►
From YouTube: Contour Community Meeting - April 14, 2020
Description
April 14, 2020
What have we been working on?
Upgrade Envoy go-control-plane #2432 @stevesloka
Upgrade Envoy v1.14.1 #2434 @stevesloka
Improve diagnostics for Secrets errors #2422 @jpeach
Updates to annotations docs for new ingress-class behaviour #2420 @youngnick
External client certificate authentication feature concluded #2390 #2410 #2250 @tsaarni
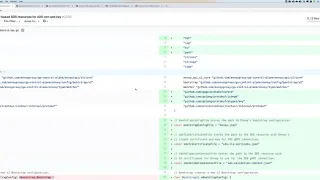
Work in progress: support for Envoy xDS certificate rotation by bootstrap config change #2333 @tsaarni
Contour donation to CNCF update
Issue discussion
The separation of metrics and health serving has been merged and will be available in Contour 1.4, due for release in two weeks time.
A
Hi
everyone
and
welcome
to
today's
meeting
the
contour
community
meeting
today
is
April
14th
2020
and
where
this
is
the
Americas
time
zone
meeting,
even
though
we
have
people
from
Australia
joining
us
today,
which
is
fantastic,
so
thank
you
so
much
yeah
we've
got
a
few
updates
that
we
want
to
go
through
today.
So
I'm
gonna
share
my
screen,
so
you
all
could
see
the
agenda
there.
We
go
so
Steve
you're
on.
B
B
So
when
we
go
to
talk
to
envoy
and
we
pass
down
and
set
up
that
XDS
connection,
we
use
all
the
types
that
exist
so
that
control
plane
gets
upgraded
from
time
to
time
and
it
kind
of
falls
in
step
with
the
Envoy
versions
at
times
that
control
plane
can
cause
changes
and
breaks
into
contours
codebase,
in
the
sense
that
hey
this
thing
was
was
an
object.
Now
it's
a
pointer
and
that
sort
of
thing.
So
this
is
just
helping
us,
keep
a
kind
of
lock
in
step
with
with
that
envoy,
those
types
and
stuff.
B
The
additional
thing
is
that
they're
starting
to
add
in
the
v3
XDS
API.
So
at
this
point
since
envoy,
1.14
that
one
got
released,
they've
frozen
the
the
v2
XDS
api,
which
is
what
contour
use
this
today.
So
no
no
features
gonna
go
into
there.
All
the
works
gonna
go
into
the
v3,
but
the
envoy
team
promised
that
they
would
keep
compatibility
for
v2
and
v3
forward.
B
So
I
think
at
some
point
we
should
look
at
moving
to
v3
assuming
everything's
in
there
I'm,
not
sure
everything
is
but
anyway.
So
this
is
just
keeping
keeping
kind
of
you
know.
Maintenance
update
and
the
second
one
I
added
was
adding
the
contour
envoy
1.14
that
one
got
released.
I
think
there
was
some
CI
issue
that
they
had
ended,
pulling
one
that
14.0
so
that
one
not
working
that
one.
B
B
D
Basically
now
in
the
contour
logs,
when
when
there
is
a
problem
with
a
secret,
you'll,
actually
get
a
little
bit
more
information
about
which
sequence
effect
was
affected
and
what
the
exact
problem
was
previously.
The
error
message
was
basically
hey.
There
was
a
problem
with
the
secret.
Now
you'll
actually
get
a
problem
with
a
message
that
tells
you
various
different
things
about
the
secret
and
then.
D
D
D
This
one
we
changed
in
control,
1.3,
we
changed
the
English
class
behavior
and
we've
had
a
few
customer
queries
about
this
one
previously
quite
a
few,
and
so
this
one
is
just
updating
the
docs
to
actually
match
what
new
behaviours
the
new
behavior
is
that
the
important
part
is
if
you
set
an
English
class
to
contour,
so
the
direct
contour.
Please
please
listen
to
this
English
class.
It
will
now
listen
to
only
that
English
class.
D
So,
yes,
I
specified
exactly
what
happens
in
each
case.
If
you
don't
specify
an
ingress
costs,
the
backwards
compatible
thing
we
needed
to
support
is
that
if
you?
So
if
you
don't
specify
an
English
class
to
contour
the
program,
you
can
still
specify
an
English
class
of
contour
on
ingresses
and
have
contour
pick
it
up
by
default.
If
you
don't
configure
that
again
backwards
compatibility
there.
So
that's
why
it
was
a
little
bit
complicated
to
explain
yeah.
So
that
was
the
point
of
that.
It's
just
to
make
sure
that
the
documentation
is
correct.
A
C
So
so
now
we
finalized
the
external
client
certificate.
Authentication.
The
the
first
PR
in
the
list
of
PR
theories
is
the
one
that
was
pending
pending
class.
These
other
ones
like
like
this
documentation.
