►
Description
No description was provided for this meeting.
If this is YOUR meeting, an easy way to fix this is to add a description to your video, wherever mtngs.io found it (probably YouTube).
A
Let's
go
through
a
typical
use
case
for
threat
detection.
I
have
slack
set
up
as
a
notifier
in
my
stack
rocks
platform,
and
it
just
told
me
that
there
is
a
deployment
that
has
been
spawned
with
a
read,
write,
root
file
system
and
then
that
same
deployment
of
process
with
uid
0
has
been
launched.
So
I'm
going
to
click
on
the
link,
and
this
is
going
to
bring
me
directly
to
those
violations
that
I
just
saw
in
my
notifier.
A
I
can
see
a
variety
of
things
from
ubuntu
package
manager
getting
executed
to
a
container
using
a
read,
write
file
system
and
then
also
just
in
general,
the
process
with
uid
0..
Now
I
can
see
that
over
15
binders
were
executed
with
19
different
arguments
using
that
uid
0.
You
can
see
the
container
id
the
exact
arguments
the
time
stamp
on
when
that
was
executed,
and
I
can
see
in
this
case
the
potential
attacker
had
installed.
A
A
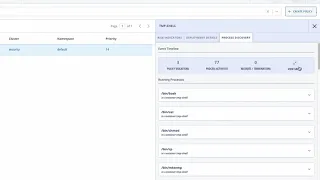
One
of
the
things
I
can
do
is
if
I
want
to
get
some
more
forensics
into
this,
I'm
going
to
head
over
to
the
wrist
tab
and
I'm
going
to
specifically
look
for
that
deployment
and
I'm
going
to
look
for
the
temporary
shell
and
once
I
find
this,
I'm
actually
going
to
go
over
to
process
discovery,
and
I
want
to
view
a
timeline
of
some
of
these
events.
So
this
will
show
me
the
pod-
and
this
is
also
going
to
show
me
every
single
list
of
executable
processes
within
this
pod.
A
It's
going
to
show
me
the
exact
timeline
of
when
those
events
happened,
how
they
happened,
and
I
can
look
at
these
events,
including
container
restarts
and
terminations
and
anything
else.
I
can
even
drill
down
into
this
and
view
it
within
the
container.
If
I
had
multiple
containers
to
see
how
that
was
executed
and
then
using
this
information,
I
could
even
export
this
for
the
purpose
of
forensics
and
analysis
and
send
this
to
some
of
my
teammates.
So
this
is
an
example
of
how
you
get
detected
on
a
threat.
