►
From YouTube: UniMatrix Technical Board Call 2021-08-31
A
B
B
D
D
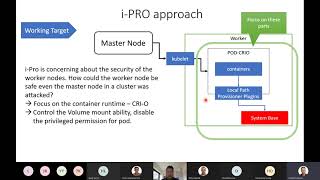
So
we
are
concerned
about
how
we
can
protect
our
working
note,
because
in
the
reals
in
in
the
real
life,
maybe
the
hacker
they
can
attack
to
the
master
node.
I
assume
so
when
the
at
the
master
node
will
hide
it
by
the
the
hacker.
So
he
can
deploy
some
ports
that
have
fully
permissions
to
access
to
the
system
and
so
from
that
he
scan
fully.
D
So
our
target
in
here
is
that
we
will
focus
on
the
container
runtime
we're
using
the
we
will
increase,
improve
the
security
for
the
container
run
temp
and
in
years
we
select
the
trial
and
the
function
that
we
want
to
to
add
to
improve.
The
security
is
that
we
want
to
control
fully
control
the
the
bomb's
melting
function,
abilities
and
also
we
will
dispose
the
privilege
port
permissions,
so
it's
at
least
this
can
prevent
the
masternode
deploy
the
the
ports
that
have
the
privilege
permissions.
D
So,
with
this
target,
we
have
two
methods
from
the
method:
one
we
can.
I
think
we
can
using
the
some
control
the
linux
kernel.
Security
modules
like
app
are
more
or
similar
notes,
but
with
this
approaching,
we
have
to
add
some
attrition
libraries
or
our
dependencies
so
and
also
we
maybe
have
to
change
something
in
our
kernels,
so
we
want
to
avoid
it
at
the
first
time.
D
D
D
But
after
with
the
the
previous
methods
we
found,
they
have
some
support
that
we
need
to
consider-
and
I
think
with
this
point
here-
is
that
in
the
case
that
if
the
hacker
they
can
create
a
fake
port,
I
mean
he
deploy
a
port
that
has
the
same
or
quite
similar
permissions
with
the
normal
port.
So
maybe
he
can
freely
to
accept
to
the
system
base
without
the
chinese
without
the
energy
acknowledged
from
the
worker.
Note.
D
B
A
Yeah
well
answer
all
this
one
way
I
mean,
so
we
don't
actually
have
a
specific
device
for
orchestration
the
device
requirements
for
the
orchestration,
we're
just
using
our
already
existing
app
guys.
That's,
but
that's
not
a
standardized
api,
so
that's
part
of
our
native
apis
for
managing
devices
and
so
on.
B
B
Maybe
the
ecosystem
can
be
selected
by
the
integrators
freely.
Therefore,
so
in
case
of
eyebrow,
so
I
will
try
to
use
the
kubernetes,
in
addition,
so
in
case
of
actually
subtract
to
use
the
ansible
and
the
container,
maybe
docker
and
therefore
so
so
far.
So
we
we
try
to
share
the
both
of
them
with
the
users.
B
It
means
we
we
should
provide
the
both
of
the
reference
implementation.
So
in
this
meeting,
so
I
would
like
to
discuss
the
security
and,
of
course,
so
so
the
invest
according
to
the
investigation.
Until
now,
so
ipro
found
several
issues
about
the
community
security.
However,
so
we
will
continue
a
continuously
investigate
the
security
about
kubernetes,
and
so
we
will
solve
all
issues
by
the
uni
matrix
version
1.0.
B
A
A
B
E
E
E
This
is
an
example
and
our
entry
is
ended,
using
device
control
load
and
remove
using
device
denied.
For
instance,
we
can
echo
this
three
into
the
c
group
interface,
so
this
this
means
allow
the
cpu
cgroup
1
to
read
and
make
node
the
device,
usually
known
as
the
dv
knot
and
doing
echo
er
a
to
the
file
system
like
this
means
we'll
remove
all
the
with
all
the
other
device
permissions.
E
And
about
this
is
called
using
this
comp.
This
compa
is
the
computer
and
it's
a
computer
security
facility
in
this
kernel
which
allow
a
represent
to
make
a
one-way
transition
into
a
security
state
where
it
cannot
make
any
system
called
expat.
Xd
signal
return,
read
write
to
a
already
open
file
decrypter,
and
we
can
enable
this
call
model
through
cisco
and
cisco.
E
E
Then
we
save
the
configure
file
and
try
to
load
container
with
the
second
configure.