One
was
a
bit
earlier,
but
the
last
one
was
was
a
pending
for
big
because
of
the
team
SMI,
it's
a
nine
name,
binding
work
that
centrist
was
doing
ordinary
Burke,
that
James
was
doing
and
and
after
that
was
finalized,
we
finalized
the
API
parts
which
are
now
merged.
Today,.
C
It
is,
it
is
not
possible,
then,
for
external
clients
to
to
to
use
client
certificates
and
I
will
will
will
check
that
validate
that
according
to
a
CA
or
or
or
a
bundle
of
CIA's
if
needed.
That's
that's
basically
it
for
that,
and
then
there
is
another
one
that
has
been
also
ongoing
for
quite
a
while.
C
We
previously
concluded
the
support
for
rotating
certificates
at
the
contour
and
for
this
XTS
gr,
pc
connection,
and
now
now
I
got
changed
also
merged
in
any
way
that
it
can,
and
we
also
can
rotate
its
own
in
this
case,
client
certificate
that
it
uses
when
connecting
to
to
contour.
But
there
is
still
one
change
which
which
is
now
this
working
process.
We
are
in
order
to
take
that
certificate,
rotations
report
in
and
go
into
use.
C
There
is
a
need
to
change
the
anyway
bootstrap
configuration
that
contour
creates
when,
when
running
the
controller,
bootstrap
command,
and
the
idea
here
is
that
we
need
couple
of
new
files
in
addition
to
their
old
bootstrap
file.
These
new
files
are
presenting
the
SDS
resources
which,
which
typically
in
in
a
normal
case
when
contour,
is
serving
SDS
resources
to
anyway.
They
they
are
sent
by
out
the
TR
PC
connection,
but
obviously
because
this
is
now
about
G,
RPC
connection
or
two
certificates
that
are
needed
before
the
TR
PC
connection
is
established.
C
So
these
SDS
resources
are
now
written
as
files
in
the
file
system
by
this
bootstrap
command.
So
if
you
go
back
to
the
text
text
part
of
this,
what
the
conversation
port
there
in
the
second
comment
from
from
yeah
this
one
here
here,
is
an
example
that,
besides
of
this
quality,
Kenworth
Jason,
we
alternate
to
other
other
resources
other
occasion,
files
that
represents
these
resources
as
files,
and
you
know
that
there
is
still
the
approach:
how
how
to
change
the
contour
bootstrap
command-line
parameters
to
make
it
make
it
possible
to
create
these
new
files.
C
D
Yeah
so
I
think
the
problem.
The
problem
here
is
that
the
students
that
the
the
way
that
envoy
has
implemented
this
thing
and
needs
those
three
files
and
we
gotta
have
somewhere
to
put
it
there.
So
the
I
don't
think
it's
the
there
is
it
has
to
it
needs
to
be
injected
in
order.
So
basically,
in
order
for
envoy
to
do
this,
that's
why
it
needs
to
be
injected
and
that's
why
it's
not
that
users
need
to
inject
a
per
se.
D
It's
that,
in
order
for
this
to
be
able
to
be
hot
reloaded,
we
need
to
inject
it
talking.
We
need
the
bootstrap
to
inject
this
stuff
in
the
right
way,
so
that
once
we
do
that,
then
the
we
can
reference,
the
secrets
that
we
for
for
those
things
in
communities
and
it
will-
and
it
means
that
then,
when
you
update
those
secrets,
both
envoy
and
contour,
will
automatically
rotate
the
sequencing
use
so
that
there's
no
restarting
and
required
so.
B
D
B
D
The
problem
here,
though,
is
that
it's
not
just
those
three
files
that
one
needs
all
the
way
actually
needs
to
additional
like
basically,
they
like
substitute,
protobuf
files
that
says
that
that
lets
you
fool
SDS
into
using
into
using
the
actual
cert
files
as
a
source
port.
So
it's
a
secret
data
and
so
there's
actually
two
extra
files
that
need
aside
from
the
envoy,
jason
config
yeah,
that's
them
there
that
are
just
on
the
screen,
they're
literally
just
a
little
a
little
text
file.
D
D
C
C
These
like
product
of
JSON
representations
from
from
the
disk
and
in
in
the
boot
configuration
in
the
TLS
configuration
you
can
you
can
either
you
can
in
any
way.
You
can
point
into
like
directly
to
do
certificate
files
like
that
they
put
stuff
that
we
used
today,
but
there
is
an
alternative
also
to
point
into
SDS
resource,
and
in
that
description
of
SDS
resource
you
can
either
point
to
an
SDS
resource
in
in
the
XDS
server
or
a
file
in
a
file
system,
and
this
was
something
that
existed
already
there
there
before.
C
D
I
said
it
so
the
short
version
is
because
I'm
away,
yeah
and
the
slightly
longer
version
is
you
can't
inline
those
files
into
the
bootstrap
config.
