
you
need
to
check
that
those
dynamic
symbols
are
set
up
correctly,
all
right
so
I
guess
at
this
point.
I
can
do
a
little
demo
of
how
this
all
works.
I
F
I
So
things
that
I
wish
were
no
standard
because
you
didn't
think
you
could
use
a
standard
library
in
sgx
right,
so
the
I/o
traits
are
very
useful,
abstractions
and
I
wish.
They
were
just
supported
in
no
standard,
because
you
know
we
might
be
able
to
build
some
kind
of
rewrite
abstraction
using
user
calls.
I
But
you
know
you
want
two
traits
to
be
available
same
holds
for
a
hashmap
and
hash,
yet
they
currently
not
support
it
because
it
append
on
a
rant
grade
and
the
rant
grade
is
not
supported
in
no
standard,
but
in
sgx
there's
an
instruction
you
can
call
for
randomness.
So
there's
no
reason
that
this
would
not
be
supported
things
that
I
wish
were
stable.
I
Inline
assembly
I
use
a
lot,
there's
a
lot
of
no
standard
stuff
that
is
exported
in
standards,
but
when
you
use
it
without
standards,
not
actually
stable,
see
unions.
Those
are
useful
for
talking
to
the
kernel.
Driver
and
I
would
also
like
to
prevent
moving
things
out
of
a
type
without
changing
the
memory
layout,
which
is
kind
of
finicky
right
now.
But
I
hear
that
this
should
be
fixed
in
the
future.
All
right
so
the
whole
chain
from
yet
this
was
going
to
be
demoed.
I
Well,
the
whole
chain
from
rusty
to
help
to
SG
excess
is
I
built
into
a
cargo
subcommand
called
cargo
build
Enclave,
so
you
don't
have
to
manually
run
all
this,
but
that
subcommand
is
currently
a
little
hairy.
I
guess
and
some
things
in
cargo
could
be
improved
to
make
it
less
hairy.
So
I'd
like
to
be
able
to
build
different
features
when
using
building
for
test
or
building
for
packaging
and
because
those
tests
or
the
package
will
not
be
on
in
SG
x.
I
K
I
K
I
D
I
J
I
Library,
so
the
instructions
that
are
used
to
set
up
enclaves
before
they're
being
run
are
running
kernel
mode.
So
you
need
a
special
kernel
driver.
The
windows
10
comes
with
its
own
built-in
API
to
load
on
clays
for
linux,
I've
written
kernel
driver
that
is
not
production
ready,
but
you
can
use
it
sits
on
my
github
in
this
repository
I
know:
intel
has
their
own
linux
driver
that
hopefully
they're
going
to
release
in
a
couple
months.
I,
don't
think,
there's
a
Mac
driver
yet.
J
I
J
L
I
Yeah
so
there's
a
special
Enclave
called
a
launch
Enclave
that
is
distributed
by
Intel,
and
that's
it
only
uncle
agent.
You
can
run
on
your
processor
without
any
extra
crypto
checks
that
need
to
be
verified.
Ish,
longish
Enclave
has
a
built-in
policy
that
can
basically
authorized
utter,
am
close
to
be
run
and
one
of
the
policies
is
any
Enclave
can
run
in
debug
mode.
Any
uncle,
if
you
want,
can
run
a
debug
mode
so
but.
I
G
I
F
G
It
seems
like
there's
this
really
good
use
ace
for
this
sort
of
technology,
which
is
incompatible
with
the
idea
like
epid,
which
would
be
individual
CPUs.
Have
a
public
key
in
cap
up
lik
encryption
key
such
that,
if
you're
trying
to
use
something
like
host
provisioning
right
and
you're
trying
to
inject
the
root
secret
by
which
you
drive
all
your
other
secrets
to
provision
a
host
into
this
head
straight,
like
you
could
encrypt
that
master
secret
to
a
cpu
specific
key.
Does
astri
X?
Let
you
do
anything
like
that
today
or
does
epid
you.
G
I
So
I
think
you
can
do
this
right,
because
you
can,
you
would
be
able
to
generate
a
private
public/private
key
pair
inside
and
sjax
Enclave
and
then
store
that
private
key
using
the
ceiling
mechanism
and
then
the
only
way
to
unseal
it
is
you
know
again
by
running
that
same
Enclave,
so
it
is
unclear,
could
then
perform
the
operation.
You
want
it
cool
all
right,
all
right,
yeah,
there's
another
question
up
front
here:
I.
I
I
I
I
I
So
I
want
to
talk
to
you
a
little
bit
about
this
difference
between
running
like
something
on
your
own
hardware
and
running
it
in
the
cloud,
and
you
have
this.
You
know
divided
control
in
the
cloud
where
you
know
someone
else
is
providing
computation
and
storage
for
you
and
you
don't
really
know.
If
what
they're
doing
with
your
computation
storage
is,
you
know
the
right
thing,
so
this
research
kind
of
aims
to
fix
that
problem
in
a
way
that
current
my
clients
cannot
verify
using
your
current
methods.
I
So
we'll
skip
over
this,
but
so
you
know
very
important
currently
in
the
clouds.
You
are
vulnerable
to
attacks
from
insiders
and
co-tenants,
and
you
know
using
secure
our
case.
You
can
protect
from
that
alright.
So
a
little
background
in
certificate.