Above
then
we
can
run
docker,
commander
and
load
this
configure
file.
So
in
this
container
we
we
deny,
we
deny
change
models.
This
call,
so
the
contender
will
return
fair
when
he
when
he
wants
to
chat-
and
you
want
to
change
mode
of
a
file
in
container
in
the
last
about
the
file
and
capability.
E
E
E
E
E
A
Yeah
one
comment:
I
mean
app
armor
and
sec
comp.
You
have
different
sections
on
that,
but
they
are
basically
doing
similar
things
that
that
I
mean
sec.
Comp
is
also
an
lsm,
so
it's
either.
Actually
you
can
use
both
of
them.
At
the
same
time,
I
guess
it's
a
kernel
option
that
you
enable
so
both
of
them
are
cisco,
provides
prevent
cisco.
I
think
app
armor
can
also
do
more
things.
App
armor
can,
for
example,
filter
also
access
to
debussed
services.
A
A
Yeah,
but
the
problem
is
that,
let's
say
the
let's
say
you
make
a
an
application
that
is
supposed
to
run
on
a
camera,
and
then
one
camera
is
using
second
and
another.
Camera
is
using
app
armor
and
basically
that
application
will
have
to
provide
a
app
armor
profile
and
a
second
both
of
these
kind
of
profiles
to
be
able
to
run
with
the
container
runtime.
So
it's,
but
these
things
can
be
automatically
generated
by
some.
A
A
Yeah
but
independently,
if
you're,
using
an
lsm
like
a
farmer
or
second,
the
the
same
principle,
the
this
is
global
in
your
system
so
independently.
If
they
run
in
a
container
or
if
they
run
natively
on
the
os
it
they
you
have
to
provide
when
you
run
an
application,
even
if
it's
inside
the
container
it's
outside.
C
A
A
A
So
yeah
that's
one
thing:
we
should
also
have
a
look.
I'm
not
sure
how
good
the
gitlab's
security
scanning
is
and
one
another
thing
is
to
reduce
the
attack
surface
by
minimizing
the
containers.
So,
for
example,
there's
a
tool
called
docuslim
which
does
this.
It
checks
what
whatever
libraries
that
an
application
is
using
and.
A
A
Things
like
app
armor
profiles,
so
it
will
check
whatever
system
calls
that
your
application
is
making
and
create
an
app
armor
profile
for
the
application
that
you
can
include
the
same
thing
for
second,
I
think
I
haven't
tried
this
part
myself.
I've
I've
used
docker
slim
to
kind
of
to
minimize
the
runtime
containers
that
we
that
we
have
in
our
index,
samples
like
for
larot
and
for
dbus
and
so
on.
A
So
this
can
be
quite
easily
done
by
enabling
some
compiler
flags
and
linker
flags
it
at
the
cost
of
some
runtime
cost.
I
think
you
can
lose
like
five
percent
five
to
ten
percent,
what
I've
seen
so
depending
on
on
which
flags
you
enable
so
and
then
we
come
to
the
lsms.
So
I
think
we
should
generate
profiles
for
for
some
for
the
either
for
app
armor
or
for
second
or
for
both
of
them.
So
when
you
do,
when
you
write
an
application,
you
will,
you
will
include.
A
A
A
A
A
A
A
B
B
B
A
I'm
not
sure
I
should
do
all
of
that,
so
I
can
take
care
of
a
few
this,
but
also
I'm
not
sure
we
are.
I
mean
at
this
point.
I
still
think
this
is
up
in
the
air
to
be
decided.
It's
not.
These
are
just
these
six
bullets
that
we
I
wrote
down
is
just
some
that
came
from
the
top
of
my
head.
I'm
sure
there
are
more
things
to
to
think
about
so
at
this
point
not
sure
if
we
can
make
something
really
concrete,
but
yeah
I
can.
A
A
A
B
A
A
A
B
E
B
B
A
A
So
you,
some
other
program,
must
open
these
files
to
this
to
the
debuss
system
socket.
So
it's
probably
not
a
lot
of
work
to
do
that,
but
I
had
a
look-
and
I
just
found
it
was
much
it's
easier.
It
was
easier
for
me
to
use
the
bus
daemon
for
the
sample,
but
it's
definitely
possible
to
use
debuss
broker,
but
then
we
have
someone
has
to
write
a
small
launcher
that
will
open
these
open
the
socket
or
create
it
if
it's
needed
and
then
pass
it
on
cd
bus
pro.