They
need
to
be
separate
files
because,
because
this
is
like
connecting
to
another
cluster
I'm
using
the
using
air
quotes
there.
That
just
happens
to
be
served
out
of
a
file
on
disk.
Instead
of
you
know,
instead
of
talking
back
to
the
main
console
cluster,
we
learn
a
better
way
to
is.
That
is
another
way
to
explain
in
storage.
Oh
yeah,.
D
Does
that
clear
up
a
little
bit
white
wine
needs
to
be
separated.
It's
just
it's
just
envoy
needs
of
like
that,
because
of
the
way
that
the
it
presents
actually
a
different
cluster.
That
we
are
you
yeah
I
mean
I
agree
would
be
really
nice
if
we
didn't
need
to
output
two
extra
files
for
four
reasons,
but
I
mean
it
seems
like
they're
just
onward
reasons,
and
this
comes
on
hashtag,
just
long
boy,
things
sure.
B
Yeah
I
mean,
if
that's
what
it
is,
it's
what
it
is.
I
just
worry
that
excuse
me
that
folks
could
abuse
that
somehow,
but
maybe
I'm
I
need
to
look
at
the
the
docs
and
see
see
how
those
files
are
used
in
stuff.
A
little
better,
so
I
understand,
yeah
you
better.
My
initial
reaction
was
I
was
worried
that
people
would
start
abusing
the
boostrap
to
like
turn
on
different
things.
They
wanted
to
folks
are
always
like:
hey
I'm
gonna
go.
Do
X,
Y,
&
Z,
you
know
and
they've
tried
it
like.
D
Yes,
I'm
saying
if
you
could
have
a
look
at
that,
that
would
be
great.
You
know
so
I
think
I
think,
because
the
bootstrap
is
now
just
saying
when
you
turn
that
on
though
the
bootstrap
is
just
saying,
look
in
this
direct
like
look
here
for
specific
SDS
resources,
I,
don't
think,
there's
a
way
that
you
can
without
changing
the
go
code
that
does
the
bootstrap
that
you
can
actually
like.
Have
it
do
anything
else,
I
think.
A
E
I'll
give
it
a
quick
update,
so
the
as
you
all
know,
we
have
been
undergoing
donation
of
contour
to
CN
CF,
it's
process
going
well.
Sikh
Network
has
finished
its
assessment
thumbs
up
there
and
the
last
part
right
now
is
a
lot
of
people
that
use
contour.
Don't
want
to
be
disclosed
publicly
that
they're
using
contour.
That
has
been
the
case
with
a
lot
of
networking
products,
and
things
are
kind
of
sitting
at
the
front
door
of
your
infrastructure
and
at
the
front
door
of
your
clusters
and
your
your
cloud
native
apps.
E
So
what
we're
doing
is
a
mod
client
who
is
our
TOC
sponsor,
put
him
in
contact
with
several
of
the
customers
and
and
in
the
users
of
contour
there's
a
few
companies
that
are
basically
talking
to
you
in
private.
So
hopefully
good
things
are
being
told
in
those
discussions.
I'm
just
clearing
my
throat
here
and
you
know,
and
if
all
goes
well,
maybe
it's
gonna
be
put
up
for
a
vote
in
the
next
couple
of
weeks.
A
D
F
Hi
I'm,
just
just
one
question:
it's
the
one
thing
that
we're
sort
of
waiting
on
for
some
more
internal
compliance
reason.
It
is
separation
of
their
health
from
the
metrics
endpoints
I
know.
There's
a
merge,
PR
I,
think
that
looks
like
it's
slated
for
1.4
and
just
wondering
if
there's
any
guidance
on
when
1.4
is
gonna,
when
we
think
that.
E
End
of
this
month,
so
look
for
it
baby.
You
know
good
might
be
right
at
the
edge
at
the
cusp
of
the
month
we
tried
to
ship
monthly
now
Mike
also
come
to
the
cadence
were
every
month.
Whatever
is
on
the
track.
Will
ship
no
matter
what
so
we're
not
gonna
I
mean.
Maybe
we'll
wait
a
few
days
here
and
there,
depending
on
a
critical
feature.
E
A
Alright,
alright
and
that's
it
for
today.
Thank
you
so
much
for
for
joining
everyone.
Oh
thank
you
so
much
for
the
discussion
here,
I'll
post,
the
recording,
of
course
up
on
YouTube
later
today,
and
with
that
see
you
all
on
the
next
community
meeting.
As
you
all
know,
we
host
them
bi-weekly
in
different
time
zones,
so
yeah
just
keep
a
look
out
on
the
project:
contoured
io
/
community
page.
If
you
have
any
questions
on
when
that
is,
and
with
that
have
a
great
day,
everyone
thank.