Transparency
is
a
way
to
kind
of
improve
the
status
quo
in
the
public
key
infrastructure
ecosystem,
and
the
idea
is
that
all
certification
authorities
publish
their
certificates
in
a
public
append
only
log,
and
this
highlights
mishe
issued
certificates
in
particular.
I
If
you
connect
to
a
website
and
there,
the
certificate
certificate
you
get
from
them
is
not
in
the
log.
You
know
you
know
something's
up,
because
supposedly
all
certificates
are
supposed
to
be
in
a
lock.
On
the
other
hand,
if
malicious
certificate
appears
in
the
log
well,
you
can
now
see
that
it
is
in
fact
in
the
log
and
you
can
take
appropriate
action.
I
So
you
kind
of
multiple
these
logs
and
these
can
be
monitored
by
people
for
admission
shoot
certificates,
and
then
the
logs
can
also
be
audited
about
having
people
to
make
sure
that
these
logs
are
self
consistent
and
that
they
in
fact
are,
and
only
all
right,
so
goal
for
this
project
is
to
be
able
to
host
what
I
call
secure
services.
So
secure
servers
have
to
handle
user
data
securely,
they
have
to
protect
against
insider
attacks.
The
operation
of
the
servers
needs
to
be
somehow
verifiable
by
a
client
and
would
be
nice
if
legacy.
I
Clients
can
also
you
know,
have
some
security
from
this
system
and
there
should
be
some
incremental
deployment
path.
For
you
know,
most
practical
implementations
on
some
good
performance
and
also
software
updates
need
to
be
supported,
which
you
know
sometimes
people
in
the
research
community
kind
of
forget
all
right.
So
our
threat
model
is
that
an
adversary
is
able
to
control
the
network,
as
well
as
the
host
operating
system
running
our
secure
enclaves,
but
the
user
is
fully
trusted
as
well
as
as
client
and,
of
course,
a
secure.
I
I
I
I
So
you
know
as
a
strawman
proposal,
we
can
just
say:
okay,
the
client
you
know
needs
to
connect
to
the
server
and
then
request
the
remote
at
the
station
and
then
hopefully
it
all
works.
The
client
gets
back
this
remote
at
the
station,
which
is
assigned
signature,
whether
it
is
a
signature
over
the
hash
of
the
program.
So
this
do.
You
client
can
of
course
check
two
signature
and
banana
is
this
hash
looks
like
okay,
fine?
What
what
does
this
hash
represent?
Is
you
know?
I
So
you
know
you
might
be
able
to
build
a
client.
It
just
has
a
built-in
hash
for
your
specific
service,
but
then
how
you're
going
to
handle
updates,
because
are
you
going
to
send
out
a
new
client
every
time
you
update
your
server?
That's
knob
viously
not
going
to
happen.
Also.
If
there
are
many
sort
of
these
kind
of
services
out
there
are
you
going
to
distribute
a
client
for
every
service?
That's
also
seems
a
little
intractable,
so
main
question
we're
trying
to
solve
here.
Is
you
know?
I
How
do
you
know
which
of
these
code
identities
are
valid
and
secured?
Like
represents
some
secure
servers
that
you
want
to
connect
to
all
right.
So,
as
I
mentioned
before,
using
like
being
able
to
use
this
TLS
private
key
kind
of
indicates
that
you're
talking
to
this
secure
Enclave,
so
you
don't
really
need
a
live,
remote
and
cessation.
I
Instead,
you
can
just
somewhere
have
published,
and
at
a
station
that
indicates
that
particular
public
key
belongs
to
a
particular
enclave
right,
so
just
the
same
way
that
a
TLS
certificate
provides
is
binding
between
the
TLS
public
key
as
end
a
subject.
Name
example,
calm
and
that
this
at
the
station
can
provide
the
binding
between
particular
enclave
code
and
is
public
key.
So
now
that
you
both
these
two
things,
you
kind
of
have
a
binding
between
unclear
code
in
a
particular
certificate.
I
I
The
certification
authority
will
sign
a
certificate
and
upload
it
to
certificate
transparency,
log
and
the
attestation
will
be
sent
to
the
attestation
transparency
log.
The
certificate
will
go
back
to
the
secure
Enclave
in
the
server,
and
now
the
user
can
just
connect
to
the
server
and
verify
your
certificate.
I
And
now
anyone
can
go
and
look
at
the
attestation
transparency
log
and
see
what
service
is
tied
to
a
particular
public
key
and
then
use
a
certificate
transparency
log
to
look
at
what
like
domain
name
is
associated
with
that
public
key
and
therefore
what
service
is
a
soda
with
what
domain
name
all
right,
so
a
certificate
transparency.
You
have
this
ID
that
certification
authorities
publish
everything
old,
our
certificates
to
depend
only
log
which
will
highlight
miss
issued
certificates.
I
I
J
I
I
So
the
thing
with
STX
is
at
least
in
a
computer
security
resource
community
is
that
it
seems
to
be
kind
of
a
cure-all
like
everything
that
people
have
been
designing
crazy
crypto
for
for
the
past
20
years,
you
can
do
like
very
easily
in
sgx,
with
the
same
kind
of
like
trust
model,
except
now
you
have
to
trust
a
hardware.
In
addition
to
whatever
primitive
you
were
using
yeah
all
right,
any
other
questions.
