►
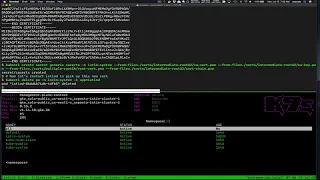
From YouTube: Istio 1.6 Deep Dive Certificate Rotation (Part 3)
Description
In this 4-part series, we look at how to rotate Istio CA certs without interruption.
In this section we look at how to trust multiple Root CAs to set up rotation without disruption
About us https://solo.io
Manage multi-cluster Istio with Service Mesh Hub https://solo.io/products/service-mesh-hub/
Istio 1.6 https://istio.io/latest/news/releases/1.6.x/announcing-1.6/
Questions? https://slack.solo.io
A
Thanks
again
for
continuing
along
with
this
video
series,
we
are
exploring
how
to
rotate
ISTE
O's
CA
signing
certificates
with
minimal
downtime.
In
previous
videos.
We
saw
that
changing
the
route
will
cause
downtime,
especially
going
from
and
SEO
self
sign
and
generated
root,
CA
to
maybe
one
that
you
want
to
use.
A
But
then
we
also
saw
that
if
you
rotate,
the
intermediate
certificates
and
those
intermediates
have
the
same
route
that
you
won't
see.
Downtime
and
now
in
this
video
video
3
we're
going
to
see
how
to
introduce
the
you
know
if
you
need
to
rotate
your
route
CA,
which
isn't
something
that
happens
very
often
but
will
happen,
and
you
need
to
be
able
to
handle
it
without
downtime.
A
What
we
want
to
do,
for
that
is
make
sure
that,
for
a
period
of
time
that
we're
able
to
trust
the
old
route
as
well
as
the
new
route,
so
that
we
don't
have
a
breakage
in
traffic
in
the
previous
videos
we
took,
we
saw
the
breakdown
and
the
structure,
and
we
can
do
it
again,
our
certificates.
So
far,
we
showed
that
for
certificates
or
intermediate
signed
by
route
a
so.
We
introduced
through
a
and
route
a
to
that
this
didn't.
A
A
A
Okay,
so
we're
going
to
create
the
CA
certs
with
we're
not
going
to
change
the
intermediate,
yet
we're
not
going
to
change
anything.
All
we're
doing
is
introducing
or
we're
changing
the
route
so
that
we
trust
both
a
and
B
routes.
It's
an
intermediate
chain
is
still
assigned
by
route
a
but
we're
introducing
the
the
routes
that
that
are
that
trust
both
a
and
B.
A
A
A
A
A
But
we
shouldn't
see
that
here
all
we've
done
is
introduced,
route,
B
haven't
changed
the
CAS
or
the
the
we
haven't
changed
the
intermediate
yet
so,
if
you
make
this
collar
should
work,
and
it
does
now
in
the
next
video
we're
going
to
introduce
the
CA
that's
been
signed
by
B
and
the
pods
now
should
trust
both
a
and
B.
So,
even
though
we're
rotating
the
route
we
shouldn't
see
any
breakage
in
the
communication
stay
tuned
to
the
next
video.
